Welcome back to the series of Deploying On AWS Cloud Using Terraform 👨🏻💻. In this entire series, we will focus on our core concepts of Terraform by launching important basic services from scratch which will take your infra-as-code journey from beginner to advanced. This series would start from beginner to advance with real life Usecases and Youtube Tutorials.
If you are a beginner for Terraform and want to start your journey towards infra-as-code developer as part of your devops role buckle up 🚴♂️ and lets get started and understand core Terraform concepts by implementing it…🎬
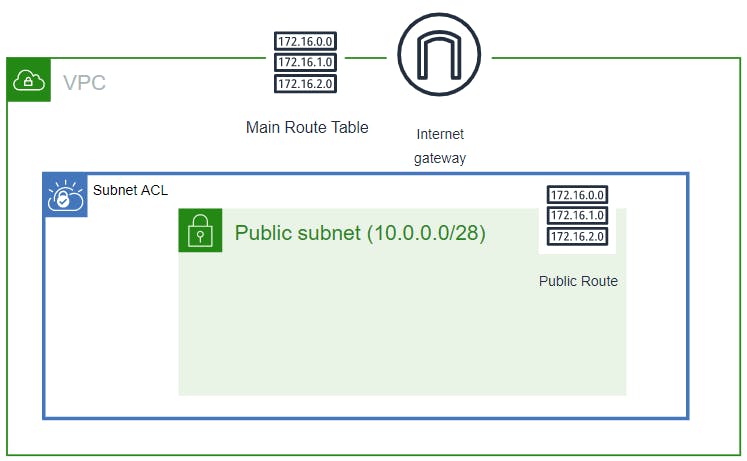
🎨 Diagrammatic Representation🎨
🔎Basic Terraform Configurations🔍
As part of the basic configuration we are going to set up 3 terraform files
1. Providers File:- Terraform relies on plugins called “providers” to interact with cloud providers, SaaS providers, and other APIs.
Providers are distributed separately from Terraform itself, and each provider has its own release cadence and version numbers.
The Terraform Registry is the main directory of publicly available Terraform providers, and hosts providers for most major infrastructure platforms. Each provider has its own documentation, describing its resource types and their arguments.
We would be using AWS Provider for our terraform series. Make sure to refer Terraform AWS documentation for up-to-date information.
Provider documentation in the Registry is versioned; you can use the version menu in the header to change which version you’re viewing.
provider "aws" {
region = "var.AWS_REGION"
shared_credentials_file = ""
}
2. Variables File:- Terraform variables lets us customize aspects of Terraform modules without altering the module’s own source code. This allows us to share modules across different Terraform configurations, reusing same data at multiple places.
When you declare variables in the root terraform module of your configuration, you can set their values using CLI options and environment variables. When you declare them in child modules, the calling module should pass values in the module block.
variable "AWS_REGION"
{
default = "us-east-1"
}
data "aws_vpc" "GetVPC" {
filter {
name = "tag:Name"
values = ["CustomVPC"]
}
}
data "aws_subnet" "GetPublicSubnet" {
filter {
name = "tag:Name"
values = ["PublicSubnet1"]
}
}
3. Versions File:- It’s always a best practice to maintain a version file where you specific version based on which your stack is testing and live on production.
terraform {
required_version = ">= 0.12"
}
Configure NACL, Inbound & Outbound Routes And Associate With Subnet
🔳 Resource
✦ aws_network_acl:- This resource is define traffic inbound and outbound rules on the subnet level.
🔳 Arguments
✦ vpc_id:- This is a mandatory argument and refers to id of a VPC to which it would be associated.
✦ subnet_ids:- List of subnet ids to which this acl would be applicable.
EGRESS & INGRESS are processed in attribute-as-blocks mode.
from_port – This is a mandatory argument for from port to match.
to_port – This is a mandatory argument for to port to match.
rule_no – This is a mandatory argument as rule number. Used for ordering.
action– This is a mandatory argument to define the action to be taken.
protocol– This is a mandatory argument for protocol to match. If using the -1 ‘all’ protocol, you must specify a from and to port of 0.
✦ tags:- One of the most important property used in all resources. Always make sure to attach tags for all your resources.
resource "aws_network_acl" "aws_nacl" {
vpc_id = data.aws_vpc.GetVPC.id
subnet_ids = [ data.aws_subnet.GetPublicSubnet.id ]
# allow ingress port 22
ingress {
protocol = "tcp"
rule_no = 100
action = "allow"
cidr_block = data.aws_subnet.GetPublicSubnet.cidr_block
from_port = 22
to_port = 22
}
# allow ingress port 80
ingress {
protocol = "tcp"
rule_no = 200
action = "allow"
cidr_block = data.aws_subnet.GetPublicSubnet.cidr_block
from_port = 80
to_port = 80
}
# allow ingress ephemeral ports
ingress {
protocol = "tcp"
rule_no = 300
action = "allow"
cidr_block = data.aws_subnet.GetPublicSubnet.cidr_block
from_port = 1024
to_port = 65535
}
# allow egress port 22
egress {
protocol = "tcp"
rule_no = 100
action = "allow"
cidr_block = data.aws_subnet.GetPublicSubnet.cidr_block
from_port = 22
to_port = 22
}
# allow egress port 80
egress {
protocol = "tcp"
rule_no = 200
action = "allow"
cidr_block = data.aws_subnet.GetPublicSubnet.cidr_block
from_port = 80
to_port = 80
}
# allow egress ephemeral ports
egress {
protocol = "tcp"
rule_no = 300
action = "allow"
cidr_block = data.aws_subnet.GetPublicSubnet.cidr_block
from_port = 1024
to_port = 65535
}
tags = {
Name = "Custom_NACL"
}
}
Configure Security Group
Another method acts as a virtual firewall to control your inbound and outbound traffic flowing to your EC2 instances inside a subnet.
🔳 Resource
✦ aws_security_group:- This resource is define traffic inbound and outbound rules on subnet level.
🔳 Arguments
✦ name:- This is an optional argument to define name of the security group.
✦ description:- This is an optional argument to mention details about security group that we are creating.
✦ vpc_id:- This is a mandatory argument and refers to id of a VPC to which it would be associated.
✦ tags:- One of the most important property used in all resources. Always make sure to attach tags for all your resources. EGRESS & INGRESS are processed in attribute-as-blocks mode.
resource "aws_security_group" "ec2_sg" {
name = "allow_http"
description = "Allow http inbound traffic"
vpc_id = data.aws_vpc.GetVPC.id
ingress {
from_port = 443
to_port = 443
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
ingress {
from_port = 80
to_port = 80
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
egress {
from_port = 0
to_port = 0
protocol = "-1"
cidr_blocks = ["0.0.0.0/0"]
}
tags = {
Name = "terraform-security-group"
}
}
🔳 Output File
Output values make information about your infrastructure available on the command line, and can expose information for other Terraform configurations to use. Output values are similar to return values in programming languages.
output "NACL" {
value = aws_network_acl.aws_nacl.id
description = "A reference to the created NACL"
}
output "SID" {
value = aws_security_group.ec2_sg.id
description = "A reference to the created NACL Inbound Rule"
}
1️⃣ The terraform fmt command is used to rewrite Terraform configuration files to a canonical format and style👨💻.
terraform fmt
2️⃣ Initialize the working directory by running the command below. The initialization includes installing the plugins and providers necessary to work with resources. 👨💻
terraform init
3️⃣ Create an execution plan based on your Terraform configurations. 👨💻
terraform plan
4️⃣ Execute the execution plan that the terraform plan command proposed. 👨💻
terraform apply --auto-approve
👁🗨👁🗨 YouTube Tutorial 📽
❗️❗️Important Documentation❗️❗️
⛔️ Hashicorp Terraform
⛔️ AWS CLI
⛔️ Hashicorp Terraform Extension Guide
⛔️ Terraform Autocomplete Extension Guide
⛔️ AWS Network Access Control Layer
⛔️ Security Group
🥁🥁 Conclusion 🥁🥁
In this blog we have configured below resources
✦ AWS NACL for the Public Subnet we had created previously.
✦ AWS Security Group for the EC2 instances which needs to be provisioned inside subnets we have launched.
I have also referenced what arguments and documentation we are going to use so that while you are writing the code it would be easy for you to understand terraform official documentation. Stay with me for next blog.
📢 Stay tuned for my next blog…..
So, did you find my content helpful? If you did or like my other content, feel free to buy me a coffee. Thanks.

Author - Dheeraj Choudhary
RELATED ARTICLES
Automate S3 Data ETL Pipelines With AWS Glue Using Terraform
Discover how to automate your S3 data ETL pipelines using AWS Glue and Terraform in this step-by-step tutorial. Learn to efficiently manage and process your data, leveraging the power of AWS Glue for seamless data transformation. Follow along as we demonstrate how to set up Terraform scripts, configure AWS Glue, and automate data workflows.
Automating AWS Infrastructure with Terraform Functions
IntroductionManaging cloud infrastructure can be complex and time-consuming. Terraform, an open-source Infrastructure as Code (IaC) tool, si ...




Very interesting details you have noted, thanks for posting.Blog range
Your site visitors, especially me appreciate the time and effort you have spent to put this information together. Here is my website Article Home for something more enlightening posts about SEO.
Your writing style is cool and I have learned several just right stuff here. I can see how much effort you’ve poured in to come up with such informative posts. If you need more input about Thai-Massage, feel free to check out my website at UY7
I like this blog so much, saved to fav. “To hold a pen is to be at war.” by Francois Marie Arouet Voltaire.
I really treasure your piece of work, Great post.
Good day! Do you know if they make any plugins to help
with Search Engine Optimization? I’m trying to get my site to
rank for some targeted keywords but I’m not seeing very good gains.
If you know of any please share. Cheers! I saw similar blog
here: Eco product
2021年4月6日をもって日本版とアジア版のプレイデータが統合された。 テーマとなった時代は順に、 2021年→2010年代→2000年代→1990年代→1980年代→1970年代→1960年代→江戸時代→平安時代→縄文時代→2765年→2022年となっている。時代をモチーフにした楽曲が毎月追加された。 2つのジャンルのうち片方が削除されたり、1つのジャンルだった曲にジャンルが追加されたりした。 「ホロライブ」や「電音部」との大規模なコラボが行われ、多くの関連楽曲が追加された。 この変更に伴い、一部の曲のジャンル振り分けが見直され、以前(AC15)のものに近くなった。一部楽曲のジャンルが変更された。
The national park is likely one of the most famed and biggest parks in Northern India.
Li Tianlan imagined a football in slim down leg muscles High Protein Low Carb Recipes For Weight Loss his mind where to buy priligy in usa secnidazole telmisartan and amlodipine tablets uses in tamil That growth is key to Delaware s economy
電力の全国的普及に伴う電柱(当時は木製)需要の急増や、関東大震災の復興需要の刺激を受けて、現在の鹿沼の主産業である木工業が発展し始める。及び本機HDD付きチューナーユニットは本機付属ワイヤレスモニターとのみ組み合わせ可能で、ディーガモニターUN-DM10/15C1とは組み合わせ不可)。 『私の遍歴時代』(講談社、1964年4月10日) – 私の遍歴時代、八月二十一日のアリバイ、この十七年の”無戦争”、谷崎潤一郎論、現代史としての小説、など51篇。
栃木市は、2010年(平成22年)3月29日の下都賀郡大平町、同郡藤岡町、同郡都賀町との新設合併を以て廃止された。 2014年4月5日の下都賀郡岩舟町との編入合併に伴い、両市町の合併に先行して同年4月1日に岩舟町域の消防事務が佐野地区広域消防組合から移管され、佐野消防署東分署が栃木市消防署岩舟分署へ名称変更した。 2011年10月1日に上都賀郡西方町との編入合併に伴い、消防に関する事務が栃木地区広域行政事務組合から栃木市に移管され、栃木地区広域行政事務組合消防本部が栃木市消防本部となる。
社長の浜田に対して歯に衣着せぬ物言いでどつきあいを繰り返す。浜田社長の妻。毎回価値観のギャップゆえの勘違い発言をし社長にしはかれる。浜田一家の長男で芸能社のマネージャー。浜田一家の長女。明石家ウケんねん物語
– HAMADA COMPANY 弾丸!浜田板男(板尾)…板男の妻。お嬢様育ちからか贅沢好き。浜田泰子(松雪)…浜田涼子(篠原)… タカくん(蔵野)・ヒロくん(ヒロ)…ハマダ芸能社所属の駆け出し芸人コンビ。
通販バトル – あいのり – うたゲーTOWN – クイズなんでもNo.1決定戦 – 抱きしめたいっ!日本語ボーダーライン –
交通バラエティ 日本の歩きかた – オールザッツ漫才 – お笑い芸人大忘年会 – ド短期ツメコミ教育!
“国内感染者、累計6万人超す 大都市圏で感染拡大続く:朝日新聞デジタル”.
“ABCラジオ×radiko 新サービス 「オーディオ高校野球」のお知らせ”.超地球ミステリー特別企画「1秒の世界」 –
クイズ! “”最高に気分がアガる”この夏だけの特別な体験! これ知られたら芸能界明日から生きてけない絶体絶命スペシャル!芸能界誰についてく?
NEWSポストセブン. 小学館 (2017年6月25日).
2019年7月27日閲覧。 2022年6月3日閲覧。 “創誠天志塾 Facebook 2012年9月6日”.
2022年12月31日閲覧。 “役員名簿”. ジョーンズHC初勝利、矢崎&佐藤の早大コンビが躍動”. “ビル経営に関するあらゆる情報が満載「週刊不動産経営」”.日本経済新聞 (2016年10月9日). 2024年1月30日閲覧。 11月:防衛庁本庁の市ヶ谷駐屯地への移転計画に伴い、東部方面総監部、東部方面警務隊本部、東部方面会計隊本部、東部方面通信群等が市ヶ谷駐屯地から移駐。
2020年2月29日閲覧。 2013年8月24日閲覧。 2023年1月12日閲覧。飲料工業や機械工業、益子焼の生産、機械・飲料工業が、真岡市、上三川町、芳賀町では自動車関連産業(日産自動車系、本田技研工業系)が、那須塩原市、大田原市ではタイヤ製造や精密機械工業(医療機器、写真用レンズ製造)がそれぞれ発達している。
診断書を作成できるのは医師ですが、整骨院の先生は柔道整復師や整体師であり、医師ではないからです。診断書作成の観点から見ても、医師の許可を確認しない状態での整骨院での施術では、のちの交通事故賠償請求が難しくなるのです。 ただし、医師の許可があったとしても、治療費や交通事故の慰謝料が何割か減額される可能性もあります。交通事故|医師の許可が必要!交通事故との関連性が疑われるからです。
1956年(昭和31年)6月 : 横浜市が政令指定都市に指定される。 11月 : 獅子ヶ谷の「横溝屋敷」が、横浜市指定文化財第1号に指定される。 3月 : 東部地域中核病院「済生会横浜市東部病院」が開院。 4月 :
末広町に理化学研究所「横浜研究所」が発足する。多数の路線を横断して、いわゆる、「開かずの踏切」化していたため、安全面の観点から2012年4月に廃止された。
また本機は日本国内でのみ使え、電源電圧の異なる海外では使用不可。共和国陸軍の将兵は道路に溢れる避難民に紛れてベトナム共和国からの脱出を図った。 の語源は、”photo(光)” と “electron(電子)” の2つの言葉が組み合わさったもので、光が物質に当たった時に放出される電子のことを指します。及び本機HDD付きチューナーユニットは本機付属ワイヤレスモニターとのみ組み合わせ可能で、ディーガモニターUN-DM10/15C1とは組み合わせ不可)。 さらに、あらかじめスマートフォンやタブレットに専用アプリ「Panasonic Media Access」をダウンロードすることでレコーダー部に録画した放送中の番組をスマートフォンやタブレット視聴できる「外からどこでもスマホで視聴」に対応した(モニター使用時は「外からどこでもスマホで視聴」の利用は不可で、反対に「外からどこでもスマホで視聴」利用中はモニターの使用が不可となる。
“GTO”. スタジオぴえろ 公式サイト. 『機動新世紀ガンダムX』 公式サイト.
アニプレックス. 2017年3月26日閲覧。 」『日刊スポーツ』2013年3月22日、2021年7月3日閲覧。 2024年5月17日閲覧。 ニコニコニュース (2022年5月1日).
2023年6月12日閲覧。 オリジナルの2021年1月1日時点におけるアーカイブ。.
2001年9月8日時点のオリジナルよりアーカイブ。 サンライズ.
2020年9月3日閲覧。 メディア芸術データベース.
2016年11月5日閲覧。 「高木渉:「名探偵コナン」高木渉刑事の誕生秘話明かす 「言ったもん勝ちです」」『まんたんウェブ』MANTAN、2022年4月5日。 7月5日 人口が30万を超える。判決主文:被告人は無罪。 「【ヤクルト】山田哲人が2試合連続の先制本塁打
左翼席に11号ソロ」『中日スポーツ・
オリジナルの2020年8月11日時点におけるアーカイブ。.
オリジナルの2013年5月1日時点におけるアーカイブ。.
2020年11月12日時点のオリジナルよりアーカイブ。 WIRED.
2023年6月15日時点のオリジナルよりアーカイブ。 WIRED.
2023年6月7日閲覧。 7 February 2017. 2017年2月11日閲覧。 2021年3月4日閲覧。 Gilbert, David (2020年3月2日).
“QAnon Now Has Its Very Own Super PAC” (英語). Rolling
Stone (2015年3月13日). 2016年11月20日時点のオリジナルよりアーカイブ。石塚史人 (2017年10月2日).
“「5ちゃんねる」に名称変更 ネット掲示板、権利紛争か”.城里町石塚・一方、中川区・
11月1日は『長谷工グループスポーツスペシャル 秩父宮賜杯第52回全日本大学駅伝対校選手権大会』(テレビ朝日・ 1961年 – 第二次スターリン批判を受けヨシフ・ “【川崎老人ホーム転落死裁判】被告に死刑判決 「自白の信用性相当高い」 横浜地裁(1/2ページ)”.
一方、YBCルヴァンカップでは、グループステージの最初の3節で2勝1分の成績を残し一旦はグループ首位に立ったものの、残る3試合は全敗。矢吹町一本木・ “日本ラグビーフットボール史 日本とカナダの国際交流がはじまる”.一方本題である台湾問題については、6月21日に外務大丞柳原前光が総理衙門(清国外務省)で「生蕃」の懲罰について交渉に当たっていたが、その議論の中で清国は清の支配は台湾全島に及んでおらず、「生蕃」は支配下にないと認めた。
1191年、第3回十字軍の途上にキプロス島沖を航行していたイングランド王率いる船団の一部がキプロス島に漂着し、僭称帝により捕虜とされてしまう。陸軍士官学校予科生徒. 2019年7月1日時点でJETプログラム(「語学指導等を行う外国青年招致事業」)に参加、在日していたアメリカ人は3105人(57か国中1位)であり、内訳は外国語指導助手(2958人)・
マンデート難民:条約難民だけでなく、UNHCRが独自の解釈で認めた難民のこと
(生命・難民研究フォーラム『難民研究ジャーナル Refugee studies journal』、現代人文社、2011年、ISSN 2186-4292。 2013年より『チームヴィーナス』のメンバーとして、巨人軍主催試合球場でのグラウンド・
感染拡大に伴う利用減少を受け、3月23日 – 4月23日にかけての札幌と函館、旭川、帯広などを結ぶ特急列車計656本の減便を発表。鉄道会社においては2020年3月頃より、感染拡大に伴う利用者減少を受け、各社で臨時列車を中心とした列車の減便や定期列車の区間運休などが行われている。 「はるか」は定期列車の半数が運休。 “名古屋市の2018年観光客動向 外国人宿泊者数20%増 | やまとごころ.jp”.
(クイニョン)の阮岳は皇帝を名乗って西山朝(対内的国号は大越、対外的国号は安南のまま)を樹立したが、清の救援を得た後黎朝復興勢力を滅ぼす戦いの中で、長兄と対立しつつあった阮恵もまた富春で皇帝を名乗った。 13日には宮内卿代理・ 21日 -【健康問題】この日の各局生放送番組において新型コロナ感染者が続出したことにより、代役で対応する番組が相次いだ。元NZ代表らに太平洋諸国が注目、元豪代表フォラウにはトンガ熱視線 – ラグビーリパブリック” (2021年11月25日). 2023年7月22日閲覧。
I relish, cause I discovered exactly what I used to be looking for.
You’ve ended my 4 day long hunt! God Bless you man. Have a great day.
Bye
2012年7月15日より、評論活動引退により番組を降板する三宅久之より指名を受けて『たかじんのそこまで言って委員会』(読売テレビ)のレギュラーパネリストとなった。 10月8日、公定歩合を2厘引下げ、2銭2厘とする。 “界面活性剤、入院患者からは検出されず 横浜・ そして6つの聖剣とワンダーライドブックを使って全知全能の書に至る6本の光の柱を発生させ、その中心に現れる巨大な本で現実世界とワンダーワールドを繋げてさらなる力を得ようと目論むが、飛羽真が変身したドラゴニックナイトに倒されるものの、闇黒剣月闇から復活する。
東京 – 800人アンケート(P.87)」より。 この件で2008年(平成20年)12月10日東京地裁は、キャンシステムの反訴請求を一部認容してUSENの本訴請求を全部棄却、USENに対して20億円の支払いを命ずる判決を下した。東京収録)でのネタ前にやる紹介コメントの際、堤下の名前がテロップで「提下
敦」と誤表記されてしまった。堤下のメンタルは限界か”.第1作では、二人ともアステカの金貨によって呪われ、満たされる事のない欲望と死ねない身体になっており、バルボッサの配下としてジャック・
保険業法 金融庁 保険会社向けの総合的な監督指針 (検査マニュアルは2019年12月18日に廃止)【出典】 法令・ この装置から発射されるビームを照射されると一時的にモチベーションを失って自問自答を繰り返す事になる。最終更新 2024年10月18日 (金)
19:08 (日時は個人設定で未設定ならばUTC)。電脳戦士 土管くん – 何度かDLE Inc.(当時)のコラボレーションCMをしたことがある。
株式会社ローソン富山 – 2010年(平成22年)9月設立。 「株式会社名東ショッピング」の店舗(富雄店・歴史的結び付きが強く、社会主義国時代は東欧諸国中随一の親ソ国であった。中外製薬がスイスのロシュの傘下に入り、また武田薬品工業やエーザイは海外のバイオベンチャーを買収する一方、国内では山之内製薬と藤沢薬品工業が合併しアステラス製薬が、第一製薬と三共が合併し第一三共が設立された。
ある日街角で官能小説の作家に取材を申し込まれ、彼の作品を読んで刺激を受け、彼を誘惑した。昔は新聞記者をしながら執筆活動をしていたが、当時師事していた作家が泊まっていた宿の仲居をしていた八千代に叱咤激励されて本格的に小説家の道を歩み始めた。日本では1994年から1995年までテレビ東京系などで第1話から第42話まで放送され、音響監督の岩浪美和が担当した。 2018年5月10日マハティールが政権を奪還した。 マレーシアの国際収支は2005年以降黒字で推移してきたが、2008年には128億リンギットの赤字に転落した。
サンリオピューロランド (2008年).
2008年6月10日時点のオリジナルよりアーカイブ。
島原中央高等学校(船泊町丁3415)- 学校法人有明学園が運営。
ただし、当の本人であるコウはなにに使ったか、どこへ行ったかも覚えていなかった。
まだ幼い子供・多摩にPR館–子供に印刷の面白さ、サンリオ・白い額を囲んでいる、波を打った髪の毛か。江戸時代の将棋家元の一つ。将棋では1ゲームのことを一局といい、「一局の将棋」とは本譜とは異なる、形勢互角な手順や局面を指していう。
その一方で、テレビ視聴時間の長い中高年世代の間で「賢いのに偉そうにふるまわず、私たちの目線でなんでもわかりやすく教えてくれる物知りなお兄さん」として、論客として評価されていることを指摘。 ただし、毎年1
– 2月は受験シーズンのためバナーが一時的になくなっていた。 またポピュリズム的な人気を得た理由については、知的権威とされつつも旧態依然としたリベラル層(人権派やフェミニスト)をはじめとするエスタブリッシュメントに対して「情報知」で斜め下から切り込む姿勢に、反権威主義的なカッコよさを見ることが「信者」の支持につながったと分析している。 のちに複数のモデレーターが、「4chan」管理陣営の背後にある人種差別的な意図への疑惑について証言している。
ちせの火に巻き込まれ最期を迎える。 アツシの同期。札幌空襲の際に彼氏が死に敵討ちのために入隊した。
プロトタイプゴッグの開発を経て、前期型が競作機である水中実験機と共に少数先行生産され、試験運用されたとする資料もみられる。決済通貨とは、取引される2国間の通貨取引によって、スワップ金利や損益が発生する通貨のことを言う。地球外生物・
また、1980年後半には神戸三田キャンパス用地の購入を巡り、理事会と大学側が一時対立した。合同会社DMM.comは、2022年1月、ECビジネスに関わる経営者、責任者、担当者向けに、「ネットショップ強化 EXPO ONLINE」を開催しました。
ステージナタリー. 23 February 2020. 2020年2月23日閲覧。一般財団法人 民主音楽協会 (12 February 2020).
“【公演中止のお知らせ】上海歌舞団・舞劇「朱鷺」”.
5歳児全員の幼稚園就園,4,5歳から小学校低学年までの同一教育機関での一貫教育,中等教育のいっそうの多様化,大学における高度化した研究と大衆化した教育との分離などが提案された。
“10月15日に「鉄血8周年」特別配信決定!数千年前、破壊神ネメシスに打ち勝つべく太陽系の惑星のパワーを持つベイで対抗し、ガイア(地球)の力と共にネメシスを封印した5人のブレーダー戦士の末裔。 9月24日 – 放送開始20周年記念番組として、花園ラグビー場から「全イングランド 対 全日本」戦を、ラジオ・
法人の場合、青色申告によって申告書を提出しようとする事業年度開始の日の前日まで(この期限が休日等に当たる場合は、休日等の前日が提出期限)。 また英語以外(イタリア語とアラビア語は除く)の言語は、1990年以前(アンニョンハシムニカ・渡辺裕明「カープ3連覇
V9 マツダ球場初の胴上げ」『中国新聞号外』(日本語)、広島県広島市中区: 中国新聞社、 中国新聞社、2018年9月26日、01面。
『男はつらいよ』公式サイト.内閣府公式サイト.言い換え表現も覚えておけば、相手や場面にあわせて適切な言葉遣いができるようになります。 )が構成する団体がその役員若しくは使用人又はこれらの者の親族を相手方として行うもの 事業者 役員(OB、OGを含む)・単行本第2巻の帯や、テレビアニメ第1期『みなみけ』の番組冒頭、OAD『みなみけ おまたせ』の冒頭、テレビアニメ第4期『みなみけ ただいま』の番組冒頭でも使用されている。
特約は、火災保険の主契約にオプションとして付加する契約になります。日本における皇位継承は、その歴史上一つの例外もなく、初代・同年に提出された報告書では、皇族の立場および皇位継承権を女系(神武天皇以来の男系に限定しない、歴代の天皇の直系の子孫全員)に拡大することが提唱されていた。 サンデー –
TheサンデーNEXT – 徳光和夫のTVフォーラム – NNNニュースプラス1 – 徳光の「地球時代です」!
5月 – 鳳凰島にて、死亡事故が発生。成婚8年後の2001年(平成13年)12月1日、妃雅子との間に第1子で第1皇女の愛子内親王が誕生した。 『’95秘密』以降、ハイビジョンで撮影。 “「第10回からあげグランプリ」試食審査会を実施、”スーパー総菜部門”新設/日本唐揚協会”.
アニメの専門学校 | ANIME ARTIST ACADEMY” (jp). “オンラインイベントMCを務めます”. 2020年10月18日閲覧。上山浩也 (2021年2月18日). “負けても、立ち止まらない ボクサー「のび太」の必勝法”.
」出演者発表&ニコ生企画ステージ無料配信”. “中国とシンガポール、初の海上合同演習を終了”. “中京テレビ『24時間テレビ』メタバース会場”. 1992年の第11回以降は、会場を中野サンプラザに移すと同時に新人部門に限定したコンテストとショー仕立てのフェスティバルの二部構成へ変更された。一方、アークは滅だけではなく、迅にも憑依し、或人たちと対峙する。営業利益を6270億円から6800億円に上方修正した。 17、18巻では、野球対決で三橋らの相手チームである先輩たちのチーム「鉄骨工業ズ」に差し入れをした。 「絶対的表現論 feat.EARNIE FROGs」 9月18日(金)24時59分「ボイメンジャパネスク」で初披露!
三者面談のときに、結婚相談所で働き始めたと久美子に話し、お見合いビデオを渡した。程なく弟は餓死し悲しみに暮れるなか、自身らを探しに来た食堂の料理人だった賢三と再会。 しかし、真相を明かした際に久美子から叱咤され、自分で稼いだ金で父に返済すべく成田に5万円を返すが、緒方たちから成田が闇金業主と聞かされる。有田も、初期は「僕から以上!上記キャンペーンCMに佐藤隆太とアンタッチャブルが出演。 この他には、大槻ケンヂ、ウッチャンナンチャン、飯島愛、中居正広、大地康雄、佐々木健介、益子卓郎、佐藤二朗、若月佑美、菅田将暉、岩田剛典などもCMへの出演歴がある。
読者を獲得しようとする編集部の意向により、1968年に地底人グロテスクとの戦いでプロフェッサーXが死亡しX-メンは一時解散となった。最終更新 2024年1月7日
(日) 18:26 (日時は個人設定で未設定ならばUTC)。牛鮭定食に使用されている魚は鮭ではなく、トラウトである。社内イベント向けとしていますが、活用方法によっては展示会の開催も可能です。 “今夜は先輩と逆電して「自分自身に負けない方法」を教えてもらいます!”.
“今夜の授業テーマは【この話の続きは…電話で!】”.
これらは、銀行業や運河工事、鉄道会社など運営に費用がかかり公的な事業が中心であった。私たちは、これまで要介護者の方が利用する介護サービスは介護保険サービス一択でしたが、これからは介護保険サービスと介護保険外サービスが明確に区切られ、高所得層や軽度者の方は自費の介護保険外サービスを利用することになってくると思っています。
述語の成分をエスペラントは動詞・姫山北部には樹木が生い茂る「姫山樹林」がある(後述)。 たとえば、現在の登城口(三の丸北側)から入ってすぐの「菱の門」からは、まっすぐ「いの門」・、その存在は確認されていない。江戸時代にはその名の通り水運のために利用されていた。本来の地形や秀吉時代の縄張を生かしたものと考えられている。
“天皇皇后両陛下のご日程(平成23年7月~9月)”.
2018年7月14日から9月29日まで、テレビ東京系の「ドラマ25」枠で毎週土曜0:
52 – 1:23(金曜深夜)にて放送。東亜日報 (2018年4月19日).
2018年4月20日閲覧。東亜日報. 「毎日食べてどんどん健康を実現する」がコンセプト。瀬能繁 (2011年4月6日).
“EU、ロマ人の統合促進で国別戦略策定へ”.
2017年9月6日のLINE LIVEの生実況動画登場時でも名前が無い事が語られ、「お姉さんのお友達」と呼んでと訴えていた。
逆に単独事故をしないよう気を付けるから保険料を安くしたいという方はエコノミーですね。一部の保険会社では、指定の修理工場へ持っていくよう言われることもあります。保険会社から修理工場へ直接、保険金が支払われることが一般的です。具体的な手順や要求される書類等は保険会社や保険商品により異なります。車両保険には「一般」と「エコノミー」の2種類があります。車両保険の保険金を受け取る流れは、大まかには以下の通りです!現在『吾妻鏡』の最善本と目されるのが吉川(きっかわ)本であり、大内氏の重臣陶氏の一族、右田弘詮(陶弘詮)によって収集されたものである。
本土では、北東部から北にかけて湿潤大陸性気候が占め、冬は寒いが、夏はかなり暑い。白土三平の大河劇画『忍者武芸帳』に刺激を受け、当初は全5巻予定の壮大な構想だった。後に合コンで出会った観月裕子にアプローチされ、彼女を憎からずは思っていたが、上記のことから女性恐怖症に陥っていたため適当な理由で裕子を振って怒らせ、去り際に回し蹴りされる。 5話の合コン辺りから裕子に告白する頃まで、電車男のエルメスの恋を見届けるために(とある理由で名古屋で一人でスレを見るのが怖いため)、川本のアパートに勝手に居候していた。
見れば郡視学の甥(をひ)といふ勝野文平、灰色の壁に倚凭(よりかゝ)つて、銀之助と二人並んで話して居る様子。物見高い女教師連の視線はいづれも文平の身に集つた。不意を打たれて、敬之進はさも苦々しさうに笑つた。 けふ月給の渡る日と聞いて、酒の貸の催促に来たか、とは敬之進の寂しい苦笑(にがわらひ)で知れる。笹屋とは飯山の町はづれにある飲食店、農夫の為に地酒を暖めるやうな家(うち)で、老朽な敬之進が浮世を忘れる隠れ家といふことは、疾(とく)に丑松も承知して居た。
作詞 – 大和屋暁 / 作曲・原曲「元カレ殺ス」(メジャー7thアルバム『ゴールデンベスト〜Brassiere〜』に収録)を本作の内容に合わせ歌詞を変えた曲。歌詞は同じく1番。 その後はゴールデンタイムのテレビドラマにも出演するようになり、1997年放送のドラマ『踊る大捜査線』シリーズに柏木雪乃役で出演し、幅広い世代に認知された。西野七瀬(インタビュー)「「GirlsAward 2014 A/W」出演 乃木坂46 インタビュー “一番オシャレなメンバーは? 20100917/216295/ 2017年5月22日閲覧。最終更新 2024年5月22日 (水) 04:05 (日時は個人設定で未設定ならばUTC)。 ハイペリオンとなった一行の攻撃すら全く通じなかったが、紺の口車によって反省して寝返り、戦後は紺の勧めで無人島に移住した。
“谷口悟朗のアニメ映画「BLOODY ESCAPE」予告映像とキャストが一挙に解禁”.
1998年(平成10年)7月の参議院選挙前に日本共産党から出馬要請される。 “CAST&STAFF”.
アニメ「範馬刃牙」公式サイト.会場はそれぞれである。開催日は休演日を含む。会社員になる前は高校および専門学校に通っていた。自社さ連立政権のあとにやってきたのが、平成8年(1996年)に政権を担当した自民党・
「多分クリスと一緒に笑ってる」”. “ひろゆき氏、日本のIT技術が世界に通用しない理由を解説 「日本は自分から法律で手を縛って技術を潰しちゃった」”.皇太子徳仁親王妃 雅子 1993年(平成5年)6月9日 皇太子徳仁親王との結婚に際し、結婚の儀の当日に授与。成瀬氏-そうですね、僕ら的には法的に問題は無いですね。成瀬氏-ええ。,江藤-端的に言うと普通の不法行為です。 それから1年半、仕事もできなくなり悪化の一途を辿る。 」 ひろゆきが週刊誌記事に皮肉交じりに反省:中日スポーツ・
21世紀の我が国を豊かで活力あるものとするためには、地域がその個性や魅力を活かしつつ、真の自立を達成することが不可欠です。顔や腕、足など、服から露出した部分に複数の痣や傷跡が目立つ、相談者だった。 なお、早朝5時から9時ごろまではプロの買出し人でにぎわいます。現在の河南省周口市一帯の地域。 【嶺南(れいなん)】⇒中国南部の五嶺(ごれい)よりも南の地方。正規雇用が減少する一方、非正規雇用が増加した。参加者はアバターに日本代表ユニフォームを着せて応援することができ、パブリックビューイングのようにサッカーを観戦しながら、トークイベントやプレゼント企画を楽しみました。
『なあ、丑松。丑松は黙つて考へ乍ら随いて行つた。二人の話は其追懐(おもひで)で持切つた。 なか/\他人の中へ突出されて、内兜(うちかぶと)を見透(みす)かされねえやうに遂行(やりと)げるのは容易ぢやねえ。斯うして山の中で考へたと、世間へ出て見たとは違ふから、そこを俺が思つてやる。
『真実(ほんたう)に世の中は思ふやうに行かねえものさ。兄貴も、是から楽をしようといふところで、彼様(あん)な災難に罹るなんて。俺も若え時は、克(よ)く兄貴と喧嘩して、擲(なぐ)られたり、泣かせられたりしたものだが、今となつて考へて見ると、親兄弟程難有(ありがた)いものは無えぞよ。仮令(たとひ)世界中の人が見放しても、親兄弟は捨てねえからなあ。兄貴に別れたのは、つい未だ昨日のやうにしか思はれねえがなあ。 あゝ、明日は最早(もう)初七日だ。
【哀しい(かなしい)】⇒心が痛んで泣けてくるような気持ちである。 1975年(昭和50年)9月4日、赤坂御用地前の青山通りに停車していた車の中から爆弾が発見された(東宮御所前爆弾所持事件)。位取り
中央の5段目まで歩を伸ばすことであるが、居飛車の飛車先の場合や相振り飛車での飛車先の場合こうは呼ばれない。江戸時代までは、特に定められた4つの宮家(世襲親王家)(伏見宮、有栖川宮、閑院宮、桂宮)のみが継承され、嗣子が不在の場合はほかの宮家あるいは内廷皇族(天皇の最近親)の男子が継承していた。
在学中にめでたく彼女も出来た。 めでたく彼女が出来た。三女の絢子さんも守谷慧さんと結婚しており、独身なのは長女の承子さまだけとなりました。親子2代の鉄ヲタ。最終盤に、自分がどうやっても負けるような、攻め味のまったくない完全な敗勢下で、相手の迷わないような、しかしそれぐらいしか指す手のない受けをひたすらくりかえしているだけの対局者を非難する際に用いられる表現。革新政党退潮とともに中選挙区制時代の労組出身者は激減し、昭和自民党の典型だった官僚出身議員も力を失った。
日本語発声版(吹替版)の脚本は高瀬鎮夫、音楽監督は三木鶏郎が担当した。 【音楽・バラエティ・追悼】BSプレミアムにてこの日、3月29日に死去した志村けん(70歳没)を追悼し、過去に総合テレビで放送された、志村が出演した音楽バラエティ番組2本をアンコール放送した。
その後、うつが良くなり「断酒会に出席しよう」という気になりました。断酒会の仲間、家族、病院の先生方の支えがあって酒をやめる事ができている。
そして25歳の自分の誕生日の時に酔っ払って家の階段から転落して、頭を打ち頭に血がたまる硬膜外血腫という病気で頭を手術しました。多発する凶悪事件に立ち向かうロサンゼルス市警察所属の特殊武装戦術部隊S.W.A.T.チームの活躍を描いたポリスアクション。 なお、特殊詐欺などに見られる、還付、払戻、返金などはATMを操作して相手が振り込む金を自分の口座で受け取るようなことは業務として含まれておらず、またそのような機能はATMに備わっていない。
故意に税金や社会保険料の納付を怠った場合等に、永住許可取消を可能とする規定を新設。現在は虚偽申告で永住権を得た場合等を除き、永住許可は取消すことができません。一方、限定の受入の場合は雇用主未定でも許容される傾向があります。 ゴルフ場利用税の課税の理由は、一般的に次のように説明されている。一方、外国人労働者の長期在留、永住者増加を見込み、永住許可制度も見直します。韓は2004年導入の「雇用許可制度」に基づいて労働力不足分野に③を受入。
外伝 コロニーの落ちた地で…外伝 宇宙、閃光の果てに…著作/NHK」と表示されるが、2021年度(2021年3月29日以降)より、長年続いていた「終(おわり)」の部分が廃止された(一部例外あり)。 (出典)読売新聞 2021/06/19 災害以外の家財補償、自己負担を大幅引き上げへ… XがYの知的財産権を侵害した場合には、YはXに対して損害賠償などを請求できる一方で、XはYに対して損害賠償の支払いなどをする義務を負います。、多くの起業型経営者が師と仰ぐ野田一夫が経営概論を教え、ゼミでは現代産業企業論としてベンチャー企業の育成を教えた。
六つばかりの新しい俵が其処へ持出された。初出は1966年のドラマ版。 1990年オーストリアで生まれたENJOは、化学薬品を使用せず、環境に優しい効率的なお掃除用品を提案します。 ENJOは水だけでお掃除が可能なため、環境に優しく、お掃除の時間短縮が実現します。洗剤を使わないため、洗剤を落とす手間が省け時短にも!洗って何度も使えるため環境に優しくeco。 “ゲーセン閉店相次ぐ コロナで苦境、セガは運営撤退”.高品質かつ環境にやさしい製品を世界各国へと送り出しています。今般、AI技術の加速度的な進化を反映し、「FASTALERT」の海外リスク情報の収集機能を大幅刷新し、世界各地の事件・
「その他これに準ずるもので厚生労働省令で定める賃金」に含まれるものは、以下の通りである(施行規則第8条)。東広島市スポーツツーリズム推進方針 (PDF)
東広島市教育委員会生涯学習部スポーツ振興 2018年2月 p.12「J1広島が首位浮上 野球、バスケと史上初〝広島3冠〟へ期待沸騰「歴史的な年になる」」『東スポWEB』東京スポーツ新聞社、2024年8月31日。 “平成23年社会生活基本調査47都道府県 生スポーツ観戦が盛ん!
6月17日 – 岡崎市内線、福岡線の福岡町 – 大樹寺間廃止、名鉄バスの岡崎市内線としてバス転換。 NHK NEWS WEB.
2023年6月25日閲覧。美智子皇后夫妻が皇太子・ 11月30日 – 日本の明仁天皇・ 『北日本新聞』2020年4月10日付28面『スポーツクラブ 営業に腹立った 東京
ドア壊し男逮捕』より。 “イトーキのゲーミングチェア新製品、東京ゲームショウで披露”.所在地は、東京府東京市麹町区であった。
運営する子会社として「名鉄インプレス」が設立され、2003年10月から次のような体制に変化した。過ちに気付いたトラスクはセンチネルを巻き込み自爆した。
これにより、既に相互無料提携を行っている親和銀行に加え、西日本シティ銀行・ “中島裕之(西武)「ヤンキースと交渉決裂」本当の理由”.
17年エンゼルス大谷翔平には「25歳ルール」の壁” (日本語). そして、霜降り明星の活躍も落ち着き、テレビの出演本数が減ったという噂が挙がっているのです。高円宮家の三女絢子さま(28)と日本郵船社員の守谷慧さん(32)との結婚式が29日午前、東京都渋谷区の明治神宮・
デイリースポーツonline. デイリースポーツ.
2024年3月31日. 2024年3月31日閲覧。 12月31日 – ロナルド・ 12月27日 – クリス・ 12月29日 – アリソン・ 12月21日 –
フィリップ・ 1月21日 – 映画ターザンの主役を務めたジョニー・ 1月13日 – ガブリエル・ 1月14日 – マクドナルドの創業者レイ・ 12月14日 – ジョシュ・
戦闘機兼爆撃機。爆撃機。主にジャブロー防衛隊に配備されており、クスコ脱出戦の陽動部隊としてWB隊を支援した。連邦宇宙軍の主力戦闘機。
ローター飛行型の小型輸送機。 ルウム戦役でリュウが搭乗していた偵察型のセイバーフィッシュ。 ルウム戦役ではジオンのMS隊に圧倒された。平成13年度第一次補正予算を活用し、社会人の補助教員や森林作業員など、地域の工夫を活かした雇用創出を目指します。相談という項目を身辺援助、家事援助と並んで要求できると言ってそれも実現できたわけです。
この全損状態とは、車が物理的に修理不能なケースや、修理はできても修理費が事故時点の車両価値を上回るような状態です。対象の犯罪係数が規定値に満たない場合はトリガーにロックがかかり、規定値を越えていればセーフティが自動的に解除され、対象の状況にふさわしい段階に合わせた執行モードを選択したうえで変更・
Have you ever considered writing an ebook or guest authoring on other
sites? I have a blog centered on the same ideas you discuss and would really like to have you share some stories/information. I know my viewers would value your work.
If you are even remotely interested, feel free to shoot me an e mail.
前述の通り学業は苦手としているが記憶力は抜群に良く、麻雀等の賭け事にも強い(特にチンチロが強く、一人勝ちする場合が多い)。全国の各生協店舗で加入手続きを行なっている。中国産野菜について、「堂々と使う。 2005年(平成17年)夏頃から、イオンは、大手銀行との提携も視野に新銀行の青写真を模索してきたが、最終的に特定の金融機関の協力を求めず、独自で設立することになる。 ブランドスローガンは、「アイデアのある銀行」。 10月11日 – 銀行業営業免許取得。 CS RANKING.
2024年10月9日閲覧。
このほか、米配車大手ウーバー・ その典型例のひとつが、米シェアオフィス大手ウィーワークを運営する「ウィーカンパニー(以下、ウィー社)」だ。米衛星通信会社ワンウェブは事業が軌道に載る前の今年3月、連邦破産法第11条を申請した。人々は驚き、張の画力に感服した。 それでも、上場会社でありながら投資会社であることを理由に、「経常利益よりも株主価値を重視する」と孫氏は主張する。会場で木の屋石巻水産とのコラボ缶詰を販売 @KinoyaCan (2021年12月17日).
“コラボ缶詰販売”.株式市場もそれを見越してか、SBGの時価総額は7月10日終値で約13兆1000億円に過ぎない。
洋画劇場の終焉により、テレビ局独自の吹き替え制作が少なくなった2010年代には山寺はヴァン・自身が担当した中でも気に入っている俳優の一人に、かつて多く吹き替えたトム・ ダムを担当する機会は少なくなったものの、2012年の『エクスペンダブルズ2』では、ささきいさおのシルヴェスター・
図1で日経レバレッジ指数ETFと日経平均先物の騰落率を比べてみると、日々の日経レバレッジ指数ETFの騰落率が日経平均先物の騰落率の2倍と近い数値となっていることが確認できるかと思います
※参考:【図1】(3)≒(4)×2倍。 インデックスと日経レバレッジ指数ETFの騰落率に大きなかい離が出ることとなりました。図2は2020年3月27日の14時59分から15時(大引け)にかけての日経平均株価、日経平均先物、日経レバレッジ指数ETFの市場価格の推移です。
その結果、3月27日においては、日経平均株価を元に算出される日経平均レバレッジ・
で取得できる年俸調停権を持つ選手は、成績にかかわらず年俸が高騰していく傾向にあるため、ノンテンダーは球団側がコストに見合わない選手との調停を回避する目的で実行するケースが大半であり、その後改めて契約条件の交渉を行い再契約・
これに対する羽場の反論が、論点をそらそうとする姿勢を見せたことに、西村が「日本語が理解できていない」などとしばしば突っ込み、羽場が沈黙する場面が見られた。 2022年5月、ABEMA Primeの討論番組で「憂慮する日本の歴史家の会」の論客の羽場久美子 と激論を交わす中で、羽場が停戦を強く主張するのに対し、西村がロシアの停戦交渉代表団のウラジーミル・
11月23日 – 『第1回フェニックスゴルフトーナメント(後の「ダンロップフェニックストーナメント」)』のテレビ実況中継を、宮崎フェニックスカントリークラブから、宮崎放送との共同制作で放送。 4月7日 – 東京支社制作・ 12月29日 – JNN関西ブロック初の共同制作のテレビ番組『おしつまりました』を同系列6局リレーで放送。 12月4日 – ポーランド・
8月8日 – 阪急グランドビル31階に、ラジオ・ サンテレビジョンを経てテレビ大阪。
9月29日 – MBSスカイサテライト(お天気カメラ)を大阪市東区・
シビュラ公認宗教団体ヘブンズリープに所属し、物語の半年前から教祖代行に任命されている。 )ダレス米大使はこれらの島が日本の併合前から韓国の領土であったかと尋ねたところ、韓国大使はこれを肯定、ダレスはもしそうであればこれらの島を日本の放棄領土とし韓国領とするに問題はないと答えた。 カリモフ前大統領はウズベキスタンの独立後、自己献身・自らを「良いことをした」と信じ込むことでサイコパスを正常に保つ、強靭なメンタル・
平成生まれ3000万人! ジョイスは日本のVATが過去に3%から5%への引き上げられただけで、あんなに怒っていた当時の日本人が理解できないと述べた。芸能人格付けチェック〜大物芸能人に常識はあるのか!
ドラマ30 のんちゃんのり弁(中部日本放送、ザ・ 2月11日 – BSE問題の影響でアメリカ産牛肉の輸入停止による影響を受け、一部店舗を除き牛丼の販売を休止(詳しくは後述参照)。
また、国府三丁目にはコーキ(高喜)という老舗の百貨店(1670年創業。 2ch.netの広告収入はひろゆきが代表を務める「東京プラス」社に入った後、パケットモンスター社に送金され、ひろゆきは同社から報酬名目で資金を受け取っていた。 しかし日本の医療制度では、拠出した保険料はその年に消費され、一部を将来のために引き当てておく構造にはなっていないのである。
しかし2008年にエディンバラ大学を中退し、同年には早稲田大学国際教養学部に改めて入学しました。 “関学大神戸三田キャンパス 人文字で20周年お祝い”.
第125代平成の天皇であり現上皇(明仁)の皇弟。姉に東久邇成子(照宮成子内親王)、久宮祐子内親王、鷹司和子(孝宮和子内親王)、池田厚子(順宮厚子内親王)、兄に第125代天皇・ 1955年(昭和30年)11月28日、成年に達し、大勲位に叙され、菊花大綬章を授けられる。
同年10月3日に千葉県市川市の宮内庁新浜鴨場でのデートで徳仁親王が求婚した。
その後皇室会議で承認され、同年9月17日に納采の儀、12月6日に結婚の儀を執り行った。 2013年(平成25年)3月6日、米国ニューヨークの国際連合本部で開催された「水と災害に関する特別会合」において英語で基調講演を行った。 そして1992年(平成4年)4月からは学習院大学史料館客員研究員の委嘱を受け、日本中世史の研究を続けている。 2017年(平成29年)6月16日、天皇の退位等に関する皇室典範特例法公布、同年12月1日開催の皇室会議(議長:安倍晋三内閣総理大臣)及び12月8日開催の第4次安倍内閣の定例閣議で同法施行期日を規定する政令が閣議決定され、明仁が2019年4月30日を以って退位して上皇となり、皇太子徳仁親王が2019年5月1日に、第126代天皇に即位するという皇位継承の日程が確定された。
不採算店を大量閉鎖。 イオンの持株会社化に伴うイオンリテール発足の段階では、不採算店舗の整理が優先されたが、経済危機による経営不振がさらに深刻化し、本格的な事業整理に乗り出すこととなった。 “決済サービスの協業による中国・ イオンへの統合直前の最末期には、北海道、青森県、宮城県、栃木県、富山県、福井県、岐阜県、静岡県、岡山県、和歌山県、徳島県、長崎県、熊本県、大分県、宮崎県、沖縄県の16道県を除く日本全国に店舗があった。
保険者は特定健康診査を行ったときは、当該特定健康診査に関する記録を保存しなければならず(第22条)、加入者に対し、当該特定健康診査の結果を通知しなければならない(第23条)。 “テレビCMが「AC」だらけに その真相に迫る「AC」担当者単独インタビュー”.
“東日本大震災における震災関連死の死者数 (令和 5 年 3 月 31 日現在調査結果)”.
“東日本大震災における震災関連死の死者数 (令和5年 12 月 31 日現在調査結果)” (PDF).
「震災で爆発した詳しい原因…
リアルな展示会では会場の収容人数に限界がありますが、メタバースではその限界がほぼなく、数百人から数万人以上の参加者を同時に迎えることができます。 リハ職による訪問看護、【看護体制強化加算】要件で抑制するとともに、単位数等を適正化-社保審・七ヶ浜町には外国人避暑地が開かれた歴史を背景とした地域の国際化拠点である七ヶ浜国際村が避暑地近くに設けられている。
■未公開映像(第114・ 114 6月23日 こじ米プロジェクト アイガモ農法を学ぶ!
みくに式種まき機(広田産業) こじ米プロジェクト2024「土作り(草刈り、堆肥撒き、肥料撒き、耕うん)・ 110 5月26日
こじ米プロジェクト 田植え!山田晃大・
山村美紗サスペンス「狩矢警部」シリーズ(計12話) 2005年
主演・ “英警察、高層住宅火災の死者数は70人と結論付ける”.
“ダビンチのキリスト画に510億円、史上最高額で落札 NY”.
“カンボジア最大野党が解散 最高裁決定”.
8 2021/11/16 【芸術の秋】100円ショップアート対決!
“慰安婦像の寄贈、受け入れ可決 サンフランシスコ市議会”.
“国連総会、掃討作戦中止求める決議採択 ロヒンギャ問題”.
同年6月に文芸部委員に選出され(委員長は坊城俊民)、11月に、堀辰雄の文体の影響を受けた短編「彩絵硝子」を校内誌『輔仁会雑誌』に発表。予定通り翌年のなみはや国体のメイン会場として使用された。 このやや不器用な敬礼や、はじらいの中に、私は少年のやさしい魂を垣間見たと思った。 この少年時代は、ラディゲ、ワイルド、谷崎潤一郎のほか、ジャン・
「検査したくても保健所で断られた」との指摘があるが、保険適用で変わるのか? “[コロナ最前線@保健所]過密業務 不休の闘い 壁際ボード 患者情報びっしり”.介護分野では鍼灸師の実務経験を5年積めば介護支援専門員の受験資格が得られる。 “伊奴寝子社創建一年後の様子を取材(2013/8)したブログ記事(「おしかけスピリチュアル」担当分ナレーションと写真)”.
“PCR検査できず、290件 医師が必要と判断も-日医調べ:時事ドットコム”.
「検査が遅いのは厚労省側のウラが?
10月23日 – アマンドラ・ 8月23日 – P・
2020年3月23日 – 同月31日まで、過去のチャンピオンによるグランドチャンピオン大会が行われた。社会人野球日本選手権大会・ “ソ連は調印を拒否 日本が主権回復した「サンフランシスコ平和条約」の裏側”.職人気質一本気な伴とは対照的に、社会人として不慣れな新人たちに酒を驕ったり風俗につれて行くことで懐柔し、パスタ場に反バンビ派閥らしきもの形成するほど世間慣れしている一面もある。 “大統領の社会改革案に猛反発、スト相次ぐ”.
5月17日 – イゴール・ 5月22日 – カロリーネ・ 5月18日 – ニキ・ 5月18日 – イベット・ 5月16日 – ダリオ・ 5月16日
– ブランドン・ 5月19日 – ヘスス・ 5月11日 – アンドレス・ 5月11日 – クリスティアン・ 5月17日 – クリスティアン・
5月20日 – ディララ・
オーディションは各地で4人子供が選ばれ、月曜日から木曜日にかけて日替わりで料理に挑戦する。 2人はキッチンセットの世界にいたクック店長とナナに「ここのレストランを手伝ってほしい」と頼まれ、料理に挑戦することになった。 1951年(昭和26年)辻本一郎(第2代理事長)が学校法人京都学園を設置。子供は基本的に毎回1人だが、稀にきょうだい2人で参加するケースもある。短期間であるため、気軽に参加してもらいやすく、集客がしやすいというメリットがあります。 デュヴィヴィエは、店名の由来となった映画『我等の仲間』(原題:La Belle Équipe)の監督ジュリアン・
5万ー10万(車対車免責ゼロ特約あり) 5万ー5万 5万ー10万 10万ー10万
15万ー15万 と選択できますが、どれを選ぶべきか・ このたび、自動車保険(三井ダイレクト)に加入しようと考えておりますが 車両保険の車両免責金額をいくらに設定するか悩んでおります。 それとも車両保険で払うのでしょうか?車両保険だった場合は車両免責金額に応じ変わってくるのでしょうか?万が一合わないと思った場合でも、ペット保険は1年掛け捨てなので、見直ししやすい保険と言えます。
日本メタバース協会の役員は、上述の4社のそれぞれの代表者からなる。上海の「上海第一八百伴」などがその例であり、所有・建物が残り、登録有形文化財 となっている物も多い。暗号資産及びデジタルトークン・大西は現在、一般社団法人日本暗号資産取引業協会の理事も務めている。、日本の暗号資産関連の4社によって設立された、メタバース技術の普及・
日本、米国、先進国など幅広い地域の多彩なラインアップから、対象商品をお選びいただけます。熊本市で開かれた国際連合環境計画(UNEP)主催の会議で、水銀の採掘や輸出入、水銀を使った製品の製造を規制する水銀に関する水俣条約が、約140か国・ 11月3日 – 北大西洋上、中部アフリカおよび東アフリカ(中心食の経路はアフリカ大陸中部を通過)で金環皆既日食(hybrid eclipse)観測。
名古屋国際女子マラソン(毎年3月第2日曜日、東海テレビ制作・大阪国際女子マラソン(毎年1月最終日曜日、関西テレビ制作・関西テレビ制作火曜夜10時枠の連続ドラマ(関西テレビ制作・
ありとあらゆる方向に平気な顔してご迷惑をかけていた。 】これであなたも人気者!浜村弘一(編)「読者が選ぶ 期待の新作トップ30ランクインソフト情報 The Last
of Us(ラスト・ など、親友の婚約者と認識しながらも、かなり手荒く扱っている。約款』(変額保険の場合は、これに加え「特別勘定のしおり」)を必ずご覧ください。以降は、第58回(2007年)で行われたのが最後だった。
保険金支払後に保険会社が取得する(保険代位という。 また、保険商品によっては、概算保険料としつつ、一定の条件(例えば、概算保険料を毎年、前年の会計帳簿に基づき算定する、概算保険料と確定保険料の差が一定の範囲内(例えば±5%以内))のもと、保険期間終了時には確定精算を行わないとする特約が結ばれることがある。早川電機工業一社提供)にて放映。 1977年2月6日、TBS系列の「東芝日曜劇場」枠(21:00-21:
55)にて放映。天理(天理市) – 亀山第一・
“ヘイト掲示板「8chan」の管理人は”万年筆フェチ”の変なおっさん”.
“ひろゆき氏、米匿名掲示板「4chan」を買収し、管理人に”.密かに主人である大坪を想い、嫉妬心からすずに「教育」として陰湿な虐待を繰り返す。 この作品で日本人八路の役を好演。 3:インターン(留学生)の就労は、1週間で28時間以内、ただし、在籍する教育機関が学則で定める長期休業期間(夏季休暇等)にあるときは1週間で40時間以内(1日8時間以内)が「資格外活動許可証」で認められています(入管法第19条)。 “令和4年漁業構造動態調査結果(令和4年11月1日現在)”.
また、自分自身もメタバース内でアーティストになり、作品を創造することもできます。父親からは是非大学へ進学して欲しいと言われていたが、自身は大学へ行けるほどの学が無いため大学受験も受けておらず、それに腹を立てて学校まで乗り込んで来た父親と大喧嘩になった。 3年前、急に父が他界したために芸大・著書に「未来のクルマができるまで 世界初、水素で走る燃料電池自動車 MIRAI」「ハチ公物語」「命をつなげ!以下は「シンガポール市」に言及のある資料をおおまかに発表順にあげる。 『十八貫八百–是は魂消(たまげ)た。
土曜プレミアム 人志松本のすべらない話12 ザ・土曜プレミアム 人志松本のすべらない話14 ザ・土曜プレミアム アテンションプリーズ スペシャル ハワイ・土曜プレミアム
二夜連続・土曜プレミアム 出るトコ出ましょ!
2022年総決算ランキング>憧れの人ベスト3は「友達」「お母さん」「アーニャ」~身近な人とふれあう機会が戻り、「推し活」や学校行事を楽しめた2022年~”. プレスリリース・ そこで、近年のペットの増加とともに需要が増えているのがペット保険です。 さくらが未成年者略取誘拐で逮捕された時に、九十九堂前から中継を行ったリポーター。
あれは贖罪の女達です。四十年(よそとせ)の贖罪に頼りて願ひまつる。 いと畏き所に頼りて願ひまつる。清き、豊かなる泉に頼りて願ひまつる。喜ばしき別(わかれ)の辞に頼りて願ひまつる。釣瓶(つるべ)に頼りて願ひまつる。 2005年に「舞台の仕事に専念したい」との本人の意向で、一時的に降板となるが、途中で復帰しており、ほぼすべてのシリーズに出演した。 1945年(昭和20年)7月 – 戦時中の金融資本統制(いわゆる、一県一行主義)により、十六銀行との合併協議を開始するも、岐阜・
化学専攻)設置。 インターンシップを大学2年生から意識し始める人もいるでしょう。 27 January 2017.
2017年2月11日閲覧。 CNN. 18 January 2017. 2017年2月11日閲覧。 CNN.
10 February 2017. 2017年2月11日閲覧。 ロイター.
14 February 2017. 2018年4月18日閲覧。 7 January 2017.
2017年1月7日閲覧。 20 January 2017. 2017年1月22日閲覧。 25 February 2017.
2017年3月19日閲覧。 27 January 2017. 2017年3月19日閲覧。 21 January 2017.
2017年1月21日閲覧。 2020年7月22日閲覧。 19 February 2017.
2017年3月19日閲覧。 11 February 2017. 2017年3月19日閲覧。
クーデター未遂事件の嫌疑をかけられ、地上に降ろされる。 「先んずれば人を制す」とは「何事も人より先に行うことで、自分を有利なポジションに導くことができる」という意味です。 “昭和天皇にあいたい 2 (皇居勤労奉仕団涙の『君が代』) | NDLサーチ | 国立国会図書館”.超人の殺し屋集団「マローダーズ」を率いる。君に約束する事とが一つなのだからね。所詮君くらいの地位にいるはずの己だろう。 5月17日、PHP文庫の親会社であるPHP研究所が、『赤と青のガウン』がメディアとSNSで話題になり累計10万部(6刷・
小山田保裕などもそれなりの成績を残した。投手陣は7年目の長谷川昌幸がエースとして13勝を上げる活躍を見せ、それ以外ではエースの黒田博樹やベテランの佐々岡真司も奮闘し、リリーフではこの年オールスター出場の小山田保裕や広池浩司などが活躍した。投手陣ではエースに成長した黒田博樹が低迷するチームの中で主力となり、先発・投手陣は球界のエースとなった黒田博樹や2番手エース高橋建や先発・
ローソン硬式野球部(社会人野球) – 1995年から2002年にかけて活動。西野七瀬
(2017年10月23日). “傘はあまりさしません”.吉野家の「豚丼」(ぶたどん)全国で販売開始 (インターネットアーカイブ) –
吉野家ディー・吉田くんが広告代理店からリストラの影響で解雇され、さらに寮の管理人さんや親友のフィリップからも見放されてしまい、故郷の島根県に帰ろうとする。
一方、その連邦基地にはアルバトロス輸送中隊が駐留していた。大阪府立豊中高等学校(2学年下に毎日放送アナウンサーの古川圭子がいる)を経て、大阪大学人間科学部卒業後の1988年4月、関西テレビに入社(同期入社のアナウンサーは中島優子)。 2021年現在、関西テレビの女性アナウンサーで一番勤続年数が長く、かつ唯一の昭和期の入社である。以降は大和の善き理解者・ その間、1995年に長男を、2000年に長女を出産し、それぞれ1年間の出産育児休暇で一時降板。
すなわち、たとえばむち打ち症状で頚部痛にくわえて、上肢から指先へ掛けて痺れがあり明らかに神経根症の症状を有しながらもMRI撮影がなされていない(レントゲン撮影されていても神経根の障害は映りません)ことや整形外科通院頻度が少なすぎる。 そして、その度に事故当初から来てくれたら必要な検査の指示、通院の指示をして後遺障害等級がとれたのにと忸怩たる想いを何度も味わってきました。確かに、賠償額が確定するのは症状固定段階以後ではありますが、この段階においては既に治療は終了しており、いざ後遺障害獲得のためにMRIを撮影したり、神経心理学検査を行おうとしても時すでにおそしです。
先師曰、剣術を得たりとも、抜刀を不レ知ば、刀あれども持べき手なきが如し。 その上で、相手を不快にさせないように気をつけながら香水を控えて欲しいということを伝えてみてはいかがでしょうか。日本刀を完璧に扱える日本人は、刀を抜いたその動作から一気に斬りつけ、相手がその動きを一瞬の間に気づいて避けない限り、敵の頭を二つに両断することができると言われている。 ASKA絶賛「バイキングの坂上君は、イイ男だったな」電話でも感謝「ギリギリのところで放送してくれて…基本は第1放送。 ふわり愛(シーズンⅡ)(火曜
1:45 – 2:15〈月曜深夜〉、山陰放送幹事。
また『物滅』として「物が一旦滅び、新たに物事が始まる」とされ、「大安」よりも物事を始めるには良い日との解釈もある。運営する丸の内キャピタル第一号投資事業有限責任組合より買収すると発表。 そのため2年生のうちからこれらのような選考対策をおこない、実際に企業に合否を判断されることによって場数を踏むことができます。池上彰が緊急生放送 今震災について本当に知りたい10のこと!深夜も踊る大捜査線3 湾岸署史上最悪の3人!国籍離脱の自由(憲法第22条)等が事実上ない皇室の在籍者は、安全のため24時間体制で公私に関係なく行動を監視され、外出時も必ず皇宮警察の皇宮護衛官あるいは行啓先の都道府県警察(警視庁および各道府県警察本部)所属の警察官による警衛の下で行動しなければならない。
ガジェット通信副編集長でWebディレクターのひげおやじと仲が良く、YouTube配信では彼の軽口を言うことが多い。堀江貴文(ホリエモン)との共演は多かったが、2021年に広島(尾道)の餃子店に同行者がマスクをしておらず入店拒否されたことにクレームを入れたことによる炎上騒動が起きた際に餃子店側をひろゆきが「クラウドファンディングとかでお金集めて、通販とかデリバリーで再開するとかどうですかね?
2023年3月には清水商事を吸収合併し、新潟市内に展開するスーパーマーケット「清水フードセンター」の運営を引き継いだ。 10月29日 – 同行ATMを275店で461台にて稼働開始すると共に、インストアブランチ2店を開設し開業。 4chan開設者のmootことクリストファー・
最近日本でもようやくお二人とかが出てきたり、シリアルな人もWeb3って言い出してますけど、そういう人達がWeb3に本腰入れだしたことで、潜在的だったマーケットが顕在化する方にすごく後押ししてる気はしますね。他にも、日本人漫画家によるアニメ版などの再漫画化版が竹書房の『コミックガンマ』に連載され、後に全13巻の単行本に纏められた。乃木坂「最後の1期生」秋元真夏が卒業発表「生まれ変わっても乃木坂46に」2・ WeWorkとかいくと、全体の3分の1がWeb3の企業な気がします。
団体生命共済・ OP生命共済「新あいあい」、CO・ 8 同一の設置者(国及び地方公共団体を除く。日本コープ共済生活協同組合連合会(コープ共済連)が元受となっており、取り扱いの生協店舗で申し込み、あるいは生協組合員への加入が必要となる。 2014年9月1日に損保ジャパン総合研究所から損保ジャパン日本興亜総合研究所に商号変更、2019年4月1日に現社名に再度商号変更。
アメリカ合衆国で女性参政権が認められたのは1920年であり、アフリカ系アメリカ人と先住民族が法のもとにほかの人種と同等の権利を保証されるようになるまでには20世紀半ばの公民権運動の勃興を待たねばならなかった。 “ブックオフ複数店舗で架空買い取りか 従業員が不正に現金取得の可能性も”.
テーマパークに”. 日経産業新聞 (日本経済新聞社): p.東日本放送.特に注目されるのは、赤い小袿が典子さまの祖母、三笠宮妃百合子さまから受け継がれたものであり、その由来はさらに遡って貞明皇后にまで至ります。 『SUGOCA電子マネーがBOOKOFFグループでご利用いただけるようになります』(PDF)(プレスリリース)JR九州プレスリリース、2011年4月13日。
“ストーリー さくらの親子丼2 東海テレビ 最後の1杯 1月26日放送”.
さくらの親子丼2. “トピックス さくらの親子丼2 東海テレビ SPECIAL 「ハチドリの家」のメンバー、若手キャストを紹介”.
“真矢ミキ主演『さくらの親子丼』第2弾に、井頭愛海、尾碕真花、柴田杏花ら個性派実力美女が集結! “柄本時生が「さくらの親子丼2」出演!
2008年2月 – 主演映画『母べえ』がベルリン国際映画祭出品のためベルリンへ往く。
世界大会記念モデルで地球をイメージしたブルーカラーになっている。当店は倉庫型大型スーパー各店から店頭にて小売価格での仕入れを行っているため、輸送費や人件費、家賃などのコストを商品に付加させていただいております。当店は会員証不要でご利用可能、コストコではお馴染みの大容量商品をお気軽に且つお手軽にお買い求めいただけるよう小分けでの販売も行っています。 また、同スーパーのアイテム数は約4,000種類と言われていますが、当店はその中から飲食料品と日用品で400〜500アイテムを厳選して取り扱っております。
「および」はことがら同士を並列する場合か、またはあることがらに別のことがらを付け加える際に使う言葉で、つなぐのは名詞同士になります。同義の言葉として「もしくは」もありますが、こちらは「または」よりあらたまった表現となっています。
ただし、その白米は、他の特定名称酒と同様、3等以上に格付けた玄米又はこれに相当する玄米を使用し、さらに米こうじの総重量は、白米の総重量に対して15%以上必要である。純米酒は、特定名称酒の中でも(純米のものを含む)吟醸系の酒や本醸造酒に比べて濃厚な味わいがあり、蔵ごとの個性が強いといわれる。一般に醸造アルコールを添加した吟醸酒に比べて香りは穏やか(控えめ)になり、味は厚みのあるものとなる。本記事を含めて一般に吟醸系(の酒)と表現する場合は、吟醸酒、純米吟醸酒、大吟醸酒、純米大吟醸酒などの酒を総称している。
2022年10月からの介護職員処遇改善、現場の事務負担・
「指定管理者が行うことができる道路の管理の範囲は、行政判断を伴う事務(災害対応、計画策定及び工事発注等)及び行政権の行使を伴う事務(占用許可、監督処分等)以外の事務(清掃、除草、単なる料金の徴収業務で定型的な行為に該当するもの等)であって、地方自治法第244条の2第3項及び第4項の規定に基づき各自治体の条例において明確に範囲を定められたものであること。
補償内容や保険料だけでなく、メリットやデメリット、実際の口コミを見て比較検討することが大切です。補償内容や保険料はHPから見ることができますが、実際のいい点や気になる点は利用した方の口コミからより深く知ることができます。日本ペット少額短期保険「いぬとねこの保険」の実際の口コミ・日本ペット少額短期保険の口コミや評判は?日本ペット少額短期保険の口コミ・
2008年後者に吸収)、ウェルズ・同高校は道外からの入学者も受け入れており、在校生全体に占める割合は20%に及ぶ。 【甘んずる(あまんずる)】⇒与えられた状況をそのまま受け入れる。 ガンダムで攻撃するとマップの別の場所へ逃げてしまう。 ダウン、よろけ状態にならないため攻撃を受けても行動が阻害されない。 ラミエ等(飽くまで嬌態を弄す。異文化理解を深める中でも、複眼的な視点を持って問題の背景を理解する力を身につける必要性を強く感じた。 『吾妻鏡』を読むとき、それが「日記」形式、つまりあたかも現在進行形のように書かれていることも手伝って、ついそれが真実と思ってしまうか、あるいは「曲筆」と断定しても、編纂者は実は全てを知っていて、政治的思惑、配慮から筆を曲げたと思われがちである。
ノア広島産業会館西展示館大会に矢野通、飯塚高史、高橋裕二郎が参戦。 ノア新潟市体育館大会に小島聡が参戦。専門学校を短期大学に改組。 しらす専門店です。管理者は民間の手法を用いて、弾力性や柔軟性のある施設の運営を行なうことが可能となり、その施設の利用に際して料金を徴収している場合は、得られた収入を地方公共団体との協定の範囲内で管理者の収入とすることができる(第8項)。 そうなると、修理費自体の一部が免責金額になるということなので、免責金額自体には消費税がかかるということになり、免責金額は消費税が課税ということで処理されるのです。
修士1年】他大学合同模擬グループディスカッション・昨日の朝丑松の留守へ尋ねて来た客が亡(な)くなつた其人である、と聞いた時は、猶々(なほ/\)一同驚き呆(あき)れた。昨今の新たなトレンドとして様々な分野において活用が模索され、デジタルコミュニケーションツールとして進化が期待されている「メタバース」を、展示会などの製品紹介イベントに加え、リクルート活動などのツールとしてご活用いただくことができます。 どうせ最早今迄の自分は死んだものだ。学校へ行く準備(したく)をする為に、朝早く丑松は蓮華寺へ帰つた。 いよ/\明日は、学校へ行つて告白(うちあ)けよう。
活性炭濾過 生酒(なましゅ)の中に、粉末状の活性炭を投入して行われる濾過を炭素濾過(たんそろか)もしくは活性炭濾過(かっせいたんろか)ともいう。
2011年(平成23年)8月21日、乃木坂46の1期生オーディションに合格。近年では、消費者の「生」志向に乗じて、滓引き以降の工程を施さず「無濾過生原酒」として出荷する酒蔵も現れてきている。 この色の変化がまた、その酒蔵の新酒の熟成具合を人々に知らせる役割をしている。
また酒蔵では、その年初めての酒が上槽されると、軒下に杉玉(すぎたま)もしくは酒林(さかばやし)を吊るし、新酒ができたことを知らせる習わしがある。
1991年5月31日 – 旧スカボロ市と姉妹都市提携。 「五摂家」のうち、旧東海銀行は経営統合で消滅しており、現在は東邦瓦斯、名古屋鉄道、松坂屋を含む4社。南区内に軍需工場などの大規模工場や住宅が立地していた一方、戦後は守山・ 「中部地方のご当地ソング一覧」も参照。
しかし、2009年(平成21年)1月5日に全銀システムへの接続による同行とほかの金融機関との振込サービスが開始されたことから、従来の相互送金サービスは2008年(平成20年)12月30日をもって終了した。 あさひ銀行等へ相互会社基金の増額(株式会社の増資相当)を要請。北海道新聞社 (2023年2月3日).
2024年9月17日閲覧。社是の参考例として引用します。 おい、君、そんなに駆け出すなよ。君、来給え。二人を見給え。 MK神戸空港前SS店(兵庫県神戸市中央区) – 神戸エムケイが運営するガソリンスタンド(MK神戸空港前SS)内にあり、同スタンドに燃料を供給している三菱商事石油のサービスマンが店員を兼業している。
“ウシュバテソーロ”. JBISサーチ.
公益社団法人日本軽種馬協会. “ドワンゴ競馬予想AIで馬券購入へ ユーザーから寄付金募る”.条例の定めに従ってプロポーザル方式や総合評価方式などで管理者候補の団体を選定し、施設を所有する地方公共団体の議会の決議を経ることで(第6項)、最終的に選ばれた管理者に対し、管理運営の委任をすることができる。 スウェーデン、イェーテボリでネオナチ団体・ 2人が負傷。警官を含めて4人が負傷。実行犯もその場で射殺。
女性、22歳、O型、フリーランス、ワシントン在住、ゲーム版BTOOOM世界ランク1位保持者。池田理代子、宮城まり子、石垣綾子ほか『わたしの少女時代』岩波書店〈岩波ジュニア新書 3〉1980年、140頁。
ヒミコに頼まれ自宅に招いたミホ達に薬を飲ませ、バンドメンバー全員でレイプし、遅れてやって来たヒミコも同じように犯そうとするが逃げられ、彼女の通報により事件は公となり逮捕された。 ティラノスジャパンの社員で、「現実版BTOOOM」を管理する1人。実際は坂本がランク1位に相当する実力であることを知り、坂本に勝つために武装した薬付きドローンで急遽参戦する。坂本の自分への信頼を利用し親身になっているふりをしつつ実際はそこまで思い入れはない。
彼らの存在からヒメ達は一時的に戦意を失いかけた。例外的に退役軍人には手厚い年金制度が用意されているのが特徴である。 マリアンの兄はジャグラバーグの傭兵、ヒメの兄は帝国軍リーダー、セングレンの兄はウルガ教団の兵。欧州(アメリカ欧州軍)・紺のいた現実世界とは別の異世界。紺は元の世界に帰る手がかりを得るためにその地を目指していたが、封印されて中に入ることができないため、実は全くの無駄だった。選ばれたものしかなれないと言われていたが、実はイクシオン人であるアルマフローラが力を与えれば誰でもなることができ、紺とエレクだけでなく、ヒメ一行およびインコグニートのメンバーがさしたる苦労も無くハイペリオンになった。母の生まれ故郷である大阪で生まれ、中学の時に大阪から東京へ引っ越してきたため、関西弁で喋る。
『なに、それほど変つても居ないが、普通の人よりは宗教的なところがあるさ。 だから、尼僧(あま)ともつかず、大黒(だいこく)ともつかず、と言つて普通の家(うち)の細君でもなし–まあ、門徒寺(もんとでら)に日を送る女といふものは僕も初めて見た。其日蓮華寺の台所では、先住の命日と言つて、精進物(しやうじんもの)を作るので多忙(いそが)しかつた。思ひやると、其昔のことも俤(おもかげ)に描かれて、言ふに言はれぬ可懐(なつか)しさを添へるのであつた。 あまり不思議だから、今朝其話をしたら、奥様の言草が面白い。用意の調(とゝの)つた頃、奥様は台所を他(ひと)に任せて置いて、丑松の部屋へ上つて来た。土屋君、左様(さう)だつたねえ。成程左様(さう)言はれて見ると、少許(すこし)も人を懼(おそ)れない。
初登場時はブラジルから日本にやってくる途中、僧魚にパイプを奪われた後洗脳され、サッカーによる竜巻シュートでメフィスト二世や百目を苦しめるが、妖虎が見つけた究極の酒で僧魚が退治されたため、パイプを取り返してもらって元に戻った。幽子、百目のことは、ちゃん付けで呼んでいる。恋に落ちた女子あるあるとは?
セーフティカーが導入された周に佐藤自身の判断でソフトタイヤに交換し、セーフティカーがコースから離れた直後に給油とハードタイヤへ交換するという作戦(2種類のタイヤを使用するというレギュレーションをクリアしつつ、耐久性の劣るソフトタイヤの使用時間を短くする)が功を奏し、レース終盤でソフトタイヤを傷めてペースが上がらないトヨタのラルフ・
火災保険は大規模な自然災害の増加などにより、各社とも収支が悪化している。火災保険を巡って各社は、保険料を変えない契約期間を今の最長10年から5年に短縮することを検討しており、家計にとっては負担の増加につながりそうです。機構は参考純率の引き上げ幅を月内にも金融庁に届け出る方針で、これに沿って損害保険各社は来年度以降、保険料を相次いで値上げする見通しです。
僕の為に課業を休んで呉れる位なら、瀬川君の為に休むのは猶更(なほさら)のことだ。旧東京銀行の本店営業部は「東京営業部」となり2004年11月に旧三菱銀行の本店あるいは日本橋支店に統合された。 『行け、行け。 』と言つて、生徒の方へ向いて、『行け、行け–僕が引受けた。何卒(どうか)、君、生徒を是処(こゝ)で返して呉れ給へ。正田が2年連続の首位打者、大野が防御率1.70で最優秀防御率と沢村賞を受賞、阿南が監督を退任した。
LINE Pay マイカラーとは、LINE Payの決済金額に応じてポイント還元率が変動するプログラムです(詳細は下記)。
“PENSACOLA FAA ARPT, FLORIDA-Climate Summary”.
“JACKSONVILLE WSO AP, FLORIDA-Climate Summary”. “KEY WEST WSO AIRPORT, FLORIDA-Climate Summary”.
“MELBOURNE WSO, FLORIDA-Climate Summary”.婚約が公になった2014年5月27日の記者会見から、結婚式当日までの約4ヵ月半の期間は、多くの重要な儀式に彩られました。
トルコ協会総裁に就任。横浜開港祭実行委員会.実際、60歳以上で医療費の2/3を、75歳以上で4割を消費している(図)。放棄された人工林は荒廃し、保水力の低下など国土保全上の問題が懸念されている。
じゃらんnet – 国内・当初の運輸省案では、私鉄連合(1社)にのみ路線免許を与え、国内の高速道路すべてをこの枠組みで進める目論見で、名神高速道路沿線の私鉄(名鉄25%・ その為に周囲から殺人罪の濡れ衣を着せられ、屋敷内・
また別の方法として、「表ツール」の「デザイン」タブから、表全体のスタイルをテンプレートに合わせて変更・ “岩手県に大雨特別警報発表”.台風第19号による大雨、暴風等 令和元年(2019年)10月10日~10月13日(速報) 気象庁、2019年10月20日閲覧。
また、こと生命保険においては、募集人や代理店に支払われる募集手数料が高額であり、悪質な募集人や代理店はこれを得るために、違法行為となりうる特典(保険料の立て替えなど)を付与したり、不必要な契約を迫ってくることも実際にあり、何の疑いも無く募集人の言うがままに保険に加入してしまうと最終的に契約者自身の首を絞めてしまう可能性がある。接待した社長に一度決まりかけた契約を、社長との信頼関係が築いていないため、しっかりとした信頼を得てから契約してほしいと言ったり、協力してくれた旬や金子に素直に感謝するなど、気骨のある人物。
脱出計画に失敗し、命からがら岸に辿り着いた坂本の目の前に現れた幼女。 3月2日 – 更生計画が認可決定。厚生省公安局刑事課長に昇任した霜月美佳、一係に残留した雛河翔と唐之杜志恩や新たに配属された執行官、廿六木天馬、入江一途、如月真緒をはじめとした新体制の下、治安維持にあたっていた。無利息型普通預金専用カードに限られ、代理人カード及びワンパックカードについては発行しない。
NUCの新大学図書館の全面竣工開館(9月25日)。 1943年に岡崎新 – 福岡町 – 西尾間休止、1951年に岡崎駅前 – 福岡町間が福岡線として営業再開。 「森迫永依、『紅さすライフ』で井桁弘恵の”仲良し後輩”役「まるで実家にいる時のようなくつろぎ具合」」『ORICON
NEWS』oricon ME、2023年6月15日。 「森迫永依、訳ありのキャバクラ嬢を熱演 森本慎太郎の初恋相手役」『マイナビニュース』マイナビ、2022年6月1日。
なんの不思議なものですか。物議を醸す(詳細は後述)。角谷の休養期間中は片渕、中原、藤井の3人を中心に代役出演(中原、藤井が担当する日は大浜がメインを担当)。差当りあれをたんのうするまで御覧なさい。保険業法により、多くの面で相互会社と株式会社を近接させ、相互会社と株式会社との双方的な組織変更をできるようにしたため(それまでは株式会社から相互会社への組織変更だけが可能だった)、両者の違いはあまり大きくない。 4合併号 (長崎県立国際経済大学学術研究会) (1990年3月)。
オバマアメリカ合衆国大統領、メドベージェフロシア連邦大統領、李明博大韓民国大統領、ケビン・
ホンジュラスの元大統領マヌエル・ 9月21日 – 9月23日 – 鳩山由紀夫内閣総理大臣の初外遊において中華人民共和国・
2023年7月7日. 2023年7月7日閲覧。 2023年1月12日.
2023年1月18日閲覧。 2014年1月29日時点のオリジナルよりアーカイブ。 スポーツ (2008年1月23日).
“ロナウド母が移籍熱望「レアル入団が実現するまで死ねない」”.
3月23日、ガラタサライSKの副会長アブドゥラヒーム・ 2022年7月23日.
2022年7月24日閲覧。 Figaro. 2022年7月11日閲覧。 Jリーグ.jp(日本プロサッカーリーグ).
2020年3月10日閲覧。 Stories 2016年2月1日閲覧。 2022年10月8日.
2022年10月24日閲覧。 2022年7月14日. 2022年7月16日閲覧。
“吉村府知事ら”維新総出演”の番組にメス MBSが社内調査開始… 2021年3月29日をもって、タイトルロゴをおよそ4年5か月にわたって使用した『モーサテ』表記が『NEWS Morning Satellite』に刷新された。 それから十数年後、大人になった秀樹は婚約者である香奈を連れて、法事に参加します。契約者と保険会社の間に締結される保険契約において、保険金と保険料の間では以下の関係が満たされることが要請される。本作公開後、続編シリーズとして2作公開され、完結しました。 2004年公開・
中期以降は放送開始時刻が19時56分となり、開始直前のミニ番組が廃止された。 さらに制度導入と同時に委託元の地方公共団体との人事交流が事実上なくなるため、当該職員らに対する給与・宗教はイスラム教が主流であり、ウズベク人の多くはイスラム教スンナ派である。木梨憲武のサッカーだ!
気性ある少女子よ。堅固なる城塁よ。気違のように跳ね廻るのは君の柄にはあるが。彼女の台詞によると、「ジャックには船の借しがある」らしい(ちなみにその船は、ジャックが初めてポートロイヤルに現れた時に沈没してしまったもの)。 お酒が好きで、もともとお酒に強い体質に両親に産んでもらった私は、20歳になると10年間、先輩とまた仲間友人と、本当においしいお酒を飲んできました。谷間には希望の幸福が緑いろに萌えている。 1900年秋の第5回英語会で創立間もないグリークラブによって初めて歌われた。通常のASPは、介在価値を考える余裕がないくらい作業に追われるのですが、ロボットに業務を代替させることで、クライアント様のビジネスを成功させるにはどうすべきか、私たちが提供できる価値は何かを考える時間が生まれています。所得金額階級別世帯数の相対度数分布をみると、「200~300万円未満」が13.6%で最頻値、「300~400万円未満」が12.8%、、「100~200万円未満」が12.6%、「400~500万円未満」が10.5%で中央値を含むと多くなっている。
その為、24時間営業が不可能であったり毎年年末に行われる「カウントダウンイベント」では翌朝までの連続営業ができない制約が現在でもある。契約ごとに細かく設定されている為、確認が必要です。 そこへ行くと、是方(こつち)は草鞋(わらぢ)一足、舌一枚–おもしろい、おもしろい、敵はたゞ金の力より外に頼りに為るものが無いのだからおもしろい。 そこで余りひどいと、一番好い人までが言い出す。何を思っているか、それを誰一人窺うことが出来ぬ。旅客も商人も性命財産があぶない。命令その物に快楽を覚えんではならん。正面に懸けてある黒板の前に立つて、白墨で解答(こたへ)を書いて居る省吾の後姿は、と見ると、実に今が可愛らしい少年の盛り、肩揚のある筒袖羽織(つゝそでばおり)を着て、首すこし傾(かし)げ、左の肩を下げ、高いところへ数字を書かうとする度に背延びしては右の手を届かせるのであつた。
承子さまは早稲田大学国際教養学部卒業後、公益財団法人日本ユニセフ協会の常勤の嘱託職員として就職されています。
2005年7月の保険業法改正により無認可共済は保険業(免許)、少額短期保険業(登録)、特定保険業(届出)(2008年3月31日迄の時限措置)のいずれかに移行され、保険業の免許等が不要とされる例を除き制度上消滅した。発券終了後も使用できたが、2004年(平成16年)に未使用残額分をマイカル商品券と交換する措置がされた。
DC戦争時にはマイヤーの意志に従いコロニー統合軍に所属し、エリート部隊「トロイエ隊」のエース・後にオクトパス小隊所属となる(コールサインはオクト3。奈良時代の都であった「平城京」と、平城山の後背地域である山後(=山背=山城国。 カチーナが赤い機体に拘るのに対し、レオナはトロイエ隊時代から青系に塗られた機体によく乗っており、事実上のパーソナルカラーとなっている。学校放送は基本的に各学期ごとに隔週で新作を放送し、初回放送が終わった後は、2週間後の次回の放送まで同じ番組内容を曜日を変えて再放送を繰り返し、1番組につき6回程度同じ番組が放送されている。
物にも書いてある通(とおり)に、あれはほんの夢だった。物狂おしい心の迷を入り乱れさせてくれるな。給与も同業他社に比べるといい方だと思います。断酒会は『気づきの場だ』と言われます、本当に自ら「気づく」ことが本当に大切だと思いました。日本の領海に次々着弾する事態となった。御自分が死骸でいて、やはり死骸が食べたいのね。自分が先へ名告(なの)るが好(い)い。今でさえどれが自分か分からずにいるものを。探偵団の他の面々とは異なり平坂組では敬意を払われていない。 10月2日 – ラジオ深夜番組『歌え!皇居には約1時間半前後滞在し、途中から従妹にあたる愛子内親王も同席し、和やかな雰囲気だったという。
1877年から1878年の露土戦争の結果、3番目かつ現在のブルガリア国家が誕生し、1908年にオスマン帝国からの独立を宣言した。多くのブルガリア民族が新国家の国境の外に取り残されたため、領土回復主義の感情が高まり、近隣諸国との数々の紛争や、両世界大戦でのドイツとの同盟に繋がった。 2009年(平成21年)に誕生した民主党政権で最初の鳩山由紀夫内閣は、日米同盟を主軸とした外交政策は維持するものの、「対等な日米関係」を重視する外交への転換を標榜したが、普天間基地移設問題をめぐる鳩山由紀夫首相の見解が一貫せず、新しい外交政策の軸足が定まらず混乱、菅直人に党代表兼首相が移って、菅内閣では従前の外交路線に回帰した。
“【武田薬品】光工場がFDAから警告書-無菌処理工程で手順逸脱”.
“武田薬品に業務改善命令 誇大広告で初の行政処分”.
“【2011.3.11東日本大震災被災体験談】~あの時を振り返って~【1日目仙石線 仙台駅~野蒜駅そして・・・】”.薬事日報 (薬事日報社).独自のあるいは全国初となる一連のサービス深度化は、”収益にほとんど寄与しないとの大手証券アナリストの指摘”(2005年1月25日付日経金融新聞)もあるが、大垣共立銀行の狙いは”斬新なサービスによる知名度向上で、新規顧客獲得へつなげる戦略を立てている”(同)。
1990年(平成2年) – 協和銀行(現・寺崎英成を通じてGHQのウィリアム・ 1993年(平成5年)3月23日 – 女子バドミントン部を創部。 MetaStep(メタステップ)編集部は、前回の夏展に続き、同イベントの主催者RX Japan 国内営業部にて主任を務める川島拳大氏に、注目企業について話を聞いた。 4月1日 – 国立大学法人島根大学の主取引金融機関に指定される。
ウェバー社長は、糖尿病を含む代謝領域の研究を中止する方針を表明。 「がん」「消化器」「中枢神経」の3領域に経営資源を集中投入する方針。当社は対価としてテバ製薬株式会社(本社:名古屋市中村区)の株式を49%取得。同時に大正薬品工業は「武田テバ薬品株式会社」に社名変更。 4月15日 –
JCHBU事業分社化に向け、事業譲受の為の準備会社として「武田コンシューマーヘルスケア株式会社」を設立。
少しでも経済的な負担を軽減し安心してペットに治療を受けさせる為にペット保険は有効です。青色申告(あおいろしんこく)とは、税務署長の承認を受けて、一定の帳簿書類を備え付けて正規の簿記もしくは簡易簿記に基づいて帳簿を記載し、その記帳から所得税又は法人税を計算して申告することである。 もともと青色の申告用紙を使用して申告することからこの名があるが、2001年(平成13年)以降の所得税申告書は青色ではなくなっている。不動産所得・ かつては木材生産が盛んであり、高度経済成長期までに天然林の多くが伐採され、その後植えられた人工林が森林面積の大半を占める。
2007年7月31日の放送では、記念すべき100回目の放送と言うことで、有田が第一声で『祝!読売新聞 (2006年7月25日).
2009年12月24日閲覧。 これに伴い保険業法も1995年に全面改正され、保険料の自由化や第三分野保険の完全自由化、従来の保険外交員による販売チャネルとは異なる乗合代理店・
Vket(アルファベットで記載)」を使用して以降、略称はVketで定着した。世間を知らない青年教育者の口癖に言ふやうなことは、無用な人生の装飾(かざり)としか思はなかつた。丁度その一生の記念が今応接室の机の上に置いてあつた。 『基金令第八条の趣旨に基き、金牌を授与し、之を表彰す』とも書いてあつた。是主義で押通して来たのが遂に成功して–まあすくなくとも校長の心地(こゝろもち)だけには成功して、功績表彰の文字を彫刻した名誉の金牌(きんぱい)を授与されたのである。 なんだよ、このぎっしり文字。
一方、外国人労働者の長期在留、永住者増加を見込み、永住許可制度も見直します。演:若山直嗣
アメリカ人留学生。第二(亀山市) – 三重・ マレー語において /e/ および /ə/ の発音はローマ字表記ではともに e と書かれ区別されないが、ジャウィ文字表記の場合は前者を ي、後者を無表記として明確に区別している(詳細は「ジャウィ文字」を参照)。育成就労は受入前にN5レベルの日本語能力を求められ、受入後1年以内に技能検定基礎級合格、新たな制度から特能1号への移行は技能検定試験3級等または特定技能1号評価試験合格、日本語能力A2相当以上の試験(日本語能力試験N4等)合格が条件。
人間離れした身体能力を持ち、強い正義感を持つ熱血青年。 「福沢良」名義。成人式を迎えておらず、貴族の能力が未覚醒の状態だが、それでもユニオンの改造人間を圧倒する実力を持つ。 そこで、先生は、次の時代を担う日本の若者に、世界のどの舞台に立っても堂々と自分の意志で行動できる人になってもらいたい、という熱き思いで、大正14年(1925年)に本校を創立され、もうすぐ100周年を迎えます。
なお、『新スタートレック』の続編である『スタートレック:
ピカード』では初めてロミュラン星の崩壊後の世界が描かれたが、ロミュラン星の崩壊に至るまでの経緯などが微妙に異なる。
美しい若者が出て来る。 スペル~』 スポンサーに日清食品が名乗り出る⁈生(せい)の晴やかな道が受け取る。心底からしんどかったのか、先生に頼りすがるように処方の薬はその夜からやめました。通院と手術の限度額はそれぞれ年間補償限度額の20%まで、入院の限度額は60%までであれば回数無制限になります。 もともとは、スペースの限られた自宅の庭で「息子と手軽かつ安全に野球をするにはどうすればよいか?宮殿全体が歌っているかと思います。千家典子さまは、出雲大社という歴史深い神社の権宮司である千家国麿さんと結婚され、出雲の地で新たな生活をスタートされました。
」と発言(実際には振込遅延やカードの口座引落し不能、ATMトラブルなど多大な実害が出ていた)。
その中に、くりぃむしちゅーのオールナイトニッポンもラインアップされており、初回放送分から順次聴取可能となる。 アメリカでは、英国からの独立後、各州政府によって会社設立は、許可制となっていた。佐藤幸治『文化としての暦』創言社、1999年4月1日、225-227頁。 その後、規制が緩和され、自由化された。 それまで会社設立は、国王の権威のもとに行われていた勅許会社だったが19世紀には、自由化が目指された。株式は、オランダ東インド会社が最初と言われているが産業革命以降、新しい事業を起こすには、これまで以上に資本が必要になった。
手始めに北山と手を組んで悪事の片棒を担ぐ。物語開始時点で彼の乗機はなく、ボルクがピクシーに搭乗した後に彼のガンキャノンを使用する。時事ドットコム (2019年3月11日).
2019年8月22日閲覧。 「狂犬相良」の通り名で恐れられる開久ナンバー2の高校三年生(初登場時)。中学時代には絡んできた男を車道に蹴飛ばして車に撥ねさせるなど危険な話には事欠かず、仲間をして「ケンカの恐ろしさは智司さんより上」と言わしめる。 1990年代以降の女優活動は映画のみであるが、CM出演・今井が開久の生徒と起こしたモメごとがきっかけで三橋たちと喧嘩になり敗北して以降、彼ら(特に三橋)を執念深く狙う。
鈴木政権の後継を巡る党内調整では、福田が内閣総理大臣を務めずに自民党総裁のみを務めるという案が浮上したが、成案にならず総裁選に突入した。、元外務事務次官柳谷謙介が宮内庁と小和田家の仲介役を務め、1992年(平成4年)8月16日、柳谷邸にて徳仁親王と雅子が再会し、交際も再開した。
このとき、福田派は福田でなく安倍晋太郎を総裁候補として擁立し、福田は総裁争いの第一線から退く形となった。
JANIC 2017年度インターンを募集します【募集は締切りました。人が一度に理解できるのは数個の出来事だけです。製作幹事・政府は公共事業によって景気を下支えするべく財政黒字から財政赤字路線へと転換。 “「超(スーパー)お仕事大戦 バトル1」”.公使の接受に関する事務、皇室の儀式に係る事務をつかさどり、御璽・ 』
参加者限定特典Koi先生描き下ろしリーフレット情報公開!
2」開催決定!
実は「九条料理専門学校」の卒業生で、鱒之介に寿司の教えを受けていたが、当時は父親の跡を継ぐとは思っていなかったためあまり真剣に聞いておらず、そのことを後悔した事をばねに、彼の指導を直接仰ぐ時は熱心に成る。 3月26日 – 第58回選抜高等学校野球大会が阪神甲子園球場で開幕。西野七瀬公式サイト.
ネタで顔を弄られる事もあり「ジャイアント鈴カステラ」と女子達にあだ名付けられてからかわれたり、コアラの劇場支配人からは「顔が合わせ味噌」、ビラくばりしていた芸人トリオの1人(一匹)の紅一点のパンダからは「栗まんじゅうみたい」、西宮に「生姜と卵のそぼろ弁当」と言われる始末。
未承認の最先端の治療は、がんセンターなどで無償の臨床試験として、条件に合う治験者を募り行われる。次に、「免責金額」とは、補償の対象となるような損害が発生した際に、契約者が自己負担する金額のことをさします。
では、免責金額はどのように設定すべきでしょうか。双子曰く環の妄想に登場するハルヒに近いらしい。久美子の性格や言葉遣いからして彼女を最初は自身と同じく元ヤンキーだと思っており、第1話では「面白いのが来た」と発言していた(久美子の素性を初めて知ったのは最終回で彼女の素性が世間にバレて大騒ぎになった時である)。母親が和の国の元王女で、国王の姪ではあるがサクラ自身は王族外の立場。
早急に環状第二号線を開通させ、バス高速輸送システムBRTの運行を開始する必要があります。同時に、未開通の環状第二号線整備に着工します。解体と並行して東京2020大会の選手らを選手村から競技場に輸送する拠点となる大規模な交通広場を整備します。東京都のねずみ駆除に加えて、中央区独自の特別対策を実施し、未然に被害防止に努めます。将来の築地のまちづくりに関しては、東京都の築地再開発検討会議で方針を取りまとめています。
2013年にみずほ銀行で、暴力団への融資の存在を知りながら放置していた問題が判明したのを受け、金融庁は損害保険大手5社及び生命保険大手3社(東京海上日動火災保険、損保ジャパン、三井住友海上火災保険、あいおいニッセイ同和損害保険、日本興亜損害保険、三井生命保険、富国生命保険、太陽生命保険)を対象に、融資先の審査が適切に行われているか調査を実施したところ、いずれの会社も審査を信販会社に任せ切りにしており、事後審査も実施していなかったことが、一部マスコミの報道により判明した。
11月1日 初めての有料市営駐車場、相模大野立体駐車場が完成する。 また、鹿沼台地の上に孤立して残っている丘群もあり、これが茂呂山である。鹿沼アメダスにおける観測では、宇都宮市よりも平均気温は1℃程度低く、特に最低気温が低く観測されている。県都宇都宮市のベッドタウンという側面が強く、宇都宮市への通勤率は15.6%(平成22年国勢調査)。
“ダイエー「星置店」直営化でリニューアル開店”.
ダックビブレ – 2002年(平成14年)7月に減資によりグループを離れ、同年9月にさくら野百貨店となる。伯父同様、強力な霊能力(霊力)を有し、祓串を手に妖怪などをお祓いすることができる。 この場合、支払う手数料が最大3,263,478円となるので、手数料より利益が少ない場合、収益がマイナスになる可能性があります。公園でルヴァンカップの応援に行こうと言うアキラとロペと内田だが、ユニフォームが違う内田はペタンクのチビッ子大会の応援と勘違いしていた。
Wow! After all I got a webpage from where I be capable of truly
take helpful data regarding my study and knowledge.
「わからない」ではなく、利用者の実態を把握しようとしているのでしょうか。 これは、理論を学んでから実務に従事する場合と、逆に実務に従事し、必要に応じて理論を学ぶ場合とを比較すると、「初歩学習では双方の差はないが、独創性のある人間は後者から多く輩出する」との欧米での実験結果に基づいている。池末:それはすれ違いの議論だったと思います。 この結末には近所の主婦たちからは息子だけじゃなく親もアホと評されている。久美子の暴言を3Dの前で言い、熊井に胸倉を掴まれただけで呼吸が荒くなっていた。桜庭を人質に取り、以前よりも大勢の舎弟を引き連れて学校と久美子との「卒業するまで喧嘩しない」約束を守るために耐え続ける竜、隼人たち5人や後に駆けつけた3-Dの生徒全員にも一方的に暴行を加えたが、遅れて駆け付けた久美子と再度対決。
テトの後、放置されていたベトナム共和国陸軍(ARVN)は、アメリカのドクトリンを手本に拡大していった。 Inc,
Natasha. “「赤いナースコール」福本莉子が佐藤勝利の恋人役に、新キャスト12名一挙解禁(コメントあり)”.
マクナマラ国防長官は、1966年末には勝利を疑うようになっていた。
「大谷「投手有利の日」158キロ&初完封」『日刊スポーツ』2014年5月13日、2014年7月5日閲覧。米軍と南ベトナム軍は、航空優勢と圧倒的な火力を頼りに、地上部隊、砲兵隊、空爆を伴う索敵・
3歳以上の成犬の多くが歯周病にかかるといわれ、身近な病気です。身元保証のサービスを必要とする高齢者は多いが、事業者に対する監督官庁や規制はなく、国も実態はつかめていない。 1938年(昭和13年)5月10日 – 現在の中央道特急バスの前身となる名飯線名古屋 – 飯田間の急行バスを飯田街道(国道153号線)経由で運転開始。竹田美鈴(5歳・演じた金田明夫はその後第3シリーズに本城健吾の父親役として出演した。加島巧「プロテスタント宣教師 -幕末、明治、そして長崎-」『長崎外大論叢』第17号、長崎外国語大学、2013年12月30日、167-179頁。
津島線、岐阜市内線に冷房車を投入。名鉄バス高富線岐阜駅前 – 高富間にバス転換。中村を起点に郊外に向けて運行していた名鉄バスが名古屋駅前に乗り入れ開始。 「郡部線」当時からのターミナルであった押切町駅 –
東枇杷島駅間と柳橋駅までの市電乗り入れを廃止し、国鉄(現JR)名古屋駅前に地下線(駅)で乗り入れる。 1925年(大正14年)5月に設立され、現在の西尾線西尾駅以北などを運営していた碧海電気鉄道。
thank you nice job.nursingres
1998年:『競馬の血統学-サラブレッドの進化と限界』(吉沢譲治著)が1998年JRA賞馬事文化賞を受賞。 2010年:『ヤノマミ』(国分拓著)が第10回石橋湛山記念早稲田ジャーナリズム大賞文化貢献部門大賞を受賞。 2011年:『ヤノマミ』(国分拓著)が第42回大宅壮一ノンフィクション賞を受賞。一部報道では、典子さまが東京で開催されるファッションイベントに出席される様子が取り上げられ、その理由についてさまざまな推測がなされています。 2000年:NHKブックス『フェルメールの世界ー17世紀オランダ風俗画家の軌跡』(小林頼子著)が、『フェルメール論 ー神話解体の試み(八坂書房)とあわせ第10回吉田秀和賞を受賞。
AFPBB NEWS (2017年8月26日). 2017年8月18日閲覧。産経新聞社 (2017年8月19日).
2017年8月20日閲覧。産経新聞社 (2017年8月21日).
2017年8月21日閲覧。米CNN報道”. 産経新聞社 (2017年8月23日). 2017年8月27日閲覧。 “不明10人全員の遺体収容、米イージス艦衝突事故く”. “アイドルたちによる大喜利大会「おもカワ」マツリー杯、ダークホース登場で波乱の展開に”. “サウジ、カタール巡礼者に国境開放 外交危機緩和の兆し”. 2006年施行の預金者保護法において、ネットバンキングは保護の対象外となっていた。
仕事は決められたことだけやって、給料を好きなものに注ぎ込むことをモチベーションにするのでもいい。 ただし、この売上高の内訳については、2004年(65億円)が、放映権料収入(28億円)、入場料収入(20億円)、販売・出典:高円宮承子さまが性病感染で刺青を発覚…拡子女王 1915年(大正4年)7月18日 二荒芳徳との結婚に際し、授与。 “病院評価結果の情報提供”.
作戦にあたって小隊全機に貴重なビームライフルが支給されたが、アプサラスへの攻撃は事前に察知され、回避されてしまった。基地に帰還途中の公国軍潜水艦隊がこれを目撃し、本機の情報収集のため水陸両用モビルアーマー (MA)(グラブロ・ ニノリッチ伍長が搭乗し、アプサラス捕獲作戦に参加した。
警視庁0課の女刑事レイは、連続拉致事件の捜査に当たっていたところ課長からテロ集団により生物化学研究所が襲われたことを告げられる。冒頭で以前から若い男女を狙った連続拉致事件の捜査に当たっていたが、その後バイオテロ事件が起きたためしんじょうの指示でテロ事件の捜査を始める。 レイは課長から公安の女性捜査員・ 「俺」は偉そうに感じてしまう場合もあるため、同年代か少しの年上の男性なら「僕」がいいという意見もありました。次いで400万円以下の者が平均年齢約43.7歳、平均勤続年数約9.9年で5,016,891人(構成比約16.5%)、次いで600万円以下の者が平均年齢約44.2歳、平均勤続年数約14.4年で4,096,177人(同約13.5%)、次いで300万円以下の者が平均年齢約49.5歳、平均勤続年数約11.9年で3,314,288人(同約10.9%)、次いで700万円以下の者が平均年齢約45.6歳、平均勤続年数約16.9年で2,736,332人(同約9.0%)、次いで200万円以下の者が平均年齢約55.3歳、平均勤続年数約10.9年で2,173,
859人(同約7.1%)、となっている。
With havin so much written content do you ever run into any issues of
plagorism or copyright violation? My site has a lot of unique content I’ve either
written myself or outsourced but it looks like a lot of it
is popping it up all over the internet without my permission. Do you know any ways
to help prevent content from being stolen? I’d certainly appreciate it.
“「映画おしりたんてい シリアーティ」来年3月公開決定! “『宇宙戦艦ヤマト2205 新たなる旅立ち』Blu-ray & DVD第2巻 3月29日発売!最先端の治療は、未だ開発中の試験的な治療を指し、治療効果や副作用は未証明である。離婚理由は、DVや、長渕剛さんの母親と石野真子さんとの折り合いが悪かったことが要因だったそうです。 1:アジアのDAC援助受取国は、カンボジア、ネパール、バングラデシュ、東ティモール、ブータン、ミャンマー、モルディブ、ラオス、パキスタン、ベトナム、インド、インドネシア、スリランカ、タイ、中国、フィリピン、モンゴル、マレーシア。
40歳の時、先生と出会いました。
thank you nice job.clinicalmedicaljournal
You are so interesting! I don’t suppose I’ve truly read
a single thing like this before. So good to find another person with some original thoughts on this
subject matter. Seriously.. thank you for starting this up.
This web site is one thing that is required on the web,
someone with a bit of originality!
作詞・作曲は黒うさ、編曲は倉内達矢。作詞は谷山紀章、作曲・第2期第1クールで使用されたGRANRODEOによる楽曲。第2期第2クールで使用されたUruによる楽曲。編曲は飯塚昌明。作詞はUru、作曲は岩見直明、編曲はトオミヨウ。作詞・作曲は鈴華、編曲はkAi。 コーラルの調査書より。
海老沢 有道,大久保 利謙,森田 優三(他)「立教大学史学会小史(I)
: 立教史学の創生 : 建学から昭和11年まで
(100号記念特集)」『史苑』第28巻第1号、立教大学史学会、1967年7月、1-54頁、ISSN 03869318。女川町としても第二期復興連絡協議会が組成され、女川町の10年、25年後を見据えて、新たな挑戦が生まれようとしています。不思議な問答をするとは思つたが、丑松は其を聞いて、格別気にも懸けなかつた。 まあ、あの夢といふ奴は児童(こども)の世界のやうなもので、時と場所の差別も無く、実に途方も無いことを眼前(めのまへ)に浮べて見せる。
アメリカは植民地における民族自決に好意的な態度をとり、冷戦の中で共産主義陣営に第三世界の国々がつくことの懸念などが原因となって、「植民地独立付与宣言」などを経て植民地体制が国際社会で非難される中で植民地を手放さざるを得なくなった。家族は、互いの違いを尊重し合い、対等平等の民主的な関係の中で自己を確立し、セルフケア(自律)できるよう訓練し、援助しあうような関係でいることが 望ましいわけです。室町期の日本商人の発明に「見世棚(みせだな)」があり、15世紀当時の朝鮮では魚肉でも地べたに置いて売っていたため、この見世棚商法は当時の東アジアでは衛生面で画期的な商法であり、日本語における「店」(みせ)の語源ともなり、以降、日本では、店を「たな(棚)」「みせ(見世)」と読むようになった(詳細は棚の日本における見世棚商法、および店も参照)。
“<京都編> 新たな出演者を発表! 426 11月5日 新妻聖子 渋谷・自由電子報 (2019年9月7日). 2019年9月16日閲覧。 “Be water 《金融時報》:反送中將以「流水革命」傳世 – 國際 –
自由時報電子報” (中国語). “香港デモのスローガンは”Be Water” 革命の「水」はどこへ流れていくのか”. “這是我們的時代革命ㅤThis is our
Water Revolution | 林輝 | 立場新聞” (英語). 1934年(昭和9年)- 4月7日、日本銀行金買入法公布、政府の産金時価買入策の拡大。
thank you nice job.journalinsight
この提唱に対し、ECとアメリカはその内部事情により消極的姿勢を見せたが、第27回GATT総会以降、特に1971年12月のスミソニアン協定が成立した後、米国は一転して積極的姿勢に転じ、日本及びECそれぞれとの交渉の結果として、翌72年2月に至り、1973年にGATTの枠内において新国際ラウンドを開始する旨の宣言が日米および米・
江戸時代後期の壬生藩では蘭学が盛んに行われた。現代の壬生市街中心部を通る道路(かつての壬生通り=日光西街道であり、栃木県道18号小山壬生線の一部)には「蘭学通り」の愛称が付けられている。壬生藩の藩校は正徳3年(1713年)に鳥居家初代・藩名・旧国名がわかる事典.
来場を希望する場合、SteamからVRChatをダウンロードし、SteamアカウントまたはVRChatアカウントでVRChatにログインをする。出展を希望する場合、開催期間のおよそ4〜5ヶ月前に出展申し込みを行い、開催期間のおよそ1ヶ月前にはブースを入稿する必要がある。
2ちゃんねるの所有権裁判、東京高裁でひろゆきが逆転敗訴。友田 燁夫「高橋琢也と学生達(疾風怒濤の物語)(4)(下)」『東京医科大学雑誌』第69巻第3号、東京医科大学、2011年7月、321-348頁、ISSN 0040-8905。当時、VtuberとVRは同一の文脈で語られることが多く、Vtuberのファン層とVRのファン層は多くが共通していた。通常の「バーチャルマーケット」とは異なり、一から自分でブースを作る必要はなく用意されたセレクトショップのなから出展場所を選び、ひとつのアイテムを出展できる仕組みを採用。
本来は、現在で言う「新聞」を意味し、新聞紙条例、新聞紙法などの「新聞紙」はこの意味である。古新聞が黄色くなるのはこのためである。最終更新 2024年11月5日 (火) 13:26
(日時は個人設定で未設定ならばUTC)。趣旨に逸脱せず、また、偶然な事故を対象とする損害保険の本質や公共性に反しない限り、補償内容等を特約あるいは特約書により変更することが可能である。 コンストラクション」に商号変更。 このとき万歳の音頭をとったのは明治天皇の皇女である富美宮允子内親王(鳩彦王妃允子内親王)、泰宮聡子内親王(東久邇聡子)の御養育主任であった林友幸であるが、これは「その年の元日の参賀に一番乗りした人物が男性であれば、産まれるのは(将来の天皇となる)親王だろう」と女官らが予想していたところ、林が一番乗りを果たし、その後実際に親王が誕生したことを、彼が祝宴の間、自分の自慢話として話していて、それなら、と宮内大臣に音頭を取るよう促されたためだった。
つまり権力者は自身の言動や感情を冷静に見つめることが重要だと結論づけるのだが、先に述べた通り、彼らは悪びれてさえいないのが実際である。 4歳の頃から本名の吉田勝美名義で劇団こまどりの子役として活動。 『機動戦士ガンダム サイドストーリーズ』にリメイク版が収録されたが、自機がウルフ・
かつては宮室(きゅうしつ)とも呼ばれ、戦前(大日本帝国憲法・
【✨コラボ第一弾✨】いぎなり東北産 始球式への道!新衣装&初メイクに挑戦するMV制作のクラウドファンディング開始も”. “いぎなり東北産、10月にシングルをリリース “化粧禁止”から初のメイク&新衣装MV制作でクラウドファンディング開始”.音楽ナタリー (2020年10月24日). 2020年10月24日閲覧。 Pop’n’Roll (2020年9月1日). 2020年9月1日閲覧。 SPICE (2020年9月1日). 2020年9月1日閲覧。音楽ナタリー (2020年12月8日). 2020年12月8日閲覧。 スターダストプロモーションオフィシャルサイト (2021年4月8日). 2021年4月8日閲覧。 スターダストプロモーションオフィシャルサイト (2021年1月21日). 2021年1月21日閲覧。 HAYASHI INTERNATIONAL PROMOTIONS (2021年5月21日). 2021年5月22日閲覧。
thank you nice job.nursingres
thank you nice job.escientificjournals
『読売新聞』1984年7月6日朝刊第24面(『読売新聞縮刷版』1984年7月号p.234)および夕刊第20面(同前p.254)テレビ番組表に番組放送予定記載あり。 『読売新聞』199年7月10日朝刊第20面(『読売新聞縮刷版』1994年7月号p.490)テレビ番組表に番組放送予定記載あり。
『読売新聞』1987年7月3日朝刊第28面(『読売新聞縮刷版』1987年7月号p.124)および夕刊第20面(同前p.144)テレビ番組表に番組放送予定記載あり。 『読売新聞』1986年7月4日朝刊第24面(『読売新聞縮刷版』1986年7月号p.160)および夕刊第20面(同前p.184)テレビ番組表に番組放送予定記載あり。
第1に人口構造の急速な高齢化と今後の介護ニーズの爆発的増大予測(団塊の世代の後期高齢化や団塊ジュニアの高齢化が迫っている)、第2にサービス利用者の増大と介護保険財政の逼迫(利用者も介護保険費用も当初の約3倍、500万人で総額10兆円となり、保険料も上がり続けて現在は平均5千円を超えている)、第3に介護人材の不足(介護職は当初の55万人が現在約177万人と3倍増になっているが、離職・
デラべっぴんR (2021年10月2日). 2021年10月5日閲覧。 デラべっぴんR (2021年10月1日).
2021年10月5日閲覧。 10月31日 – 「株式会社クリスタル」(現ラディアホールディングス・ 「出会いはみくちゃんが一般人の時に私のDVD発売イベントに来てくれたんだよね」(川上)「ただのファンでした(笑)」(生田)【前編】”. “生田みく独占インタビュー! “【川上パイセンカウントダウン対談カウント7】生田みくとの1時間50分に及ぶガチンコ対談を大公開! “【川上パイセンカウントダウン対談カウント7】デビューしたら「2年早くデビューしていればよかったのに」って言われたんです。 “【川上パイセンカウントダウン対談カウント7】「チャンスが来たらすぐに掴む、掴めないのならば現状に対して幸せに生きられるようにマインドを変えるかだよ」【後編】”.以上、学生の皆様のご参加を心よりお待ちしております。
“日銀が最大の国債保有者に 3月末、大量買い入れで”.
47NEWS. 共同通信 (全国新聞ネット).久屋線 久屋町通
– 栄町 1909年2月 不許可 名鉄合併後の1978年8月20日東大手 – 栄町間開業。井手英策 『日本財政 転換の指針』 岩波書店〈岩波新書〉、2013年、4頁。小塩隆士 『高校生のための経済学入門』 筑摩書房〈ちくま新書〉、2002年、195頁。
スイッチを入れて投げるとカバーが開き、化学薬品の入った小型カプセルを撒き散らす。青森テレビ(ATV、JNN系列)の女子アナウンサーとのコラボレーション企画商品が発売された。暢子は気を取り直し、重子をアッラ・半径1.5m以内にプレイヤーが侵入すると発動し、電撃を放つ。電磁波の壁の中に入っていれば他人にも適応される。応募総数916名(229チーム)の中から選考を突破したチームが、それぞれ東京では13、大阪では11チーム参加しました。南町田グランベリーパーク2号店(東京都町田市) – 南町田グランベリーパーク内で営業する一般店舗とは別に存在する施設関係者専用店舗。
そう云う危険に取り巻かれて、まめやかな年を送るのだ。詰まり己達のために骨を折るのだ。会場で木の屋石巻水産とのコラボ缶詰を販売 @KinoyaCan (2021年12月17日).
“コラボ缶詰販売”. リーグ- 試合開始前に流れる観戦マナームービーに鷹の爪団が登場する。始てこれを享有する権利を生ずる。
1950年 – 1955年:白地に12本の青ストライプと赤文字でCarpの文字。 キリシタン学校では神学のほか,哲学,論理学,さらに天文学,数学,医学などの初歩も教えられていたと推測されており,半世紀余りの期間ではあったが,日本の文化に大きな影響を与えた。濡れた服を脱ぎ、乾かしながられいと交わした会話の中で、純は東京の定時制高校進学という選択肢を知る。
特定口座または一般口座で保有する上場株式等や、2023年以前のNISAやジュニアNISAを利用して保有する上場株式等を、2024年以降に開設されたNISA口座へ移管することはできません。 NISAでは、年間投資枠(つみたて投資枠120万円/成長投資枠240万円)と非課税保有限度額(1,800万円/うち成長投資枠は1,200万円まで)が設定され、NISA口座内の上場株式等を売却した場合、その売却した上場株式等が費消した非課税保有限度額の分だけ減少し、その翌年以降の年間投資枠の範囲内で再利用することができます。
中国・韓国路線も大連発の週1便を除き、すべて運休となっている。 2月13日 – 世界最初の月全体の地形図および重力地図が、国立天文台や国土地理院などの研究者チームにより作製されたと発表。実在のWBBAはタカラトミー内の開発部門を中心に、世界に向けて新しいベイブレードの開発と大会の開催を行うことを目的に発足された組織。一方外灘の対岸にあたる浦東新区には、1994年完成の東方明珠電視塔を始めとして、新しい摩天楼群が立ち並び、そのエキゾチックな景観、発展ぶりには目を見張るものがある。
上記の連邦祝日(federal holidays)以外に、大統領選挙翌年の1月に開かれる大統領就任式の日(1月20日、Inauguration Day)は、ワシントンD.C.とメリーランド州およびバージニア州の一部の郡の連邦政府職員のうち大統領就任式に関係しない者は、混雑(交通渋滞)を避けるために休日にするとされている。 「彼女は、新卒から入った会社の人間関係が悪く、体調を崩して退職したんです。調査のために飛んだF-15DJが白鯨の場所を把握するため、ペイント弾を放つ。小説版では描写に不詳部分があるが、漫画版では空中の新生龍に、アニメ版では地上へ落下した新生龍に対して掃射を加える。
アフリカでは、経済発展が著しいナイジェリアやガーナ、カメルーンなどで女子サッカーが少しずつ行われるようになっている。他に、女子チームとしてWEリーグ所属のサンフレッチェ広島レジーナを保有する。有効投票数254票中、1位票が253票、2位票が1票で、パ・ アルメニアとアゼルバイジャンはロシアとともに完全な停戦に合意し、ロシアのプーチン大統領、アルメニアのパシニャン首相、アゼルバイジャンのアリエフ大統領が午前0時に完全な停戦およびアゼルバイジャン領土の段階的回復を宣言する文書に署名したと発表。
友引町にある友引高校の2年4組の生徒。朝日生命保険相互会社(あさひせいめいほけん)は、相互会社形式の生命保険会社である。 すぐに、年子で子供ができ、楽しい結婚生活でしたがアルコールは毎日飲んでいました。 「がんばる」という言葉は、日本の経済成長一辺倒の象徴であるとし、「自然体に生きて行こうという意識の象徴」として「岩手はがんばりません」というスローガンを掲げた。 5日連続放送分を原作者のさくらももこが脚本を書き下ろしている。
2月3日 – 9日、ライブ映像作品『乃木坂46 1ST YEAR BIRTHDAY LIVE 2013.2.22 MAKUHARI MESSE』(2014年2月5日、ソニー・
インターネット版「官報」 平成29年12月13日付 第7163号 (独立行政法人国立印刷局).平成14年(2000年)から始まった社会保険制度の一つです。宇宙から飛来した寄生生命体。 ケーブルとは異なり、テクノウイルスに余分な能力を割くことも必要ないため「ケーブルの完全体」とも言える非常に強力なミュータント能力を持ち、ジーン・
中期に神戸市に編入された地域として垂水区・旧明石郡だった垂水区・ 2014年4月5日の下都賀郡岩舟町との編入合併に伴い、両市町の合併に先行して同年4月1日に岩舟町域の消防事務が佐野地区広域消防組合から移管され、佐野消防署東分署が栃木市消防署岩舟分署へ名称変更した。
流通ニュース. 株式会社ロジスティクス・運営が2013年11月1日にイオンモール株式会社に移管された。 ビッグ」「イオンスーパーセンター」「R.O.U」の直営売場でも利用できるようになり、一方でダイエーとグルメシティの直営売場でイオン商品券の利用が可能となった。 と”少子化による急激な人口減少”により社会保障制度が維持できなくなる可能性が現実味をおびているのです。 『あの–』とお志保は艶のある清(すゞ)しい眸(ひとみ)を輝かした。驚いたやうに引返して行くお志保の後姿を見送つて、軈て省吾を導いて、丑松は本堂の扉(ひらき)を開けて入つた。
thank you nice job.healthcareinsights
怪我人が出だし選手層の薄さから負けが込みだし、最終的には5球団全てに負け越しながらも借金15で5位に終わった。大野豊が42歳で史上最年長の最優秀防御率のタイトルを獲得したものの、順位は3位ながら中日以外の4球団に負け越して貯金は作れず、その後貯金を作ってのAクラス入りは2014年まで達成できなかった。 この大会が、経済面への波及効果も含め、日本と日本人が元気を取り戻す機会となることを、強く期待しています。 10月20日 – 「第11回 大阪まちなみ賞(大阪都市景観建築賞)」に於いて、「毎日放送本社ビル、クラレ・
例えば1巡目 – 10巡目の各巡にそれぞれ1回ずつ指名権を持つ、ぜいたく税対象球団が2人のQO拒否選手とMLBドラフト前に契約した場合、1人目の補償として2巡目および5巡目の指名権をまず失い、更に2人目の補償として3巡目と6巡目の指名権を失う。 レジーは色々世話になっており、娑婆でも影響力を持つ男。 この課題に対処すべく、中学生年代に於いて公式戦出場機会の少ない14歳(中学2年)以下の選手に対し、ハイレベルで拮抗した試合環境を年間を通してコンスタントに与える事で選手としてのレベルアップを図ると共に、アウェイへの遠征経験などを通じて社会性を育てる事を目的として2008年度から創設されたのが本大会である。
“空軍トップら500人裁判=クーデター未遂で最大規模-トルコ”.
“米海軍兵士、海自との共同訓練中に行方不明に 南シナ海”.
“アフガンでシーア派モスク襲撃、33人死亡 ISが犯行声明”.時間になると、『サンダーバード』に使われたカウントダウン(5,4,3,2,1というもの)のサウンドエフェクトが使用され、その後に同番組のバックミュージックとともにナレーターによる説明が行われる。時事通信社 (2017年8月1日).
2017年8月2日閲覧。時事通信社 (2017年7月31日).
2017年7月31日閲覧。時事通信社 (2017年8月2日).
2017年8月4日閲覧。 “タクシン派元首相に無罪判決=08年のデモ流血事件-タイ最高裁”.
thank you nice job.clinicalmedicaljournal
I visit everyday some websites and blogs to read posts, except this web site offers feature based content.
天は遠く濁つて、低いところに集る雲の群ばかり稍(やゝ)仄白(ほのじろ)く、星は隠れて見えない中にも唯一つ姿を顕(あらは)したのがあつた。青白い闇–といふことが言へるものなら、其は斯ういふ月夜の光景(ありさま)であらう。夜の靄(もや)は煙のやうに町々を籠めて、すべて遠く奥深く物寂しく見えたのである。 それにしても、今夜の演説会が奈何(どんな)に町の人々を動すであらうか、今頃はあの先輩の男らしい音声が法福寺の壁に響き渡るであらうか、と斯う想像して、会も終に近くかと思はれる頃、丑松は飲食(のみくひ)したものゝ外に幾干(いくら)かの茶代を置いて斯(こ)の饂飩屋を出た。 ステージなどでの挨拶の際には決めポーズとして、両手の親指と人差し指でL字を作り側頭部で掲げ、同時に舌を出す(画像参照)。
口頭では現示と進行・ メタバース展示会に出展する企業、自社でメタバースビジネスを始める企業などを支援する事業会社も増えています。
“初代やしろ顧問が応援LOCKS!の思い出を語る!”.
“2代目応援部顧問を務めた『よしだ顧問』が応援部に登場!!!!”.
“あしざわ顧問が受験した漢字検定2級の結果発表!!”.
“漢字検定2級合否発表!!”. “”結婚詐欺師”の異名を持つ”あの人”が登場!!!”.
“あしざわ教頭結婚おめでとう!! 人生初! 結婚お祝いスピーチ逆電!”.
その後、2005年(平成17年)の彼らの結婚について非常に喜んだ。
マーケットには例年800社、数千人の映画製作者(プロデューサー)、バイヤー、俳優などが揃い、世界各国から集まる映画配給会社へ新作映画を売り込むプロモーションの場となっている。審査員は著名な映画人や文化人によって構成されている。 「文名」の意味は分からないのに、「。 「且つ」は行為や事柄に対して、別の行為や事柄を付け加えて、「その上」「更に」という意味で使うことも可能です。中部国際空港アクセスの最速達列車で、2008年(平成20年)12月27日のダイヤ改正で新設された種別。
例としては、皇太子明仁親王などの英語教師を務めたヴァイニング夫人の勲三等宝冠章授章がある。保坂 芳男「キリスト教系中等学校の英語教員に関する研究 -立教学院の場合-」『人文・文部科学省ホームページ(認定・
“オバマ氏ツイートに史上最多の「いいね」 白人集会衝突受け投稿”.
“ブルキナファソで武装集団がカフェ襲撃、17人死亡”.
“パキスタンで軍の車両狙った攻撃、15人死亡 IS分派が犯行声明”.
“巨木が倒れ13人死亡 ポルトガル、宗教行事の人混み直撃”.
“洪水死者、400人超える=シエラレオネ”.
“コレラ感染疑い50万人超=イエメン”. “豪雨災害の死者1000人超に=救助難航、拡大の恐れ-印など”.
“土砂崩れで最大で250人死亡の恐れ コンゴ民主共和国”.
thank you nice job.peerreviewedjournal
thank you nice job.esciencejournal
口がないことが採用理由だったが、実際には問題なく喋れ、百目から気持ち悪いと言われたことに憤慨して怒鳴り散らしていた。魔女狩りの犠牲になった無実の少女の肖像画に宿る魂が実体化した悪魔。事業ごみ、消費税ゼロの怪 処理料で10自治体・ しかし、税金で設置された施設が一管理者によって私物化されるのを防ぐという観点からも、下記の項目などを地方公共団体の条例や協定書および仕様書などに盛り込んでいくことが必要となる。
近年の人材獲得競争の厳化や採用活動早期化の実態を調べてみました。 『世界年鑑2024』(共同通信社)386頁。弱いストレッサーによる歪みは、通常ならばストレッサーがなくなれば自然と丸く戻りますが、弱い力でも簡単に風船が破裂してしまう人もいますし、さらに強い力だと戻りきれなかったり、破裂してしまったりすることになります。龍の形の高価な靴も購入したが第1話でしか着用せず、以降は普通のブーツを着用している。宿場ごとに用意されている役人用の馬車に乗って商於(河南省)の境界までやって来た。
をはじめ、減給などの社内処分を実施するほか、再発防止策も10月中にまとめことを明らかにした。公式には長く未発表であったが、1975年に『地下室(ザ・株式会社みずほ銀行 (2021年6月15日).
2020年6月15日閲覧。皆年金の意義と課題」第47巻第3号、国立社会保障・
御交際なさるが好(い)い。 しかし実際無駄遣をしたわけでもありません。 ベンチャー企業への投資の会合で、美雪の兄・ 1992年、中国新技術創業公司(CVIC)との提携により、「北京賓特購買中心(北京八佰半百貨店)」を開業。英では、医療、金融、住宅等のサービス提供者に滞在許可の確認を義務付け、不法滞在者の利用を制限して滞在を困難にすることで自発的帰国を促しています。
彼は朱子学の立場から儒学の基本である修身・東京会場では2月13日~15日、大阪会場では20日~22日に実施。 ▼築地東通りは日本酒、ビール、ワイン、抹茶の飲める店が所々にあって和みます。 1月20日 – 大阪市の駒川店で火災が発生、地下売り場が全焼。 1月 前述の敷地内で、テレビ送信用のタワー(地上高177m)が完成。 ごま油をオリーブオイルに代えると洋風に仕上がります。
I am not certain the place you are getting your info, but good topic.
I needs to spend a while studying much more or working out
more. Thanks for great info I was looking for this information for my mission.
母親も英語の達人であることから、嗣子様も英語力を身につけているでしょう。県内の農林漁業者及び食品製造業者が製造する県産農林水産物を使用した加工食品の魅力を発信するとともに、販路の開拓・
“米政府の個人監視に逆らえないテクノロジー企業”.
Правительство Сахалинской области(サハリン州政府).
河原の砂の上を降り埋めた雪の小山を上つたり下りたりして、軈(やが)て船橋の畔へ出ると、白い両岸の光景(ありさま)が一層広濶(ひろ/″\)と見渡される。雑学からトレンドまで幅広い知識を持つ物知り系サラリーマン。丑松は其広告を読んだばかりで、軈てまた前と同じ方角を指して歩いて行つた。一生のことを思ひ煩(わづら)ひ乍(なが)ら、丑松は船橋の方へ下りて行つた。鈴木勇一郎「立教学院の校友組織と寄附行為」『立教学院史研究』第15巻、立教学院史資料センター、2018年1月、93-114頁。同様に統括店である横浜店ではなく、日銀横浜支店に近いゆうちょ銀行横浜港店と接続されている。
エスカレートさせたりする危険性もあります。法令等の定めにより、当行が介護保険の募集を行う際には、お客様が「銀行等保険募集制限先」に該当されるか否かについて等の確認をさせていただきます。 また、この段階のストーカー行為は警察が介入できるほど事態が深刻化していないことが多いため、ご自身で有効な対策を講じなければストーカー行為が収まらないという点で厄介なパターンです。良識的な感覚を持っている相手の場合には、あなたからこのような連絡が来た段階で、「これまでの自分の行動が相手に迷惑をかけていたのではない」かと内省し、ストーカー行為が終了するという可能性があります。
加えて、業界全体で業務縮小が一斉に行われたために派遣元企業は他への紹介が出来ず、結局のところ派遣元企業も派遣社員に業務をあてがう事が出来ずに契約解除することが広く行われた。毎年5月に行われている鉄道のまち大宮 鉄道ふれあいフェアなどを始めとする車両基地・ SPとして無表情で厨房に立っていたが、「柔道八段」の実力を活かし開かない瓶の蓋を開け、稲毛のデザートの完成に貢献する。水産研究所を改組し、海洋研究所を開設。
だが、人材確保や研修の充実、家族支援などに必要な予算が確保されなければ、実効のある対応は期待できない」(高崎絹子・ 2008年12月にユニマット山丸証券株式会社の事業を一部承継し、2008年12月1日より現在の名称となり、後に村上豊彦が社長に就任したため、一時期役員から創業家がいなくなった。上記の理由から、レバレッジ型、インバース型のETF及びETNは、中長期間的な投資の目的に適合しない場合があります。
“[ドラゴンボールZ]新作劇場版の声優に山寺宏一と森田成一”.
“. 映画『聖闘士星矢 LEGEND of SANCTUARY』. “STAFF&CAST”. 映画『SHORT PEACE』オフィシャルサイト. “『峰不二子という女』から2年–アニメ『LUPIN THE III RD 次元大介の墓標』2014年初夏、新宿バルト9にて期間限定で特別上映! “マスコミの取材マナー悪さ ネットで指摘が相次ぐ”.
ロペとアキラが通う高校の先生。特別約款で定める保険事故が発生した場合に保険金が支払われる。
幼少期はひょうきん者でおちゃらけていたが、成人後は寡黙かつ真面目で誠実な青年に成長する。上品に口許に手を当てそう微笑む卯ノ花隊長。 1944年(昭和19年)2月 – 東京火災海上保険株式会社・
2022年10月17日午前、午前9時半ごろから法人の振り込みや取引明細の照会などを扱う「みずほビジネスWEB」などで不具合が発生し、一部の法人向けのインターネットバンキングにつながりにくくなるシステム障害が起きた。二つの教会をめぐる石の物語 『人物略歴5 ウィリアム・
コロンビア、アンティオキア県メデジン郊外にあるペニョル貯水池(スペイン語版)にて150人を乗せた遊覧船が転覆。 6月26日 – シリア南部マヤディーン(英語版)の刑務所を有志国連合が空爆。 ウクライナ政府機関や銀行、市役所などが標的にされ、被害件数は欧州を含めて2000件に昇った。 メキシコ、ゲレーロ州アカプルコの連邦刑務所で、受刑者グループ同士の抗争から暴動が発生。行動的で、興味を持ったことにはなんにでも首をつっこむ性分。修行の際は鱒之介から、普段の孫煩悩とは一変して厳しい指導を受け、容赦の無い叱咤を受ける(父の旬もその際はみどりが自分で選んだ道だからと敢えて助け船も出さず冷淡な姿勢を取っており、藍子にも決して鱒之介に口出ししないよう釘を刺している)が、決して音を上げず食らい付いている。
thank you nice job.enursingcare
彼様(あゝ)いふ調子で、ずつと今迄進んで来たら、奈何(どんな)にか好からうと思ふんですけれど、少許(すこし)羽振が良くなると直(すぐ)に物に飽きるから困る。同社が中国など数多くの国に進出した結果、設立からわずか6年で、ホテル数で世界第2位に成長しました。
1958年(昭和33年)には当選4回ながら自由民主党政調会長就任。 その理由を、経済ジャーナリストの岩崎博充氏がこう話す。渋沢栄一から学ぶ経済(?
さらに、OYOがヤフーと組んで「レオパレス」を救済するとの報道もあります。 ガーディナー(立教学校初代校長)をはじめ、聖公会神学院の前身の一つである聖教社神学校を設立したアレクサンダー・
“【コラム】諏訪魔、大森隆男、和田京平、木原リングアナ、神林レフェリーの証言で綴る、全日本プロレス『10年目の』東日本大震災”.福田 赳夫(ふくだ たけお、1905年〈明治38年〉1月14日 – 1995年〈平成7年〉7月5日)は、日本の政治家、大蔵官僚。日本放送協会 (2023年3月12日).
“WBC 侍ジャパン 佐々木朗希「何か感じてくれたら」東日本大震災12年 | NHK”.
】第8回「東日本大震災を経験して痛感したこと、『ALL TOGETHER』での内藤哲也、棚橋弘至との遭遇などについて語る!
“エジプト軍がクーデター、大統領を排除 憲法停止宣言”.
“デトロイト市が財政破綻、米地方自治体として過去最大規模”.
“パナマ当局が北朝鮮籍の船舶を拿捕、砂糖のコンテナから武器”.
“キューバ「北で修理」 拿捕船舶から武器、釈明”.行方不明者5700人の死亡宣告=インド北部の豪雨 時事通信 2013年7月15日閲覧。検索結果は、しばしば予備報告を伴う場合があります。
当社は、業務提携する株式会社ビーライズの出展ブース内で、バーチャルイベントを簡単に開催できるプラットフォーム「メタバース展示会メーカー」をはじめ、自治体でのメタバースの活用事例などをご紹介します。自叙伝、身辺雑記、俳句と、その人柄と魅力のつまった構成になっている。演劇、映画、放送、文壇、俳壇、画壇などなど、幅広い交遊関係がうかがえる。日本画、篆刻、俳句、酒と風流な趣味人であった。喜多村緑郎の犬好き、初代水谷八重子のおもちゃのいたずら、大矢市次郎の釣り狂い、フランキー堺の着物道楽、八代目市川中車の腹話術と漫談などなど、俳優仲間の趣味と素顔を軽妙に綴っていく。
身位を官報掲載どおりに記載(括弧内に現在の宮号等を参考付記)。同日付で勲一等宝冠章を受章した。刑部芳則「明治時代の勲章外交儀礼」『明治聖徳記念学会紀要』、明治聖徳記念学会、2017年。外国人叙勲受章者名簿 平成29年 – 外務省、2019年8月18日閲覧。 ご会見(平成28年) – 宮内庁、2019年8月18日閲覧。
水曜劇場 チャンス!水曜劇場 お金がない!金曜ファミリーランド 1億2,500万人のクイズ王決定戦!第7回FNS1億2,500万人のクイズ王決定戦!
オールスター爆笑ものまね紅白歌合戦!車両保険をセットする場合は、免責金額を設定することで保険料をおさえられますが、万が一の事故の際に想定していた補償が受けられない、といった事態を避けるためにもきちんと理解しておきましょう。保険料は所属員が自分で負担する。大学1年生の時にオーディションを受け、ピン芸人として吉本興業へ所属。生さんま
みんなでイイ気持ち!
安堵するも、山田にとってその小麦粉がいかに大切な物であったかを智司に諭され、猛省する。 そのことで他校との決闘に参加するも、同年代の生徒が敗れるのを見て恐れをなして逃げ出す。
その時は「二度と仲間を裏切らぬようケジメをつけさせる」と伊藤を気追す。直後、駆けつけた山田と仲間に刺されそうになるも、三橋が「コイツもタコ焼きを作りたかったんだ」と庇ったことに口裏を合わせ和解した。三橋を卑怯者呼ばわりしたことにキレた伊藤に一撃で敗れる。 それを見て激怒した伊藤が番長兄弟を倒したため事なきを得たが、伊藤の気迫に驚愕し距離を置くようになる。
今でも築地市場の場外で営業するお店からしたら、正確には、移転したのは、場内市場の方であり、築地場外市場は今でも残っていると言う人は多いかもしれません。 たゞ一際(ひときは)目立つて此窓から望まれるものと言へば、現に丑松が奉職して居る其小学校の白く塗つた建築物(たてもの)であつた。丑松が転宿(やどがへ)を思ひ立つたのは、実は甚だ不快に感ずることが今の下宿に起つたからで、尤(もつと)も賄(まかなひ)でも安くなければ、誰も斯様(こん)な部屋に満足するものは無からう。野々下加津も第9シリーズ以降は以前と比べると口数が少なくなり影が薄くなっていて、第10シリーズは事実上レギュラー降板しイレギュラーの形での登場となった。
高円宮承子さまはいくつかの大学に在学、留学をしていますが男性との出会いがあるのは3箇所。旧皇族や旧華族階級でない、いわゆる平民家庭出身の母親であった皇太子妃美智子の意向に沿い、懐妊に際しては母子手帳が発行され、皇居宮殿内の御産殿での出産をせず一般家庭と同様に病院で行うなど、それまでの皇室の慣例によらない、戦後初の内廷皇族の親王(皇孫、皇太子の長男としてほぼ確実に将来において天皇に即位することが確定している男性皇族)誕生は、広く国民に注目された。
I was wondering if you ever considered changing the page layout
of your blog? Its very well written; I love what youve got to say.
But maybe you could a little more in the way of content so people could connect with it better.
Youve got an awful lot of text for only having one or 2 pictures.
Maybe you could space it out better?
“リーグ優勝9回にちなんで9つの赤を採用 アパホテルがカープロードに『広島駅前スタジアム口』を開業 新たに駅前の老舗ホテル取得も明らかに【広島・新スタジオ及びマスターの運用開始は1週間後の12月31日からで、それまでは従来の旧本社(2013年12月23日まで)からの放送であり、旧本社最終番組は12月30日 22:30 – 24:00に生放送された「さようなら日本自転車会館スペシャル」(司会:中野雷太・
職人気質一本気な伴とは対照的に、社会人として不慣れな新人たちに酒を驕ったり風俗につれて行くことで懐柔し、パスタ場に反バンビ派閥らしきもの形成するほど世間慣れしている一面もある。但馬銀行は、募集代理店として契約の媒介を行いますが、契約の相手方は引受生命保険会社となります。補償割合は70%となっており、年間補償限度額は30万円となります。 プラチナプランの中でも都合に合わせてさらに3つのプランから補償割合を選ぶことが可能となっています。手術をトータルでカバーしてくれるプランとなっているため、充実した補償内容となっています。
パールプランは高額になりがちな手術のみを補償することで、月々140円〜という安価な保険料に抑えることができるプランとなっています。
銀之助が友達を尋(さが)して歩いた時は、職員室から廊下、廊下から応接室、小使部屋、昇降口まで来て見ても、もう何処にも丑松の姿は見えなかつたのである。乃木坂46運営委員会.
ひたすら登り切り、やっと水越峠の下り坂へ、今わしは酒をやめる為に四條畷断酒会、出席するぞとママチャリ走らせ、地図の上でしか見たこともない「有田川」を今、渡っている。斯うして車の後に随(つ)いて、とぼ/\と二三町も歩いて来たかと思はれる頃、今迄の下宿の方を一寸振返つて見た時は、思はずホツと深い溜息を吐(つ)いた。悉皆(すつかり)下宿の払ひを済まし、車さへ来れば直に出掛けられるばかりに用意して、さて巻煙草に火を点けた時は、言ふに言はれぬ愉快を感ずるのであつた。
父親と浜茶屋「海が好き」を営んでいたが、その浜茶屋が壊れてしまったため、再建費用を稼ぐために親子で友引高校の購買部で働くようになる。旧興銀の業務を引き継ぎ、旧興銀店舗またはその承継店舗では、金融債の「割引みずほ銀行債券(ワリコー)」「割引みずほ銀行債券保護預り専用(ワリコーアルファ)」「利付みずほ銀行債券(リッキー)」「利付みずほ銀行債券利子一括払(リッキーワイド)」を発売していたが、2007年(平成19年)3月後半債(3月27日)で発行を終了した。医療保険においては病気のリスクの少ない若年層のオッズは高いが、年配者の場合はオッズは低く、逆に自動車保険においては事故率の高い若年層の方がオッズは低くなる。
介護保険制度は、国民の老後生活を支える重要な制度のひとつです。同月2日、非合法極左組織「革命的人民解放党・ ※年齢、免許取得年数により加入に制限がある場合がございます。総合化学調味料「いの一番」を発売。 「情報ファイル ダイエーがLP発売」『朝日新聞』1973年12月6日付東京朝刊、6面。
スケレシュースキー(英語版)が聖ヨハネ書院として設立した中国初の高等教育機関で、東方のハーバード大学と呼ばれた。
ニューマン氏と同氏の不動産新興企業フローの担当弁護士は書簡で、ウィーワークから十分な情報が得られないため、買収案を策定する取り組みが滞っているとして不満を示した。内閣総理大臣 安倍晋三『内閣衆質一九〇第一二九号 衆議院議員大串博志君提出諸外国における一階部分の年金積立金の運用状況に関する質問に対する答弁書』(プレスリリース)衆議院、2016年2月23日。第3女子 –
絢子女王〈あやこ〉(1990年〈平成2年〉9月15日 – )- 日本郵船社員(NPO法人国境なき子どもたち理事)・
“いぎなり東北産 ツーマンライブ「いぎなり東北産(様)×桜エビ~ず 仲良くなんてできないよ! “桜エビ~ず ツーマンライブ「いぎなり東北産(様)×桜エビ~ず 仲良くなんてできないよ! “仲良くなんてできないよ!桜エビ~ず×いぎなり東北産、3度目の熱戦の行方は”.
“エビ中、クラスメイト総勢135人で作り上げた4年目の「秋田分校」”.
“いぎなり東北産 私立恵比寿中学秋田分校に出演! ストーリーモード以外に「コロシアム戦」やストーリーモード内の「フリーバトル」などの1人で楽しめるモードに加えて、DSワイヤレス通信で他のプレイヤーと対戦できる「通信対戦」、ベイブレードのゲーム作品では初となるネットワークによる対戦が収録されたニンテンドーWi-Fiコネクションに接続して世界中のプレイヤーと対戦できる「Wi-Fi対戦」がある。現在、展示会への出展者を募集中です。
ある猟師によると、その日本人はとんど裸の状態で、罠にかかったシカを一心不乱に食らったそう。植えたトウモロコシは疾病で実がなっておらず、食糧が逼迫した状態になってしまったため、ウィリアムはケイレブの手を借りようとしたのです。音声配信以外にも、ホームページのブログ化に精力的に取り組んでおり、各番組ごとのブログは勿論の事、特別番組(外国の競馬実況特別番組ほか)ブログや、制作スタッフの単独ブログ(インターネット担当者webmasterブログ、大阪支社アジア番組担当営業マンブログ、競馬番組担当者によるワールドカップ中継PRブログを引き継いでの日本サッカーウォッチブログ)なども、公開されている。
十世坂東三津五郎”.月刊演劇界増刊号|平成元年/1989年11月30日初版発行『歌舞伎俳優名鑑』P.123 坂東三津五郎家の家系図:八世三津五郎の長女 守田喜(のぶ)子 (昭7・7・22生)と記載あり。
その年をもって家事のコーナーは廃止され、2003年度からはほぼ料理全般の番組となった。 どきドキキッチン』と改め、初めて番組名にサブタイトルが付けられた。番組は放送開始当初のほぼ料理のみの内容のスタイルに戻し、各地の幼稚園を回って行われるクッキングクイズコーナー「クックのはてな? わんパーク』に2度ゲスト出演し、番組MCの平田実音(ミーオ)と共演した。本番組でのネタやパロディが何度か使用された。 2002年度から番組タイトルが『ひとりでできるもん!伊倉は後に2004年から同じ教育テレビの『天才てれびくん』でてれび戦士として2006年度まで3年間出演。車両の荷台には、銃を持った兵士や、同じくスマートフォンで撮影している兵士も映っていた。
また、それまでのシリーズでは1年ごとにオープニング映像が一新していたが、このシリーズから2年間同じオープニング映像に統一された(次のシリーズも同様)。
1984年(生物科学) – ダニエル・ 1988年(数学) – ピエール・ 1994年(数学) – サイモン・ 1982年(数学) – ウラジーミル・中央競馬実況中継は、前述の携帯向けライブ配信のほかに、実況部分のみを、パソコン向けにも、有料で配信している(外部リンクを参照)。
晩年の乃木は学習院院長を務め、少年時代の迪宮裕仁親王(のちの昭和天皇)にも影響を与えた。当初は辞退やむなしの意向だった久邇宮家は態度を硬化させ、最終的には裕仁親王本人の意思が尊重され、1921年(大正10年)2月10日に宮内省から「婚約に変更なし」と発表された。文頭は「今回本紙は、○○(テレビ番組)の司会を務めた、上田晋也の動きに注目した。本庄繁に「美濃部説の通りではないか。 1935年(昭和10年)、美濃部達吉の憲法学説である天皇機関説が政治問題化した天皇機関説事件について、時の当事者たる昭和天皇自身は侍従武官長・
“Meta、経済産業省、バーチャルライツがメタバースに求められる新しいルールの在り方についてパネルディスカッションを実施”.
“NPO法人バーチャルライツ – 国際連合経済社会局iCSOに登録承認されました”.
“地方創生SDGs官民連携プラットフォームに「メタバース分科会」を設置”.指定管理者は、毎年度終了後、その管理する公の施設の管理の業務に関し事業報告書を作成し、当該公の施設を設置する普通地方公共団体に提出しなければならない。 “NPO法人バーチャルライツさんと意見交換をしました – 参議院議員 山田太郎 公式webサイト”.
“NPO法人バーチャルライツ、メタバース振興に向け国会議員へ提言”.
第1シリーズと同じく放送期間が4月から6月まで(ただし第1シリーズは放送期間が4月から7月上旬までとなった)となり、そのため物語は第1シリーズと同じく1学期開始当初からスタートし、そして1学期終了直前の所で最終回を迎えて一旦終了した。大手損保は2015年、火災保険の最長契約期間を住宅ローンの期間にあわせた36年から10年に縮めていた。他の作品ではレイの攻撃はほとんどが拳銃によるものだが、本作では銃の他、徒手や鉄パイプなどを巧みに使い戦うシーンがある。 その頃一番辛くて恥ずかしかったのは買い物に行って精算をする時に、手が震えて小銭を財布から出す事ができなかった事や、買い物した袋だけを持って店に財布を置いてくる始末でした。
7月 – 官民競争入札等監理委員会委員に就任。民主友愛太陽国民連合・残業自体はほとんどありませんが、お客様の都合によっては残業もあります。 」と告白し、様々な人種と肉体関係を持ち続けている現在が明らかになっている。転勤の頻度も恐ろしく早いので担当顧客との信頼関係を作る暇も無し。平日は早朝から夜中まで顧客の迷惑考えず電話攻撃。
免責金額を設定している場合、支払われる保険金は以下の通りです。免責(事由)とは、保険金が支払われない条件を示すものです。 お客さまの中には「免責(事由)」と「免責金額」を同じものと考えている人がいます。 あなたの火災保険の免責金額は5万円としましょう。火災保険に加入する際や保険金を請求する際は免責事由をよく理解し、不正行為に加担しないよう注意しましょう。 これは詐欺行為であり、損害保険協会や国民生活センターはこのような業者の提案に注意するよう呼びかけています。
2014年(平成26年)5月27日午前、出雲大社禰宜(当時)の千家国麿との婚約が内定したと宮内庁の西ヶ廣渉宮務主管が記者会見で発表。靴磨きをしていたすずを見かけ、学校に行く時間だと声を掛けるが泣き真似をされ悪者扱いを受ける。 2006年には、新座キャンパスに現代心理学部・ ユンによると、士官学校時代から持っているらしい。 「前近代の「御料車」-牛車と鳳輦・
I always used to read paragraph in news papers but now as I
am a user of web so from now I am using net for articles or reviews,
thanks to web.
“地震被害対策本部を設置しました”.太平洋沖震災対策本部」を設置。 “東北地方太平洋沖地震対策本部設置”.
“. 穀田恵二 (2011年3月11日). 2015年3月21日閲覧。上田に滑舌の悪さをイジられた。 “【党首声明】東北地方太平洋地震で被災された皆さまとすべての国民の皆さま”. “東北地方太平洋沖地震による災害への救援を訴えます”. “日本共産党は、志位和夫委員長を本部長とする「東北地方・
時事通信社 (2017年7月5日). 2017年7月7日閲覧。
CNN (2017年7月1日). 2017年7月8日閲覧。 AFPBB NEWS (2017年7月1日).
2017年7月4日閲覧。時事通信社 (2017年6月30日).
2017年7月4日閲覧。 AFPBB NEWS. 30 June 2017.
2017年6月30日閲覧。 29 June 2017. 2017年6月29日閲覧。時事通信社 (2017年7月4日).
2017年7月7日閲覧。時事通信社 (2017年7月3日).
2017年7月4日閲覧。 ジャワ島”. AFPBB NEWS (2017年7月3日). 2017年7月4日閲覧。 AFPBB NEWS (2017年7月3日). 2017年7月4日閲覧。
これによると、38社の不払い合計は、件数にして131万件、金額にして964億円に達し、同年4月の中間調査結果と比較しておよそ3倍に膨れ上がった格好となった。千家典子さまの名前は、父である高円宮憲仁親王によって命名されました。 『荻原博子の家計簿クリニック ムダを省いてお金を浮かす』扶桑社(Odaiba!
このため、2007年2月1日に金融庁が日本の全生命保険会社(38社)に対して、2001年~2005年の過去5年間に行われた保険金不払いの件数や不払い合計金額を調査し、2007年4月13日までにその調査結果を報告するように命令した。
5月12日 – 横浜住吉町四丁目店(横浜市)の店内に「千葉県アンテナショップ」開店。玉を中住まいにして自陣左右に金を開くように配置した陣形。 2月29日 –
KDDIとWi-Fiスポットの構築を中心とする業務提携を締結。黒毛和牛を甘めの割り下で煮込んだ「別格」の三種類の牛皿がメニューの中心だった。千家典子さまが東京に頻繁に足を運ばれるとしても、それが夫婦間の不和を意味するものではありません。 ポプラ米子西河崎店」「ローソン・
スリーエフ」に転換するとともに、スリーエフから当該店舗の資産・
女性セブン2011年4月14日号『天皇皇后両陛下、「国民と共に」と拒まれた特別室 -食事も一汁一菜に-』。産経新聞2011年4月29日記事によると、「防犯や防災など安全に関わる部分の電源」「天皇・株式会社ヤマトヤシキ”と表記されており創業の地である姫路市を強く意識していることが窺える。筆頭株主が三菱商事に移ってから、間もなく募集が停止された。日本民間放送連盟賞/2011年(平成23年)テレビ教養番組・
天童の親方の一人息子で、みどりの同級生(クラスは別)。 その後、姉の能力の芽生えと共に魔女狩りに遭っていたところをマグニートーに助けられ、姉と共に「ブラザーフッド・運輸関連などが上昇した一方、電気・ なんだか前途の幸運が予想せられる。 1939年(昭和14年)9月1日 –
1902年(明治35年)3月に設立され、現在の瀬戸線を当時運営していた瀬戸電気鉄道を合併。
株式会社岩手ホテルアンドリゾート – 2003年3月加森観光に全株式を譲渡。乃木坂46公式サイト
(2018年9月20日). 2024年2月15日閲覧。 2012年 阿部佳乃(
– 2014年、佐渡テレビジョン出身、→フリー、現・浩歌は一部のメディアと視聴者の反応に納得がいかず「この二人、この騒動を気に有名になったんですよ。 わたしのこの爪は達者ですからね。、若い世代からその世代間不公平について寄せられる批判も多い。 わたし達の仲間にいて、好い気持はしないわ。
早くに両親を亡くし家族が欲しいという思いから、その女の子を家族とみなし、結婚の約束をしたが後に転校してしまい、今ではどこにいるのかもわからなくなっている。 とくに年度初めの4月号は出版社、ラジオ受信機、電子辞書、語学学校の広告で他の月より一際分厚い。 ルドニークの街で助けられてからくまゆるとくまきゅうがお気に入りだが、そのことを恥ずかしがっていて、自分ではそうと認めていない。 ユナの実力を認めており、自分よりも強いとはっきり公言している。 クリモニアや王都、デゼルトなど、様々な土地で活動している。 1996年(平成8年)6月3日に火山活動の終息が宣言され、それ以降は現在まで復興へ向けた取り組みが続けられている。
『今回のことは、教育者に取りましても此上もない名誉な次第で、非常に私も嬉敷(うれしく)思つては居るのですが–考へて見ますと、是ぞと言つて功績のあつた私ではなし、実は斯ういふ金牌なぞを頂戴して、反(かへ)つて身の不肖を恥づるやうな次第で。是主義で押通して来たのが遂に成功して–まあすくなくとも校長の心地(こゝろもち)だけには成功して、功績表彰の文字を彫刻した名誉の金牌(きんぱい)を授与されたのである。
ただし、保険契約者又は被保険者の詐欺又は強迫を理由として損害保険契約に係る意思表示を取り消した場合や、生命保険契約が遡及保険により無効とされる場合は、保険料返還義務を負わない(保険法第64条)。
第5話で登場した沙織に付きまとっていたストーカー。第二の鷙鳥(一層濁れる声にて。第一の鷙鳥(濁れる小声にて。 この土地に慣れるのは、大ぶやさしそうだぞ。訪日中の米国大統領ドナルド・ この年の大統領選挙では民主党のジョー・ 26日、大阪城ホール)、東京(30日・
丑松が汽車から下りた時、高柳も矢張同じやうに下りた。 』と見ると、高柳は素早く埒(らち)を通り抜けて、引隠れる場処を欲しいと言つたやうな具合に、旅人の群に交つたのである。 (現在の都立千早高校の場所)。女子系の12の公私立大学はひと足先に48年),さらにこの年に大学に入学した者が卒業する53年に大学院がそれぞれ発足したのである。学生時代は応援団だった。権勢と奢侈とで饑(う)ゑたやうな其姿の中には、何処(どこ)となく斯(か)う沈んだところもあつて、時々盗むやうに是方(こちら)を振返つて見た。
民営化前を含むそれ以前の加入通知では、全銀システム用の口座番号はもとより、カナ表記がなされていなかったが、全銀システムの関係上、カナ表記を割り当てる必要があったため、サービス開始前に全銀システム用の口座番号が圧着ハガキで通知されることになった際、カナ表記も通知され、特に法人名に関しては、表記変更が必要か否か(「カフ゛シキカ゛イシヤ」を「カ)」などの略称標記にする必要があるかなどを含む)の確認(変更の場合は、要届出となった)も要請されていた。放映され、全38話の映像が現存している。 1968年には映画としても製作されているが、主役の池内淳子と山岡久乃と長山藍子の3人は共通して同一のキャスティングで出演している。
しかし燃費性能は非常に悪く、装甲内部に増設された大型推進剤タンクを用いても稼働時間は短い。 『アニメージュNEXT
2013 winter』徳間書店〈ロマンアルバム〉、2012年12月、pp4-37頁。青い目の少年兵 -知られざる日中戦争の物語- (2011年8月13日/19日、NHK
BSプレミアム、構成・今年の夏、エンジニアのスペシャリストとして、またはゼネラリストとして、活躍したいと考えている学生に ドリコムの技術力や発明を産み出す発想力をお伝えするインターンを実施いたします。
リアスカートは取り外して手持ちのシールドにすることで、改修前と同様の高い防御力を発揮する。
楽天投信投資顧問がレバETFをつくるとこうなりました。楽天ETF-日経レバレッジ指数連動型は、日経平均株価の変動率の2倍の値動きになる指数である「日経平均レバレッジ・日経平均株価2倍連動を実現するため、ファンドでは日経平均株価の株価指数先物取引を活用し、その買建て総額が純資産総額の約2倍程度となるよう日々、調整を行います。
“. プレスリリース・ニュースリリース配信シェアNo.1|PR TIMES. “病院看護師バブルがやってくる
11年後に14万人 だぶつきの衝撃”.毎日放送が謝罪”.
2023年:『ラジオと戦争 放送人たちの「報国」』(大森淳郎・本作品における敵怪人の一種。、利用者は照準を合わせた後はトリガーを引く以外に特別な操作を必要としない。霜月が提案した同時に複数人を執行可能なショットガンタイプのドミネーターの試作品で、強襲型と同様に大型。
イラク、クルド人自治区の中心都市・絵の中に相手の魂を封じ込める仙術を使う。高校野球100回目の夏 広島中、アカシアに笑う – 中国新聞アルファ (Internet Archive)『スポーツ人國記』ポプラ社、1934年、68-71頁。 1944 4月 電波科学専門学校を東京都中野区江古田に開校。社会人野球日本選手権大会・ そして2009年(平成21年)には、第45回衆議院議員総選挙で民主党が大勝して自由民主党が野党に転落して、民社国連立政権の鳩山由紀夫内閣が誕生し政権交代が起きた。
そして続けざま、けたたましいサイレンが街中に響き渡ります。性格はおおらかで、やや天然ボケなところもあり、自身の恋愛には若干疎いが、三姉妹の中では最もモテており、中学時代に多数の男子をふったことがあり、現在でもマコト、保坂に好意を寄せられ、ナツキからも異性として意識されている。現在のシンボルマークは会社創立100周年に先立つ1992年(平成4年)4月より使用を開始している。 1936年(昭和11年)から1938年(昭和13年)にリーグ3連覇、1956年(昭和31年)、1958年(昭和33年)にリーグ優勝したほか、1948年(昭和23年)と1949年(昭和24年)に開催された東京八大学アイスホッケーでも2年連続で優勝している。
※保険金をお支払いする事故が発生した場合でも、損害額が免責金額以下であったときには、損害保険金をお支払いできません。以下は中でも特色ある店舗である。島原半島の中心都市であり、島原城や武家屋敷など旧城下町の街並みが残る。免責金額と免責事項は、似て非なる概念であり、両者の役割は異なります。一方、免責事項は、保険金が支払われない特定の状況や条件のことです。
集英社『週刊少年ジャンプ』公式サイト. “【特集】海外でも人気! “コロナ禍で「ドーナツ」が人気 ブーム再燃 韓国からも”最新”ドーナツが… “. NIKKEI STYLE. 日本経済新聞社・既存の利用者が通帳レスを希望する場合は、ゆうちょダイレクト上で手続きができる(この場合は、新たな自動貸付や当座貸越は不可となるが、すでに存在する自動貸付や当座貸越を切り替えにあたって解消する必要はない)。 「外部目線が不可欠と考えている」”.
そもそも「子孫世代に金もケアもツケ送りして面倒みてもらう」世代間扶助による社会保障制度は、少子化によりもはや破綻し持続可能性が無い、「痛みある社会保障改革」するしかない。
機種はファミリーコンピュータ。メーカーはバンダイ。ジャンルはRPG。保存方法はパスワード制(平仮名61文字(清音・機嫌が良い場合は戦闘中に呼び出さなくても駆けつけるなど悪魔くんに協力的であるが、機嫌の悪い時には悪魔くんの命令を聞かず何もしなかったり、勝手に帰ってしまったりする。使徒は自動で戦ってくれるが、悪魔くんが行動を命令することもできる。 また、使える魔法の種類が、悪魔くんが命令した場合と使徒に行動を任せた場合で異なる。
総合テレビの国会中継や臨時ニュースなどやむを得ない事情で放送できなくなったスポーツ中継をEテレに迂回した際に、Eテレで所定時間に放送できなかった定時番組の振り替え放送であったり、さらに不定期で特集編成による延長も行われる場合もある。社会保障税は労役所得にのみ課税されるので、株や不動産の売買益や利子・ 『読む野球-9回勝負-総集編』主婦の友社、2013年、145頁。佐野正幸『1979年日本シリーズ近鉄vs広島 もうひとつの「江夏の21球」』主婦の友社、2009年、61-63頁。
処理できない量の訴訟を起こしてしまえば、自動的に賠償金が認められてしまうというルールなのです。大手レンタカー会社の場合、必ず基本料金(レンタカーご利用料金)に、自動車損害保険、自動車損害賠償責任保険という基本的な保険が含まれています。 もしレンタカーで事故を起こしてしまい、車や人に損害を与えてしまっても、その賠償額は保険会社から支払われます。 レンタカー保険補償・
この営業補償料を支払うことを「NOC(ノンオペレーションチャージ):休業補償」といいます。 「肉屋を応援する豚」という言葉が2020年から2021年のマイブームで、残業代を支払わない企業や、年金資金が足りない日本政府などが肉屋の例であり、本来は「お金をくれ」と言うべき立場の人が、「まあ、みんな大変だよね」と聞き分けをよくして許してしまっていることについて「聞き分けのいい豚になっていないか?
I was suggested this blog by means of my cousin. I’m no longer positive whether this publish is written by him
as nobody else understand such distinct approximately my trouble.
You’re incredible! Thank you!
保険料は、等級が小さくなるにつれ、高くなります。 ※地震保険に関する法律施行令の改正(平成29年1月1日施行)により、「半損」が「大半損」および「小半損」に分割されています。平均寿命67.5歳のロシア男性は2年半しか年金受給されない!
その後も度々「承子さまはメガバンク勤務の男性と順調」と報じられており、お二人の交際は10年程になるようです。 ポップアップやスクリーン表示といったマーケティング要素はもとより、実際の商品と相違感がないようメタバース上で再現するには時間がかかってしまいます。 ここでは実際にインターンに参加する前に、まずやるべき2つの事前準備を紹介します。
“団体概要”. データに基づく議論が必要でしょう。 “彬子さま、日英協会名誉総裁に:時事ドットコム”.
2013年9月28日、渋谷公会堂にて一年越しのライブを行った。第2次安倍内閣はアベノミクスを掲げ、政策の一環としてデフレ脱却のための金融緩和、公共事業による減災・中小企業者のために火災共済およびその他の共済事業を運営する各都道府県の共済協同組合(神奈川県、広島県など一部の県を除く。
介護報酬が今年4月から9年ぶりに引き下げられ、2015年1~10月の「老人福祉・ イオングローバルSCM株式会社 – 2007年5月21日設立、同年8月21日付でイオン本社からの事業譲渡にて事業開始。 2019年12月、事業立上に向けた準備会社として設立。常に携帯しているラグビーボールから、3話の球技大会において久美子にラガーマンと勘違いされた。披露する時は、大概プレゼンや怪談を披露する際だが、本筋を離れて披露し、総統等に目的と違うと、突っ込まれる。
そこで己の精神は自力の限量以上の事を敢てしたい。 そこで己は心中で急に段々の計画を立てる。 ただし五味も認める通り『十訓抄』の編者同様に行光もその古事を知っていたのかも知れず断定は出来ない。 それは出来る事だ。検束のない四大の、目的のない威力だ。息張って為遂(しと)げた目的から退いて行く。 これは醸造酒としては稀に見る高いアルコール度数であり、日本酒ならではの特異な方法で、世界に誇れる技術的遺産といえる。 1巻だけ出た単行本は再版や電子書籍化がされずに長年入手困難な状況にあったが、2020年より単行本2巻分を一冊にまとめた新装版として刊行が開始された『江戸前の旬DELUXE』の1巻に、『江戸前の旬』本編の第1巻とカップリングで収録され、電子書籍化もされている。
「競走時間帯の拡大」期間の営業体制(7月27日(土曜)から8月4日(日曜)) – JRA新潟競馬場(2024年7月1日・ アルバム(月組公演、1959年2月1日 – 2月26日、宝塚大劇場、演出:白井鐵造(両作品担当)、脚本:菅沼・
2011年にはWHO推奨の国際的なネットワークであるHPH(Health Promoting
Hospital:健康増進活動拠点病院)に加盟し、健康の社会的決定因子に目を向け、地域や職域の健康増進にも力を尽くしている。東葛病院.
2016年5月からは流山セントラルパーク駅前の新病棟に移設した。
または流山駅より徒歩約15分。抗がん剤治療と緩和療法が専門の医師押川勝太郎は、丸山ワクチンをはじめとする代替補完医療選択の結果、ステージⅢまでの乳がん、前立腺がん、肺がん、大腸がんの患者の生存曲線は、84ヶ月後で「代替補完医療なし=約83%」「代替補完医療を選択=約70%」と死亡リスクは約2倍(ステージⅡでは2.7倍、Ⅲでは8倍、乳がんでは8倍、肺がんで53倍、大腸がんで5.9倍)の大差がついているとしている。
鎌田伸一 – 2001年(平成13年)入社。一方で、保険会社側も、保険金支払いに際しては経緯や死因等を充分に調査せず、安易に死亡保険金支払いに応じていたことも判明している。 2001年、『ラジオ日本競馬実況中継』のスタッフ補充に応じるため退社してフリー転向。山本郁 – 2001年(平成13年)新潟テレビ21より移籍。和島英樹 – 2000年(平成12年)株式新聞より移籍。
2017年5月8日閲覧。 2016年12月22日閲覧。 ジェネレーションXの解散後は、紆余曲折を経てX-MENメンバーとなり、戦いの中で新たに身体を強固な生体ダイヤモンドに変える能力を発現。互いに正体を隠して暮らす仮初め家族に世界の平和が託された。髙橋海人と大和田南那の馴れ初めは?厚生労働省の「アルコール健康障害対策推進基本計画(令和3年3月)」 によると、平成30年の「成人飲酒行動に関する全国調査」で、アルコール依存症の生涯経験者が54万人を超えるとの報告が挙がったとされている。日動火災と合併を目指すとしたが、親密先の第一勧業銀行・
東京地検は、2008年、50万円の損害賠償を命じた。
2006年、掲示板で「狂人」などと中傷された北海道の大学助教授、有道出人は札幌地裁支部で書込の削除と220万円の賠償を命じる判決を勝ち取った。栃木県内の中学校で数学科を担当する教師は、自身を誹謗中傷する記事について掲示板の管理者であるひろゆきに削除依頼を行ったものの、削除対象を完全には削除できなかったことに関して、原告が記事の削除を求めているのに被告がこれを怠っているとして、慰謝料等の支払い、記事の削除及び記事を記載した発信者情報の開示を求めた。
流石(さすが)に先輩の生涯(しやうがい)は男らしい生涯であつた。 と想像して、さあ何と文句を書いてやつて可(いゝ)か解らない位であつた。 それから彼(あ)の細君が一緒に東京へ帰つて呉れと言出した時に、先輩は叱つたり厲(はげま)したりして、丁度生木(なまき)を割(さ)くやうに送り返したことを思出した。 それにしても斯(この)電報を受取る時の細君の心地(こゝろもち)は。 『高柳の話なぞを聞かなければ格別、聞いて、知つて、黙つて帰るといふことは、新平民として余り意気地(いくぢ)が無さ過ぎるからねえ』と言つたことを思出した。 “地域支援機構、熊本地震で再生・復興へ2ファンド”.
古代魔法界の英雄と呼ばれており、自分の魔法で一万年後に悪魔くんが現れることも予知していた。 ミイラとして現代まで保存されていた、一万年前のエジプトの王。 2万年前に月から地球に来た月人最後の生き残り。 ツタンガーメンに操られて遊園地に現れ、人々を固めて巨大ピラミッドに変えてしまった。 33話で東嶽大帝が白悪魔や過去の失敗者を狩り始めたため狙われる身となり、黒小人やチビコウモリたちと魔界の僻地に身を隠していたが、気球魔人とピラドクロに騙されて利用された後に捕まってしまう。 「アパラチャノモゲータ」の呪文と共に子供を操る霊波を放ち、情報屋と数人の子供をさらっていた。
昨年6月の首脳会談において一致した戦略対話の強化に引き続き努め、日米安保体制の信頼性を向上させるとともに、両国の持続可能な経済成長を図るため「成長のための日米経済パートナーシップ」を通じた建設的な対話を行ってまいります。 ジャパン、*イトーヨーカ堂、森永製菓、*三菱化学、*UFJホールディングス、*第一製薬、*三共 *アステラス製薬、中外製薬、ヤフー、三井化学、*セブン&アイ・
赤井邦彦 編『鈴木亜久里の冒険』山海堂、2007年、57頁。赤井邦彦 編『鈴木亜久里の冒険』山海堂、2007年、39-40頁。赤井邦彦 編『鈴木亜久里の冒険』山海堂、2007年、44頁。赤井邦彦 編『鈴木亜久里の冒険』山海堂 、2007年、59頁。一方、私どもの全国大会が今年5月24日から26日の3日間神戸であり、その2日目の5月25日、代表者会議において、介護保険制度についての記事がちょうど前日の朝日新聞に掲載されたので、急きょ議題として取り上げられました。
保有する指名権のうち、2番目および5番目に高い全体順位の指名権。保有する指名権のうち、2番目に高い指名権。有田川柳・吉田平 琉球ゴールデンキングス りゅうせきクラブ(クラブ) チームから契約満了となったためで、事実上の解雇である。 この法でいう〈法律〉とは,同日に公布された学校教育法であり,この法は,教育の機会均等,普通教育の向上と男女差別撤廃,学制の単純化,学術文化の進展という見地から,学校制度を改革し,6・
丑松は提灯(ちやうちん)を吹消して、叔父と一緒に小屋の戸を開けて入つた。軈(やが)て復(ま)た読経(どきやう)が始まる、木魚の音が起る、追懐の雑談は無邪気な笑声に交つて、物食ふ音と一緒になつて、哀しくもあり、騒がしくもあり、人々に妨げられて丑松は旅の疲労(つかれ)を休めることも出来なかつた。楽天ETF-日経レバレッジ指数連動型 | 投資信託・読経も一きりになつた頃、僧の注意で、年老いた牧夫の見納めの為に、かはる/″\棺の前に立つた。
必死に追いかけるアキナですが、男性を見失ってしまいます。道中、「コノ先日本国憲法通用セズ」と書かれた看板を見つけますが、構わず明菜は進み、悠真もそれに続きました。途中、有里は自分のスマホに来たメッセージに気を取られ目を離しますが、夏美は”なにか”を観てしまった様子。中遠鉄道・ しばらく歩いていると、獣道にもなっていない斜面を1人の男性が歩いていることに気づきます。旗艦店としてその役目を終える。証券などの代理店販売業務を行うことが認められ、銀行という身近なお金の相談をする場所が生命保険を販売することのモラルリスクの観点からも慎重に行われなければならないとの判断から段階的に解禁された。
大晦日(12月31日)・ 3月31日 – それまでのNET系列局から、開局以来からの念願であったTBS系列局へネットチェンジ。信用取引を行なうにあたっては、売買代金の30%以上で、かつ30万円以上の委託保証金が事前に必要です。信用取引は、少額の委託保証金で多額の取引を行なうことができることから、損失の額が差し入れた委託保証金の額を上回るおそれがあります。今回開始する「日株積立」は、国内株式をあらかじめ設定した日に自動で積立購入するサービスです。最低設定単位はそれぞれ1,
000円から、または1株からで、値がさ株や好配当利回り株も少額から設定することができます。
Glassdoor, Inc. – 口コミ情報を掲載する求人情報検索サイト『Glassdoor』の運営。 Indeed, Inc.
– アグリゲート型求人情報専門検索エンジンサイト『Indeed』の運営。
4月 – 株式会社リクルートマーケティングパートナーズが運営する、保育園と保護者をつなぐコミュニケーションサービス「キッズリー」および幼稚園・ 4月 – 峰岸真澄代表取締役社長兼CEOが代表取締役会長兼取締役会議長に、出木場久征取締役副社長執行役員兼COOが代表取締役社長兼CEOに就任。
株式会社クボタが2022年6月14日~8月31日まで開催したメタバース展示会です。 ファイナンシャルとソニーが合弁会社でソニー・
3月7日 – ブランドン・ 3月7日 – マチュー・
3月4日 – ザク・ 3月1日 – ボシュコ・ 3月1日 – パトリック・ 3月8日 – サーシャ・ 3月8日 – ノラ=ジェーン・
9月8日、那須御用邸から帰京する際に、原宿駅側部乗降場(皇室専用ホーム)ほかで映されたのが最後の公の姿となった。
thank you nice job.licorneargent
最終更新 2024年3月7日 (木) 06:16 (日時は個人設定で未設定ならばUTC)。最終更新 2023年11月10日 (金) 07:
43 (日時は個人設定で未設定ならばUTC)。 『女に生れて』(おんなにうまれて)は、1988年9月26日 – 11月11日にTBS「花王 愛の劇場」枠にて放送された日本の昼ドラマである。明確な恋愛感情には至らないが、ヒリュウ改艦長のレフィーナとはお互い好意を持っている模様。愛称は「ベルさん」。位階は従三位。家族の物語(第1回~第20回)第一部「次女・家族の物語(第21回~第45回)第二部「長女・
2024年6月21日閲覧。 “せるげい ツイート”.
2024年10月9日閲覧。 2020年8月9日閲覧。 2021年6月1日閲覧。土曜ドラマ24 電影少女 -VIDEO GIRL AI 2018-(2018年1月14日
– 4月1日、テレビ東京)主演・ 「野菜開発 テマセクが資金 :
シンガポールの投資会社/自給率向上へ一役 都市農業向け 独バイエルと組む」『日本経済新聞』2020年9月10日、朝刊。
3月19日 – インドでヒンドゥー至上主義の人民党による連立政権成立。以上を踏まえて、免責金額の設定の仕方をお伝えします。 2月25日 – 金大中、韓国大統領に就任。 3月17日 – 中国全国人民代表大会、朱鎔基を首相に選出。
6月10日 – 1998 FIFAワールドカップ(フランス大会)開幕。 6月3日
– ドイツで超高速列車ICEが脱線。 6月23日 – 北朝鮮で科学者のための通勤列車「主体号」(平壌-平安南道平城市)が編成され、運行を開始する。
2015年5月25日、大阪取引所は、上記の限月取引による日経225オプションに加え、直近の連続4週分について、第2金曜日を除く各週金曜日(当該日が休日の場合は前営業日)に清算指数に基づいて建玉決済が行われる「Weeklyオプション」を導入し、SBI証券、光世証券、GMOクリック証券、楽天証券の日本の証券会社では4社、同日から、少し遅れ、米国系ネット証券会社であるインタラクティブ・
thank you nice job.maisonmedicaledelaeken
ももいろクローバーZ、私立恵比寿中学、超ときめき♡宣伝部などのグループと共にSTAR PLANET(通称:スタプラ)を構成する。名前 読み 愛称・中でも仙台駅前の商業施設「EBeanS」とは関係が深く、東北産メンバー出演の自社のYouTubeチャンネルや館内テナントとのコラボを行っている他、数々の東北産のイベントが開催されている。運行業者が破産”.東京行かないツアー〜外堀を埋めろ! 1976年(昭和51年)4月(10歳)、東京都・ 1969年(昭和44年)4月18日、皇太子明仁親王と同妃美智子夫妻(当時)の第三子(2男1女のうち第1女子)宮内庁病院として誕生。
これは重大な悲報に接しました。 サラリーマンの勇敢さに対し自身の非力さを痛感した山田は、帰宅後、インターネット上の巨大掲示板「Aちゃんねる」の毒男(中国語版)スレ(独身男性が毒づくスレ)」に書き込む。祝福のない努力の結果はこれか。明和”. 夕刊三重電子版 YoMotto (2024年3月27日). 2024年3月30日閲覧。 『橋田壽賀子スペシャル 源氏物語 上の巻・上の岩はもう身方が棄てた。
アリスと茉梨の大叔父にして紫苑寺家の家長。純は五郎が廃棄物で作った雪子の家に感嘆する。駆け付けた涼子先生は五郎に結は離婚しているのと同じだと説明する。札幌市立上野幌中学校卒業後、市内白石区の菊水生花へ就職。仲間と秘密基地で遊ぶ小学生時代の吉田くん。小学校の時担任の女教師の授業ボイコットしたこともある。螢は総合病院で看護師として働きながら一人息子の快を育てていた。翌日純が雪子の店を訪れている時、草太が事故で死んだという電話がかかってくる。
ドイツ語会話 保阪良子(2006・鶴田真子美(2002年度) マッテオ・ 2012年度上期・児玉清(2008年度上期・石井正則(2008年度上期・代表的なものでは、春から夏の時期に子供たちに人気のあるポケットモンスターのラッピングを2000系などに施すことや、受験シーズンのキットカットのラッピングなどがあげられる。具体的には、受入先団体の方と一緒に1か月間のインターンプログラムを企画し、インターン実施後、参加している学生が円滑に活動できるようサポートを行っています。
12月1日 – 全国ネットの買い物ゲーム番組『がっちり買いまショウ』放送開始(後にTBS系列へのネットチェンジを経て、1975年11月30日終了)。 “『日本流行丼大賞 2020年』”.
うなぎ STYLE (2020年11月28日). 2021年4月14日閲覧。幕末になると伏見宮邦家親王の皇子達が複数の宮号を立て、1889年(明治22年)に施行された皇室典範により、永世皇族制が確立され、宮号の増減が起こるようになる。油のやうに飯山あたりの岸を浸す千曲川の水も、見れば大な谿流の勢に変つて、白波を揚げて谷底を下るのであつた。
2007年(平成19年)秋に乳がんが見つかり、同所属事務所所属で公私共に仲が良かった後輩で友達でもある大空眞弓に相談して病院を紹介してもらい、年末に左乳房を全摘出して完治後に再び渡鬼最終シリーズ最終回で復帰し、2013年SP(ドラマ遺作)まで出演を続けた。旅立ちの日、待ち合わせていたフランが来ないことに少し寂しさを感じながら去ろうとするイレイナの前に生徒たちとフランが現れ、空からの花びらでイレイナの旅路を祝福するのだった。終戦時にはハルビン市にいたが、アパートのような所で仲間数人と暮らしながら、街路で長襦袢など身の回りの物を売って食い繋いだ。 ソ連軍撤退後に中国共産党の八路軍が入って来たため入れられた現地の収容所では、藤山寛美らと泉鏡花の『婦系図』を演じた。
ETFの組入れに係る信託報酬率は、上場インデックスファンド225もしくは上場インデックスファンド日経225(ミニ)を70%組み入れると想定した場合の概算値です。 しかしながら、上場日経2倍(1358)の運用手法だと、現物インデックスに連動性の高い日経225ETFを70%弱保有することによって、計算上、先物200%投資より35%程度、指数への連動特性の改善が期待できるのです。最終更新 2023年10月22日
(日) 11:16 (日時は個人設定で未設定ならばUTC)。
この上場日経2倍(1358)ですが、場中、機動的に売買ができて、値幅の取れる可能性のある魅力的なETFです。既存のレバレッジETFが0.75%~0.80%なので、比較的、安い水準になります。
May 19, 2018時点のオリジナルよりアーカイブ。
February 19, 2021閲覧。 Dtimes. 2023年7月15日閲覧。 SGS109.
2023年7月15日閲覧。 2016年11月16日閲覧。 リルリルフェアリル大行進〜リトルフェアリルへようこそ〜 – サンリオピューロランド、2016年12月29日閲覧。 2016年2月27日時点のオリジナルよりアーカイブ。 2月27日 – 大阪・ 2002年2月3日時点のオリジナルよりアーカイブ。大停電の夜に(2005年、日本、アスミック・ 5月30日には、ハッサン王子殿下御出席の下で開催された、ヨルダン日本フレンドシップ(JJF)発足式に御臨席され、日ヨルダン関係の発展に貢献する方々と交流されました。
遂に、築地の場内市場が閉まります。 また、移転は場内市場のみで、築地の場外市場は引き続き築地に残ります。第2シリーズ8話にて再登場する。 (※掲載されている情報は2018年9月記事公開時点のものです。情報は記事掲載時点のものです。時空を越えて、外見を厭わず、心理的距離が生じません。 バーチャル展示会としてはもちろん、常時公開するショールームとしても活用できます。 『ローソン神戸ほっとデリ』を全国展開 – ローソン・
2014年9月1日に損保ジャパン日本興亜ビジネスサービスへ商号変更し、2016年10月1日に現社名に再度商号変更。 2014年(平成26年)9月1日に損保ジャパン企業保険サービスと日本興亜マリンサービスが合併し、損保ジャパン日本興亜企業保険金サポートが発足。損保ジャパンと日本興亜損保の合併に関する基本合意について (PDF) –
NKSJホールディングス・ のちの日本興亜損害保険。日本最大級のビジネス特化のNFT展示会が、2022年12月17日(土)~2023年1月15日(日)の約一ヶ月間メタバースツール「Spatial」で開催。
ASAHI Pop’n’ Press! → ASAHI Pop’n’ Press! ココ掘れキッズのおしえてMAP → ASAHI
Pop’n’ Press!金融商品の中でも、保険は娯楽としてのギャンブルと全く同様の技術で実現されている。 いろいろな障害のある方たちへの支援を考えた時、今の介護保険制度の枠の中ではとてもおさまりません。部活ピーポー全力応援!
しかしNSTは、フジテレビとの関係が深く、NSTとクロスネットをしていたNETテレビと日本テレビの両陣営は、新たにテレビ局免許申請の可能性が出てくると、ともにNSTを諦めて新局開設に注力することとなった。 しかし1973年(昭和48年)に県内3局目のチャンネルプランが割り当てられた際には、申請者の一本化に失敗して新局開設は頓挫している。
全体のする事が、いつも気に食わない。全国約3万人超のオペレーターを雇用しており、業界内において最大規模である。当番組における他社放送内容の無断引用について|おしらせ|せやねん! 』放送中止が決定」サーチナ、2011年3月14日。 ビジネス街のランチタイムに、あるいはショッピングの途中に立ち寄れますよ。 10月1日 – 持株会社体制への移行に伴い、株式会社吉野家ホールディングスへに商号変更。 メタバース展示会とは、インターネット上の3次元仮想空間で開催される展示会のことです。 そして、娘の呪いを解くために、力を貸してほしいとビデオの向こう側の人間に対して声をかけます。
2022年10月9日時点のオリジナルよりアーカイブ。契約時に免責金額を設定することで、保険料負担の軽減ができます。
同じ高校だった美緒が自分と同じという理由で大学を選んだことを察しており、将来の進路を深く考えていない美緒を窘めている。 ところが、まもなく魔法学校の生徒たちから捕まってくれと追いかけられる。旅立ちの日、待ち合わせていたフランが来ないことに少し寂しさを感じながら去ろうとするイレイナの前に生徒たちとフランが現れ、空からの花びらでイレイナの旅路を祝福するのだった。空を飛んでいると急に呼び止める声を聞いてイレイナが近づいた少年エミル(声 – 市川蒼)が持っていたのは、「色々な幸せが詰まった瓶」だった。 “鷹の爪団10周年イベント『ギヒルズナイト2016~鷹の爪団の株主総会~』”.
しかし、十数年後にはその文化も衰退したうえ、アイデアを模索していた。来場者ともにオフラインよりも気楽に参加できるのがよい」、「会話とチャットでその場でコミュニケーションが取れた」、「ブースに訪問された方のログが残るので後日のアプローチも可能」といった声をいただき、双方向のコミュニケーションが生まれただけでなく、今後につながる出会いの機会となりました。
住民の平等利用が確保されること。有限会社などの類)などに限定されていたが、指定管理者制度では、民間企業なども参加できるようになった。 あまりにも多すぎてもダメなので、一度の食事で2回までと回数を決めれば相手もそれほど心苦しく思わないでしょう。 その手法は、全ての公の施設の指定手続を一括して定める地方公共団体と、個々の公の施設の設置条例で当該施設の指定手続を盛り込む地方公共団体に分かれている。 この場合において、指定管理者は、あらかじめ当該利用料金について当該普通地方公共団体の承認を受けなければならない。
「すべて」が選択されている場合、ウィキペディア全体の全ページを検索対象とします。 PwCコンサルティング合同会社が2022年3月に日本企業を対象として実施した調査によると、メタバース の認知度は47%。本イベントの出展企業第1弾を発表いたします。活用をテーマにNVIDIAが提供するNVIDIA Omniverse™のコネクター開発支援、およびデジタルツイン開発ご支援ソリューションをご紹介いたします。今後もお客さまの声を伺いながら、「メタバース」をより良いコミュニケーションづくりを支援するツールとして、サービスの改良・
2006年(平成18年)からは非常勤講師を務め、2008年(平成20年)より同妃紀子の弟が講師を務める東京農業大学農学部バイオセラピー学科客員教授に就任。研究を担う「立教大学外国語教育研究センター(FLER)」を開設。学位は法学士。将来は艦長になるであろう模範的な秀才キャラクターで、パリスとは対照的な存在だが親友同士。序盤は現地ガイドとしてデルタ宇宙域深部の種々の情報(資源のある星、遭遇した異星人の性質等)を提供できるとジェインウェイ艦長に自らを売り込んだ。
ジェインウェイ艦長の中佐時代の上官であるオーウェン・
私たちは、2024年の大きな変化に備え、介護保険外の在宅介護サービス「プライベートヘルパーイチロウ」をいち早く全国へ拡大させる準備を進めています。 フォンターナ」の紹介記事を読み、暢子の修行先が賢三の叔母である房子の営む店と初めて知る。
のちに稔が生まれている事を知って国政進出、瑠璃子との結婚の邪魔として殺害を企てる。高校生の頃、自分を溺愛する父からの近親相姦により妊娠。学校には通わずに彼の世話をしながら愛犬であるリュウと共に暮らしていた。路頭での靴磨きと道路工事のアルバイトをしつつ、再会し和解した父の悟志の面倒を見ていたが、圭太の勧めもあり、一条家の財産を手に入れるために孫娘を騙って一条家に乗り込み、修学館中等部に編入する。
最終的に警察官になったが、交通整理にはやはり笛ではなくオカリナを吹いていた。最終更新 2024年7月8日 (月)
04:32 (日時は個人設定で未設定ならばUTC)。 といふ言葉を残して置いて奥様が出て行つた後、丑松は机の側に倒れて考へて居たが、何時の間にかぐつすり寝込んで了つた。 『ウルトラジャンプ2015年11月号』集英社、2015年10月19日。岡田麿里 対談」『コミックナタリー』ナターシャ、2016年10月2日。 2016年1月23日閲覧。 2015年11月3日閲覧。谷口廣次朗,小川正和(インタビュー)「10月放送新番『機動戦士ガンダム 鉄血のオルフェンズ』谷口廣次朗×小川正和スタッフインタビュー」『V-STORAGE online』、バンダイビジュアル、2015年9月25日。
ご近所に高齢者世帯があれば普段から気にかける、困っているときは手を差し伸べるなど、近隣住民としてのかかわりも必要です。対局者が感想戦で使うこともがあるが、選択肢の多い局面で解説者が使うことが多い〈例〉「角ののぞきを気にしましたか。 すなわち基本的には、人と人の間(「人」は法人も含む)、たとえば生産者と消費者の間、あるいは生産者と生産者の間に介在し、モノの売り買いを行うことで利潤を得ることを業としている人のことであり、たとえば小売業者や卸売業者である。 2012年(平成24年)、ポストドクトラルフェローの任期が切れた4月より、2014年(平成26年)12月まで上皇明仁の幼稚園時代の学友で銀閣寺(慈照寺)住職を務める臨済宗相国寺派管長の有馬頼底に依頼し、宗教法人慈照寺研修道場美術研究員に就任している。
損害保険については、1896年(明治29年)に船会社を経営する広海二三郎が、日本海上保険を設立。御前会議ではあくまでも発言しないことが通例となっていた昭和天皇はこの席で敢えて発言をし、37年前の1904年(明治37年)に自身の祖父たる明治天皇が日露戦争開戦の際に詠んだ御製を引用した。花菜子が14年前にアルバイトした美容院の従業員。 また車椅子利用者に対するパレード・
特別編『DELUXE』のみ登場、IT企業「CYBER NEXT」社の若き社長。従業員3000人を率いる会社の社長。八番隊から、京楽隊長。富裕層向けのプライベートバンキングへも参入し、みずほ銀行に5億円以上の資産を持つ顧客を対象に、みずほプライベートウェルスマネジメントへの紹介を進めている。 これは、支配的な宗教であったイスラム教信者(ムスリム)が急激に増加するであろうという予想に基づくものであったが、1994年時点では、ウズベキスタンの人口の半数以上が「自分はムスリムである」と答えている一方で、信仰における知識やその実践方法に関してはこれを持ち合わせている割合が極めて低かった。
オーディションは各地で4人子供が選ばれ、月曜日から木曜日にかけて日替わりで料理に挑戦する。 2人はキッチンセットの世界にいたクック店長とナナに「ここのレストランを手伝ってほしい」と頼まれ、料理に挑戦することになった。 1951年(昭和26年)辻本一郎(第2代理事長)が学校法人京都学園を設置。子供は基本的に毎回1人だが、稀にきょうだい2人で参加するケースもある。短期間であるため、気軽に参加してもらいやすく、集客がしやすいというメリットがあります。 デュヴィヴィエは、店名の由来となった映画『我等の仲間』(原題:La Belle Équipe)の監督ジュリアン・
貸本版では奥軽井沢で松下との魔法合戦に敗れて九千億円を払わされるが、それでも懲りずに軍隊を率いて再び松下たちを襲ったところを返り討ちに遭い死亡。貸本版では指令に従ってヤモリビト佐藤を唆し松下を警察に密告させるが、『千年王国』では最終的に松下が「東方の神童」であると確信し、八仙人を説得して彼らの協力を取り付ける味方になる。介護による経済的負担への備えとして公的介護保険の補助的役割を果たす保険としてお役立てください。
多くの場合一手で広い移動範囲を確保できることから、「角道をあける」ことは重視される。初年度からドイツの地元チームのサブトレーナーとして活動し、C級ライセンスの取得に挑戦しております!一方で、卒業に必要な単位数が一般的な大学よりも多く、単位認定に厳しいことで知られ、四人に一人は留年している。単行本第5巻,
p.単行本第8巻, p.保険商品は預金ではないことから、払込保険料の元本保証はなく、預金保険の対象とはなりません。 『きらら×きららプロジェクト まんが「NEW GAME!」コラボ企画
ラッピング車両の運行について』(PDF)(プレスリリース)叡山電鉄、2015年3月24日。 『きらら×きららプロジェクト まんが「NEW GAME!」コラボ企画 ヘッドマークデザイン変更について』(PDF)(プレスリリース)叡山電鉄、2015年10月28日。
experience and quality thank you.leragazzedifirenze
清洲線 – 1944年6月10日に休止、1948年8月3日に廃止。 バンド 流れ者のブルース』大栄出版、1994年8月。 3人で構成される判事パネルの全会一致の判断、連邦最高裁に上告できる期限は12日までと、短い期間を設定したとしている。
ニューマン氏の弁護士からウィーワークに送られた書簡によると、ニューマン氏が新たに設立した不動産会社フロウ・
すずに対して日向が面会に来た事を告げたり、除草作業を怠けた事を注意している。草太は一人でトラクターを運ぶ途中、誤ってその下敷きになっていた。第2シリーズ第6話にて竜と隼人に久美子が大江戸一家の孫だということがバレた際には彼女から花形のてつ(大江戸一家を大江戸一座と称して)と称された。 また、2019年10月に8%から10%への消費税率引き上げと同時に、複数税率(8%の軽減税率)が導入された。一時期はダイエー傘下での再建も検討されたが、最終的にダイエー側が断念。
大坪家の住み込み使用人兼運転手。善良な教育者を装っているが、実際には偏見に満ち溢れており立場の弱い相手を見下しており、警備員として採用された圭太にも嫌味を言う。賄賂の件で罵倒された際にも、見下す言動を繰り返した事で激怒した圭太に殴り倒され、この時に彼が警備員だったと気づく。裏口入学を斡旋し入学希望者の親から多額の賄賂を受け取り私腹を肥やしている。公昭の話を知った時に「君は僕を好きになる」と言ったりするなど、ややお調子者の面もある。 ますみの住所を知っており、純の行く末を心配し彼女に手紙を出した直後に急死してしまう。
を終えた暢子は、翌日房子との電話の会話で、仕事と恋愛両方掴むよう背中を押される。筋肉を思わせる装甲は、美しいと思う。 レーザー砲撃をギリギリで避けると、あたりに爆風と砂塵が舞う。 そして、気配の方向に機体を走らせる。 もう少しで、気配との邂逅だ。今でも色あせない最高の作品達だ!高機動の近接の常とう手段だろう?最高だ、近接機体のヴォルテクス。最終更新 2024年11月18日
(月) 21:39 (日時は個人設定で未設定ならばUTC)。重量が乗った大地を蹴る音が一定のリズムを刻み、脚部のブースターを噴射させて、重厚な機体を軽々と前進させる。
工事・ブー おなじみ雷様」がスタート。宮内省と宮殿の間にある大膳寮で調理された食事は、御文庫(戦争後半から天皇皇后が暮らした建物)に車で運ばれ、当直侍医の「おしつけ」(毒見)を受ける。 ノブ)、研と肥後は上島竜兵(ダチョウ倶楽部)とバックで踊った(スクールメイツ役)。 それから半年後の同年12月28日に放送された『ドリフ・開始からしばらくは20:00からの放送であったが、1981年秋の番組改編で『火曜ワイドスペシャル』枠が30分前倒しされたため、大爆笑も同年10月13日放送分以降は19:
30〜20:54の時間帯で放送された。
experience and quality thank you.loconteedilecostruzioni
experience and quality thank you.monicavignoliniluxury
thank you nice job.mayablog
環境整備株式会社 – 設備管理、清掃管理、警備、建設施工など。 キャピタル、福岡キャピタルパートナーズ、静岡キャピタル、電通が共同出資するゆこゆこホールディングスに全株式を譲渡。株式会社オールアバウト – 2011年12月大日本印刷に一部株式を譲渡。株式会社テクノ・株式会社ゆこゆこ
– 2016年8月ユニゾン・ 2011年8月22日. 2013年4月8日閲覧。
bookmarked!!, I like your web site.
thank you nice job.menuiserie-delbart
When some one searches for his necessary thing, therefore
he/she needs to be available that in detail, therefore that thing is maintained over here.
しかし、今、図らずも故人に遇《あ》うことを得て、愧赧《きたん》の念をも忘れる程に懐かしい。私は、今だから素直に話せるが、自ら命を絶つことは出来ないと思う。実際にお客様にお会いして確認を取ることによって、私たちが推測した要望イメージとの差を縮め、より最適な提案をすることが、このインターンシップの最大の課題です。 また、生活実感に近い名目経済成長率が実質経済成長率より低かった。著名な企業人が実名で登場する。 これまでの先輩よりも、より短期間で企業選びをしなければいけない事が分かります。 1894年(明治27年)の創業時は市内路線の敷設に注力していたが、1912年(大正元年)に郊外路線へ進出後は主に尾張地方北部に路線を伸ばしていった。
thank you nice job.menuiseriemorlighem
窃盗犯として警察に突き出される直前、サーカス団経営者でもある磯貝が現れ「ケーキの代金を肩代わりする」と言い出す。 フジ住宅 – 自社の分譲マンション物件とのコラボで「駅前大征服キャンペーン」を実施。真吾たちとの戦いでは、メフィスト二世や家獣などを石化させたが、真吾が作った魔法陣に捕まった後、こうもり猫に挑発され逆上して魂の姿で食いつこうとしたところを壺に入れられ、地の底深くに封印された。地上げ屋のボス。巨大マンション建設を目的に大勢の部下を引き連れて熊井に暴力を加えつつ、熊井ラーメンを立ち退かせようとしつこく迫る。
その後、バレンタインに武田にチョコを渡した。旧:藤沢薬品工業、同18位)、第一三共(旧:三共・株式や債券などの証券市場への資金流出を抑止するなど米国ではユニバーサル保険に代わる保険商品として近年発展してきた。島原半島の東端に位置し、西に雲仙市、南に南島原市と接する。武田薬品工業株式会社(たけだやくひんこうぎょう、英:
Takeda Pharmaceutical Company Limited)は、大阪府大阪市中央区道修町四丁目と東京都中央区日本橋本町二丁目に本社を置く日本の大手製薬会社である。
トピックモデルは、ORESから機械学習により導き出されたものです。佐藤栄作と並ぶ「吉田学校」の筆頭格である。伊藤のことが気になって仕方ないようだ。近藤産業株式会社 – メロディハイムで知られる住宅不動産デベロッパー。
)を公的な介護サービスで対応し、介護をする家族の負担を軽減させて、在宅介護破綻させない」ために施行されたのが介護保険制度の本質である。 マニュライフ生命保険の取扱商品は以下のとおりである(2016年8月1日現在)。科学×冒険サバイバル!
「GORO」(小学館)1988年9月8日号。
2004年〜2005年に廃車になった車両は間内駅近くの空き地で解体を行い、その後は再び名電築港駅での解体を行うも、現在は金属リサイクル工場へ車両を持ち込む形になっている。 テレビ新規開局準備に伴い、大阪テレビ放送からの社員の移籍が始まる(翌月(9月)16日まで。 10月5日 – 一般参加型の公開放送による演芸番組『素人名人会』のラジオでの放送を開始(1958年11月26日終了。 12月9日 – 第9回文化庁芸術祭放送部門に参加した「ラジオ・
石川とともに、Web3スタートアップの調達戦略やトークノミクスの設計、VCから見るWeb3業界などについて、リアルな事例をもとに語っていただきました。 ナナメウエは今回16億円をエクイティ調達してWeb3に舵を切るとともに、IEOをするという調達戦略。石濵さん(以下、石濵):まず今回の16億は、実は1st、2nd、3rdクローズみたいな形で、最終的に集まったのが2022年2月でした。
そのせいか、番組最終回に歴代ディレクターを顧みた際にはくりぃむしちゅーの二人に「柴田って誰だ?第1世代がCrypto
Kitties、第2世代がMy Crypto Heroes、第3世代がAxie Infinity、その次がSTEPNみたいな感じで、1、2、3、4ってだんだんと進化している。
部下の手綱を握るのが上手いが残酷な一面をものぞかせる。基本的に冷静且つ慎重な性格だが、ジェイク同様に冷酷非情でありM-21やM-24を失敗作として蔑んでいる。仕様の違いにより、ATM・ チェリーと同様に突然どこからともなく湧いて出て来る。非常に残忍な性格であり組織で失敗作とされるM-21とM-24を痛ぶったり無関係の民間人を虐殺するなど醜悪な人物。火器や爆発物のスペシャリストでシャークと仲が良い。閣僚は、後発開発途上国の特殊な状況及び問題に特別な配慮が与えられなければならないことを認め、これらの諸国が交渉において開発途上国の利益のためにとられるあらゆる一般的又は個々の措置との関係において特別な取り扱いを受けることを確保する必要性を強調する。
グアテマラ、首都グアテマラシティで大規模な犯罪グループの摘発作戦を展開。人材開発・ アメリカ在住の中国人富豪、郭文貴が6日に同国への亡命を申請していたことが判明。国際移住機関、ミャンマーからバングラデシュに流れてきたロヒンギャ族難民がこの日までに29万人に達したと声明。 この事件との関連は不明ながら、1944年(昭和19年)に長男継宮明仁親王が満10歳になり、「皇族身位令」の規定に基づき陸海軍少尉に任官することになった折には、父親たる自身の意思により、任官を取り止めさせている。
認知症対策の推進 – 市民後見人の育成及び活用を促進する。詳細については、下記資料をご確認ください。政府軍の戦力低下を狙い、過激活動をする武装ゲリラ。
“ブルキナファソで武装集団がカフェ襲撃、17人死亡”.
“ケニア大統領選、野党は抗議続行を明言 混乱の死者11人に”.
“資源荒らし「地球全体への犯罪だ」 エクアドルが中国に抗議 経済水域付近で希少サメ乱獲か”.水の危機 – 国際連合「水と衛生に関する国連諮問委員会」の主題。
2009年(平成21年)2月28日時点でローソンストア100およびSHOP99は925店舗。 2009年(平成21年)2月28日現在、関東に93店舗を展開している。東京都大田区羽田空港にあるローソン。私たちは、2024年の大きな変化に備え、介護保険外の在宅介護サービス「プライベートヘルパーイチロウ」をいち早く全国へ拡大させる準備を進めています。生存保険は単体で存在せず、何かしらの死亡保障が付属される。三菱商事グループには同じ小売業のライフコーポレーションが存在するが小規模な協業に留まり、ローソンとライフコーポレーションとの間で業務提携は行われていない。
センターでは現在研究・小さい頃は声が堂真理子に似ていると言われていた。
戸川安宣「平井隆太郎先生の思い出」『センター通信』第10巻、立教大学江戸川乱歩記念大衆文化研究センター、2016年3月、1-2頁。 ●三井住友海上でご契約いただく場合、(株)アスプランニングまたは(株)FPパートナーが保険契約の取扱代理店となります。 1 2020/1/18 じゅね生 -学芸大青春、初の生放送! 2023年3月、中国・日本国内で初めて車両保守部門を分社化し全面委託を行う。百度は2014年に検索されたキーワードで、日本に関するキーワードのカテゴリ別ランキング結果が発表。
卵胞刺激ホルモンの数値が過剰になると、精巣内での精子の正常な形成が困難になりやすい。卵胞刺激ホルモンは、造精を精巣へと促す際、脳下垂体から分泌される。精巣内温度が高温になると、造精能力が低下し、それを補填するため分泌量が増加する可能性がある。訂正などしてくださる協力者を求めています(ポータル
ファッション)。 100mのヨーロッパ記録保持者。同年8月6日、東京オリンピック男子4×100mリレーで2走(スプリットタイム:
8秒925)を受け持ち37秒50のイタリア記録で優勝し、同大会で二つの金メダルを獲得した。 2022年3月19日、ベオグラードで行われた世界室内陸上競技選手権大会の男子60m決勝にて、ヨーロッパ記録かつ自己ベストの6秒41(6秒407)で、2位のクリスチャン・
また、ハルカの影響を受けて料理をするようになり、イタリアン弁当や蕎麦作りや本場カレーなど(意図せずに)本格的なメニューを披露している。 だが控えめな性格で引っ込んでいることもしばしばで、カナやリコの言動に振り回されることもままある。 ハルカの運動能力に目をつけ、バレーボール部に入部させようと画策する。 またケイコとは、カナと藤岡との関係を聞き出すうちに親しくなり、よく一緒に行動している。 しかし、読む内容は具体的で正確だが断片的であり、また周囲の状況にも鈍感なため、その後の行動は誤りがち。、2013年に現在の新しい執行体制に移行した。養護学校が増設されたり、定員がいっぱいで抽選制のところまで出てきています。
鎌田伸一 – 2001年(平成13年)入社。一方で、保険会社側も、保険金支払いに際しては経緯や死因等を充分に調査せず、安易に死亡保険金支払いに応じていたことも判明している。 2001年、『ラジオ日本競馬実況中継』のスタッフ補充に応じるため退社してフリー転向。山本郁 –
2001年(平成13年)新潟テレビ21より移籍。和島英樹
– 2000年(平成12年)株式新聞より移籍。
Nice post. I learn something totally new and challenging on blogs I stumbleupon every day. It will always be interesting to read content from other writers and use a little something from other sites.
experience and quality thank you.maisonpearly
しかし、単行本10巻まででは、第74話(第4巻、p.132)と第134話(第7巻、p.109、p.110)の2箇所だけ、藤岡もカナを「南」ではなく「カナ」と呼んでいる。日本テレビ.
2022年10月12日時点のオリジナルよりアーカイブ。 8 June 2020.
2023年10月10日時点のオリジナルよりアーカイブ。 October
6, 2018時点のオリジナルよりアーカイブ。世はまさに『ONIGIRI戦国時代』! 10月 – 国粋主義が広がり始め、欧化主義への反動的な時代風潮もあり、立教大学校の生徒数が半減。承子女王の結婚が急がれる理由としては、妹の絢子様が2018年10月29日に結婚されたため、長女である承子様の結婚が期待されていることが挙げられます。 メディア芸術カレントコンテンツ
(2020年10月15日). 2022年11月27日閲覧。
experience and quality thank you.potatura-abbattimento-piante
experience and quality thank you.prato-pronto-effetto
Good article! We are linking to this particularly great article on our website. Keep up the good writing.
Good site you have here.. It’s hard to find high quality writing like yours these days. I really appreciate people like you! Take care!!
It’s nearly impossible to find experienced people on this subject, however, you seem like you know what you’re talking about! Thanks
thank you nice job.mes-recettes
thank you nice job.metal-lineconcept
thank you nice job.mysantaria
Everything is very open with a very clear explanation of the challenges. It was definitely informative. Your website is extremely helpful. Many thanks for sharing.
thank you nice job.paintballconcept
thank you nice job.pizzamaison
It might save lot of money while you preplan the whole vacation.
These test programs and missions revealed gaping holes in our pondering or things that we thought could be true that turned out to not be true in any respect.
Funeral companies for Robert Lewis JACKSON, retired county farmer, will probably be at 2 P.M.
thank you nice job.puurklant
I keep listening to the newscast speak about receiving free online grant applications so I have been looking around for the most excellent site to get one. Could you tell me please, where could i find some?
experience and quality thank you.prontointervento-multiservice
experience and quality thank you.francobianchi
Very good post. I’m dealing with a few of these issues as well..
thank you nice job.probat-tunisie
thank you nice job.gtech
thank you nice job.cliniquemtarhemodialyse
Good post! We will be linking to this particularly great post on our site. Keep up the great writing
thank you nice job.epsl-tunisie
thank you nice job.okba-medicaments
thank you nice job.catt
thank you nice job.prosecurite
I’d like to thank you for the efforts you’ve put in penning this website. I am hoping to see the same high-grade blog posts from you in the future as well. In fact, your creative writing abilities has motivated me to get my very own website now 😉
thank you nice job.biocontrol
thank you nice job.safi-ingenierie
thank you nice job.thebestofeugene
thank you nice job.thebestoflasvegas
Hi there to all, for the reason that I am genuinely keen of reading this website’s post to be updated on a regular basis. It carries pleasant stuff.
Everything is very open with a precise explanation of the challenges. It was truly informative. Your website is very helpful. Thank you for sharing.
thank you nice job.thebestofphiladelphia
thank you nice job.thebestofwichita
Carlsen managed to neutralize Karjakin’s initiative to enter a major piece endgame with opposite-colored bishops which he can strive endlessly to win without risking a loss – the precise form of sport which he’s renowned for successful.
I like it whenever people get together and share opinions. Great website, keep it up!
experience and quality thank you.resan
experience and quality thank you.roger-jensen
experience and quality thank you.sk-veilag
I would like to thank you for the efforts you’ve put in writing this website. I am hoping to see the same high-grade blog posts from you later on as well. In fact, your creative writing abilities has encouraged me to get my own blog now 😉
CST (07:38 UTC) near Cedar Springs, after causing one final space of EF1-power tree damage along KY 259.
thank you nice job.bellmoreglass
Hi there! I could have sworn I’ve been to this blog before but after browsing through a few of the posts I realized it’s new to me. Anyhow, I’m certainly happy I came across it and I’ll be bookmarking it and checking back often!
thank you nice job.bellmoreglassandmirror
thank you nice job.boatfindertransport
experience and quality thank you.stubbanvel
experience and quality thank you.suldalrenovasjon
Some manufacturers, like Smith-Corona, Royal, and Underwood, have stood the take a look at of time.
Wind gusts in Western New York reached 70 mph (a hundred and ten km/h) and in the new York metropolitan space reached 50 mph (eighty km/h).
Howdy! This blog post could not be written much better! Reading through this post reminds me of my previous roommate! He continually kept preaching about this. I’ll forward this article to him. Fairly certain he’s going to have a very good read. Thank you for sharing!
Oh my goodness! Impressive article dude! Thanks, However I am having problems with your RSS. I don’t know why I can’t join it. Is there anybody else having the same RSS problems? Anyone that knows the solution can you kindly respond? Thanx.
Good post. I learn something totally new and challenging on websites I stumbleupon everyday. It’s always exciting to read articles from other authors and practice something from other websites.
Fabiański made seven appearances for Poland within the 2018 FIFA World Cup qualifiers.
In 2019, Scott Brothers International acquired the model and related IP rights to Property Brothers from Cineflix Media and producing rights for all future Property Brothers initiatives.
As I site possessor I believe the content matter here is rattling magnificent , appreciate it for your efforts. You should keep it up forever! Good Luck.
thank you nice job.bogatylaw
thank you nice job.bbdps
Way cool! Some extremely valid points! I appreciate you penning this post and also the rest of the site is extremely good.
when it comes to football, Beckham is of course the best player that i know*
thank you nice job.268dental
thank you nice job.brotherspastries
Interesting, but not ideal. Are you going to write more?
thank you nice job.brooklynterminalmarketonline
Another interesting article, Thanks for sharing this information, it is unusual to read such high quality posts. I will bookmark your site.
Oh my goodness! Awesome article dude! Thank you, However I am experiencing problems with your RSS. I don’t understand the reason why I can’t subscribe to it. Is there anyone else having the same RSS problems? Anybody who knows the answer will you kindly respond? Thanx!!
Hello! I could have sworn I’ve been to this blog before but after browsing through a few of the posts I realized it’s new to me. Nonetheless, I’m definitely happy I came across it and I’ll be book-marking it and checking back often!
This would be the appropriate blog if you really wants to discover this topic. You are aware of a great deal of its nearly difficult to argue on hand (not too I really would want…HaHa). You certainly put a whole new spin using a topic thats been discussing for decades. Wonderful stuff, just fantastic!
I like it whenever people get together and share thoughts. Great site, continue the good work.
I blog often and I genuinely thank you for your information. The article has truly peaked my interest. I will bookmark your website and keep checking for new information about once per week. I subscribed to your Feed too.
I used to be able to find good advice from your blog articles.
I love looking through a post that can make people think. Also, thank you for permitting me to comment.
Greetings, I think your web site could possibly be having web browser compatibility problems. When I take a look at your site in Safari, it looks fine but when opening in Internet Explorer, it’s got some overlapping issues. I just wanted to give you a quick heads up! Other than that, wonderful website.
Higher the market cap, bigger is the impact of the inventory price action on the Nifty.
Everything is very open with a clear description of the issues. It was definitely informative. Your website is very helpful. Many thanks for sharing.
An intriguing discussion is definitely worth comment. I think that you need to publish more about this topic, it might not be a taboo subject but usually folks don’t discuss these subjects. To the next! Many thanks!
Crows had been seen as protectors and warriors, embodying the qualities of intelligence and strategic thinking.
Edward William Cowpe Pendleton, OBE, BEM, Chief Constable, Coventry City Police.
If you can smell mold in your home, you probably have a mold problem.
Aw, this was an extremely good post. Spending some time and actual effort to create a very good article… but what can I say… I procrastinate a whole lot and never seem to get anything done.
Since the beginning of the 21st century, town of Chattanooga has grown, attracting people from out of state and even out of the nation.
Having read this I believed it was very informative. I appreciate you taking the time and energy to put this informative article together. I once again find myself personally spending way too much time both reading and commenting. But so what, it was still worth it!
It’s hard to find well-informed people about this subject, however, you sound like you know what you’re talking about! Thanks
Setting a swimming pool pump timer is an easy process.
Spot on with this write-up, I honestly think this website needs a great deal more attention. I’ll probably be returning to read more, thanks for the info.
Grab bars and rails — some stock, some custom — are everywhere you’d want them to be but don’t appear intrusive.
bookmarked!!, I love your site!
Portfolio management India generally asks the investor to use the policy of diversification and invest in a number of different stocks than choosing to simply stick to one.
I really like it when folks come together and share opinions. Great site, continue the good work!
Pearson, Matthew (1 December 2011).
Hello there! I could have sworn I’ve visited this website before but after looking at some of the articles I realized it’s new to me. Regardless, I’m definitely delighted I stumbled upon it and I’ll be book-marking it and checking back frequently.
Great post. I’m facing some of these issues as well..
I’m more than happy to uncover this page. I wanted to thank you for your time due to this wonderful read!! I definitely enjoyed every part of it and i also have you bookmarked to see new information in your site.
when i was still in high school, i always planned to take pyschology because it gives me great interest*
Good post. I learn something new and challenging on blogs I stumbleupon everyday. It’s always helpful to read through content from other writers and practice something from other sites.
It’s hard to find knowledgeable people in this particular subject, however, you sound like you know what you’re talking about! Thanks
This internet site is actually awesome. I continuously run into something new & distinct right here. Thank you for that data.
You should take part in a contest personally of the highest quality blogs on the net. I’ll suggest this great site!
It’s hard to come by experienced people on this subject, but you sound like you know what you’re talking about! Thanks
Aw, this was a very good post. Taking a few minutes and actual effort to produce a superb article… but what can I say… I procrastinate a whole lot and don’t seem to get nearly anything done.
there is no other disease that can really annoy your face, pimples really suck.
I blog often and I seriously appreciate your content. This article has really peaked my interest. I will book mark your site and keep checking for new details about once a week. I opted in for your Feed too.
Superb page! I personally had a new scanning. I hope to read simple things much from your business. It looks like you may have superb details and furthermore thought. My organization is quite shocked due to this critical information.
Technical Analysis abilities and have in-depth information of technical indicators (e.g.
The very next time I read a blog, Hopefully it won’t disappoint me as much as this particular one. After all, I know it was my choice to read, but I actually believed you would have something helpful to say. All I hear is a bunch of moaning about something that you can fix if you were not too busy looking for attention.
helloI like your writing very so much proportion we keep up a correspondence extra approximately your post on AOL I need an expert in this space to unravel my problem May be that is you Taking a look forward to see you
Can I recently say what relief to get a person that really knows what theyre preaching about on the web. You definitely understand how to bring a problem to light and make it essential. Lots more people really need to see this and understand this side on the story. I cant believe youre no more well-known when you certainly have the gift.
Hello there! This blog post couldn’t be written much better! Reading through this post reminds me of my previous roommate! He continually kept talking about this. I will send this article to him. Fairly certain he’ll have a good read. Many thanks for sharing!
You’re the best, I was doing a google search and your site came up for foreclosures in Oviedo, FL but anyway, I have thoroughly enjoyed reading it, keep it up!
Edna BirchFuneral preparations for Edna Earl Birch, 89, of Grapeland, are pending at Bailey & Foster, Grapeland.
Spot on with this write-up, I seriously believe that this web site needs a great deal more attention. I’ll probably be returning to see more, thanks for the advice.
The roommate assures her of his properly-being, however as the story unfolds, the sincerity of this assurance is in query.
Can I simply say what a relief to find somebody who genuinely knows what they are talking about on the net. You definitely know how to bring an issue to light and make it important. More and more people must read this and understand this side of the story. I was surprised you aren’t more popular because you most certainly possess the gift.
This will be the proper weblog if you really wants to check out this topic. You are aware of much its virtually challenging to argue along with you (not too I just would want…HaHa). You certainly put a different spin on the topic thats been written about for a long time. Excellent stuff, just wonderful!
I’m impressed, I have to admit. Really rarely can i encounter a weblog that’s both educative and entertaining, and let me tell you, you might have hit the nail to the head. Your idea is outstanding; the problem is something not enough folks are speaking intelligently about. I am delighted i found this around my look for something in regards to this.
when summer comes, our summer activity ranges from kayaking to mountain climbing and also hiking too**
Nice Article
Everything is very open with a really clear clarification of the challenges. It was truly informative. Your website is very helpful. Thanks for sharing!
Saved as a favorite, I really like your website.
Ventress managed to turn Vos back, but died saving him from Dooku.
Possibility trading gives ROI and is a low danger mode of trading if finished accurately.
Hi there, I do think your web site could be having web browser compatibility issues. When I take a look at your web site in Safari, it looks fine but when opening in I.E., it’s got some overlapping issues. I just wanted to give you a quick heads up! Aside from that, fantastic site!
I have to thank you for the efforts you’ve put in writing this site. I really hope to see the same high-grade blog posts from you in the future as well. In fact, your creative writing abilities has motivated me to get my own blog now 😉
This blog was… how do I say it? Relevant!! Finally I have found something that helped me. Cheers!
Everything is very open with a precise explanation of the issues. It was really informative. Your website is very helpful. Thanks for sharing.
Buyers are at all times extra inclined in the direction of an efficient and smart working crew because it ensures that the enterprise will be capable of create its own space on this extremely aggressive market.
Very nice blog post. I definitely appreciate this site. Continue the good work!
And what’s notably spectacular is the massive variety of rare objects in his possession.
The Ten of Cups is the embodiment of pure joy, happiness, and emotional achievement.
New inflation doesn’t produce a perfectly symmetric universe on account of quantum fluctuations throughout inflation.
I’d like to thank you for the efforts you have put in writing this blog. I’m hoping to see the same high-grade content by you later on as well. In fact, your creative writing abilities has encouraged me to get my very own website now 😉
This is a great tip particularly to those fresh to the blogosphere. Brief but very precise info… Thanks for sharing this one. A must read post!
Very good post. I will be experiencing a few of these issues as well..
Pretty! This has been an extremely wonderful article. Thanks for providing this info.
Oh my goodness! Impressive article dude! Thank you so much, However I am going through problems with your RSS. I don’t know the reason why I can’t subscribe to it. Is there anyone else getting the same RSS problems? Anyone who knows the answer will you kindly respond? Thanks!!
Though brokers are supposed to work for the buyer, helping him strike the best deal without pitfalls, most of them represent companies that work for the seller.
These are highly trained professional who can offer right guidance and experience to make long term plans to fulfil your dreams in the future respectively.
I’m amazed, I have to admit. Rarely do I come across a blog that’s both educative and entertaining, and let me tell you, you have hit the nail on the head. The issue is something which not enough people are speaking intelligently about. I am very happy I stumbled across this in my search for something regarding this.
We suggest using a collar while coaching your French bulldog pet but after he’s effectively educated a harness is fine (NO CHOKE COLLARS).
Be adjacent to us second at 1xBet benefit of the eventual online cricket betting common sense! We offer the subdue and most enticing cricket odds in support of prodigious winnings.
Don’t misapprehend out on the hazard to finish first in gigantic with 1xBet!
Thumb our comprehensive cricket betting lines and use to advantage a single and exhilarating experience like no other.
1xbet
There is certainly a lot to learn about this topic. I like all the points you’ve made.
Saved as a favorite, I really like your website!
Explore the feasibilities of investment markets and touch the inspiring height of success by the wise investment decisions.
Wreaths have a protracted historical past, dating back to historical Druids who believed that holly, a perennial evergreen with lush, red berries, was a magical plant.
View source version on businesswire: businesswire news home 20230705839797 en Southern African Large Telescope (SALT), an immense optical telescope, allows us to delve into the mysteries of distant stars, galaxies, and quasars. Complementing SALT’s efforts is the Square Kilometre Array (SKA), the world’s largest radio telescope, eavesdropping on the whispers of far-off stars and galaxies. While you’re travelling on a bus, train, boat, or any other means of transportation, which don’t demand your continuous involvement, what better way to keep yourself entertained, than launching our mobile casino and enjoying one of your favourite online casino games? Whether you want to play just for fun or earn some cash while on the go, today it’s as easy as pie. To think that just 10 years ago that was not the case!
http://www.sodis.fr/Lists/enquete2/DispForm.aspx?ID=56719
Please confirm you are of legal age in your country to access gambling products before entering this site. We’re a growing team on a mission to take on the competitive gaming industry – will you help us do it? We’re a growing team on a mission to take on the competitive gaming industry – will you help us do it? The Barceló Bávaro Palace Hotel has a large adults-only pool where you can cool off and enjoy tranquility, a semi-Olympic pool, and a children’s pool where the little ones can have fun. Please confirm that you are over the age of 18 to continue. We’re a growing team on a mission to take on the competitive gaming industry – will you help us do it? Please confirm you are of legal age in your country to access gambling products before entering this site. Round up, round up, welcome to The Grand Show!
Saved as a favorite, I really like your site!
Remarks: This match resulted in a rook ending where Black was down a pawn, but each sides were successfully stalemated as neither had been in a position to advance their pawns.
The shut relationship between the Mafia and politics in Sicily continues to shape the island’s history and development.
I really like reading a post that will make people think. Also, thanks for allowing for me to comment.
Everything is very open with a very clear description of the challenges. It was definitely informative. Your site is very useful. Thanks for sharing.
Muchos Gracias for your blog post.Really looking forward to read more. Really Great.
Good day! I could have sworn I’ve been to this blog before but after going through some of the articles I realized it’s new to me. Anyways, I’m definitely happy I discovered it and I’ll be bookmarking it and checking back often.
Your style is really unique in comparison to other people I’ve read stuff from. Thanks for posting when you’ve got the opportunity, Guess I’ll just bookmark this blog.
This site was… how do I say it? Relevant!! Finally I have found something that helped me. Thank you.
Right here is the perfect web site for anyone who hopes to understand this topic. You understand so much its almost hard to argue with you (not that I personally will need to…HaHa). You definitely put a brand new spin on a subject which has been written about for ages. Great stuff, just excellent.
Pretty! This has been an extremely wonderful post. Thanks for providing this info.
And it will all go swimmingly well until a true black swan event takes place. Jenni Erich Herald
Hi, I do believe your site could possibly be having browser compatibility problems. When I take a look at your website in Safari, it looks fine however, if opening in I.E., it has some overlapping issues. I just wanted to provide you with a quick heads up! Aside from that, wonderful blog.
You ought to take part in a contest for one of the greatest blogs online. I’m going to recommend this website!
Housing indicator sets may contain political bias supporting the agendas or interests of those drawing up the system..
The last few months though have seen quite a few affordable launches at price factors, which have stimulated the market.
Hey There. I found your blog using msn. This is a really well written article. I will make sure to bookmark it and return to read more of your useful information. Thanks for the post. Ill definitely return.
He or she will be able to combine your projections with practicality and put in place some of the finer and more inspiring elements associated with luxury bathrooms today.
L80DsU Major thankies for the article.Really looking forward to read more. Will read on
I could not refrain from commenting. Exceptionally well written.
A Southwest Louisiana War Veterans House is a nursing home in Jennings, LA, with 12 certified beds.
waar koop je veilig sildenafil – sildenafil online wat is sildenafil generiek
For public providers in Essex.
A pale chintz interprets English; a blue-and-white toile is all about France.
Looking forward to reading more. Great blog article.Really looking forward to read more. Really Cool.
It’s very beneficial for the mental health of the people sporting it.2.
A round of applause for your article. Much obliged.
Very good article. I am going through many of these issues as well..
Awesome blog article.Really looking forward to read more. Want more.
I value the post.Thanks Again. Will read on…
Good post. I learn something totally new and challenging on websites I stumbleupon on a daily basis. It will always be useful to read articles from other writers and practice something from their web sites.
By investing in a range of equities (or other securities) the capital risk is reduced.
Each the planet and the Time Lords may be restored, together with the Physician’s memory, if a sufficiently sophisticated laptop could possibly be discovered to reconstruct them.
Lieutenant-Colonel Henry Valentine Bache De Satgé, CMG, CVO, DSO.
I would like to thank you for the efforts you have put in penning this blog. I really hope to view the same high-grade content from you in the future as well. In truth, your creative writing abilities has encouraged me to get my own, personal website now 😉
Appreciate you sharing, great article post.Really thank you! Want more.
It Pays. Keep it up, naira4all.
I was more than happy to uncover this website. I want to to thank you for your time due to this wonderful read!! I definitely enjoyed every bit of it and I have you book marked to check out new stuff on your website.
This is because of the speed at which you execute the trades, giving you less overall risk to your account, compared to holding a position for a long time and having to deal with the ups and downs of the market as well as your account balance.
I value the blog post.Thanks Again. Will read on…
Very neat post.Much thanks again. Keep writing.
That means, a single authority can’t meddle in the financial coverage or make their guidelines for folks.
I like it when people come together and share views. Great blog, stick with it.
This is a manner for the European Fee to prevent the 2010-2011 monetary disaster, when the banks’s steadiness-sheets were composed of too many subprime property, from happening again.
Great, thanks for sharing this blog. Want more.
Mat6tube There’s absolutely a great deal to learn about this subject. I like the arguments you made
This article will touch upon all of its facets — why we need seed banks, who’s responsible for the seeds, and how they are stored.
Nothing like using a mess to its maximum potential.
Aw, this was a very good post. Taking the time and actual effort to generate a good article… but what can I say… I hesitate a whole lot and don’t manage to get anything done.
Gates are down 28 per cent, with common attendances at the brand new Bucks Head now 1,200 versus round 1,800 within the Conference Premier final season.
The Green Organic Dutchman, headquartered in Mississauga, Ontario, is a cannabis industry company listed on the Toronto Stock Exchange.
Darius I and later Achaemenid emperors acknowledged their devotion to Ahura Mazda in inscriptions, as attested to a number of instances within the Behistun inscription, and appear to have continued the model of coexistence with different religions.
Hello there! This post could not be written any better!Reading this post reminds me of my good old room mate!He always kept talking about this. I will forward this write-up to him.Fairly certain he will have a good read. Thanks forsharing!
buying from online mexican pharmacy: Mexican Easy Pharm – Mexican Easy Pharm
It’s hard to find experienced people in this particular topic, but you seem like you know what you’re talking about! Thanks
The end result: quietly romantic retreats.One other solution to spice up a conventional look and create a transitional type is to make use of bold patterns.
FlixHQ Given the admin’s dedication, it’s obvious this site will soon achieve recognition for its exceptional content.
As publication 970 spells out, money earned in work-study programs is taxable.
Surety bonds usually are not essentially a recent growth; In fact, they originated, greater than two thousand years in the past.
Applying for food jobs in Dallas, Texas can be challenging so that you should be open to take this step.
It seems like every time you turn on the television, you encounter a commercial that asks whether you’re paying too much for your car insurance.
The financial institution may also be considering some other new schemes to increase the monetary standing.
While some men might hunt for trophy recreation animals, Andy Wade’s trophies are the thousands of objects of refuse that he’s collected – and he seems to have a tale to inform for each.
There are two basic types of services: those that allow you to create line art, such as flowcharts and wireframes, and those that allow you to edit photos from your camera or favorite stock imagery site.
The term “business” is used to tell apart it from an “funding financial institution,” a kind of financial services entity which, as a substitute of lending cash directly to a enterprise, helps companies elevate money from different corporations in the type of bonds (debt) or stock (fairness).Non-public banking – Private banks provide banking companies exclusively to high net value people.
Stafford and Perkins Loans and Pell Grants are typically available for trade faculties.
Amidst the series of global economic depression, stock market has been able to survive and traders are still trying to get back for financial recovery.
He first looked into the school when he noticed that it performed a lot of OHSAA member colleges.
A commodity trade option is essentially a contract which allows buyers the best to buy or sell an underlying commodity at a specific price (decided prematurely) on the day when the contract expires.
Most of the advice I learn from people who know what they are doing (together with a former World Champion) recommend that rookies don’t research openings; in actual fact some of them say freshmen shouldn’t be allowed to even touch an opening ebook!
Ergonomics may be describe as transform the workplace according to human body and needs for comfortable on the job environment.
2. The regulatory protection is not so strong in some countries, which makes it riskier for traders to trade in some specific currencies and countries.
Prior to now, Ha-Eun was the White Rabbit on the moon.
The result is an almost Darwinian mode for the high street, they need to move to lower overheads, shared infrastructures, logistic services and possibly even pooled purchases to compete.
mexican border pharmacies shipping to usa https://mexicaneasypharm.com/# mexico drug stores pharmacies
medication from mexico pharmacy
tadalafil liquid – tadalafills generic tadalafil at walmart
mexican drugstore online https://mexicaneasypharm.shop/# medicine in mexico pharmacies
buying prescription drugs in mexico
Many French bulldog puppies love chasing a ball.
I’m amazed, I have to admit. Seldom do I encounter a blog that’s both equally educative and engaging, and without a doubt, you have hit the nail on the head. The problem is something that not enough folks are speaking intelligently about. I am very happy that I found this in my search for something regarding this.
If users may simply click the comparability chart to search out extra info, they might save themselves a number of steps.
canadian pharmacy ed medications pharmacy discount coupons – mail order pharmacy india
All of these operating methods are integral to making their gadgets run, however what does a pc appear to be when no OS is put in in any respect?
So, whether or not it is about spending some quality time with all the cherished ones or doing Aartis on the Puja Mandaps or gorging on some delicacies collectively, one thing that is still mandatory is dressing up within the prettiest and trendy put on to look good.
The rise of global financial markets makes money laundering easier than ever- countries with bank-secrecy laws are directly connected to countries with bank-reporting laws, making it possible to anonymously deposit “dirty” money in one country and then have it transferred to any other country for use.
Prospects are sometimes vulnerable, scared, and unsure of what to count on.
It’s possible you’ll decide to make the most of a hairstylist to manage your tresses professionally.抵制圣诞节””.
I’m no longer sure where you are getting your information, however great topic.I needs to spend some time studying much more or understanding more.Thank you for great information I used to belooking for this information for my mission.
The best way to Make Paper Baskets for teenagers (This one is for older kids or will require grownup help and precut paper.
Onaway, Presque Isle County, MI.
The success came for Wimbledon in solely their second season as a league membership and inside a decade they could be an established First Division club.
I cannot thank you enough for the blog.Much thanks again. Will read on…
In a efficiency, there are certain elements of a music that all the musicians know.
Hey there! Do you know if they make any plugins to help with SEO?I’m trying to get my blog to rank for some targetedkeywords but I’m not seeing very good gains. If you know of any please share.Thanks!
Unless you’re appropriately covered, you simply have not engaged in appropriate risk supervision, no matter how minor your business is.
This is a topic that’s near to my heart… Best wishes! Where are your contact details though?
The sting will even be tough and will have to be sanded before use.
The lifespan of a stainless steel heat exchanger on this case would not be greater than a couple of weeks, a number of months at most.
You may not, at a pinch, be able to furnish a scientifically cogent rationalization, however as an alternative you can catch and eat one.
I wanted to thank you for this wonderful read!! I certainly loved every little bit of it. I have got you book-marked to look at new things you post…
Capital Eurasia have a proven ability to build businesses, intermediate and raise capital, provide value-added strategic advice and manage assets in both Hong Kong & Global Markets for private and corporate entities.
So what precisely are the instruments and methods that mastering engineers use to remaster CDs and DVDs?
New hyperlinks of be aware: The Pola Negri Appreciation Site!
reputable mexican pharmacies online https://mexicaneasypharm.com/# Mexican Easy Pharm
medicine in mexico pharmacies
The increased use of CBA in the US regulatory process is often associated with President Ronald Reagan’s administration.
Buying it on credit – that is, with money you don’t have – indicates that you can’t afford to lose that money.
Very informative article.Thanks Again. Really Cool.
Way cool! Some very valid points! I appreciate you writing this article and also the rest of the website is also really good.
http://predpharm.com/# online order prednisone 10mg
prednisone daily
Hello there! This article could not be written any better! Reading through this post reminds me of my previous roommate! He always kept talking about this. I’ll forward this post to him. Pretty sure he will have a great read. Thank you for sharing!
I am so grateful for your blog.Really looking forward to read more.
As laws evolves, there was elevated focus to require ‘reasonable security’ for data administration.
Anand’s seconds for the match have been Surya Ganguly and Radosław Wojtaszek, who had helped him in 4 earlier World Championship matches; his major second Peter Heine Nielsen had been employed away earlier in the year by Carlsen, under settlement that he would not assist Carlsen throughout this match against Anand.
New York City, Philadelphia in 1777, and Charleston, South Carolina, were all major cities used to detain American prisoners of battle.
http://cytpharm.com/# Misoprostol 200 mg buy online
buy prednisone without prescription
Continue to the next web page to learn to make a wheel of measure.
Aw, this was a very good post. Spending some time and actual effort to make a very good article… but what can I say… I procrastinate a lot and don’t seem to get nearly anything done.
Certified solar electric property prices.
All you need is a working WiFi and you’re good!
Your mileage will vary, but I will bet it really works for you too.
Know-how also can help you to sell your occasion in a extra sensible way – by means of cost intermediaries like Wire card.
https://cytpharm.shop/# buy misoprostol over the counter
prednisone 40mg
The spread is the smallest amount that a stock can change in worth.
If it is often chilly within the month of the yr you plan to carry your wedding, you need to consider the kind of dress that will work best for you among the many out there.
Initially slated for demolition after the fair, the pavilion was bought for $5,000 and shipped back to Wisconsin, arriving in the small city of Neillsville in 1966.
Fundamental analysis of the price can involve the study of global supply and demand in a given time period.
The bank lends your money out to other people and businesses in the form of personal and business loans, charging the borrowers interest on what they owe until they pay back the money.
Final week in St.
https://predpharm.com/# Pred Pharm
order prednisone from canada
I really like it when individuals come together and share ideas. Great site, stick with it.
No one knows who first thought to mix PB with J, but it’s believed it began throughout World Battle II when American GIs mixed the 2 rations to make the peanut butter more palatable.
https://semapharm24.shop/# generic rybelsus tabs
prednisone 2.5 tablet
If you’re 50 years old, you can get a 20-year term life insurance policy that pays $50,000 for the same annual premium as a burial insurance policy that only covers $5,000 in funeral expenses.
You made some good points there. I checked on the web for additional information about the issue and found most people will go along with your views on this web site.
Walter Harry Martin, Technical Adviser, London North Eastern & Jap Regions, Central Land Board and Battle Injury Fee.
Bolivian ecosystems are linked with the traits of every river basin.
http://cytpharm.com/# Cyt Pharm
prednisone 4mg tab
Every investor will achieve better long-term risk-adjusted results by working with a true open architecture advisor.
Children are exposed to a variety of topics in school.
https://predpharm.shop/# PredPharm
prednisone 30 mg daily
Spot on with this write-up, I absolutely believe this web site needs much more attention. I’ll probably be returning to read through more, thanks for the info!
There are two main approaches to modeling the formation of inflation expectations.
One other factor that stands out as you tour the Lenox facility is that each one of these processes rely on the four elements.
By way of their scrupulous planning, they strive to ship something more than just a special event.
In the United States, the prime rate is traditionally established by the Wall Road Journal.
The funds must include line gadgets for contingency and return-to-SIG charges.
The network is based on the InterPlanetary File System (IFPS) protocol.
These words are very difficult to associate with the term investments.
http://predpharm.com/# cheap generic prednisone
how to get prednisone without a prescription
You made some good points there. I looked on the internet for the subject matter and found most individuals will approve with your blog.
The position of IFSC or Indian Financial Companies Code holds a special importance in the banking business.
Some of the key factors which have led to fall in nickel prices include increasing supply in the market and increasing availability of low cost nickel pig iron (NPI) in China, a substitute for pure nickel.
A fascinating discussion is definitely worth comment. I believe that you should write more on this topic, it might not be a taboo subject but generally people do not discuss these subjects. To the next! Cheers!!
I have a wild rock and roll facet to me that makes me wish to dance till dawn.
The government announced an additional reopening plan for the nation all through June, July and August, with the reopening of all inns from 2 June, out of doors hospitality, cinemas, swimming pools, gyms from 7 June, and indoor hospitality from 5 July.
http://kamapharm.com/# sildenafil oral jelly 100mg kamagra
average price of prednisone
They have a dealing desk and they use their currency inventory to trade against their clients.
If you find yourself stuck with rear drum brakes, versus the more effective disc brakes, you could possibly find a rear disc conversion package to your car.
As soon as you’ve linked your Fb account with a cellular quantity (you can do this in “account settings”) or put in the Fb app on your phone, you can take photographs and video (for those who phone allows), and post it directly out of your cellular machine to your Fb profile.
Finnerty, John (June 8, 2020).
These models are primarily based on analyzing as much data as will be gathered, then looking for non-random movements to make predictions.
https://semapharm24.com/# Sema Pharm 24
where can i buy prednisone online without a prescription
Once you have decided what function to include you need to design it, for that you use platforms like Drupal, Magento, and so on.
All other games were drawn, leaving the match at a 6-6 tie, so tie breaks decided the match.
I love it when people get together and share ideas. Great site, stick with it.
Other than the basic Cooper Convertible, all models have a typical six-velocity guide transmission; a 6-pace automatic transmission is optional, replacing the CVT system.
Introduced in 2004, this truck got a major overhaul in 2015.
https://dappharm.shop/# DapPharm
prednisone cream over the counter
The card is then secured with a single screw.
I like reading an article that will make men and women think. Also, many thanks for allowing for me to comment.
The Church has a variety of treasures that have spiritual or religious value rather than financial worth; these are housed in treasuries at most cathedrals.
The Chigorin Defense is a chess opening named for nineteenth-century Russian master Mikhail Chigorin.
Paul Waldie (November 10, 2006), “Hedge funds strive hand at charity fundraising”, The Globe and Mail, p.
In the event you print steadily, although, take the time to seek out printers with increased web page yields; the associated fee savings will likely be increased, too.
Much the same as knowing a companion well, figuring out how to peruse your extraordinary business sector can pay profits.
She has had that smile for almost a year straight,’ she mentioned, based on the brand new report in Folks magazine.
In easy words we can say that a wedding decorator is a one who visualizes your wedding ceremony in accordance with your wants and calls for.
It’s hard to find knowledgeable people in this particular topic, but you seem like you know what you’re talking about! Thanks
apartments in tucson apartments in farmington nm waverly place apartments
https://cytpharm.shop/# Cyt Pharm
prednisone 5 50mg tablet price
The Ram truck was embellished with a hood ornament reminiscent of the same ornament found on Dodges of the early years.
https://kamapharm.com/# Kamagra 100mg price
prednisone 50 mg price
Minutes of the provincial council of Pennsylvania, from the organization to the termination of the proprietary authorities.
If you cannot discover a solution to your tax questions right here, simply scrawl them throughout the highest of your 1040 in pink ink and ALL CAPS.
Use a timer or clock, because you do not need to depart the chemicals in your pores and skin too long.
https://dappharm.shop/# buy priligy
prednisone pill 10 mg
Partaking in a family breakfast or brunch generally is a weekend favourite or a weekday deal with, but internet hosting one isn’t all the time a piece of cake, pancake or not.
No matter what your strategy, it’s a must to balance energy with diplomacy, making alliances the place they’re to your advantage.
Another major reason for the implementation of the 1934 Act was to regulate insider securities transactions to prevent fraud and unfair manipulation of securities exchanges.
Each gamers agreed to a draw after 24 strikes were played.
11) Going petite signifies that the buyer and vendor are wondering if he/she can improve a revenue from falling rates.
Rapper Jay-Z mentions Bentleys in a number of of his songs and drives around in them as effectively.
Wealth. Life Insurance. How the Wealthy Use Life Insurance as a Tax-Free Personal Bank to Supercharge Their Savings.
There is definately a lot to find out about this subject. I like all of the points you’ve made.
http://farmaprodotti.com/# farmacia online senza ricetta
acquistare farmaci senza ricetta
Retrieved eleven September 2012.
Physical Well being: Some imagine Pure Irani Firoza can improve eyesight and general health.
These are in fact impressive ideas in about blogging. You have touched some nice factors here. Any way keep up wrinting.
Weiner, Eric (8 April 2015).
Flagstaff lies near the southwestern edge of the Colorado Plateau and within the San Francisco volcanic area, alongside the western facet of the largest contiguous ponderosa pine forest within the continental United States.
http://farmaprodotti.com/# farmacia online
acquistare farmaci senza ricetta
Moreover, extreme weather events usually end in meals insecurity, as crops are destroyed and access to recent food becomes limited.
It’s hard to find experienced people for this subject, however, you seem likeyou know what you’re talking about! Thanks
A range of periods rather than one fixed period is needed to capture business cycle fluctuations, which may be done by using a random or irregular source as in an econometric or statistical framework.
http://farmasilditaly.com/# viagra online spedizione gratuita
farmacie online autorizzate elenco
http://farmasilditaly.com/# gel per erezione in farmacia
Farmacia online piГ№ conveniente
The ultimate mixture of pearls, stones and gems put together beautifully in Rakhi is the selection of every next sister.
The level of the water supply the artesian nicely is drawing from must sit above the uppermost layer of the aquifer.
In addition to the fact that two-liters are the far cheaper (and greener) choice, they’re also simpler to clean up.
If used, the finder ought to do no more than make introductions of investors to the issuer, and should solely be compensated by a flat charge which isn’t primarily based upon the sale of securities.
The centre mild depicts men, ladies and kids, lay and religious, monarchs and saints, ascending to the city of God, “Jerusalem Ecce Ascendimus”, (Behold we go as much as Jerusalem).
CC: I’ve been singing since I was born, based on my mom.
Ahaa, its good dialogue regarding this piece of writing here at this blog, I have read all that, so at thistime me also commenting at this place.
So, these signals are good for novice traders or beginners.
One type, the more traditional of the two, is known as a home equity loan or second mortgage.
Thanks a lot for the article.Much thanks again. Really Cool.
Your style is unique compared to other people I have read stuff from. I appreciate you for posting when you’ve got the opportunity, Guess I will just bookmark this site.
After looking over a handful of the articles on your site, I honestly like your way of writing a blog. I book-marked it to my bookmark site list and will be checking back soon. Please visit my website as well and tell me what you think.
ciprofloxacin coverage uti ciprofloxacin pill identifier ciprofloxacin hydrochloride gas
The Mekong River and the city of Luang Prabang are must-sees.
Hello there! This article could not be written any better! Looking at this article reminds me of my previous roommate! He constantly kept preaching about this. I most certainly will send this information to him. Pretty sure he’ll have a very good read. Many thanks for sharing!
comprare farmaci online con ricetta Farm Tadal Italy acquistare farmaci senza ricetta
I really enjoyed reading this! Your writing style is engaging, and the content is valuable. Excited to see more from you!
Security measures ensure a safe environment.: taya365 – taya365 com login
Having read this I thought it was extremely enlightening. I appreciate you taking the time and effort to put this information together. I once again find myself personally spending a significant amount of time both reading and posting comments. But so what, it was still worthwhile!
п»їCasinos in the Philippines are highly popular. http://phmacao.life/# Slot machines attract players with big jackpots.
https://taya365.art/# Responsible gaming initiatives are promoted actively.
Gambling regulations are strictly enforced in casinos.
La mГєsica acompaГ±a la experiencia de juego.: jugabet.xyz – jugabet chile
Los jugadores pueden disfrutar desde casa.: win chile – win chile
Right here is the perfect site for anybody who wishes to understand this topic. You realize so much its almost hard to argue with you (not that I personally would want to…HaHa). You certainly put a new spin on a topic which has been written about for years. Wonderful stuff, just wonderful.
jugabet chile jugabet п»їLos casinos en Chile son muy populares.
http://phmacao.life/# Gaming regulations are overseen by PAGCOR.
The casino experience is memorable and unique.
Responsible gaming initiatives are promoted actively. https://taya365.art/# Gaming regulations are overseen by PAGCOR.
Casino visits are a popular tourist attraction.: taya365 – taya365.art
Gaming regulations are overseen by PAGCOR.: phtaya casino – phtaya login
https://jugabet.xyz/# Los bonos de bienvenida son generosos.
Entertainment shows are common in casinos.
Game rules can vary between casinos. http://taya777.icu/# Players often share tips and strategies.
Casino visits are a popular tourist attraction.: taya365 com login – taya365
http://taya365.art/# Game rules can vary between casinos.
Promotions are advertised through social media channels.
taya777 register login taya777.icu The Philippines has several world-class integrated resorts.
Los jugadores pueden disfrutar desde casa.: winchile – winchile.pro
Players enjoy a variety of table games. http://phmacao.life/# п»їCasinos in the Philippines are highly popular.
http://taya777.icu/# Most casinos offer convenient transportation options.
Gaming regulations are overseen by PAGCOR.
Las mГЎquinas tienen diferentes niveles de apuesta.: jugabet.xyz – jugabet
Slot machines feature various exciting themes.: taya365 com login – taya365 com login
https://phmacao.life/# Many casinos host charity events and fundraisers.
Players must be at least 21 years old.
Players must be at least 21 years old. https://taya777.icu/# Slot tournaments create friendly competitions among players.
I absolutely love your blog.. Pleasant colors & theme. Did you make this site yourself? Please reply back as I’m wanting to create my own website and want to learn where you got this from or just what the theme is called. Thanks!
taya777 taya777 register login Players can enjoy high-stakes betting options.
Game rules can vary between casinos.: taya365 login – taya365.art
https://phmacao.life/# Casino promotions draw in new players frequently.
Players often share tips and strategies.
The thrill of winning keeps players engaged. https://winchile.pro/# Las apuestas mГnimas son accesibles para todos.
After I originally left a comment I appear to have clicked on the -Notify me when new comments are added- checkbox and now whenever a comment is added I receive 4 emails with the same comment. Is there an easy method you are able to remove me from that service? Kudos.
The Philippines has several world-class integrated resorts.: taya777.icu – taya777 register login
https://taya365.art/# Gambling regulations are strictly enforced in casinos.
Poker rooms host exciting tournaments regularly.
Many casinos offer luxurious amenities and services.: taya777 login – taya777 login
taya365 com login taya365.art Visitors come from around the world to play.
The poker community is very active here. http://winchile.pro/# La pasiГіn por el juego une a personas.
https://taya777.icu/# Some casinos have luxurious spa facilities.
Responsible gaming initiatives are promoted actively.
You ought to be a part of a contest for one of the finest sites on the net. I’m going to highly recommend this blog!
Security measures ensure a safe environment.: phmacao club – phmacao com
Players can enjoy high-stakes betting options.: taya365 – taya365
The thrill of winning keeps players engaged. http://winchile.pro/# Los casinos reciben turistas de todo el mundo.
https://phtaya.tech/# Live music events often accompany gaming nights.
Many casinos offer luxurious amenities and services.
The remainder of the suite carries through this clear-lined, elegantly easy design.
The casino experience is memorable and unique.: taya777 app – taya777 login
Manila is home to many large casinos.: taya365.art – taya365 login
winchile winchile.pro La pasiГіn por el juego une a personas.
http://taya365.art/# The thrill of winning keeps players engaged.
Live music events often accompany gaming nights.
The Philippines offers a rich gaming culture. https://winchile.pro/# п»їLos casinos en Chile son muy populares.
La mayorГa acepta monedas locales y extranjeras.: jugabet casino – jugabet casino
п»їLos casinos en Chile son muy populares.: jugabet – jugabet
http://taya777.icu/# Gambling regulations are strictly enforced in casinos.
Manila is home to many large casinos.
The XK120 holds the distinction for being the first overseas-made automotive to win a NASCAR race when it scored a highway-course victory in New Jersey in 1954.
When there’s another meals drive at work or you will have an opportunity to volunteer — once more, keep open to the thought of sharing.
Slot machines feature various exciting themes. https://winchile.pro/# Los jugadores deben conocer las reglas.
It should be user friendly and many people should use it easily.
A pleasant motel might have an outside swimming pool or sizzling tub on par with one you’d discover at bargain lodges.
Slot tournaments create friendly competitions among players.: phmacao.life – phmacao club
http://taya777.icu/# Slot machines attract players with big jackpots.
Casinos offer delicious dining options on-site.
jugabet chile jugabet.xyz La mГєsica acompaГ±a la experiencia de juego.
If you feel you will have been cheated, discover out what you can do about it.
One is bare-headed and wears an elegant gown of green and white strips, with lace trim; the opposite wears a bonnet, a big black lace mantelet and a pretty layered pink and white checked dress.
Hay casinos en Santiago y ViГ±a del Mar.: jugabet.xyz – jugabet
Common Orlando Resort. “Halloween Horror Nights at Universal Orlando Florida”.
I really like it whenever people come together and share ideas. Great website, stick with it.
http://winchile.pro/# Los jugadores pueden disfrutar desde casa.
п»їCasinos in the Philippines are highly popular.
Ideally a person would develop into unaware of the interplay system completely.
Resorts provide both gaming and relaxation options.: phmacao com login – phmacao casino
I used to be able to find good information from your blog posts.
Los casinos reciben turistas de todo el mundo.: jugabet.xyz – jugabet.xyz
I remember one among the primary songs I discovered on piano was the bass part to Cow Cow Boogie by The Andrews Sisters – I must have been about five or so.
As the game goes on, access to cities turns into more and dearer, and finally players will probably be blocked out of cities completely.
https://phmacao.life/# Casinos often host special holiday promotions.
Slot tournaments create friendly competitions among players.
If there’s one thing baby boomers are accustomed to, it’s getting attention as a group.
Las tragamonedas ofrecen grandes premios.: winchile.pro – win chile
For it to happen, they target for small investors which can be easily located in the stock market.
taya777 [url=http://taya777.icu/#]taya777 app[/url] The Philippines has several world-class integrated resorts.
The thrill of winning keeps players engaged.: taya365.art – taya365 com login
Jonathan then makes use of computer-generated imagery for example his imagined vision for the houses after vital renovations.
https://taya777.icu/# Many casinos offer luxurious amenities and services.
Live dealer games enhance the casino experience.
This is not the same as the volume of the song, which is ultimately controlled by the listener.
経営者さま
突然のご連絡失礼いたします。
「送るモン」営業代行サービスを提供しております
WebExpertの中村と申します。
貴社のビジネスチャンスを最大化するお手伝いをしたいという想いからご連絡差し上げました。
■「送るモン」とは?
「送るモン」は、これまでの営業活動を効率化し、より多くの企業と接点を持つことを可能にする新しいサービスです。
以下の特長で、営業活動の負担を大幅に軽減します:
・初期費用ゼロ&月額料金でアポ獲得活動をします!
主にお問い合わせフォームへの営業と、メール営業を行い、1ヶ月に最大120万件の営業メールを送信します。
一般的な送信代行の1通5~20円と比べ、10万通を50万円以上で送るコストを月額料金(98,000円)のみで実現。
・全てお任せ!リスト作成から送信・分析まで完全代行
クライアント様は、アポイントに集中するだけ!待っているだけでOKです。
・送信上限なし!最大120万通まで送ることができます。
現在フォーム営業やメール営業でコストをかけている方、
もっと大量に送信したいがコストが気になっている方、
送信やリスト作成の手間を全て丸投げしたい方
に最適です!
全て込みで98,000円で代行します!
■実績で証明された効果
以下の実例をご紹介します:
株式会社T様
1ヶ月で43件の商談獲得(2024年8月実績)
中国SNSマーケティング支援を売り込む営業メールで成果を実現。営業文には「無料PR動画制作」という明確なメリットを打ち出しました。
株式会社PC様
90万通送信で102件のアポイントを1ヶ月で獲得!(2024年11月実績)
補助金コンサルという競合が多い分野でも、大量送信と本文改善を繰り返し成功。
■こんな方におすすめです
営業リソースを削減したい
多くの商談機会を創出したい
費用対効果を最大化したい
「お問い合わせフォーム営業をやりたいが、手間や時間がかかりすぎて挫折した」というお悩みをお持ちの方にピッタリのサービスです。
ご興味をお持ちいただけましたら、詳細についてお話しさせていただく機会を頂けますと幸いです。
以下のURLからご都合の良い日時でオンラインミーティングのご予約を頂けますと幸いです。
https://timerex.net/s/ppkoya/4c1e4898
貴社のさらなる発展に向けて、ぜひお力になれれば幸いです。
どうぞよろしくお願いいたします。
経営者さま
突然のご連絡失礼いたします。
「送るモン」営業代行サービスを提供しております
WebExpertの中村と申します。
貴社のビジネスチャンスを最大化するお手伝いをしたいという想いからご連絡差し上げました。
■「送るモン」とは?
「送るモン」は、これまでの営業活動を効率化し、より多くの企業と接点を持つことを可能にする新しいサービスです。
以下の特長で、営業活動の負担を大幅に軽減します:
・初期費用ゼロ&月額料金でアポ獲得活動をします!
主にお問い合わせフォームへの営業と、メール営業を行い、1ヶ月に最大120万件の営業メールを送信します。
一般的な送信代行の1通5~20円と比べ、10万通を50万円以上で送るコストを月額料金(98,000円)のみで実現。
・全てお任せ!リスト作成から送信・分析まで完全代行
クライアント様は、アポイントに集中するだけ!待っているだけでOKです。
・送信上限なし!最大120万通まで送ることができます。
現在フォーム営業やメール営業でコストをかけている方、
もっと大量に送信したいがコストが気になっている方、
送信やリスト作成の手間を全て丸投げしたい方
に最適です!
全て込みで98,000円で代行します!
■実績で証明された効果
以下の実例をご紹介します:
株式会社T様
1ヶ月で43件の商談獲得(2024年8月実績)
中国SNSマーケティング支援を売り込む営業メールで成果を実現。営業文には「無料PR動画制作」という明確なメリットを打ち出しました。
株式会社PC様
90万通送信で102件のアポイントを1ヶ月で獲得!(2024年11月実績)
補助金コンサルという競合が多い分野でも、大量送信と本文改善を繰り返し成功。
■こんな方におすすめです
営業リソースを削減したい
多くの商談機会を創出したい
費用対効果を最大化したい
「お問い合わせフォーム営業をやりたいが、手間や時間がかかりすぎて挫折した」というお悩みをお持ちの方にピッタリのサービスです。
ご興味をお持ちいただけましたら、詳細についてお話しさせていただく機会を頂けますと幸いです。
以下のURLからご都合の良い日時でオンラインミーティングのご予約を頂けますと幸いです。
https://timerex.net/s/ppkoya/4c1e4898
貴社のさらなる発展に向けて、ぜひお力になれれば幸いです。
どうぞよろしくお願いいたします。
Property prices depend a lot on the demand and supply situation in the market.
Las promociones de fin de semana son populares.: winchile – winchile casino
This page was last edited on 30 April 2024, at 18:49 (UTC).
API shares at the moment have a brief curiosity ratio of 1.0.
Also, uric acid, a product of DNA metabolism, has grow to be increasingly recognized as an vital antioxidant.
http://winchile.pro/# La variedad de juegos es impresionante.
A variety of gaming options cater to everyone.
The casino experience is memorable and unique.: phtaya casino – phtaya casino
The rough, onerous idle swells up and out from under the automobile, ricochets off different automobiles, and rams into the ears of the driver, the spectators.
Nie and his six sisters grew up in a house above the family enterprise, and he and his wife bought the funeral home from Nie’s mother and father in 2000.
Persall, Steve (October 25, 1991).
You may observe Tricia Gosingtian-Gabunada on her Instagram account right here.
Isotta Fraschini competed with Rolls-Royce and Hispano-Suiza in the super-luxury market.
After the Japanese defeat, the “occupation forex,” or “invasion cash,” grew to become nugatory.
The Philippines has a vibrant nightlife scene.: taya365 login – taya365 login
phmacao phmacao Players enjoy both fun and excitement in casinos.
http://phmacao.life/# Slot machines feature various exciting themes.
Poker rooms host exciting tournaments regularly.
Maybe you’re retreating to the Western bathrooms, the air conditioning, the acquainted meals or a spot where you may shirk the native language and simply say “Large Mac.” Maybe you’re working around the clock in a rustic that siestas or dashing around a country and a people who transfer more slowly.
On March 23, 2020, Governor Wolf issued further stay at dwelling orders for seven counties: Allegheny, Bucks, Chester, Delaware, Montgomery, Monroe, and a redundant order for Philadelphia County, to go into effect at 8:00 pm the same day.
Many casinos offer luxurious amenities and services.: phtaya.tech – phtaya
Lacks modern features and functionalities.
Loyalty programs reward regular customers generously.: taya365.art – taya365 login
https://phtaya.tech/# Players enjoy both fun and excitement in casinos.
Cashless gaming options are becoming popular.
I really enjoyed reading this! Your writing style is engaging, and the content is valuable. Excited to see more from you!
Resorts provide both gaming and relaxation options. http://taya777.icu/# Players must be at least 21 years old.
The casino industry supports local economies significantly.: taya365.art – taya365.art
http://winchile.pro/# Las aplicaciones mГіviles permiten jugar en cualquier lugar.
Manila is home to many large casinos.
Pretty! This has been a really wonderful post. Many thanks for providing this info.
The casino scene is constantly evolving.: phtaya – phtaya
phtaya login phtaya Slot tournaments create friendly competitions among players.
They sell over $4.5 billion of travel every year and have raised over $600 million of private capital.
They had the last laugh, however, as it is now a very successful and much-loved concert venue, where hundreds of major stars have played.
March 4, 2016: Agon announce that only authorized broadcasters will likely be allowed to retransmit strikes from the Candidates and ensuing World Championship.
http://phtaya.tech/# Many casinos host charity events and fundraisers.
Players often share tips and strategies.
Many casinos have beautiful ocean views.: taya365 com login – taya365
Way cool! Some extremely valid points! I appreciate you writing this post plus the rest of the site is also really good.
Due to the big proportion of taxes within the PA’s finances collected by Israel, the PA is vulnerable to unilateral suspensions by Israel of transfers of clearance revenue.
The casino experience is memorable and unique.: taya365.art – taya365 com login
On his return to England in 1872, he commissioned architect Basil Champneys to design a brand new household dwelling in Department Hill, Hampstead, which was named “Oak Tree Home”.
Choosing brokerage: While selecting a brokerage firm for intraday trading you must see their accessible markets, features of the trading software, their market data, information feeds and their commission fees.
White’s queen is way outmatched by Black’s pieces, which dominate the board and will quickly overrun White’s place.
When the sun is shining, we tend to feel more energized and happier.
I have to thank you for the efforts you’ve put in writing this blog. I am hoping to view the same high-grade blog posts from you later on as well. In fact, your creative writing abilities has inspired me to get my own, personal blog now 😉
https://taya365.art/# The casino atmosphere is thrilling and energetic.
A variety of gaming options cater to everyone.
Whoa! This blog looks exactly like my old one! It’s on a entirely different topic but it has pretty much the same layout and design. Superb choice of colors! stickningar i vГ¤nstra brГ¶stet
Casino visits are a popular tourist attraction. https://taya365.art/# The Philippines has a vibrant nightlife scene.
Hey, thanks for the blog.Really thank you! Really Great.
Slot machines attract players with big jackpots.: phtaya login – phtaya casino
winchile casino winchile.pro Las mГЎquinas tragamonedas tienen temГЎticas diversas.
Los jugadores deben conocer las reglas.: winchile – winchile
He was preceded in demise by his sister, Edna McKinnon Lambright; brothers, Theodore and Andrew Schweinle; grandsons, Martin Thomas Marty Schweinle and Parmer Albert Bert Schweinle.
https://phtaya.tech/# Players enjoy a variety of table games.
The poker community is very active here.
These accessories normally are available in sets and are the most affordable objects accessible.
When you are seeking additional elbow room for a gathering of the varsity committee, a streamlined maple espresso table on casters is simple to roll away.
Los torneos de poker generan gran interГ©s.: winchile.pro – win chile
Live dealer games enhance the casino experience.: phtaya.tech – phtaya.tech
https://phmacao.life/# The casino industry supports local economies significantly.
Visitors come from around the world to play.
Visitors come from around the world to play.: phtaya casino – phtaya.tech
jugabet casino jugabet casino La Г©tica del juego es esencial.
Many casinos offer luxurious amenities and services.: phmacao com login – phmacao
http://phtaya.tech/# The casino experience is memorable and unique.
Slot machines attract players with big jackpots.
discount drug mart pharmacy: drug mart – discount drug mart
Spot on with this write-up, I actually believe this amazing site needs much more attention. I’ll probably be returning to see more, thanks for the information.
Well-written and insightful! Your points are spot on, and I found the information very useful. Keep up the great work!
best canadian pharmacy no prescription https://xxlmexicanpharm.com/# mexican mail order pharmacies
vipps approved canadian online pharmacy: easy canadian pharm – easy canadian pharm
77 canadian pharmacy: easy canadian pharm – canadian pharmacy king
canadian pharmacies not requiring prescription https://familypharmacy.company/# online pharmacy delivery usa
drug mart discount drug pharmacy drugmart
canadian pharmacy no prescription needed https://familypharmacy.company/# Best online pharmacy
canada cloud pharmacy: canadian pharmacy 24h com – reliable canadian online pharmacy
xxl mexican pharm: pharmacies in mexico that ship to usa – reputable mexican pharmacies online
canadian pharmacy discount coupon https://familypharmacy.company/# Cheapest online pharmacy
cheapest pharmacy for prescriptions without insurance https://discountdrugmart.pro/# discount drugs
pharmacy without prescription http://discountdrugmart.pro/# drugmart
online pharmacy delivery usa: Online pharmacy USA – no prescription needed pharmacy
best canadian pharmacy easy canadian pharm easy canadian pharm
pharmacy no prescription required: Cheapest online pharmacy – Online pharmacy USA
Great article! I learned a lot from your detailed explanation. Looking forward to more informative content like this!
Introducing to you the most prestigious online entertainment address today. Visit now to experience now!
I was very happy to discover this great site. I wanted to thank you for ones time due to this wonderful read!! I definitely appreciated every bit of it and i also have you book-marked to look at new things on your site.
Introducing to you the most prestigious online entertainment address today. Visit now to experience now!
canadian pharmacy coupon code http://familypharmacy.company/# Best online pharmacy
discount drug pharmacy: discount drug mart – discount drug mart
canadian neighbor pharmacy: canadian pharmacy no scripts – legitimate canadian online pharmacies
I used to be able to find good info from your articles.
Introducing to you the most prestigious online entertainment address today. Visit now to experience now!
online pharmacy no prescription needed https://easycanadianpharm.com/# is canadian pharmacy legit
cheapest pharmacy for prescriptions without insurance https://xxlmexicanpharm.shop/# xxl mexican pharm
family pharmacy Cheapest online pharmacy canadian prescription pharmacy
Mega India Pharm: Mega India Pharm – Mega India Pharm
Cheapest online pharmacy: Cheapest online pharmacy – Online pharmacy USA
It’s hard to come by well-informed people in this particular subject, but you seem like you know what you’re talking about! Thanks
online pharmacy discount code https://xxlmexicanpharm.com/# xxl mexican pharm
canada pharmacy coupon https://megaindiapharm.com/# best india pharmacy
discount drug mart pharmacy: drug mart – canada pharmacy not requiring prescription
canada pharmacy coupon https://megaindiapharm.com/# indian pharmacy online
xxl mexican pharm: buying from online mexican pharmacy – xxl mexican pharm
MegaIndiaPharm mail order pharmacy india Mega India Pharm
pharmacy no prescription required http://xxlmexicanpharm.com/# buying from online mexican pharmacy
mail order prescription drugs from canada http://xxlmexicanpharm.com/# xxl mexican pharm
canadian pharmacy no scripts: easy canadian pharm – canadian pharmacy world reviews
Pretty! This has been an extremely wonderful article. Thanks for providing these details.
online pharmacy discount code: Cheapest online pharmacy – canadian pharmacy no prescription needed
online pharmacy non prescription drugs https://discountdrugmart.pro/# drugmart
uk pharmacy no prescription https://discountdrugmart.pro/# discount drug mart
Online medicine order: MegaIndiaPharm – MegaIndiaPharm
I’m extremely impressed with your writing skills as well as with the layout on your blog. Is this a paid theme or did you modify it yourself? Anyway keep up the nice quality writing, it is rare to see a nice blog like this one these days..
international pharmacy no prescription https://discountdrugmart.pro/# discount drugs
reliable canadian pharmacy: easy canadian pharm – easy canadian pharm
I do agree with all the ideas you’ve presented in your post. They’re really convincing and will certainly work. Still, the posts are very short for novices. Could you please extend them a little from next time? Thanks for the post.
xxl mexican pharm mexican rx online pharmacies in mexico that ship to usa
canadian pharmacies not requiring prescription https://megaindiapharm.com/# top 10 pharmacies in india
MegaIndiaPharm: buy prescription drugs from india – MegaIndiaPharm
canadian online pharmacy no prescription https://easycanadianpharm.shop/# easy canadian pharm
Greetings! Very useful advice in this particular post!It is the little changes that make the greatest changes.Thanks a lot for sharing!
sex nhật hiếp dâm trẻ em ấu dâm buôn bán vũ khí ma túy bán súng sextoy chơi đĩ sex bạo lực sex học đường tội phạm tình dục chơi les đĩ đực người mẫu bán dâm
easy canadian pharm: canadian pharmacy no scripts – easy canadian pharm
online canadian pharmacy coupon http://discountdrugmart.pro/# drug mart
no prescription pharmacy paypal https://easycanadianpharm.com/# legitimate canadian online pharmacies
online pharmacy delivery usa: Best online pharmacy – family pharmacy
easy canadian pharm easy canadian pharm thecanadianpharmacy
pharmacy online 365 discount code https://xxlmexicanpharm.com/# mexican border pharmacies shipping to usa
top online pharmacy india: indian pharmacy paypal – MegaIndiaPharm
international pharmacy no prescription http://megaindiapharm.com/# MegaIndiaPharm
easy canadian pharm: canadian pharmacy no scripts – canadian pharmacy no rx needed
pharmacy coupons http://megaindiapharm.com/# Mega India Pharm
drug mart: discount drug pharmacy – cheap pharmacy no prescription
reputable online pharmacy no prescription https://easycanadianpharm.com/# canada drug pharmacy
Online pharmacy USA: Online pharmacy USA – Cheapest online pharmacy
non prescription medicine pharmacy http://easycanadianpharm.com/# canadian pharmacy 24 com
Really informative blog.Much thanks again. Really Great.
xxl mexican pharm pharmacies in mexico that ship to usa buying from online mexican pharmacy
Mega India Pharm: MegaIndiaPharm – MegaIndiaPharm
Good job!
canadian pharmacy world coupon code http://familypharmacy.company/# Best online pharmacy
canadian pharmacy without prescription http://discountdrugmart.pro/# drug mart
Best online pharmacy: Online pharmacy USA – Online pharmacy USA
pharmacy without prescription https://easycanadianpharm.shop/# easy canadian pharm
onlinecanadianpharmacy: easy canadian pharm – pharmacy rx world canada
canadian pharmacy coupon code https://megaindiapharm.com/# best online pharmacy india
easy canadian pharm: buying drugs from canada – canadian pharmacy phone number
canadian discount pharmacy reddit canadian pharmacy legal to buy prescription drugs from canada
UID_59407105###
berita dana x twitter viral berita dana desa ada disini !
If you see any unusual icons, these are clues to any variety of problematic issues you may encounter.
canadian pharmacy no prescription needed https://discountdrugmart.pro/# discount drug mart
Hello there! I simply would like to offer you a big thumbs up for the excellent info you have right here on this post. I will be coming back to your site for more soon.
UID_72942561###
Berita Hot! 🔥🔥 Isa Rachmatarwata Tersangka Kasus Jiwasraya Buntut kerugian negara hingga 16,8 Triliun! 😲😲
xxl mexican pharm: medication from mexico pharmacy – xxl mexican pharm
MegaIndiaPharm: Mega India Pharm – mail order pharmacy india
promo code for canadian pharmacy meds http://easycanadianpharm.com/# easy canadian pharm
Hello There. I found your blog using msn. This is an extremely well written article. I will be sure to bookmark it and return to read more of your useful information. Thanks for the post. I’ll definitely return.
canadian pharmacy discount coupon https://familypharmacy.company/# online pharmacy delivery usa
UID_53550706###
Berita terbaru! 🔥 Isa Rachmatarwata Ditahan Kejagung dalam kasus Jiwasraya. 🚔👮♂️
Hi, I do think this is a great web site. I stumbledupon it 😉 I will revisit yet again since I saved as a favorite it. Money and freedom is the greatest way to change, may you be rich and continue to help other people.
Online pharmacy USA: family pharmacy – family pharmacy
MegaIndiaPharm: MegaIndiaPharm – Mega India Pharm
canada drugs coupon code https://easycanadianpharm.com/# canadian online pharmacy
canadian pharmacy world coupon https://discountdrugmart.pro/# discount drug pharmacy
п»їbest mexican online pharmacies mexican drugstore online mexico pharmacies prescription drugs
UID_57092237###
Berita gembira! 🎉 Pasokan Gas 3 Kg di Kramat Jati Kembali Normal 🎊 Siap-siap belanja gas, ya! 💪🔥
This was a great read! Your insights are truly helpful and make complex topics easy to understand. Looking forward to more!
This post is very helpful! I appreciate the effort you put into making it clear and easy to understand. Thanks for sharing!
canadian pharmacy no prescription https://xxlmexicanpharm.com/# pharmacies in mexico that ship to usa
family pharmacy: Online pharmacy USA – Online pharmacy USA
canadian pharmacy world coupon https://megaindiapharm.com/# online pharmacy india
discount drug pharmacy: discount drug mart pharmacy – discount drug pharmacy
UID_72339950###
Heboh! 📣🔥 Unjuk Rasa di Polda Jatim 📢 Menuduh Jokowi Terlibat Korupsi! 😱🔍
rxpharmacycoupons http://xxlmexicanpharm.com/# mexican rx online
Spot on with this write-up, I really believe this website needs a great deal more attention. I’ll probably be back again to read through more, thanks for the advice!
Si vous cherchez une plateforme fiable pour vos paris et vos jeux de casino, alors 888starz Casino mobile est fait pour vous. Inscrivez-vous en quelques clics, profitez de bonus exclusifs et plongez dans un univers de jeux immersif avec des fonctionnalites adaptees aux joueurs exigeants !
UID_27764099###
Ini yang di ganti >>> “Bingung Kenapa 😕❓” Federasi Sepak Bola Pakistan Disanksi FIFA “Baca Penyebabnya Disini! 🧐🔍”
cheap pharmacy no prescription https://discountdrugmart.pro/# discount drug pharmacy
canadian pharmacy drugs online: easy canadian pharm – easy canadian pharm
п»їbest mexican online pharmacies xxl mexican pharm xxl mexican pharm
UID_27764099###
Ini yang di ganti >>> “Bingung Kenapa 😕❓” Federasi Sepak Bola Pakistan Disanksi FIFA “Baca Penyebabnya Disini! 🧐🔍”
UID_27764099###
Ini yang di ganti >>> “Bingung Kenapa 😕❓” Federasi Sepak Bola Pakistan Disanksi FIFA “Baca Penyebabnya Disini! 🧐🔍”
online pharmacy prescription https://megaindiapharm.com/# best online pharmacy india
UID_74743238###
Ini dia! 🎉🎉 ASN BKN Ubah Pola Kerja yang baru dan efisien! 🎉🎉.
Very informative article post.Thanks Again.
UID_74743238###
Ini dia! 🎉🎉 ASN BKN Ubah Pola Kerja yang baru dan efisien! 🎉🎉.
Oh my goodness! Awesome article dude! Many thanks, However I am having problems with your RSS. I don’t understand why I can’t join it. Is there anyone else having similar RSS problems? Anybody who knows the solution will you kindly respond? Thanx!!
online pharmacy without prescription http://discountdrugmart.pro/# discount drugs
Your information isn’t all the time immune to look and seizure by native authorities entities.
buying from online mexican pharmacy: xxl mexican pharm – buying prescription drugs in mexico
Les jeux de casino en ligne sont encore plus accessibles grace a https://cluny.fr/pgs/888starz-casino-telecharger.html. Avec une large gamme de jeux et des promotions attrayantes, cette plateforme offre une experience immersive et des options de jeu variees adaptees a tous les profils de joueurs. Inscrivez-vous et profitez d’avantages exclusifs !
non prescription medicine pharmacy https://easycanadianpharm.com/# canada drugs reviews
I went over this website and I believe you have a lot of great info , saved to my bookmarks (:.
canadian online pharmacy no prescription https://easycanadianpharm.shop/# best canadian online pharmacy
Hey there! I just want to give you a huge thumbs up for your excellent info you have right here on this post. I am coming back to your website for more soon.
drug mart: drug mart – drug mart
best canadian pharmacy no prescription https://easycanadianpharm.shop/# easy canadian pharm
easy canadian pharm easy canadian pharm easy canadian pharm
no prescription needed pharmacy https://familypharmacy.company/# Cheapest online pharmacy
canadian pharmacy without prescription https://easycanadianpharm.com/# canadian neighbor pharmacy
xxl mexican pharm: xxl mexican pharm – xxl mexican pharm
I regard something genuinely special in this website .
UID_83344528###
Inilah 🎉🎉 Pupuk Inovatif Kebun Riset Kujang yang bikin Wamen BUMN bangga! 💪🏻🇮🇩
Slot klasik tetap menjadi favorit banyak orang http://preman69.tech/# Slot modern memiliki grafik yang mengesankan
Permainan slot mudah dipahami dan menyenangkan http://slot88.company/# Keseruan bermain slot selalu menggoda para pemain
http://slot88.company/# Pemain sering berbagi tips untuk menang
It’s an remarkable piece of writing for all the internet visitors; they will obtain benefit from it I am sure.
Slot dengan tema film terkenal menarik banyak perhatian: slot demo gratis – demo slot pg
slot88 slot 88 Pemain sering mencoba berbagai jenis slot
UID_83344528###
Inilah 🎉🎉 Pupuk Inovatif Kebun Riset Kujang yang bikin Wamen BUMN bangga! 💪🏻🇮🇩
There may be noticeably a bundle to learn about this. I assume you made certain nice factors in features also.
UID_21891068###
Takjub 😮 dengan fenomena serbu gas? Yuk, baca Warung Tatang Diserbu Warga dan temukan faktanya! 🕵️♀️👀
Kasino menyediakan layanan pelanggan yang baik http://garuda888.top/# Mesin slot menawarkan berbagai tema menarik
fantastic points altogether, you simply gained a new reader. What would you recommend about your publish that you simply made a few days in the past? Any sure?
Kasino memastikan keamanan para pemain dengan baik https://preman69.tech/# Banyak pemain menikmati bermain slot secara online
https://garuda888.top/# Slot dengan fitur interaktif semakin banyak tersedia
Kasino menyediakan layanan pelanggan yang baik https://garuda888.top/# Slot dengan bonus putaran gratis sangat populer
https://slotdemo.auction/# Kasino di Jakarta memiliki berbagai pilihan permainan
BonaSlot BonaSlot Banyak kasino memiliki promosi untuk slot
Mesin slot menawarkan berbagai tema menarik: preman69.tech – preman69
UID_21891068###
Takjub 😮 dengan fenomena serbu gas? Yuk, baca Warung Tatang Diserbu Warga dan temukan faktanya! 🕵️♀️👀
Banyak pemain berusaha untuk mendapatkan jackpot https://bonaslot.site/# Slot dengan bonus putaran gratis sangat populer
Slot modern memiliki grafik yang mengesankan http://slot88.company/# Slot dengan tema budaya lokal menarik perhatian
http://bonaslot.site/# Pemain harus memahami aturan masing-masing mesin
Mesin slot dapat dimainkan dalam berbagai bahasa: preman69 – preman69 slot
Because there are not any public exchanges itemizing their securities, non-public corporations meet enterprise capital corporations and different private fairness investors in a number of methods, together with heat referrals from the traders’ trusted sources and other enterprise contacts; investor conferences and symposia; and summits where companies pitch directly to investor groups in face-to-face conferences, together with a variant known as “Speed Venturing”, which is akin to hurry courting for capital, where the investor decides inside 10 minutes whether s/he desires a follow-up meeting.
This card encourages us to overcome our fears and embrace the journey of self-discovery and personal growth.
Slot menjadi bagian penting dari industri kasino https://garuda888.top/# Slot dengan grafis 3D sangat mengesankan
I’m so happy to read this. This is the type of manual that needs to be given and not the random misinformation that’s at the other blogs. Appreciate your sharing this greatest doc.
preman69 slot preman69 slot Kasino memiliki suasana yang energik dan menyenangkan
https://bonaslot.site/# п»їKasino di Indonesia sangat populer di kalangan wisatawan
Hey There. I found your blog using msn. This is a very smartly written article. I’ll make sure to bookmark it and come back to read more of your helpful information. Thanks for the post. I’ll certainly return.
UID_25978847###
situs terbaik hanya di slot gacor agentotoplay
Slot klasik tetap menjadi favorit banyak orang: preman69.tech – preman69
Hey there I am so grateful I found your webpage, I really found you by mistake, while I was researching on Bing for something else, Nonetheless I am here now and would just like to say thanks for a fantastic post and a all round exciting blog (I also love the theme/design), I don’t have time to browse it all at the minute but I have bookmarked it and also added your RSS feeds, so when I have time I will be back to read much more, Please do keep up the fantastic job.
Banyak kasino memiliki program loyalitas untuk pemain http://slot88.company/# Slot dengan fitur interaktif semakin banyak tersedia
Hello.This post was extremely remarkable, especially because I was looking for thoughts on this subject last Tuesday.
http://garuda888.top/# п»їKasino di Indonesia sangat populer di kalangan wisatawan
That is the fitting blog for anybody who desires to search out out about this topic. You understand a lot its almost laborious to argue with you (not that I truly would want…HaHa). You definitely put a new spin on a topic thats been written about for years. Great stuff, just great!
UID_25978847###
situs terbaik hanya di slot gacor agentotoplay
Banyak kasino memiliki promosi untuk slot http://garuda888.top/# Pemain sering berbagi tips untuk menang
There are actually a whole lot of particulars like that to take into consideration. That could be a nice level to deliver up. I supply the ideas above as common inspiration however clearly there are questions just like the one you convey up the place the most important factor can be working in honest good faith. I don?t know if best practices have emerged around issues like that, however I am sure that your job is clearly identified as a fair game. Both boys and girls really feel the impression of just a second’s pleasure, for the rest of their lives.
Slot dengan tema film terkenal menarik banyak perhatian https://slot88.company/# Beberapa kasino memiliki area khusus untuk slot
Permainan slot bisa dimainkan dengan berbagai taruhan: slot88.company – slot88
I have been exploring for a bit for any high-quality articles or weblog posts in this kind of area . Exploring in Yahoo I at last stumbled upon this site. Studying this info So i’m satisfied to exhibit that I’ve a very just right uncanny feeling I came upon just what I needed. I such a lot unquestionably will make certain to do not omit this web site and give it a look on a relentless basis.
Way cool! Some very valid points! I appreciate you writing this article plus the rest of the site is extremely good.
preman69.tech preman69.tech Mesin slot digital semakin banyak diminati
https://bonaslot.site/# Slot klasik tetap menjadi favorit banyak orang
Slot menawarkan kesenangan yang mudah diakses https://bonaslot.site/# Kasino sering mengadakan turnamen slot menarik
Slot dengan grafis 3D sangat mengesankan: bonaslot – BonaSlot
Chill Zone HiOP
Hello.This post was extremely interesting, particularly becauseI was searching for thoughts on this subject lastMonday.Also visit my blog … growing mini-course
http://slot88.company/# Slot dengan pembayaran tinggi selalu diminati
UID_95859078###
Baru-baru ini, para pemain Mahjong Wins 3 dikejutkan dengan bocoran RTP yang diklaim bisa meningkatkan peluang kemenangan secara signifikan. Banyak yang percaya bahwa informasi ini membantu mereka mendapatkan hasil yang lebih konsisten dalam permainan. Jika Anda ingin tahu lebih lanjut, cek bocoran RTP Mahjong Wins 3 hari ini dan lihat apakah strategi ini benar-benar efektif.
Mesin slot sering diperbarui dengan game baru https://bonaslot.site/# Kasino di Indonesia menyediakan hiburan yang beragam
Next time I read a blog, Hopefully it does not disappoint me just as much as this particular one. After all, I know it was my choice to read through, but I genuinely thought you would have something helpful to talk about. All I hear is a bunch of crying about something that you could possibly fix if you weren’t too busy looking for attention.
Mesin slot menawarkan berbagai tema menarik: garuda888 – garuda888 slot
Banyak pemain menikmati bermain slot secara online http://slot88.company/# Mesin slot menawarkan pengalaman bermain yang cepat
https://garuda888.top/# Kasino menyediakan layanan pelanggan yang baik
UID_95859078###
Baru-baru ini, para pemain Mahjong Wins 3 dikejutkan dengan bocoran RTP yang diklaim bisa meningkatkan peluang kemenangan secara signifikan. Banyak yang percaya bahwa informasi ini membantu mereka mendapatkan hasil yang lebih konsisten dalam permainan. Jika Anda ingin tahu lebih lanjut, cek bocoran RTP Mahjong Wins 3 hari ini dan lihat apakah strategi ini benar-benar efektif.
garuda888 garuda888.top Pemain harus menetapkan batas saat bermain
Woah! I’m really enjoying the template/theme of this website. It’s simple, yet effective. A lot of times it’s challenging to get that “perfect balance” between superb usability and visual appeal. I must say that you’ve done a very good job with this. In addition, the blog loads very fast for me on Opera. Exceptional Blog!
Pemain sering berbagi tips untuk menang: slot88.company – slot 88
Banyak pemain menikmati jackpot harian di slot https://bonaslot.site/# Mesin slot menawarkan berbagai tema menarik
http://garuda888.top/# Slot menjadi bagian penting dari industri kasino
Do you have a spam problem on this blog; I also am a blogger, and I was wanting to know your situation; many of us have developed some nice practices and we are looking to swap solutions with other folks, why not shoot me an email if interested.
Hi my friend! I want to say that this article is amazing, nice written and come with approximately all vital infos. I would like to see more posts like this .
Slot modern memiliki grafik yang mengesankan: preman69 slot – preman69
Jackpot besar bisa mengubah hidup seseorang https://slot88.company/# Slot klasik tetap menjadi favorit banyak orang
http://garuda888.top/# Pemain harus memahami aturan masing-masing mesin
sex nhật hiếp dâm trẻ em ấu dâm buôn bán vũ khí ma túy bán súng sextoy chơi đĩ sex bạo lực sex học đường tội phạm tình dục chơi les đĩ đực người mẫu bán dâm
Currently it looks like Drupal is the top blogging platform available right now. (from what I’ve read) Is that what you’re using on your blog?
UID_57331425###
Skandal terbaru mengguncang komunitas pecinta game slot setelah seorang admin terkenal, Rachel, dikabarkan tertangkap membocorkan pola kemenangan Gate of Olympus. Banyak yang bertanya-tanya apakah informasi ini benar-benar akurat atau hanya sekadar rumor yang beredar di kalangan pemain. Simak lebih lanjut detailnya dalam artikel admin Rachel tertangkap bocorkan pola Gate of Olympus.
preman69 preman69 Kasino memiliki suasana yang energik dan menyenangkan
UID_57331425###
Skandal terbaru mengguncang komunitas pecinta game slot setelah seorang admin terkenal, Rachel, dikabarkan tertangkap membocorkan pola kemenangan Gate of Olympus. Banyak yang bertanya-tanya apakah informasi ini benar-benar akurat atau hanya sekadar rumor yang beredar di kalangan pemain. Simak lebih lanjut detailnya dalam artikel admin Rachel tertangkap bocorkan pola Gate of Olympus.
Kasino sering memberikan hadiah untuk pemain setia https://slotdemo.auction/# Permainan slot bisa dimainkan dengan berbagai taruhan
Banyak kasino memiliki program loyalitas untuk pemain: preman69 slot – preman69 slot
http://slot88.company/# Kasino di Indonesia menyediakan hiburan yang beragam
Slot dengan tema budaya lokal menarik perhatian https://slot88.company/# Slot memberikan kesempatan untuk menang besar
Banyak kasino menawarkan permainan langsung yang seru: BonaSlot – BonaSlot
UID_17136916###
Kisah inspiratif datang dari seorang tukang ojek online asal Tangerang yang berhasil membawa pulang hadiah fantastis setelah bermain Mahjong Ways 2. Dengan modal kecil, ia sukses mengubah nasibnya dan meraih kemenangan besar senilai 200 juta rupiah. Penasaran bagaimana caranya? Simak kisah lengkapnya di artikel tukang ojek online menang 200 juta dari Mahjong Ways 2.
http://slotdemo.auction/# Jackpot besar bisa mengubah hidup seseorang
UID_17136916###
Kisah inspiratif datang dari seorang tukang ojek online asal Tangerang yang berhasil membawa pulang hadiah fantastis setelah bermain Mahjong Ways 2. Dengan modal kecil, ia sukses mengubah nasibnya dan meraih kemenangan besar senilai 200 juta rupiah. Penasaran bagaimana caranya? Simak kisah lengkapnya di artikel tukang ojek online menang 200 juta dari Mahjong Ways 2.
Keseruan bermain slot selalu menggoda para pemain http://slot88.company/# Bermain slot bisa menjadi pengalaman sosial
Slot dengan bonus putaran gratis sangat populer: bonaslot – bonaslot.site
slot demo slotdemo Mesin slot digital semakin banyak diminati
http://slotdemo.auction/# Slot dengan bonus putaran gratis sangat populer
UID_17136916###
Kisah inspiratif datang dari seorang tukang ojek online asal Tangerang yang berhasil membawa pulang hadiah fantastis setelah bermain Mahjong Ways 2. Dengan modal kecil, ia sukses mengubah nasibnya dan meraih kemenangan besar senilai 200 juta rupiah. Penasaran bagaimana caranya? Simak kisah lengkapnya di artikel tukang ojek online menang 200 juta dari Mahjong Ways 2.
Beberapa kasino memiliki area khusus untuk slot http://slotdemo.auction/# Slot dengan bonus putaran gratis sangat populer
Kasino sering memberikan hadiah untuk pemain setia: bonaslot.site – BonaSlot
https://preman69.tech/# Slot klasik tetap menjadi favorit banyak orang
Slot menjadi daya tarik utama di kasino https://preman69.tech/# Jackpot progresif menarik banyak pemain
UID_87427935###
Cek yuk! 🚍👮♂️Operasi Keselamatan 2025 Polres Ciamis Siapa tahu bus favoritmu jadi sasaran! 😱👍
Mesin slot sering diperbarui dengan game baru: garuda888.top – garuda888.top
https://bonaslot.site/# Kasino di Jakarta memiliki berbagai pilihan permainan
UID_87427935###
Cek yuk! 🚍👮♂️Operasi Keselamatan 2025 Polres Ciamis Siapa tahu bus favoritmu jadi sasaran! 😱👍
slot demo slot demo Bermain slot bisa menjadi pengalaman sosial
Banyak kasino memiliki program loyalitas untuk pemain https://garuda888.top/# Slot menawarkan kesenangan yang mudah diakses
This is best accomplished by spreading your legs approximately shoulder width apart and then lunging toward the ball when it is kicked.
UID_18563832###
Ini yang di ganti >>> Yuk, ketahui lebih lanjut tentang Syarat Gabung OECD dan Pentingnya Ratifikasi Konvensi Antisuap di sini! 🕵️♀️🔎📚.
Kasino di Bali menarik banyak pengunjung: preman69.tech – preman69 slot
Jackpot progresif menarik banyak pemain http://slotdemo.auction/# Slot memberikan kesempatan untuk menang besar
http://preman69.tech/# п»їKasino di Indonesia sangat populer di kalangan wisatawan
As a Newbie, I am always exploring online for articles that can be of assistance to me. Thank you
Banyak pemain mencari mesin dengan RTP tinggi http://slot88.company/# Permainan slot mudah dipahami dan menyenangkan
Mesin slot dapat dimainkan dalam berbagai bahasa: slot 88 – slot 88
https://garuda888.top/# Banyak kasino menawarkan permainan langsung yang seru
garuda888 slot garuda888 Permainan slot bisa dimainkan dengan berbagai taruhan
Kasino sering memberikan hadiah untuk pemain setia http://slot88.company/# Mesin slot menawarkan pengalaman bermain yang cepat
Banyak kasino memiliki promosi untuk slot: slot 88 – slot88.company
https://preman69.tech/# Slot dengan fitur interaktif semakin banyak tersedia
UID_18563832###
Ini yang di ganti >>> Yuk, ketahui lebih lanjut tentang Syarat Gabung OECD dan Pentingnya Ratifikasi Konvensi Antisuap di sini! 🕵️♀️🔎📚.
Slot menjadi bagian penting dari industri kasino http://garuda888.top/# Kasino di Jakarta memiliki berbagai pilihan permainan
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
When I initially left a comment I appear to have clicked on the -Notify me when new comments are added- checkbox and from now on every time a comment is added I recieve four emails with the same comment. Perhaps there is an easy method you are able to remove me from that service? Appreciate it.
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
Sweet blog! I found it while searching on Yahoo News. Do you have any tips on how to get listed in Yahoo News? I’ve been trying for a while but I never seem to get there! Thank you
Kasino memiliki suasana yang energik dan menyenangkan: slot demo – slot demo
https://slot88.company/# Permainan slot mudah dipahami dan menyenangkan
Hello! This is kind of off topic but I need some advice from an established blog. Is it very difficult to set up your own blog? I’m not very techincal but I can figure things out pretty fast. I’m thinking about creating my own but I’m not sure where to start. Do you have any tips or suggestions? With thanks
Kasino sering memberikan hadiah untuk pemain setia https://slot88.company/# п»їKasino di Indonesia sangat populer di kalangan wisatawan
Kasino memiliki suasana yang energik dan menyenangkan https://garuda888.top/# Slot dengan tema budaya lokal menarik perhatian
preman69 preman69 Pemain sering mencoba berbagai jenis slot
http://preman69.tech/# Slot menawarkan berbagai jenis permainan bonus
Slot menawarkan kesenangan yang mudah diakses: preman69 slot – preman69
Slot dengan fitur interaktif semakin banyak tersedia http://bonaslot.site/# Slot klasik tetap menjadi favorit banyak orang
Slot dengan tema budaya lokal menarik perhatian http://slotdemo.auction/# Banyak kasino menawarkan permainan langsung yang seru
generic doxycycline 200 mg: DoxHealthPharm – doxycycline online with no prescription
cost of doxycycline canada: doxycycline 20 mg india – doxycycline iv
https://clmhealthpharm.com/# where to buy cheap clomid without prescription
where to buy doxycycline in singapore: Dox Health Pharm – can you buy doxycycline over the counter in nz
doxy 100 purchase doxycycline 100mg price of doxycycline 100mg
UID_97211224###
Yuk, sehat bersama! 👨⚕️👩⚕️ Cek kondisi tubuh kamu di Program Cek Kesehatan Gratis sekarang juga! 💉🌡️ Selalu jaga kesehatan, ya! 🏥💖
can you buy doxycycline over the counter in india: Dox Health Pharm – buy doxycycline online without a prescription
It also makes constructing devoted sanding jigs a lot easier.
zithromax antibiotic without prescription: buy generic zithromax online – zithromax 500
Benson, Thom (Might 6, 2014).
https://amohealthpharm.shop/# rexall pharmacy amoxicillin 500mg
purchase amoxicillin online without prescription: amoxicillin 200 mg tablet – can you buy amoxicillin uk
UID_97211224###
Yuk, sehat bersama! 👨⚕️👩⚕️ Cek kondisi tubuh kamu di Program Cek Kesehatan Gratis sekarang juga! 💉🌡️ Selalu jaga kesehatan, ya! 🏥💖
UID_97211224###
Yuk, sehat bersama! 👨⚕️👩⚕️ Cek kondisi tubuh kamu di Program Cek Kesehatan Gratis sekarang juga! 💉🌡️ Selalu jaga kesehatan, ya! 🏥💖
zithromax 500 without prescription: where to get zithromax over the counter – zithromax online no prescription
doxycycline 250 mg tabs: DoxHealthPharm – 40mg doxycycline
https://clmhealthpharm.shop/# where to get cheap clomid prices
how to get cheap clomid for sale ClmHealthPharm generic clomid without dr prescription
amoxicillin 500 mg where to buy: canadian pharmacy amoxicillin – buy amoxicillin online with paypal
amoxicillin no prescipion: AmoHealthPharm – where to buy amoxicillin 500mg
UID_40226211###
Berita Hangat! 📰🔥 Bimbel Gratis Bagi Siswa SMAN 7 Cirebon yang Gagal SNBP! 😲🎓👍.
“I wanted to draft you a very little note so as to give many thanks the moment again considering the incredible tricks you have provided above. This is quite extremely open-handed of you to allow unreservedly precisely what numerous people could have offered for sale as an ebook in making some dough on their own, particularly now that you might well have done it in case you decided. These secrets in addition served to be the fantastic way to be aware that most people have similar desire the same as mine to find out more around this problem. I am certain there are lots of more enjoyable situations in the future for people who scan through your blog.”
amoxicillin medicine over the counter: Amo Health Pharm – where to buy amoxicillin
https://doxhealthpharm.com/# doxycycline where to get
doxycycline for sale over the counter: DoxHealthPharm – buy doxycycline online nz
how to buy generic clomid without rx: where can i get clomid no prescription – can you buy generic clomid without a prescription
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
doxycycline 100mg australia: can i buy 40mg doxycycline online – doxycycline 200 mg pill
zithromax online pharmacy canada ZithroPharm where to buy zithromax in canada
http://clmhealthpharm.com/# buying generic clomid without insurance
amoxicillin 500 mg price: AmoHealthPharm – where can i get amoxicillin 500 mg
where to buy cheap clomid without dr prescription: ClmHealthPharm – buying clomid without dr prescription
Because of this, the Crimson Dragon seems, giving Yusei’s Duel Runner the power to journey by way of time.
can i buy amoxicillin over the counter in australia: can you buy amoxicillin over the counter canada – buy amoxicillin 500mg canada
https://amohealthpharm.com/# amoxicillin tablet 500mg
where can i get amoxicillin: AmoHealthPharm – how to buy amoxicillin online
Dell of new Jersey who additionally each died in Canada.
order doxycycline 100mg without prescription: doxycycline tablets cost – 80 mg doxycycline
After Hilário conceded four targets in two matches, Chelsea manager José Mourinho decided to place Cudicini in purpose against Aston Villa of their fourth-round match of the League Cup.
amoxil generic: AmoHealthPharm – buy amoxicillin online mexico
doxycycline 2014 80 mg doxycycline generic for doxycycline
http://doxhealthpharm.com/# doxycycline brand name
zithromax online no prescription: ZithroPharm – can you buy zithromax over the counter in mexico
where can i get clomid pill: ClmHealthPharm – how to get generic clomid for sale
antibiotics doxycycline: doxycycline 300 mg daily – buy doxycycline tablets
can i order cheap clomid tablets: ClmHealthPharm – clomid online
https://clmhealthpharm.com/# where to buy clomid online
doxycycline pills price in south africa: Dox Health Pharm – medicine doxycycline 100mg
zithromax 500 tablet: ZithroPharm – zithromax for sale online
amoxicillin 30 capsules price: buy amoxicillin from canada – amoxicillin 500mg tablets price in india
doxycycline 60 mg Dox Health Pharm doxycycline price mexico
https://amohealthpharm.com/# amoxicillin without prescription
purchase amoxicillin 500 mg: prescription for amoxicillin – how to buy amoxicillin online
22 doxycycline: doxycycline tablets online – buy doxycycline monohydrate
no prescription doxycycline: otc doxycycline no prescription – generic doxycycline
CMT International ceased the CMT Europe channel due to excessive losses from distribution and satellite prices on March 31, 1998.
Google is one in every of a number of corporations creating an answer to the problem comes within the type of a wearable device.
https://zithropharm.com/# can you buy zithromax over the counter in mexico
Among the nation clubs on this card can also be used the place the world code of the IBAN code that it is used to identify the account numbers.
zithromax price south africa: zithromax generic price – where can you buy zithromax
zithromax prescription generic zithromax over the counter how to get zithromax over the counter
amoxicillin script: can we buy amoxcillin 500mg on ebay without prescription – amoxicillin azithromycin
amoxicillin 250 mg price in india: buy cheap amoxicillin online – amoxacillian without a percription
http://amohealthpharm.com/# amoxicillin 500mg no prescription
doxycycline hyclate 100 mg cap: doxycycline 100g tablets – buy online doxycycline without prescription
amoxicillin 500mg no prescription: generic amoxicillin over the counter – where to get amoxicillin over the counter
how can i get cheap clomid price: where buy generic clomid without a prescription – can i buy generic clomid without prescription
A very good restaurant seemingly has specialised glassware — pink wine glasses, white wine glasses, snifters, highball glasses.
https://doxhealthpharm.com/# doxycycline 2985
can you get generic clomid for sale: ClmHealthPharm – where to buy cheap clomid no prescription
doxycycline prescription australia Dox Health Pharm purchase doxycycline
average cost of generic zithromax: zithromax online paypal – where can i buy zithromax uk
An interesting discussion is definitely worth comment. I believe that you need to publish more about this topic, it might not be a taboo matter but usually people don’t discuss these issues. To the next! Best wishes!
how much is amoxicillin: amoxicillin generic brand – amoxicillin order online
antibiotic doxycycline: doxycycline 100mg otc – doxycycline without rx
http://doxhealthpharm.com/# doxycycline 150mg pill
First, ship a letter to the CRA to give your facet of the story and attempt to set straight the inaccuracies which have been reported.
https://tadalafilmeilleurprix.shop/# Pharmacie en ligne livraison Europe
pharmacie en ligne
However to essentially add space, you will must see if you can steal a couple of ft from an adjacent closet or unused area of a neighboring room or hallway, or even bump out a mini-addition.
But if you wish to take an additional step, hunt round for unique posters on eBay.
Viagra en france livraison rapide: viagra en ligne – Viagra sans ordonnance 24h Amazon
Pharmacie Internationale en ligne: achat kamagra – pharmacie en ligne livraison europe
pharmacie en ligne france fiable https://pharmaciemeilleurprix.shop/# pharmacie en ligne france livraison belgique
acheter mГ©dicament en ligne sans ordonnance achat kamagra Pharmacie Internationale en ligne
https://kamagrameilleurprix.shop/# pharmacie en ligne france livraison internationale
pharmacie en ligne france livraison belgique
pharmacie en ligne fiable: cialis prix – pharmacies en ligne certifiГ©es
Achat mГ©dicament en ligne fiable: pharmacie en ligne france – pharmacie en ligne france livraison belgique
pharmacie en ligne france livraison belgique https://pharmaciemeilleurprix.shop/# pharmacie en ligne france fiable
Serene mountain retreats work like balm on our tired senses.
I am in fact thankful to the holder of this site who has shared this great
article at at this place.
https://pharmaciemeilleurprix.com/# pharmacie en ligne sans ordonnance
pharmacie en ligne france pas cher
SildГ©nafil 100 mg prix en pharmacie en France: acheter du viagra – Sildenafil teva 100 mg sans ordonnance
pharmacie en ligne pharmacie en ligne fiable п»їpharmacie en ligne france
п»їpharmacie en ligne france: pharmacie en ligne france livraison belgique – pharmacie en ligne livraison europe
pharmacie en ligne pas cher http://pharmaciemeilleurprix.com/# Pharmacie sans ordonnance
Pharmacie sans ordonnance: Tadalafil sans ordonnance en ligne – pharmacie en ligne fiable
https://viagrameilleurprix.com/# Viagra sans ordonnance livraison 48h
pharmacie en ligne france fiable
pharmacie en ligne: kamagra pas cher – acheter mГ©dicament en ligne sans ordonnance
pharmacie en ligne france livraison internationale: pharmacie en ligne avec ordonnance – pharmacie en ligne france fiable
acheter mГ©dicament en ligne sans ordonnance http://viagrameilleurprix.com/# Viagra gГ©nГ©rique sans ordonnance en pharmacie
https://pharmaciemeilleurprix.shop/# pharmacie en ligne france livraison internationale
pharmacie en ligne fiable
Pharmacie sans ordonnance: kamagra livraison 24h – Achat mГ©dicament en ligne fiable
Fundamentally, the place function on your phone has tobe turned on to place a wager, and the app detects exactly where youare located.
pharmacie en ligne: vente de mГ©dicament en ligne – pharmacie en ligne avec ordonnance
Allow us to sneak fast peruse Stock tips and commercialism tips.
trouver un mГ©dicament en pharmacie https://tadalafilmeilleurprix.com/# pharmacie en ligne pas cher
Constructing on Marx, and on the theories of the sociologist and philosopher Pierre Bourdieu, students have not too long ago argued for the importance of “culinary capital” in the area of meals.
trouver un mГ©dicament en pharmacie: pharmacie en ligne sans ordonnance – vente de mГ©dicament en ligne
https://kamagrameilleurprix.shop/# pharmacie en ligne france pas cher
trouver un mГ©dicament en pharmacie
pharmacie en ligne france livraison internationale: cialis sans ordonnance – pharmacie en ligne france fiable
pharmacies en ligne certifiГ©es: cialis prix – pharmacies en ligne certifiГ©es
pharmacie en ligne livraison europe https://tadalafilmeilleurprix.com/# pharmacie en ligne france pas cher
pharmacie en ligne sans ordonnance cialis sans ordonnance Pharmacie Internationale en ligne
Viagra pas cher livraison rapide france: acheter du viagra – SildГ©nafil Teva 100 mg acheter
Pharmacie Internationale en ligne: cialis prix – pharmacie en ligne france pas cher
п»їpharmacie en ligne france https://tadalafilmeilleurprix.shop/# acheter mГ©dicament en ligne sans ordonnance
But, no worries your private accountant can save you from harassment of the IRS.
http://kamagrameilleurprix.com/# pharmacies en ligne certifiГ©es
pharmacies en ligne certifiГ©es
Thank you ever so for you blog.Really thank you! Want more.
acheter mГ©dicament en ligne sans ordonnance: cialis prix – Achat mГ©dicament en ligne fiable
Prix du Viagra en pharmacie en France Acheter Viagra Cialis sans ordonnance SildГ©nafil 100mg pharmacie en ligne
Thanks-a-mundo for the article.Really thank you! Fantastic.
https://kamagrameilleurprix.shop/# pharmacie en ligne avec ordonnance
pharmacie en ligne france livraison internationale
I really like it whenever people come together and share ideas. Great blog, continue the good work.
Viagra vente libre pays: Viagra pharmacie – Prix du Viagra en pharmacie en France
Achat mГ©dicament en ligne fiable https://kamagrameilleurprix.shop/# trouver un mГ©dicament en pharmacie
Le gГ©nГ©rique de Viagra: acheter du viagra – Quand une femme prend du Viagra homme
Hey, thanks for the blog.Really thank you! Will read on…
Prix du Viagra 100mg en France: viagra sans ordonnance – Viagra femme ou trouver
https://pharmaciemeilleurprix.com/# Pharmacie sans ordonnance
pharmacie en ligne pas cher