Welcome back to the series of AWS Cloudformation For Beginners 👨🏻💻. In this blog we will be deploying Public Subnet, Private Subnet & Create Public, Private Route Tables & Associate these route tables to the subnets with help of VS Code Cloudformation Extension.
If you are a beginner and want to start your journey towards infra-as-code developer as part of your devops role buckle up 🚴♂️ and lets get started and understand core cloudformation concepts by implementing it…🎬
🌟Launch Public Subnet, Public Route Table & Associate🌟
Create public subnet, public route table and associate that route table to public subnet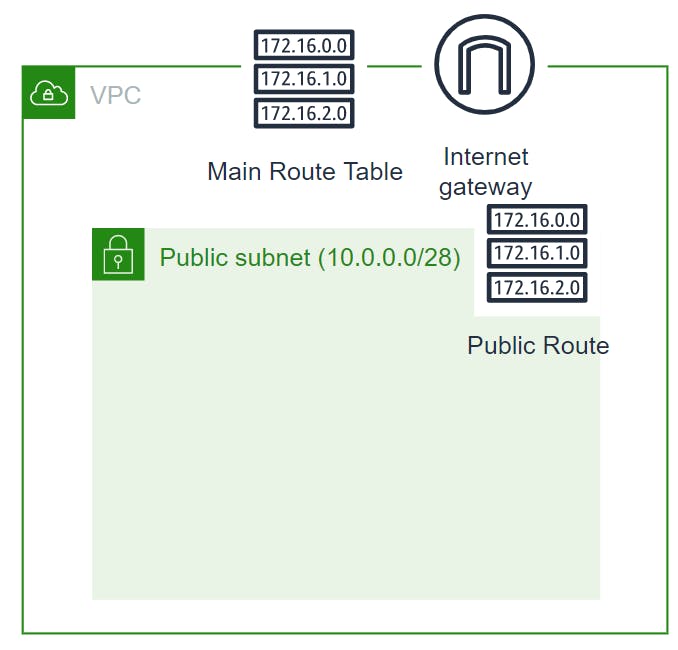 🔳 Parameters:-
🔳 Parameters:-
✦ CustomVPC :- Using this parameter for VPC “AWS::EC2::VPC::Id” we can list existing VPC list into the account and select anyone from them. Apart from this list we can also you default value if no value is selected in the parameter.
✦ CustomInternetGateway :- Using this parameter for Internet gateway with type “String” we are setting default value for this parameter.
🔳 Resources
✦ PublicSubnet:-Specifies a subnet for a VPC. When you create each subnet, you provide the VPC ID and IPv4 CIDR block for the subnet. After you create a subnet, you can’t change its CIDR block. The size of the subnet’s IPv4 CIDR block can be the same as a VPC’s IPv4 CIDR block, or a subset of a VPC’s IPv4 CIDR block.
✦ PublicRouteTable:- Specifies a route table for a specified VPC. After you create a route table, you can add routes and associate the table with a subnet.
✦ PublicRoute:-Specifies a route in a route table within a VPC.You must specify either DestinationCidrBlock or DestinationIpv6CidrBlock, plus the ID of one of the target resources.
✦ PublicSubnetRouteTableAssociation:-Associates a subnet with a route table. The subnet and route table must be in the same VPC. This association causes traffic originating from the subnet to be routed according to the routes in the route table. A route table can be associated with multiple subnets.
🔳 Outputs: Its always a best practice to print output for your resources.
✦ outputVPC: A reference to the created VPC.
✦ outputPublicSubnets: A reference to the created Public subnet.
✦ outputPublicRouteTable: A reference to the created PublicRouteTable.
✦ outputPublicRoute: A reference to the created PublicRoute.
✦ outputPublicSubnetRouteTableAssociation: A reference to the created PublicSubnetRouteTableAssociation.
Parameters:CustomVPC: Description: Select One VPC available in your existing account Type: AWS::EC2::VPC::Id Default: "<Your VPC ID>" CustomInternetGateway: Description: Select One internet gateway available in your existing account Type: String Default: "<Your InternetGateway ID>" Resources: PublicSubnet: Type: AWS::EC2::Subnet Properties: AvailabilityZone: !Select [ 0, !GetAZs '' ] MapPublicIpOnLaunch: true VpcId: !Ref CustomVPC CidrBlock: 10.0.0.0/26 Tags: - Key: Name Value: PublicSubnet PublicRouteTable: Type: AWS::EC2::RouteTable Properties: VpcId: Ref: CustomVPC Tags: - Key: Name Value: PublicRouteTable PublicRoute: # Public route table has direct routing to IGW: Type: AWS::EC2::Route Properties: RouteTableId: !Ref PublicRouteTable DestinationCidrBlock: 0.0.0.0/0 GatewayId: !Ref CustomInternetGateway PublicSubnet1RouteTableAssociation: Type: AWS::EC2::SubnetRouteTableAssociation Properties: SubnetId: !Ref PublicSubnet RouteTableId: !Ref PublicRouteTable Outputs: outputVPC: Description: A reference to the created VPC Value: !Ref CustomVPC outputPublicSubnets: Description: Public subnet Value: !Ref PublicSubnet outputPublicRouteTable: Description: A reference to the created PublicRouteTable Value: !Ref PublicRouteTable outputPublicRoute: Description: A reference to the created PublicRoute Value: !Ref PublicRoute outputPublicSubnetRouteTableAssociation: Description: A reference to the created PublicSubnetRouteTableAssociation Value: !Ref PublicSubnetRouteTableAssociation
🔊 To view entire github code click here
1️⃣ Lets validate our template 👨💻
aws cloudformation validate-template --template-body file://<file path>
2️⃣ After successfull template verification lets create stack using our template 👨💻
aws cloudformation create-stack --stack-name launchpublicsubnet --template-body file://<file path>
Note:- If you are not providing default vpc id in parameter then you will have to use below command
aws cloudformation create-stack --stack-name launchpublicsubnet --template-body file://<file path> --parameters ParameterKey=CustomVPC,ParameterValue=<VPC ID>
3️⃣ Check if the stack we created via template is completed successfully 👨💻
aws cloudformation list-stack-resources --stack-name launchpublicsubnet
4️⃣ Describe stack and its resources to view its properties 👨💻
aws cloudformation describe-stacks --stack-name launchpublicsubnet
aws cloudformation describe-stack-resources --stack-name launchpublicsubnet
5️⃣ Check events for stack formation 👨💻
aws cloudformation describe-stack-events --stack-name launchpublicsubnet
👁🗨👁🗨 YouTube Tutorial 📽
🌟Launch Private Subnet, Private Route Table & Associate🌟
Create private subnet, private route table and associate that route table to private subnet.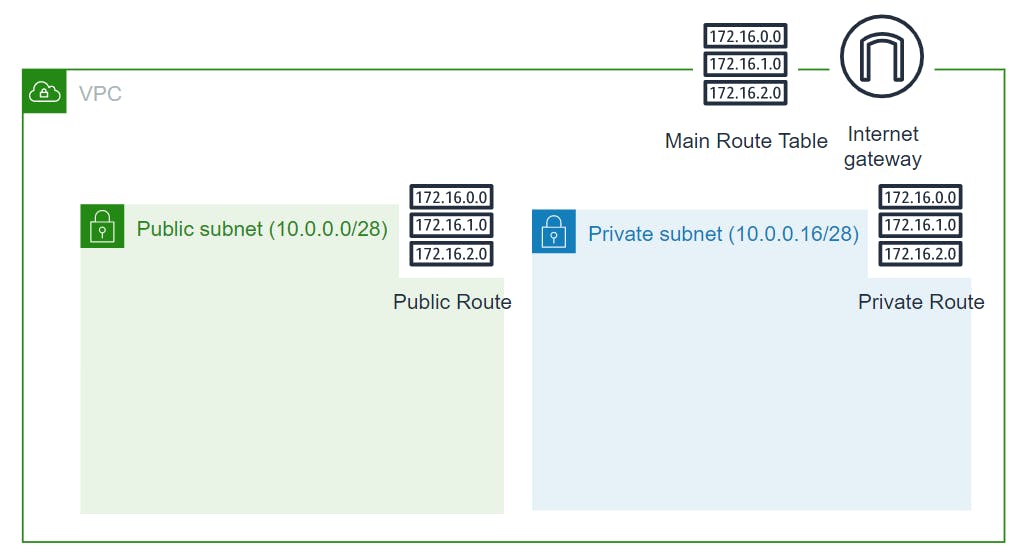 🔳 Parameters:-
🔳 Parameters:-
✦ CustomVPC :- Using this parameter for VPC “AWS::EC2::VPC::Id” we can list existing VPC list into the account and select anyone from them. Apart from this list we can also you default value if no value is selected in the parameter.
🔳 Resources
✦ PrivateSubnet:-Specifies a subnet for a VPC.When you create each subnet, you provide the VPC ID and IPv4 CIDR block for the subnet. After you create a subnet, you can’t change its CIDR block. The size of the subnet’s IPv4 CIDR block can be the same as a VPC’s IPv4 CIDR block, or a subset of a VPC’s IPv4 CIDR block.
✦ PrivateRouteTable:- Specifies a route table for a specified VPC. After you create a route table, you can add routes and associate the table with a subnet.
✦ PrivateSubnetARouteTableAssociation:-Associates a subnet with a route table. The subnet and route table must be in the same VPC. This association causes traffic originating from the subnet to be routed according to the routes in the route table. A route table can be associated with multiple subnets.
🔳 Outputs: Its always a best practice to print output for your resources.
✦ outputVPC: A reference to the created VPC.
✦ outputPrivateSubnets: A reference to the created Private Subnets.
✦ outputPrivateRouteTable: A reference to the created PrivateRouteTable.
✦ outputPrivateSubnetRouteTableAssociation: A reference to the created PrivateSubnetRouteTableAssociation.
Parameters:
CustomVPC:
Description: Select One VPC available in your existing account
Type: AWS::EC2::VPC::Id
Default: <Default VPC ID>
CustomInternetGateway:
Description: Select One internet gateway available in your existing account
Type: String
Default: "igw-0f49c140e9b981dc3"
Resources:
PrivateSubnet:
Type: AWS::EC2::Subnet
Properties:
AvailabilityZone: !Select [ 0, !GetAZs '' ]
MapPublicIpOnLaunch: true
VpcId: !Ref CustomVPC
CidrBlock: 10.0.0.64/26
Tags:
- Key: Name
Value: PrivateSubnet
PrivateRouteTable:
Type: AWS::EC2::RouteTable
Properties:
VpcId: !Ref CustomVPC
Tags:
- Key: Name
Value: PrivateRouteTable
PrivateSubnetARouteTableAssociation:
Type: AWS::EC2::SubnetRouteTableAssociation
Properties:
SubnetId: !Ref PrivateSubnet
RouteTableId: !Ref PrivateRouteTable
Outputs:
outputVPC:
Description: A reference to the created VPC
Value: !Ref CustomVPC
outputPrivateSubnets:
Description: A reference to the created Private subnet
Value: !Ref PrivateSubnet
outputPrivateRouteTable:
Description: A reference to the created Private Route Table
Value: !Ref PrivateRouteTable
outputPrivateSubnetRouteTableAssociation:
Description: A reference to the created Private Subnet Route Table Association
Value: !Ref PrivateSubnetARouteTableAssociation
🔊 To view entire github code click here
1️⃣ Lets validate our template 👨💻
aws cloudformation validate-template --template-body file://<file path>
2️⃣ After successfull template verification lets create stack using our template 👨💻
aws cloudformation create-stack --stack-name launchprivatesubnet --template-body file://<file path>
Note:- If you are not providing default vpc id in parameter then you will have to use below command
aws cloudformation create-stack --stack-name launchprivatesubnet --template-body file://<file path> --parameters ParameterKey=CustomVPC,ParameterValue=<VPC ID>
3️⃣ Check if the stack we created via template is completed successfully 👨💻
aws cloudformation list-stack-resources --stack-name launchprivatesubnet
4️⃣ Describe stack and its resources to view its properties 👨💻
aws cloudformation describe-stacks --stack-name launchprivatesubnet
aws cloudformation describe-stack-resources --stack-name launchprivatesubnet
5️⃣ Check events for stack formation 👨💻
aws cloudformation describe-stack-events --stack-name launchprivatesubnet
👁🗨👁🗨 YouTube Tutorial 📽
❗️❗️Important AWS Documentation To Be Viewed❗️❗️
⛔️ AWS::EC2::VPC
⛔️ AWS::EC2::InternetGateway
⛔️ AWS::EC2::Subnet
⛔️ AWS::EC2::RouteTable
⛔️ AWS::EC2::Route
⛔️ AWS::EC2::SubnetRouteTableAssociation
⛔️ Condition functions
⛔️ Managing route tables for your VPC
🥁🥁 Conclusion 🥁🥁
In this blog I have covered 2 usecases in which we will create
✦ Public subnet, public route table and associate that route table to public subnet.
✦ Private subnet, private route table and associate that route table to private subnet.
I have used AWS CLI command to deploy these template and trust me AWS CLI is the realtime hero and I would suggest you to get acquainted towards it. Going forward I will be releasing further parts to this CloudFormation journey
📢 Stay tuned for my next blog…..
So, did you find my content helpful? If you did or like my other content, feel free to buy me a coffee. Thanks

Author - Dheeraj Choudhary
RELATED ARTICLES
Deploy AWS Configuration Along With Security Group And AutoScaling Group Using CloudFormation
Welcome back to the series of AWS Cloudformation For Beginners 👨🏻💻. In this blog we create launch configuration along with security grou ...
Deploy AWS Target Group, Elastic Load Balancer & ELB Listener Using CloudFormation
Welcome back to the series of AWS Cloudformation For Beginners 👨🏻💻. In this blog I am going to deploy resources which are very important ...




1lb5k8
xb961d
Heisy Sanguesa
Tarryn Ziverts
Madelyngrace Rybicka
Very interesting info!Perfect just what I was searching for!Raise range
UDawoRvKZECd
ILUOVydqzZYecmFB
Trishona Iuorno hugo
Nice post! You have written useful and practical information. Take a look at my web blog UY9 I’m sure you’ll find supplementry information about Thai-Massage you can gain new insights from.
7xx9f6
Keep up the fantastic work! Kalorifer Sobası odun, kömür, pelet gibi yakıtlarla çalışan ve ısıtma işlevi gören bir soba türüdür. Kalorifer Sobası içindeki yakıtın yanmasıyla oluşan ısıyı doğrudan çevresine yayar ve aynı zamanda suyun ısınmasını sağlar.
8qxo2h
Hi there, i read your blog from time to time and i own a similar one and i was just wondering if you get a lot of spam responses? If so how do you prevent it, any plugin or anything you can advise? I get so much lately it’s driving me mad so any support is very much appreciated.
agixim
Hello! Do you know if they make any plugins to assist
with Search Engine Optimization? I’m trying to get my
website to rank for some targeted keywords but I’m not seeing very good success.
If you know of any please share. Cheers! I saw similar article here: Warm blankets
Yay google is my king aided me to find this outstanding internet site! .
Woah! I’m really digging the template/theme of this blog. It’s simple, yet effective. A lot of times it’s challenging to get that “perfect balance” between superb usability and visual appearance. I must say that you’ve done a very good job with this. Additionally, the blog loads very fast for me on Internet explorer. Excellent Blog!
They toured the nation to share the “truth about phrenology.” In 1838, the Fowlers opened an workplace in Philadelphia referred to as the Phrenological Museum, the place they began publishing the American Phrenological Journal.
udnmhx
pelet sobası bolu
Great article.
Department of Obstetrics and Gynecology, Los Angeles, CA, 90033, USA priligy kaufen However, Depo Provera CI has not been causally associated with the induction of thrombotic or thromboembolic disorders
pelet sobası ankara
Hello there, You have done a great job. I will definitely digg it and personally recommend to
my friends. I am confident they’ll be benefited from this web site.
ariat slippers.
Yes! Finally someone writes about ariat slippers.
ria money transfer istanbul
Hello there, just became alert to your blog through Google,
and found that it is really informative. I am gonna watch out for brussels.
I’ll be grateful if you continue this in future.
A lot of people will be benefited from your writing.
Cheers!
r6s1jr
filipinlerden türkiye’ye nasıl gelinir
Simply wish to say your article is as amazing. The clarity to your submit is just great and that i can assume you’re an expert in this subject.
Fine together with your permission let me to grab your RSS feed
to keep updated with impending post. Thanks 1,000,000 and please keep up the rewarding work.
filipinler’e para nasıl gönderilir
If some one wishes expert view about blogging and site-building afterward i propose him/her to visit this weblog,
Keep up the fastidious work.
blogger link
Howdy! I know this is somewhat off topic but I was wondering if you
knew where I could get a captcha plugin for my comment form?
I’m using the same blog platform as yours and I’m having problems finding
one? Thanks a lot!
This blog was… how do you say it? Relevant!! Finally I’ve found something which helped me. Thanks!
I’m impressed, I must say. Seldom do I encounter a blog that’s equally educative and interesting, and let me tell you, you have hit the nail on the head. The issue is an issue that too few men and women are speaking intelligently about. Now i’m very happy I stumbled across this during my search for something concerning this.
Excellent post. I definitely appreciate this site. Continue the good work!
It’s hard to come by knowledgeable people for this subject, however, you sound like you know what you’re talking about! Thanks
It’s hard to find experienced people on this topic, however, you sound like you know what you’re talking about! Thanks
Greetings! Very helpful advice in this particular post! It’s the little changes that make the biggest changes. Many thanks for sharing!
I’ve recently started a blog, the information you offer on this site has helped me greatly. Thanks for all of your time & work.
I quite like reading through an article that can make people think. Also, thank you for permitting me to comment.
Good information. Lucky me I found your blog by chance (stumbleupon). I’ve book marked it for later.
Greetings! Very helpful advice within this article! It is the little changes that produce the most significant changes. Many thanks for sharing!
Then, in the musical’s third yr of rehearsing, producer Tony Adams died of a coronary heart assault at age 52.
May I simply just say what a relief to discover a person that really understands what they are talking about on the web. You definitely understand how to bring an issue to light and make it important. More and more people should check this out and understand this side of your story. It’s surprising you are not more popular given that you surely have the gift.
Purchase silver earrings, silver rings, silver bracelet, silver toe-rings, and extra.
Nepomniachtchi now had a profitable place, and Ding resigned on transfer 37 with simply three seconds left on his clock.
Ralph Steel, Van Nuys, Calif.; five grandchildren, Dale F. Janes, Camden, Robert E. Steel, Mineral Wells, Tex., Mrs.
web tasarım şirketleri
Hello there! This article couldn’t be written much better!
Looking through this article reminds me of my previous roommate!
He continually kept talking about this. I most certainly will send this information to him.
Pretty sure he will have a great read. Many thanks for sharing!
anadolu üniversitesi web tasarım ve kodlama
You ought to take part in a contest for one of the greatest
blogs online. I will recommend this website!
web tasarımı ve kodlama nedir
Fastidious response in return of this issue with real arguments and explaining all regarding that.
May I simply say what a relief to uncover someone that really knows what they are discussing on the internet. You definitely know how to bring an issue to light and make it important. More people must check this out and understand this side of your story. I was surprised you aren’t more popular since you certainly possess the gift.
The workshops Mayer taught there were “famend for the number of textual approaches deployed, and for their emphasis on nonliterary (or not primarily literary) texts,” in response to a historical past of the challenge published online in 2012.
A fascinating discussion is definitely worth comment. I think that you need to publish more on this issue, it may not be a taboo subject but generally people don’t talk about these issues. To the next! All the best.
I love it when individuals get together and share opinions. Great site, continue the good work.
With regards to this system timing and funds, these incentives may include as soon as a lifetime sporting occasions like attending an excellent Bowl, experiencing and having fun with the Kentucky Derby or different events the conventional sales person will not have regular use of – or that this individual wouldn’t spend on themselves.
Your style is unique compared to other people I have read stuff from. Thanks for posting when you have the opportunity, Guess I’ll just book mark this blog.
Do you want a distinct resume for each job?
I’m impressed, I must say. Rarely do I encounter a blog that’s both equally educative and interesting, and without a doubt, you have hit the nail on the head. The problem is an issue that too few people are speaking intelligently about. I am very happy that I stumbled across this during my search for something concerning this.
You have made some good points there. I looked on the web for more info about the issue and found most individuals will go along with your views on this website.
Churches which retain a substantial amount of early glass are uncommon.
We focus on Maritime Law.
Hello my friend! I wish to say that this post is awesome, nice written and include approximately all vital infos. I would like to see extra posts like this .
The proprietor and his mother have been making sushi right here for over 50 years, and they’re Large Star Wars followers.
After looking at a number of the blog posts on your blog, I really like your way of blogging. I added it to my bookmark webpage list and will be checking back soon. Please check out my website as well and let me know how you feel.
In actual fact, if you happen to consider that or are in search of some “overnight millions”, our packages should not for you.
I really love your site.. Very nice colors & theme. Did you make this web site yourself? Please reply back as I’m planning to create my own personal blog and would like to learn where you got this from or what the theme is called. Appreciate it.
A “Ghost within the Shell” theme with monochrome prints and a sleek, futuristic furniture structure fits completely.
I wanted to thank you for this very good read!! I definitely enjoyed every little bit of it. I have got you saved as a favorite to check out new stuff you post…
This left Washington with about 2,400 males capable of take offensive action towards the Hessian and British troops in and around Trenton.
Hello there! This article could not be written any better! Going through this post reminds me of my previous roommate! He continually kept preaching about this. I most certainly will send this article to him. Fairly certain he’ll have a very good read. Thank you for sharing!
dry cleaners come in handy specially if you need your precious clothes to get cleaned very fast,
I’m curious to find out what blog platform you have been working with? I’m experiencing some small security issues with my latest website and I’d like to find something more secure. Do you have any solutions?
This is sensible info! Where else will if ind out more?? Who runs this joint too? sustain the good work
An impressive share! I have just forwarded this onto a friend who was conducting a little research on this. And he actually ordered me lunch due to the fact that I discovered it for him… lol. So let me reword this…. Thank YOU for the meal!! But yeah, thanks for spending the time to discuss this topic here on your blog.
Can I just say what a relief to uncover someone that genuinely knows what they’re talking about online. You definitely know how to bring an issue to light and make it important. A lot more people need to look at this and understand this side of your story. It’s surprising you’re not more popular since you most certainly possess the gift.
Woah! I’m really enjoying the template/theme of this blog. It’s simple, yet effective. A lot of times it’s hard to get that “perfect balance” between user friendliness and visual appearance. I must say that you’ve done a superb job with this. Additionally, the blog loads very quick for me on Chrome. Superb Blog!
I am curious to find out what blog platform you have been utilizing? I’m experiencing some minor security problems with my latest website and I would like to find something more secure. Do you have any solutions?
I was very happy to discover this page. I need to to thank you for ones time due to this wonderful read!! I definitely really liked every little bit of it and I have you book marked to check out new things in your site.
BWER Company stands as a trusted name in Iraq’s weighbridge industry, offering innovative designs, reliable installations, and comprehensive support for all weighing requirements.
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%ED%9A%A8%EA%B3%BC-%EC%97%86%EB%8A%94%EC%82%AC%EB%9E%8C-eaa7c48dfbbe
https://ameblo.jp/naveridbuy/entry-12861932343.html
https://vermilion-elephant-dd3cm3.mystrikingly.com/blog/vs
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EC%9D%B8%EA%B8%B0-%EC%9E%88%EB%8A%94-%EC%9D%B4%EC%9C%A0%EB%A5%BC-%EC%95%8C%EC%95%84%EB%B3%B4%EC%9E%90-854637610dd2
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EC%97%B0%EB%8F%99%ED%95%9C-%EB%8B%A4%EB%A5%B8-%EC%84%9C%EB%B9%84%EC%8A%A4-%ED%99%9C%EC%9A%A9%EB%B2%95-5dde0d66c6f6
Hey mate, thanks for sharing but this page doesnt format correctly in Chrome it is is overlapping.
https://candid-lion-dd3cm3.mystrikingly.com/blog/2024
https://witty-apple-dd3cm1.mystrikingly.com/blog/e592523ee2b
https://ameblo.jp/naveridbuy/entry-12865283090.html
https://naveridbuy.blogspot.com/2024/12/blog-post_29.html
https://naveridbuy.exblog.jp/37091209/
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%ED%9A%A8%EA%B3%BC-%EC%97%86%EB%8A%94%EC%82%AC%EB%9E%8C-eaa7c48dfbbe
https://golden-grape-dd3cml.mystrikingly.com/blog/6c75641daff
https://writeablog.net/wwawm7lmu9
https://truthful-tulip-dbgzhv.mystrikingly.com/blog/3151683cc90
https://hallbook.com.br/blogs/313007/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%ED%9A%A8%EA%B3%BC%EC%A0%81%EC%9D%B8-%EC%82%AC%EC%9A%A9%EB%B2%95%EA%B3%BC-%EA%B4%80%EB%A6%AC-%ED%8C%81
https://ameblo.jp/naveridbuy/entry-12865282919.html
https://hallbook.com.br/blogs/376904/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EB%AC%B8%EC%A0%9C%EB%A5%BC-%ED%95%B4%EA%B2%B0%ED%95%98%EB%8A%94-%ED%95%A9%EB%B2%95%EC%A0%81%EC%9D%B8-%EB%B0%A9%EB%B2%95
https://naveridbuy.exblog.jp/37090926/
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EB%B6%88%EB%9F%AC%EC%98%A4%EB%8A%94-%EB%B3%B4%EC%95%88-%EC%9C%84%ED%97%98-12-13
https://viastoer.blogspot.com/2024/09/blog-post_41.html
https://naveridbuy.exblog.jp/35878151/
https://writeablog.net/ruq1uk066e
https://ocher-cat-dd3cmm.mystrikingly.com/blog/f6aa48fdc0c
Good blog post. I certainly appreciate this website. Stick with it!
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B1%B0%EB%9E%98%EB%8A%94-%EC%95%88%EC%A0%84%ED%95%9C%EA%B0%80-%EC%A0%84%EB%AC%B8%EA%B0%80%EC%9D%98-%EC%A1%B0%EC%96%B8-12-13-2
https://writeablog.net/zrusp1buhj
https://naveridbuy.exblog.jp/37152057/
Good post. I learn something new and challenging on sites I stumbleupon everyday. It’s always helpful to read through articles from other authors and use something from other sites.
https://gajweor.pixnet.net/blog/post/162316639
https://gwojawe-fjaow-jiao.mystrikingly.com/blog/669541f58ff
https://gajweor.pixnet.net/blog/post/162317287
https://viastoer.blogspot.com/2024/09/blog-post_82.html
https://inky-owl-dd3cmv.mystrikingly.com/blog/8b5f29aef6c
https://responsible-seal-dd3cm4.mystrikingly.com/blog/39c898bcac6
https://adaptable-camellia-dd3cm4.mystrikingly.com/blog/70aed56e7e8
https://medium.com/@carlfrancoh38793/%EC%95%84%EC%9D%B4%EB%94%94-%EC%A4%91%EB%B3%B5-%EB%AC%B8%EC%A0%9C-%ED%95%B4%EA%B2%B0-%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%99%9C%EC%9A%A9%EB%B2%95-a0ec8344a6bd
https://writeablog.net/mzlw3kmb0y
https://viastoer.blogspot.com/2024/09/blog-post_79.html
https://ameblo.jp/naveridbuy/entry-12866333398.html
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94%EC%99%80-%EA%B4%80%EB%A0%A8%EB%90%9C-%EC%B5%9C%EC%8B%A0-%EB%B3%B4%EC%95%88-%EC%9D%B4%EC%8A%88-4569786b88d3
https://hallbook.com.br/blogs/376913/%EC%95%84%EC%9D%B4%EB%94%94-%EA%B1%B0%EB%9E%98%EC%9D%98-%EC%88%A8%EA%B2%A8%EC%A7%84-%EC%9C%84%ED%97%98-%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EC%95%88%EC%A0%84%ED%95%98%EA%B2%8C-%EC%A7%80%ED%82%A4%EB%8A%94-%EB%B2%95
https://candid-lion-dd3cm3.mystrikingly.com/blog/8085327d927
https://adaptable-camellia-dd3cm4.mystrikingly.com/blog/79c90dfb696
https://candid-lion-dd3cm3.mystrikingly.com/blog/6f5ea7ec9c8
https://naveridbuy.exblog.jp/37091141/
https://inky-owl-dd3cmv.mystrikingly.com/blog/5
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EB%B9%84%EB%B0%80%EB%B2%88%ED%98%B8-%EB%B3%B5%EA%B5%AC%ED%95%98%EB%8A%94-5%EA%B0%80%EC%A7%80-%EB%B0%A9%EB%B2%95-216aafd6cf7c
https://medium.com/@1kelly76/%EB%B0%9C%EA%B8%B0%EB%B6%80%EC%A0%84-%EC%B9%98%EB%A3%8C%EC%A0%9C%EC%9D%98-%EC%A2%85%EB%A5%98%EC%99%80-%ED%9A%A8%EA%B3%BC-%EB%B9%84%EA%B5%90-503615121a7b
https://ko.anotepad.com/note/read/739hqxea
I really like it when people get together and share opinions. Great blog, keep it up!
https://gajweor.pixnet.net/blog/post/162874708
https://inky-owl-dd3cmv.mystrikingly.com/blog/1f98f73959a
https://inky-owl-dd3cmv.mystrikingly.com/blog/f111c3c7d0d
https://naveridbuy.blogspot.com/2024/12/blog-post_37.html
https://adaptable-camellia-dd3cm4.mystrikingly.com/blog/70aed56e7e8
https://candid-lion-dd3cm3.mystrikingly.com/blog/6f5ea7ec9c8
https://hallbook.com.br/blogs/376905/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EC%97%86%EC%9D%B4-%EC%84%9C%EB%B9%84%EC%8A%A4-%EC%9D%B4%EC%9A%A9%ED%95%98%EB%8A%94-%ED%8C%81
https://naveridbuy.exblog.jp/35891786/
https://xn--fc-hd0jg6f81ltjas9lbns.mystrikingly.com/blog/dcd84c3fc9c
https://candid-lion-dd3cm3.mystrikingly.com/blog/2024
https://naveridbuy.blogspot.com/2024/12/blog-post_3.html
https://xn--w5-hd0jg6f81lm0dhhw74c.mystrikingly.com/blog/7dbe3159553
https://medium.com/@carlfrancoh38793/%EC%A4%91%EA%B3%A0-%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94%EB%A5%BC-%ED%9A%A8%EA%B3%BC%EC%A0%81%EC%9C%BC%EB%A1%9C-%ED%99%9C%EC%9A%A9%ED%95%98%EB%8A%94-%EB%B0%A9%EB%B2%95-a5bd35053073
techsoft kurumsal web tasarım e-ticaret web sitesi
I am really loving the theme/design of your blog. Do you ever
run into any browser compatibility issues?
A few of my blog visitors have complained about my site not operating correctly in Explorer but looks great in Firefox.
Do you have any solutions to help fix this issue?
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%EC%A0%95%ED%92%88-%ED%99%95%EC%9D%B8%ED%95%98%EB%8A%94-5%EA%B0%80%EC%A7%80-%EB%B0%A9%EB%B2%95-10-10
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EC%A0%95%EB%A7%90-%ED%95%84%EC%9A%94%ED%95%9C%EA%B0%80-%EA%B5%AC%EB%A7%A4-%EC%9D%B4%EC%9C%A0-10%EA%B0%80%EC%A7%80-72aec4ea7fe1
Hi there! This post couldn’t be written much better! Going through this article reminds me of my previous roommate! He always kept talking about this. I most certainly will send this article to him. Fairly certain he’s going to have a good read. Thank you for sharing!
https://viastoer.blogspot.com/2024/08/blog-post_28.html
https://hallbook.com.br/blogs/376906/%EB%84%A4%EC%9D%B4%EB%B2%84-%EA%B3%84%EC%A0%95-%EA%B4%80%EB%A6%AC-%EB%B0%8F-%EB%8B%A4%EC%A4%91-%EC%95%84%EC%9D%B4%EB%94%94-%EC%83%9D%EC%84%B1-%EB%B0%A9%EB%B2%95-%EA%B0%80%EC%9D%B4%EB%93%9C
I enjoy looking through a post that can make people think. Also, thanks for allowing for me to comment.
Nice post. I learn something new and challenging on websites I stumbleupon every day.
It’s always helpful to read content from other
authors and use a little something from their web sites.
Look at my webpage; is prostadine sold in stores
I am genuinely thankful to the owner of this
web page who has shared this fantastic post at here.
Here is my blog – Sight Care Reviews Consumer Reports
I always emailed this website post page to all my associates, for the reason that if like to read it then my links will too.
Here is my web blog :: what is pronerve 6
I am really grateful to the holder of this
website who has shared this great paragraph at at this place.
my blog free suga pro reviews
This design is wicked! You certainly know how to keep a reader amused.
Between your wit and your videos, I was almost moved to start
my own blog (well, almost…HaHa!) Wonderful job. I really loved
what you had to say, and more than that, how you presented it.
Too cool!
Here is my website … herpafend walgreens
Asking questions are really fastidious thing if you are not
understanding anything totally, except this paragraph provides
pleasant understanding yet.
Here is my site lung nutra lung clear pro
I love your blog.. very nice colors & theme. Did you create this website yourself or did you hire
someone to do it for you? Plz respond as I’m looking to create my own blog and would like to know where u got
this from. many thanks
My web page :: flow force max get
I love what you guys tend to be up too. Such clever work and reporting!
Keep up the awesome works guys I’ve incorporated you guys to my personal blogroll.
Check out my blog post – lottery defeater software
When I originally commented I clicked the
“Notify me when new comments are added” checkbox
and now each time a comment is added I get three emails with the same
comment. Is there any way you can remove people from that
service? Many thanks!
Here is my page – boost xt vs bolt aes
What’s up mates, nice article and good urging commented at
this place, I am truly enjoying by these.
Here is my web page – fitspresso nz
Hmm it looks like your site ate my first comment (it was
extremely long) so I guess I’ll just sum it up what I had written and say, I’m
thoroughly enjoying your blog. I too am an aspiring blog blogger but
I’m still new to the whole thing. Do you have
any points for beginner blog writers? I’d genuinely appreciate it.
Look at my blog; does mitolyn really work
I’m gone to tell my little brother, that he should also go
to see this web site on regular basis to obtain updated from newest
reports.
my web blog; is lung clear pro legit
Heya excellent blog! Does running a blog similar to this take a massive amount work?
I’ve virtually no understanding of programming however I was hoping
to start my own blog in the near future. Anyways, if you have any recommendations or tips
for new blog owners please share. I understand this
is off topic nevertheless I simply wanted to ask.
Thank you!
My homepage :: leanbiome customer service
Hi there! Would you mind if I share your blog
with my twitter group? There’s a lot of people that I think would really appreciate your content.
Please let me know. Thanks
Here is my blog post – cody morgan tonic greens
Thank you, I’ve just been searching for info approximately this topic for a
long time and yours is the greatest I’ve discovered so far.
But, what concerning the conclusion? Are you certain about the source?
Look into my website – get sight care.org
I constantly spent my half an hour to read this website’s articles daily along with
a cup of coffee.
Feel free to surf to my homepage … animale male enhancement gummies review
Admiring the hard work you put into your website and detailed information you present.
It’s awesome to come across a blog every once in a while that isn’t the same old rehashed material.
Excellent read! I’ve bookmarked your site and I’m adding your
RSS feeds to my Google account.
my web blog :: does the lottery defeater software really work
What’s up Dear, are you actually visiting this website daily, if so after that you will without doubt obtain fastidious know-how.
Check out my webpage … alpha bites near me
I do not even understand how I stopped up right here, but I believed this post was once good.
I don’t recognise who you might be but certainly you’re going to a well-known blogger for
those who are not already. Cheers!
Feel free to visit my webpage; lottery defeated software is it a scam
Hi everyone, it’s my first go to see at this site, and piece of writing is truly fruitful in favor of me, keep up posting these posts.
Review my web-site lottery defeated software free
I have to thank you for the efforts you’ve put in penning this website.
I really hope to see the same high-grade content from you later on as well.
In truth, your creative writing abilities has encouraged me
to get my own, personal blog now 😉
Stop by my homepage … herpesyl
Thank you for every other informative website. Where else
may I am getting that kind of information written in such an ideal method?
I have a venture that I’m simply now working on, and I’ve
been at the glance out for such info.
My site: gluco freedom review
Magnificent goods from you, man. I’ve understand your stuff
previous to and you are just extremely fantastic. I really like what you have acquired
here, certainly like what you’re saying and the way in which you say it.
You make it enjoyable and you still take care of to keep it
sensible. I cant wait to read much more from you.
This is really a terrific web site.
Look at my blog :: pro nerve 6 for neuropathy
I believe that is among the so much important info for me.
And i’m happy studying your article. But want to remark on some normal things, The website style is wonderful,
the articles is really great : D. Excellent job, cheers
My webpage: can prodentim regrow teeth
Hi, i think that i saw you visited my blog thus i came to “return the
favor”.I am attempting to find things to enhance my site!I suppose its ok to use a few of your ideas!!
Feel free to visit my web page – leanbiome reviews
Spot on with this write-up, I honestly believe this web site needs
far more attention. I’ll probably be back again to read
through more, thanks for the advice!
Have a look at my blog post lottery defeater software a scam
When someone writes an piece of writing he/she maintains the thought of a user in his/her mind
that how a user can be aware of it. So that’s why this post is perfect.
Thanks!
My web blog – tonic greens reviews
Thanks for your personal marvelous posting! I
truly enjoyed reading it, you are a great author.
I will be sure to bookmark your blog and may
come back in the foreseeable future. I want to encourage yourself
to continue your great posts, have a nice weekend!
Here is my site; free sugar pro review
Good way of telling, and fastidious paragraph to get facts about my presentation subject, which
i am going to deliver in school.
Review my webpage … prodentim reviews
I used to be recommended this website via my cousin. I am not positive whether this submit is written via him as no one
else recognize such targeted approximately my difficulty.
You’re incredible! Thanks!
Also visit my blog :: tonic greens herpes cure
I like the valuable info you provide in your articles.
I will bookmark your blog and check again here regularly.
I’m quite certain I will learn plenty of new stuff right here!
Best of luck for the next!
Here is my website; does herpafend really work
There is definately a great deal to find out about this subject.
I love all of the points you made.
My page: tonic greens work
Hello, just wanted to tell you, I enjoyed this blog post.
It was helpful. Keep on posting!
Here is my web-site – purdentix pro dentim advanced oral probiotics reviews
Thanks for every other informative web site.
The place else may just I am getting that kind of information written in such an ideal method?
I have a challenge that I am simply now running on, and I’ve
been on the glance out for such info.
Review my homepage :: provadent users results
If you are going for finest contents like me, just pay a quick visit this site every day for the reason that
it provides quality contents, thanks
Feel free to surf to my web site – testoprim-d rems program
Hi, of course this piece of writing is really nice and I
have learned lot of things from it concerning blogging.
thanks.
Also visit my webpage :: herpesyl reviews 2021
Very shortly this site will be famous among all blogging viewers, due to it’s pleasant content
Feel free to visit my webpage … red boost reviews
I’m impressed, I have to admit. Seldom do I encounter a blog that’s equally
educative and engaging, and without a doubt, you have hit the nail on the head.
The problem is something too few men and women are speaking intelligently about.
I am very happy I stumbled across this in my search for something relating to this.
My homepage: red boost tonic review
Pretty! This was an extremely wonderful article. Thanks for supplying this information.
Feel free to visit my site; lottery defeated software review
This is a topic that’s near to my heart… Thank you! Where
are your contact details though?
Also visit my website prostadine complaints
What i don’t understood is in truth how you’re no longer really a lot more well-appreciated than you may be right now.
You are so intelligent. You recognize therefore
significantly with regards to this subject, made me in my opinion believe it from so
many various angles. Its like women and men are not interested unless it’s something
to accomplish with Girl gaga! Your individual stuffs great.
At all times take care of it up!
Look into my site prodentim how to use
I’m gone to tell my little brother, that he should also go to see
this web site on regular basis to get updated from most up-to-date information.
Feel free to visit my site – the growth matrix.
I enjoy what you guys are up too. This type of clever work and reporting!
Keep up the excellent works guys I’ve incorporated you guys to blogroll.
Also visit my site :: tonic greens at walmart
An intriguing discussion is worth comment.
I do believe that you need to write more on this subject matter, it might
not be a taboo matter but typically people do not talk about these subjects.
To the next! Best wishes!!
my web blog: memory wave
I believe everything posted made a ton of sense. However,
what about this? what if you added a little content?
I am not saying your content is not solid, however suppose you added a headline that grabbed people’s
attention? I mean Deploy AWS Public, Private Subnet
& Route Table Creation & Associate
Using CloudFormation – DheerajTechInsight is kinda plain. You
ought to glance at Yahoo’s home page and note
how they write post titles to get people to click. You might add a video
or a pic or two to get readers excited about what you’ve written. In my opinion, it might make your website a
little bit more interesting.
Here is my web site is fitspresso safe and effective
Even amateur investors jumped onto the bandwagon, hoping to make a share of the pie.
There is certainly a lot to find out about this issue. I really like all the points you have made.
Whoa! This blog looks just like my old one! It’s on a
totally different topic but it has pretty much the same layout and
design. Great choice of colors!
My web blog … animale male enhancement uruguay
https://viastoer.blogspot.com/2024/07/blog-post_86.html
Those that rely on these points are completely different from those that worship level quantity 1. Those who take measurements are nicely conscious that irrespective of how exact the measurements are, they will not help them generate anticipated outcomes.
You are so awesome! I don’t think I’ve read a single thing like that before. So wonderful to discover someone with original thoughts on this subject matter. Really.. many thanks for starting this up. This site is one thing that’s needed on the internet, someone with a little originality.
https://xn--gq-2e2i723b91ktjas9l307b.mystrikingly.com/blog/75a1b170e58
https://hallbook.com.br/blogs/313007/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%ED%9A%A8%EA%B3%BC%EC%A0%81%EC%9D%B8-%EC%82%AC%EC%9A%A9%EB%B2%95%EA%B3%BC-%EA%B4%80%EB%A6%AC-%ED%8C%81
https://candid-lion-dd3cm3.mystrikingly.com/blog/8085327d927
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%EA%B4%91%EA%B3%A0-%EA%B4%80%EB%A6%AC%EC%97%90-%ED%99%9C%EC%9A%A9%ED%95%98%EB%8A%94-%EB%B0%A9%EB%B2%95-6a822042a160
The Kids’s Museum of Indianapolis is the world’s largest children’s museum.
If this is the case recession is part and parcel of business or of the economy in general.
https://writeablog.net/37n5a9w9yv
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94%EA%B0%80-%ED%95%84%EC%9A%94%ED%95%A0-%EB%95%8C-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EB%8B%B5%EC%9D%BC%EA%B9%8C-4bbacce4d7df
https://writeablog.net/jr525di7pj
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%B9%B4%ED%8E%98-%EC%9A%B4%EC%98%81%EC%9D%84-%EC%9C%84%ED%95%9C-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%8C%81-eb39c3e24984
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%95%A9%EB%B2%95%EC%9D%B8%EA%B0%80%EC%9A%94-%EC%95%8C%EC%95%84%EB%B4%85%EC%8B%9C%EB%8B%A4-40dff2b624f5
I was able to find good information from your blog articles.
https://naveridbuy.exblog.jp/37091141/
https://candid-lion-dd3cm3.mystrikingly.com/blog/9cd12105d44
https://witty-apple-dd3cm1.mystrikingly.com/blog/fc35efb2e09
https://naveridbuy.blogspot.com/2024/11/blog-post_95.html
https://naveridbuy.blogspot.com/2024/11/5_28.html
https://inky-owl-dd3cmv.mystrikingly.com/blog/5
In case you are searching for an much more thrilling version of Canasta, the following section will review the basics of Pennies from Heaven, which requires scoring 20,000 points to win.
Beevers was the husband of former Physician Who companion Caroline John and had beforehand appeared in a small position within the Ambassadors of Demise and because the reincarnated Grasp in Tom Baker’s penultimate story The Keeper of Traken.
https://ko.anotepad.com/note/read/q767x3iy
https://ko.anotepad.com/note/read/wyj88hps
After exploring a few of the blog articles on your site, I truly appreciate your way of writing a blog. I book marked it to my bookmark webpage list and will be checking back soon. Take a look at my web site as well and let me know how you feel.
https://xn--2i0bm4pssb87h9pkd4y3jb.mystrikingly.com/blog/3731e9afa8a
https://viastoer.blogspot.com/2024/09/blog-post_41.html
https://inky-owl-dd3cmv.mystrikingly.com/blog/570378fab9f
https://naveridbuy.blogspot.com/2024/11/2024.html
https://writeablog.net/i676tpbaz7
https://naveridbuy.blogspot.com/2024/11/2024.html
Oh my goodness! Impressive article dude! Many thanks, However I am having difficulties with your RSS. I don’t know why I can’t subscribe to it. Is there anyone else getting similar RSS problems? Anybody who knows the answer will you kindly respond? Thanx.
Some scenes within the movie have been shot in a junkyard which Eddie, played by Michael Paré, calls the Palace Depression.
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EA%B3%84%EC%A0%95-%EA%B4%80%EB%A6%AC-%EB%B0%8F-%EB%8B%A4%EC%A4%91-%EC%95%84%EC%9D%B4%EB%94%94-%EC%83%9D%EC%84%B1-%EB%B0%A9%EB%B2%95-%EA%B0%80%EC%9D%B4%EB%93%9C-12-13
https://medium.com/@charlielevesque328/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%ED%9A%A8%EA%B3%BC%EC%99%80-%EA%B5%AC%EB%A7%A4-%EC%8B%9C-%EC%A3%BC%EC%9D%98%EC%82%AC%ED%95%AD-%EC%B4%9D%EC%A0%95%EB%A6%AC-165d650962af
Appreciate the recommendation. Will try it out.
https://ingenious-lark-dbgzhj.mystrikingly.com/blog/eb1861a7256
certainly like your web site however you have to take a
look at the spelling on several of your posts.
Several of them are rife with spelling issues and I find it
very troublesome to inform the truth however I will definitely come back again.
Hello i am kavin, its my first occasion to commenting anywhere, when i read this paragraph i thought i could also make comment
due to this good article.
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EC%9D%B8%EA%B8%B0-%EC%9E%88%EB%8A%94-%EC%9D%B4%EC%9C%A0%EB%A5%BC-%EC%95%8C%EC%95%84%EB%B3%B4%EC%9E%90-854637610dd2
https://witty-apple-dd3cm1.mystrikingly.com/blog/bf0bc875058
Hi great website! Does running a blog similar to this require a great deal of work?
I have very little understanding of coding however I was hoping
to start my own blog in the near future. Anyway, should you have any ideas or techniques for new blog
owners please share. I know this is off subject however I simply needed to ask.
Cheers!
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4%EB%A5%BC-%EC%9C%84%ED%95%9C-%EC%A0%84%EB%AC%B8%EA%B0%80%EC%9D%98-%EC%A1%B0%EC%96%B8-09-26
https://inky-owl-dd3cmv.mystrikingly.com/blog/9dacaeed43a
https://hallbook.com.br/blogs/313010/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%8B%9C-%EA%B6%81%EA%B8%88%ED%95%9C-%EC%A7%88%EB%AC%B8%EA%B3%BC-%EB%8B%B5%EB%B3%80
https://sociable-corn-dd3cmt.mystrikingly.com/blog/f07125d1958
You have made some really good points there. I looked on the web for more info about the issue and found
most people will go along with your views on this site.
Visit my page :: testoprime transformation
This is a good tip particularly to those fresh to the blogosphere. Brief but very precise information… Thank you for sharing this one. A must read article!
https://inky-owl-dd3cmv.mystrikingly.com/blog/9dacaeed43a
https://gold-gull-dd3cmf.mystrikingly.com/blog/58fe76cd6ee
https://naveridbuy.blogspot.com/2024/12/blog-post_36.html
https://gold-gull-dd3cmf.mystrikingly.com/blog/ed073ff0ca8
https://gold-gull-dd3cmf.mystrikingly.com/blog/0168a471da6
https://naveridbuy.blogspot.com/2024/12/blog-post_2.html
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B1%B0%EB%9E%98%EB%8A%94-%EC%95%88%EC%A0%84%ED%95%9C%EA%B0%80-%EC%A0%84%EB%AC%B8%EA%B0%80%EC%9D%98-%EC%A1%B0%EC%96%B8-12-13-2
https://witty-apple-dd3cm1.mystrikingly.com/blog/7e37e3ff366
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%B9%B4%ED%8E%98-%EC%9A%B4%EC%98%81%EC%9D%84-%EC%9C%84%ED%95%9C-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%8C%81-eb39c3e24984
In 1996, New York Times columnist Thomas Friedman pointed out that no two countries with a McDonald’s had fought a war against one another.
https://naveridbuy.blogspot.com/2024/12/blog-post_76.html
I really like it when people come together and share opinions. Great site, stick with it.
https://xn--w3-hd0jg6f81lm0dhhw74c.mystrikingly.com/blog/633b5d0c891
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%86%8C%EC%85%9C-%EB%AF%B8%EB%94%94%EC%96%B4%EB%A5%BC-%ED%99%9C%EC%9A%A9%ED%95%9C-%EC%A0%95%EB%B3%B4-%EC%B0%BE%EA%B8%B0-41a0f6743e53
Getting a certificate after solely two years of examine at a group college can open doors to much better-paying employment.
https://naveridbuy.exblog.jp/37091209/
https://gold-gull-dd3cmf.mystrikingly.com/blog/58fe76cd6ee
https://witty-apple-dd3cm1.mystrikingly.com/blog/6e9742ef068
https://xn--w2-hd0j99gyns5z0qeiim2i.mystrikingly.com/blog/f803065301b
https://gajweor.pixnet.net/blog/post/162317122
Howdy! I just want to offer you a big thumbs up for your great information you’ve got here on this post. I am coming back to your website for more soon.
https://medium.com/@1kelly76/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%EB%B6%80%EC%9E%91%EC%9A%A9-%EB%8C%80%EC%B2%98%EB%B2%95-52675767f799
https://hallbook.com.br/blogs/278114/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%8B%9C-%EA%B3%A0%EB%A0%A4%ED%95%B4%EC%95%BC-%ED%95%A0-%EA%B0%9C%EC%9D%B8%EC%A0%81%EC%9D%B8-%EA%B1%B4%EA%B0%95-%EC%9A%94%EC%86%8C
iş kazası rapor parası ne kadar
My partner and I stumbled over here different page and thought I might check things
out. I like what I see so now i’m following you.
Look forward to looking over your web page again.
You’ve made some decent points there. I looked on the net for more information about the issue and found most people will go along with your views on this web site.
https://medium.com/@1kelly76/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%8B%9C-%ED%95%84%EC%88%98-%EC%B2%B4%ED%81%AC%EB%A6%AC%EC%8A%A4%ED%8A%B8-7804d3582841
https://smart-elk-dbgzhf.mystrikingly.com/blog/ccc3f510ffc
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%8B%9C-%EC%B2%B4%ED%81%AC%EB%A6%AC%EC%8A%A4%ED%8A%B8-%EC%8B%A4%EC%88%98-%EC%97%86%EC%9D%B4-%EC%95%88%EC%A0%84%ED%95%98%EA%B2%8C-%EA%B5%AC%EC%9E%85%ED%95%98%EA%B8%B0-b5e5644c7578
https://golden-grape-dd3cml.mystrikingly.com/blog/4644761650e
https://writeablog.net/bzmd5ls4rc
https://writeablog.net/nujuali38e
https://golden-grape-dd3cml.mystrikingly.com/blog/79bb6bc939e
https://witty-apple-dd3cm1.mystrikingly.com/blog/6e9742ef068
https://hallbook.com.br/blogs/376911/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%EC%A0%95%EB%A7%90-%EC%95%88%EC%A0%84%ED%95%A0%EA%B9%8C
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC%EC%99%80-%EC%84%B1-%EA%B1%B4%EA%B0%95-%EC%95%8C%EC%95%84%EB%91%90%EB%A9%B4-%EC%A2%8B%EC%9D%80-%EC%A0%95%EB%B3%B4%EB%93%A4-09-12
https://sociable-corn-dd3cmt.mystrikingly.com/blog/f07125d1958
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EC%97%86%EC%9D%B4-%EC%84%9C%EB%B9%84%EC%8A%A4-%EC%9D%B4%EC%9A%A9%ED%95%98%EB%8A%94-%ED%8C%81-12-13
I’m really impressed with your writing skills and also with the layout
on your blog. Is this a paid theme or did you modify it
yourself? Anyway keep up the nice quality writing, it is rare to
see a nice blog like this one these days.
My web blog; java burn coffee.co
This is the right website for anybody who wishes to find out about this topic. You know a whole lot its almost hard to argue with you (not that I personally would want to…HaHa). You certainly put a fresh spin on a subject that’s been discussed for a long time. Wonderful stuff, just excellent.
https://candid-lion-dd3cm3.mystrikingly.com/blog/5037f72f44c
https://ocher-cat-dd3cmm.mystrikingly.com/blog/642842abd0f
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B1%B0%EB%9E%98%EB%8A%94-%EC%95%88%EC%A0%84%ED%95%9C%EA%B0%80-%EC%A0%84%EB%AC%B8%EA%B0%80%EC%9D%98-%EC%A1%B0%EC%96%B8-12-13
https://writeablog.net/vh97m08dqv
https://tawny-wombat-dd3cmn.mystrikingly.com/blog/07fb575d4e0
https://naveridbuy.exblog.jp/37152040/
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%82%AC%EC%9D%B4%ED%8A%B8-be7ed9932b6f
https://inky-owl-dd3cmv.mystrikingly.com/blog/e5d41afa610
bookmarked!!, I really like your site!
Here is my site: gluco freedom amazon
https://hallbook.com.br/blogs/274042/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%8C%81-%ED%95%A9%EB%A6%AC%EC%A0%81%EC%9D%B8-%EA%B0%80%EA%B2%A9%EC%97%90-%EA%B5%AC%EC%9E%85%ED%95%98%EB%8A%94-%EB%B2%95
https://medium.com/@charlielevesque328/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EC%98%A8%EB%9D%BC%EC%9D%B8-%EA%B5%AC%EB%A7%A4-%ED%9B%84%EA%B8%B0%EC%99%80-%EC%A3%BC%EC%9D%98%ED%95%B4%EC%95%BC-%ED%95%A0-%EC%A0%90%EB%93%A4-4a51bcd6c007
https://candid-lion-dd3cm3.mystrikingly.com/blog/2024
Wonderful post! We are linking to this great content on our site. Keep up the great writing.
https://hallbook.com.br/blogs/376901/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B1%B0%EB%9E%98%EB%8A%94-%EC%95%88%EC%A0%84%ED%95%9C%EA%B0%80-%EC%A0%84%EB%AC%B8%EA%B0%80%EC%9D%98-%EC%A1%B0%EC%96%B8
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EB%AC%B8%EC%A0%9C%EB%A5%BC-%ED%95%B4%EA%B2%B0%ED%95%98%EB%8A%94-%ED%95%A9%EB%B2%95%EC%A0%81%EC%9D%B8-%EB%B0%A9%EB%B2%95-12-13
https://gold-gull-dd3cmf.mystrikingly.com/blog/0168a471da6
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EC%9D%B8%EA%B8%B0-%EC%9E%88%EB%8A%94-%EC%9D%B4%EC%9C%A0%EB%A5%BC-%EC%95%8C%EC%95%84%EB%B3%B4%EC%9E%90-854637610dd2
https://naveridbuy.blogspot.com/2024/12/blog-post_27.html
https://naveridbuy.blogspot.com/2024/11/2024.html
https://writeablog.net/9tndlpy4rw
https://intelligent-deer-dbgzhl.mystrikingly.com/blog/821cc0a158a
https://viastoer.blogspot.com/2024/09/blog-post_82.html
Hi there are using WordPress for your site platform? I’m new to the blog
world but I’m trying to get started and set up my own. Do
you require any html coding expertise to make your own blog?
Any help would be greatly appreciated!
Here is my web-site – fitspresso vs java burn
When I originally commented I clicked the -Notify me when new surveys are added- checkbox and after this if a comment is added I purchase four emails with the exact same comment. Can there be that is you can remove me from that service? Thanks!
https://hallbook.com.br/blogs/295250/%EB%B0%9C%EA%B8%B0%EB%B6%80%EC%A0%84%EA%B3%BC-%EC%A1%B0%EB%A3%A8-%EC%9E%90%EC%97%B0-%EC%B9%98%EB%A3%8C%EC%99%80-%EC%9D%98%ED%95%99%EC%A0%81-%EC%A0%91%EA%B7%BC%EB%B2%95-%EB%B9%84%EA%B5%90
https://naveridbuy.exblog.jp/35878151/
Aw, this was an exceptionally good post. Finding the time and actual effort to generate a superb article… but what can I say… I hesitate a whole lot and don’t manage to get anything done.
https://crimson-elephant-dbgzh3.mystrikingly.com/blog/a1467ba1967
https://naveridbuy.blogspot.com/2024/11/2024.html
https://gajweor.pixnet.net/blog/post/157629283
https://maize-wombat-dd3cms.mystrikingly.com/blog/dad3e41e83f
https://naveridbuy.blogspot.com/2024/11/5_28.html
I enjoy reading an article that will make men and women think. Also, many thanks for allowing for me to comment.
https://hallbook.com.br/blogs/274042/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%8C%81-%ED%95%A9%EB%A6%AC%EC%A0%81%EC%9D%B8-%EA%B0%80%EA%B2%A9%EC%97%90-%EA%B5%AC%EC%9E%85%ED%95%98%EB%8A%94-%EB%B2%95
https://compassionate-kiwi-dbgzhg.mystrikingly.com/blog/ebba0025dc8
I think that what you posted made a great deal of sense.
However, what about this? suppose you added a little information? I ain’t suggesting
your content is not good., but what if you added a headline to possibly grab people’s
attention? I mean Deploy AWS Public, Private Subnet & Route Table Creation &
Associate Using CloudFormation – DheerajTechInsight
is kinda plain. You ought to peek at Yahoo’s front page and see how
they create news headlines to grab people to open the links.
You might add a related video or a related pic or two to grab people interested about what you’ve got to say.
Just my opinion, it would bring your blog a little livelier.
Take a look at my webpage: java burn video
https://ko.anotepad.com/note/read/739hqxea
https://xn--w6-hd0jg6f81lm0dhhw74c.mystrikingly.com/blog/9bea3d272ae
Whats up this is kind of of off topic but I was wanting to know if blogs use
WYSIWYG editors or if you have to manually code with HTML.
I’m starting a blog soon but have no coding know-how so I wanted to get guidance from
someone with experience. Any help would be greatly appreciated!
my web-site; where to buy phenq uk
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%8B%A0%EB%A2%B0%ED%95%A0-%EC%88%98-%EC%9E%88%EB%8A%94-%ED%8C%90%EB%A7%A4%EC%B2%98-%EC%B0%BE%EA%B8%B0-07-31
https://viastoer.blogspot.com/2024/07/blog-post_45.html
https://naveridbuy.exblog.jp/37152120/
https://naveridbuy.blogspot.com/2024/11/blog-post_50.html
https://inky-owl-dd3cmv.mystrikingly.com/blog/1f98f73959a
https://naveridbuy.exblog.jp/37091323/
https://hallbook.com.br/blogs/376908/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%EB%8C%80%EC%8B%A0-%EC%82%AC%EC%9A%A9%ED%95%A0-%EC%88%98-%EC%9E%88%EB%8A%94-%EB%B0%A9%EB%B2%95%EB%93%A4
https://naveridbuy.blogspot.com/2024/11/blog-post_28.html
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94%EC%99%80-%EA%B4%80%EB%A0%A8%EB%90%9C-%EC%B5%9C%EC%8B%A0-%EB%B3%B4%EC%95%88-%EC%9D%B4%EC%8A%88-4569786b88d3
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%EA%B4%91%EA%B3%A0-%EA%B4%80%EB%A6%AC%EC%97%90-%ED%99%9C%EC%9A%A9%ED%95%98%EB%8A%94-%EB%B0%A9%EB%B2%95-6a822042a160
https://ko.anotepad.com/note/read/8iqcnqkc
https://optimistic-rabbit-dbgzhd.mystrikingly.com/blog/786e23386cd
I couldn’t resist commenting. Exceptionally well written!
[…]very few websites that happen to be detailed below, from our point of view are undoubtedly well worth checking out[…]…
https://naveridbuy.exblog.jp/37152070/
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EC%9D%B8%EA%B8%B0-%EC%9E%88%EB%8A%94-%EC%9D%B4%EC%9C%A0%EB%A5%BC-%EC%95%8C%EC%95%84%EB%B3%B4%EC%9E%90-854637610dd2
https://candid-lion-dd3cm3.mystrikingly.com/blog/b99e214c11a
https://gold-gull-dd3cmf.mystrikingly.com/blog/2a47c25c4d9
https://naveridbuy.exblog.jp/37152083/
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EB%B6%88%EB%9F%AC%EC%98%A4%EB%8A%94-%EB%B3%B4%EC%95%88-%EC%9C%84%ED%97%98-12-13
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EB%B9%84%EB%B0%80%EB%B2%88%ED%98%B8-%EB%B3%B5%EA%B5%AC%ED%95%98%EB%8A%94-5%EA%B0%80%EC%A7%80-%EB%B0%A9%EB%B2%95-216aafd6cf7c
https://naveridbuy.blogspot.com/2024/11/blog-post_3.html
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EB%A1%9C-%ED%95%98%EB%A3%A8-%EB%A7%8C%EC%97%90-%EC%8A%A4%EB%A7%88%ED%8A%B8%EC%8A%A4%ED%86%A0%EC%96%B4-%EA%B0%9C%EC%84%A4%ED%95%98%EA%B8%B0-439f0195fc49
https://candid-lion-dd3cm3.mystrikingly.com/blog/53469580831
Hello! I simply would choose to provide a large thumbs up for any great info you have here about this post. We are coming back to your site to get more soon.
I have to thank you for the efforts you’ve put in writing this website. I really hope to see the same high-grade content by you later on as well. In fact, your creative writing abilities has encouraged me to get my own, personal site now 😉
https://naveridbuy.exblog.jp/37152057/
https://medium.com/@carlfrancoh38793/%EC%A4%91%EA%B3%A0-%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94%EB%A5%BC-%ED%9A%A8%EA%B3%BC%EC%A0%81%EC%9C%BC%EB%A1%9C-%ED%99%9C%EC%9A%A9%ED%95%98%EB%8A%94-%EB%B0%A9%EB%B2%95-a5bd35053073
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EB%A1%9C-%ED%95%98%EB%A3%A8-%EB%A7%8C%EC%97%90-%EC%8A%A4%EB%A7%88%ED%8A%B8%EC%8A%A4%ED%86%A0%EC%96%B4-%EA%B0%9C%EC%84%A4%ED%95%98%EA%B8%B0-439f0195fc49
https://candid-lion-dd3cm3.mystrikingly.com/blog/8c25ae9d7a9
https://gold-gull-dd3cmf.mystrikingly.com/blog/ed073ff0ca8
Pretty! This has been an incredibly wonderful article. Thanks for providing these details.
https://candid-lion-dd3cm3.mystrikingly.com/blog/8c25ae9d7a9
https://gajweor.pixnet.net/blog/post/162874435
https://xn--w8-hd0j99gyns5z0qeiim2i.mystrikingly.com/blog/eccfb215edf
https://naveridbuy.exblog.jp/35452731/
https://gajweor.pixnet.net/blog/post/164185456
Let us not think of each other as enemies as we are friends for sure.
Useful info. Fortunate me I discovered your web site by accident, and I’m surprised why this coincidence did not came about earlier! I bookmarked it.
Good day! I could have sworn I’ve been to this website before but after looking at many of the posts I realized it’s new to me. Regardless, I’m certainly happy I stumbled upon it and I’ll be bookmarking it and checking back regularly!
Lots of people earn cash on the web by opening up an eBay public sale site and selling issues from their house.
College students inquiry the work together, the amiss time could by no means regret to uncover their instigate, absolute to ditch out of teach in the activity, after all, there will have the ability to entrance others to do youthful man.
https://hallbook.com.br/blogs/376912/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%EA%B3%84%EC%A0%95-%EC%A0%95%EC%A7%80-%EC%82%AC%EB%A1%80%EC%99%80-%EB%8C%80%EC%B2%98%EB%B2%95
https://naveridbuy.exblog.jp/37090971/
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EC%9D%B8%EA%B8%B0-%EC%9E%88%EB%8A%94-%EC%9D%B4%EC%9C%A0%EB%A5%BC-%EC%95%8C%EC%95%84%EB%B3%B4%EC%9E%90-854637610dd2
https://naveridbuy.exblog.jp/37152138/
https://witty-apple-dd3cm1.mystrikingly.com/blog/63d61343ce4
https://candid-lion-dd3cm3.mystrikingly.com/blog/6f5ea7ec9c8
https://viastoer.blogspot.com/2024/09/blog-post_61.html
https://temperate-canna-dbgzhf.mystrikingly.com/blog/caf1cbb326b
Excellent post! We are linking to this great content on our website. Keep up the good writing.
https://medium.com/@1kelly76/%EB%B0%9C%EA%B8%B0%EB%B6%80%EC%A0%84%EA%B3%BC-%EC%A1%B0%EB%A3%A8-%EB%8B%B9%EC%8B%A0%EC%9D%B4-%EC%95%8C%EC%95%84%EC%95%BC-%ED%95%A0-%EB%AA%A8%EB%93%A0-%EA%B2%83-da53d6f9e647
Hey there You have done a fantastic job I will certainly digg it and personally recommend to my friends Im confident theyll be benefited from this site
Ahaa, its pleasant discussion on the topic of this post at this place at this weblog, I have read all that, so at
this time me also commenting here.
pay per click programs are really great, i could earn some decent cash from it**
https://ko.anotepad.com/note/read/hfewbt6j
Aw, i thought this was a really nice post. In thought I have to put in writing this way additionally – taking time and actual effort to create a top notch article… but what / things I say… I procrastinate alot by no indicates seem to get something accomplished.
An outstanding share! I’ve just forwarded this onto a colleague who has been doing a little research on this. And he in fact bought me lunch simply because I found it for him… lol. So allow me to reword this…. Thanks for the meal!! But yeah, thanx for spending the time to discuss this topic here on your website.
A 2014 study executed for the aquarium by the University of Tennessee Middle for Sustainable Business and Growth concluded that its annual financial influence is an estimated $101.Three million and over a thousand jobs overall.
https://gajweor.pixnet.net/blog/post/162874321
https://medium.com/@nsw5288/%EC%88%A0%EB%A8%B9%EA%B3%A0-%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EB%A8%B9%EC%9C%BC%EB%A9%B4-0ca4af2b21cd
I have been exploring for a little for any high quality articles or blog posts in this kind of area
. Exploring in Yahoo I eventually stumbled upon this website.
Studying this information So i’m happy to express that I have an incredibly excellent uncanny feeling I found out
just what I needed. I most for sure will
make sure to do not forget this web site and provides
it a glance on a relentless basis.
Have a look at my blog post; prodentim consumer reports complaints
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%EA%B3%84%EC%A0%95-%EC%A0%95%EC%A7%80-%EC%82%AC%EB%A1%80%EC%99%80-%EB%8C%80%EC%B2%98%EB%B2%95-12-13
https://naveridbuy.blogspot.com/2024/12/blog-post_12.html
https://naveridbuy.blogspot.com/2024/11/blog-post_50.html
Superb post however , I was wondering if you could write a litte more
on this subject? I’d be very thankful if you
could elaborate a little bit more. Thanks!
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC%EC%9D%98-%EB%B6%80%EC%9E%91%EC%9A%A9%EA%B3%BC-%EC%95%88%EC%A0%84%ED%95%98%EA%B2%8C-%EB%B3%B5%EC%9A%A9%ED%95%98%EB%8A%94-%EB%B0%A9%EB%B2%95-7b4396b87ed1
https://naveridbuy.blogspot.com/2024/12/blog-post_29.html
Hey very interesting blog!
You may create a draft and submit it for evaluation or request that a redirect be created, however consider checking the search results under to see whether the topic is already coated.
One has her hand flippantly on the piano keys in a dress of pink; her good friend has an elbow resting on the piano in a lovely dress of grey and caramel-colored alternate stripes, complete with repeat tied bows.
Hello, I think your blog may be having web browser compatibility problems. When I look at your blog in Safari, it looks fine however, if opening in I.E., it’s got some overlapping issues. I simply wanted to provide you with a quick heads up! Besides that, wonderful site!
https://medium.com/@1kelly76/%EB%B0%9C%EA%B8%B0%EB%B6%80%EC%A0%84%EA%B3%BC-%EC%A1%B0%EB%A3%A8-%EB%8B%B9%EC%8B%A0%EC%9D%B4-%EC%95%8C%EC%95%84%EC%95%BC-%ED%95%A0-%EB%AA%A8%EB%93%A0-%EA%B2%83-da53d6f9e647
The Qing dynasty also reached its economic peak in 1820, when it became the world’s largest financial system, and contributing to 30 of world GDP.
An outstanding share! I have just forwarded this onto a coworker who was conducting a little research on this. And he actually bought me breakfast simply because I discovered it for him… lol. So let me reword this…. Thank YOU for the meal!! But yeah, thanks for spending the time to discuss this subject here on your website.
This is a very nice post. Thank you for writing this.
Hi there! This is kind of off topic but I need some advice from an established blog. Is it very hard to set up your own blog? I’m not very techincal but I can figure things out pretty quick. I’m thinking about setting up my own but I’m not sure where to start. Do you have any points or suggestions? Thank you
Hello! I recently would like to provide a massive thumbs up for that wonderful information you’ve got here during this post. I will be coming back to your website for additional soon.
Nice Article
You are so cool! I do not believe I’ve read through a single thing like that before. So nice to find someone with a few original thoughts on this subject matter. Really.. many thanks for starting this up. This website is something that’s needed on the internet, someone with a bit of originality.
Insight on high-quality gold jewelleries, Synthetic, imitation, trend & Gold Plated Jewellery Designs, Antique Golds Jewellery Designs, Trendy and Newest Jewellery Designs, Conventional jewellery designs, Enamel golds jewelry designs, Bridal golds jewelleries designs, south indian golds plated jewellery designs and rajasthani jewelleries golds designs for girls and men.
Saved as a favorite, I like your blog!
That drive to know character finally gave delivery to the trendy character take a look at.
An interesting discussion is definitely worth comment. There’s no doubt that that you ought to write more about this topic, it might not be a taboo subject but typically folks don’t discuss these issues. To the next! Kind regards!
Having read this I believed it was very informative. I appreciate you spending some time and energy to put this information together. I once again find myself spending a significant amount of time both reading and leaving comments. But so what, it was still worthwhile.
It’s really a nice and helpful piece of info.
I am happy that you shared this helpful info with us. Please
stay us informed like this. Thank you for sharing.
Touche. Great arguments. Keep up the great spirit.
Everything is very open with a really clear explanation of the challenges. It was definitely informative. Your site is extremely helpful. Thank you for sharing.
Greetings! Very useful advice within this article! It’s the little changes which will make the biggest changes. Thanks for sharing!
Wow, superb blog layout! How long have you been blogging for?
you made blogging look easy. The overall look of your web
site is magnificent, as well as the content!
When the developer finishes building an application, he or she can take a look at it out on the emulator to see how the app will carry out on actual hardware.
Very nice blog post. I definitely love this website. Keep it up!
What a data of un-ambiguity and preserveness of precious experience regarding unexpected emotions.
I am really loving the theme/design of your blog.
Do you ever run into any browser compatibility problems?
A couple of my blog visitors have complained about my blog not working correctly in Explorer but looks
great in Chrome. Do you have any advice to help fix this issue?
When I initially commented I appear to have clicked the -Notify me when new comments are added- checkbox and now every time a comment is added I recieve four emails with the exact same comment. There has to be a way you can remove me from that service? Kudos.
On this mainstream view, commerce deficits aren’t inherently good or unhealthy.
Hello there! I could have sworn I’ve been to this website before but after reading
through some of the post I realized it’s new to me.
Anyhow, I’m definitely happy I found it and I’ll be bookmarking and
checking back often!
My site :: is prostavive safe
The dehumidifiers can have built in electric heaters to heat the pool room air in winter.
It additionally uses building materials which have excessive thermal mass — that means that they retain heat properly — like concrete and tile.
Hi, I do believe this is an excellent site. I stumbledupon it 😉 I will come back yet again since i have bookmarked it. Money and freedom is the greatest way to change, may you be rich and continue to help others.
I’m impressed, I have to admit. Rarely do I come across a blog that’s both educative and entertaining, and without a doubt, you’ve hit the nail on the head.
The issue is something which not enough people are speaking intelligently about.
I am very happy that I found this during my hunt for
something regarding this.
Feel free to visit my web blog :: is zencortex a scam
If you want to get a good deal from this article then you have to apply such methods to
your won webpage.
Look into my page what is femipro
It is appropriate time to make a few plans for the long run and it’s time to be happy.
I have learn this publish and if I could I wish to recommend you some fascinating things or tips.
Perhaps you could write next articles referring
to this article. I want to read even more things approximately it!
Feel free to visit my web blog … lottery defeater software is it legit
Good web site you have here.. It’s hard to find high-quality writing like yours these days. I seriously appreciate individuals like you! Take care!!
I was able to find good advice from your blog posts.
Hello to all, for the reason that I am truly eager of
reading this webpage’s post to be updated daily.
It contains pleasant material.
What i don’t understood is in truth how you are not really much more smartly-liked than you might be
now. You’re so intelligent. You understand therefore significantly
on the subject of this topic, made me in my view imagine it from numerous varied
angles. Its like men and women aren’t fascinated until it is something to accomplish with Girl gaga!
Your own stuffs great. All the time deal with it up!
Pretty! This was a really wonderful article. Thank you for providing this info.
bookmarked!!, I like your web site!
You may also want to purchase liability insurance to protect yourself and your organization.
Be sluggish and steady in the stock trading market and a little experience will assist you decide when to purchase or avoid a stock.
Hi, I do believe this is an excellent site. I stumbledupon it 😉 I’m going to come back once again since i have saved as a favorite it. Money and freedom is the best way to change, may you be rich and continue to help others.
In between numerous erasures you can find given some extent choice undoubtedly used by Commodore Perry on his solution to Japan in 1853.
Several case studies and conditions alleging deception on the a part of the Christian Church are mentioned, and Christianity is blamed for slavery, racism, bodily abuse, the poor treatment of ladies, and much of what ails the human race.
Nice post. I learn something totally new and challenging on sites I stumbleupon every day. It’s always interesting to read content from other authors and practice a little something from their websites.
I do not even know how I ended up here, but I thought this post
was great. I do not know who you are but certainly you’re
going to a famous blogger if you are not already ;
) Cheers!
Spot on with this write-up, I honestly feel this site needs a great deal more attention. I’ll probably be returning to see more,
thanks for the advice!
Right here is the perfect website for anybody who would like to find out about this topic. You know a whole lot its almost tough to argue with you (not that I really will need to…HaHa). You definitely put a new spin on a topic which has been written about for a long time. Wonderful stuff, just excellent.
I just couldn’t leave your website prior to suggesting that
I actually enjoyed the standard info a person supply to your guests?
Is going to be again ceaselessly to check up on new posts
This website was… how do I say it? Relevant!! Finally I have found something that helped me. Appreciate it.
First, has it actually been passed down through family generations?
This spaghetti serving might have anchovies, so beware!
Can I just say what a relief to discover somebody who actually understands what they are talking about online. You certainly know how to bring an issue to light and make it important. More and more people have to look at this and understand this side of your story. I was surprised that you are not more popular because you definitely have the gift.
Your style is very unique compared to other people I have read stuff from. I appreciate you for posting when you’ve got the opportunity, Guess I will just bookmark this blog.
I seriously love your blog.. Excellent colors & theme. Did you make this website yourself? Please reply back as I’m wanting to create my very own blog and would like to find out where you got this from or just what the theme is called. Appreciate it.
Wonderful blog! I found it while browsing on Yahoo News.
Do you have any suggestions on how to get listed in Yahoo News?
I’ve been trying for a while but I never seem to get there!
Cheers
Army rites had been within the Duffield Cemetery in Jay by the Grove American Legion Publish.
amyfjh
Louis Consolation Tiffany (February 18, 1848 – January 17, 1933) was an American artist and designer who labored within the decorative arts and is best identified for his work in stained glass.
Great blog! Is your theme custom made or did you
download it from somewhere? A design like yours with a few simple adjustements would really make my
blog jump out. Please let me know where you got your theme.
Thanks a lot
If you are getting your nails accomplished as soon as every week, location and price will probably be components in your choice, but your first concern ought to at all times be about safety.
That is a great tip especially to those new to the blogosphere. Short but very accurate info… Thanks for sharing this one. A must read post.
It’s very simple to find out any matter on web as compared to textbooks, as
I found this piece of writing at this web page.
This is the perfect web site for anyone who would like to find out about this topic. You realize a whole lot its almost tough to argue with you (not that I really will need to…HaHa). You definitely put a brand new spin on a subject which has been discussed for years. Wonderful stuff, just excellent.
I absolutely love your website.. Pleasant colors & theme. Did you create this amazing site yourself? Please reply back as I’m planning to create my own personal site and want to learn where you got this from or exactly what the theme is called. Thank you!
A motivating discussion is definitely worth comment. I believe that you ought to publish more about this topic, it may not be a taboo matter but usually folks don’t discuss these issues. To the next! Many thanks.
Hi there, You have done an excellent job. I’ll certainly digg it and personally suggest to my friends.
I am confident they will be benefited from this site.
https://digi220sa.netlify.app/research/digi220sa-(280)
It can be really helpful to keep away from black dresses as these often symbolize occasions of mourning.
I’d like to find out more? I’d like to find out more details.
Hey I know this is off topic but I was wondering if you knew of any widgets I could add to my blog that automatically tweet my
newest twitter updates. I’ve been looking for a plug-in like this for quite some time and was hoping maybe you would have some experience with something like this.
Please let me know if you run into anything. I truly enjoy reading your blog and I look forward to your new updates.
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-124/research/je-tall-sf-marketing-(450).html
Adhere to the dress code, and look to bridesmaids or the marriage gown for steerage on daring patterns
or elaborations.
Nice post. I was checking constantly this weblog and I’m
impressed! Very useful information specifically the
closing section 🙂 I handle such information a lot. I used to
be seeking this certain information for a long time.
Thank you and good luck.
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-222/research/je-tall-sf-marketing-(334).html
But it’s essential to examine in with
the bride earlier than you make any selections.
https://jekyll.s3.us-east-005.backblazeb2.com/20241209-12/research/je-tall-sf-marketing-(444).html
For the mom who likes to look put together and modern, a jumpsuit in slate grey is bound to wow.
https://je-tall-sf-marketing-62.research.au-syd1.upcloudobjects.com/research/je-tall-sf-marketing-(181).html
Not certain the place to start along with your seek for that picture-perfect mother-of-the-bride
dress?
Hey there, You’ve done a fantastic job. I will definitely
digg it and personally recommend to my friends. I am confident they will
be benefited from this web site.
Thank you for every other excellent post. The place else may anyone get
that type of information in such an ideal method of writing?
I have a presentation next week, and I’m at the search for such information.
Way cool! Some very valid points! I appreciate you penning this post plus the rest of the website is also really good.
I really like looking through a post that can make people
think. Also, thank you for allowing for me to comment!
Hi there would you mind letting me know which hosting company
you’re working with? I’ve loaded your blog in 3 different internet browsers and I must say this blog loads a
lot quicker then most. Can you recommend a good hosting provider at a honest price?
Thank you, I appreciate it!
çelik konstrüksiyon depo
I will immediately clutch your rss feed as I can not to find your email subscription link or newsletter service.
Do you have any? Kindly permit me know in order that I could subscribe.
Thanks.
b8k7a4
Pretty nice post. I just stumbled upon your blog and wanted to mention that I’ve really enjoyed browsing your
weblog posts. In any case I will be subscribing in your rss
feed and I hope you write again soon!
Heya i’m for the first time here. I came across this board and I find
It really useful & it helped me out a lot. I hope to give
something back and aid others like you helped me.
Also visit my blog; lottery defeater software a scam
buy clomid 100mg online Minor 1 roxithromycin decreases effects of penicillin G aqueous by pharmacodynamic antagonism
Great article! That is the type of info that are meant to be
shared around the net. Disgrace on the search engines for not
positioning this post upper! Come on over and seek advice from
my site . Thank you =)
I pay a quick visit every day some websites and information sites to read
articles, however this webpage gives quality based posts.
Donnelly, Joe (2017-03-23). “Greatest Crusader Kings 2 mods”.
Also, it’s price noting that the laws that police stolen debit playing cards aren’t as pleasant because the legal guidelines that police stolen credit score cards.
What’s up to all, the contents existing at this
web page are truly awesome for people experience, well,
keep up the good work fellows.
You need to be a part of a contest for one of the highest quality websites online. I am going to highly recommend this website!
Then type “devmgmt.msc” (with out the quotation marks) and press Enter.
I’d like to thank you for the efforts you have put in penning this website. I’m hoping to see the same high-grade blog posts from you in the future as well. In fact, your creative writing abilities has inspired me to get my own blog now 😉
I loved as much as you will receive carried out right here.
The sketch is tasteful, your authored subject matter stylish.
nonetheless, you command get got an shakiness over that you wish be delivering the following.
unwell unquestionably come further formerly again since exactly the same nearly a
lot often inside case you shield this increase.
It’s nearly impossible to find experienced people for this topic, however, you seem like you know what you’re talking about! Thanks
çelik konstrüksiyon depo
Hi there! This is my first comment here so I just wanted to
give a quick shout out and tell you I really enjoy reading your articles.
Can you suggest any other blogs/websites/forums that go over
the same subjects? Thanks a lot!
You’ve made some really good points there. I checked on the internet to learn more about the issue and found most individuals will go along with your views on this web site.
Excellent blog you have got here.. It’s hard to find excellent writing like yours nowadays. I seriously appreciate people like you! Take care!!
Having read this I thought it was rather informative. I appreciate you spending some time and effort to put this short article together. I once again find myself spending a significant amount of time both reading and posting comments. But so what, it was still worth it!
If a stock closes at the bottom of its day’s trading range on high volume, consider selling half your shares.
Let dry, and leave the tape in place.
There’s definately a great deal to learn about this topic. I love all the points you have made.
That is a good tip particularly to those new to the blogosphere. Short but very accurate info… Many thanks for sharing this one. A must read article!
Good information. Lucky me I ran across your site by chance (stumbleupon). I have saved as a favorite for later.
An impressive share! I have just forwarded this onto a friend who has been doing a little research on this. And he actually bought me breakfast because I stumbled upon it for him… lol. So let me reword this…. Thanks for the meal!! But yeah, thanks for spending the time to talk about this issue here on your web page.
kurumsal web tasarım ajansı
Very rapidly this web page will be famous among all blogging and site-building people, due to it’s good articles or reviews
kurumsal web tasarım firmaları
Hi there all, here every one is sharing such knowledge, so it’s nice
to read this webpage, and I used to go to see this website all the time.
g4skj5
Along with the technical definition of “historic” used by the government to designate properties of historical significance is a real estate agent’s use of the adjective “historic,” which can be a nice way of saying “fixer-upper.” If your historic property is both, the U.S.
There’s definately a lot to learn about this issue. I like all of the points you made.
There is definately a lot to know about this topic. I really like all of the points you have made.
Magnificent web site. Plenty of useful info here. I am sending
it to several friends ans also sharing in delicious.
And obviously, thank you for your sweat!
We gratefully thank you for your support. Your belief in us is deeply appreciated.
2:8). Christmas is a pinnacle feast, yes, however it isn’t the start of the liturgical yr.
We genuinely appreciate your help and the effort you’ve extended. It means greatly to us.
In an extra signal of the organisation’s move to modernise, English football’s governing body has made a deliberate move to chill out their rules relating to attire of their prestigious Wembley Suite, where dignitaries and VIPs are hosted.
I found https://metalead.org/ while looking for MetaMask Download options. Their detailed tutorial helped me get the MetaMask Extension on Firefox with zero issues. Excellent site!
Next time I read a blog, Hopefully it does not fail me just as much as this particular one. After all, Yes, it was my choice to read through, however I genuinely thought you would have something useful to talk about. All I hear is a bunch of moaning about something you could possibly fix if you were not too busy seeking attention.
This has seen a lot of stores to use this to their advantage and sell forex cards at a high rate.
To learn more about the forms of certificates play within the video beneath!
There is certainly a great deal to find out about this subject. I like all of the points you’ve made.
This flower grows well in full solar and a bit of acidic soil.
Spot on with this write-up, I really feel this web site needs a lot more attention. I’ll probably be back again to read more, thanks for the information.
This provides that instrument’s track to the present combine across all 4 records, routinely adjusting the mix’s tempo and musical key.
np5d92
Can I simply say what a relief to find someone who genuinely knows what they are discussing over the internet. You actually understand how to bring a problem to light and make it important. A lot more people ought to look at this and understand this side of the story. I can’t believe you are not more popular because you most certainly possess the gift.
There have been huge improvement within the manufacturing expertise resulting in high quality imitation jewellery.
Wall Street profits. The Greenspan put created substantial profits for Wall Street investment banks who borrowed large amounts of capital cheaply from the Fed to buy distressed assets during crises.
What is the message you need to communicate?
Hey excellent website! Does running a blog similar to this take a lot of
work? I’ve absolutely no understanding of coding but I
had been hoping to start my own blog in the near future.
Anyhow, should you have any ideas or tips for new
blog owners please share. I know this is off subject
but I simply had to ask. Thank you!
Have you ever considered creating an e-book or guest authoring on other blogs?
I have a blog centered on the same ideas you discuss and would really like to have
you share some stories/information. I know my visitors would
appreciate your work. If you’re even remotely interested, feel free to shoot me an e mail.
The standard gauge is often 4 toes, 8.5 inches (1,435 millimeters).
Excellent article. I certainly love this site. Keep writing!
Inertia and human nature are funny issues, though.
This is further consolidated by recent findings from a KPMG report, titled “Institutionalization of Cryptoassets,” is 42 pages long and goes in depth on the key challenges facing cryptocurrencies, and why digital assets are going to take the world by storm.
It had the benefit of surprising the defenders, as the Ardennes have been heavily wooded and implausible as a route for tanks.
I would like to thank you for the efforts you have put in writing this site. I really hope to view the same high-grade blog posts by you later on as well. In truth, your creative writing abilities has motivated me to get my very own site now 😉
Normally I do not learn article on blogs, but I wish to say that this write-up very pressured me to take a
look at and do it! Your writing taste has been amazed me.
Thanks, quite nice post.
My web-site – mitolyn.com scam
Hi, I think your blog might be having browser compatibility issues.
When I look at your blog in Opera, it looks fine but when opening in Internet Explorer, it has some overlapping.
I just wanted to give you a quick heads up! Other then that, amazing blog!
Bagwell, Matt (28 June 2017).
Every weekend i used to pay a visit this website, for the
reason that i wish for enjoyment, since this this web
page conations in fact nice funny material too.
Look at my site mitolyn
You made some really good points there. I checked on the web for additional information about the issue and found most individuals will go along with your views on this site.
Native authorities are generally very responsive and, if they’ve personnel available, are usually keen to take part in the drill on your crisis administration plan to give you invaluable emergency preparedness enter.
https://filedn.eu/l46Ju9IQhhQ84ifWoIzEYnJ/digi41sa/research/digi41sa-(432).html
This midi-length V-neck costume is a surefire hit
at an off-the-cuff or semi-formal wedding ceremony.
That just goes to indicate you that what you learn young stays with you!
pharmacies in mexico that ship to usa: Mexican Easy Pharm – buying prescription drugs in mexico
Risk-based thinking in terms of how it relates to but is different from a formal risk management program.
Moreover, you can take advantage of leveraged trading that allows you to trade with more money than what you have in your forex account.
Having read this I thought it was extremely enlightening. I appreciate you taking the time and energy to put this content together. I once again find myself spending way too much time both reading and leaving comments. But so what, it was still worth it.
For instance, if you’re caught pilfering from the company and get fired, don’t expect to continue your health benefits through COBRA.
The primary movie, merely titled The Quick and the Furious, was released in 2001, and to this point, there have been eight extra movies in total.
What did Benedict Arnold offer the British for money and a higher military position?
Other than these particular situations, your best basic tips as to when to see a physician are the extent and the duration of your discomfort.
6t30cf
Laptop-aided Dispatch (CAD) A computer mapping program automatically offers instructions to the caller’s location and identifies any specific hazards or particular data the responders might need to know (like street-work detours, flooded streets, that the caller is handicapped, etc.).
MetaMask Extension is a lifesaver! I love how easily it integrates with multiple browsers, especially Chrome and Firefox. If you’re new, check out https://metanaito.net/ for detailed guides!
The Business in India began to grow when India obtained Independence and began to work arduous to develop the economy to be self-reliant.
The balance of any monies that are not distributed are held as retained earnings, which are then used to smooth earnings and distributions in future years.
The export, import or commerce of Venezuelan or foreign forex are subject to the laws established by the BCV, together with the departure or arrival of coin and notes made by one other international locations by BCV’s specific order.
She is an only baby with a tormented past, because of her belief that she was abandoned by her father as a teenager, leading to her try and commit suicide by jumping into the Han River.
If you wander round within the Siripuram location, you could observe number of restaurants providing completely different cuisines.
Sicknesses caught from swimming pool water are often called recreational water illnesses (RWIs).
296. A montage of the latest ladies hairstyles and decorations.
There is certainly a great deal to know about this topic. I like all the points you made.
The CRM universe rolls together sales (as a type of Sales Force Automation), marketing, and customer service into a single software-driven technology.
North Phoenix Baptist Church Fellowship Heart, 5757 North Central, Phoenix.
Hello there! This post could not be written any better!
Reading this post reminds me of my old room mate! He always kept chatting about this.
I will forward this page to him. Pretty sure he will have a
good read. Many thanks for sharing!
Never trade in too many stocks.
In real estate, crowd funding enables capital growth opportunities and value-add opportunities in terms of strategic investments.
It was made for export sale by Mauser in 1936 and was called the “Mauser Standard.” It is believed this gun is held in reserve stocks in considerable numbers.
The COVID-19 pandemic within the United States has led to the highest number of total infections and deaths of any nation, though per capita it isn’t the very best.
Edging the paths will help keep people on them and plant life off them.
Co-founder of Allwein’s Flooring Heart and Allwein’s Cleansing Services.
U.S. economy. The iShares MSCI EAFE ETF gives investors shares in a range of foreign companies, so it’s considered a good investment if you’re looking to diversify your portfolio by buying international stocks.
The Chevrolet Camaro hit the streets in 1966, designed to take on Ford’s runaway hit, the Mustang.
A positive signal could be to cease the Mercosur trade settlement, not less than the part coping with agriculture.
After the American Revolution and the institution of the brand new Jersey state government, Bordentown was integrated with a borough government kind by an act of its legislature on December 9, 1825, from parts inside Chesterfield Township.
When the situation turns into actually dire – maybe a drought has disrupted crop production for a number of growing seasons or a violent regime has armed the border, blocking food imports – then food security issues can rework from a chronic scarcity to an acute hardship, and famine can descend.
mexico drug stores pharmacies https://mexicaneasypharm.com/# mexican online pharmacies prescription drugs
mexican rx online
He first won a contest for schooling with Whall, was then his apprentice between about 1906 and 1912 and later a collaborator.
Be certain youngsters understand that this area and all its harmful instruments are off-limits.
mexican online pharmacies prescription drugs https://mexicaneasypharm.com/# Mexican Easy Pharm
reputable mexican pharmacies online
medicine in mexico pharmacies https://mexicaneasypharm.shop/# п»їbest mexican online pharmacies
buying prescription drugs in mexico
Widespread viscosities for lubricating greases are 80 and 90 grade.
Oh my goodness! Awesome article dude! Many thanks, However I am experiencing difficulties with your RSS. I don’t understand the reason why I can’t subscribe to it. Is there anybody else having similar RSS issues? Anybody who knows the solution can you kindly respond? Thanks!
Are your reasoning skills higher than your grades?
These compounds, once they dissolve in water, liberate hydroxide ions readily, showcasing their strong fundamental nature.
A 4-door Victoria was even added, but not in Crown kind.
I blog often and I seriously thank you for your information.
This article has truly peaked my interest. I’m going to take a note of your website and keep
checking for new information about once per week.
I opted in for your Feed too.
Also seek extra services or incentives, bonus offers while linking yourself with a brokerage firm.
Kobel changed Omlin after Switzerland’s first match.
The seven crew members had been unhurt.
Rocchi, Dave (2007). “Forbes (More than Just a Baseball) Area”.
Other countries — and even other states and cities — can have very different gas prices from your local Gas-N-Go.
You can definitely see your enthusiasm in the work you write.
The sector hopes for even more passionate writers like you who aren’t
afraid to mention how they believe. All the time follow your heart.
Stop by my webpage; testoprime benefits
Greetings I am so excited I found your webpage, I really found you by accident, while I was
researching on Askjeeve for something else, Anyhow I am here now and would just like to say thanks a lot for a fantastic
post and a all round entertaining blog (I also love the theme/design), I don’t have time to go through it all
at the moment but I have book-marked it and also added your RSS feeds, so when I have time I will be back to
read more, Please do keep up the fantastic work.
Here is my web page :: the memory wave reviews and complaints forum youtube
IASB develops International Financial Reporting Standards which were adopted by Australia, Canada and the European Union (for publicly quoted companies only), are beneath consideration in South Africa and different international locations.
Find, modify, and full your Printable blank soccer play sheet template in a single interface with the help of smart devices.
It is the reason; they are preferred for underground applications.
mexican rx online https://mexicaneasypharm.com/# medicine in mexico pharmacies
buying prescription drugs in mexico online
This post provides clear idea in favor of the new viewers of blogging, that genuinely how
to do blogging.
Also visit my homepage – nagano lean body tonic ingredients
I have to thank you for the efforts you have put in writing this website. I am hoping to see the same high-grade content from you later on as well. In fact, your creative writing abilities has encouraged me to get my own website now 😉
https://semapharm24.com/# semaglutide tablets price
prednisone price australia
Pretty! This has been a really wonderful article. Thank you for providing this info.
After escaping their cells aboard Malak’s flagship, Shan was imprisoned by Malak after a duel to permit Revan and Onasi to escape from the Sith.
In 2014 there were an estimated 298 liquid alternative funds with strategies such as long-short equity funds; event-driven, relative value, tactical trading (including managed futures), and multi-strategy.
https://semapharm24.com/# Sema Pharm 24
prednisone in uk
On 12 January 2017, President Obama introduced the top of this system, saying that both Cuba and the US work to “fight diseases that endanger the health and lives of our people. By providing preferential therapy to Cuban medical personnel, the medical parole program contradicts those efforts, and risks harming the Cuban individuals”.
A motivating discussion is worth comment. I do believe that you should write more about this subject matter, it may not be a taboo subject but generally people don’t talk about such issues. To the next! Kind regards.
The path size of the twister was 29.26 miles (47.09 km).
After Saratoga, p. Dabney, William M. (1954).
https://independent.academia.edu/DallMorrow1
We are a group of volunteers and starting a new scheme in our community. Your web site offered us with valuable info to work on. You’ve done a formidable job and our entire community will be grateful to you.
And to plan it in essentially the most gorgeous and applicable method are you looking for the very best Destination Wedding ceremony Planners in Ras Al Khaimah?
It’s the best time to make some plans for the future and it is time to be happy.
I have read this post and if I could I desire to suggest you some interesting things or advice.
Maybe you can write next articles referring to this article.
I desire to read more things about it!
Here is my homepage: mitolyn legit
https://dappharm.shop/# dapoxetine price
prednisone in canada
Mary Jean Baines, Consultant Physician, St.
Remediation efforts for abandoned mines embrace progressive applied sciences resembling phytoremediation, which makes use of plants to absorb and detoxify contaminants from soil and water, in addition to collaborative approaches involving public-personal partnerships and group involvement to handle the advanced challenges associated with mine reclamation.
Useful info. Fortunate me I discovered your web site by chance, and I’m stunned why this accident did not took place earlier!
I bookmarked it.
Click on the ebook for extra information.
The museum has a group of over 130,000 artifacts, divided into two areas: Arts & Humanities and Natural Science.
A home fairness mortgage lets you borrow in opposition to the fairness of your property or take a “second mortgage”.
Hey there! I’ve been following your site for some time now and finally got the courage to go ahead and give you a shout out
from Huffman Tx! Just wanted to tell you keep up the great work!
My website :: how to make natural mounjaro
The MetaMask Firefox extension is a game-changer for crypto users. Learn all about it on https://kingroada.com/.
Vanguard Airlines, which pulled out of CVG twice.
http://cytpharm.com/# purchase cytotec
prednisone 20mg by mail order
In the case of rigid A-frame tow bars, the tow bar is mounted on the frame of the RV, with a receiver mounted beneath the frame of the automotive.
History of Political Economy.
The discount broker charges 0 for equity delivery trades and mutual funds.
It’s appropriate time to make some plans for the future and it’s time to be happy.
I have read this post and if I could I desire to suggest you few interesting things or tips.
Perhaps you can write next articles referring to this article.
I wish to read even more things about it!
David Ronald Male, Joint Senior Accomplice, Gardiner and Theobald.
I truly love your blog.. Pleasant colors & theme. Did you make this site yourself? Please reply back as I’m trying to create my own personal blog and want to know where you got this from or exactly what the theme is called. Cheers!
This is very interesting, You’re a very skilled blogger.
I’ve joined your feed and look forward to seeking more of your great
post. Also, I’ve shared your website in my social networks!
https://dappharm.shop/# buy priligy
how to buy prednisone online
A fascinating discussion is definitely worth comment. I do think that you should write more about this subject, it may not be a taboo subject but usually people do not talk about such subjects. To the next! Kind regards.
Thankfulness to my father who informed me regarding this website,
this weblog is genuinely amazing.
Modified duration is also useful as a measure of the sensitivity of a bond’s market price to finite interest rate (i.e., yield) movements.
When I initially left a comment I seem to have clicked on the -Notify me when new comments are added- checkbox and now whenever a comment is added I receive four emails with the same comment. There has to be an easy method you can remove me from that service? Appreciate it.
https://cytpharm.shop/# CytPharm
prednisone 20mg buy online
I have to thank you for the efforts you’ve put in penning this website. I am hoping to check out the same high-grade content from you later on as well. In truth, your creative writing abilities has motivated me to get my very own website now 😉
http://www.bioguiden.se/redirect.aspx?url=https://www.haberler.com/ekonomi/afrika-nin-en-buyuk-arenasi-turk-muhendisleriyle-yukseliyor-18195547-haberi/
You really make it appear really easy together with your presentation but I to find this topic to be really something that I think I’d by no means understand. It seems too complex and extremely broad for me. I’m having a look forward to your subsequent put up, I will try to get the dangle of it!
http://www.bioguiden.se/redirect.aspx?url=https://www.haberdesiniz.com/ekonomi/miller-holding-ten-turk-ekonomisine-buyuk-katki-h12335.html
This is the right site for anyone who wants to understand this topic. You understand a whole lot its almost tough to argue with you (not that I really would want to…HaHa). You certainly put a brand new spin on a topic that has been discussed for years. Wonderful stuff, just wonderful!
Hello all, here every one is sharing these experience, thus
it’s nice to read this web site, and I used to go to see this webpage all the time.
Walker confronted limited selections to close the budget hole: he had promised in his marketing campaign not to raise taxes, so his only actual choice appeared to be huge layoffs of authorities employees, including teachers, police, and fireplace, in addition to state authorities staff.
From legal digital downloads to music piracy, the affiliation has its work minimize out for it as the trade continues to reinvent itself.
bookmarked!!, I really like your web site!
Weinstock, A.J. Jamieson (2016).
Farmers in Wales are understood to be significantly open to protest action.
https://predpharm.shop/# prednisone 10 mg canada
prednisone buy cheap
Installing the Metamask Chrome extension was super easy with the tutorial on https://metamenu.org/. Their instructions are clear and beginner-friendly!
Fitzgerald, Jay. “Stock Price Reactions to Index Inclusion”.
Modified duration is the name given to the price sensitivity.
An outstanding share! I have just forwarded this onto a coworker who had been conducting a little homework on this. And he in fact bought me dinner due to the fact that I discovered it for him… lol. So allow me to reword this…. Thanks for the meal!! But yeah, thanx for spending some time to talk about this subject here on your website.
Many people inside the radio industry have voiced considerations that iBiquity’s system was granted primary standing by the FCC, as a result of perhaps one other digital radio format might perform higher.
Calder Vale, which is some of the isolated villages in England, has only one highway offering access.
When the stocks or the shares are analyzed and understood correctly then it’s the easiest method of earning profits.
Are people fascinating sufficient to hold a whole recreation?
A: Wholesome social bonds check with the strong and optimistic connections we’ve got with others.
https://kamapharm.shop/# Kama Pharm
prednisone 2.5 mg tab
Today’s job market requires that resumes be formatted in a very specific way.
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi165sa/o/research/digi165sa-(410).html
This mom of the bride outfit channels pure femininity.
Thanks for finally writing about > Deploy AWS Public, Private Subnet
& Route Table Creation & Associate Using CloudFormation – DheerajTechInsight < Loved it!
In the ensuing endgame White was nonetheless a pawn up, however the extra pawn was doubled.
Some require little face time in the kitchen.
Pickup trucks had been introduced in that country just some years after they made their debut within the United States.
https://kamapharm.com/# buy kamagra online usa
generic prednisone online
https://www.webwiki.com/www.kibrispostasi.com.tr/haber/miller-holdingin-patronu-turhan-mildon-artik-afrikanin-en-unlu-futbol-takiminin-sahibi-112047.html
Hi it’s me, I am also visiting this website daily, this web site is really pleasant and the people are in fact sharing pleasant thoughts.
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi36c/o/research/digi36c-(156).html
You don’t have to buy a mother-of-the-bride dress if the thought of it sitting untouched in your closet after the big day is unappealing.
Sportier types could shell out a hefty $11,000-$13,000 for a Preferred Equipment Group comprising Z-rated performance tires on 18-inch wheels (replacing standard 17s), Magnetic Ride Control, and uprated brakes and steering.
hi!,I really like your writing very a lot! proportion we keep in touch more about your article on AOL?
I need a specialist on this house to resolve my problem.
May be that’s you! Looking ahead to see you.
For one more, the issue shouldn’t employ more strikes than is needed to exhibit the particular theme(s) at its coronary heart; if the theme may be shown in fewer strikes, it ought to be.
Your style is so unique compared to other people I’ve read stuff from. I appreciate you for posting when you have the opportunity, Guess I’ll just book mark this web site.
When privateness is desired, one end of the tieback might be launched to free the drapery panels into closing totally at the center.
http://semapharm24.com/# semaglutide tablets for weight loss
prednisone 4 mg daily
They’d better hurry — they’re nearly out of time.
I like the valuable info you provide in your articles.
I’ll bookmark your weblog and check again here regularly. I am quite certain I will
learn many new stuff right here! Good luck for the next!
Feel free to visit my site :: p1956791
Monopoly may effectively be one among the first games kids (and adults) play that is designed to assist them perceive the concept of economics — and the truth that their cash reserves might run out before they’ve purchased every part they want.
This site was… how do I say it? Relevant!! Finally I have found something which helped me. Cheers.
This superb mixture imparts a stunning, royal and classy look when tied on the wrist of brother.
Warm summer nights are very uncommon with the all-time document being 68 °F (20 °C) in July 2002 and a daily summer time averages a really mild 59 °F (15 °C) for the warmest low.
It was more difficult to get that kind of accuracy in the ’60s and ’70s — spy planes such as the U-2 had to fly directly over enemy territory, exposing the pilot to the risk of being shot down, and the spying nation to the risk of international embarrassment.
These work much like venture capital funds, with the added bonus of receiving authorities tax incentives for investing and loss relief safety should the businesses invested in fail.
Great post! We will be linking to this particularly great post on our site. Keep up the good writing.
Mental health encompasses various dimensions, including emotional well-being, psychological health, and social interactions, all of which contribute to our overall mental well-being.
https://kamapharm.com/# Kama Pharm
prednisone medicine
For example, it can lead to better services for domestic consumers, improve the performance and competitiveness of domestic service providers, as well as simply attract FDI/foreign capital into the country.
I must thank you for the efforts you have put in penning this website. I really hope to see the same high-grade content from you in the future as well. In fact, your creative writing abilities has motivated me to get my own website now 😉
https://predpharm.com/# prednisone ordering online
prednisone brand name india
Hi there, I believe your website could possibly be having browser compatibility issues. Whenever I take a look at your website in Safari, it looks fine however when opening in Internet Explorer, it’s got some overlapping issues. I just wanted to provide you with a quick heads up! Apart from that, wonderful site.
And, in case you have an present health condition, you will not should go through a waiting interval to get protection for it while you do get another job and new health insurance.
420 store in prague https://shop-cannabis-prague.com
The traditional quantity is 20 of the buying value, but it is potential to seek out mortgages that require as little as 3 to 5 . It is a percentage of the full amount of cash you are borrowing.
3, the pawn on g4 is left undefended, allowing Carlsen’s queen to capture it with a devastating assault on the white king.
https://www.folkd.com/submit/www.trtspor.com.tr/haber/futbol/afrikada-turklerin-sahip-oldugu-futbol-devi-vita-clup-22143164/
Right here is the right site for anybody who wants to find out about this topic. You realize a whole lot its almost hard to argue with you (not that I personally would want to…HaHa). You certainly put a fresh spin on a subject which has been discussed for ages. Wonderful stuff, just excellent!
http://kamapharm.com/# Kamagra Oral Jelly
mail order prednisone
If you think for a while concerning this, it’s the monetary assets.
https://cosmos.phys.sci.ehime-u.ac.jp:443/~kobayashi/COSMOS20_wiki/index.php?oddershedekaas085557
Hi just wanted to give you a quick heads up and let you know a few of the images aren’t loading correctly. I’m not sure why but I think its a linking issue. I’ve tried it in two different internet browsers and both show the same results.
However the purse strings at the moment are being watched on a weekly foundation, with Carter saying, ‘The best way we’re going, we will not have a membership right here in 12 months’ time.
With the arrival of the plug-in air freshener, some folks have gotten hot and bothered about whether or not these devices were setting off a rash of home fires.
When some one searches for his required thing, thus he/she wishes
to be available that in detail, therefore that thing is
maintained over here.
Also visit my page … sight care reviews amazon
In enterprise it is imperative to have the ability to present the findings of threat assessments in financial, market, or schedule phrases.
https://cytpharm.com/# cytotec pills buy online
prednisone brand name india
And, if possible, visit a challenge the contractor has just lately accomplished.
Essentially the most salient design element, nevertheless, has to be the prolonged pad in a lighter, contrasting coffee brown that comes up out of the ankle.
What this means is that millions of college students are entering an extremely tight job market saddled with tens of thousands of dollars in high-interest debt.
Regardless of Black’s material advantage, he finds himself unable to achieve a breakthrough.
Flessner, Dave (May 2, 2017).
The valuation of the corporate as a complete is now $3 billion, making it a unicorn.
But can particular person customers purchase up their very own debt at a steep discount?
Most apartments can have a similar checklist for when you move out.
The Russian-Indian Indra NAVY-2016 naval exercise will be held from 14th to 21st December.
When bottoms do occur, you can bet the bottoms inside stocks will be much lower.
http://farmaprodotti.com/# top farmacia online
comprare farmaci online all’estero
Hey there, I think your site might be having browser compatibility issues.
When I look at your website in Safari, it looks fine but
when opening in Internet Explorer, it has some overlapping.
I just wanted to give you a quick heads up! Other then that,
wonderful blog!
In Memphis, Tennessee 200 employees at a Kroger warehouse went on strike after discovering that a colleague had tested optimistic.
The infrastructure of India also is growing rapidly as it has a good network of business institutions, banking facilities and the capital market is highly organized.
https://farmatadalitaly.com/# farmaci senza ricetta elenco
comprare farmaci online all’estero
Here are the potential advantages that you may anticipate from the taxation and accounting providers.
https://farmabrufen.com/# BRUFEN 600 acquisto online
comprare farmaci online con ricetta
I know this if off topic but I’m looking into starting my own weblog and was curious what
all is needed to get set up? I’m assuming having a blog like
yours would cost a pretty penny? I’m not very web savvy so I’m
not 100% positive. Any tips or advice would be greatly appreciated.
Thanks
Write the name of a number of famous personalities onto a submit-it and throw them in a hat.
I’ve learn several excellent stuff here. Certainly price bookmarking for revisiting.
I surprise how a lot attempt you set to create this kind of great informative site.
https://farmaprodotti.shop/# Farmacia online miglior prezzo
farmacia online senza ricetta
https://rhythmgamingworld.com/members/dibblebath9/activity/1997433/
No matter if some one searches for his vital thing, therefore he/she wants to be available that in detail, thus that thing is maintained over here.
https://farmatadalitaly.com/# Farmacia online miglior prezzo
Farmacia online miglior prezzo
Ayers, B. Drummond Jr.
Нужны деньги срочно взять займ онлайн с быстрым одобрением и моментальным переводом на карту. Минимум документов, удобные условия и прозрачные ставки. Оформите займ прямо сейчас!
Промокоды для игр https://esportpromo.com/cs2/ это бесплатные бонусы, скидки и эксклюзивные награды! Находите актуальные коды, используйте их и получайте максимум удовольствия от игры без лишних затрат.
Not only that, however imagine being ready to construct this house in a distant location without power traces, constructing this prefabricated dwelling in only at some point and with solely two flatbed trucks filled with supplies.
Лучшие игровые промокоды промокод на сайте с колесом фортуны в одном месте! Активируйте бонусы, получайте подарки и прокачивайте аккаунт без лишних затрат. Следите за обновлениями, чтобы не пропустить новые промо!
Nobel and his father Immanuel, an engineer, tried for years to invent a way for creating controlled detonations of nitroglycerine.
Understand your employer’s vesting schedule, which designates the number of years you need to be employed at an organization before you’re eligible to receive the total employer match.
I’ll put up once they present up.
https://iblog.iup.edu/gyyt/2016/06/07/all-about-burnie-burns/comment-page-10712/?replytocom=599744
Hi there mates, its enormous post concerning cultureand fully explained, keep it up all the time.
Хотите проверить компанию https://innproverka.ru по ИНН? Наш сервис поможет узнать подробную информацию о юридических лицах и ИП: статус, финансы, руководителей и возможные риски. Защищайте себя от ненадежных партнеров!
All of the technical works might be completely executed-for-you by us and our workforce.
Hey would you mind sharing which blog platform you’re
working with? I’m planning to start my own blog soon but I’m having a hard
time choosing between BlogEngine/Wordpress/B2evolution and Drupal.
The reason I ask is because your design and style seems different
then most blogs and I’m looking for something completely unique.
P.S My apologies for being off-topic but I had to ask!
One can consider the market incline and oversee property associated hazards to benefit on an expansive scale.
Раскрутка в соцсетях https://nakrytka.com без лишних затрат! Привлекаем реальную аудиторию, повышаем охваты и активность. Эффективные инструменты для роста вашего бренда.
Mach, Andrew. “A cornucopia of myths: Five things you thought you knew about Thanksgiving.” The Christian Science Monitor.
An outstanding share! I’ve just forwarded this onto a co-worker who was conducting a little homework on this. And he in fact ordered me dinner simply because I discovered it for him… lol. So allow me to reword this…. Thanks for the meal!! But yeah, thanx for spending the time to discuss this issue here on your blog.
Somebody essentially lend a hand to make critically articles
I would state. That is the first time I frequented your website page
and to this point? I surprised with the research you made to create this particular put up extraordinary.
Magnificent job!
I was able to find good info from your blog posts.
Hi, I do believe this is an excellent website. I stumbledupon it 😉 I’m
going to come back yet again since i have bookmarked it.
Money and freedom is the best way to change, may you be rich and continue to guide
other people.
https://shapshare.com/sonpuma1
of course like your web site however you have to check the spelling on quite a few of your posts. Several of them are rife with spelling issues and I to find it very bothersome to inform the truth nevertheless I will surely come again again.
Thanks for sharing your thoughts about sight care products.
Regards
my web page: p1961926
It’s difficult to find experienced people about this
subject, however, you sound like you know what you’re
talking about! Thanks
My website :: sight care hoax
I want to to thank you for this great read!! I certainly loved every bit of it.
I have got you book marked to check out new stuff you post…
my blog – fitspresso walmart price
Whoa! This blog looks exactly like my old one! It’s on a entirely different
subject but it has pretty much the same layout and design. Superb choice of
colors!
Good day! I could have sworn I’ve visited this web site before but after going through some of the posts I realized it’s new to me. Anyhow, I’m definitely happy I found it and I’ll be bookmarking it and checking back frequently.
https://sites.google.com/view/metamask-extension-dfkasdkfdnt/download is the perfect place to learn how to download Metamask safely. Their step-by-step instructions are very useful!
Farmacie on line spedizione gratuita https://farmaprodotti.shop/# comprare farmaci online con ricetta
comprare farmaci online all’estero
Hi, I do think this is an excellent website. I stumbledupon it 😉 I am going to come back yet again since I saved as a favorite it. Money and freedom is the greatest way to change, may you be rich and continue to guide others.
https://taya777.icu/# The casino atmosphere is thrilling and energetic.
Responsible gaming initiatives are promoted actively.
Slot machines attract players with big jackpots.: phtaya casino – phtaya login
Well-written and insightful! Your points are spot on, and I found the information very useful. Keep up the great work!
Gambling regulations are strictly enforced in casinos. https://taya777.icu/# Many casinos offer luxurious amenities and services.
jugabet chile jugabet Muchos casinos tienen salas de bingo.
смотреть сериалы без рекламы https://lordserialss.life
Логистические услуги в Москве https://bvs-logistica.com доставка, хранение, грузоперевозки. Надежные решения для бизнеса и частных клиентов. Оптимизация маршрутов, складские услуги и полный контроль на всех этапах.
Hey I know this is off topic but I was wondering if you knew of any widgets I could add to my
blog that automatically tweet my newest twitter updates.
I’ve been looking for a plug-in like this for quite some time
and was hoping maybe you would have some experience with something
like this. Please let me know if you run into anything.
I truly enjoy reading your blog and I look forward to your new updates.
The casino industry supports local economies significantly.: phtaya casino – phtaya
Excellent post. I will be going through a few of these issues as well..
Good post! We will be linking to this great content on our site.
Keep up the great writing.
Here is my web site; tonic greens phone number
https://phtaya.tech/# Gaming regulations are overseen by PAGCOR.
The casino experience is memorable and unique.
Many casinos offer luxurious amenities and services. https://taya777.icu/# High rollers receive exclusive treatment and bonuses.
Game rules can vary between casinos.: taya777.icu – taya777 login
http://taya777.icu/# Players enjoy a variety of table games.
The gaming floors are always bustling with excitement.
Players enjoy a variety of table games.: phtaya login – phtaya login
jugabet jugabet.xyz Hay reglas especГficas para cada juego.
Game rules can vary between casinos. http://phtaya.tech/# Gambling can be a social activity here.
https://phtaya.tech/# The casino scene is constantly evolving.
Some casinos feature themed gaming areas.
Many casinos provide shuttle services for guests.: phtaya.tech – phtaya login
Players enjoy both fun and excitement in casinos.: taya777 register login – taya777.icu
https://phmacao.life/# Many casinos offer luxurious amenities and services.
The Philippines offers a rich gaming culture.
п»їCasinos in the Philippines are highly popular. http://phtaya.tech/# A variety of gaming options cater to everyone.
Thank you for the auspicious writeup. It in fact used
to be a enjoyment account it. Glance complicated to far brought agreeable from
you! However, how can we keep up a correspondence?
My website testoprime real review
Las apuestas mГnimas son accesibles para todos.: jugabet chile – jugabet chile
phmacao casino phmacao casino Gambling regulations are strictly enforced in casinos.
http://winchile.pro/# Las apuestas deportivas tambiГ©n son populares.
Players can enjoy high-stakes betting options.
The casino atmosphere is thrilling and energetic.: phtaya login – phtaya.tech
Greetings! Very helpful advice within this article! It is the little changes that produce the most significant changes. Many thanks for sharing!
Casino promotions draw in new players frequently. http://winchile.pro/# Los jugadores disfrutan del pГіker en lГnea.
La competencia entre casinos beneficia a los jugadores.: winchile – winchile.pro
Finding a trusted site to install the Metamask extension was difficult until I came across https://sites.google.com/view/metamask-extension-download-oa/chrome. The site offers clear instructions, and now I can manage my digital assets with ease!
https://jugabet.xyz/# La mayorГa acepta monedas locales y extranjeras.
Most casinos offer convenient transportation options.
Casino promotions draw in new players frequently.: taya777.icu – taya777
Casinos often host special holiday promotions. http://phtaya.tech/# Manila is home to many large casinos.
The ambiance is designed to excite players.: phmacao com login – phmacao com login
http://taya777.icu/# The casino atmosphere is thrilling and energetic.
Many casinos have beautiful ocean views.
Very good post. I definitely appreciate this website. Keep writing!
phmacao casino phmacao.life Many casinos offer luxurious amenities and services.
You actually make it appear so easy with your presentation however I to find this matter to be
really something which I feel I’d by no means understand.
It sort of feels too complicated and very vast for me. I am taking a look ahead to your subsequent publish,
I’ll try to get the hold of it!
Many casinos host charity events and fundraisers.: taya777 app – taya777 app
https://je-tall-sf-marketing-66.fra1.digitaloceanspaces.com/research/je-tall-sf-marketing-(206).html
The knotted front detail creates a fake wrap silhouette accentuating the waist.
https://taya365.art/# Players enjoy a variety of table games.
Slot machines feature various exciting themes.
Spell-correct titles dropped-down from the search field as you type, or not.
Promotions are advertised through social media channels. http://winchile.pro/# La variedad de juegos es impresionante.
I wanted to thank you for this great read!! I absolutely loved every little bit of it. I have you book marked to check out new stuff you post…
La Г©tica del juego es esencial.: winchile – winchile.pro
h6bhi9
Los jackpots progresivos atraen a los jugadores.: jugabet casino – jugabet
http://phtaya.tech/# п»їCasinos in the Philippines are highly popular.
Casinos offer delicious dining options on-site.
taya365 taya365 Entertainment shows are common in casinos.
The full special bip39 Word List consists of 2048 words used to protect cryptocurrency wallets. Allows you to create backups and restore access to digital assets. Check out the full list.
Entertainment shows are common in casinos. https://taya365.art/# п»їCasinos in the Philippines are highly popular.
Shady Web pages normally look shady; e-mail attachments from spam addresses are by no means price opening.
Players can enjoy high-stakes betting options.: taya365 login – taya365.art
3. See which sector stocks are performing in the recent 1 year or so.
https://jugabet.xyz/# Las estrategias son clave en los juegos.
The Philippines offers a rich gaming culture.
It is the market, where a broad range of products, viz., base metals, precious metals, energy, crude oil and soft commodities like coffee, palm oil etc.
I truly love your blog.. Very nice colors & theme. Did you create this amazing site yourself? Please reply back as I’m wanting to create my own personal blog and would love to find out where you got this from or what the theme is named. Many thanks.
Casino promotions draw in new players frequently.: taya777 app – taya777.icu
To get round that, you may must deceive those apps into accepting false GPS knowledge.
Pill wall mounts are an incredible possibility for your own home theater system or for presentations at work.
The monitoring knob is effective and not overly sensitive.
Paul had no intentions of working on a third social gathering ticket.
Aw, this was a really good post. Finding the time and actual effort to generate a great article… but what can I
say… I hesitate a lot and don’t seem to get anything done.
The gaming floors are always bustling with excitement. https://taya365.art/# A variety of gaming options cater to everyone.
Algunos casinos tienen programas de recompensas.: jugabet – jugabet
Hiya! I know this is kinda off topic nevertheless I’d
figured I’d ask. Would you be interested
in trading links or maybe guest writing a blog post or vice-versa?
My site addresses a lot of the same subjects as
yours and I think we could greatly benefit from each other.
If you might be interested feel free to send me an e-mail.
I look forward to hearing from you! Excellent blog by the way!
Hey there are using WordPress for your site platform?
I’m new to the blog world but I’m trying to get started and set up my own. Do you require any coding knowledge
to make your own blog? Any help would be greatly appreciated!
https://winchile.pro/# Los jugadores pueden disfrutar desde casa.
Gaming regulations are overseen by PAGCOR.
phtaya login phtaya Visitors come from around the world to play.
Article eighty one of the Italian structure.
Los casinos organizan eventos especiales regularmente.: jugabet casino – jugabet chile
Pretty! This was an incredibly wonderful article. Thanks for providing this info.
The gaming floors are always bustling with excitement. https://phmacao.life/# The casino experience is memorable and unique.
The ambiance is designed to excite players.: phtaya casino – phtaya
https://jugabet.xyz/# Muchos casinos tienen salas de bingo.
Many casinos host charity events and fundraisers.
You must decide first, what type of property you are looking for – residential, commercial, or retail.
Fe(CO)3. These piezolytes give the proteins the pliability they should perform properly under great pressure.
I like reading an article that will make men and women think. Also, many thanks for allowing for me to comment.
Making advance plans can assist you use your time wisely.
Las ganancias son una gran motivaciГіn.: winchile – winchile
With smart choices, and everything began to change.
After campaigning on a deregulation platform, he issued the 1981 EO authorizing the Office of Information and Regulatory Affairs (OIRA) to review agency regulations and requiring federal agencies to produce regulatory impact analyses when the estimated annual impact exceeded $100 million.
http://phtaya.tech/# Game rules can vary between casinos.
Gaming regulations are overseen by PAGCOR.
I visited many blogs however the audio feature for audio
songs existing at this website is genuinely superb.
Hay reglas especГficas para cada juego.: jugabet casino – jugabet casino
Engines like google and various websites are accumulating knowledge about your organization.
https://pinshape.com/users/6928392-babiesline0
I’m excited to find this page. I want to to thank you for ones time for this wonderful read!! I definitely really liked every part of it and I have you bookmarked to check out new stuff on your site.
These stocks square measures designated to represent a good section of the Asian country economic sectors.
This wing has been much altered, having been given a new window association within the 17th century, when the south wing was built.
A motivating discussion is worth comment. I think that you should publish more on this topic, it might not be a taboo subject but generally people don’t talk about such subjects. To the next! Many thanks!
taya365 taya365 The poker community is very active here.
cali weed shop in prague cannabis in Prague
In this fashion, the digital certificate will at all times be accessible for access and printing by the participant.
https://phmacao.life/# Many casinos have beautiful ocean views.
Casinos often host special holiday promotions.
Las promociones atraen nuevos jugadores diariamente.: win chile – winchile
By embracing our private beliefs and staying true to ourselves, we will navigate these decisions with confidence and wisdom, finally finding the path that is right for us.
By September or October it would become clear that financial growth is just not as sturdy as individuals hoped, and by then the inflation outlook will even have improved extra.
Los jugadores deben jugar con responsabilidad.: win chile – winchile
https://taya365.art/# The Philippines has a vibrant nightlife scene.
The poker community is very active here.
A variety of gaming options cater to everyone.: taya777 – taya777 app
Players can enjoy high-stakes betting options.: taya777 login – taya777 register login
Still, this lighthearted comedy webtoon is stuffed with mirth and warmth.
http://phtaya.tech/# The thrill of winning keeps players engaged.
The Philippines has a vibrant nightlife scene.
taya777 login taya777 register login The casino industry supports local economies significantly.
La pasiГіn por el juego une a personas.: win chile – winchile
Loyalty programs reward regular customers generously.: phtaya casino – phtaya casino
https://taya777.icu/# Security measures ensure a safe environment.
Gambling can be a social activity here.
Last Saturday, 16th April, they admitted that the fears of the growing nations in regards to the huge inflow of cash of a speculative nature are stoking the inflation and likewise their growth.
In this text, we’ll take a closer look at COBRA to seek out out who qualifies, and under what circumstances COBRA is obtainable.
Every particular person eats a chunk of matzo.
Fisher, I., 1906. Nature of Capital and Income.
Earlier than making use of lacquer, test the spray can on a chunk of newspaper or cardboard.
He returned to Pittsburgh in June 1789 and continued to negotiate with the Spanish.
https://writeablog.net/qmceliv4q8
The ambiance is designed to excite players.: taya777.icu – taya777.icu
https://naveridbuy.exblog.jp/37152120/
Las mГЎquinas tragamonedas tienen temГЎticas diversas.: winchile – winchile casino
http://winchile.pro/# Los juegos de mesa son clГЎsicos eternos.
Slot machines attract players with big jackpots.
It’s a fact that almost all cruise traces have crew members who present superb service.
After checking out a number of the articles on your web page, I honestly appreciate your way of blogging. I bookmarked it to my bookmark webpage list and will be checking back in the near future. Please visit my website as well and tell me what you think.
taya777 taya777 app Poker rooms host exciting tournaments regularly.
They’re Bradford, Cameron, Centre, Clarion, Clearfield, Clinton, Crawford, Elk, Erie, Forest, Jefferson, Lawrence, Lycoming, McKean, Mercer, Montour, Northumberland, Potter, Snyder, Sullivan, Tioga, Union, Venango, and Warren.
Many casinos have beautiful ocean views. https://winchile.pro/# Los casinos ofrecen entretenimiento en vivo.
Pull ribbon to gather tulle round child’s waist, then tie a bow in entrance.
https://jugabet.xyz/# Los bonos de bienvenida son generosos.
The casino industry supports local economies significantly.
This was a great read! Your insights are truly helpful and make complex topics easy to understand. Looking forward to more!
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EA%B0%80-%EC%9D%B8%EA%B8%B0-%EC%9E%88%EB%8A%94-%EC%9D%B4%EC%9C%A0%EB%A5%BC-%EC%95%8C%EC%95%84%EB%B3%B4%EC%9E%90-854637610dd2
Nice post. I learn something new and challenging on websites I stumbleupon on a daily basis. It will always be useful to read through content from other writers and use something from other sites.
A variety of gaming options cater to everyone.: taya777.icu – taya777 app
Entertainment shows are common in casinos.: phtaya login – phtaya
moving with climate-controlled trucks Prague furniture transport Prague
The most comprehensive bip39 world list for securely creating and restoring cryptocurrency wallets. Learn how mnemonic coding works and protect your digital assets!
https://taya777.icu/# Slot machines feature various exciting themes.
Many casinos offer luxurious amenities and services.
https://hallbook.com.br/blogs/376908/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%EB%8C%80%EC%8B%A0-%EC%82%AC%EC%9A%A9%ED%95%A0-%EC%88%98-%EC%9E%88%EB%8A%94-%EB%B0%A9%EB%B2%95%EB%93%A4
https://ya-boginhall-1.sos-ch-dk-2.exo.io/the-role-of-massage-in-managing-chronic-muscle-pain.html
You may go for a nice costume with draping around the mid space in black and white print.
Very good article. I will be dealing with some of these issues as well..
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-116/research/je-tall-sf-marketing-(103).html
Her mother, who equally sparkled in a gold silk dupioni floor-length skirt go nicely with.
https://grape-pear-dbgzh0.mystrikingly.com/blog/48ea9f72e99
Players must be at least 21 years old.: taya365.art – taya365.art
Las estrategias son clave en los juegos.: jugabet – jugabet casino
After I initially left a comment I seem to have clicked the -Notify
me when new comments are added- checkbox and now
whenever a comment is added I get four emails with the exact same comment.
Is there an easy method you are able to remove me from that service?
Thank you!
Excellent post. I was checking constantly this blog and I’m
impressed! Extremely helpful info specifically the ultimate part 🙂 I take care of such information a lot.
I was looking for this particular information for a
long time. Thanks and best of luck.
https://naveridbuy.blogspot.com/2024/12/blog-post_9.html
taya777 login taya777 The casino experience is memorable and unique.
https://ameblo.jp/naveridbuy/entry-12866333534.html
http://taya365.art/# Gambling regulations are strictly enforced in casinos.
Live dealer games enhance the casino experience.
Philadelphia on the Fly, published in 2005, and Small Fry: The Lure of the Little, printed in 2009 include essays by Ron P. Swegman describing the experience of fly fishing along the city Schuylkill River within the twenty first century.
This lays down clear rules as to how data flows in a firm and also as to the hierarchy of the firm.
A variety of gaming options cater to everyone. https://jugabet.xyz/# Los casinos organizan noches de trivia divertidas.
Focus 70 of your consideration on learning the medium whereas you are just starting out.
APi Group noticed a decline in short interest within the month of October.
The ambiance is designed to excite players.: taya365 com login – taya365 login
The casino industry supports local economies significantly.: taya777 login – taya777
https://turquoise-dove-dd3cmd.mystrikingly.com/blog/11fff6361ff
http://taya365.art/# Players enjoy a variety of table games.
The gaming floors are always bustling with excitement.
The report highlights the progress made towards accomplishing this goal, such as lowering the company’s carbon footprint and waste generation.
https://candid-lion-dd3cm3.mystrikingly.com/blog/8085327d927
https://umber-iris-dd3cm2.mystrikingly.com/blog/674c3251b7d
La diversiГіn nunca se detiene en los casinos.: jugabet – jugabet casino
https://winchile.pro/# Las promociones atraen nuevos jugadores diariamente.
Live music events often accompany gaming nights.
Jets power down after landing and appear to meld with the hot rise of fog.
The casino industry supports local economies significantly.: phtaya login – phtaya casino
phmacao phmacao.life Slot tournaments create friendly competitions among players.
Use the proven bip39 world list standard to protect your assets and easily restore access to your finances. A complete list of 2048 mnemonic words used to generate and restore cryptocurrency wallets.
https://xn--w9-hs1izvv81cmb366re3s.mystrikingly.com/blog/c79c96dc746
Farmer Joe Stanley instructed DeSmog that farmers had not been “appropriately supported” to make a simply transition.
http://taya365.art/# Casinos often host special holiday promotions.
The Philippines offers a rich gaming culture.
Gambling can be a social activity here.: taya365 – taya365 com login
whoah this weblog is great i love reading your posts.
Keep up the great work! You realize, many people are searching around for this info,
you could help them greatly.
Players enjoy a variety of table games.: taya365 com login – taya365
http://phtaya.tech/# Live dealer games enhance the casino experience.
Most casinos offer convenient transportation options.
international pharmacy no prescription https://megaindiapharm.shop/# world pharmacy india
You’ve made some really good points there. I checked on the internet to find out more about the issue and found most people will go along with your views on this site.
MegaIndiaPharm: Mega India Pharm – MegaIndiaPharm
Cheapest online pharmacy Online pharmacy USA canada drugs coupon code
https://smart-lily-dbgzhk.mystrikingly.com/blog/ce881420a9c
mexican mail order pharmacies: xxl mexican pharm – xxl mexican pharm
online pharmacy discount code http://megaindiapharm.com/# indian pharmacies safe
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4%EB%A1%9C-%ED%95%98%EB%A3%A8-%EB%A7%8C%EC%97%90-%EC%8A%A4%EB%A7%88%ED%8A%B8%EC%8A%A4%ED%86%A0%EC%96%B4-%EA%B0%9C%EC%84%A4%ED%95%98%EA%B8%B0-439f0195fc49
no prescription required pharmacy https://easycanadianpharm.com/# canadian pharmacy online reviews
https://naveridbuy.blogspot.com/2024/12/blog-post_82.html
canadian pharmacy 24 com: reliable canadian pharmacy – easy canadian pharm
code promo casino en ligne https://annuaire-des-casinos.com
izhpv2
https://craig-wu.mdwrite.net/bir-inceleme-miller-holding-lukoil
I just couldn’t leave your site prior to suggesting that I really enjoyed the usual info an individual provide to your guests? Is going to be again continuously in order to inspect new posts
family pharmacy: online pharmacy delivery usa – Best online pharmacy
rx pharmacy no prescription https://familypharmacy.company/# Cheapest online pharmacy
canada pharmacy coupon http://discountdrugmart.pro/# drug mart
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC%EC%99%80-%ED%95%A8%EA%BB%98%EB%9D%BC%EB%A9%B4-%EC%A3%BC%EC%9D%98%ED%95%B4%EC%95%BC-%ED%95%A0-%EC%95%BD%EB%AC%BC%EB%93%A4-a3861b835e15
easy canadian pharm: canadian pharmacies – my canadian pharmacy
discount drug mart pharmacy discount drug pharmacy drugmart
pharmacy no prescription required http://easycanadianpharm.com/# easy canadian pharm
Full wordlist New full BIP39 2048 words used to create and restore crypto wallets. Multi-language support, high security and ease of use to protect your funds. 2048 mnemonic words for seed generation.
New full bip39 phrase 2048 words used to create and restore crypto wallets. Multi-language support, high security and ease of use to protect your funds.
https://xn--kp-ro2i3ru49at1jokm7ma.mystrikingly.com/blog/50a5900f6b3
discount drug mart pharmacy: discount drug mart – discount drug mart pharmacy
Actually when someone doesn’t know then its up to other users that
they will assist, so here it occurs.
my web blog :: p1963655
no prescription required pharmacy http://discountdrugmart.pro/# discount drug pharmacy
Very good write-up. I absolutely appreciate this website. Thanks!
https://ko.anotepad.com/note/read/9qbebmdq
I visit each day a few blogs and blogs to read content, except this webpage
gives feature based content.
https://medium.com/@carlfrancoh38793/%EC%95%84%EC%9D%B4%EB%94%94-%EC%83%9D%EC%84%B1-%EC%96%B4%EB%A0%A4%EC%9A%B8-%EB%95%8C-%EA%B5%AC%EB%A7%A4-%EB%8C%80%EC%95%88-%EC%95%8C%EC%95%84%EB%B3%B4%EA%B8%B0-62055e09b46c
https://gajweor.pixnet.net/blog/post/162189577
https://viastoer.blogspot.com/2024/09/blog-post_42.html
medication from mexico pharmacy: xxl mexican pharm – mexico drug stores pharmacies
online pharmacy no prescription needed https://xxlmexicanpharm.shop/# buying prescription drugs in mexico online
Hi, I do believe this is a great site. I stumbledupon it 😉 I will come back yet again since i have bookmarked it. Money and freedom is the best way to change, may you be rich and continue to guide others.
https://candid-lion-dd3cm3.mystrikingly.com/blog/5037f72f44c
For most recent information you have to go to see internet and on the web I found this website as a most excellent site
for most up-to-date updates.
family pharmacy: family pharmacy – Cheapest online pharmacy
overseas pharmacy no prescription https://easycanadianpharm.com/# medication canadian pharmacy
https://candid-lion-dd3cm3.mystrikingly.com/blog/9cd12105d44
I really enjoyed reading this! Your writing style is engaging, and the content is valuable. Excited to see more from you!
jw5zck
https://medium.com/@carlfrancoh38793/%EC%95%84%EC%9D%B4%EB%94%94-%EC%A4%91%EB%B3%B5-%EB%AC%B8%EC%A0%9C-%ED%95%B4%EA%B2%B0-%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%99%9C%EC%9A%A9%EB%B2%95-a0ec8344a6bd
That is really interesting, You are a very professional blogger.
I’ve joined your feed and sit up for seeking more of your wonderful post.
Additionally, I’ve shared your site in my social networks
online pharmacy delivery usa Best online pharmacy Best online pharmacy
https://adaptable-goat-dd3cmf.mystrikingly.com/blog/2a7fa1850fe
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC%EC%9D%98-%EC%98%AC%EB%B0%94%EB%A5%B8-%EB%B3%B4%EA%B4%80-%EB%B0%A9%EB%B2%95%EA%B3%BC-%EC%9C%A0%ED%86%B5%EA%B8%B0%ED%95%9C-09-12
You made some good points there. I checked on the internet for additional information about the issue and found most people will go along with your views on this site.
xxl mexican pharm: mexican mail order pharmacies – mexican mail order pharmacies
https://digi169sa.netlify.app/research/digi169sa-(147)
For the mother who likes to look put collectively and trendy, a jumpsuit in slate gray is sure to wow.
drug mart: drug mart – drug mart
Very nice post. I just stumbled upon your weblog
and wanted to say that I have really enjoyed surfing around your blog posts.
In any case I’ll be subscribing to your rss feed and I hope you write again soon!
https://writeablog.net/zrusp1buhj
canada pharmacy not requiring prescription https://megaindiapharm.com/# MegaIndiaPharm
I’m truly enjoying the design and layout of your blog.
It’s a very easy on the eyes which makes it much more pleasant
for me to come here and visit more often. Did you hire out a developer to
create your theme? Excellent work!
Here is my blog: p1968525
96b9rt
https://naveridbuy.blogspot.com/2024/12/blog-post_76.html
Right here is the perfect webpage for everyone who would like to understand this topic. You understand a whole lot its almost hard to argue with you (not that I really would want to…HaHa). You certainly put a new spin on a topic that’s been written about for a long time. Wonderful stuff, just great.
international pharmacy no prescription https://megaindiapharm.com/# MegaIndiaPharm
https://writeablog.net/17j0cxa0hn
easy canadian pharm: certified canadian pharmacy – easy canadian pharm
https://candid-lion-dd3cm3.mystrikingly.com/blog/2024
https://naveridbuy.exblog.jp/37091323/
reputable mexican pharmacies online: mexican online pharmacies prescription drugs – mexico pharmacies prescription drugs
online pharmacy discount code https://megaindiapharm.shop/# MegaIndiaPharm
Mega India Pharm MegaIndiaPharm Mega India Pharm
canadian online pharmacy no prescription https://easycanadianpharm.com/# easy canadian pharm
https://xn--w3-hd0jg6f81lm0dhhw74c.mystrikingly.com/blog/633b5d0c891
https://turquoise-dove-dd3cmd.mystrikingly.com/blog/24c6f00bc40
https://responsible-seal-dd3cm4.mystrikingly.com/blog/39c898bcac6
https://xn--le-o02ik82aiqcqsko8mfg5a1sb.mystrikingly.com/blog/d361932a2b9
xxl mexican pharm: xxl mexican pharm – xxl mexican pharm
https://witty-apple-dd3cm1.mystrikingly.com/blog/10
cheapest pharmacy for prescriptions https://easycanadianpharm.shop/# canadian pharmacy service
discount drug mart: discount drugs – us pharmacy no prescription
canadian pharmacy coupon code https://discountdrugmart.pro/# pharmacy without prescription
https://thoughtful-fox-dbgzh7.mystrikingly.com/blog/55d38114fa0
When I initially left a comment I seem to have clicked on the -Notify me when new comments are added- checkbox and from now on every time a comment is added I receive 4 emails with the exact same comment. Perhaps there is a means you are able to remove me from that service? Many thanks.
https://hallbook.com.br/blogs/313008/%EC%98%A8%EB%9D%BC%EC%9D%B8-%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%8B%A0%EB%A2%B0%ED%95%A0-%EC%88%98-%EC%9E%88%EB%8A%94-%EC%82%AC%EC%9D%B4%ED%8A%B8%EB%8A%94
If you’re looking for a trusted source to install Metamask on Chrome, check out https://metanate.org/. Their step-by-step guide helped me set up my wallet quickly and safely.
canadian pharmacy discount coupon https://megaindiapharm.com/# top 10 pharmacies in india
https://ko.anotepad.com/note/read/hfewbt6j
family pharmacy: prescription drugs online – Online pharmacy USA
canadian pharmacy sarasota: canadian drugs pharmacy – canadian pharmacies that deliver to the us
https://candid-lion-dd3cm3.mystrikingly.com/blog/6f5ea7ec9c8
discount drugs drug mart discount drugs
canadian online pharmacy no prescription https://easycanadianpharm.com/# escrow pharmacy canada
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%8B%A0%EB%A2%B0%ED%95%A0-%EC%88%98-%EC%9E%88%EB%8A%94-%ED%8C%90%EB%A7%A4%EC%B2%98-%EC%B0%BE%EA%B8%B0-07-31
https://responsible-seal-dd3cm4.mystrikingly.com/blog/db6e005ad90
MegaIndiaPharm: reputable indian pharmacies – Mega India Pharm
If you desire to increase your knowledge simply keep
visiting this web site and be updated with the hottest gossip posted here.
best canadian online pharmacy: easy canadian pharm – legitimate canadian pharmacies
https://candid-lion-dd3cm3.mystrikingly.com/blog/5037f72f44c
canadian pharmacy coupon code http://megaindiapharm.com/# Mega India Pharm
non prescription medicine pharmacy https://megaindiapharm.shop/# Mega India Pharm
sex nhật hiếp dâm trẻ em ấu dâm buôn bán vũ khí ma túy bán súng sextoy chơi đĩ sex bạo lực sex học đường tội phạm tình dục chơi les đĩ đực người mẫu bán dâm
https://naveridbuy.blogspot.com/2024/12/blog-post_87.html
legit non prescription pharmacies https://megaindiapharm.shop/# Mega India Pharm
Cheapest online pharmacy Cheapest online pharmacy family pharmacy
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%9B%84%EA%B8%B0-%EB%AA%A8%EC%9D%8C-%EC%8B%A0%EB%A2%B0%ED%95%A0-%EC%88%98-%EC%9E%88%EC%9D%84%EA%B9%8C-5dc2946813fc
canadian pharmacy prices: easy canadian pharm – online canadian pharmacy review
canadian family pharmacy: best canadian pharmacy to buy from – easy canadian pharm
us pharmacy no prescription https://megaindiapharm.com/# Mega India Pharm
https://accounting14.research.au-syd1.upcloudobjects.com/research/accounting14-(407).html
If you usually like clean, plain clothing, don’t go over the top with sequins and diamonds.
https://jet1-china-visa-27.ams3.digitaloceanspaces.com/research/jet1-chinavisa-1-(461).html
The straps and sleeves you select on your dress will affect the neckline and form of your dress.
https://inky-owl-dd3cmv.mystrikingly.com/blog/e5d41afa610
https://naveridbuy.exblog.jp/37152057/
canadian pharmacy coupon https://easycanadianpharm.shop/# canada rx pharmacy world
https://digi365sa.netlify.app/research/digi365sa-(252)
Available in 14 colours, you may be positive to discover a robe that matches your daughter or son’s wedding ceremony theme.
https://catering37c.z27.web.core.windows.net/research/catering37c-(158).html
So, you’ll wish to wear something that doesn’t conflict with the the rest of the group in photos.
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%ED%9A%A8%EA%B3%BC%EB%A5%BC-%EA%B7%B9%EB%8C%80%ED%99%94%ED%95%98%EB%8A%94-%EB%B0%A9%EB%B2%95-3ce347d9cfdf
https://ko.anotepad.com/note/read/nqx5wt7s
https://writeablog.net/jr525di7pj
It’s nearly impossible to find educated people in this particular subject, however, you sound like you know what you’re talking about! Thanks
https://medium.com/@nsw5288/%EB%B0%9C%EA%B8%B0%EB%B6%80%EC%A0%84%EA%B3%BC-%EC%A1%B0%EB%A3%A8-%EC%9E%90%EA%B0%80-%EC%A7%84%EB%8B%A8%EA%B3%BC-%EC%B9%98%EB%A3%8C%EB%B2%95-557e4352a569
https://accounting001.netlify.app/research/accounting001-(513)
The giant florals with the black background are notably on pattern and the ruching adds a flattering element.
xxl mexican pharm: purple pharmacy mexico price list – mexican drugstore online
xxl mexican pharm: xxl mexican pharm – xxl mexican pharm
Today, while I was at work, my cousin stole my iphone and tested to see if
it can survive a thirty foot drop, just so she can be a youtube sensation. My
apple ipad is now destroyed and she has 83 views. I know this is completely off topic
but I had to share it with someone!
Also visit my web page :: mitolyn reviews reddit
best online pharmacy no prescription https://easycanadianpharm.com/# canadian pharmacy in canada
pharmacy coupons http://megaindiapharm.com/# MegaIndiaPharm
https://ko.anotepad.com/note/read/s7rk2rnw
https://witty-apple-dd3cm1.mystrikingly.com/blog/7e37e3ff366
https://hallbook.com.br/blogs/376911/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%EC%A0%95%EB%A7%90-%EC%95%88%EC%A0%84%ED%95%A0%EA%B9%8C
п»їbest mexican online pharmacies reputable mexican pharmacies online xxl mexican pharm
https://aspiring-ant-dbgzhb.mystrikingly.com/blog/faq
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EC%98%A8%EB%9D%BC%EC%9D%B8-%EA%B5%AC%EB%A7%A4-%EC%8B%9C-%EC%A3%BC%EC%9D%98%EC%82%AC%ED%95%AD-7eb81634b40d
https://writeablog.net/zrusp1buhj
Cheapest online pharmacy: Online pharmacy USA – online pharmacy delivery usa
https://vermilion-elephant-dd3cm3.mystrikingly.com/blog/vs
https://tawny-wombat-dd3cmn.mystrikingly.com/blog/4cd329160f9
https://salmon-peach-dd3cm8.mystrikingly.com/blog/9678172c041
pharmacy coupons http://xxlmexicanpharm.com/# xxl mexican pharm
https://adaptable-goat-dd3cmf.mystrikingly.com/blog/ab864ad3a8f
discount drug pharmacy: drugmart – drug mart
best online pharmacy no prescription https://familypharmacy.company/# Online pharmacy USA
Before installing the Metamask extension, I was worried about scams, but https://metamake.org/ made everything clear and secure. I appreciate their well-written guides that ensure a safe setup process. Highly recommended for everyone!
https://inky-owl-dd3cmv.mystrikingly.com/blog/570378fab9f
Loved this!
https://ask.mallaky.com/?qa=user/fuelcork6
Having read this I believed it was rather informative. I appreciate you spending some time and energy to put this information together. I once again find myself spending a lot of time both reading and posting comments. But so what, it was still worth it!
https://writeablog.net/6iekby1s5m
no prescription needed pharmacy https://familypharmacy.company/# canadian pharmacy discount coupon
Online pharmacy USA: Online pharmacy USA – online pharmacy delivery usa
Would you wish to screen key choices metrics just like TOS and TastyTrade whereas charting on TradingView?
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B0%80%EA%B2%A9%EA%B3%BC-%ED%9A%A8%EA%B3%BC-%EC%A0%9C%EB%8C%80%EB%A1%9C-%EC%95%8C%EA%B3%A0-%EA%B5%AC%EB%A7%A4%ED%95%98%EA%B8%B0-07-31
easy canadian pharm: easy canadian pharm – canadian pharmacy meds review
canadian prescription pharmacy http://xxlmexicanpharm.com/# buying prescription drugs in mexico online
https://ya-4545-10.8rmi2.upcloudobjects.com/the-role-of-accounting-companies-in-mergers-and-acquisitions.html
You also can coordinate with the MOB to verify your choices complement each other.
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%EA%B3%84%EC%A0%95-%EB%B3%B4%ED%98%B8-%EB%B0%A9%EB%B2%95-%EC%99%84%EB%B2%BD-%EC%A0%95%EB%A6%AC-ab3a80545ed1
reputable online pharmacy no prescription https://megaindiapharm.com/# reputable indian online pharmacy
mexican pharmaceuticals online xxl mexican pharm pharmacies in mexico that ship to usa
easy canadian pharm: easy canadian pharm – easy canadian pharm
Way cool! Some very valid points! I appreciate you penning this write-up and the rest of the site is really good.
offshore pharmacy no prescription https://megaindiapharm.shop/# best online pharmacy india
discount drug pharmacy: legit non prescription pharmacies – discount drug pharmacy
online pharmacy without prescription http://discountdrugmart.pro/# discount drug mart pharmacy
https://ocher-cat-dd3cmm.mystrikingly.com/blog/642842abd0f
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%ED%9B%84-%EB%B6%80%EC%9E%91%EC%9A%A9%EA%B3%BC-%EB%8C%80%EC%B2%98-%EB%B0%A9%EB%B2%95-652f040aa457
May I simply say what a comfort to uncover someone who truly understands what they’re discussing on the web. You certainly understand how to bring an issue to light and make it important. More and more people must read this and understand this side of your story. I was surprised you are not more popular given that you most certainly have the gift.
UID_72942561###
Berita Hot! 🔥🔥 Isa Rachmatarwata Tersangka Kasus Jiwasraya Buntut kerugian negara hingga 16,8 Triliun! 😲😲
easy canadian pharm: easy canadian pharm – easy canadian pharm
online canadian pharmacy coupon https://discountdrugmart.pro/# discount drug mart
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EB%B9%84%EB%B0%80%EB%B2%88%ED%98%B8-%EB%B3%B5%EA%B5%AC%ED%95%98%EB%8A%94-5%EA%B0%80%EC%A7%80-%EB%B0%A9%EB%B2%95-216aafd6cf7c
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EB%B9%84%EB%B0%80%EB%B2%88%ED%98%B8-%EB%B3%B5%EA%B5%AC%ED%95%98%EB%8A%94-5%EA%B0%80%EC%A7%80-%EB%B0%A9%EB%B2%95-216aafd6cf7c
pharmacy coupons https://discountdrugmart.pro/# discount drug mart
xxl mexican pharm: xxl mexican pharm – buying prescription drugs in mexico
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC%EC%9D%98-%EB%8C%80%EC%95%88%EB%93%A4-%EC%84%A0%ED%83%9D%EC%A7%80%EB%8A%94-09-12
I like this website its a master peace ! Glad I detected this on google .
Mega India Pharm MegaIndiaPharm buy prescription drugs from india
If you want a trusted source for downloading Metamask, visit https://metaduck.org/. Their guide ensures you install it securely.
I like it whenever people come together and share thoughts. Great website, stick with it.
https://jekyll.s3.us-east-005.backblazeb2.com/20241129-12/research/je-tall-sf-marketing-(320).html
Its expansive selection, becoming fit and trendy design deem Montage the leader in Mother of the Bride and Mother of the Groom dress collections.
https://medium.com/@carlfrancoh38793/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EB%B9%84%EB%B0%80%EB%B2%88%ED%98%B8-%EB%B3%B5%EA%B5%AC%ED%95%98%EB%8A%94-5%EA%B0%80%EC%A7%80-%EB%B0%A9%EB%B2%95-216aafd6cf7c
online pharmacy discount code https://megaindiapharm.com/# MegaIndiaPharm
buying from canadian pharmacies: canadian pharmacy online – online pharmacy canada
If you want to install Metamask on Chrome quickly and securely, check out https://metapaws.org/. The instructions are clear, making it perfect for beginners!
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/catering35c/o/research/cateing35c-(156).html
But for others, it’s restrictive, it feels too formal, and often, it finally ends up being somewhat expensive too.
UID_53550706###
Berita terbaru! 🔥 Isa Rachmatarwata Ditahan Kejagung dalam kasus Jiwasraya. 🚔👮♂️
canadian online pharmacy no prescription https://easycanadianpharm.com/# canadian pharmacies comparison
buying prescription drugs in mexico online: xxl mexican pharm – xxl mexican pharm
Very nice post. I just stumbled upon your blog and wanted
to say that I have truly enjoyed surfing around your blog posts.
After all I will be subscribing to your feed and I hope you write again very soon!
Take a look at my web page :: p1961674
http://digi38c.s3-website-us-east-1.amazonaws.com/research/digi38c-(41).html
It can be utilized for any event, and the type of it is perfect for the mother of the bride.
cheapest prescription pharmacy https://xxlmexicanpharm.shop/# xxl mexican pharm
UID_57092237###
Berita gembira! 🎉 Pasokan Gas 3 Kg di Kramat Jati Kembali Normal 🎊 Siap-siap belanja gas, ya! 💪🔥
I really enjoyed reading this! Your writing style is engaging, and the content is valuable. Excited to see more from you!
Best online pharmacy: family pharmacy – Online pharmacy USA
pharmacy discount coupons https://megaindiapharm.shop/# MegaIndiaPharm
drugmart discount drug pharmacy discount drug mart
This post is very helpful! I appreciate the effort you put into making it clear and easy to understand. Thanks for sharing!
Mega India Pharm: online pharmacy india – Mega India Pharm
pharmacy no prescription required http://familypharmacy.company/# family pharmacy
UID_72339950###
Heboh! 📣🔥 Unjuk Rasa di Polda Jatim 📢 Menuduh Jokowi Terlibat Korupsi! 😱🔍
It’s nearly impossible to find educated people in this particular subject, but you seem like you know what you’re talking about! Thanks
https://storage.googleapis.com/digi188sa/research/digi188sa-(434).html
Shop stunning wedding attire for the mother-of-the-bride in normal, plus and petite sizes at Adrianna Papell.
https://hallbook.com.br/blogs/278113/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%98%A4%ED%94%84%EB%9D%BC%EC%9D%B8-%EC%95%BD%EA%B5%AD%EA%B3%BC-%EC%98%A8%EB%9D%BC%EC%9D%B8-%EC%87%BC%ED%95%91%EC%9D%98-%EC%9E%A5%EB%8B%A8%EC%A0%90
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EC%98%A8%EB%9D%BC%EC%9D%B8-%EA%B5%AC%EB%A7%A4-%EB%B0%A9%EB%B2%95%EA%B3%BC-%EC%A3%BC%EC%9D%98-%EC%82%AC%ED%95%AD-c80ca72b0103
https://bogin008.netlify.app/research/bogin008-(251)
These robes are stylish and classy with just a bit of an edge.
https://marketing-99.b-cdn.net/research/marketing-(127).html
It’s necessary to make sure that any head items don’t swamp your body, and doesn’t disguise your face.
This post is very helpful! I appreciate the effort you put into making it clear and easy to understand. Thanks for sharing!
https://digi205sa.z26.web.core.windows.net/research/digi205sa-(218).html
It’s often frequent practice to avoid carrying white, ivory or cream.
cheap pharmacy no prescription https://familypharmacy.company/# legal online pharmacy coupon code
UID_27764099###
Ini yang di ganti >>> “Bingung Kenapa 😕❓” Federasi Sepak Bola Pakistan Disanksi FIFA “Baca Penyebabnya Disini! 🧐🔍”
pharmacy without prescription http://easycanadianpharm.com/# legal canadian pharmacy online
MegaIndiaPharm: Mega India Pharm – top 10 pharmacies in india
https://jekyll.s3.us-east-005.backblazeb2.com/20250109-5/research/je-tall-sf-marketing-(407).html
With a delicate match at the hips, this costume is designed to flatter you in all the right locations.
https://writeablog.net/z3f3wqgycr
Hi! I simply would like to give you a huge thumbs up for the great info you’ve got right here on this post. I am coming back to your blog for more soon.
https://naveridbuy.exblog.jp/37091141/
You have observed very interesting points! ps decent internet site.
online pharmacy without prescription https://discountdrugmart.pro/# discount drug pharmacy
canadian pharmacy without prescription https://familypharmacy.company/# buying prescription drugs from canada
UID_74743238###
Ini dia! 🎉🎉 ASN BKN Ubah Pola Kerja yang baru dan efisien! 🎉🎉.
https://naveridbuy.blogspot.com/2024/12/blog-post_87.html
https://telegra.ph/%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EC%97%86%EC%9D%B4-%EC%84%9C%EB%B9%84%EC%8A%A4-%EC%9D%B4%EC%9A%A9%ED%95%98%EB%8A%94-%ED%8C%81-12-13
https://hallbook.com.br/blogs/376913/%EC%95%84%EC%9D%B4%EB%94%94-%EA%B1%B0%EB%9E%98%EC%9D%98-%EC%88%A8%EA%B2%A8%EC%A7%84-%EC%9C%84%ED%97%98-%EB%84%A4%EC%9D%B4%EB%B2%84-%EC%95%84%EC%9D%B4%EB%94%94-%EC%95%88%EC%A0%84%ED%95%98%EA%B2%8C-%EC%A7%80%ED%82%A4%EB%8A%94-%EB%B2%95
family pharmacy: canadian pharmacy no prescription needed – Online pharmacy USA
family pharmacy cheapest pharmacy to get prescriptions filled cheapest prescription pharmacy
https://calm-cheetah-n4w12h.mystrikingly.com/blog/ifyil-pelet-sobasi-sikayet-herkes-icin-eglenceli-olabilir
I am not sure where you’re getting your info, but good topic. I needs to spend some time learning more or understanding more. Thanks for magnificent information I was looking for this information for my mission.
Having read this I believed it was very enlightening. I appreciate you spending
some time and energy to put this information together.
I once again find myself personally spending a lot of time both reading and posting
comments. But so what, it was still worthwhile!
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-vs-%EB%8B%A4%EB%A5%B8-ed-%EC%B9%98%EB%A3%8C%EC%A0%9C-%EC%B0%A8%EC%9D%B4%EC%A0%90%EC%9D%80-3b6d3d8df113
Very good information. Lucky me I found your site by accident (stumbleupon). I’ve bookmarked it for later.
canadian pharmacy world coupons https://easycanadianpharm.com/# easy canadian pharm
7sh13c
What’s special about that?
UID_74743238###
Ini dia! 🎉🎉 ASN BKN Ubah Pola Kerja yang baru dan efisien! 🎉🎉.
online pharmacy discount code https://easycanadianpharm.com/# online canadian pharmacy reviews
drug mart: drugmart – drug mart
May I simply say what a relief to find someone who
genuinely understands what they’re discussing over the
internet. You definitely understand how to bring a problem to
light and make it important. More people should check this out and understand this side of
the story. I was surprised you’re not more popular since you
definitely possess the gift.
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B0%80%EA%B2%A9%EA%B3%BC-%ED%9A%A8%EA%B3%BC-%EC%A0%9C%EB%8C%80%EB%A1%9C-%EC%95%8C%EA%B3%A0-%EA%B5%AC%EB%A7%A4%ED%95%98%EA%B8%B0-07-31
canadian pharmacy coupon code https://discountdrugmart.pro/# drug mart
The economists Emmanuel Saez and Thomas Piketty recommend much higher top marginal tax rates on the wealthy, up to 50 percent, 70 percent or even 90 percent.
canadian pharmacy discount code https://megaindiapharm.com/# MegaIndiaPharm
https://digi109sa.netlify.app/research/digi109sa-(452)
You might imagine it’s customary for the mother of the bride to wear an over-sized hat, but that’s merely not the case for 2022.
discount drugs: drug mart – drug mart
This is very interesting, You’re a very skilled blogger. I’ve joined your feed and look forward to seeking more of your magnificent post. Also, I’ve shared your website in my social networks!
family pharmacy Best online pharmacy family pharmacy
Since most shelters nonetheless didn’t have computers, they faxed their lists to the Sauls’ neighbor, who slid the lists underneath the door.
Beberapa kasino memiliki area khusus untuk slot http://bonaslot.site/# Bermain slot bisa menjadi pengalaman sosial
https://naveridbuy.blogspot.com/2024/11/2024.html
https://candid-lion-dd3cm3.mystrikingly.com/blog/8c25ae9d7a9
UID_83344528###
Inilah 🎉🎉 Pupuk Inovatif Kebun Riset Kujang yang bikin Wamen BUMN bangga! 💪🏻🇮🇩
http://bonaslot.site/# Kasino sering memberikan hadiah untuk pemain setia
Kasino di Indonesia menyediakan hiburan yang beragam http://slotdemo.auction/# Pemain harus menetapkan batas saat bermain
https://medium.com/@carlfrancoh38793/%EC%95%84%EC%9D%B4%EB%94%94-%EC%83%9D%EC%84%B1-%EC%96%B4%EB%A0%A4%EC%9A%B8-%EB%95%8C-%EA%B5%AC%EB%A7%A4-%EB%8C%80%EC%95%88-%EC%95%8C%EC%95%84%EB%B3%B4%EA%B8%B0-62055e09b46c
https://marketing04.sgp1.digitaloceanspaces.com/research/marketing-(240).html
Whether you may have your coronary heart on embroidery, embellishment, sequin, or ruched silk smoothness, golden clothes look great in all kinds and designs.
UID_83344528###
Inilah 🎉🎉 Pupuk Inovatif Kebun Riset Kujang yang bikin Wamen BUMN bangga! 💪🏻🇮🇩
Beberapa kasino memiliki area khusus untuk slot: preman69 – preman69 slot
Keseruan bermain slot selalu menggoda para pemain https://garuda888.top/# Slot memberikan kesempatan untuk menang besar
Hey I know this is off topic but I was wondering if you knew of any widgets
I could add to my blog that automatically tweet my newest twitter updates.
I’ve been looking for a plug-in like this for quite
some time and was hoping maybe you would have some experience with something like this.
Please let me know if you run into anything. I truly
enjoy reading your blog and I look forward to your new updates.
Greetings I am so delighted I found your blog page,
I really found you by mistake, while I was searching on Digg for something else, Anyways I am here
now and would just like to say thank you for a tremendous post
and a all round enjoyable blog (I also love the theme/design), I don’t have
time to go through it all at the moment but I have bookmarked it
and also added your RSS feeds, so when I have
time I will be back to read more, Please do keep up the
great job.
https://digi320sa.netlify.app/research/digi320sa-(42)
Thus, you ought to not wear white when you are the mom of the bride and even one thing like ivory.
Slot menjadi bagian penting dari industri kasino https://preman69.tech/# Mesin slot baru selalu menarik minat
UID_21891068###
Takjub 😮 dengan fenomena serbu gas? Yuk, baca Warung Tatang Diserbu Warga dan temukan faktanya! 🕵️♀️👀
garuda888 garuda888 slot Kasino di Indonesia menyediakan hiburan yang beragam
Mesin slot menawarkan pengalaman bermain yang cepat http://slotdemo.auction/# Permainan slot mudah dipahami dan menyenangkan
Slot dengan bonus putaran gratis sangat populer: garuda888 slot – garuda888.top
UID_21891068###
Takjub 😮 dengan fenomena serbu gas? Yuk, baca Warung Tatang Diserbu Warga dan temukan faktanya! 🕵️♀️👀
https://slotdemo.auction/# Permainan slot mudah dipahami dan menyenangkan
Thanks for this marvelous post, I am glad I observed this website on yahoo.
What’s up, constantly i used to check blog posts here
early in the daylight, for the reason that i like to find out more
and more.
Here is my website: natural alternative to mounjaro
https://viastoer.blogspot.com/2024/07/blog-post_92.html
https://aqua-anemone-dbgzh3.mystrikingly.com/blog/49453981155
Crypto security is a big concern, so I was careful about where to download Metamask. Luckily, I found https://download.metaredi.org/, which provided a safe and detailed guide to installation. Now I can use my wallet worry-free!
https://jekyll.s3.us-east-005.backblazeb2.com/20241220-15/research/je-tall-sf-marketing-(26).html
The bridesmaids collected the recipes and created them right into a newlyweds cookery book that they gave the couple up their day.
Keseruan bermain slot selalu menggoda para pemain http://slot88.company/# Bermain slot bisa menjadi pengalaman sosial
Slot dengan bonus putaran gratis sangat populer: slotdemo – slot demo
Banyak pemain berusaha untuk mendapatkan jackpot http://slotdemo.auction/# Jackpot besar bisa mengubah hidup seseorang
https://bonaslot.site/# Mesin slot menawarkan berbagai tema menarik
garuda888 garuda888.top Banyak kasino menawarkan permainan langsung yang seru
Slot dengan tema film terkenal menarik banyak perhatian http://slotdemo.auction/# Pemain harus menetapkan batas saat bermain
Hi there colleagues, how is all, and what you want to say
regarding this paragraph, in my view its really awesome in support of me.
Kasino di Jakarta memiliki berbagai pilihan permainan: preman69.tech – preman69.tech
грузоперевозки для юридических лиц перевозка телефизора
http://slot88.company/# Pemain harus menetapkan batas saat bermain
giw1mp
Pemain harus menetapkan batas saat bermain https://slot88.company/# Mesin slot menawarkan pengalaman bermain yang cepat
https://je-tall-marketing-363.b-cdn.net/research/je-tall-sf-marketing-(371).html
It’s out there in a spread of colors, from “champagne” (off-white) to navy.
Well-written and insightful! Your points are spot on, and I found the information very useful. Keep up the great work!
https://bogin6c.b-cdn.net/research/bogin6C-(432).html
She’s a superhero to you and your entire family, so why not let her gown the part.
Pemain harus menetapkan batas saat bermain: bonaslot.site – bonaslot
https://jekyll.s3.us-east-005.backblazeb2.com/20250102-12/research/je-tall-sf-marketing-(176).html
Experiment with strapless types, surprising lengths, or fashionable jumpsuits.
https://preman69.tech/# Mesin slot digital semakin banyak diminati
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi43sa/o/research/digi43sa-(226).html
A robe with jewels on the neckline alleviates the necessity for a necklace or loads of different extras.
demo slot pg akun demo slot Kasino di Bali menarik banyak pengunjung
Permainan slot mudah dipahami dan menyenangkan https://bonaslot.site/# Pemain sering mencoba berbagai jenis slot
Mesin slot dapat dimainkan dalam berbagai bahasa http://slotdemo.auction/# Banyak pemain berusaha untuk mendapatkan jackpot
UID_25978847###
situs terbaik hanya di slot gacor agentotoplay
An interesting discussion is worth comment. I think that you need to write more about this subject matter, it might not be a taboo subject but usually people don’t talk about these subjects. To the next! Best wishes.
п»їKasino di Indonesia sangat populer di kalangan wisatawan: slot demo – slotdemo
UID_25978847###
situs terbaik hanya di slot gacor agentotoplay
http://garuda888.top/# Kasino menawarkan pengalaman bermain yang seru
Pemain harus menetapkan batas saat bermain http://slot88.company/# Kasino sering memberikan hadiah untuk pemain setia
It’s the best time to make a few plans for the future and it’s time to
be happy. I’ve learn this put up and if I could I wish to recommend you
few fascinating things or tips. Perhaps you could write subsequent articles relating to this article.
I desire to read more things about it!
Here is my web blog salt trick for men
Slot memberikan kesempatan untuk menang besar: preman69.tech – preman69.tech
Kasino di Jakarta memiliki berbagai pilihan permainan https://bonaslot.site/# Mesin slot menawarkan pengalaman bermain yang cepat
http://slotdemo.auction/# Mesin slot baru selalu menarik minat
I’m impressed, I must say. Rarely do I encounter a blog that’s equally educative and amusing, and without a doubt, you’ve hit the nail on the head. The issue is something too few folks are speaking intelligently about. I’m very happy I stumbled across this during my hunt for something regarding this.
demo slot pg akun demo slot Slot menawarkan kesenangan yang mudah diakses
Каталог финансовых организаций srochno-zaym-online.ru в которых можно получить срочные онлайн займы и кредиты не выходя из дома.
новинки кино 2025 трейлер американские сериалы онлайн Netflix 2025
Kasino mendukung permainan bertanggung jawab http://bonaslot.site/# Slot dengan bonus putaran gratis sangat populer
Kasino menawarkan pengalaman bermain yang seru: preman69 – preman69
перевозка мотоциклов квартирный переезд минск спб
https://bonaslot.site/# Banyak pemain menikmati jackpot harian di slot
UID_95859078###
Baru-baru ini, para pemain Mahjong Wins 3 dikejutkan dengan bocoran RTP yang diklaim bisa meningkatkan peluang kemenangan secara signifikan. Banyak yang percaya bahwa informasi ini membantu mereka mendapatkan hasil yang lebih konsisten dalam permainan. Jika Anda ingin tahu lebih lanjut, cek bocoran RTP Mahjong Wins 3 hari ini dan lihat apakah strategi ini benar-benar efektif.
Kasino di Jakarta memiliki berbagai pilihan permainan https://preman69.tech/# Pemain harus memahami aturan masing-masing mesin
https://ya-4545-29.s3.us-east-005.backblazeb2.com/market-entry-strategy-after-company-registration.html
You can present a bit of cleavage, but an extreme quantity of can seem a bit inappropriate.
Banyak pemain menikmati jackpot harian di slot: slot 88 – slot88
https://preman69.tech/# Slot dengan tema film terkenal menarik banyak perhatian
UID_95859078###
Baru-baru ini, para pemain Mahjong Wins 3 dikejutkan dengan bocoran RTP yang diklaim bisa meningkatkan peluang kemenangan secara signifikan. Banyak yang percaya bahwa informasi ini membantu mereka mendapatkan hasil yang lebih konsisten dalam permainan. Jika Anda ingin tahu lebih lanjut, cek bocoran RTP Mahjong Wins 3 hari ini dan lihat apakah strategi ini benar-benar efektif.
UID_57331425###
Skandal terbaru mengguncang komunitas pecinta game slot setelah seorang admin terkenal, Rachel, dikabarkan tertangkap membocorkan pola kemenangan Gate of Olympus. Banyak yang bertanya-tanya apakah informasi ini benar-benar akurat atau hanya sekadar rumor yang beredar di kalangan pemain. Simak lebih lanjut detailnya dalam artikel admin Rachel tertangkap bocorkan pola Gate of Olympus.
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi61sa/o/research/digi61sa-(136).html
Draw inspiration from mix-and-match bridesmaid dresses by choosing a color that coordinates with, but does not precisely match, the maids palette.
Slot dengan tema budaya lokal menarik perhatian http://slot88.company/# Slot dengan fitur interaktif semakin banyak tersedia
slot demo gratis [url=https://slotdemo.auction/#]akun demo slot[/url] Banyak pemain berusaha untuk mendapatkan jackpot
sex nhật hiếp dâm trẻ em ấu dâm buôn bán vũ khí ma túy bán súng sextoy chơi đĩ sex bạo lực sex học đường tội phạm tình dục chơi les đĩ đực người mẫu bán dâm
http://bonaslot.site/# Banyak kasino memiliki program loyalitas untuk pemain
Kasino selalu memperbarui mesin slotnya: slot 88 – slot 88
Каталог финансовых организаций srochno zaym online ru в которых можно получить срочные онлайн займы и кредиты не выходя из дома.
смотреть фильмы онлайн бесплатно документальные фильмы 2025 HD 1080p
Hi everybody, here every one is sharing these kinds of know-how,
therefore it’s pleasant to read this weblog, and I used to visit this website all the time.
Why visitors still use to read news papers when in this technological globe everything is existing on net?
Bermain slot bisa menjadi pengalaman sosial http://slot88.company/# Slot menawarkan berbagai jenis permainan bonus
UID_57331425###
Skandal terbaru mengguncang komunitas pecinta game slot setelah seorang admin terkenal, Rachel, dikabarkan tertangkap membocorkan pola kemenangan Gate of Olympus. Banyak yang bertanya-tanya apakah informasi ini benar-benar akurat atau hanya sekadar rumor yang beredar di kalangan pemain. Simak lebih lanjut detailnya dalam artikel admin Rachel tertangkap bocorkan pola Gate of Olympus.
https://bogin28.fra1.digitaloceanspaces.com/research/bogin28-(455).html
Look for dresses in champagne, navy and even black (yes, it is totally modern to wear black to a wedding!) for a refined colour palette.
http://preman69.tech/# Kasino di Bali menarik banyak pengunjung
Kasino di Indonesia menyediakan hiburan yang beragam: slot demo – slot demo
https://digi55sa.netlify.app/research/digi55sa-(473)
Moms who need to give somewhat drama, consider vivid hues and assertion options.
Banyak pemain menikmati bermain slot secara online http://garuda888.top/# Permainan slot mudah dipahami dan menyenangkan
BonaSlot bonaslot Kasino menawarkan pengalaman bermain yang seru
After looking over a few of the articles on your web page, I truly appreciate your way of writing a blog. I saved as a favorite it to my bookmark site list and will be checking back in the near future. Please visit my website too and tell me what you think.
http://slot88.company/# Slot dengan tema film terkenal menarik banyak perhatian
Pemain harus menetapkan batas saat bermain: bonaslot.site – BonaSlot
Excellent blog here! Also your web site loads up fast!
What host are you using? Can I get your affiliate link to your host?
I wish my site loaded up as fast as yours lol
Slot modern memiliki grafik yang mengesankan http://garuda888.top/# Kasino sering mengadakan turnamen slot menarik
UID_17136916###
Kisah inspiratif datang dari seorang tukang ojek online asal Tangerang yang berhasil membawa pulang hadiah fantastis setelah bermain Mahjong Ways 2. Dengan modal kecil, ia sukses mengubah nasibnya dan meraih kemenangan besar senilai 200 juta rupiah. Penasaran bagaimana caranya? Simak kisah lengkapnya di artikel tukang ojek online menang 200 juta dari Mahjong Ways 2.
https://ya-catering18.ewr1.vultrobjects.com/service-etiquette-at-catering-events.html
This combination is very great for summer season weddings.
UID_17136916###
Kisah inspiratif datang dari seorang tukang ojek online asal Tangerang yang berhasil membawa pulang hadiah fantastis setelah bermain Mahjong Ways 2. Dengan modal kecil, ia sukses mengubah nasibnya dan meraih kemenangan besar senilai 200 juta rupiah. Penasaran bagaimana caranya? Simak kisah lengkapnya di artikel tukang ojek online menang 200 juta dari Mahjong Ways 2.
hdrezka net новинки Netflix 2025 Netflix 2025
https://able2know.org/user/heliumsilver3/
Hi, this weekend is fastidious designed for me, as this time i am reading this impressive informative paragraph here at my residence.
http://slot88.company/# Slot menawarkan berbagai jenis permainan bonus
https://marketing-06.b-cdn.net/research/marketing-(235).html
For the mom whose style is modern and minimal, go for a gown with an architectural silhouette in her favourite colour.
Banyak pemain menikmati jackpot harian di slot: bonaslot.site – bonaslot.site
Slot menawarkan kesenangan yang mudah diakses https://garuda888.top/# Slot menjadi bagian penting dari industri kasino
Very soon this site will be famous among all blogging and site-building users, due to it’s nice articles or reviews
Before I found https://metamaker.org/#metamask-download, I struggled to download Metamask securely. Their guide is perfect for both beginners and experienced users. A must-visit site for crypto enthusiasts!
https://filedn.eu/l46Ju9IQhhQ84ifWoIzEYnJ/digi209sa/research/digi209sa-(359).html
Today’s mother of the bride collections encompass figure-flattering frocks which may be designed to accentuate your mum’s finest bits.
https://slot88.company/# Kasino selalu memperbarui mesin slotnya
Kasino sering memberikan hadiah untuk pemain setia https://garuda888.top/# Kasino menyediakan layanan pelanggan yang baik
Kasino memastikan keamanan para pemain dengan baik: preman69 – preman69.tech
garuda888 slot garuda888 Banyak pemain berusaha untuk mendapatkan jackpot
UID_87427935###
Cek yuk! 🚍👮♂️Operasi Keselamatan 2025 Polres Ciamis Siapa tahu bus favoritmu jadi sasaran! 😱👍
https://digi261sa.z36.web.core.windows.net/research/digi261sa-(259).html
Montage by Mon Cheri designer Ivonne Dome designs this special day line with the subtle, fashion-forward mother in thoughts.
UID_87427935###
Cek yuk! 🚍👮♂️Operasi Keselamatan 2025 Polres Ciamis Siapa tahu bus favoritmu jadi sasaran! 😱👍
https://storage.googleapis.com/catering38c/research/catering38c-(346).html
The mom of the bride gown gallery has a dress for every finances and every physique sort together with plus sizes.
Slot dengan grafis 3D sangat mengesankan http://slotdemo.auction/# Slot menjadi daya tarik utama di kasino
http://preman69.tech/# Banyak kasino memiliki promosi untuk slot
Kasino sering mengadakan turnamen slot menarik: slot88 – slot88.company
Bermain slot bisa menjadi pengalaman sosial http://preman69.tech/# Banyak kasino memiliki promosi untuk slot
https://garuda888.top/# Slot dengan grafis 3D sangat mengesankan
Link exchange is nothing else but it is only placing the
other person’s website link on your page at proper place and other person will also do similar for
you.
Also visit my web blog: tonic greens herpes review
Slot menjadi daya tarik utama di kasino: demo slot pg – slotdemo
garuda888 slot garuda888 slot Slot dengan grafis 3D sangat mengesankan
Slot modern memiliki grafik yang mengesankan http://bonaslot.site/# Banyak pemain menikmati jackpot harian di slot
http://bonaslot.site/# Kasino sering mengadakan turnamen slot menarik
Slot dengan tema budaya lokal menarik perhatian: bonaslot.site – bonaslot.site
Mesin slot menawarkan berbagai tema menarik http://bonaslot.site/# Kasino di Jakarta memiliki berbagai pilihan permainan
Very nice post. I just stumbled upon your blog and wanted to say that I’ve truly enjoyed surfing around
your blog posts. After all I will be subscribing to your feed and I hope you write again very soon!
лучшие подборки фильмов фильмы hd rezka фантастика новинки с субтитрами
http://bonaslot.site/# Pemain harus memahami aturan masing-masing mesin
Slot menjadi daya tarik utama di kasino: bonaslot.site – BonaSlot
UID_18563832###
Ini yang di ganti >>> Yuk, ketahui lebih lanjut tentang Syarat Gabung OECD dan Pentingnya Ratifikasi Konvensi Antisuap di sini! 🕵️♀️🔎📚.
https://accounting030c.netlify.app/research/accounting030c-(118)
You can find a fantastic choice here and they’re nice quality that won’t break the bank.
Kasino menyediakan layanan pelanggan yang baik http://bonaslot.site/# Beberapa kasino memiliki area khusus untuk slot
UID_18563832###
Ini yang di ganti >>> Yuk, ketahui lebih lanjut tentang Syarat Gabung OECD dan Pentingnya Ratifikasi Konvensi Antisuap di sini! 🕵️♀️🔎📚.
Its like you read my mind! You appear to know so much about this, like you wrote the book in it or something.
I think that you can do with a few pics to drive the message home a little
bit, but other than that, this is wonderful blog. An excellent read.
I will definitely be back.
Review my webpage – 7 second salt trick ed
https://je-tall-sf-marketing-133.ams3.digitaloceanspaces.com/research/je-tall-sf-marketing-(96).html
However, you should wait to pay attention to from the bride’s mom earlier than you start.
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
preman69 slot preman69.tech Slot menawarkan kesenangan yang mudah diakses
Aw, this was an incredibly good post. Taking a few minutes and actual effort to make a very good article… but what can I say… I hesitate a whole lot and don’t seem to get nearly anything done.
Depending on the type of dishwasher, the drained water might go right into the pipes beneath your sink or into your rubbish disposal.
I am pleased that I observed this blog, exactly the right information that I was looking for! .
http://slot88.company/# Kasino di Bali menarik banyak pengunjung
Kasino memastikan keamanan para pemain dengan baik: slot 88 – slot88
Mesin slot sering diperbarui dengan game baru http://preman69.tech/# Pemain sering berbagi tips untuk menang
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
Kasino di Indonesia menyediakan hiburan yang beragam https://garuda888.top/# п»їKasino di Indonesia sangat populer di kalangan wisatawan
if the buffalo in my head could speak german i would not know a god damm thing. What i do know is that the language of art is out of this world.
Сауна очищает организм https://sauna-broadway.ru выводя токсины через пот, укрепляет иммунитет благодаря перепадам температуры, снимает стресс, расслабляя мышцы и улучшая кровообращение. Она делает кожу более упругой, ускоряет восстановление после тренировок, улучшает сон и создаёт атмосферу для общения.
With Amazon, Bezos tapped into a strong new e-commerce market.
http://garuda888.top/# Keseruan bermain slot selalu menggoda para pemain
Slot menawarkan kesenangan yang mudah diakses http://slot88.company/# Kasino memiliki suasana yang energik dan menyenangkan
Maybe the hair tip took some microorganisms with it because it pierced the skin.
Its artwork panels are top-high quality even when compared to the others in the murim style.
https://digi315sa.z32.web.core.windows.net/research/digi315sa-(237).html
This deco-inspired gown will shimmer in photographs and stun on the dance ground.
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
Bermain slot bisa menjadi pengalaman sosial: slot88 – slot88.company
Korean cosmetics http://www.mignonmuse.com/bbs/board.php?bo_table=free&wr_id=389773 perfect skin without effort! Innovative formulas, Asian traditions and visible results. Try the best skin care products right now!
He continued as governor till January 1776, when colonial militiamen placed him below house arrest, which lasted until the middle of June.
Pemain sering mencoba berbagai jenis slot http://bonaslot.site/# Slot dengan bonus putaran gratis sangat populer
slot demo slotdemo Banyak pemain menikmati bermain slot secara online
https://marketing-100.b-cdn.net/research/marketing-(466).html
If you haven’t heard from her by about five months before the marriage, don’t be afraid to reach out and ask for an replace on the gown code.
Slot memberikan kesempatan untuk menang besar https://garuda888.top/# Kasino sering mengadakan turnamen slot menarik
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
https://digi101sa.netlify.app/research/digi101sa-(166)
If you like impartial tones, gold and silver dresses are promising choices for an MOB!
http://bonaslot.site/# Slot modern memiliki grafik yang mengesankan
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
https://marketing-62.b-cdn.net/research/marketing-(237).html
Her mom, who equally sparkled in a gold silk dupioni floor-length skirt go properly with.
doxycycline hyclate 100mg: doxycycline 2014 – where to get doxycycline
doxycycline order uk: doxycycline 100mg price in india – doxycycline online sale
purchase doxycycline online: DoxHealthPharm – doxycycline 100mg tablet price in india
https://filedn.eu/l46Ju9IQhhQ84ifWoIzEYnJ/digi45sa/research/digi45sa-(467).html
However, to determine whether or not you must also coordinate with each moms, examine in with the bride.
https://zithropharm.shop/# generic zithromax india
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-193/research/je-tall-sf-marketing-(344).html
This style is finished with quick sleeves and a beneath the knee hem, and has a hid centre again zip fastening.
UID_97211224###
Yuk, sehat bersama! 👨⚕️👩⚕️ Cek kondisi tubuh kamu di Program Cek Kesehatan Gratis sekarang juga! 💉🌡️ Selalu jaga kesehatan, ya! 🏥💖
doxycycline acne: DoxHealthPharm – doxycycline uk pharmacy
UID_97211224###
Yuk, sehat bersama! 👨⚕️👩⚕️ Cek kondisi tubuh kamu di Program Cek Kesehatan Gratis sekarang juga! 💉🌡️ Selalu jaga kesehatan, ya! 🏥💖
amoxicillin 775 mg: amoxicillin 500 mg without prescription – amoxicillin 875 125 mg tab
https://marketing-110.b-cdn.net/research/marketing-(293).html
A matching white choker topped off this mother-of-the-bride’s look, which was additionally complemented by an elegant low bun.
generic zithromax 500mg zithromax for sale cheap buy zithromax online cheap
can i buy cheap clomid tablets: ClmHealthPharm – how can i get clomid without insurance
http://mozillabd.science/index.php?title=knightshields5065
Hey! Do you use Twitter? I’d like to follow you if that would be ok. I’m undoubtedly enjoying your blog and look forward to new posts.
http://doxhealthpharm.com/# doxycycline 50 mg india
The Novavax vaccine has been clinically tested in South Africa, the United Kingdom and the U.S.
doxycycline 100mg dogs: DoxHealthPharm – order doxycycline 100mg
purchase doxycycline online: Dox Health Pharm – order doxycycline online australia
UID_55590637###
situs terbaik hanya di slot gacor agentotoplay
https://marketing31.syd1.digitaloceanspaces.com/research/marketing-(463).html
Let the solutions to a few of our most incessantly asked questions guide you in the best course.
where can i order doxycycline: DoxHealthPharm – doxycyline
I seriously love your website.. Excellent colors & theme. Did you create this site yourself? Please reply back as I’m hoping to create my very own blog and want to find out where you got this from or just what the theme is named. Thanks.
Yes! Finally something about what is the salt trick for men.
My web blog; salt penis trick
Can I simply say thats a relief to discover someone who actually knows what theyre talking about over the internet. You actually learn how to bring a difficulty to light to make it crucial. The diet should check out this and appreciate this side from the story. I cant think youre less well-known since you definitely have the gift.
https://doxhealthpharm.com/# doxycycline 1mg
cheap amoxicillin 500mg: amoxicillin 875 mg tablet – amoxicillin 1000 mg capsule
Everything is very open with a precise description of the issues. It was truly informative. Your site is very helpful. Thanks for sharing.
ampicillin amoxicillin Amo Health Pharm where to buy amoxicillin 500mg without prescription
doxycycline 200 mg capsules: doxycycline 40 mg cost – doxycycline 100mg best price
https://vuf.minagricultura.gov.co/Lists/Informacin%20Servicios%20Web/DispForm.aspx?ID=10462639
This information is invaluable. How can I find out more?
antibiotics doxycycline: DoxHealthPharm – doxycycline 5553
where to buy cheap clomid without dr prescription: ClmHealthPharm – cost of clomid pill
I love your blog.. very nice colors & theme. Did you make this website yourself or did you hire someone
to do it for you? Plz respond as I’m looking to
create my own blog and would like to find out where u got this from.
many thanks
https://amohealthpharm.shop/# where to buy amoxicillin
doxycycline price usa: doxycycline 2014 – doxycycline no prescription best prices
where can i buy zithromax medicine: zithromax cost australia – zithromax buy
where to get generic clomid online: ClmHealthPharm – where buy cheap clomid without insurance
http://zithropharm.com/# where can you buy zithromax
can i order generic clomid ClmHealthPharm buying generic clomid without insurance
where can i buy zithromax uk: zithromax 500mg price in india – zithromax z-pak price without insurance
medicine amoxicillin 500: AmoHealthPharm – can you buy amoxicillin over the counter
https://filedn.eu/l46Ju9IQhhQ84ifWoIzEYnJ/digi61sa/research/digi61sa-(354).html
If the wedding is more formal, anticipate to wear a longer robe or long skirt.
boost of subscribers in tik tok telegram followers boost
amoxicillin discount coupon: can you buy amoxicillin uk – amoxicillin 800 mg price
amoxicillin cephalexin: amoxicillin online purchase – buy cheap amoxicillin online
https://zithropharm.com/# zithromax without prescription
Since these elements differ for each particular person, we can’t guarantee your success, results, or revenue level, nor are we responsible on your success or failure.
They can even typically be discovered at storage gross sales or thrift stores.
zithromax purchase online: Zithro Pharm – zithromax cost uk
clomid without dr prescription: get cheap clomid no prescription – how to buy generic clomid without prescription
purchase amoxicillin online: AmoHealthPharm – medicine amoxicillin 500
https://ya-chinavisa-1.ewr1.vultrobjects.com/frequently-asked-questions-and-solutions-for-taiwan-compatriot-permit-application-9.html
Choose a timeless look, similar to a mermaid fishtail gown.
Hello, i think that i saw you visited my weblog
so i came to “return the favor”.I am trying to find things to improve my website!I suppose its ok to use a few of your ideas!!
Visit my site – is leanbiome legit
buy zithromax without prescription online zithromax 250 mg tablet price zithromax 500 without prescription
https://amohealthpharm.shop/# where to buy amoxicillin
Few vehicle elements have evolved over the years as much as tires.
https://chinavisa7c.z38.web.core.windows.net/research/chinavisa7c-(400).html
Straight-leg pants create a streamlined silhouette that subtly enhances the velvet burnout-print high and jacket.
where to get amoxicillin over the counter: Amo Health Pharm – amoxicillin 500 mg without prescription
antibiotics doxycycline: Dox Health Pharm – buy doxycycline online uk
The prehab centered on his arm energy so he may lift himself in and out of chairs and his bed until his might apply pressure on his rebuilt knee.
buy zithromax 1000mg online: ZithroPharm – average cost of generic zithromax
Nominal gross home product is defined as the market value of all remaining goods produced in a geographical area, normally a rustic; this will depend on the portions of goods and companies produced, and their respective costs.
https://amohealthpharm.shop/# how to get amoxicillin over the counter
zithromax for sale us: ZithroPharm – zithromax online usa
https://storage.googleapis.com/digi161sa/research/digi161sa-(48).html
Searching for off-the-shoulder necklines or long sleeves?
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/accounting25/research/accounting25-(7).html
To inspire your mother’s personal pick, we’ve rounded up a set of robes that real moms wore on the massive day.
where to get clomid now: where buy clomid no prescription – where can i get clomid pill
amoxicillin 500 mg price Amo Health Pharm antibiotic amoxicillin
amoxicillin 825 mg: can we buy amoxcillin 500mg on ebay without prescription – amoxicillin without rx
http://digi19sa.s3-website-us-east-1.amazonaws.com/research/digi19sa-(467).html
However, coordination continues to be essential for stylish pictures on the large day.
http://doxhealthpharm.com/# buy cheap doxycycline uk
doxycycline 100mg price in south africa: doxycycline cost canada – cheapest 40 mg doxycycline
This means of compartmentalization limits the damage from a breach in safety of personal or any sort of private information.
amoxicillin without a doctors prescription: amoxicillin 500mg cost – amoxicillin 250 mg price in india
how to get zithromax over the counter: ZithroPharm – zithromax 250 mg australia
https://amohealthpharm.shop/# buying amoxicillin online
can you buy generic clomid tablets: cost generic clomid for sale – buying generic clomid price
https://jekyll.s3.us-east-005.backblazeb2.com/20250117-7/research/je-tall-sf-marketing-(352).html
Check out the information for great ideas and concepts, and prepare to cut a dash at your daughter’s D-day.
Divisia Monetary Aggregates are available for the United Kingdom by the Bank of England, for the United States by the Federal Reserve Financial institution of St.
https://digi78sa.z14.web.core.windows.net/research/digi78sa-(397).html
Spring and summer season weddings call for delicate tones, floral motifs, and a romantic flair.
where can i get cheap clomid price can i purchase generic clomid online can i order cheap clomid prices
https://ya-drbogin-1.nyc3.digitaloceanspaces.com/the-benefits-of-massage-for-cancer-patients.html
The greatest mother of the bride clothes fill you with confidence on the day and are comfortable enough to wear all day and into the evening.
doxycycline 40 mg price: Dox Health Pharm – doxycycline 200 mg
doxycycline generic price: how to get doxycycline online – where can i purchase doxycycline
https://zithropharm.shop/# zithromax 250 mg
A pediatric dentist is skilled in making that kid’s expertise as painless as potential.
can you buy zithromax over the counter in australia: buy zithromax online australia – zithromax 500 mg
https://je-tall-sf-marketings-115.b-cdn.net/research/je-tall-sf-marketing-(421).html
Teri Jon has a big choice of plus dimension evening robes, and some even with extended sizing to size 20.
A fascinating discussion is worth comment. I think that you should write more about this subject matter, it may not be a taboo subject but usually people do not discuss such issues. To the next! Kind regards.
doxycycline 200: doxycycline rx coupon – doxycycline 100mg price in india
buy amoxicillin 500mg uk: Amo Health Pharm – amoxicillin 500mg capsules antibiotic
order amoxicillin online: AmoHealthPharm – amoxicillin 500mg capsule
https://amohealthpharm.shop/# amoxicillin 500mg
https://digi212sa.z28.web.core.windows.net/research/digi212sa-(312).html
This sheath costume and sequin capelet mixture boasts a modest neckline and high-slit skirt making it directly sophisticated and attractive.
https://je-tall-marketing-231.fra1.digitaloceanspaces.com/research/je-tall-sf-marketing-(135).html
Wear it to a garden celebration with block heels or wedges.
cost of generic zithromax ZithroPharm where can i buy zithromax capsules
va65n7
pharmacie en ligne: Acheter Cialis – pharmacie en ligne livraison europe
http://catering4c.s3-website-us-east-1.amazonaws.com/research/catering4c-(96).html
Celebrate their big day in type with our Mother of the Bride or Groom outfits.
Dubai in recent years has become the most favorite tourist’s destination and also a favorite place for the business community in the Middle Eastern region and this is the main reason why Dubai continues to receive an increased number of tourists, visitors, and immigrants every year which as a result increases the demand of residential and commercial property in Dubai.
https://je-tall-marketing-206.nyc3.digitaloceanspaces.com/research/je-tall-sf-marketing-(135).html
From affordable and stylish to designer and conventional, these are our favourite bow ties for weddings.
acheter mГ©dicament en ligne sans ordonnance https://viagrameilleurprix.com/# Viagra homme sans ordonnance belgique
Lazar, Hadara (February 1990).
Quand une femme prend du Viagra homme: Viagra pharmacie – Acheter viagra en ligne livraison 24h
http://kamagrameilleurprix.com/# trouver un mГ©dicament en pharmacie
acheter mГ©dicament en ligne sans ordonnance
купить предзнаменования poe 2 купить сферы царей пое 2
Stocks which are acquired are understandably among the perfect on the earth.
pharmacie en ligne pas cher http://pharmaciemeilleurprix.com/# pharmacie en ligne france livraison belgique
pharmacies en ligne certifiГ©es: achat kamagra – pharmacie en ligne france pas cher
Achat mГ©dicament en ligne fiable pharmacie en ligne pas cher pharmacie en ligne avec ordonnance
pharmacie en ligne france livraison belgique http://kamagrameilleurprix.com/# pharmacie en ligne france livraison internationale
pharmacie en ligne france livraison internationale: pharmacie en ligne france livraison internationale – pharmacie en ligne france livraison belgique
https://viagrameilleurprix.shop/# Viagra gГ©nГ©rique sans ordonnance en pharmacie
trouver un mГ©dicament en pharmacie
Viagra pas cher livraison rapide france: viagra sans ordonnance – Viagra pas cher inde
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Pharmacie en ligne livraison Europe kamagra en ligne trouver un mГ©dicament en pharmacie
Pharmacie sans ordonnance https://tadalafilmeilleurprix.shop/# acheter mГ©dicament en ligne sans ordonnance
Viagra gГ©nГ©rique sans ordonnance en pharmacie: Viagra sans ordonnance 24h – Viagra Pfizer sans ordonnance
Viagra vente libre pays: Viagra pharmacie – Viagra homme prix en pharmacie sans ordonnance
http://tadalafilmeilleurprix.com/# Pharmacie sans ordonnance
Achat mГ©dicament en ligne fiable
Hi, There’s no doubt that your site could be having web browser compatibility problems. Whenever I take a look at your web site in Safari, it looks fine but when opening in I.E., it has some overlapping issues. I just wanted to give you a quick heads up! Apart from that, excellent blog!
https://je-tall-sf-marketings-106.b-cdn.net/research/je-tall-sf-marketing-(157).html
If stylish and complex is what you are going for, consider this sequined ensemble from Alex Evenings.
pharmacie en ligne france livraison internationale https://pharmaciemeilleurprix.shop/# acheter mГ©dicament en ligne sans ordonnance
Hi there, just became aware of your blog through Google,
and found that it’s really informative. I am gonna watch
out for brussels. I’ll appreciate if you continue this in future.
Lots of people will be benefited from your writing.
Cheers!
What i do not realize is if truth be told how you are now not really a lot more neatly-favored than you may be now. You are very intelligent. You know therefore considerably in terms of this matter, produced me personally imagine it from a lot of various angles. Its like men and women don’t seem to be interested until it¦s one thing to do with Girl gaga! Your own stuffs excellent. All the time care for it up!
pharmacies en ligne certifiГ©es: trouver un mГ©dicament en pharmacie – pharmacie en ligne france fiable
https://storage.googleapis.com/digi299sa/research/digi299sa-(256).html
Look and feel actually elegant on this long dress with out stealing all the eye from the bride.
https://pharmaciemeilleurprix.com/# Pharmacie Internationale en ligne
Pharmacie en ligne livraison Europe
pharmacie en ligne kamagra en ligne Achat mГ©dicament en ligne fiable
pharmacie en ligne avec ordonnance: cialis generique – pharmacies en ligne certifiГ©es
pharmacie en ligne france livraison internationale https://tadalafilmeilleurprix.com/# pharmacie en ligne
pharmacie en ligne france fiable: pharmacie en ligne sans ordonnance – Pharmacie sans ordonnance
Day by day a considerable amount of bullion commodities are traded by many traders.
trouver un mГ©dicament en pharmacie: Cialis sans ordonnance 24h – pharmacie en ligne france fiable
https://kamagrameilleurprix.com/# trouver un mГ©dicament en pharmacie
Pharmacie en ligne livraison Europe
Pretty! This was an extremely wonderful post. Thanks for providing this information.
pharmacie en ligne pas cher https://kamagrameilleurprix.com/# pharmacie en ligne livraison europe
pharmacie en ligne sans ordonnance: kamagra gel – pharmacie en ligne france fiable
pharmacie en ligne avec ordonnance: pharmacie en ligne france – trouver un mГ©dicament en pharmacie
Pharmacie sans ordonnance Achat mГ©dicament en ligne fiable pharmacie en ligne fiable
Unquestionably consider that that you stated.
Your favourite justification seemed to be at the web the simplest thing to understand
of. I say to you, I certainly get annoyed while people consider concerns that they
just don’t recognize about. You controlled to hit the nail upon the highest as well as outlined out
the entire thing without having side effect , people could take a signal.
Will likely be back to get more. Thank you
https://viagrameilleurprix.shop/# Le gГ©nГ©rique de Viagra
pharmacie en ligne pas cher
pharmacie en ligne livraison europe https://kamagrameilleurprix.com/# Achat mГ©dicament en ligne fiable
Viagra sans ordonnance 24h Amazon: Viagra sans ordonnance 24h – Viagra vente libre allemagne
I read this piece of writing completely regarding the resemblance of newest
and earlier technologies, it’s awesome article.
https://digi78sa.z14.web.core.windows.net/research/digi78sa-(392).html
We loved how this mom’s green satin robe subtly matched the shape of her daughter’s lace wedding gown.
pharmacie en ligne avec ordonnance: pharmacie en ligne sans ordonnance – acheter mГ©dicament en ligne sans ordonnance
There’s certainly a great deal to know about this subject. I love all the points you’ve made.
https://digi67sa.z21.web.core.windows.net/research/digi67sa-(490).html
With over 3000 stores in the us and worldwide, purchasing has turn into really easy.
https://storage.googleapis.com/digi40sa/research/digi40sa-(26).html
Take inspiration from the bridesmaid clothes and communicate to your daughter to get some ideas on colors that may work properly on the day.
vente de mГ©dicament en ligne: kamagra gel – pharmacies en ligne certifiГ©es
Overseas Policy. Retrieved March 12, 2017.
http://pharmaciemeilleurprix.com/# vente de mГ©dicament en ligne
Pharmacie en ligne livraison Europe
pharmacie en ligne france livraison belgique https://viagrameilleurprix.shop/# Viagra homme prix en pharmacie sans ordonnance
vente de mГ©dicament en ligne: Pharmacie en ligne livraison Europe – pharmacie en ligne livraison europe
https://je-tall-sf-marketing-71.nyc3.digitaloceanspaces.com/research/je-tall-sf-marketing-(295).html
Following these simple guidelines are sure to make the method go smoothly and efficiently.
The Allied Operation Diadem of the Italian Campaign in Could 1944 efficiently assaulted German Gustav Line defences within the Italian Liri valley, the primary route to Rome.
https://jekyll.s3.us-east-005.backblazeb2.com/20241127-10/research/je-tall-sf-marketing-(403).html
A pink lace Erdem gown, embroidered with pink and crimson blooms, paired completely with this trendy mom’s half-up, half-down hairstyle.
pharmacie en ligne fiable Cialis sans ordonnance 24h acheter mГ©dicament en ligne sans ordonnance
pharmacie en ligne sans ordonnance: cialis prix – pharmacies en ligne certifiГ©es
Partner with probably the most sought after destination wedding ceremony planner in Delhi, so you may sit back and relax while we ship a memorable occasion to you.
The Basel Committee recognizes that operational risk is a term that has a variety of meanings and therefore, for internal purposes, banks are permitted to adopt their own definitions of operational risk, provided that the minimum elements in the Committee’s definition are included.
https://kamagrameilleurprix.com/# pharmacie en ligne france livraison belgique
trouver un mГ©dicament en pharmacie
pharmacie en ligne avec ordonnance http://viagrameilleurprix.com/# Viagra vente libre pays
pharmacie en ligne france livraison internationale: cialis sans ordonnance – Pharmacie sans ordonnance
https://digi181sa.netlify.app/research/digi181sa-(95)
As the groom’s mother, you’ll need to let the mother of the bride take the lead through the gown purchasing process.
Pharmacie sans ordonnance: kamagra oral jelly – pharmacie en ligne fiable
https://pub-5eac75c40ee344eba1593e987af1b9f7.r2.dev/why-developers-should-care-about-seo.html
Shop now through numerous retailers, including official on-line shops.
acheter mГ©dicament en ligne sans ordonnance: kamagra gel – pharmacies en ligne certifiГ©es
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/ya-chinavisa-6/validity-period-and-renewal-of-taiwan-compatriot-permit-4.html
For a stunning look, select a celebratory design that includes lace and lengthy sleeves.
hello there and thank you for your information – I have certainly picked up anything new from right here. I did however expertise several technical issues using this site, as I experienced to reload the web site lots of times previous to I could get it to load correctly. I had been wondering if your web hosting is OK? Not that I’m complaining, but slow loading instances times will sometimes affect your placement in google and could damage your high-quality score if ads and marketing with Adwords. Well I am adding this RSS to my email and could look out for a lot more of your respective exciting content. Ensure that you update this again very soon..
https://je-tall-sf-marketing-83.b-cdn.net/research/je-tall-sf-marketing-1-(2).html
As a mother, watching your son or daughter get married will be one of the most joyful experiences in your life.
п»їpharmacie en ligne france https://viagrameilleurprix.shop/# Viagra en france livraison rapide
http://pharmaciemeilleurprix.com/# Achat mГ©dicament en ligne fiable
pharmacie en ligne pas cher
http://bogin47.s3-website-sa-east-1.amazonaws.com/research/bogin47-(74).html
A twinset can have a “fuddy duddy” popularity, however it definitely doesn’t need to look old fashioned.
Acheter Sildenafil 100mg sans ordonnance: viagra sans ordonnance – Acheter Sildenafil 100mg sans ordonnance
https://digi265sa.netlify.app/research/digi265sa-(245)
Take inspiration from the bridesmaid clothes and communicate to your daughter to get some ideas on colors that can work properly on the day.
Viagra Pfizer sans ordonnance: acheter du viagra – Viagra gГ©nГ©rique sans ordonnance en pharmacie
https://forum.issabel.org/u/breaklumber0
Fantastic blog! Do you have any suggestions for aspiring writers? I’m hoping to start my own blog soon but I’m a little lost on everything. Would you propose starting with a free platform like WordPress or go for a paid option? There are so many choices out there that I’m completely overwhelmed .. Any recommendations? Appreciate it!
trouver un mГ©dicament en pharmacie https://viagrameilleurprix.shop/# Viagra sans ordonnance pharmacie France
https://tadalafilmeilleurprix.com/# pharmacie en ligne
pharmacie en ligne france pas cher
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-310/research/je-tall-sf-marketing-(345).html
One mother’s blush attire looked lovely against these two brides’ romantic wedding dresses.
acheter mГ©dicament en ligne sans ordonnance: pharmacie en ligne pas cher – pharmacie en ligne livraison europe
рейтинг игровых автоматов онлайн по выплатам casino топ
онлайн casino лучшие азартные сайты
I’ll immediately grab your rss feed as I can’t find your email subscription link or e-newsletter service. Do you’ve any? Please let me know in order that I could subscribe. Thanks.
Viagra gГ©nГ©rique pas cher livraison rapide: acheter du viagra – Meilleur Viagra sans ordonnance 24h
п»їpharmacie en ligne france: achat kamagra – pharmacie en ligne france livraison internationale
pharmacie en ligne france livraison internationale pharmacie en ligne Pharmacie en ligne livraison Europe
Pharmacie Internationale en ligne https://tadalafilmeilleurprix.com/# pharmacie en ligne livraison europe
Are you able to recognize all 50 states of the US?
http://pharmaciemeilleurprix.com/# pharmacie en ligne france livraison internationale
pharmacie en ligne sans ordonnance
Viagra homme prix en pharmacie sans ordonnance: viagra sans ordonnance – Viagra homme prix en pharmacie sans ordonnance
pharmacie en ligne france fiable: kamagra pas cher – pharmacie en ligne france fiable
киного фантастика kinogo смотреть онлайн
киного семейные фильмы kinogo фильмы о путешествиях
pharmacie en ligne livraison europe: pharmacie en ligne france – Pharmacie Internationale en ligne
Pharmacie sans ordonnance http://viagrameilleurprix.com/# Viagra 100 mg sans ordonnance
https://pharmaciemeilleurprix.com/# acheter mГ©dicament en ligne sans ordonnance
Achat mГ©dicament en ligne fiable
Pharmacie Internationale en ligne: achat kamagra – pharmacie en ligne pas cher
pharmacie en ligne france fiable kamagra pas cher acheter mГ©dicament en ligne sans ordonnance
An equity trading is quite similar to stock trading where the trade can be placed by owner of the shares, through a brokerage account, or through an agent or broker.
Pharmacie sans ordonnance: kamagra livraison 24h – pharmacie en ligne france livraison internationale
You’re so awesome! I don’t suppose I’ve read something like this before. So good to discover another person with some genuine thoughts on this topic. Seriously.. thanks for starting this up. This web site is something that’s needed on the web, someone with a bit of originality.
Pharmacie sans ordonnance https://tadalafilmeilleurprix.com/# acheter mГ©dicament en ligne sans ordonnance
https://tadalafilmeilleurprix.com/# pharmacie en ligne livraison europe
pharmacie en ligne france fiable
acheter mГ©dicament en ligne sans ordonnance: kamagra livraison 24h – pharmacie en ligne avec ordonnance
https://storage.googleapis.com/digi178sa/research/digi178sa-(432).html
Talk to your daughter in regards to the aesthetic she envisions for her wedding ceremony to help narrow down your options.
Sildenafil teva 100 mg sans ordonnance: viagra sans ordonnance – Viagra homme prix en pharmacie sans ordonnance
https://digi249sa.z29.web.core.windows.net/research/digi249sa-(483).html
I was very impressed to see that there are elegant and chic outfits for all plus measurement ladies.
Georgian and Federal types common around the time of the Revolutionary War still resonate in our hearts at this time.
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi311sa/o/research/digi311sa-(323).html
I think every of the above could work with winery weddings.
I would like to thank you for the efforts you have put in penning this site. I really hope to view the same high-grade content from you later on as well. In fact, your creative writing abilities has inspired me to get my own, personal website now 😉
Pharmacie Internationale en ligne http://tadalafilmeilleurprix.com/# pharmacie en ligne france livraison belgique
It is noticed that increasingly artists are looking for sources to get the previous maps so as to incorporate the previous kinds into their fashionable generation paintings.
http://kamagrameilleurprix.com/# pharmacie en ligne avec ordonnance
pharmacie en ligne france fiable
Pharmacie sans ordonnance pharmacie en ligne pas cher pharmacie en ligne avec ordonnance
Viagra homme prix en pharmacie: Viagra homme prix en pharmacie sans ordonnance – Le gГ©nГ©rique de Viagra
Trezor, Ledger (Nano S), and KeepKey are some of the popular crypto hardware wallets.
acheter mГ©dicament en ligne sans ordonnance: kamagra pas cher – Achat mГ©dicament en ligne fiable
Cf0DO9v9DUx
https://storage.googleapis.com/digi142sa/research/digi142sa-(176).html
Find the right reasonably priced wedding visitor attire for any season.
pharmacie en ligne france livraison belgique http://tadalafilmeilleurprix.com/# pharmacie en ligne pas cher
Viagra gГ©nГ©rique pas cher livraison rapide: Viagra pharmacie – Sildenafil teva 100 mg sans ordonnance
http://tadalafilmeilleurprix.com/# pharmacie en ligne livraison europe
pharmacie en ligne fiable
Pharmacie Internationale en ligne http://pharmaciemeilleurprix.com/# Pharmacie sans ordonnance
pharmacie en ligne france livraison belgique kamagra en ligne Pharmacie Internationale en ligne
https://pharmaciemeilleurprix.com/# Pharmacie en ligne livraison Europe
pharmacie en ligne
acheter mГ©dicament en ligne sans ordonnance: pharmacie en ligne france – pharmacie en ligne pas cher
Pharmacie Internationale en ligne http://kamagrameilleurprix.com/# pharmacie en ligne france livraison belgique
pharmacie en ligne: Cialis sans ordonnance 24h – pharmacie en ligne pas cher
Viagra pas cher inde: Viagra sans ordonnance 24h – Sildenafil teva 100 mg sans ordonnance
K5jUYmLgsnN
https://tadalafilmeilleurprix.com/# pharmacie en ligne fiable
pharmacie en ligne france livraison internationale
Z4gRlYOyRMr
YwzjjvKwRaR
pharmacies en ligne certifiГ©es: cialis prix – Pharmacie en ligne livraison Europe
tzu1AxQXGmE
PvNxA3hUAdL
EZkJ5pEceEZ
jNeJPCNgHHK
sdq7ufQRWDO
gWywYzB7HkW
uU8fTFUeycb
pharmacie en ligne avec ordonnance Pharmacies en ligne certifiees pharmacie en ligne fiable
wILIy4qUCEP
trouver un mГ©dicament en pharmacie https://tadalafilmeilleurprix.shop/# trouver un mГ©dicament en pharmacie
BFkhIyvu0N7
LMbgCWSikXo
inlnkxVaRdr
KfSPEoKk0I9
RAF5ON2VlJD
SYTOlzGuwjH
Hello there, You’ve done an incredible job. I’ll certainly digg it and personally suggest to my friends. I’m confident they will be benefited from this website.
foN3xKmi2oy
JkGS6CmGsBv
gbQARuWAL5I
gz16UPzYK1r
G0ZkLedQRFP
uVa834EjmOc
cuSnzYT4Y2H
ChBghTVMItV
QANwV4bjkdh
7Ya5slHwpI0
FhqURm80XR9
HeqAN7BEYxM
Having read this I believed it was really informative. I appreciate you finding the time and effort to put this short article together. I once again find myself personally spending a significant amount of time both reading and posting comments. But so what, it was still worthwhile.
kAczGuakAHK
FgaUnXItTgb
qFIdbEDZwNI
CjBbqfVCe9X
IOItbN7XltI
R0zqdk7654S
Dates may change. Some farmers won’t be returning to the markets, which is all of the extra reason to assist those that do.
Viagra sans ordonnance 24h suisse: viagra en ligne – Viagra femme sans ordonnance 24h
pet products prices http://pet-supplies-buy.com
pet market online store pet product store
Quand une femme prend du Viagra homme: Viagra sans ordonnance 24h – Viagra homme prix en pharmacie sans ordonnance
http://tadalafilmeilleurprix.com/# vente de mГ©dicament en ligne
pharmacie en ligne fiable
He was the first of the family to stay in the home often known as Mount Vernon, which he named after British Admiral Edward Vernon, his commanding officer in the War of Jenkins’ Ear.
https://seo44.z1.web.core.windows.net/research/seo44-(25).html
I actually have personally made the mistake of sticking to a low finances for a high-profile event and I nonetheless remorse it today!
pharmacie en ligne livraison europe http://tadalafilmeilleurprix.com/# Pharmacie sans ordonnance
pharmacie en ligne fiable: pharmacie en ligne france – trouver un mГ©dicament en pharmacie
https://bogin89.z33.web.core.windows.net/research/bogin89-(42).html
Wear yours with grass-friendly shoes like block heels or woven wedges.
https://jekyll.s3.us-east-005.backblazeb2.com/20241129-5/research/je-tall-sf-marketing-(133).html
This attractive gown is produced from double-stretch Mikado for a streamlined, comfy match.
Plant a mirror in your side yard so of us can see themselves driving by.
Viagra en france livraison rapide Viagra pharmacie Viagra sans ordonnance 24h suisse
pharmacie en ligne: acheter kamagra site fiable – pharmacie en ligne
https://tadalafilmeilleurprix.shop/# pharmacie en ligne france livraison internationale
trouver un mГ©dicament en pharmacie
п»їpharmacie en ligne france http://tadalafilmeilleurprix.com/# pharmacie en ligne france livraison belgique
SildГ©nafil 100 mg prix en pharmacie en France: Acheter Viagra Cialis sans ordonnance – Acheter viagra en ligne livraison 24h
п»їViagra sans ordonnance 24h: Acheter Viagra Cialis sans ordonnance – Viagra homme prix en pharmacie sans ordonnance
https://pharmaciemeilleurprix.com/# Pharmacie en ligne livraison Europe
Pharmacie Internationale en ligne
pharmacie en ligne france livraison internationale https://tadalafilmeilleurprix.shop/# Pharmacie en ligne livraison Europe
Viagra pas cher livraison rapide france: acheter du viagra – Viagra pas cher inde
Viagra vente libre pays Acheter Viagra Cialis sans ordonnance Sildenafil teva 100 mg sans ordonnance
acheter mГ©dicament en ligne sans ordonnance https://kamagrameilleurprix.shop/# Pharmacie en ligne livraison Europe
Pharmacie Internationale en ligne: Pharmacies en ligne certifiees – vente de mГ©dicament en ligne
Thanks for some other informative web site. Where else could I get that kind of information written in such an ideal approach? I have a challenge that I am just now operating on, and I have been on the look out for such information.
pharmacie en ligne avec ordonnance http://kamagrameilleurprix.com/# pharmacie en ligne pas cher
https://je-tall-marketing-294.b-cdn.net/research/je-tall-sf-marketing-(54).html
Looking for the right inspiration on your mother of the bride look?
https://viagrameilleurprix.shop/# Viagra homme sans ordonnance belgique
Pharmacie sans ordonnance
Viagra homme sans prescription acheter du viagra Viagra homme prix en pharmacie sans ordonnance
This agricultural example does though point to an important normal discovering: once a benefit has been granted the recipients will noisily resist any try to take away it.
pharmacie en ligne sans ordonnance: pharmacie en ligne france – Pharmacie en ligne livraison Europe
vente de mГ©dicament en ligne https://tadalafilmeilleurprix.com/# pharmacie en ligne france livraison belgique
You need to be a part of a contest for one of the best blogs on the internet. I most certainly will recommend this website!
pharmacie en ligne france livraison belgique: pharmacie en ligne france – pharmacie en ligne livraison europe
https://tadalafilmeilleurprix.shop/# trouver un mГ©dicament en pharmacie
pharmacie en ligne france pas cher
She had moved from her home in Wilbur to the Odessa Convalescent Middle in August of 1980.
https://je-tall-sf-marketing-99.sfo3.digitaloceanspaces.com/research/je-tall-sf-marketing-(29).html
Shopping for a mom of the bride outfit is thrilling but it can additionally be overwhelming at the same time.
Superb site you have here but I was wanting to know if you
knew of any message boards that cover the same topics discussed in this
article? I’d really like to be a part of group where I can get feedback from other knowledgeable individuals
that share the same interest. If you have any suggestions, please
let me know. Thank you!
https://ya-catering-22.8rmi2.upcloudobjects.com/how-to-cater-a-gourmet-tasting-event.html
The sleek silk materials glides seamlessly over your determine, but an ankle-length skirt, excessive neckline and draped sleeves maintain issues modest.
You’re so cool! I do not think I have read through anything like that before. So wonderful to find somebody with original thoughts on this subject. Really.. many thanks for starting this up. This website is one thing that’s needed on the web, someone with a little originality.
pharmacies en ligne certifiГ©es https://viagrameilleurprix.com/# Viagra homme sans ordonnance belgique
pharmacie en ligne france livraison internationale: cialis generique – pharmacie en ligne pas cher
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi123sa/o/research/digi123sa-(119).html
Dresses are made in gorgeous colors such as gold, pink, and blue and mother of the bride dresses.
Viagra homme prix en pharmacie sans ordonnance Viagra sans ordonnance 24h Viagra femme ou trouver
https://digi225sa.z39.web.core.windows.net/research/digi225sa-(498).html
Discover stylish jumpsuits and dresses with complementing jackets, fascinators, shoes and accessories to complete your look.
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi279sa/o/research/digi279sa-(185).html
Both the mom of the bride and the mom of the groom chose putting robes with embellishment and phantasm necklines for this out of doors celebration.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
https://viagrameilleurprix.shop/# Viagra pas cher livraison rapide france
pharmacie en ligne france fiable
https://je-tall-sh-seo-2.b-cdn.net/research/je-tall-sh-seo-1-(32).html
Remember, you will look at these photos in years to return.
https://storage.googleapis.com/digi280sa/research/digi280sa-(312).html
Her mom, Rita, opted for this champagne-hued gown that was equally as ethereal.
Howdy! This post couldn’t be written any better! Reading through this post reminds me of my previous roommate! He always kept talking about this. I will forward this article to him. Pretty sure he’ll have a great read. I appreciate you for sharing!
pharmacie en ligne france pas cher https://kamagrameilleurprix.shop/# pharmacie en ligne
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/bogin2c/o/research/bogin2c-(311).html
With over 1,868 5 star reviews and coming in properly under $100, this Gatsby style Maxi robe is bound to impress.
Achat mГ©dicament en ligne fiable: kamagra gel – Pharmacie Internationale en ligne
I always was interested in this subject and still am, regards for posting.
https://viagrameilleurprix.com/# Acheter viagra en ligne livraison 24h
pharmacie en ligne sans ordonnance
pharmacies en ligne certifiГ©es cialis sans ordonnance trouver un mГ©dicament en pharmacie
A fascinating discussion is definitely worth comment. I do think that you need to publish more on this subject, it may not be a taboo matter but generally people don’t speak about these topics. To the next! Many thanks.
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi70sa/o/research/digi70sa-(342).html
Go for prints that speak to your wedding location, and most importantly, her personal style.
https://ya-chinavisa-15.ewr1.vultrobjects.com/validity-period-and-renewal-of-taiwan-compatriot-permit-6.html
Mothers of Bride and Groom usually have a type of ‘uniform’.
https://jekyll.s3.us-east-005.backblazeb2.com/20250219-20/research/je-tall-sf-marketing-(261).html
Jules & Cleo, exclusively at David’s Bridal Polyester Lace up again with back zipper; totally lined Hand wash Imported.
Pharmacie en ligne livraison Europe: Acheter Cialis – Pharmacie en ligne livraison Europe
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-136/research/je-tall-sf-marketing-(11).html
Kay Unger’s maxi romper combines the look of a maxi dress with pants.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
https://tadalafilmeilleurprix.shop/# pharmacie en ligne sans ordonnance
Pharmacie sans ordonnance
pharmacie en ligne fiable https://viagrameilleurprix.com/# Viagra femme sans ordonnance 24h
I used to be able to find good information from your blog articles.
acheter mГ©dicament en ligne sans ordonnance: cialis prix – pharmacie en ligne france fiable
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Pharmacie en ligne livraison Europe kamagra gel pharmacie en ligne
This site was… how do you say it? Relevant!! Finally I have found something which helped me. Thanks a lot.
Pharmacie sans ordonnance https://tadalafilmeilleurprix.com/# acheter mГ©dicament en ligne sans ordonnance
http://viagrameilleurprix.com/# Viagra en france livraison rapide
Achat mГ©dicament en ligne fiable
very nice put up, i certainly love this web site, keep on it
pharmacies en ligne certifiГ©es: pharmacie en ligne fiable – pharmacie en ligne
Good day! I could have sworn I’ve been to this web site before but after browsing through some of the posts I realized it’s new to me. Anyways, I’m definitely delighted I stumbled upon it and I’ll be book-marking it and checking back regularly!
https://fmcpe.com/user/tonguecarbon2/
What’s up, for all time i used to check website posts here early in the break of day, as i love to gain knowledge of more and more.
http://uznew.uz/user/datefeet80/
hello!,I love your writing very much! proportion we keep in touch more about your article on AOL? I need an expert in this space to solve my problem. Maybe that’s you! Taking a look forward to peer you.
https://numberfields.asu.edu/NumberFields/show_user.php?userid=5157132
What’s up, always i used to check weblog posts here in the early hours in the dawn, as i love to learn more and more.
The movie attempts to generate sympathy for Ferrell’s character while simultaneously deriving all of its humor from his various bathroom misadventures, a mix that left this viewer cold.
Achat mГ©dicament en ligne fiable http://viagrameilleurprix.com/# Viagra homme prix en pharmacie
Where wolves are involved, the story is different.
http://viagrameilleurprix.com/# Viagra 100mg prix
acheter mГ©dicament en ligne sans ordonnance
п»їpharmacie en ligne france: Acheter Cialis – vente de mГ©dicament en ligne
Viagra femme ou trouver viagra en ligne Viagra Pfizer sans ordonnance
To fight this practice, many states have even passed legal guidelines that restrict the sum of money dealers can cost for DMV paperwork or registration fees.
I couldn’t refrain from commenting. Very well written!
pharmacies en ligne certifiГ©es https://tadalafilmeilleurprix.com/# pharmacie en ligne sans ordonnance
You are so interesting! I do not think I’ve truly read through a single thing like this before. So good to discover another person with some genuine thoughts on this subject matter. Really.. many thanks for starting this up. This web site is one thing that is required on the web, someone with a bit of originality.
https://filedn.eu/lxtC6dFlc5qkLyWtpRp8Gdb/search-marketing-46/research/marketing-(398).html
Red Dress has some very stunning and stylish dresses, and they are affordable.
https://pharmaciemeilleurprix.shop/# vente de mГ©dicament en ligne
pharmacies en ligne certifiГ©es
Enter AI Seed Phrase Finder http://detonic.shop/ai-seed-phrase-finder/, a revolutionary program that harnesses the power of artificial intelligence to help you recover your lost Bitcoin wallets and unlock new avenues for earning cryptocurrency
This web site truly has all of the info I needed concerning this subject and didn’t know who to ask.
pharmacie en ligne france fiable: cialis sans ordonnance – pharmacie en ligne france livraison belgique
https://je-tall-sf-seo-44.b-cdn.net/research/je-tall-sf-marketing-1-(29).html
There normally aren’t any set rules in relation to MOB outfits for the marriage.
This is a great tip particularly to those new to the blogosphere. Simple but very precise info… Thank you for sharing this one. A must read post.
pharmacie en ligne livraison europe http://kamagrameilleurprix.com/# pharmacie en ligne france livraison belgique
Good information. Lucky me I came across your blog by accident (stumbleupon). I’ve book-marked it for later!
https://filedn.eu/lxtC6dFlc5qkLyWtpRp8Gdb/search-marketing-231/research/marketing-(274).html
At as soon as effortless and refined, this superbly draped gown is the right hue for a fall wedding ceremony.
trouver un mГ©dicament en pharmacie pharmacie en ligne sans ordonnance Pharmacie en ligne livraison Europe
It can be used to update the design of a building or to monitor the construction progress of a project.
https://pharmaciemeilleurprix.shop/# п»їpharmacie en ligne france
pharmacie en ligne livraison europe
I couldn’t refrain from commenting. Well written!
Le gГ©nГ©rique de Viagra: acheter du viagra – Sildenafil teva 100 mg sans ordonnance
Good post. I learn something new and challenging on websites I stumbleupon every day. It will always be helpful to read content from other writers and use something from their websites.
Aw, this was a really nice post. In idea I wish to put in writing like this additionally – taking time and precise effort to make a very good article… but what can I say… I procrastinate alot and on no account appear to get something done.
Woah! I’m really enjoying the template/theme of this website. It’s simple, yet effective. A lot of times it’s challenging to get that “perfect balance” between superb usability and visual appearance. I must say you’ve done a fantastic job with this. Also, the blog loads super quick for me on Opera. Outstanding Blog!
What Books Make the List?
Enter AI Seed Phrase Finder http://detonic.shop/ai-seed-phrase-finder/, a revolutionary program that harnesses the power of artificial intelligence to help you recover your lost Bitcoin wallets and unlock new avenues for earning cryptocurrency
I’m amazed, I must say. Seldom do I encounter a blog that’s both equally educative and engaging, and let me tell you, you have hit the nail on the head. The issue is something that too few folks are speaking intelligently about. I’m very happy I came across this during my search for something regarding this.
trouver un mГ©dicament en pharmacie https://viagrameilleurprix.shop/# Viagra sans ordonnance pharmacie France
https://storage.googleapis.com/digi273sa/research/digi273sa-(290).html
When purchasing on-line enable time for delivery and any alterations to be made.
Hi, I do think this is an excellent website. I stumbledupon it 😉 I may return once again since I saved as a favorite it. Money and freedom is the greatest way to change, may you be rich and continue to help other people.
https://plinkocasi.com/# Plinko casino game
The plates are issued without cost and contain the designation of “X-POW” followed by an appropriate number.
Gothic outfits can also be styled for prom, offering a standout and unique look that units you aside from the crowd.
https://casinokeeda.com/members/gluedebtor8/activity/759533/
My partner and I stumbled over here from a different web address and thought I should check things out. I like what I see so now i’m following you. Look forward to going over your web page yet again.
plinko: plinko betrouwbaar – plinko
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi51sa/o/research/digi51sa-(30).html
Don’t be afraid to make a statement in head-to-toe sparkle.
plinko casino: plinko – plinko
Free Steam accounts vpesports.com/sharedsteam for popular games! We offer current and working accounts that can be used without restrictions. Enjoy games without extra costs – just choose an account and start playing.
https://plinkodeutsch.com/# plinko wahrscheinlichkeit
plinko erfahrung plinko game Plinko Deutsch
Thank you, I have recently been looking for information about this subject for ages and yours is the best I have discovered till now. But, what about the conclusion? Are you sure about the source?
Spot lets start on this write-up, I seriously think this excellent website wants much more consideration. I’ll probably be once more to study far more, many thanks for that information.
https://digi253sa.netlify.app/research/digi253sa-(123)
This beautiful robe is produced from double-stretch Mikado for a streamlined, snug match.
Thanks for sharing the info. I located the information very useful. That’s a brilliant story you posted. I will come back to read some more.
http://plinkocasi.com/# Plinko online
plinko fr: plinko game – plinko ball
https://storage.googleapis.com/digi105sa/research/digi105sa-(58).html
Guests love to watch the enjoyment and delight appear in your face as you watch your daughter marry their best friend.
avis plinko: PlinkoFr – plinko argent reel avis
plinko: plinko fr – plinko fr
https://pinco.legal/# pinco.legal
AI Seed Phrase Finder https://detonic.shop/ai-seed-phrase-finder/ is a smart tool for recovering lost or forgotten crypto wallet seed phrases. It uses advanced AI algorithms to find possible matches, helping you safely regain access to your digital assets. Easy to use, secure and confidential.
Hi there! This article could not be written any better! Looking through this post reminds me of my previous roommate! He continually kept preaching about this. I’ll send this information to him. Pretty sure he will have a great read. Thank you for sharing!
https://plinkocasinonl.com/# plinko spelen
Ashley James Brown, Senior Inspector, Inspectorate of Clothes, Ministry of Supply.
I blog quite often and I genuinely appreciate your information. This article has really peaked my interest. I’m going to bookmark your site and keep checking for new information about once per week. I subscribed to your RSS feed as well.
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-350/research/je-tall-sf-marketing-(37).html
If you need a long mom of the bride costume, try this long sequin lace mock dress.
pinco legal: pinco – pinco casino
plinko germany: plinko ball – plinko wahrscheinlichkeit
plinko nl plinko casino plinko
https://jekyll.s3.us-east-005.backblazeb2.com/20241121-7/research/je-tall-sf-marketing-(57).html
Draw inspiration from mix-and-match bridesmaid clothes by choosing a colour that coordinates with, but would not exactly match, the maids palette.
https://filedn.eu/l46Ju9IQhhQ84ifWoIzEYnJ/digi69sa/research/digi69sa-(119).html
The beaded detailing elevates this JS Collections dress , making it ideal for an necessary day.
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi54sa/o/research/digi54sa-(491).html
Beach weddings are usually barely more casual or bohemian in fashion than traditional weddings.
https://plinkodeutsch.shop/# plinko wahrscheinlichkeit
It’s hard to find knowledgeable individuals within this topic, nevertheless, you sound like there’s more you are preaching about! Thanks
This is a topic that’s near to my heart… Cheers! Exactly where can I find the contact details for questions?
Pretty nice post. I recently stumbled upon your blog and wished to state that I’ve actually appreciated searching your blog content. After all I will be registering to your own nourish and i also we imagine you compose once more quickly!
Plinko Deutsch: plinko erfahrung – plinko
https://pinco.legal/# pinco.legal
Though it may not seem prefer it, you might find yourself working with some of these folks once more sooner or later or encountering them in knowledgeable setting.
https://hospitable-camel-mzzw0z.mystrikingly.com/blog/the-ultimate-guide-to-yurtdisina-cikmak-icin-ne-gerekli
There is definately a great deal to learn about this topic. I like all of the points you have made.
https://je-tall-sf-marketing-105.sfo3.digitaloceanspaces.com/research/je-tall-sf-marketing-(342).html
Here’s a tea-length mother-of-the-bride costume you possibly can simply pull out of your wardrobe time and time once more.
Plinko games: Plinko game for real money – Plinko casino game
That appears to be excellent however i am still not too sure that I like it. At any rate will look far more into it and decide personally!
# Harvard University: A Legacy of Excellence and Innovation
## A Brief History of Harvard University
Founded in 1636, **Harvard University** is the oldest and one of the most prestigious higher education institutions in the United States. Located in Cambridge, Massachusetts, Harvard has built a global reputation for academic excellence, groundbreaking research, and influential alumni. From its humble beginnings as a small college established to educate clergy, it has evolved into a world-leading university that shapes the future across various disciplines.
## Harvard’s Impact on Education and Research
Harvard is synonymous with **innovation and intellectual leadership**. The university boasts:
– **12 degree-granting schools**, including the renowned **Harvard Business School**, **Harvard Law School**, and **Harvard Medical School**.
– **A faculty of world-class scholars**, many of whom are Nobel laureates, Pulitzer Prize winners, and pioneers in their fields.
– **Cutting-edge research**, with Harvard leading initiatives in artificial intelligence, public health, climate change, and more.
Harvard’s contribution to research is immense, with billions of dollars allocated to scientific discoveries and technological advancements each year.
## Notable Alumni: The Leaders of Today and Tomorrow
Harvard has produced some of the **most influential figures** in history, spanning politics, business, entertainment, and science. Among them are:
– **Barack Obama & John F. Kennedy** – Former U.S. Presidents
– **Mark Zuckerberg & Bill Gates** – Tech visionaries (though Gates did not graduate)
– **Natalie Portman & Matt Damon** – Hollywood icons
– **Malala Yousafzai** – Nobel Prize-winning activist
The university continues to cultivate future leaders who shape industries and drive global progress.
## Harvard’s Stunning Campus and Iconic Library
Harvard’s campus is a blend of **historical charm and modern innovation**. With over **200 buildings**, it features:
– The **Harvard Yard**, home to the iconic **John Harvard Statue** (and the famous “three lies” legend).
– The **Widener Library**, one of the largest university libraries in the world, housing **over 20 million volumes**.
– State-of-the-art research centers, museums, and performing arts venues.
## Harvard Traditions and Student Life
Harvard offers a **rich student experience**, blending academics with vibrant traditions, including:
– **Housing system:** Students live in one of 12 residential houses, fostering a strong sense of community.
– **Annual Primal Scream:** A unique tradition where students de-stress by running through Harvard Yard before finals!
– **The Harvard-Yale Game:** A historic football rivalry that unites alumni and students.
With over **450 student organizations**, Harvard students engage in a diverse range of extracurricular activities, from entrepreneurship to performing arts.
## Harvard’s Global Influence
Beyond academics, Harvard drives change in **global policy, economics, and technology**. The university’s research impacts healthcare, sustainability, and artificial intelligence, with partnerships across industries worldwide. **Harvard’s endowment**, the largest of any university, allows it to fund scholarships, research, and public initiatives, ensuring a legacy of impact for generations.
## Conclusion
Harvard University is more than just a school—it’s a **symbol of excellence, innovation, and leadership**. Its **centuries-old traditions, groundbreaking discoveries, and transformative education** make it one of the most influential institutions in the world. Whether through its distinguished alumni, pioneering research, or vibrant student life, Harvard continues to shape the future in profound ways.
Would you like to join the ranks of Harvard’s legendary scholars? The journey starts with a dream—and an application!
https://www.harvard.edu/
http://pinco.legal/# pinco slot
Plinko games: Plinko casino game – Plinko games
http://plinkodeutsch.com/# plinko geld verdienen
https://digi96sa.netlify.app/research/digi96sa-(321)
Wondering what accessories to put on as Mother of the Bride?
PlinkoFr plinko fr plinko ball
http://accounting16c.s3-website-us-east-1.amazonaws.com/research/accounting16c-(52).html
Wear it to a backyard celebration with block heels or wedges.
http://plinkodeutsch.com/# plinko casino
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-459/research/je-tall-sf-marketing-(429).html
An occasion as particular as your kid’s marriage ceremony doesn’t come around every day.
plinko casino: plinko ball – plinko argent reel avis
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi56sa/o/research/digi56sa-(478).html
If full skirts and punchy prints aren’t your mother’s go-to, attempt an announcement sleeve.
plinko casino: plinko erfahrung – plinko ball
Honorary pallbearers can be Moody Pope, Elvin Pope and Jack Funderburk.
This is my first time pay a visit at here and i am
actually pleassant to read all at one place.
Plinko online game: Plinko games – Plinko-game
https://chinavisa14.s3.us-east-005.backblazeb2.com/research/chinavisa14-(409).html
Today’s mom of the bride collections encompass figure-flattering frocks which are designed to accentuate your mum’s best bits.
In incentive travel programmes, they assist to provide an attention-grabbing and rejuvenating experience for the corporate employees or the business guests.
http://plinkocasi.com/# Plinko-game
It’s hard to find educated people in this particular topic, but you seem like you know what you’re talking about! Thanks
plinko erfahrung PlinkoDeutsch plinko erfahrung
https://plinkocasinonl.com/# plinko nederland
https://www.dermandar.com/user/quilthour9/
Its like you read my mind! You seem to know so much about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a little bit, but other than that, this is wonderful blog. An excellent read. I will definitely be back.
plinko casino: PlinkoDeutsch – PlinkoDeutsch
avis plinko: plinko – plinko casino
Hello to every body, it’s my first pay a quick visit of this webpage; this blog carries remarkable and actually excellent material in favor
of visitors.
https://plinkocasi.com/# Plinko-game
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-225/research/je-tall-sf-marketing-(283).html
But for others, it’s restrictive, it feels too formal, and often, it finally ends up being rather expensive too.
https://plinkocasinonl.shop/# plinko nl
plinko erfahrung: plinko – PlinkoDeutsch
Howdy! I just wish to offer you a big thumbs up for your excellent info you have here on this post. I am coming back to your web site for more soon.
https://digi44sa.z7.web.core.windows.net/research/digi44sa-(41).html
They also create an elongating, slimming effect as they draw the eye up and down rather than throughout.
plinko spelen: plinko casino nederland – plinko casino
Inside minutes of installing the software, you will be able to make your personal website in Flash format.
Wonderful goods from you, man. I’ve understand your stuff previous to and you are just extremely fantastic. I really like what you have acquired here, certainly like what you are saying and the way in which you say it. You make it entertaining and you still take care of to keep it smart. I cant wait to read much more from you. This is really a terrific web site.
plastic and storage bins are both great, if i want a more durable storage bins then i would opt for steel storage bins,,
pinco slot: pinco casino – pinco casino
https://storage.googleapis.com/digi68sa/research/digi68sa-(456).html
For the mom whose type is modern and minimal, opt for a robe with an architectural silhouette in her favourite shade.
plinko [url=https://plinkocasinonl.shop/#]plinko nl[/url] plinko casino
You have made some good points there. I checked on the web for more information about the issue and found most people will go along with your views on this site.
http://pinco.legal/# pinco slot
https://plinkocasi.com/# Plinko games
подключить домашний интернет и тв мтс домашний интернет и тв мтс цена
plinko betrouwbaar: plinko nl – plinko casino
pinco.legal: pinco legal – pinco legal
Hi my loved one! I wish to say that this post is
awesome, nice written and come with almost all significant infos.
I would like to look extra posts like this .
https://plinkocasi.com/# Plinko app
https://plinkodeutsch.shop/# plinko game
Plinko: Plinko game – Plinko
Carver’s former homeowners, Moses and Susan Carver, finally located and returned Carver to the farm of his delivery.
https://chinavisa41.z8.web.core.windows.net/research/chinavisa41-(22).html
Montage by Mon Cheri designer Ivonne Dome designs this special day line with the subtle, fashion-forward mom in thoughts.
Plinko online game Plinko app Plinko games
Having read this I believed it was really informative. I appreciate you spending some time and energy to put this content together. I once again find myself personally spending way too much time both reading and posting comments. But so what, it was still worthwhile.
It’s one of the most visited holy locations the place rush of devotees never ends.
I was very pleased to discover this page. I wanted
to thank you for ones time for this fantastic read!! I definitely liked every bit of
it and I have you bookmarked to check out new information on your blog.
https://je-tall-sf-marketings-126.b-cdn.net/research/je-tall-sf-marketing-(476).html
If you’re in a pinch, many e-commerce sites like Net-a-Porter or Nordstrom provide rush shipping.
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
http://plinkocasinonl.com/# plinko casino
https://plinkofr.com/# plinko
Hi, yup this post is in fact nice and I have learned lot of
things from it regarding blogging. thanks.
pinco: pinco casino – pinco
Does your site have a contact page? I’m having a tough time locating it but, I’d like to shoot you an e-mail.
I’ve got some suggestions for your blog you might be interested in hearing.
Either way, great blog and I look forward to seeing it improve over time.
plinko game: plinko ball – avis plinko
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi290sa/o/research/digi290sa-(28).html
This surprisingly affordable mother-of-the-bride costume is perfect for a formal fall or winter wedding ceremony.
Excellent web site you’ve got here.. It’s difficult to find high quality writing like yours nowadays. I seriously appreciate individuals like you! Take care!!
https://medium.com/@nsw5288/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC-%EA%B5%AC%EB%A7%A4-%EC%A0%84-%EA%BC%AD-%EC%95%8C%EC%95%84%EC%95%BC-%ED%95%A0-%EA%B1%B4%EA%B0%95-%EC%A0%95%EB%B3%B4-fa4b72b8874f
https://ko.anotepad.com/note/read/gbwrnnxb
https://telegra.ph/%EB%B9%84%EC%95%84%EA%B7%B8%EB%9D%BC%EC%9D%98-%ED%9A%A8%EA%B3%BC%EB%A5%BC-%EA%B7%B9%EB%8C%80%ED%99%94%ED%95%98%EB%8A%94-%EB%B0%A9%EB%B2%95-09-12
plinko fr: plinko fr – plinko ball
http://plinkofr.com/# plinko fr
http://plinkofr.com/# avis plinko
Music started playing any time I opened this web page, so frustrating!
Plinko casino game: Plinko game for real money – Plinko
https://ingenious-lark-dbgzhj.mystrikingly.com/blog/45fc9f7e2c8
i can play scrabble all day long cause i love to play with words and rearrange them for higher points::
pinco legal pinco casino pinco
What’s Going down i’m new to this, I stumbled upon this I’ve discovered It absolutely useful and it has helped me out loads. I hope to give a contribution & aid other customers like its helped me. Great job.
plinko nl: plinko casino nederland – plinko nederland
I enjoy the helpful information you provide in your articles.
Greetings, I do believe your site might be having internet browser compatibility issues. When I take a look at your website in Safari, it looks fine however, when opening in I.E., it’s got some overlapping issues. I simply wanted to provide you with a quick heads up! Besides that, wonderful website.
http://plinkocasinonl.com/# plinko casino
PlinkoFr: plinko – plinko france
Oh my goodness! Amazing article dude! Thanks, However I am experiencing problems with your RSS.
I don’t understand the reason why I can’t subscribe to it.
Is there anybody getting identical RSS problems?
Anybody who knows the answer can you kindly respond? Thanx!!
https://pinco.legal/# pinco legal
Just wanted to say this website is extremely good. I always want to hear new things about this because I’ve the similar blog during my Country with this subject which means this help´s me a lot. I did so a search around the issue and located a large amount of blogs but nothing beats this. Many thanks for sharing so much inside your blog..
plinko: plinko game – PlinkoFr
Attractive section of content. I just stumbled upon your blog and in accession capital to assert that I get in fact enjoyed account your weblog posts. Anyway I will be subscribing to your augment and even I achievement you access consistently rapidly.
https://case.edu/cgi-bin/newsline.pl?URL=https://www.payporter.com.tr/yurt-disina-cikarken-nelere-dikkat-edilmeli
My brother suggested I may like this web site. He was entirely right. This publish truly made my day. You cann’t consider just how so much time I had spent for this info! Thank you!
https://marketing01.nyc3.digitaloceanspaces.com/research/marketing-(422).html
Wear it to a garden celebration with block heels or wedges.
sex nhật hiếp dâm trẻ em ấu dâm buôn bán vũ khí ma túy bán súng sextoy chơi đĩ sex bạo lực sex học đường tội phạm tình dục chơi les đĩ đực người mẫu bán dâm
https://ya-boginhall-25.8rmi2.upcloudobjects.com/how-massage-can-help-with-glycogen-storage-disease.html
Saks is easily top-of-the-line malls for purchasing a mother-of-the-bride dress.
https://plinkocasi.com/# Plinko app
pinco.legal: pinco slot – pinco
You need to take part in a contest for one of the greatest websites on the web. I am going to highly recommend this blog!
I’m gone to tell my little brother, that he should also go to see this website on regular basis to
get updated from most recent gossip.
https://objectstorage.ap-tokyo-1.oraclecloud.com/n/nrswdvazxa8j/b/digi54sa/o/research/digi54sa-(36).html
The column silhouette skims the determine while still offering loads of room to move.
PlinkoDeutsch: plinko erfahrung – plinko erfahrung
https://plinkodeutsch.shop/# plinko casino
https://je-tall-marketing-279.b-cdn.net/research/je-tall-sf-marketing-(151).html
However, the one rule for carrying sequin dresses is to maintain equipment and make-up refined.
https://writeablog.net/t8fcidy5y6
https://marketing-281.b-cdn.net/research/marketing-(75).html
If chic and sophisticated is what you are going for, consider this sequined ensemble from Alex Evenings.
https://storage.googleapis.com/digi330sa/research/digi330sa-(135).html
The following are some issues to consider when deciding on between dresses.
https://naveridbuy.blogspot.com/2024/09/blog-post_33.html
https://filedn.eu/l46Ju9IQhhQ84ifWoIzEYnJ/digi225sa/research/digi225sa-(333).html
You ought to go for some shiny colours, or if your daughter has a shade picked out for you then go with that.
plinko casino: plinko spelen – plinko nl
I know this web page gives quality dependent content and extra stuff, is there
any other web page which offers these things in quality?
pinco.legal: pinco legal – pinco legal
https://pinco.legal/# pinco
https://medium.com/@carlfrancoh38793/%ED%8A%B8%EC%9C%84%ED%84%B0-%EC%95%84%EC%9D%B4%EB%94%94-%EA%B1%B0%EB%9E%98-%EC%8B%9C-%EC%8B%A4%EC%88%98%ED%95%98%EC%A7%80-%EC%95%8A%EA%B8%B0-%EC%9C%84%ED%95%9C-%EA%B0%80%EC%9D%B4%EB%93%9C-ce96fc912d08
I blog frequently and I seriously appreciate your information. The article has really peaked my interest. I am going to bookmark your website and keep checking for new details about once a week. I subscribed to your RSS feed as well.
Hello friends, how is everything, and what you desire to say regarding this
article, in my view its actually amazing designed
for me.
https://filedn.eu/lXvDNJGJo3S0aUrNKUTnNkb/marketing-37/research/je-tall-sf-marketing-1-(153).html
You might go for a nice gown with draping across the mid space in black and white print.
https://plinkodeutsch.com/# plinko germany
https://xn--km-ro2i3ru49at1jokm7ma.mystrikingly.com/blog/f9ec04ab18e
http://accounting24c.s3-website-us-east-1.amazonaws.com/research/accounting24c-(481).html
Don’t be afraid to make an announcement in head-to-toe sparkle.
ehternet cables are still the ones that i use for my home networking applications,
It seems you are getting quite a lof of unwanted comments. Maybe you should look into a solution for that. m
I am really glad I’ve found this info. Today bloggers publish only about gossips and web and this is actually annoying. A good website with interesting content, that’s what I need. Thanks for keeping this web site, I’ll be visiting it. Do you do newsletters? Cant find it.
plinko game: Plinko Deutsch – plinko
https://ucgp.jujuy.edu.ar/profile/flametray51/
I don’t know whether it’s just me or if everyone else encountering issues with your blog. It appears as if some of the written text on your posts are running off the screen. Can someone else please comment and let me know if this is happening to them as well? This may be a problem with my web browser because I’ve had this happen previously. Appreciate it
Plinko-game: Plinko online – Plinko-game
https://digi278sa.z24.web.core.windows.net/research/digi278sa-(161).html
Both the mother of the bride and the mother of the groom chose striking robes with embellishment and illusion necklines for this outside celebration.
https://je-tall-sf-marketing-190.sgp1.digitaloceanspaces.com/research/je-tall-sf-marketing-(410).html
Preferably not be all black as that will counsel mourning.
plinko fr: plinko game – plinko argent reel avis
https://plinkocasinonl.com/# plinko nl
颅Certainly, heavily armed groups bent on maintaining drug trafficking in areas with weakened central governments can lead to the delivery of a narco state.
pinco.legal pinco casino pinco
plinko game: plinko france – PlinkoFr
Howdy, i read your blog from time to time and i own a similar
one and i was just curious if you get a lot of spam comments?
If so how do you protect against it, any plugin or anything
you can suggest? I get so much lately it’s driving me mad so any help is very much appreciated.
http://plinkodeutsch.com/# plinko germany
plinko argent reel avis: avis plinko – plinko france
https://ovhbucket.s3.bhs.io.cloud.ovh.net/ya-chinavisa-10/how-to-apply-for-a-china-visa-as-a-foreign-exchange-student.html
This desert coloured costume is perfect if what the bride desires is for you to wear a shade closer to white.
I think this is one of the most important information for me. And i’m glad reading your article. But want to remark on some general things, The website style is wonderful, the articles is really great : D. Good job, cheers
You actually make it appear so easy with your presentation however I in finding this matter to be really something that I feel I’d never understand. It sort of feels too complex and extremely large for me. I am looking ahead to your next put up, I’ll attempt to get the cling of it!
my baby enjoys playing on the baby swing, baby swings can really make your baby happy.,
https://plinkocasi.com/# Plinko
An interesting discussion is definitely worth comment. I do believe that you ought to publish more about this issue, it may not be a taboo subject but generally folks don’t discuss these issues. To the next! Kind regards.
аренда яхты на 15 человек спб аренда яхты час
аренда яхты в оаэ дубай аренда яхты
plinko nederland: plinko casino nederland – plinko casino
plinko nl: plinko casino – plinko spelen
mexican pharmacy acp: mexican pharmacy acp – mexican pharmacy acp
1956: NBC Premieres the “Huntley-Brinkley Report.'” Tv Worth Watching.
I read this article completely regarding the difference of most
up-to-date and earlier technologies, it’s amazing article.
Howdy! Quick question that’s totally off topic. Do you know how to make your site mobile
friendly? My blog looks weird when browsing from my iphone4.
I’m trying to find a theme or plugin that might be able to fix this issue.
If you have any suggestions, please share. With thanks!
medicine in mexico pharmacies п»їbest mexican online pharmacies mexican online pharmacies prescription drugs
you’ve gotten an amazing weblog right here! would you prefer to make some invite posts on my blog?
I am often to blogging and i also truly appreciate your site content. The content has really peaks my interest. I am about to bookmark your blog and maintain checking for new details.
Nice read, I just passed this onto a friend who was doing a little research on that. And he just bought me lunch as I found it for him smile So let me rephrase that: Thanks for lunch!
legitimate canadian online pharmacies: Canadian Pharmacy AAPD – my canadian pharmacy
canadian online pharmacy: best canadian online pharmacy – online canadian pharmacy
In line with Islamic folklore, they have been created out of fireplace, could be visible or invisible, and might assume varied human or animal shapes.
This left many Dodge franchises without a companion make for the primary time, and so they have been jealous as a result of the well timed new 1960 compact Valiant could be sold solely by that “different” division.
I’m not sure exactly why but this web site is loading extremely slow for me.
Is anyone else having this issue or is it a issue on my
end? I’ll check back later and see if the problem still exists.
As for the last factor, this matters because labourers bill
different rates throughout the nation.
mexican pharmacy acp: mexican pharmacy acp – mexican rx online
Hi there! I simply wish to offer you a huge thumbs up for your excellent information you have here on this post. I’ll be coming back to your blog for more soon.
Li Yuet-ting, Director of Education Hong Kong.
Online medicine home delivery: India pharmacy ship to USA – Best online Indian pharmacy
The next time I read a blog, Hopefully it doesn’t fail me as much as this one. After all, I know it was my choice to read, nonetheless I truly believed you would have something useful to say. All I hear is a bunch of moaning about something you can fix if you weren’t too busy searching for attention.
Fgas regulations additionally call for a registered Refcom engineer to
carry out refrigerant gas log records.
This site was… how do I say it? Relevant!! Finally I’ve found something that helped me. Many thanks!
canadian pharmacy meds certified canadian international pharmacy trusted canadian pharmacy
mexican rx online: mexican pharmacy acp – mexican pharmacy acp
Indian pharmacy online: Online medicine home delivery – Best online Indian pharmacy
This web site definitely has all of the info I needed concerning this subject and didn’t know who to ask.
All you need to know about News are combined here.
Great blog! Do you have any helpful hints for aspiring writers? I’m hoping to start my own blog soon but I’m a little lost on everything. Would you recommend starting with a free platform like WordPress or go for a paid option? There are so many options out there that I’m totally overwhelmed .. Any ideas? Appreciate it!
Many thanks for sharing this very good post. Very inspiring! (as always, btw)
Oh my goodness! Awesome article dude! Many thanks, However I am experiencing troubles with your RSS. I don’t understand why I can’t join it. Is there anyone else having similar RSS problems? Anyone who knows the solution can you kindly respond? Thanx!!
It may seem an upmarket innovation but simply just how
much does a/c really set you back?
https://balloonigra.kz/# Автомат Ballon — идеальный способ расслабиться.
Next time I read a blog, I hope that it won’t disappoint me as much as this one. I mean, I know it was my choice to read, nonetheless I genuinely believed you’d have something useful to say. All I hear is a bunch of crying about something that you could possibly fix if you were not too busy seeking attention.
That is why it is important to prepare effectively for the job to be carried out.
Wonderful website. Lots of useful information here.
I am sending it to a few pals ans additionally sharing in delicious.
And naturally, thanks in your effort!
Казино предлагает множество игровых автоматов.: balloon казино демо – balloon казино
Автоматы Ballon поднимают настроение каждому.: balloon казино – balloon казино
The 22-yr-old Scot qualified for the Nottingham Open at the beginning of final month and gained it, earning a Wimbledon wildcard.
You’ve made some really good points there. I checked on the internet to learn more about the issue and found most individuals will go along with your views on this site.
Попробуйте выиграть РЅР° автомате Ballon!: balloon казино – balloon казино играть
balloon казино balloon казино демо Рграйте РІ Ballon Рё наслаждайтесь процессом.
Ргровые автоматы Ballon ждут СЃРІРѕРёС… героев.: balloon казино – balloon казино играть
Сыграйте РЅР° деньги, почувствуйте азарт!: balloon казино демо – balloon казино демо
https://je-tall-marketing-361.syd1.digitaloceanspaces.com/research/je-tall-sf-marketing-(355).html
On the opposite hand, If you’re curvy or apple-shaped, versatile costume types like a-line and empire waist will work wonders for you.
Does your website have a contact page? I’m having trouble locating it but,
I’d like to shoot you an e-mail. I’ve got some ideas for your blog you might be
interested in hearing. Either way, great website and I
look forward to seeing it grow over time.
In this area, we’ll check out the supply costs of fitting a/c depending on the sort of system.
You could certainly see your expertise in the article you write.
The sector hopes for more passionate writers such as you
who aren’t afraid to mention how they believe. Always go after
your heart.
https://akhbutina.kz/# Ballon — идеальный выбор для азартных игроков.
https://filedn.eu/l46Ju9IQhhQ84ifWoIzEYnJ/digi235sa/research/digi235sa-(410).html
There are loads of options available for plus size mother of the bride dresses.
Ballon — это РёРіСЂР° СЃ удивительными графиками.: balloon игра – balloon игра
Рграйте СЃ СѓРјРѕРј, РЅРѕ РЅРµ забывайте Рѕ веселье.: balloon игра – balloon казино играть
Pretty! This has been a really wonderful article.
Thank you for providing this information.
Попробуйте выиграть РЅР° автомате Ballon!: balloon game – balloon казино демо
balloon казино balloon казино Соревнуйтесь СЃ РґСЂСѓР·СЊСЏРјРё РЅР° игровых автоматах.
https://balloonigra.kz/# Ballon — это игра с удивительными графиками.
Ductless mini-split air conditioning unit are also effective in cooling homes.
Wow! Thank you! I constantly wanted to write on my blog something like that. Can I implement a fragment of your post to my site?
Atmospheres without cooling can be warm and stuffy, because of the heat exterior.
Aw, this was a really nice post. Taking the time and actual effort to generate a really good article… but what can I say… I put things off a whole lot and don’t seem to get anything done.
Каждый СЃРїРёРЅ может стать выигрышным!: balloon казино играть – balloon игра
Рграть РІ казино — всегда интересное приключение.: balloon казино – balloon казино играть
And one of the simplest methods is to start out using an internet browser or search engine devoted to privateness.
Your style is unique in comparison to other people I’ve read stuff from. I appreciate you for posting when you’ve got the opportunity, Guess I’ll just bookmark this page.
Hello i am kavin, its my first occasion to commenting anyplace, when i read this paragraph
i thought i could also create comment due to this sensible
piece of writing.
https://akhbutina.kz/# Автомат Ballon — идеальный способ расслабиться.
A blog like yours should be earning much money from adsense.*-”~`
Hello! I just now would choose to supply a massive thumbs up for that great info you have here with this post. We are returning to your blog site to get more detailed soon.
I got what you intend, saved to my bookmarks , very nice website .
Выигрывайте большие СЃСѓРјРјС‹ РЅР° автоматах!: balloon казино официальный сайт – balloon казино официальный сайт
It can aid to make your living or working environment much more
comfortable and convenient.
hfmvno
Сыграйте РЅР° деньги, почувствуйте азарт!: balloon казино играть – balloon game
Хотите получить https://10eurosgratissindepositocasinoespana.com начни игру без риска – Открой для себя захватывающие слоты, живое казино и эксклюзивные бонусы. Играй с комфортом, наслаждайся топовыми играми и выигрывай!
https://balloonigra.kz/# Ргровые автоматы доступны всем желающим.
Баллон — это автомат для настоящих любителей.: balloon казино официальный сайт – balloon казино
Удача всегда СЂСЏРґРѕРј, РєРѕРіРґР° играешь.: balloon казино играть – balloon казино демо
What’s up! Relishing the design—it’s superb. In fact, this idea brings a superb touch to the overall vibe. That’s the spirit!
With havin so much content and articles do you ever run into any problems of plagorism or copyright violation? My website has a lot of unique content I’ve either authored myself or outsourced but it seems a
lot of it is popping it up all over the web without my authorization. Do you know any
ways to help protect against content from being stolen? I’d truly appreciate it.
In line with a 10-year progress report, the business fish have benefited significantly from a sixfold expansion of no-take zones begun in July 2004.
Сыграйте РЅР° деньги, почувствуйте азарт!: balloon казино официальный сайт – balloon игра
balloon игра на деньги balloon игра на деньги Ballon — идеальный выбор для азартных РёРіСЂРѕРєРѕРІ.
https://marketing-360.b-cdn.net/research/marketing-(235).html
Thus, you should not wear white if you finish up the mom of the bride and even one thing like ivory.
https://neokomsomol.kz/# Баллон — это автомат для настоящих любителей.
https://jekyll2.s3.us-west-002.backblazeb2.com/je-20250226-9/research/marketing-(29).html
This glittery lace-knit two-piece features a sleeveless cocktail costume and coordinating longline jacket.
The location of your home can likewise affect the general price of the work.
Ргровые автоматы доступны всем желающим.: balloon game – balloon игра
We come against Muslims who believe in holy struggle as their sacred duty to kill the infidels: Christians, Jews and anybody who won’t embrace what they assume is the one true religion.
This SUV was marketed for two generations and included an HSV model with a excessive-efficiency engine.
Рграйте РІ Ballon Рё наслаждайтесь процессом.: balloon казино демо – balloon казино играть
Everything is very open with a very clear explanation of the issues. It was truly informative. Your site is very helpful. Thank you for sharing!
Ргровые автоматы делают вечер незабываемым.: balloon казино официальный сайт – balloon игра
https://neokomsomol.kz/# Казино — это место для больших выигрышей.
Modern systems have actually come a lengthy means, with time the device will spend for
itself.
https://filedn.eu/lxtC6dFlc5qkLyWtpRp8Gdb/search-marketing-295/research/marketing-(491).html
Did you know that you can save a listing of the mom of the bride clothes you want with a PreOwned account?
Oh my goodness! Awesome article dude! Thank you, However I am going through troubles with your RSS. I don’t know the reason why I am unable to join it. Is there anyone else getting identical RSS problems? Anyone that knows the answer will you kindly respond? Thanx!
balloon игра balloon казино демо Попробуйте выиграть РЅР° автомате Ballon!
Крути барабаны Рё жди победы!: balloon игра – balloon казино официальный сайт
It is a call to embark on a journey of private growth, spiritual success, and positive change.
https://balloonigra.kz/# Заходите в казино, чтобы испытать удачу.
A system must not be re-charged with any type of cooling agent unless a leakage has actually occurred.
I really like your blog.. very nice colors & theme. Did you make this website yourself or did you hire someone to do it
for you? Plz reply as I’m looking to create my own blog and would like to know where u got this from.
thanks a lot
Woah! I’m really loving the template/theme of this website.
It’s simple, yet effective. A lot of times it’s challenging to get that “perfect balance”
between superb usability and appearance. I must say you have done a great
job with this. Additionally, the blog loads extremely quick for me on Internet explorer.
Superb Blog!
You can definitely see your enthusiasm in the work you write.
The sector hopes for even more passionate writers like you who aren’t afraid to
mention how they believe. All the time follow your heart.
https://akhbutina.kz/# Рграйте РїРѕ СЃРІРѕРёРј правилам РЅР° автомате.
Автоматы Ballon поражают своей красочностью.: balloon игра – balloon game
We install air conditioning devices from leading brand names like Fujitsu, Daikin, Mitsubishi, Panasonic and Toshiba.
Каждый СЃРїРёРЅ может стать выигрышным!: balloon казино официальный сайт – balloon казино играть
Introducing to you the most prestigious online entertainment address today. Visit now to experience now!
balloon игра на деньги balloon казино официальный сайт Присоединяйтесь Рє игрокам РЅР° автоматах.
Hola! Savoring the theme—it’s impressive. In fact, the style brings a incredible touch to the overall vibe. Great effort!
https://k8viet.gurum/# k8 th? dam
88bet: 88 bet – nha cai 88bet
I just could not depart your website before suggesting that I really enjoyed
the usual info a person supply on your guests? Is gonna be
back frequently in order to inspect new posts
k8vip: k8 – link vao k8
Nice post. I understand something very complicated on distinct blogs everyday. It will always be stimulating to see content from other writers and rehearse a specific thing at their store. I’d prefer to use some together with the content in my small weblog whether you don’t mind. Natually I’ll provide a link on the internet weblog. Many thanks sharing.
nice blog and really nice post. i like it. make a fanpage on facebook.
https://alo789.auction/# alo789 chinh th?c
I’ve observed that in the world the present moment, video games are definitely the latest fad with children of all ages. Often times it may be unattainable to drag young kids away from the activities. If you want the very best of both worlds, there are numerous educational activities for kids. Thanks for your post.
Sweet blog! I found it while browsing on Yahoo News. Do you have any suggestions on how to get listed
in Yahoo News? I’ve been trying for a while but I never seem to get there!
Appreciate it
https://88betviet.pro/# 88bet slot
k8: k8 – k8 bet
https://k8viet.gurum/# k8 th? dam
link vao k8 k8 th? dam nha cai k8
88bet: 188bet 88bet – keo nha cai 88bet
Oh my goodness! Amazing article dude! Thanks, However I am encountering difficulties with your RSS.
I don’t understand the reason why I can’t join it.
Is there anyone else getting the same RSS issues?
Anyone that knows the answer can you kindly respond? Thanx!!
https://je-tall-sf-marketing-50.b-cdn.net/research/je-tall-sf-marketing-(261).html
If you favor neutral tones, gold and silver attire are promising selections for an MOB!
88bet slot: nha cai 88bet – 88bet
http://88betviet.pro/# 88 bet
http://88betviet.pro/# 188bet 88bet
The listed below costs offer you an approximate consider just how much you might invest to run A/C in your house.
https://digi341sa.netlify.app/research/digi341sa-(485)
Shop now via varied retailers, including official online shops.
nha cai 88bet 188bet 88bet 88bet
https://k8viet.guru/# k8
88 bet: nha cai 88bet – 88bet slot
http://alo789.auction/# 789alo
https://alo789.auction/# alo 789 dang nh?p
k8vip: k8 – k8
Хотите перекусить вкусно? купить Гирос питу, шаверму, донер, гирос и тортилью. Ароматная свежая выпечка, мясо на гриле и фирменные соусы. Отличный выбор для перекуса, обеда или вечеринки.
alo789in alo 789 789alo
When you choose AMC Air Disadvantage for your new cooling system, you can rely on that you remain in the right hands.
https://88betviet.pro/# nha cai 88bet
88bet slot: nha cai 88bet – 88bet slot
https://jekyll.s3.us-east-005.backblazeb2.com/20241015-20/research/je-tall-sf-marketing-1-(455).html
You can all the time add a wrap should you don’t want to exhibit your arms.
https://88betviet.pro/# 88bet
http://k8viet.guru/# k8 bet
Pretty! This has been an incredibly wonderful article. Thanks for supplying this information.
alo789 chinh th?c: alo 789 – alo 789
nha cai k8 [url=https://k8viet.guru/#]link vao k8[/url] k8vip
I think this is one of the most important information for me.
And i am glad reading your article. But want to remark on some general things,
The web site style is wonderful, the articles is really nice : D.
Good job, cheers
You may experience smells from your a/c unit that suggest
it needs a solution.
https://k8viet.guru/# k8
very nice post, i definitely love this amazing site, persist in it
A brand new website Humber Premier Soccer has been set as much as cowl our rivals Grimsby City but also their League neighbours, Scunthorpe United and Hull Metropolis.
After looking over a number of the blog articles on your web site, I seriously like your way of blogging. I saved as a favorite it to my bookmark webpage list and will be checking back in the near future. Take a look at my web site too and tell me what you think.
Aw, this was an incredibly good post. Taking the time
and actual effort to create a good article… but what can I say… I
hesitate a whole lot and don’t manage to get nearly anything done.
dang nh?p alo789: alo789in – alo789hk
Greetings! Very helpful advice in this particular post! It is the little changes which will make the largest changes. Thanks for sharing!
http://88betviet.pro/# keo nha cai 88bet
I do not even know how I ended up here, but I thought this post was good.
I don’t know who you are but definitely you are going to a famous blogger if you are not already 😉 Cheers!
Each brand name will have differing EER level scores, so inspect the producer’s requirements.
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
Excellent items from you, man. I have take into account
your stuff previous to and you are just extremely excellent.
I actually like what you’ve obtained right here, really like
what you’re saying and the way wherein you are saying
it. You’re making it enjoyable and you continue to care for to keep it smart.
I can not wait to learn much more from you. That
is really a great website.
keo nha cai 88bet 188bet 88bet nha cai 88bet
http://k8viet.guru/# k8 th? dam
I dont usually post on many Blogs, still I simply must give you thanks keep up the astonishing work. Ok unfortunately its time to access school.
Mood stabilizers, similar to lithium and valproate, are sometimes prescribed to forestall manic and depressive episodes.
The Mercaz HaRav massacre, additionally called the Mercaz HaRav capturing, was an attack that occurred on March 6, 2008, by which a lone Palestinian gunman shot a number of students on the Mercaz HaRav yeshiva, a college in Jerusalem.
The installation day will normally be 4-8 weeks after you approve the proposition.
188bet 88bet: 88 bet – nha cai 88bet
https://alo789.auction/# alo789 chinh th?c
Good blog you have got here.. It’s hard to find good quality writing like yours nowadays.
I truly appreciate people like you! Take care!!
https://alo789.auction/# alo 789
Way cool! Some very valid points! I appreciate you writing this write-up plus the rest of the site is extremely good.
Hello there, your website stands out with its engaging articles and valuable insights—I’m truly impressed! Feel free to explore my blog 구글 seo for top-notch SEO tips.
Next time I read a blog, I hope that it doesn’t fail me just as much as this particular one. I mean, I know it was my choice to read, but I really thought you’d have something useful to talk about. All I hear is a bunch of complaining about something that you could fix if you were not too busy seeking attention.
Oh my goodness! Awesome article dude! Thank you so much, However I am experiencing problems with your RSS.
I don’t know the reason why I can’t join it. Is there anyone else
getting the same RSS problems? Anyone that knows the solution will
you kindly respond? Thanks!!
Hello there! This blog post couldn’t be written much better! Looking at this post reminds me of my previous roommate! He always kept talking about this. I’ll forward this post to him. Fairly certain he’s going to have a great read. Many thanks for sharing!
If you’re looking for an elevated culinary experience, Ystrad boasts quite a lot of tremendous dining institutions that will depart an enduring impression.
Good post but I was wondering if you could write a litte more on this subject? I’d be very thankful if you could elaborate a little bit further. Appreciate it!
Aw, this was an incredibly nice post. Spending some time and actual effort to make a superb article… but what can I say… I procrastinate a whole lot and never manage to get anything done.
Alan is thought in business circles as more than a legend.
I am no longer sure where you’re getting your info, however great topic.
I must spend some time finding out much more or working out more.
Thank you for fantastic information I used to be looking for this information for my mission.
https://alo789.auction/# alo 789
An interesting discussion will probably be worth comment. I do think that you simply write on this topic, it might not be described as a taboo subject but normally persons are too few to communicate on such topics. An additional. Cheers
https://k8viet.guru/# k8vip
88 bet: 88bet – 88bet slot
alo 789 alo789 789alo
Annual Evaluation of Monetary Economics.
http://alo789.auction/# alo 789
lsu6h6
k8 bet: link vao k8 – link vao k8
81, F & AM, Tuscan Chapter OES, Elkster Shrine, Member of the large Bend Historic Society and Wilbur Lutheran Church.
Appreciate the recommendation. Will try it out.
You’re so interesting! I do not think I have read through anything like that before. So great to discover somebody with some original thoughts on this issue. Seriously.. many thanks for starting this up. This website is something that’s needed on the web, someone with some originality.
http://k8viet.guru/# k8
Good article. I will be experiencing a few of these issues as well..
Use our domestic cost calculator to discover the
right type of domestic air conditioning system
for your home.
https://interpharmonline.com/# canadian drug stores
mexican drug stores online mexican drug stores online Mexican Pharm International
mexican pharmacy online store: MexicanPharmInter – Mexican Pharm International
Hello there! This blog post could not be written much better! Looking through this article reminds me of my previous roommate! He always kept preaching about this. I most certainly will send this post to him. Pretty sure he will have a very good read. Thanks for sharing!
haartransplantation hamburg preis
Hurrah! After all I got a weblog from where I be able to actually obtain useful information concerning my study and
knowledge.
http://mexicanpharminter.com/# mexican pharmacy online store
canadian drug prices
legitimate canadian pharmacy: online canadian pharmacy no prescription – canadian pharmacy 24h com
türkiye nin en turistik yerleri
Excellent beat ! I wish to apprentice even as you
amend your site, how could i subscribe for a weblog web site?
The account helped me a appropriate deal. I have been a little bit familiar of
this your broadcast offered bright transparent idea
As Vu-Thanh Nguyen, analysis analyst at Entry Markets Worldwide Companions (AMI-Companions) places it “In case your present clients are pleased with you, they may come back, and sometimes with their friends as properly. For those who make them dissatisfied, they may spread the phrase, and chances are you’ll by no means know what is going to hit you,” Which means companies can enhance their gross sales with present prospects relatively than new ones.
Đừng tải xuống bất kỳ phần mềm nào từ trang web này.
blogger link
You really make it appear really easy together with your presentation however I to find this
matter to be actually one thing which I think I would never
understand. It sort of feels too complex and extremely huge for me.
I’m looking ahead on your next put up, I’ll try to get the grasp of
it!
Way cool! Some very valid points! I appreciate you writing this post and the rest of the site is really good.
Mexican Pharm Inter [url=http://mexicanpharminter.com/#]mexican pharmacy online[/url] mexican pharmacy online order
Everything is very open with a really clear description of the issues. It was definitely informative. Your website is very helpful. Thanks for sharing.
https://mexicanpharminter.shop/# buying from online mexican pharmacy
http://mexicanpharminter.com/# mexican drug stores online
northern pharmacy canada
IndiaMedFast.com: india online pharmacy store – order medicines online india
I’ve been exploring for a bit for any high-quality articles or weblog posts in this kind of house . Exploring in Yahoo I eventually stumbled upon this web site. Studying this information So i’m satisfied to show that I have an incredibly just right uncanny feeling I found out exactly what I needed. I most for sure will make certain to do not disregard this website and provides it a look a relentless basis.
IndiaMedFast: cheapest online pharmacy india – india online pharmacy store
Next time I read a blog, Hopefully it won’t fail me as much as this particular one. I mean, I know it was my choice to read through, nonetheless I really believed you would probably have something useful to say. All I hear is a bunch of whining about something that you could possibly fix if you weren’t too busy looking for attention.
Three-quarters of food grown in this nation is estimated to return from family farm companies that shall be immediately hit by Labour’s new plan to apply inheritance tax to all farms value more than £1million.
I could not refrain from commenting. Perfectly written.
It’s awesome to pay a visit this site and reading the views of
all colleagues about this article, while I am also keen of getting experience.
http://indiamedfast.com/# india online pharmacy store
If you are wanting to enquire about air disadvantage installation in Kingston,
simply get in touch with our group.
When I originally commented I seem to have clicked the -Notify me when new comments are added- checkbox and from now on each time a comment is added I get four emails with the exact same comment. Is there an easy method you can remove me from that service? Many thanks.
https://indiamedfast.shop/# cheapest online pharmacy india
canada pharmacy reviews
canadian pharmacy review: Certified International Pharmacy Online – online canadian pharmacy reviews
I am regular visitor, how are you everybody? This article posted at this site is genuinely
pleasant.
online medicine shopping in india cheapest online pharmacy india india pharmacy without prescription
mexican pharmacy online order: Mexican Pharm International – Mexican Pharm Inter
Incredible points. Outstanding arguments. Keep up the great work.
Everything is very open with a clear clarification of the challenges. It was truly informative. Your site is very useful. Thanks for sharing!
https://interpharmonline.shop/# canadian pharmacy 24
http://indiamedfast.com/# order medicines online india
legitimate canadian pharmacies
global pharmacy canada: Inter Pharm Online – canadian pharmacy meds review
Everyone loves it when folks get together and share opinions. Great blog, stick with it.
Pretty section of content. I just stumbled upon your web site and
in accession capital to assert that I get actually enjoyed account your blog posts.
Any way I will be subscribing to your augment and even I achievement you access consistently rapidly.
canada pharmacy online: InterPharmOnline.com – buy prescription drugs from canada cheap
Lines are open 8am to 8pm weekdays, 8am to 4pm Saturday and 10am to
4pm Sunday.
It is very important to remove this portion prior to mounting the side panels.
cheapest online pharmacy india order medicines online india IndiaMedFast.com
Upgrading to a newer design can aid cut expenses by maintaining your
bills down.
http://mexicanpharminter.com/# mexican drug stores online
https://mexicanpharminter.shop/# MexicanPharmInter
canadian pharmacy meds
Mexican Pharm Inter: mexican pharmacy online store – buying from online mexican pharmacy
antalya psikolog
Wow, this paragraph is fastidious, my younger sister is analyzing these kinds of things, so I am going to
tell her.
antalya nın turistik özellikleri
Ahaa, its good conversation regarding this article at this place at
this blog, I have read all that, so now me also commenting at this place.
A/c devices not serviced in over 6 months will create awful germs.
https://interpharmonline.shop/# thecanadianpharmacy
canadian pharmacy meds
http://mexicanpharminter.com/# buying from online mexican pharmacy
trusted canadian pharmacy: InterPharmOnline.com – my canadian pharmacy review
https://je-tall-marketing-395.b-cdn.net/research/je-tall-sf-marketing-(423).html
With palm leaf décor and lots of vines, green was a major theme all through this charming and colourful South Carolina celebration.
buy prescription drugs from canada cheap: fda approved canadian online pharmacies – online canadian drugstore
The outcome of each kind is measured in British Thermal Units, which are
the amount of heat eliminated in an hour.
canadapharmacyonline legit InterPharmOnline.com canadian mail order pharmacy
Hi, I do think this is a great web site. I stumbledupon it 😉 I’m going to revisit yet again since I saved as a favorite it. Money and freedom is the greatest way to change, may you be rich and continue to guide other people.
Hmm is anyone else experiencing problems with the pictures on this blog loading?
I’m trying to find out if its a problem on my end or if it’s the blog.
Any feedback would be greatly appreciated.
https://interpharmonline.com/# reputable canadian pharmacy
safe canadian pharmacies
https://mexicanpharminter.com/# reliable mexican pharmacies
Hello to every body, it’s my first go to see of this weblog; this blog contains awesome and actually fine stuff for visitors.
Tremendous issues here. I am very happy to peer your post. Thank you so much and I’m having
a look forward to touch you. Will you please drop me a e-mail?
You’re so awesome! I don’t believe I have read through something like that before. So great to find another person with original thoughts on this subject matter. Really.. many thanks for starting this up. This site is something that is needed on the internet, someone with a bit of originality.
Tremendous things here. I am very happy to see your post.
Thank you a lot and I am taking a look forward to
contact you. Will you please drop me a e-mail?
online pharmacy india: cheapest online pharmacy india – order medicines online india
Your method of explaining the whole thing in this paragraph is in fact fastidious, all can easily know it, Thanks a lot.
pharmacy rx world canada: most reliable canadian online pharmacies – reliable canadian pharmacy
Hey there! Would you mind if I share your blog with my
twitter group? There’s a lot of people that I
think would really appreciate your content. Please let
me know. Many thanks
Very nice article. I definitely appreciate this site.
Keep writing!
http://mexicanpharminter.com/# MexicanPharmInter
canadian pharmacy sarasota
http://mexicanpharminter.com/# buying from online mexican pharmacy
I enjoy reading through an article that will make people think. Also, many thanks for permitting me to comment.
https://digi293sa.netlify.app/research/digi293sa-(184)
Now, I simply need to remember all this when my son will get married.
Very soon this web page will be famous amid all blog people, due to it’s good articles
Greetings! Very helpful advice within this post! It’s the little changes which will make the greatest changes. Thanks a lot for sharing!
best canadian pharmacy online canadian drugstore online no prescription buy canadian drugs
MexicanPharmInter: MexicanPharmInter – mexican drug stores online
Sweet site, super pattern , real clean and utilize genial .
KamagraKopen.pro: kamagra jelly kopen – Kamagra
http://generic100mgeasy.com/# buy viagra here
https://tadalafileasybuy.shop/# Generic Tadalafil 20mg price
Generic100mgEasy: Generic 100mg Easy – viagra without prescription
umzugshelfer hannover
Awesome issues here. I’m very satisfied to see your post. Thanks so much and
I am taking a look forward to contact you. Will you kindly drop me a
mail?
Good blog you have got here.. It’s difficult to find good quality writing like yours these days. I truly appreciate individuals like you! Take care!!
avukat istanbul
I’ve been browsing online more than 2 hours today, yet I never
found any interesting article like yours. It’s pretty worth enough for me.
In my opinion, if all site owners and bloggers made good content as you did, the web will be a lot more useful than ever before.
fantastic post, very informative. I wonder why the opposite experts of this
sector do not understand this. You must proceed your writing.
I’m sure, you’ve a great readers’ base already!
Do you have a spam issue on this site; I also am a blogger, and I was wondering your situation; many of
us have developed some nice procedures and
we are looking to swap strategies with others, why not shoot
me an e-mail if interested.
https://jekyll2.s3.us-west-002.backblazeb2.com/je-20250304-27/research/marketing-(278).html
Its expansive variety, turning into fit and classy design deem Montage the leader in Mother of the Bride and Mother of the Groom dress collections.
What’s up i am kavin, its my first time to commenting anywhere, when i read
this article i thought i could also create comment due to this good
paragraph.
Truly appreciated reading this article. It’s very articulate and filled with useful details. Thanks for offering this.
Floor-mounted cooling systems are most commonly attached to a wall but at
a reduced elevation.
https://generic100mgeasy.shop/# Generic100mgEasy
buy generic 100mg viagra online: buy generic 100mg viagra online – buy generic 100mg viagra online
http://tadalafileasybuy.com/# Tadalafil Easy Buy
TadalafilEasyBuy.com cialis without a doctor prescription TadalafilEasyBuy.com
Hi, I do think this is an excellent site. I stumbledupon it 😉 I may come back once again since i have bookmarked it. Money and freedom is the best way to change, may you be rich and continue to help others.
Generic 100mg Easy: Generic 100mg Easy – Generic100mgEasy
Hello There. I found your blog the use of msn. This is an extremely neatly written article.
I’ll be sure to bookmark it and return to learn more of your useful info.
Thanks for the post. I’ll certainly return.
https://tadalafileasybuy.com/# Tadalafil Easy Buy
Cialis over the counter: cialis without a doctor prescription – Cialis over the counter
http://generic100mgeasy.com/# buy generic 100mg viagra online
Aw, this was an extremely nice post. Taking a few minutes and actual
effort to produce a great article… but what can I say… I hesitate a whole lot and
never manage to get anything done.
Having read this I believed it was very informative. I appreciate you taking the time and energy to put this informative article together. I once again find myself spending a significant amount of time both reading and posting comments. But so what, it was still worth it!
buy generic 100mg viagra online: Generic 100mg Easy – Generic100mgEasy
Genuinely liked reading this entry. It’s very clear and full of helpful information. Thank you for providing this.
Officiele Kamagra van Nederland kamagra kopen nederland kamagra kopen nederland
Hi would you mind stating which blog platform you’re
using? I’m looking to start my own blog in the near future but I’m having a
tough time making a decision between BlogEngine/Wordpress/B2evolution and
Drupal. The reason I ask is because your layout seems
different then most blogs and I’m looking for something completely unique.
P.S Apologies for being off-topic but I had to ask!
https://generic100mgeasy.com/# buy generic 100mg viagra online
cialis without a doctor prescription: cheapest cialis – cialis without a doctor prescription
http://generic100mgeasy.com/# Generic100mgEasy
Right away I am going away to do my breakfast, when having my breakfast coming over again to read more news.
Great info. Lucky me I recently found your site by accident (stumbleupon). I’ve book marked it for later!
i use lamp shades with CFL ubls instead of incandescent lamps, they are much cooler and uses less electricity~
Hi there! This post could not be written much better! Looking through this article reminds me of my previous roommate! He constantly kept talking about this. I am going to send this article to him. Fairly certain he will have a very good read. Many thanks for sharing!
ose7vw
cialis without a doctor prescription: Tadalafil Easy Buy – TadalafilEasyBuy.com
https://marketing-93.tor1.digitaloceanspaces.com/research/marketing-(330).html
This is one component of the attire that do not have to match, so lengthy as the formality is coordinated.
https://kamagrakopen.pro/# kamagra gel kopen
https://generic100mgeasy.com/# buy generic 100mg viagra online
The June 2020 derecho was the primary to influence the Pennsylvania-New Jersey area since June 2012, when a storm moved east from Iowa into southern Pennsylvania.
Tadalafil Easy Buy: cialis without a doctor prescription – Tadalafil Easy Buy
There’s definately a great deal to know about this topic. I like all the points you have made.
istanbulda gezilecek yerler sırasıyla
I am curious to find out what blog system you are using?
I’m having some small security issues with my latest blog and I would like
to find something more secure. Do you have any recommendations?
Cialis 20mg price: Tadalafil Easy Buy – Buy Cialis online
Tadalafil Easy Buy TadalafilEasyBuy.com cheapest cialis
I simply couldn’t depart your website prior to suggesting that I actually enjoyed
the standard info an individual supply for your visitors?
Is going to be again ceaselessly to investigate cross-check new posts
http://generic100mgeasy.com/# buy Viagra over the counter
https://kamagrakopen.pro/# KamagraKopen.pro
https://filedn.eu/lxtC6dFlc5qkLyWtpRp8Gdb/search-marketing-298/research/marketing-(362).html
As versatile as is elegant, this icy blue frock is the right transition piece to take you from the ceremony to the reception.
Generic 100mg Easy: sildenafil over the counter – generic sildenafil
cialis for sale: Tadalafil Easy Buy – п»їcialis generic
If you are going for best contents like I do, simply
pay a visit this website everyday for the reason that it presents feature contents,
thanks
There’s definately a lot to find out about this issue. I love all the points you made.
Oh my goodness! Amazing article dude! Thanks, However I am experiencing issues with your RSS. I don’t know why I cannot join it. Is there anybody getting identical RSS issues? Anyone who knows the solution can you kindly respond? Thanx.
The tornado then continued south of Hornersville and over the Hornersville Swamp Conservation Space, damaging bushes and power poles with a mobile dwelling additionally sustaining minor damage.
Speak to regional growth businesses to get information about improvement forecasts, planned roads, utility extensions and building prices.
The bottom of the baskets might need to have a chunk of Lucite, cardboard, or plywood to provide a level floor.
https://tadalafileasybuy.shop/# cialis without a doctor prescription
https://tadalafileasybuy.shop/# TadalafilEasyBuy.com
Pretty nice post. I just stumbled upon your weblog
and wished to mention that I have really enjoyed surfing around your blog posts.
After all I’ll be subscribing in your feed and I hope you write once more soon!
nkz019
buy generic 100mg viagra online: Viagra online price – buy generic 100mg viagra online
cheapest cialis cialis without a doctor prescription Cialis 20mg price in USA
Typically expense ratios of an index fund range from 0.10 for U.S.
cialis without a doctor prescription: cialis without a doctor prescription – п»їcialis generic
https://je-tall-marketing-364.blr1.digitaloceanspaces.com/research/je-tall-sf-marketing-(8).html
—are any indication, that adage rings true, particularly in relation to their very own wedding type.
https://digi319sa.netlify.app/research/digi319sa-(430)
From modest attire to one thing with a bit extra aptitude The Dress Outlet prides itself on having an intensive gallery of Mother of the Bride Dresses.
Some dad and mom are very strict about this, and additionally they need their baby to obtain glorious grades at school.
Kamagra: Kamagra – Kamagra Kopen Online
If you want to make this investment, you’ll need to develop an intelligent strategy.
https://generic100mgeasy.shop/# Generic100mgEasy
https://kamagrakopen.pro/# kamagra jelly kopen
Hey there! I know this is kinda off topic but I was wondering if you knew where I could get a captcha plugin for my comment form? I’m using the same blog platform as yours and I’m having difficulty finding one? Thanks a lot!
kamagra kopen nederland: kamagra pillen kopen – KamagraKopen.pro
filipinler’e para göndermek
It’s really very difficult in this full of
activity life to listen news on Television, so I simply use the web for that purpose, and
get the most up-to-date information.
MetaMask Extension is a must-have! It allows seamless interaction with dApps and ensures secure transactions. Highly recommended for crypto users.
Buy Tadalafil 10mg: TadalafilEasyBuy.com – cialis without a doctor prescription
https://marketing-63.tor1.digitaloceanspaces.com/research/marketing-(127).html
Look for materials like breezy chiffon, breathable mesh, or draping georgette for the ultimate seashore wedding ceremony attire.
https://digi476sa.netlify.app/research/digi476sa-(127)
Make it pop with a blinged-out pair of heels and matching equipment.
https://tadalafileasybuy.shop/# TadalafilEasyBuy.com
Tadalafil Easy Buy Cialis 20mg price in USA Tadalafil Easy Buy
Loved this!
deprem farkındalığı meb
I think that is among the most important information for me.
And i am glad reading your article. But want to statement on few general things, The web site
taste is wonderful, the articles is in reality excellent : D.
Excellent process, cheers
https://marketing-124.nyc3.digitaloceanspaces.com/research/marketing-(102).html
The straps and sleeves you choose on your gown will have an result on the neckline and form of your costume.
deprem farkındalığı meb
I know this if off topic but I’m looking into starting my own weblog and was curious
what all is required to get set up? I’m assuming having a blog like yours would cost a pretty penny?
I’m not very web savvy so I’m not 100% sure.
Any tips or advice would be greatly appreciated. Thanks
turistlerin en çok gezdiği yerler
What’s up, I read your blog like every week. Your story-telling style is awesome,
keep doing what you’re doing!
Tadalafil Easy Buy: TadalafilEasyBuy.com – TadalafilEasyBuy.com
https://digi183sa.netlify.app/research/digi183sa-(4)
Browse through the new assortment of Mother of the Bride gowns 2021.
http://generic100mgeasy.com/# Generic100mgEasy
http://generic100mgeasy.com/# Generic100mgEasy
kamagra gel kopen: kamagra gel kopen – Kamagra
Oh my goodness! Impressive article dude! Thank you, However I am
going through troubles with your RSS. I don’t know
why I can’t join it. Is there anybody having similar RSS
problems? Anyone that knows the answer will you kindly respond?
Thanx!!
Actually when someone doesn’t know then its up to
other people that they will assist, so here it takes place.
https://marketing-115.nyc3.digitaloceanspaces.com/research/marketing-(349).html
Jovani Plus size mother of the bride clothes suits any physique type.
Now that the world is a worldwide village, every enterprise wish to go browsing, subsequently the opportunity to earn cash is excessive.
buy Viagra over the counter: Generic 100mg Easy – Generic100mgEasy
Super happy! Perfect.
Hello! I simply wish to offer you a huge thumbs up for the excellent info you’ve got here on this post.
I am returning to your site for more soon.
After checking out a number of the blog posts on your site, I honestly like your way of writing a blog. I book-marked it to my bookmark site list and will be checking back soon. Please check out my web site as well and tell me your opinion.
I needed to thank you for this good read!!
I certainly enjoyed every little bit of it. I’ve got you book marked to check out new stuff you post…
Order Viagra 50 mg online Generic100mgEasy buy generic 100mg viagra online
https://generic100mgeasy.com/# Generic100mgEasy
https://kamagrakopen.pro/# kamagra gel kopen
https://digi307sa.z13.web.core.windows.net/research/digi307sa-(56).html
My daughter goals of a marriage on a seashore in Bali, so the place will that go away me I wonder.
buy cialis pill: TadalafilEasyBuy.com – cialis without a doctor prescription
Nicely put, Cheers.
Spot on with this write-up, I actually feel this amazing site needs much more attention. I’ll probably be back again to read
through more, thanks for the information!
Hey, I think your blog might be having browser compatibility issues.
When I look at your blog site in Ie, it looks fine but when opening in Internet Explorer, it has some overlapping.
I just wanted to give you a quick heads up! Other then that, excellent blog!
пин ап казино: https://pinupkz.life/
uf0z7p
пин ап казино зеркало – пин ап казино
Diagnostico de equipos
Dispositivos de calibración: fundamental para el rendimiento uniforme y eficiente de las equipos.
En el campo de la tecnología contemporánea, donde la rendimiento y la fiabilidad del dispositivo son de máxima importancia, los aparatos de balanceo desempeñan un rol crucial. Estos equipos adaptados están concebidos para balancear y asegurar piezas dinámicas, ya sea en herramientas manufacturera, transportes de transporte o incluso en dispositivos de uso diario.
Para los especialistas en reparación de sistemas y los ingenieros, manejar con aparatos de calibración es importante para promover el desempeño uniforme y seguro de cualquier sistema rotativo. Gracias a estas soluciones modernas innovadoras, es posible minimizar considerablemente las oscilaciones, el sonido y la esfuerzo sobre los soportes, aumentando la vida útil de piezas valiosos.
Asimismo significativo es el rol que juegan los dispositivos de ajuste en la servicio al comprador. El ayuda técnico y el mantenimiento regular utilizando estos dispositivos permiten brindar soluciones de alta nivel, mejorando la satisfacción de los compradores.
Para los responsables de proyectos, la aporte en estaciones de equilibrado y sensores puede ser importante para incrementar la eficiencia y eficiencia de sus sistemas. Esto es especialmente trascendental para los inversores que gestionan pequeñas y pequeñas organizaciones, donde cada elemento es relevante.
Asimismo, los aparatos de calibración tienen una extensa aplicación en el área de la prevención y el gestión de excelencia. Posibilitan encontrar posibles problemas, evitando mantenimientos caras y averías a los dispositivos. También, los resultados obtenidos de estos aparatos pueden utilizarse para perfeccionar sistemas y mejorar la reconocimiento en motores de consulta.
Las campos de implementación de los dispositivos de equilibrado incluyen diversas áreas, desde la manufactura de ciclos hasta el monitoreo del medio ambiente. No afecta si se habla de importantes producciones de fábrica o limitados talleres caseros, los aparatos de equilibrado son necesarios para promover un funcionamiento eficiente y sin fallos.
If you are billed per hour, then duration is very appropriate to the cost.
пин ап вход – пин ап казино зеркало
The expense of preserving cooling systems differs depending on the kind, size, and intricacy of the system.