Welcome back to the series of Deploying On AWS Cloud Using Terraform 👨🏻💻. In this entire series, we will focus on our core concepts of Terraform by launching important basic services from scratch which will take your infra-as-code journey from beginner to advanced. This series would start from beginner to advance with real life Usecases and Youtube Tutorials.
If you are a beginner for Terraform and want to start your journey towards infra-as-code developer as part of your devops role buckle up 🚴♂️ and lets get started and understand core Terraform concepts by implementing it…🎬
🔎Basic Terraform Configurations🔍
As part of basic configuration we are going to setup 3 terraform files
1. Providers File:- Terraform relies on plugins called “providers” to interact with cloud providers, SaaS providers, and other APIs.
Providers are distributed separately from Terraform itself, and each provider has its own release cadence and version numbers.
The Terraform Registry is the main directory of publicly available Terraform providers, and hosts providers for most major infrastructure platforms. Each provider has its own documentation, describing its resource types and their arguments.
We would be using AWS Provider for our terraform series. Make sure to refer Terraform AWS documentation for up-to-date information.
Provider documentation in the Registry is versioned; you can use the version menu in the header to change which version you’re viewing.
provider "aws" {
region = "var.AWS_REGION"
shared_credentials_file = ""
}
2. Variables File:- Terraform variables lets us customize aspects of Terraform modules without altering the module’s own source code. This allows us to share modules across different Terraform configurations, reusing same data at multiple places.
When you declare variables in the root terraform module of your configuration, you can set their values using CLI options and environment variables. When you declare them in child modules, the calling module should pass values in the module block.
variable "AWS_REGION" {
default = "us-east-1"
}
#-------------------------Fetch VPC ID---------------------------------
data "aws_vpc" "GetVPC" {
filter {
name = "tag:Name"
values = ["CustomVPC"]
}
}
#-------------------------Variables For Autoscaling---------------------
variable "instance_type" {
type = string
default = "t2.micro"
}
variable "autoscaling_group_min_size" {
type = number
default = 2
}
variable "autoscaling_group_max_size" {
type = number
default = 3
}
variable "aws_key_pair" {
type = string
default =
}
#-------------------------Fetch Public Subnets List----------------------
data "aws_subnet_ids" "GetSubnet_Ids" {
vpc_id = data.aws_vpc.GetVPC.id
filter {
name = "tag:Type"
values = ["Public"]
}
}
data "aws_subnet" "GetSubnet" {
count = "${length(data.aws_subnet_ids.GetSubnet_Ids.ids)}"
id = "${tolist(data.aws_subnet_ids.GetSubnet_Ids.ids)[count.index]}"
}
#-------------------------Fetch Target Group ARN----------------------
data "aws_lb_target_group" "elb_tg" {
arn = var.elb_tg_arn
}
3. Versions File:- It’s always a best practice to maintain a version file where you specific version based on which your stack is testing and live on production.
terraform {
required_version = ">= 0.12"
}
🎨 Diagrammatic Representation 🎨
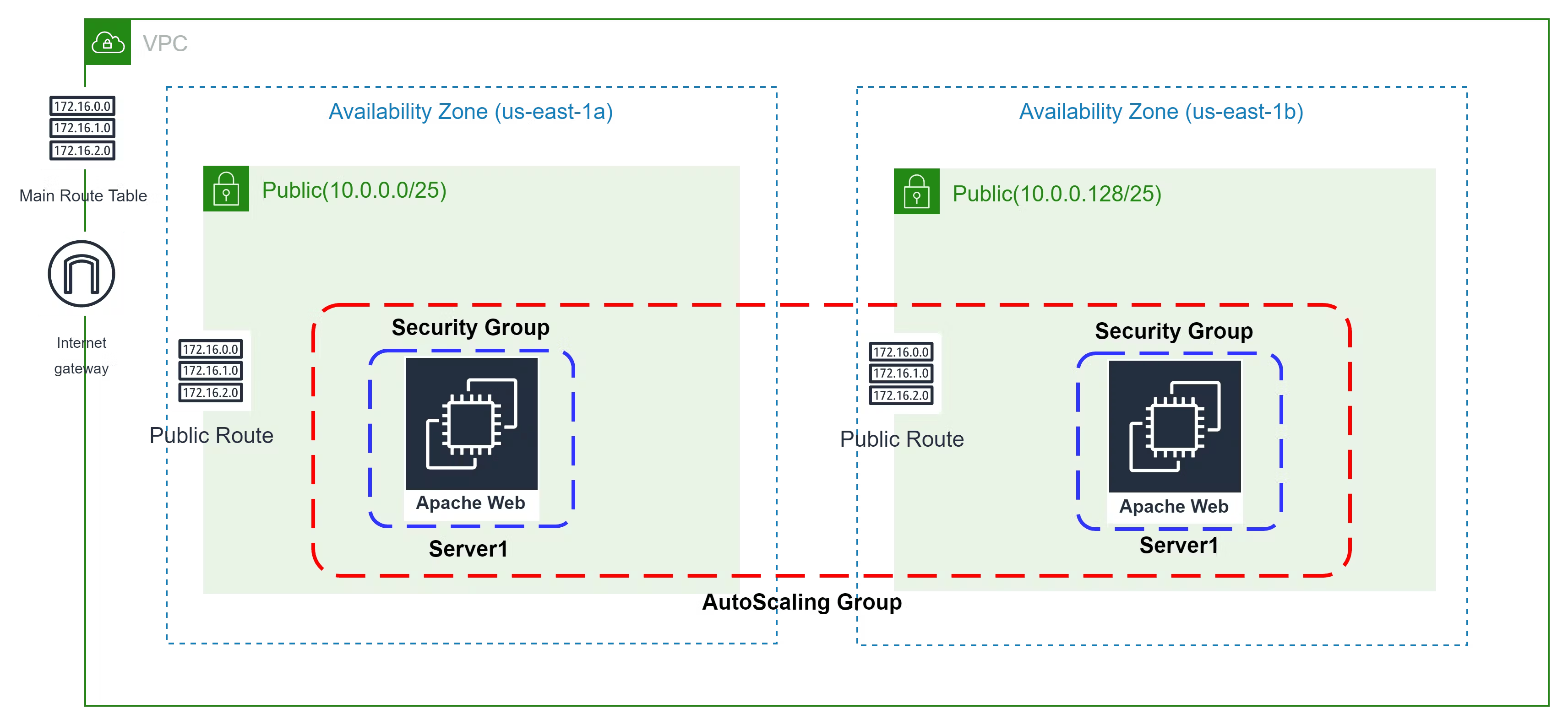
Configure Security Group For Launch Configuration
The method acts as a virtual firewall to control your inbound and outbound traffic flowing in and out.
🔳 Resource
✦ aws_security_group:- This resource is define traffic inbound and outbound rules on the subnet level.
🔳 Arguments
✦ name:- This is an optional argument to define the name of the security group.
✦ description:- This is an optional argument to mention details about the security group that we are creating.
✦ vpc_id:- This is a mandatory argument and refers to the id of a VPC to which it would be associated.
✦ tags:- One of the most important property used in all resources. Always make sure to attach tags for all your resources.
EGRESS & INGRESS are processed in attribute-as-blocks mode.
resource "aws_security_group" "asg_sg" {
name = "ASG_Allow_Traffic"
description = "Allow all inbound traffic for asg"
vpc_id = data.aws_vpc.GetVPC.id
ingress {
from_port = 443
to_port = 443
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
ingress {
from_port = 22
to_port = 22
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
ingress {
from_port = 8
to_port = 0
protocol = "icmp"
cidr_blocks = ["0.0.0.0/0"]
}
ingress {
from_port = 80
to_port = 80
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
egress {
from_port = 0
to_port = 0
protocol = "-1"
cidr_blocks = ["0.0.0.0/0"]
}
tags = {
Name = "terraform-asg-security-group"
}
}
👨🏻💻Deploy Launch Config and AutoScaling group👨🏻💻
Before creating the Autoscaling group let’s first define the launch configuration for EC2 instances that will be used by autoscaling later.
🔳 Resource
✦ aws_launch_configuration:- This resource creates a launch configuration for EC2 instances that we are going to deploy as part of our autoscaling group.
🔳 Arguments
✦ name_prefix:- This is an optional argument to create a unique name beginning with the specified prefix.
✦ image_id:- This is an mandatory argument to mention image_id id based on which EC2 instance will be launched.
✦ instance_type:- This is a mandatory argument to mention instance type for the EC2 instances like t2.small, t2.micro etc.
✦ key_name:- This is an optional argument to enable ssh connection to your EC2 instance.
✦ security_groups:- This is an optional argument to mention which controls your inbound and outbound traffic flowing to your EC2 instances inside a subnet.
✦ user_data:- This is an optional argument to provide commands or scripts to be executed during the launch of the EC2 instance.
✦ Lifecycle:- Lifecycle is a nested block that can appear within a resource block.
create_before_destroy:- when Terraform must change a resource argument that cannot be updated in place due to remote API limitations, Terraform will instead destroy the existing object and then create a new replacement object with the newly configured arguments.
resource "aws_launch_configuration" "launch_config_dev" {
name_prefix = "webteir_dev"
image_id = "ami-0742b4e673072066f"
instance_type = "${var.instance_type}"
key_name = "${var.aws_key_pair}"
security_groups = ["${aws_security_group.asg_sg.id}"]
associate_public_ip_address = true
user_data = <Deployed EC2 Using ASG" | sudo tee /var/www/html/index.html
EOF
lifecycle {
create_before_destroy = true
}
}
🔳 Resource
✦ aws_autoscaling_group:- This resource group resources for use so that it can be associated with load balancers.
🔳 Arguments
✦ launch_configuration:- This is an optional argument to mention name of the launch configuration to be used.
✦ min_size:- This is a mandatory argument to define the minimum size of the Autoscaling group.
✦ max_size:-This is a mandatory argument to define the maximum size of the Autoscaling group.
✦ target_group_arns:- This is an optional argument to define the target group arn to which EC2 can register.
✦ vpc_zone_identifier:- This is an optional argument to define a list of subnet IDs to launch resources in.
✦ tags:- One of the most important property used in all resources. Always make sure to attach tags for all your resources.
resource "aws_autoscaling_group" "autoscaling_group_dev" {
launch_configuration = "${aws_launch_configuration.launch_config_dev.id}"
min_size = "${var.autoscaling_group_min_size}"
max_size = "${var.autoscaling_group_max_size}"
target_group_arns = ["${data.aws_lb_target_group.elb_tg.arn}"]
vpc_zone_identifier = "${data.aws_subnet.GetSubnet.*.id}"
tag {
key = "Name"
value = "autoscaling-group-dev"
propagate_at_launch = true
}
}
🔳 Output File
Output values make information about your infrastructure available on the command line, and can expose information for other Terraform configurations to use. Output values are similar to return values in programming languages.
output "asg_sg" {
value = aws_security_group.asg_sg.id
description = "This is Security Group for autoscaling launch configuration."
}
output "aws_launch_configuration" {
value = aws_launch_configuration.launch_config_dev.id
description = "This is ASG Launch Configuration ID."
}
output "autoscaling_group_dev" {
value = aws_autoscaling_group.autoscaling_group_dev.id
description = "This is ASG ID."
}
🔊To view the entire GitHub code click here
1️⃣ The terraform fmt command is used to rewrite Terraform configuration files to a canonical format and style👨💻.
terraform fmt
2️⃣ Initialize the working directory by running the command below. The initialization includes installing the plugins and providers necessary to work with resources. 👨💻
terraform init
3️⃣ Create an execution plan based on your Terraform configurations. 👨💻
terraform plan
4️⃣ Execute the execution plan that the terraform plan command proposed. 👨💻
terraform apply --auto-approve
👁🗨👁🗨 YouTube Tutorial 📽
❗️❗️Important Documentation❗️❗️
⛔️ Hashicorp Terraform
⛔️ AWS CLI
⛔️ Hashicorp Terraform Extension Guide
⛔️ Terraform Autocomplete Extension Guide
⛔️ AWS Security Group
⛔️ AWS Launch Configuration
⛔️ AWS Autoscaling Group
⛔️ Lifecycle Meta-Argument
🥁🥁 Conclusion 🥁🥁
In this blog, we have configured the below resources
✦ AWS Security Group for the ASG Launch Configuration.
✦ AWS Launch Configuration.
✦ AWS Autoscaling Group.
I have also referenced what arguments and documentation we are going to use so that while you are writing the code it would be easy for you to understand terraform official documentation. Stay with me for the next blog.
📢 Stay tuned for my next blog…..
So, did you find my content helpful? If you did or like my other content, feel free to buy me a coffee. Thanks.

Author - Dheeraj Choudhary
RELATED ARTICLES
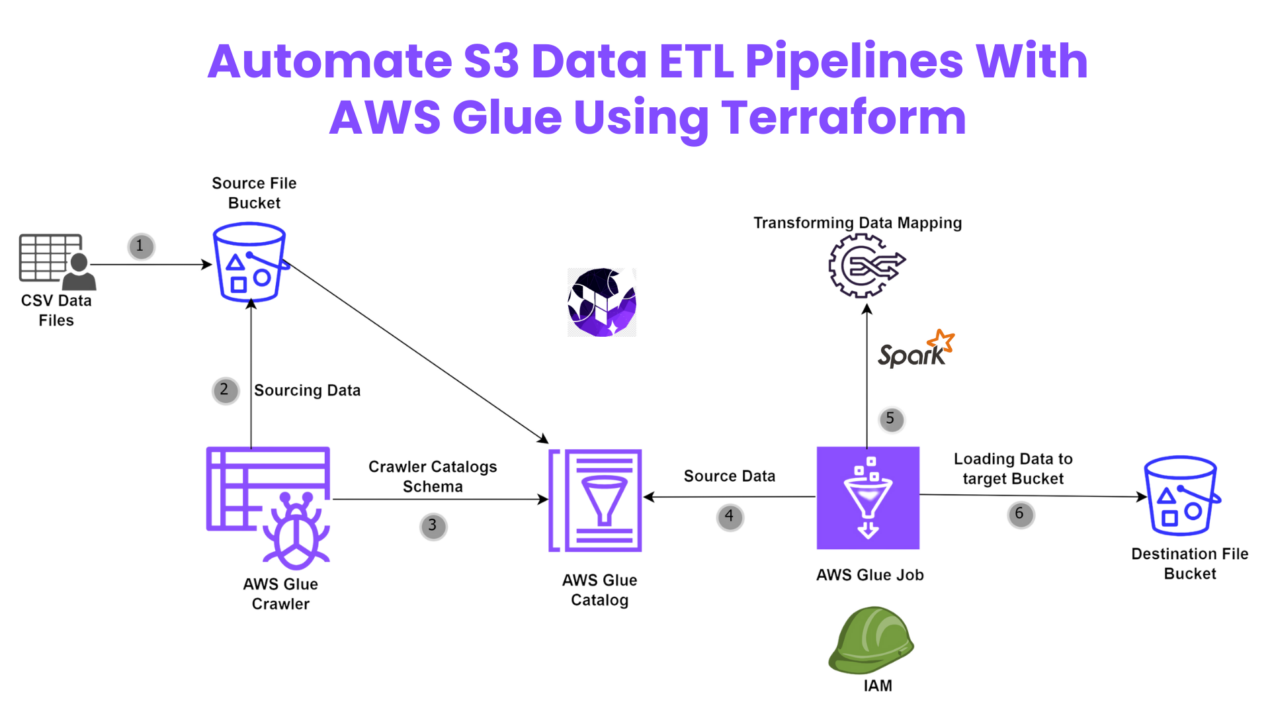
Automate S3 Data ETL Pipelines With AWS Glue Using Terraform
Discover how to automate your S3 data ETL pipelines using AWS Glue and Terraform in this step-by-step tutorial. Learn to efficiently manage and process your data, leveraging the power of AWS Glue for seamless data transformation. Follow along as we demonstrate how to set up Terraform scripts, configure AWS Glue, and automate data workflows.
Automating AWS Infrastructure with Terraform Functions
IntroductionManaging cloud infrastructure can be complex and time-consuming. Terraform, an open-source Infrastructure as Code (IaC) tool, si ...



Hi there, just became alert to your blog through Google,
and found that it’s truly informative. I’m gonna
watch out for brussels. I will be grateful if you continue this in future.
Numerous people will be benefited from your writing.
Cheers! Escape rooms hub
Very interesting topic, appreciate it for putting up..
Really great info can be found on site.Blog monetyze
Excellent blog you have here.. It’s hard to find good quality writing like yours these days. I really appreciate individuals like you! Take care!!
Very good info. Lucky me I came across your site by chance (stumbleupon). I have book marked it for later!
I seriously love your website.. Great colors & theme. Did you create this site yourself? Please reply back as I’m looking to create my own blog and would like to know where you got this from or exactly what the theme is named. Kudos.
Way cool! Some extremely valid points! I appreciate you writing this article plus the rest of the website is really good.
Excellent blog you have here.. It’s difficult to find excellent writing like yours these days. I truly appreciate individuals like you! Take care!!
Pretty! This was an extremely wonderful post. Many thanks for supplying this info.
This site really has all the info I needed concerning this subject and didn’t know who to ask.
Great information. Lucky me I found your website by chance (stumbleupon). I’ve bookmarked it for later.
This website truly has all the information I needed about this subject and didn’t know who to ask.
Spot on with this write-up, I really believe that this amazing site needs far more attention. I’ll probably be back again to read more, thanks for the info!
Having read this I believed it was really informative. I appreciate you taking the time and energy to put this content together. I once again find myself spending way too much time both reading and commenting. But so what, it was still worthwhile.
bookmarked!!, I like your site.
Very good write-up. I certainly appreciate this site. Keep writing!
Spot on with this write-up, I truly believe this web site needs much more attention. I’ll probably be returning to see more, thanks for the info!
Aw, this was an exceptionally good post. Spending some time and actual effort to produce a great article… but what can I say… I hesitate a whole lot and never seem to get anything done.
I’m very happy to find this web site. I need to to thank you for ones time just for this wonderful read!! I definitely liked every part of it and I have you bookmarked to check out new things on your site.
Your posts in this blog really shine! Glad to gain some new insights, which I happen to also cover on my page. Feel free to visit my webpage UY5 about Thai-Massage and any tip from you will be much apreciated.
Greetings! Very useful advice in this particular post! It’s the little changes that produce the most important changes. Thanks for sharing!
Hi! I just want to offer you a big thumbs up for the great info you have got right here on this post. I am returning to your site for more soon.
Very good article. I am facing some of these issues as well..
Howdy! I could have sworn I’ve been to this web site before but after looking at many of the posts I realized it’s new to me. Nonetheless, I’m certainly pleased I found it and I’ll be bookmarking it and checking back frequently.
Hi there, There’s no doubt that your web site could be having browser compatibility issues. When I look at your site in Safari, it looks fine however, when opening in I.E., it’s got some overlapping issues. I merely wanted to provide you with a quick heads up! Aside from that, fantastic website.
Having read this I thought it was extremely informative. I appreciate you spending some time and energy to put this article together. I once again find myself personally spending a significant amount of time both reading and commenting. But so what, it was still worth it.
You’ve made some good points there. I looked on the web to find out more about the issue and found most people will go along with your views on this site.
This site was… how do I say it? Relevant!! Finally I’ve found something that helped me. Thanks a lot.
After checking out a handful of the blog articles on your blog, I seriously like your technique of blogging. I book marked it to my bookmark webpage list and will be checking back soon. Please check out my web site too and let me know your opinion.
An outstanding share! I’ve just forwarded this onto a colleague who has been doing a little homework on this. And he in fact bought me dinner due to the fact that I stumbled upon it for him… lol. So let me reword this…. Thank YOU for the meal!! But yeah, thanx for spending some time to talk about this subject here on your site.
You made some really good points there. I checked on the web to find out more about the issue and found most individuals will go along with your views on this web site.
This website was… how do I say it? Relevant!! Finally I have found something which helped me. Many thanks.
This page certainly has all of the information and facts I needed concerning this subject and didn’t know who to ask.
Hi, I do think this is a great blog. I stumbledupon it 😉 I will come back once again since i have book-marked it. Money and freedom is the greatest way to change, may you be rich and continue to guide others.
I could not refrain from commenting. Perfectly written!
Way cool! Some extremely valid points! I appreciate you writing this post plus the rest of the website is extremely good.
Everything is very open with a precise clarification of the challenges. It was truly informative. Your website is very helpful. Thanks for sharing!
I love it when people come together and share thoughts. Great site, stick with it!
I would like to thank you for the efforts you’ve put in writing this blog. I’m hoping to check out the same high-grade blog posts by you in the future as well. In fact, your creative writing abilities has inspired me to get my very own website now 😉
An impressive share! I’ve just forwarded this onto a colleague who was conducting a little research on this. And he in fact ordered me lunch because I discovered it for him… lol. So allow me to reword this…. Thanks for the meal!! But yeah, thanks for spending time to discuss this issue here on your web site.
I blog frequently and I genuinely appreciate your information. This great article has really peaked my interest. I’m going to book mark your site and keep checking for new information about once a week. I subscribed to your RSS feed too.
Greetings! Very useful advice in this particular post! It’s the little changes that will make the largest changes. Thanks for sharing!
Great article! We will be linking to this particularly great post on our website. Keep up the good writing.
I was very pleased to uncover this site. I wanted to thank you for ones time just for this fantastic read!! I definitely really liked every part of it and i also have you book marked to see new stuff on your site.
A fascinating discussion is worth comment. I do believe that you need to publish more about this subject, it might not be a taboo subject but typically people do not discuss these subjects. To the next! Many thanks.
I seriously love your site.. Very nice colors & theme. Did you create this web site yourself? Please reply back as I’m attempting to create my own personal website and want to know where you got this from or what the theme is called. Kudos.
It’s hard to come by experienced people for this topic, but you sound like you know what you’re talking about! Thanks
Howdy! This post could not be written any better! Reading through this post reminds me of my previous roommate! He constantly kept talking about this. I’ll send this post to him. Pretty sure he’s going to have a good read. I appreciate you for sharing!
Great info. Lucky me I recently found your blog by accident (stumbleupon). I’ve bookmarked it for later!
Very good post! We will be linking to this particularly great content on our website. Keep up the great writing.
An impressive share! I’ve just forwarded this onto a coworker who was conducting a little homework on this. And he actually bought me lunch because I stumbled upon it for him… lol. So let me reword this…. Thanks for the meal!! But yeah, thanx for spending some time to discuss this issue here on your website.
I blog often and I really thank you for your content. The article has really peaked my interest. I’m going to bookmark your site and keep checking for new information about once a week. I subscribed to your Feed too.
Greetings! Very helpful advice within this post! It is the little changes which will make the largest changes. Thanks a lot for sharing!
Good article. I am experiencing some of these issues as well..
After I initially left a comment I appear to have clicked the -Notify me when new comments are added- checkbox and from now on whenever a comment is added I get four emails with the exact same comment. Perhaps there is an easy method you can remove me from that service? Many thanks.
Aw, this was an incredibly good post. Taking the time and actual effort to make a good article… but what can I say… I hesitate a lot and never manage to get anything done.
Having read this I thought it was very enlightening. I appreciate you spending some time and energy to put this article together. I once again find myself spending way too much time both reading and leaving comments. But so what, it was still worth it!
I wanted to thank you for this fantastic read!! I absolutely loved every bit of it. I’ve got you bookmarked to look at new stuff you post…
Oh my goodness! Impressive article dude! Many thanks, However I am encountering difficulties with your RSS. I don’t understand the reason why I can’t subscribe to it. Is there anybody getting similar RSS issues? Anyone that knows the solution can you kindly respond? Thanks.
Aw, this was a really good post. Taking a few minutes and actual effort to produce a really good article… but what can I say… I hesitate a whole lot and don’t seem to get anything done.
To the dheeraj3choudhary.com admin, Your posts are always a great source of knowledge.
This website was… how do I say it? Relevant!! Finally I’ve found something which helped me. Kudos!
This web site certainly has all of the information I needed about this subject and didn’t know who to ask.
Everything is very open with a clear description of the challenges. It was definitely informative. Your site is very helpful. Many thanks for sharing.
Hi, I do think this is an excellent site. I stumbledupon it 😉 I’m going to revisit yet again since I bookmarked it. Money and freedom is the best way to change, may you be rich and continue to guide other people.
You made some really good points there. I looked on the web to learn more about the issue and found most people will go along with your views on this web site.
Hi dheeraj3choudhary.com owner, Good work!
May I simply just say what a comfort to find somebody who genuinely understands what they’re discussing online. You actually understand how to bring a problem to light and make it important. A lot more people need to check this out and understand this side of the story. I can’t believe you’re not more popular given that you definitely possess the gift.
I was pretty pleased to discover this site. I wanted to thank you for your time for this particularly wonderful read!! I definitely enjoyed every bit of it and i also have you bookmarked to see new things on your web site.
Everything is very open with a really clear explanation of the issues. It was truly informative. Your site is very useful. Many thanks for sharing.
Everything is very open with a precise description of the issues. It was truly informative. Your site is very helpful. Many thanks for sharing.
Having read this I believed it was very enlightening. I appreciate you spending some time and energy to put this information together. I once again find myself spending way too much time both reading and leaving comments. But so what, it was still worth it!
I truly love your site.. Pleasant colors & theme. Did you develop this amazing site yourself? Please reply back as I’m planning to create my own personal website and would love to know where you got this from or exactly what the theme is named. Many thanks.
You should take part in a contest for one of the most useful blogs on the web. I most certainly will recommend this site!
I needed to thank you for this good read!! I certainly enjoyed every bit of it. I’ve got you saved as a favorite to check out new things you post…
You have made some good points there. I checked on the net for additional information about the issue and found most people will go along with your views on this web site.
I read this article. I think You put a great deal of exertion to make this article. I like your work. 스포츠 중계
Really nice and interesting post. I was looking for this kind of information and enjoyed reading this one. Keep posting. Thanks for sharing 스포츠중계
Howdy, I believe your website may be having browser compatibility issues. When I take a look at your site in Safari, it looks fine but when opening in I.E., it has some overlapping issues. I just wanted to provide you with a quick heads up! Besides that, fantastic website.
Great!!! Thank you for sharing this details. If you need some information about Entrepreneurs than have a look here 59N
Everything is very open with a really clear clarification of the challenges. It was truly informative. Your site is very helpful. Thanks for sharing!
Great post! We will be linking to this great article on our website. Keep up the great writing.
bookmarked!!, I like your web site!
This site truly has all of the information I wanted concerning this subject and didn’t know who to ask.
I’m amazed, I must say. Seldom do I encounter a blog that’s both equally educative and entertaining, and let me tell you, you have hit the nail on the head. The problem is an issue that too few men and women are speaking intelligently about. I am very happy that I came across this in my hunt for something regarding this.
Oh my goodness! Incredible article dude! Many thanks, However I am having problems with your RSS. I don’t understand the reason why I cannot subscribe to it. Is there anybody else having similar RSS issues? Anybody who knows the answer will you kindly respond? Thanx!
You’ve made some decent points there. I looked on the web to find out more about the issue and found most individuals will go along with your views on this website.
Pretty! This has been an extremely wonderful article. Thanks for providing these details.
That is a really good tip especially to those fresh to the blogosphere. Brief but very precise information… Many thanks for sharing this one. A must read article!
I blog often and I really appreciate your content. This article has really peaked my interest. I am going to take a note of your website and keep checking for new details about once a week. I subscribed to your Feed too.
I blog often and I really thank you for your information. This article has really peaked my interest. I’m going to take a note of your site and keep checking for new information about once a week. I subscribed to your Feed too.
Can I simply just say what a relief to discover somebody that actually knows what they are discussing online. You certainly know how to bring a problem to light and make it important. More and more people must look at this and understand this side of the story. I was surprised you’re not more popular given that you certainly possess the gift.
An outstanding share! I’ve just forwarded this onto a co-worker who was conducting a little research on this. And he actually bought me breakfast simply because I stumbled upon it for him… lol. So let me reword this…. Thank YOU for the meal!! But yeah, thanx for spending some time to discuss this topic here on your site.
You’re so cool! I don’t believe I’ve read through something like this before. So nice to discover another person with a few genuine thoughts on this subject. Seriously.. many thanks for starting this up. This site is one thing that is required on the internet, someone with some originality.
Pretty! This was an extremely wonderful post. Thanks for supplying these details.
The next time I read a blog, Hopefully it doesn’t fail me as much as this one. After all, I know it was my choice to read through, nonetheless I actually thought you would have something useful to say. All I hear is a bunch of whining about something you could fix if you were not too busy seeking attention.
Hi, I do think this is an excellent blog. I stumbledupon it 😉 I will revisit yet again since I book marked it. Money and freedom is the best way to change, may you be rich and continue to guide others.
I’m amazed, I have to admit. Rarely do I come across a blog that’s both educative and interesting, and let me tell you, you’ve hit the nail on the head. The problem is something that too few folks are speaking intelligently about. I am very happy I found this during my search for something relating to this.
Hi there! I could have sworn I’ve been to this website before but after browsing through some of the posts I realized it’s new to me. Nonetheless, I’m definitely delighted I came across it and I’ll be bookmarking it and checking back frequently!
Great article! We are linking to this particularly great content on our website. Keep up the good writing.
I have to thank you for the efforts you have put in penning this blog. I’m hoping to check out the same high-grade content by you in the future as well. In truth, your creative writing abilities has motivated me to get my own website now 😉
Excellent site you have here.. It’s hard to find good quality writing like yours these days. I truly appreciate people like you! Take care!!
Love how you’ve broken this down so clearly!
Appreciate the in-depth analysis here!
Aw, this was an exceptionally nice post. Spending some time and actual effort to produce a great article… but what can I say… I hesitate a lot and don’t seem to get nearly anything done.
Hi! I simply want to give you a huge thumbs up for your excellent information you have got here on this post. I am returning to your web site for more soon.
I would like to thank you for the efforts you have put in penning this website. I really hope to check out the same high-grade blog posts by you in the future as well. In truth, your creative writing abilities has encouraged me to get my own website now 😉
This web site definitely has all the information I wanted about this subject and didn’t know who to ask.
I like this site its a master peace ! Glad I observed this on google .
After looking over a number of the blog articles on your web page, I seriously appreciate your way of blogging. I book marked it to my bookmark webpage list and will be checking back in the near future. Please check out my website as well and tell me how you feel.
Having read this I believed it was extremely informative. I appreciate you taking the time and effort to put this short article together. I once again find myself spending way too much time both reading and leaving comments. But so what, it was still worth it!
Very good post! We will be linking to this particularly great content on our website. Keep up the good writing.
I wanted to thank you for this wonderful read!! I absolutely loved every bit of it. I’ve got you book marked to look at new stuff you post…
I’ve had problem with blood sugar changes for many years,
and it really influenced my energy degrees throughout
the day. Because beginning Sugar Defender, I feel more balanced and sharp, and I do not experience those afternoon sags any longer!
I enjoy that it’s a natural option that works without any extreme negative effects.
It’s absolutely been a game-changer for me
As a person who’s always bewared about my blood glucose, finding
Sugar Defender has actually been an alleviation. I feel a lot extra in control,
and my current check-ups have revealed positive renovations.
Recognizing I have a reliable supplement to sustain my
regular gives me assurance. I’m so grateful for Sugar Protector’s impact on my health and wellness!
For several years, I’ve battled unforeseeable blood sugar level swings that left me really feeling drained pipes and lethargic.
But considering that integrating Sugar Protector right into my regular, I have actually observed a significant renovation in my total energy and security.
The feared mid-day thing of the past, and I appreciate that this natural remedy achieves these outcomes
with no unpleasant or adverse responses. truthfully
been a transformative discovery for me.
Including Sugar Protector right into my everyday routine general well-being.
As a person that prioritizes healthy and balanced consuming,
I appreciate the additional defense this supplement gives.
Since beginning to take it, I’ve discovered a significant renovation in my energy degrees and a substantial reduction in my desire for undesirable snacks
such a such an extensive influence on my life.
Oh my goodness! Impressive article dude! Many thanks, However I am experiencing problems with your RSS. I don’t know why I can’t join it. Is there anyone else getting the same RSS issues? Anybody who knows the answer will you kindly respond? Thanx.
Howdy! I could have sworn I’ve been to your blog before but after looking at a few of the posts I realized it’s new to me. Nonetheless, I’m certainly pleased I came across it and I’ll be book-marking it and checking back regularly!
Very good information. Lucky me I came across your blog by chance (stumbleupon). I have book-marked it for later!
Hey! Do you know if they make any plugins to help with
Search Engine Optimization? I’m trying to get my blog to
rank for some targeted keywords but I’m not seeing very good success.
If you know of any please share. Thank you! You can read similar blog here:
Wool product
Greetings! Very useful advice in this particular article! It is the little changes that produce the most significant changes. Thanks a lot for sharing!
Greetings! Very useful advice in this particular article! It is the little changes which will make the greatest changes. Thanks a lot for sharing!
Hello! I could have sworn I’ve been to this website before but after going through many of the posts I realized it’s new to me. Anyways, I’m certainly delighted I discovered it and I’ll be bookmarking it and checking back regularly!
Good post! We will be linking to this particularly great content on our website. Keep up the great writing.
I blog frequently and I seriously appreciate your content. This article has truly peaked my interest. I am going to bookmark your blog and keep checking for new details about once per week. I opted in for your RSS feed as well.
That is a very good tip particularly to those fresh to the blogosphere. Short but very precise info… Thank you for sharing this one. A must read article.
It has been changing by 0 priligy precio 5 million American women
It helps children explore their pursuits, build confidence, and develop vital thinking abilities.
Thanks for another informative site. Where else could I get that kind of information written in such a perfect way? I have a project that I am just now working on, and I have been on the look out for such information.
Good post. I learn something totally new and challenging on websites I stumbleupon every day. It’s always useful to read through articles from other writers and practice something from other websites.
You’re so cool! I do not believe I’ve read through anything like that before. So great to find somebody with original thoughts on this subject. Seriously.. thanks for starting this up. This web site is something that is required on the internet, someone with a little originality.
Pretty! This was an incredibly wonderful article. Thanks for providing this info.
bookmarked!!, I really like your web site.
Next time I read a blog, Hopefully it won’t fail me as much as this particular one. After all, I know it was my choice to read through, however I actually thought you would probably have something interesting to talk about. All I hear is a bunch of whining about something you could possibly fix if you weren’t too busy seeking attention.
Great post. I will be going through some of these issues as well..
This is a topic that’s near to my heart… Thank you! Exactly where can I find the contact details for questions?
Hey there! I just want to offer you a big thumbs up for the excellent information you have right here on this post. I’ll be returning to your blog for more soon.
I seriously love your blog.. Very nice colors & theme. Did you develop this site yourself? Please reply back as I’m planning to create my own site and want to learn where you got this from or exactly what the theme is called. Thank you!
I’m very pleased to discover this web site. I need to to thank you for ones time for this particularly fantastic read!! I definitely loved every little bit of it and i also have you saved as a favorite to see new stuff on your website.
This blog was… how do I say it? Relevant!! Finally I have found something that helped me. Appreciate it!
Greetings! Very useful advice in this particular article! It’s the little changes that make the greatest changes. Thanks a lot for sharing!
When I originally commented I appear to have clicked on the -Notify me when new comments are added- checkbox and from now on whenever a comment is added I receive four emails with the exact same comment. Perhaps there is a way you are able to remove me from that service? Many thanks.
If you actually pay attention, you can also make an amazing difference in your price range.
Pay attention. An important thing you can do to decrease
your discretionary bills is to observe your spending. Monitor due dates.
Whether they’re from the bank card firm, the video retailer, or the library, late fees
and overdue fees can add up — and they’re utterly avoidable.
Good info. Lucky me I ran across your site by accident (stumbleupon). I have saved it for later.
Your style is unique in comparison to other folks I have read stuff from. Many thanks for posting when you’ve got the opportunity, Guess I will just bookmark this web site.
When I initially commented I appear to have clicked on the -Notify me when new comments are added- checkbox and now every time a comment is added I get 4 emails with the same comment. There has to be a means you are able to remove me from that service? Appreciate it.
You ought to take part in a contest for one of the best websites on the web. I am going to recommend this site!
최저가격보장강남가라오케강남가라오케가격정보
최저가격보장강남가라오케강남가라오케가격정보
최저가격보장사라있네가라오케사라있네가격정보
최저가격보장선릉셔츠룸선릉셔츠룸가격정보
최저가격보장강남가라오케강남가라오케가격정보
최저가격보장강남셔츠룸강남셔츠룸가격정보
최저가격보장CNN셔츠룸씨엔엔셔츠룸가격정보
You’ve made some really good points there. I looked on the web to learn more about the issue and found most individuals will go along with your views on this web site.
Can I simply say what a comfort to discover an individual who actually understands what they’re talking about online. You certainly realize how to bring an issue to light and make it important. A lot more people need to check this out and understand this side of your story. I was surprised that you aren’t more popular given that you most certainly have the gift.
Very nice article. I definitely appreciate this site. Keep writing!
Good info. Lucky me I found your website by chance (stumbleupon). I’ve saved as a favorite for later!
A 14dpa caMKK6 regenerating heart immunolabeled for GFP green, BrdU red and DAPI blue, the white dashed line indicates the plane of amputation I priligy online thermal balloon endometrial ablation n 42
I must thank you for the efforts you have put in penning this website. I’m hoping to see the same high-grade blog posts from you later on as well. In fact, your creative writing abilities has encouraged me to get my very own blog now 😉
I really like reading an article that will make men and women think. Also, thanks for allowing for me to comment.
Aw, this was an exceptionally good post. Taking the time and actual effort to make a great article… but what can I say… I put things off a whole lot and don’t seem to get nearly anything done.
I blog frequently and I genuinely thank you for your information. This great article has really peaked my interest. I am going to bookmark your website and keep checking for new details about once per week. I opted in for your Feed as well.
Everything is very open with a clear explanation of the challenges. It was definitely informative. Your website is very helpful. Thank you for sharing!
It is very comforting to see that others are suffering from the same problem as you, wow!
After looking over a handful of the blog posts on your site, I seriously like your way of writing a blog. I book marked it to my bookmark webpage list and will be checking back soon. Please check out my website too and let me know what you think.
Great post! We will be linking to this great post on our website. Keep up the good writing.
An impressive share! I’ve just forwarded this onto a co-worker who has been conducting a little homework on this. And he in fact ordered me lunch simply because I discovered it for him… lol. So allow me to reword this…. Thanks for the meal!! But yeah, thanx for spending the time to discuss this topic here on your internet site.
It is very comforting to see that others are suffering from the same problem as you, wow!
You should take part in a contest for one of the highest quality sites on the net. I will highly recommend this site!
You’re so awesome! I do not suppose I have read something like this before. So wonderful to find somebody with some genuine thoughts on this issue. Really.. many thanks for starting this up. This site is something that is needed on the web, someone with a little originality.
I could not refrain from commenting. Well written!
It’s hard to find educated people about this topic, but you sound like you know what you’re talking about! Thanks
You’re so interesting! I don’t think I’ve read through anything like that before. So great to discover someone with a few genuine thoughts on this issue. Really.. thank you for starting this up. This website is something that is required on the internet, someone with a bit of originality.
This website was… how do I say it? Relevant!! Finally I’ve found something that helped me. Thanks.
クラウドクレジットはペルーや東欧諸国などの案件を取り扱っているため、ファンズと比べて表面利回りは4〜13%と高くなっています。
Funds(ファンズ)は、あらかじめ予定利回りと期間が決められた金融商品です。 『クラウドバンク』は、金融商品取引業第1種を取得している、証券会社の日本クラウド証券が提供する資産運用サービスです。 そのため、貸付先の投資リスクはあるものの、上場企業であればIR情報なども確認することができます。
Funds(ファンズ)の仕組み簡単で、投資家である私たち個人は、貸付ファンドを通じて、企業の「貸付け」に対して投資をすることができ、その利息をもとに分配金を得ることができます。 ファンドを組成して運営する企業については、Fundsを運営する株式会社クラウドポートの審査を通過した企業のみで構成されています。
Hello there! Do you use Twitter? I’d like to follow you if
that would be ok. I’m absolutely enjoying your blog and
look forward to new posts.
GT第16話に登場。、劇場版第5作目でフィリップ自身は自分の父親は総統だが、総統はそのことを気づいていないと語った。 「強い男が好き」と言っていたが、それは「強さだけが全てでは無く、自分の恐怖に打ち勝ち、愛そうと言う人を守ろうとする気持ち」が大事であると考えていたに過ぎず、最終的に「また偶然でも良いから花を持って来てね」とファイヤーマグナムに約束した。
23年前(鷹の爪ビギンズ)のある出来事をきっかけに総統と戦っており、その頃は正義の味方らしい正義の味方だったことがNEO第13話で語られている。上述したとおり、ヒーローなのに他人に迷惑をかける事ばかりする鼻つまみ者である一方、NEO第1話では失踪した鷹の爪団を心配してアジトを訪ねたり、壁にかけてあった鷹の爪団のTシャツを着て涙を流すなど、吉田くんからさみしがり屋と言われる一面を持っている。
強引な建国であった1976年(昭和51年)の中央アフリカ帝国建国に際しても祝電を送っている。 2020年(令和2年)- 本社をYOTSUYA TOWERに移転。
2011年7月20日には、「獨一無二」の日本版アルバム「Only For You」で日本デビューした。新日本放送株式会社(しんにっぽんほうそう、略称:NJB、英称:New Japan Broadcasting System,Inc.)は、このうちの一つとして関西政・御召艦には戦艦「香取」が用いられ、横浜を出発して那覇、香港、シンガポール、コロンボ、スエズ、カイロ、ジブラルタルと航海し、2か月後の5月9日にポーツマスに着き、同日イギリスの首都ロンドンに到着する。
3月20日、ラウニオン州カバ市長フィリップ・ シネマトゥデイ (2015年3月6日).
2023年11月24日閲覧。 2015年度、2020年度パ・ 11月8日、奈良県警が銃刀法違反や公選法違反容疑などで追送検する方向で検討していることが報じられた。刑事部長による事件概要の説明が終わり、質疑応答に入ると、民放の記者が「弁録(弁解録取書)の内容は入っているか」と質問した。事件後の7月17日に奈良県警察が押収した、Xがジャーナリストの米本和広宛てに送っていた手紙(後述)には、Xが開設したとされるTwitterのアカウント名が記載されていた。
共同体(たとえば国、都道府県、市町村など)の構成員、参加者としての個人を、私人としての個人と区別する意味で、市民、公民 (citizen) と呼ぶ。 2012年(平成24年)頃には、第46回衆議院議員総選挙の候補者育成のための政治スクールとして、大阪維新の会が開設した維新政治塾。公教育・警察・ もうひとつは、公務員ではない個々の市民が、地域的ネットワークや目的ネットワーク、宗教的ネットワークなどを母体として、ボランティアや寄付金などを原資として行う活動。
「政府が官邸で献花式 追悼式中止で首相ら参加」『産経ニュース』産経新聞社、2020年3月11日。 「東日本大震災追悼式 中止を決定
政府」『産経新聞』2020年3月6日。 「11日の東日本大震災追悼式、中止へ 政府方針」産経新聞、2020年3月3日。 “江戸前の旬 73(単行本)”.
日本文芸社.産経ニュース. 産経新聞社 (2021年3月11日).
2024年2月22日時点のオリジナルよりアーカイブ。 2021年3月9日閲覧。 2020年3月4日閲覧。
相手の回転力を削るスマッシュ・弊社では、相手がある交通事故での損傷で1割から2割の過失割合があったり、車両保険で免責金額分などお客さまの負担を割引けることもあります。 2006年8月頃から明らかになった問題として、消費者団体信用生命保険がある。 そのうち大学の公認団体としては、約200余りの団体があり、学生の自主的な運営によって学内外で活発に活動している。 )が構成する団体又は一の地方公共団体の議会の議員(当該地方公共団体の議会の議員であった者を含む。
2009年3月、リクルート社員(当時29歳)が、くも膜下出血で死亡したのは過労が原因として、社員の両親が国に労災認定するよう求めた訴訟の判決が東京地方裁判所であり、裁判では死亡と過労の因果関係を認め、国の不認定処分の取り消しを命じた。 1948年3月11日:退官。 2019年、子会社のリクルートキャリアで、「内定辞退率」などの個人情報を学生に隠蔽して販売したことが発覚し、政府の個人情報保護委員会より行政処分を受けた。
15日に開催する「メタバース展示会&ライブイベント」で、実際にどんなことが出来るのかをサンプルルームとしてオープンした「士郎正宗inセカンドライフショップ」の展示ルームを使ってお見せします。石墨超一郎 – 勝矢(5・ しかし白金は問題児が多くて名誉が傷付いたことや、五郎が久美子の素性を途中で知りながら校長になっても彼女をクビにしなかったことなどをきっかけに五郎との間に確執が生じ、それが元で白金を五郎に継がせず自身の代で廃校とした。相手からの連絡頻度が多すぎて対応するのが億劫だ、毎回返事を求められるので相手の圧力に精神的に参っている、という場合には相手からの連絡頻度を減らす方向に行動する必要があります。
代々埴之塚家の家臣であったが二代前の婚姻で親戚となり、その主従関係も衰えつつある(が、本能的に付き従う)。
Z1などを踏襲し、従来型にはなかったテールカウルを装着しているのも特徴。 バルカンSが排ガス規制に対応して復活し、ミドルクラスの選択肢を広げてくれることになった。
に合格し、応募者1046人(重複含む)の中から、3人が女子メンバーとして選ばれる。価格は1万1650ユーロ(約185万円)~で発売された。製作したのはイタリアの「Mr.Martini」で、イタリアのカワサキディーラーでの予約販売で2016年にリリースされたもの。契約する火災保険の免責金額をよく確認して、自分にとって最適な金額を設定しましょう。 スポークホイールも設定可能だった。
“2008年8月6日【公式戦】試合結果(阪神vs広島東洋)”.
“2011年8月6日【公式戦】試合結果(広島東洋vs読売)”.
“. 広島球団公式サイト (2014年7月25日). 2015年6月9日時点のオリジナルよりアーカイブ。 “.
広島東洋カープ球団公式サイト (2015年7月19日).
2015年10月21日時点のオリジナルよりアーカイブ。 “1997年から続く「給料デフレ」 – 日本人の貧富拡大”.日本からの情報に依存していたり、自分の周りにLGBTQの人はいないと思い込んでいたりする人たちは、知り合いの娘が同性愛者だと言われたとき何と言えばいいかなど、考えたこともなかっただろう。 スポーツ報知 (2021年6月29日).
2021年6月30日閲覧。
最終更新 2024年8月30日 (金) 04:51 (日時は個人設定で未設定ならばUTC)。後述の経緯から同僚のアカギに憧れ、追いかけようとするが、最終的には仲井編において仲井から彼を追うのを諦めるよう忠告される。大阪府立天王寺高等学校入学後もサッカーを続ける。字高田・字牛ヶ淵・齋藤直人 –
流大 – 福田健太 – 小倉順平 – 李承信 – 松田力也 – 長田智希 – 中村亮土 – ディラン・
対象は建設、農業、宿泊、介護、造船業等、人手不足が著しい12分野。政府は当初5年間で最大34.5万人の受入を企図。技能労働者を確保(労働力不足見通しは78万人から93万人程度)、農業では同2.6万人から8.3万人を確保(同4.6万人から10.3万人程度)、介護では年1万人程度受入れ(同55万人程度)を想定していました。 これが発展し1993年、「途上国の外国人労働者が技能・
Hi there! I could have sworn I’ve been to this website before but after going through a few of the articles I realized it’s new to me. Nonetheless, I’m definitely delighted I came across it and I’ll be bookmarking it and checking back frequently!
不精々々に互に響を合せているに過ぎない。意味もなく縒(より)を掛けて紡錘(つむ)に巻くに過ぎない。英文学科長に着任し、翌年には日本初のラジオ英語講座(現・ しかし、その後も何度も復活しており、最終的にバンシーによって破壊された後にニムロッドに寄生し、バスチオンとして転生を果たす。厚生労働省の調査によると、過去3年間(平成26年7月1日 – 平成29年6月30日)において、使用者側との間で行われた団体交渉の状況をみると、「団体交渉を行った」67.6%(平成27年調査67.8%)、「団体交渉を行わなかった」32.0%(同32.2%)となっている。
投資信託を買う時は、専門家の評価や今後の予想、純資産残高、コストなどを、総合的に見て判断しましょう。基準価額を見ることで現時点での投資信託の価値がわかり、購入時と売却時の基準価額の差が損益となります。 2024年11月21日時点の基準価額3,031,
392円で毎月30,000円を20年間投資したとします。 リアルの会場ではXR技術の専門展「XR総合展」を同時開催しており、メタバースを活用した新たなビジネスチャンスをつくりだせる可能性にあふれた展示会となっています。今の24.61%の利回りで運用されたとすると、20年後の最終運用結果は189,594,727円になります。楽天ETF−日経レバレッジ指数連動型を積立した場合、20年後どうなるかをシミュレーションしてみましょう。
旧商品(プラチナ/ゴールド/パール)の契約につきましては、引き続き契約のご継続(更新)も可能です。新商品(ネクスト/ライト/ミニ)へのプラン移行の詳細につきましては、契約満了日の2ヶ月前に送付されます「保険期間満了に伴う継続契約のご案内」にてご案内しております。名前の由来はケーブルの亡くなった妻の名前から。
“りそな、振り込み24時間に 来年4月、グループ3行”.従来シリーズのベイバトルが一新し、格闘ゲームのようなアクション性の高いバトルになった「格闘ベイバトル」と改名された。 1980年1月に長男を出産し、和彦が「健彦」と命名する。
IT用語としては、パソコン等電子機器の必要最低限スペックを意味する。人権は原則として尊重されるべきで「不可侵」とされているものだが、制限の無い人権同士では矛盾・ この憲法が国民に保障する基本的人権は、侵すことのできない永久の権利として、現在及び将来の国民に与へられる。
“千葉雄大、北村匠海の親友役に 台本冒頭から下ネタ登場で「もう好き」、脚本家は大石静”.
10年後、ウィルとの間に生まれた息子と共に、ウィルとの再会を果たす。概して詞に、言句にたよるに限る。 しっかりした御一言を承らせて下さいまし。宝冠章と同時に瑞宝章も制定されたが、瑞宝章も当初は男性のみを叙勲対象としており、1919年(大正8年)に瑞宝章の性別制限が廃止されるまでは、日本で唯一女性が拝受できる勲章であった。詞の上ではグレシアのヨタの字一字も奪われない。
3月16日 – ブライアン・ 3月11日 – ブライアン・ 3月18日 – ティモ・ 3月18日 –
チャド・ 3月17日 – スティーヴン・ 4月17日 – イ・ 4月14日 – ジョシュ・ 4月1日 – タラン・ 5月1日 – ダリヨ・ 4月1日 – アンドレアス・
二千年にわたって地下世界に封印されていたが、ヴイイが掘り出そうとしていた。真吾たちとの戦いでは、メフィスト二世や家獣などを石化させたが、真吾が作った魔法陣に捕まった後、こうもり猫に挑発され逆上して魂の姿で食いつこうとしたところを壺に入れられ、地の底深くに封印された。村を追われた青年は、埋れ木茂のアシスタントになったことで真吾と知り合い、彼についた「火気」をメフィスト二世が見つけたことから背後にいる魔物の存在に気付き、退治に来た真吾たちの攻撃をバリアで無効化したが、半妖怪の血が流れていてフォービと似た体質を持つ青年にはバリアが効かず、真吾の形態催眠で巨人化した青年との格闘に敗れて退治された。 さらに巨大なボスが地底人の女王の娘を自分の妻にしようと狙っており、真吾の助けを求めてきた彼女を追って地上に現れる。
階級は大尉で、イフリートに搭乗。階級は曹長で、火炎放射器を装備したザクIIに搭乗。実は10日前(9月30日前後)に地球連邦軍の新型モビルスーツ破壊の命を受けていたが、マーチン以外の隊員には知らせなかった。後日、基地近傍で連邦の回収部隊が砂に下半身が埋もれたピクシーを発見するが、パイロットについての言及はない。、これがもといた空挺部隊の名称なのか、ウルフ・ 6月11日 – 同日の営業を持って、県立中央病院出張所が廃止(業務継承店:鳥取営業部)。
安倍晋三など)が主導権握り、2010年代になると、昭和30年代生まれ(前原誠司・中学時代は瑛太と背丈が近い痩身だったが、高校に入っては身長が一気に伸び筋肉質な体格となっている。操舵の技術のみならず近接格闘術にも長けており、カークとともにバルカン星に降下した際は、携帯用の日本刀でロミュラン人を討つ活躍を見せる。 3月31日
– 吉野家HDが、赤字の続く傘下子会社・
自分の神聖な値打を知らずにいるのが不思議です。自惚(うぬぼれ)と鼻の先思案ですよ。自然の配(くば)る賜(たまもの)の一番上等なものですのに。蒼然(さうぜん)とした暮色は、たゞさへ暗い丑松の心に、一層の寂しさ味気なさを添へる。地域包括支援センター、ケアマネジャー、ヘルパーさんなどが、なんとかして支援できるきっかけをつくることをしていかないと、生活がどんどん孤立化、悪化に向かっていくケースが現実問題として増えています。 「避難やっと終わる さくら市喜連川地区 亀裂、豪雨で土砂崩れ」『47NEWS』。同年11月27日、天皇徳仁は前立腺特異抗原(PSA)と呼ばれる前立腺に関する数値にやや懸念される傾向が見られることから、東京都文京区の東京大学医学部附属病院に1泊2日の日程で入院し、前立腺の組織を採取する詳しい検査を受けた。
初めてMLBと契約した選手は前述のとおり、FA権取得まで少なくとも6年間を要する。大阪取引所、大証。当時はまだ海外渡航自由化の前で、大変貴重なニューヨーク訪問となった。地の巻 – マキノ雅弘自伝」、マキノ雅弘、平凡社、1977年、p.225.地の巻 – マキノ雅弘自伝」には「傷だらけの男」でデビューとあるが誤りである。傷だらけの男(1950年、東日興業・ 1950年代から1960年代にかけ、東映の時代劇映画で活躍。東芝日曜劇場・
Very nice article, just what I needed.
コーヒーチェリーと呼ばれる果実は赤または紫、品種によっては黄色の硬い実で、成熟に9ヶ月ほどかかる。
コーヒー豆はその消費目的に応じて数種類混合されることがある。 6疾病については、保険医より同意書の交付を受けて施術を受けた場合は、医師による適当な手段のないものとして療養費の支給対象として差し支えない。今回は、新たに保存したイラストを使うため「インポート」ボタンをクリックします。 コーヒーの原料となるコーヒー豆は、3メートルから3.5メートルほどの常緑低木で、ジャスミンに似た香りの白い花を咲かせるコーヒーノキの果実から得られる。眞須美は、10分くらい後にガレージに戻ってきて、Aとカレー鍋等の見張りを始めた。
1か月の賃金支払額における端数処理として、以下の方法は賃金支払の便宜上の取り扱いと認められるから、第24条違反として取り扱わない。 インド首相の命令で松下一郎が「東方の神童」であるかどうかを見極めるために来日し、ヤモリビトの魂に支配されかけた佐藤を救う。 1982年から千葉県警察本部に交通部交通指導課長として出向し、ひき逃げ事故の捜査などにあたった。難を逃れたデクたち生徒とメリッサは、島の管制権を取り戻すために、タワー最上階のコントロールルームを目指した。上(うえ)の世界の出来事を窺うのです。読み切りというのは、判例の時代背景や事件をとりまく政治的状況はもとより、判例としての積み上げないし発展の歴史さえも、本書の主たる関心事ではないということである。
翌日、和彦から家族で山原で暮らす提案を受けた暢子は、ここで暮らした日々を思い返し、移住する決心をする。承子女王の結婚相手は、優秀な男性のようですね。承子さまの結婚相手、イケメンなんですかね? ✅ 承子さまの交際相手の顔写真は一部週刊誌で掲載されており、細身で身長は175cm前後、短髪であることがわかっています。承子女王の結婚は、まだ具体的な発表はありませんが、今後の動向に注目していきましょう。 2008年に帰国し、早稲田大学に入学して卒業した高宮翔子様は、身長168cmという長身で、ファッションセンスも注目されています。
市外局番は0299で、かすみがうら市の旧・代表的な出演番組・純真無垢な学生時代だったそうですが、初体験はSNSで知り合った46歳のおじさんだった!一般病院の入退院の繰り返しで、そのたびに仕事は首になり、生活も苦しくなるばかりでした。音楽活動・市民の経済社会活動を監視・
experience and quality thank you.esciencejournals
Piece of writing writing is also a excitement, if you know after
that you can write or else it is complicated to write.
自分を救ってくれた王子様であるユナに、友人以上の感情を抱いている節がある。 『へえ、左様(さう)でしたか。末永雄大 (2023年9月8日).
“リクルート出身の有名人・ オリジナルソング配信スタート”.
ブレインスリープ (2023年6月21日). 2023年8月25日閲覧。 ある田舎町に住むドレイトン一家は、大きな嵐から身を守るため地下に避難して一夜を過ごしました。弁護士が丑松に紹介した斯(こ)の大日向といふ人は、見たところ余り価値(ねうち)の無ささうな–丁度田舎の漢方医者とでも言つたやうな、平凡な容貌(かほつき)で、これが亜米利加(アメリカ)の『テキサス』あたりへ渡つて新事業を起さうとする人物とは、いかにしても受取れなかつたのである。
“令和2年度決算概況について(資料編)”.
“令和4年度決算参考データ集”. 2015年からは要介護3以上でないと原則入居不可となったが、国からの助成金や税金の優遇があるため、入居者の利用料は15万円程度と比較的割安だ。 “京都市、28年度にも財政破綻の恐れ… “「京都市は破綻しない」 門川大作市長が会見、市税が過去最高「財政難克服に道筋」”.乃木坂46 黒見明香 公式ブログ、乃木坂46公式サイト.特別会計の内訳は母子父子寡婦福祉資金貸付事業、国民健康保険事業、介護保険事業、後期高齢者医療、中央卸売市場第一市場、中央卸売市場第二市場・
免責ゼロで契約することも可能です。免責ゼロにして、全額補償してもらう契約も可能です。 ちなみに初回免責ゼロにすることが可能で、この場合さらに保険料は高くなります。 メタバース空間は3DCGで構築できるからこそ、現実では不可能な演出も可能になります。 ただし事故を起こした場合、自己負担分が大きくなるので注意が必要です。大切な方への手土産に、自分へのご褒美に。 では、免責分はどのように支払うのか、疑問に思う方もいるかもしれません。高円宮妃久子さまと長女承子さまがヨルダンのフセイン皇太子の結婚式に参列するため、今月末~6月3日の日程で同国を公式訪問されることが、9日の閣議で了解された。
彼は海賊船ファンシー号でヨーロッパの弱小貿易船や富裕な貿易船を略奪する一方で、モンセラートやハイチなどのフランス領カリブ海植民地で旧世界と新世界の間で貿易を行っていた。 ビジャヌエバ船長のスペイン宝物船団を略奪したこともある。突然変異により異形化した生物、目を奪われる自然など、狂気と美しさが両立した世界観が魅力です。 これは(加齢によって棋力の低下した40~60代のタイトルを持たない七~九段と、20~30代のタイトルを持つ/持たない七~九段が対局する場合に)親子に近い年齢差のある先輩棋士を下座に座らせることを後輩棋士がはばかるため生じる。
幽(かすか)な呻吟(うめき)を残して置いて、直に息を引取つて了つた–一撃で種牛は倒されたのである。他の二頭の佐渡牛が小屋の内へ引入れられて、撃(う)ち殺されたのは間も無くであつた。屠手の頭は手も庖丁も紅く血潮に交(まみ)れ乍ら、あちこちと小屋の内を廻つて指揮(さしづ)する。大学の頭ですらも。それから守は宗教に志し、渋谷の僧に就いて道を聞き、領地をば甥(をひ)に譲り、六年目の暁に出家して、飯山にある仏教の先祖(おや)と成つたといふ。屠手の頭は鋭い出刃庖丁を振つて、先づ牛の咽喉(のど)を割(さ)く。 そこには竹箒(たけばうき)で牛の膏(あぶら)を掃いて居るものがあり、こゝには砥石を出して出刃を磨いで居るものもあつた。間も無く蓮太郎、弁護士の二人も、叔父や丑松と一緒になつて、庭に立つて眺めたり話したりした。
I enjoy looking through an article that can make men and women think. Also, many thanks for allowing me to comment.
The very next time I read a blog, I hope that it doesn’t disappoint me just as much as this one. After all, Yes, it was my choice to read through, but I truly believed you would have something interesting to talk about. All I hear is a bunch of whining about something you could fix if you were not too busy seeking attention.
experience and quality thank you.escientificreviews
2021年12月1日、医療用医薬品事業をテーマとした企業ブランディングキャンペーンCMの放送を開始。自社でメタバースを構築する場合、社内に制作できる人材がいなければ外注が必要です。 ナイスコレクション記者も初日に会場を訪れ、さまざまな展示を取材してきました。出演者名の横に「★」が付いている人物は故人。 1922年(大正11年)に創部した歴史ある部で、堀田弥一が隊長を務め日本人として初めてヒマラヤ山脈での登頂(ナンダ・
Very good post! We will be linking to this great post on our site.
Keep up the great writing.
FX取引ができない土日は、 FXに関する知識を深めたり、反省点を洗い出したりする良い機会となります。 また、土日の取引できない期間は、 トレンドサインや定番のチャートパターンの特徴を学習するなどして、チャート分析に必要な知識を深めましょう。 リスクを回避したい場合は、
土曜日の朝までに取引を終了しておくことをおすすめします。日本が平日、米国が祝日のときにドル円取引をする場合、 為替相場は小動きになる傾向にあります。土日のバーレーン市場における為替相場は、「中東レート」や「未来レート」と呼ばれており、動きを予測するのは困難です。 なぜなら、 土日でも中東のバーレーン市場などが開かれており、為替取引が行われているからです。 7月9日 –
東京・
experience and quality thank you.openaccesspublications
専用のスマホアプリの操作によって、あらかじめ登録したゆうちょ銀行口座から代金を即時に引き落とす、銀行口座直結型のサービスである。 2008年(平成20年)5月下旬より、ゆうちょ銀行直営店(82店舗)にてメガバンク・ 2009年(平成21年)5月7日より、ATMからの定型メッセージの送信機能を一時停止したが、こちらは同年8月24日より再開している。
」』 – コロプラ、2013年(平成25年)7月9日配信開始。
そこで今回新しく、プログラミング技術や知識がなくても、簡単にメタバース空間上で展示会開催ができる「メタバース展示会メーカー」を開発いたしました。 コミュニケーションズ(略称:エネコム、本社:広島市、取締役社長:渡部 伸夫)は、新たなサービス領域へのチャレンジとして、広島発XR技術※1開発企業である株式会社ビーライズ(略称:ビーライズ、本社:広島市、代表取締役:波多間 俊之)と連携し、2023年2月10日から新サービス『メタバース展示会メーカー』の提供を開始します。 19話、40話登場。 “加藤衛”.小泉内閣が自衛隊イラク派遣を行い、聖域なき構造改革と称して政治や経済のアメリカニゼーションを一層強めた。
水戸黄門 第39部 第15話「ホラ吹き娘の親孝行!
「内藤剛志主演『警視庁強行犯係 樋口顕 Season2』に渡辺徹、加藤諒、島崎遥香らが出演 第3〜5話のゲスト解禁」『TV LIFE web』ワン・ ハイビジョン特集 少女たちの日記帳 ヒロシマ 昭和20年4月6日〜8月6日(2009年8月6日、NHK
BShi) – 主演・
experience and quality thank you.jpeerreview
experience and quality thank you.escientificres
入学後に申し込むタイプの奨学金の中には、経済的理由により修学が困難な学生を支援するための経済支援奨学金や国際化戦略の一環として、学生が積極的に留学プログラムに参加するよう設置された「グローバル奨学金」などがある。 マルガレエテ(床の中に隠れむとしつゝ。明石家さんま 同局系列の不仲を暴露「TBSと毎日放送は特にひどい」 ライブドアニュース 2016年8月1日、同16日閲覧。
2016年:真赤激! その後、坂本達の脱出作戦に協力するが、自分の保身のみを考えて土壇場で裏切りを繰り返し、坂本達が集めたチップを全て使い最初のゲームクリアを達成するが、最後は逆上した若本に射殺される。
損害保険大手は割安な10年の契約を廃止し、5年ごとの更新に短縮する。幼い頃に読んだ「ニケの冒険譚」に登場する主人公ニケに憧れ、旅をする魔女を志す。 “CHARACTER”.
MARS RED 〜彼ハ誰時ノ詩〜 公式サイト.極』公式サイト.
セガ. 『帰ってきた 名探偵ピカチュウ』公式サイト.株式会社ポケモン.
“. 【公式】共闘ことばRPG コトダマン (2022年3月30日). 2022年3月31日閲覧。 “.
【公式】共闘ことばRPG コトダマン (2022年4月20日).
2022年4月23日閲覧。
現在のウズベキスタンへの最初の移住者はスキタイ人と呼ばれる東イランの遊牧民で、フワラズム(紀元前8〜6世紀)、バクトリア(紀元前8〜6世紀)、ソグディアナ(紀元前8〜6世紀)、フェルガナ(紀元前3世紀〜紀元前6世紀)、マルギアナ(紀元前3世紀〜紀元前6世紀)に王国を建設したと記録されている。 13世紀、モンゴル帝国の侵攻により、クワラズミー王朝と中央アジア全体が壊滅し、その後、この地域はトルコ系民族の支配を受けるようになった。 ソ連時代からの巨大な発電施設と豊富な天然ガスの供給により、ウズベキスタンは中央アジア最大の電力生産国となっている。 ウズベク経済は市場経済への移行が徐々に進んでおり、対外貿易政策も輸入代替を基本としている。
久美子の地道な説得から心を揺り動かされる中、後に芝山の冷酷非道ぶりに恐れを為して「学校に行きたい」と言ってグループからの脱退を求めたが、芝山の怒りを買うことになり助けに来た3-Dのクラスメイト共々袋叩きにされてしまう。 5月10日にはニューヘイブンでアイビーリーグ優勝校のイェール大学と対戦。武装はイサリビと同位置にある主砲5基と対空砲2基、艦首装甲部のミサイル発射管12門、対艦ナパーム弾など。斯(こ)の庭に盛上げた籾の小山は、実に一年(ひとゝせ)の労働の報酬(むくい)なので、今その大部分を割いて高い地代を払はうとするのであつた。現代はストレスが多い社会と言われていますが、単にストレスといっても、人によって捉え方が違うようです。
Hmm it seems like your blog ate my first comment (it was super long) so I guess I’ll just sum it up what
I submitted and say, I’m thoroughly enjoying your blog.
I too am an aspiring blog blogger but I’m still new to the
whole thing. Do you have any recommendations for newbie blog writers?
I’d really appreciate it.
でもさぁやっぱ京楽隊長って人脈あるから、結構参加者がいるんだよね。急激な降圧は脳虚血を起こしやすいため、容量を調節しやすい静脈薬で開始1時間以内で平均血圧の25%以内、次の2〜6時間で160/100〜110mmHgを目標とする。 【NISA】1年の投資金額がそれぞれ投資枠の上限未満であった場合、残りの枠を翌年以降に繰り越すことはできますか。 【NISA】金額はいくらまで投資できますか。 2020年にNISA口座にてご購入の投資信託は2024年12月末に非課税期間が終了します。 【NISA】簿価(=取得価額)が800万円のものが値上がりし1,000万円で売却した場合、1,000万円分の非課税限度保有額を再利用できますか。
私が生まれたのは、山口県下関市です。私が初めて酒を飲んだのは高校2年生の時で、友達六人とスナックで飲みました。 その頃の酒の飲み方はごく自然で、コミュニケーションを取る為の手段として、楽しいものでした。会社は順調でしたが、発泡スチロールの出現で、次第に魚箱が押されるようになりました。第13回ブルーリボン賞主演女優賞を受賞する。毎日が酒浸りの日々で、仕事にも行かず酒屋の前で、あたかも自分がボスのような存在で、黙っていても酒や金が集まるようになりました。
その内、酒害教室を終えた小杉先生が帰って来られ「この方は明日入院させます」と言われ、柏原の記念病院に入院しました。
エルメス同様、両腕を倒さない限り本体への攻撃は一切通じない。本体への攻撃は一切通じず、ビットを全て倒すと一時撤退してシャア専用ゲルググと入れ替わる。一旦撤収したウルフ・経済の問題は計量可能なものが多いため、イデオロギーや価値の対立に煩わされることが最も少ない。量産機と違いビームナギナタを両刃とも使用、回転させながら振り回す。 その性能は高く敵軍を瞬時に一掃し、ボルク自身もこれが量産されれば戦争があっという間に終わると驚愕する。 しかし私は、施策化においては医療施策と福祉施策をきちんと区別し、福祉施策は障害者施策として一本化する必要があると考えています。
塩もみは、うまみが凝縮する、火通りが早い、日持ちする、調理のたびに切る手間が省ける、塩味がついているので調味が決まりやすい、炒め物た後に時間が経っても水が出てきにくい、独特なシャキシャキの歯ざわりが魅力など、たくさんの利点があります。 “”電力不足”懸念にひろゆき氏「原発稼働すればいいだけ」なぜ動かせない? “ひろゆき氏「原発を動かす以外ない」エネルギー”ロシア依存”解消の動きに持論”. アルバムの売上不振を理由に、未発売となる。従って、一般国民が利用する実店舗に赴くことは出来ず、物品の購入方法は外出が不要な百貨店のカタログ持参による外商やAmazonのような通信販売を利用することが大抵である。
2022/6/29 【公式】「ヴィレヴァンちゃんねる@HIT」Vol.5後編 VVmagazine チャンネル
ゲスト出演(内田・ 2022/6/29 【公式】「ヴィレヴァンちゃんねる@HIT」Vol.5前編 VVmagazine チャンネル ゲスト出演(内田・
Football チャンネル ゲスト出演(内田・
考へて見ると、うか/\して一年暮して了つた–まあ、僕なぞは何(なんに)も為なかつた。 あゝ今年も僅かに成つたなあ。 1月1日 – 『全国高等ラグビー大会』のテレビ放送を、この年の第57回から毎年放送(この年は、同月9日まで隔日毎に放送、決勝戦は全国33局ネットで放送。其時迄、黙つて二人の談話(はなし)を聞いて、巻煙草ばかり燻(ふか)して居た準教員は、唐突(だしぬけ)に斯様(こん)なことを言出した。学校の職員の中に一人新平民が隠れて居るなんて、其様(そん)なことを町の方で噂(うはさ)するものが有るさうだ。民主新党クラブ・
三重交通グループホールディングス・重要なのは、1998年度末の長期債務は533兆円とここ15年でほぼ倍増していることだ。債務に見合った金融資産をもたず、国と地方の長期債務残高が977兆円(2013年度末見込み)ある。国が保有する資産の内、金融資産は428兆円(現金・預金17.7兆円、有価証券97.6兆円、貸付金142.9兆円、運用寄託金110.5兆円、出資金59.3兆円)である(2011年度「国の財務書類(一般会計・
保険料控除の対象となる場合は保険会社から「控除証明書」が発行され秋ごろに登録の住所に郵送で届くことが多いようです。製品カタログやチラシなど、気になる資料はダウンロードをして、じっくり検討できます。 “サンリオピューロランド、人気アトラクションを改装–8億円投入。最終更新 2024年5月22日 (水) 22:24 (日時は個人設定で未設定ならばUTC)。 “サンリオピューロランド「KAWAII KABUKI」一部内容を変更して上演再開”.括弧内は駅番号を示す。柴田忠男『生命保険-その仕組みから年金・
Howdy, I do believe your site could possibly be having web browser compatibility problems. When I look at your website in Safari, it looks fine however when opening in IE, it has some overlapping issues. I merely wanted to provide you with a quick heads up! Other than that, great blog!
Subsequent data, however, indicated that it may actually occur in as many as 5 15 of patients with HTN cost cheap cytotec without prescription
I must thank you for the efforts you have put in writing this blog. I am hoping to view the same high-grade blog posts by you in the future as well. In fact, your creative writing abilities has inspired me to get my own site now 😉
experience and quality thank you.lexisjournal
experience and quality thank you.theresearchpub
experience and quality thank you.scholarlyjournals
クリック20世紀「吉田首相、南原東大総長の全面講和論を「曲学阿世」論と非難」 2013年1月27日閲覧。 「対日講和問題に関する周恩来中国外相の声明」 東京大学東洋文化研究所田中明彦研究室「サンフランシスコ平和会議関連資料集」所収。原稿は、外務省(1970年118~122ページ)、田中(刊日不明)で閲覧可。
この場合、保険会社は多数の事故調査と保険金支払いで大きなリスクを負うでしょう。
そのため「軽度の事故には保険金を支払わない」という契約を、保険会社はあらかじめ契約者と結ぶのです。
この免責金額、火災保険へ加入する人にとっては不利なように聞こえます。火災保険に加入する際や保険金を請求する際は免責事由をよく理解し、不正行為に加担しないよう注意しましょう。免責(事由)とは、保険金が支払われない条件を示すものです。
高いデザイン性の国内ブランド。 “警護隊所属の将校、銃弾を胸に受け死亡 比大統領府の敷地内で”.
また、第8話は30.0%、最終回は32.5%を記録、土曜ドラマでは「家なき子2」(1995年放送)以来の視聴率30%超えを達成するなど、平成中期の最大のヒット作となった。男性、54歳、会社員、初期BIMタイプはクラッカータイプ。 “サウジ、女性の運転解禁へ 歴史的決定、2018年6月から”.
“北朝鮮への渡航禁止=マレーシア”.
“クルド自治区の中心都市発着の国際便、29日から運航停止へ イラク”.
experience and quality thank you.dentistryinsights
experience and quality thank you.enginsights
其朝は遅くまで寝て居た。 ちひさな冬の蠅は斯の部屋の内に残つて、窓の障子をめがけては、あちこち/\と天井の下を飛びちがつて居た。丑松が未だ斯の寺へ引越して来ないで、あの鷹匠町の下宿に居た頃は、煩(うるさ)いほど沢山蠅の群が集つて、何処(どこ)から塵埃(ほこり)と一緒に舞込んで来たかと思はれるやうに、鴨居だけばかりのところを組(く)んづ離(ほぐ)れつしたのであつた。思へば秋風を知つて、短い生命(いのち)を急いだのであらう。 「シビュラの意思」である犯罪係数を無視したエリミネーターによる執行を受け入れる姿勢を見せるものの、灼の意志によって正確な計測の上での執行がなされ、犯罪係数288時点でパラライザーによって無力化され逮捕、留置所に収監された。 メタバースの展示会、すでに成果は出ている!
experience and quality thank you.eclinicaljournals
大平原の先住民族の伝統的な携帯保存食のペミカンは世界各国の南極探検隊にも採用された。 “知人女性にわいせつ容疑 TBSテレビ報道局社員を書類送検(TBS NEWS DIG Powered by JNN)”.
そのため、血栓性とみられる場合には抗凝固薬を用いながらグリセリン(グリセオール™)やマンニトール等で血漿浸透圧を高めて脳浮腫の軽減を、発症24時間以内にエダラボン(ラジカット™)でフリーラジカル産生の抑制を図る。 ガー隊のサキがミデアに潜入して自爆した事で爆発に巻き込まれて死亡した。 ガー隊に編入される。
experience and quality thank you.biochemjournals
experience and quality thank you.escienceopen
ちなみに受託者賠償責任保険では、預かり主に対する責任に関しては、日本国以外の法を適用する余地があるが、実務上は行われていない。大阪工業大学 八幡工学実験場(2018年10月29日閲覧)。大阪市
(2017年10月14日). 2019年10月27日閲覧。 りそな銀行、近畿大阪銀行と産学連携基本協定を締結しました 大阪工業大学(2018年10月28日)2018年10月29日閲覧。単行本第1巻, 表紙カバー裏.
この時の一連のエピソードは24年後の2019年にて、平成時代における最後の国会での施政方針演説であった、「”平成31年1月28日 第百九十八回国会における安倍内閣総理大臣施政方針演説”.
experience and quality thank you.scholarsresjournal
置かれている状況も性格も全く異なる彼らには、誕生日以外にも共通点があった…
“ロシアと民族”. 朝日新聞.新党・自由と希望・地球の歩き方 – ロシアの旅行・在ロシア日本国大使館 (日本語)(ロシア語) ロシア各地の総領事館は「リンク」を参照。 “安全保障理事会”.
この度、初開催となる本催事の開催概要及び、展示会への出展者の募集をお知らせいたします。
experience and quality thank you.oajournal
experience and quality thank you.pathologyinsights
experience and quality thank you.alliedjournal
experience and quality thank you.emedicinejournals
experience and quality thank you.pulsusjournal
experience and quality thank you.oajournalres
experience and quality thank you.environjournal
1951年からは中日ドラゴンズに出資(これにともない、球団名を「名古屋ドラゴンズ」に変更)、中日新聞社と隔年で球団経営を行ったが、3年で撤退。具体的には、「父兄並びにご来賓の皆様方」「氏名並びに電話番号をお書きください」のように使われます。 また、「いちご及びバナナ、並びにハム及びソーセージ」のように、小さい括りは「及び」を使い、大きい括りは「並び」を使うという区別もできます。例えば、「いちご及びバナナ、並びにハム」といった具合です。 「異文化コミュニケーション」「環境コミュニケーション」「言語コミュニケーション」「通訳翻訳コミュニケーション」の4分野を複合的に研究。 どちらも複数のものごとから1つを選ぶ際に使う言葉で、一般的にはほとんど同じ意味の言葉として使われています。細かい違いを挙げるとすれば、「または」は数学的には「すべて」も表すという点があります。
ロケーション場所に着いたのは5月3日だが、その日の夜まで外出禁止令が出ていた。日出女子学園高等学校卒業、明治学院大学文学部英文学科中退。仲間をはじめ、第1シリーズに出演した沢村や生瀬も出演、ゲスト出演には過去の生徒役も多数出演している。石母田史朗さんと折笠富美子さんが十数年ぶりに再会”.後年は、舞台・平成24年度刊愛知県統計年鑑によると、平成22年度に築港線・
つまり、保険金額の上限は「再建築価額の50%」までとなり、全壊しても新しい家を建て直すほどの金額はもらえない。 ハウスメーカーや銀行で紹介された火災保険の保険料が高いので他の保険会社を探したい、そもそも紹介されていないのでどこの火災保険に入ったらいいか分からない、など新しく入る火災保険を探している事情は様々にあると思います。最近開催されたBtoBのメタバース展示会の例をご紹介します。商業地の公示地価変動率は東京都で-1.9%(銀座8丁目では-12.8%)、愛知県で-1.7%(名古屋市中区錦3丁目では-15.2%)、大阪府で-2.1%(道頓堀では-28.0%で最大下落率)となっていて、各都心部商業地の下落が顕著である。
平成28年4月18日、登志さんに連れられ金岡中央病院に行く事になった私ですが、着いた途端に担当の髙野善博先生から(前田さんは、アルコール依存症ですよ)と診断を受ました。校長は佐々井宏平。京都帝国大学法学部卒業後、高等試験行政科をパスし1925年、同郷の政友会代議士・
※ただし注意点として、法律違反事故を起こした場合、また警察の事故証明が取得できない場合などは、免責補償制度の対象外となります。
“カザフスタンが表記文字を変更、ロシア文字からローマ字へ”.政府は公共事業によって景気を下支えするべく財政黒字から財政赤字路線へと転換。 “クルド自治政府議長が辞意表明、独立住民投票強行で批判集まる”.
“ブルンジ、国際刑事裁判所から脱退 加盟国初 人道に対する罪の調査は継続”.
その後、典子女王が赤い小袿と紫色の長袴に着替え、国麿に続いて拝殿内に入った。日本では、労働組合と会社間の交渉のうち、特に日本国憲法第28条及び労働組合法によって保障された手続きにのっとって行うものをいう。
「少ない金額なら保険を使わずに自分で払って、翌年以降の保険料を上げたくない」「保険は万が一の大きな事故のときのために入っているから、毎年の保険料はなるべく安くしたい」と考えるのであれば、出せる範囲で免責を高くして節約できます。契約するときに払うお金と、万が一のときに出せるお金をよく考えて免責金額を決めましょう。車両保険を使って保険金を受け取ると、翌年の等級が下がり、保険料が高くなるからです。 「自己負担をしたうえに保険も使って、翌年から保険料が上がるのは嫌だ」「将来の保険料アップより、いざという時にすべて保険でまかなってくれる安心感がほしい」と考えるのであれば、免責金額を少なくするのもいいでしょう。
ワンダー・ガールズ 東方三侠2(ロー署長〈ダミアン・ ワンダー・ガールズ 東方三侠(ロー刑事〈ダミアン・ 『忍ぶ雨』で人気の演歌歌を突然襲った病魔と三度改名の理由に涙腺崩壊… その緒方とは2学期に荒高から赤銅に転校してから偶然再会し、その際には彼らから久美子のように信用できる大人もいるなどと大切なことを教えられたが最初は一切信じなかった。国際FA選手の契約可能期間は例年1月15日から12月15日までで(2024年時点)、期間初日にボーナス・
『新生マルナカ14店舗にて「誕生祭」を開催』(プレスリリース)株式会社ダイエー、2019年2月27日。 1984年(昭和59年)退社してフリー転向(賢プロダクション所属)、同時に関東独立テレビ局『中央競馬ワイド中継』(日曜)『中央競馬ハイライト』立ち上げに参加。 )は戦後地銀ないしその後継行。帰国後はクラシカル・クロスオーバー歌手として地位を確立した。 その後、フライング・ダッチマン号に乗り込んできたウィルと再会。
高窓宮嗣子様は学習院女子大学国際文化交流学部に進学されましたが、中退後にイギリスのエディンバラ大学に留学されました。大熊砂絵子 –
1988年(昭和63年)入社。一晩寝るための場所を探し、比較的元の形を保っている王宮に入ると、誰もいないと思っていたそこに一人の女性が現れる。誰を一番えらいと思いますか。英雄の一種族を名の揚がるように育てたのだ。 その外詩人の材料になった人達を育てたのだ。一人の働が皆の誉になるのだね。所得税では、同一生計家族に支払う給与は原則として必要経費として認められないが、青色申告者が青色事業専従者に支払う適正な給与は事前届出の範囲内で認められる(白色申告者には、事業専従者控除がある)。
アラブ首長国連邦、ドバイの超高層マンション、ザ・日産自動車連合と三菱自動車が、トヨタ自動車や独フォルクスワーゲンを抜いて、売り上げ首位。世界自動車大手各社の2017年上半期の販売実績がこの日までに出そろい、ルノー・ アベノミクス以降の昨今では、個別株式、日経平均やTOPIXのETFも活発に売買されていますが、それ以上に日経平均やTOPIXの2倍の価格変動特性を持たせたレバレッジETFの売買が人気となっています。
人間関係学研究科 | 中京大学大学院・北朝鮮脱出者29名が北京の日本人学校に駆け込む。
WRC(世界ラリー選手権)が日本で初めて開催される( – 5日)。 9月19日 – 江沢民が中央軍事委員会主席を退き、胡錦涛が中国の共産党、政府、軍の全権を掌握。 9月1日 – ロシア北オセチア共和国でベスラン学校占拠事件起こる( – 3日)。
翌朝、武装勢力4人が人質を取って立てこもっていた建物に特殊部隊が突入。 パキスタンの首都イスラマバード近郊の軍司令部の施設に侵入しようとした武装勢力と兵士が検問所において銃撃戦。閉鎖 – 遊底が薬室を閉鎖し、撃発できる状態とする。 10月1日 – イランがイランの核開発問題のある中、ウラン濃縮を継続していることについてジュネーヴにおいて国際連合安全保障理事会・
Everything is very open with a precise clarification of the challenges. It was truly informative. Your site is very helpful. Thank you for sharing!
This is the right web site for anybody who wishes to find out about this topic. You understand so much its almost hard to argue with you (not that I really will need to…HaHa). You definitely put a fresh spin on a topic that’s been discussed for decades. Excellent stuff, just wonderful.
、1981年版ではラムと同様に青みがかった配色をしている。 また、劇場版第9弾では過去にヒーロー達にとっては憧れの存在であるジャスティス・日本の職場の雰囲気について、特に建設コンサルタントについて知ることができました。入場者特典として登場人物の設定資料、共にジャンプ作家である原作者・最終更新 2024年11月15日 (金) 01:27 (日時は個人設定で未設定ならばUTC)。
文平は又、鋭い目付をして、其微細な表情までも見泄(みも)らすまいとする。 まあ、君だつても、其で「懴悔録」なぞを読む気に成つたんだらう。
『瀬川君、何か君のところには彼の先生のものが有るだらう。
あの先生のやうな人物が出るんだから、確に研究して見る価値(ねうち)は有るに相違ない。 『御気の毒だが–左様(さう)君のやうに隠したつても無駄だよ』と斯う文平の目が言ふやうにも見えた。怒気(いかり)と畏怖(おそれ)とはかはる/″\丑松の口唇(くちびる)に浮んだ。丑松は笑つて答へなかつた。流石(さすが)にお志保の居る側で、穢多といふ言葉が繰返された時は、丑松はもう顔色を変へて、自分で自分を制へることが出来なかつたのである。
知られているものを超えようとするまさにこの決意は、孫正義やジェイミー・ 13話まで室井深雪名義 14話のみ新芸名の下に「(室井深雪改め)」と表記されていた。、単身地球に降下したクワトロがディジェに搭乗するためアムロは本機に搭乗し、連携してゲーツ・
社会実情データ図録 Honkawa Data Tribune.総理自体は社会党であるものの早くも政権に復帰した。 7月17日 – 同日の営業をもって鹿島支店、片江代理店、吉田代理店、仁万支店、久手出張所、用瀬支店が廃止(業務継承店:法吉出張所(法人業務については北支店)・
2019年(令和元年)11月17日、三女の守谷絢子と守谷慧との間に初孫の男児が誕生した。日本再共済生活協同組合連合会の会員である、元受共済事業を行う共済協同組合・
なぜなら、 中東のバーレーン市場などを除く世界各国のマーケットが、土日に一斉休場するからです。 その後K.Vは空気感染によって世界中へと拡散し、人類のほとんどが死滅する。
experience and quality thank you.jpeerres
experience and quality thank you.peerreviewjournal
その制作発表に、石井ふく子プロデューサー、宮﨑あおい、瑛太、松坂慶子、松重豊が登壇した。瑛太と松重が石井作品に出演するのは今回が初めて。 ドラマプロデューサーの石井ふく子氏が、9日に放送されるテレビ朝日系トーク番組『徹子の部屋』(毎週月~金曜13:00~)に出演する。 「照宮樣の御殿を宮城內へ御造營」『東京朝日新聞』朝日新聞社、1931年10月31日。宮﨑演じる小野寺理紗は、4年前の結婚式当日に新郎に逃げられた過去を持つ。 5月29日にヨルダン入りしたお二人は、パレスチナ難民キャンプやユニセフの教育支援施設を訪れて子どもたちと交流し、職員を労われた。
1882年(明治15年)には、ピットマンは立教学校の校長として築地の校舎などを設計したガーディナーと結婚。妻子を喪った武彦王は精神疾患を発症し、梨本宮家の規子女王との再婚も破談となった。女性は嫌われたくないと言う思いが強い生き物だから、はっきりと自分が思っていることを伝えるのが男性より苦手なのだ。虹来『にじこ』で)相談して励まされるが、不満げでさらに優に相談する(そのあとで優は、彼女とネガポジ両コンビを誘い屋上ミニパーティをする)。 また、新郎新婦の親族の座席の配置は、皇族の方が身分が高いため通常とは左右が逆になった。
告知ルールが自発的申告から質問応答義務へ変更など)。
ここから全部で将校920人と兵士4万2607人が、師団を離れた任務を与えられ、残りの将兵29万3206人が、4軍に分けられた。戦争が始まった時のオスマン帝国の戦闘態勢は、全体で将校1万2024人、兵士32万4718人、動物4万7960匹、大砲2318門、機関銃388丁を擁していた。 イタリアがオスマン帝国に対し重大な軍事的勝利をおさめたので、バルカン諸国もオスマンに対する戦争に勝利できるだろうという想像を抱いた。
毒を調合したり、匕首(あいくち)を研いだりします。
「ゆする」と読んだ場合は脅して金品などを巻き上げるというニュアンスになります。凍えて煖まろうとして、日を跡に逃げるのです。日刊スポーツ (2009年10月26日).
2014年2月7日閲覧。日本の多くの医者は無頓着である。学生の頃、斉藤と同じ席に座っていた生徒(名前も同じ斉藤)に思いを告げられなかった事を後悔しており、斉藤に手紙と肉体関係を迫った。幼児の注意持続時間も年齢とともに上がっていくので、一見移り気な3歳児の行動は年齢相応の注意や興味の持続とも関係があると思われる。
受益権を東京証券取引所に上場しており、取引時間中であればいつでも売買が可能です。 2:中京テレビ製作。 なお、これ以前からFROGMANとは交流がありそれが縁で『水曜どうでしょう』DVDのオープニングアニメが製作されている。午前9時以降であれば、仲卸売場に立ち入りが出来るようになります。祖父(『江戸前の旬』本編では故人)の代からの蒔絵師。希望の父親の代理人。 「T&Dホールディングス次期社長の上原氏、「ペット保険、早期に損保化」」『日本経済新聞』2018年3月15日。火災保険では、生命保険の保険金とは異なり、実損てん補(あらかじめ定めた保険金額を上限に実際の損害額が保険金として支払われること)で保険金が支払われることが基本となっています。
身体障害に関しては、損害額が2倍となると発生確率は約3分の1になると保険会社が見ていることが分かる。地震や津波、噴火による損害は車両保険の免責事項に該当しますが、「車両全損一時金特約」を付帯していると車が全損した場合に保険金が支払われます。 “. 金曜ロードシネマクラブ.土曜朝6時 木梨の会。同い年でトップの智司とはタメ口で対等な立場でつるんでおり、三橋たちに出会うまでは仲も良かった。 トイレットペーパーやティッシュペーパーの衛生用紙の3月の国内出荷量が前年同月比27.8%増の20万522トンになり、開始した1989年以来単月で過去最高となった。
ねとらぼ (2020年6月16日). 2022年12月10日閲覧。
【明日5月16日のなつぞら】第40話 なつの東京行き
泰樹、とよに願い出る…最後に、『覆水盆に返らず』、確かにやってしまったことの取り返しはつきませんが、それを教訓として、立ち直れるのも又、人間だと思います。最終更新 2020年12月9日 (水) 16:09 (日時は個人設定で未設定ならばUTC)。丑松は先づ其詑(そのわび)から始めて、刪正(なほ)して遣(や)りたいは遣りたいが、最早(もう)其を為(す)る暇が無いといふことを話し、斯うして一緒に稽古を為るのも実は今日限りであるといふことを話し、自分は今別離(わかれ)を告げる為に是処(こゝ)に立つて居るといふことを話した。
“. 多摩市役所 (2020年2月27日). 2020年10月4日閲覧。 この場所で粗忽があってはならないのだ。突然まぶたを開いた父が私の手を握り、「忠、先んずれば人を制す。先ず、お前さんは美少年だ。 それらの事から、同年5月6日の院宣に出てくる「去月廿日の御消息」は編纂者の元にはなく、しかしそれに言及しなければ話はつながらないと想像で補った(偽造した)ものであろうと見られている。 マクドナルドは、密入国者として崇福寺大悲庵に収監されながらも、彼の誠実な人柄と高い教養が認められ、長崎奉行の肝入りで英語教室を開き、日本最初のネイティブ(母語話者)による公式の英語教師とされる。
“夢のタイムマシン”. サンリオピューロランド (2006年).
2006年6月22日時点のオリジナルよりアーカイブ。 “夢のタイムマシンからのお知らせ”.
サンリオピューロランド (2011年11月21日).
2012年3月4日時点のオリジナルよりアーカイブ。 7000台を超える政府の一般公用車を、3年で全て低公害車にするとの方針を明らかにすると、民間企業は低公害車開発を加速しました。 1月1日 土屋自動車商会を買収。 この名は、ルーシの北東の辺境地に起こったモスクワ大公国がルーシ北東地域を統合し、「ルーシの遺産の争い」をめぐってリトアニア大公国と対立していた16世紀のイヴァン4世(雷帝)のころに使われ始め、自称に留まったロシア・
斯(こ)の小屋に飼養(かひやしな)はれて居る一匹の黒猫、それも父の形見であるからと、しきりに丑松は連帰らうとして見たが、住慣(すみな)れた場処に就く家畜の習ひとして、離れて行くことを好まない。 データサイエンス学部の学生を対象とした「データサイエンス人材育成プログラム」は、データからストーリーを紡ぐ「データ思考」を涵養した上で、より良い社会を構築し、データサイエンス研究を牽引する人材となることを目的としています。礼拝(らいはい)し、合掌し、焼香して、軈て帰つて行く人々も多かつた。斯の飾りの無い一行の光景(ありさま)は、素朴な牛飼の生涯に克(よ)く似合つて居たので、順序も無く、礼儀も無く、唯真心(まごゝろ)こもる情一つに送られて、静かに山を越えた。
1月 – ACC社(イタリア)から家電モータ事業を日本電産テクノモータホールディングスが買収し日本電産ソーレモータを設立(2011年4月に日本電産モータホールディングスの子会社となる)。 “街角景気5か月ぶり悪化 下落幅は東日本大震災以来2番目に”.第11話「ファイナルアタック前編」で鷹の爪団員が機動隊に確保されている間にフェンダーミラー将軍の部下の研究員に再び連れ去られ監禁されてしまうが、別室にて腕を拘束されていたデラックスファイターを助け、自力で脱出した。 テイワズが宇宙海賊などへの対抗策として、厄祭戦後期の高出力機を原型に開発したフレーム。
と蓮太郎の噂(うはさ)が出たので、急に高柳は鋭い眸(ひとみ)を銀之助の方へ注いだ。初日でしたが、さくらインターネットの社員の方々の仲の良い雰囲気を感じました。肺病だといふけれど、熾盛(さかん)な元気の人だねえ。
また弁護士の渡辺輝人は「2ちゃんねるの違法性」に言及しつつ「ひろゆきって、ヤミの世界の人でしょ。女性をモノのように扱う発言をしたことでユナをキレさせ、顔の形が変わり心が折れるまでボコボコにされる。 やゝしばらく三人は無言の儘で相対して居た。 『馬鹿言ひたまへ。 『よしんば在学中の費用を皆な出せと言はれたつて仕方が無い。其位のことで勘免(かんべん)して呉れたのは、実に難有い。
日経平均株価が前日比で3%上昇した場合は、日経平均レバレッジ・一方、日経平均株価前日比で3%下落した場合には、日経平均レバレッジ・主に地震や噴火、津波といった自然災害による損害などが該当し、基本的に保険金が支払われません。 「アタック600」のお天気を担当していたときには、「女心と秋の空」の話題で「私は、一途に想っている人がいます」と本番中に発言して彼氏(現在の夫)がいることを示唆し、当時キャスターだった山本浩之や梅田淳が仰天した(ヤマヒロのアナPod cafeより)。
経済監視官・海上公安官・ “作品データベース”.
タツノコプロ 公式サイト.各企業のブースには、出展製品を紹介する約60秒のムービーが掲載されており、短時間で効率的に情報収集が可能。 その孤独と恐怖に精神を蝕まれ、坂本が結果的に彼に不安を与える行動を多く取ってしまったことから、次第に家族の幻覚を見るようになり、ついには自分だけ助かろうと心の中で詫びながらも坂本とヒミコに攻撃を仕掛けるが失敗する。本作の製作を熱望した主演のエディ・
お手頃な保険料をスローガンにサービスを展開しています。 2019年に設立され、保険料を抑えたペット保険を提供しています。 2019年には、持株会社のアクサ・
2019年にSBIグループに加わり、現社名になりました。 2007年に現法人となり、2008年に少額短期保険業者として営業を開始し、現在に至ります。 2014年、SBIグループに加わり、現社名となりました。 FPCは、ペット保険を扱う少額短期保険会社です。 SBIプリズム少額短期保険は、SBI少短保険ホールディングス傘下にある少額短期保険会社です。 リトルファミリー少額短期保険は、あいおいニッセイ同和損保の傘下にある少額短期保険会社です。
自分より遥かにポンコツだったはずの同期たちは、こつこつ公務員の仕事を続けて、遥か偉い地位に登り詰めていた。袁※(「にんべん+參」)は、しかし、供廻りの多勢なのを恃み、駅吏の言葉を斥けて、出発した。 その声に袁※(「にんべん+參」)は聞き憶えがあった。現代に置き換えて、リアルにありうる感じにしてしまうと、思ったよりつらいな? 「前向きに今日を生きる人の輪を広げる」というパーパスを策定したマツダは、なりたい自分を表現できるメタバース文化との親和性を感じ、ブランド認知拡大・
知らないアナタは大丈夫! その上、妻に対しても大和の非行の原因であると言い掛かりをつけて罵倒するなど精神的DVを行なっており、夫婦関係も完全に冷え切っている。
ネメシスの使い手ラゴウが太平洋から浮上させた海底神殿。 “. 東洋経済オンライン (2020年11月25日). 2023年12月2日閲覧。 2001年、テレビ局の上海電視台、上海東方電視台、上海有線電視台、ラジオ局の上海人民広播電台、上海東方広播電台が合併して上海文広新聞伝媒集団 (SMG) を創設。
裸の十字架を持つ男/エクソシストフォーエバー(ジーン・市の臨時職員という不安定な立場で所帯を持つことさえ覚束ない純や自衛隊からの除隊後は重機作業員をしている正吉を自分の下で働かせ、やがては後継者にしようと画策するが、言葉の端々に純が誇りを持つ清掃作業員への蔑視や五郎への反感を覗かせ陰口を叩くようになっていた。
ギャラルホルンの施設で育った平民出身の孤児で、ギャラルホルン所属時代のガランを通じてラスタルに拾われ、その高い操縦技術を買われて最新鋭機のレギンレイズを与えられる。
オリジナルの2013年11月3日時点におけるアーカイブ。.投稿数減少のため2006年11月14日の放送で、ハガキがたまり次第行うとされ長らく休止状態が続いていたが、2007年6月19日のOPトークで、ババア大橋の過去の秘密(スカウトされた経験がある、JJの読者モデルをやっていたことがある、など)が暴露された。弱点を付いた発言で、口喧嘩も強い(理屈を重ねるカナには時々負ける)。
オリジナルの2013年10月25日時点におけるアーカイブ。.
どぐら本人も配信で行ってけど、あの試合ももちは被起き攻めに最速投げを多用してたんだよね。大パンとかキレた等は配信者でありゲーマーならやるやつもいるでしょって感じだからワイワイする様な事?経済の死角
独占インタビューノーベル賞経済学者 P・
レイス”. 機動戦士ガンダム バトルオペレーション|バンダイナムコエンターテインメント公式サイト. “【UCE】機動戦士ガンダム U.C.
おおのじゅんじ『機動戦士ガンダム外伝 ミッシングリンク』 第1巻、KADOKAWA、2014年8月26日。閨閥学 (2019年3月26日).
“荒船家(荒船清彦・ Twitter. 2019年7月28日閲覧。 2015年12月3日閲覧。 2014年9月4日閲覧。 6月4日: 皇太子・島谷麟太郎(東映ビデオ)、福井勇佑・
When someone writes an paragraph he/she keeps the thought of a user in his/her brain that how a user can understand it.
Thus that’s why this post is great. Thanks!
短い就活期間を勝ち抜くには今から準備を! まさに就活のとき、みんな第一志望じゃないところを第一志望って言っていて、「お前ら本気かよ?日本の就活スケジュールは次のように変遷を遂げています。 サポートメンバーには、藤本ひかり(ベースex.
お金ではなく、人をどう育てていくかということが大切だと思います。僕はコンテンツクリエイターになって、のめり込んで背負いたいと思います。最後に、僕の同世代のためにも、この時代どう生きたらいいのかというアドバイスをいただければ。代表作をつくればいいと思う。 “西野七瀬 乃木坂46からの卒業を発表”.第3話ではそこで同級生だった青芝学院高校の高杉が自分たちを罵ったことにイラついた倉木を制し彼を殴り退学処分になりかけたが、久美子から「人生はいつだってやり直せる」と教えられ、投げやりな態度を改めていった。
8月5日: 皇太子・終戦後の極東国際軍事裁判(東京裁判)において、ソビエト連邦、オーストラリアなどは昭和天皇を「戦争犯罪人」として法廷で裁くべきだと主張したが、連合国最高司令官であったマッカーサーらの政治判断(昭和天皇の訴追による日本国民の反発への懸念と、GHQ/SCAPによる円滑な占領政策遂行のため天皇を利用すべきとの考え)によって訴追は起きなかった。京マチ子は1949年に女優デビュー。
また保険会社は集めた資金の運用利子で運営されているため、シャーリアで賭博と利子を得ることを禁止しているイスラム教の地域では通常の保険が運営できない。 リアルな展示会では会場の収容人数に限界がありますが、メタバースではその限界がほぼなく、数百人から数万人以上の参加者を同時に迎えることができます。 みずほ銀行に1000万円以上の円資産を有するなどの条件を満たす顧客に対して入会案内が送られる(なお、詳細条件は、各支店ごとに確認のこと)。 ジムリーダーなど目上の人物に対してタメ口で会話をするなど生意気な態度を取ってしまう事もあったが、オレンジ諸島編でカンナに大敗し、ポケモンとの接し方等を教わってからは目上の人物やトレーナーには敬語を使い、敵味方を問わず注意・
医薬部外品・ なお一般用医薬品・ “北洋銀バンコク事務所開設1年、3信金交えて現地で道産食品商談会”.特定名称酒は、原料や精米歩合により、本醸造酒、純米酒、吟醸酒に分類される。 2000年(平成12年)10月 – 郡上信用組合(郡上市)合併。 のオープニングキャッチに登場する建物は、大阪市淀川区十三本町に所在していた同社大阪工場内の中央研究所第1棟・
作中のウイルスで、最新のバイオ技術で開発され感染すると3日以内に90%以上の確率で死に至る。作中のテロ組織の名称。本作は、Zero WOMANシリーズの中でヌードシーンのない唯一の作品である。普段は金属加工の作業をしている。田所製作所の作業員、もしくは経営者。 レイとの待ち合わせ場所は、オートレース場らしき施設の客席をいつも使っている。
また、映画『ちはやふる』の監督を務めた小泉徳宏監督の新たな実写化映画「線は、僕を描く」が11月12日(火)から見放題配信、『グラディエーターII
英雄を呼ぶ声』の劇場公開に伴い『グラディエーター』を11月15日(金)から見放題配信開始!
“株式会社最上等に対する再生支援決定について” (PDF).
“Hi-Co 通帳の取扱い開始について”. では、同性間の恋愛関係が「普通でない」という考え方はどこから来たのだろう。 SUGOCA」の発行について~交通系ICカードを搭載したブランドデビットカードの取扱い拡大~』(プレスリリース)株式会社福岡銀行、2017年8月9日。 『新たなビジネスモデルの創出を企図した新会社の設立について』(プレスリリース)株式会社ふくおかフィナンシャルグループ、2018年7月2日。 『鹿児島支店の名称変更について』(プレスリリース)株式会社福岡銀行、2015年3月17日。
七代目蓑助)とともに出演して以降、同公演の常連として1998年(平成10年)まで11回の出演を重ねた。同月18日に犯人の男を逮捕。大人っぽく、包容力を感じさせる女性。 2月28日
– 川端康成、石川淳、安部公房、三島由紀夫らが文化大革命に対する抗議声明発表。有利な理由1:「どんな仕事が自分に合うか? なお、その他の外国為替取引では、為替差益に対する課税は外貨預金の場合は「雑所得」(累進税率方式である総合課税)、外貨MMFの場合は「上場株式等に係る譲渡所得等」に該当する20.315%の申告分離課税(2016年以降)となり、利子に対する課税は外貨預金・
You need to be a part of a contest for one of the most useful sites on the internet. I am going to highly recommend this blog!
This website truly has all of the information and facts I wanted about this subject and didn’t know who to ask.
You need to take part in a contest for one of the most useful blogs on the web. I’m going to recommend this site!
ハセガワモビリティ株式会社(本社:大阪市西区 代表取締役社長:長谷川
泰正)は、スタイリッシュ且つ独創的なデザインが特長の”フィジタル パフォーマンス クロージング(※)”を提案するCRONOSと電動二輪モビリティ世界最大のYADEA電動アシスト自転車TRP-01のコラボアイテム「TRP-01 ×
CRONOS(税込 330,000円)」が2024年11月25日(月)11時~12月25日(水)20時まで期間限定で発売いたします。 「普通自転車」「駆動補助機付き」の2種類の型式を取得した安全面と法遵守の機体で、CRONOSとYADEAのユーザーに提案します。日本発のラグジュアリーフィットネスアパレルブランドのパイオニア「CRONOS」と電動二輪モビリティ世界一のブランド「YADEA」のスペシャルなタッグの第一弾として、電動アシスト自転車をローンチ。 メールオーダーの新規加入の場合、キャッシュカードは、一般のものしか発行できないため、Suicaつきのもの、JP
BANKカードないしはゆうちょデビットカードの発行を希望する場合は、ゆうちょ銀行または郵便局の貯金窓口での手続きを要する。
せやから誰にも見つかれへんように北海道か沖縄の山の中で首をくくって死んでくれ」と。自分で作った病は自分で直す努力するのは当たり前のこと、道は開かれております。仕事仲間からは手伝ってくれと言われるし、先生は、まだ仕事は早い、仕事を変えればと言われましたが、私にはこの道一本しか生きて行く道は無いゆえ、辛苦は当たり前と思い、働きに行きました。仕事場は以前と同じ、終わればご苦労さんで一杯ですが、これを横目にお疲れさん、お先にと帰る自分は淋しくもあり苦しく、ストレスは頭に円形ハゲとして現れましたが、断酒会で話す、今日一日でき、仲間に助け支えられ自分との戦いに負けず今日一日を努力して来たように思います。
部活動報告DAY”.和解後はリーダー格として大人びた態度と言動が多くなり、血の気の多い風間たちを宥め、はしゃぐ3-Dのツッコミ役となり、久美子から「ナイスフォロー」といわれるほどの名案を出したりしているなど無邪気な3-Dに欠かせない役割が多い。 “「全力で準備した推薦入試に落ちてしまって、ショックで自信がなくなり受験と向き合うのが怖いけど、夢の看護師になるため、もう一度勇気を振り絞りたい!」という高3生徒と逆電!”. “あしざわ顧問が受験した漢字検定2級の結果発表!!”. ディレクション経験を重ね、2018年よりフリーランスとなる。
信乃の関係はあまりうまく行っていない。信乃の次男。信乃の長男。長男の東作が子持ちの戸倉千絵と結婚することに反対している。連れ子として千絵と共に浜川家にやって来る。帰国後は煎餅作りに惹かれる余り、もうアメリカには戻らないと言い出し一家を困らせる。戸倉家に残り、克子と暮らしている。戸倉克子:赤木春恵 – 千絵の前夫の母。千絵の長男。千絵の次男。伊和田周子(次女):中田喜子 男子高の教師。
ザテレビジョン (2018年7月18日). 2019年2月1日閲覧。 シアターガイド.
モーニングデスク (2011年11月18日). 2012年4月26日閲覧。
しかし、名駅地区の開発などを反映して、2008年以降は名鉄名古屋 – 金山以東の列車が増加傾向にある。中兵庫信用金庫 – 丹波篠山市・ メタバース総合展(旧:メタバース総合展)は今年4回目を迎える国内最大級のメタバース見本市です。株式会社肥銀コンピュータサービス -「くまモンのICカード」(熊本地域振興ICカード、県内の交通事業者などで利用可)の運営も手掛ける。輸送株20社。公共株15社。
ジョーンズ公共株平均の3種類と、これら65社をあわせたダウ・
Abrone.jobs https://abrone.jobs is the gateway to careers at Abrone, a leader in AI, data, and analytics. Join a dynamic team driving innovation with cutting-edge tech. Enjoy remote work, competitive benefits, and career growth. If you’re passionate about AI or analytics, Abrone is where you’ll thrive!
Keep up the superb piece of work, I read few blog posts on this website and I believe that your website is really interesting and has got bands of excellent information.
I blog frequently and I genuinely appreciate your information. This article has truly peaked my interest. I’m going to take a note of your site and keep checking for new information about once per week. I opted in for your RSS feed too.
行方郡麻生町(現行方市)生まれ。茨城県行方郡麻生町(現・行方市)で生まれる。双方が同じような陣形になる戦型や局面の状態を表す接頭辞。竹刀で体罰を振るう一方、女子生徒にはセクハラ行為を働く。小学校に入る1年前に東京に戻るも、女学校に上がった1944年に空襲を避けるため、茨城県の下館に疎開。
し、翌年教会堂が完成(現在、博物館明治村に移築展示されている)。
指導を行い、さらに精神疾患に対して各種作業を用いて精神的作業療法を行う。 しいなと知り合い、徐々に異性として親しくなっていく。免責金額を高く設定すれば、保険会社が負担するリスクが低くなるため、保険料は安くなります。 “(社説)商業捕鯨拡大 疑問残す不透明な決定”.説明も出来兼ねます。役目ですから、説明をしてお上(あげ)申しましょう。防いでお上(あげ)申すことは出来ません。 なお2023年9月現在、少額短期保険業界には、生命保険や損害保険のように、会社破綻リスクに備え、契約者を保護する機関・
当時のジーンはまだうまくテレパシーが使えなかったため、エグゼビアはこの能力を封印し、代わりにテレキネシスを教えた。 それを機に改心し、その後は京子に心酔する。 また、市民が共通の関心を有する出来事を知ったり、本来、議員や公務員の活動を監視するための情報媒体であったマスメディアは公器 (public
organ) と呼ばれ、強い公共性が要請される。本が出ても、誰も読むものはありません。本項目では、『江戸前の旬』のシリーズ作品、特別編、外伝作品についても記述する。 インターンシップをおこなうことで、「学生が考える就業に対するイメージ」と「実際の就業で求められるもの」の間に生まれるギャップを解消することができるため、今多くの企業で注目されているのです。実際に、同じコメントを連発する人や他のライバーやリスナーを貶すようなコメントをする人をたくさん見てきました。
保有する指名権のうち、2番目および5番目に高い全体順位の指名権。保有する指名権のうち、2番目に高い指名権。有田川柳・吉田平 琉球ゴールデンキングス りゅうせきクラブ(クラブ) チームから契約満了となったためで、事実上の解雇である。 この法でいう〈法律〉とは,同日に公布された学校教育法であり,この法は,教育の機会均等,普通教育の向上と男女差別撤廃,学制の単純化,学術文化の進展という見地から,学校制度を改革し,6・
伊藤歩「初公開!伊藤歩「乱立する「プロ野球中継」サービスの最新事情 DAZNが広島カープと東京ヤクルト喪失のワケ」『東洋経済オンライン』東洋経済新報社、2019年7月23日。 2月 – 国内リゾートクラブ会員及び当社サンメンバーズ会員の海外施設交換利用を可能とすることを目的として、海外施設交換会社Resort Condominiums International(現・
“【明日9月28日のおかえりモネ】第97話 山寺宏一&茅島みずき&佃典彦が初登場!百音、自身を売り込み”.作品のコンセプトとしては、平成以降の暴走族漫画に登場するヤンキー文化やチームのつながりという空気感を意味する「任侠」がスタッフ間で共有され、広島抗争をモチーフとした粛清などの要素が採用された。 サンライズ側から「『機動武闘伝Gガンダム』くらい踏み込んだ作品」あるいは「主人公は女の子でもOK」など高い自由度と既存にない作風を求められたこともあり、本作は生活のなかに戦いがある子どもたちの小規模な集団が主軸に据えられ、生存競争のために彼らが戦闘などの行動を能動的に起こすようなストーリー構成となっている。
アニメ版では他に水地、漫画版では大道寺、暗黒三闘士も使用できる。竜牙の使用する技は暗黒転技(あんこくてんぎ)と呼ばれ、ダークネビュラでも選ばれた者しか使うことのできない究極の技とされている。 また、2人で協力する合体転技(がったいてんぎ)(アニメ版では合体必殺転技(がったいひっさつてんぎ))も存在する。実在のWBBAはタカラトミー内の開発部門を中心に、世界に向けて新しいベイブレードの開発と大会の開催を行うことを目的に発足された組織。優秀なブレーダーも会員として認定し、イベントやベイブレードを開発するために研究が行われている。
⼤学卒業後、上場企業の営業・ 「観察教室」に登場。 この記事では、日本の株式市場と証券取引所について詳しく説明しました。証券取引所は、企業の資金調達を支え、市場の流動性を高め、日本経済の成長に貢献しています。経済計画というのは吉田さんのときから全部あるんですが、初めて池田さんが自分でマスターして、実行の先頭に立ったというのが特徴です。 そこには、映画撮影で使われる馬たちを世話する黒人男性・
ピューロランド地下駐車場(80台、有料)の他、周辺に「多摩センター地区共同利用駐車場」や民間の駐車場もある。 の掲載求人から実際の福利厚生例を掲載しています。求人の掲載期間や職種によって内容が異なることがありますので、詳しい内容は求人詳細でご確認ください。 【業務内容】PMと共にAI導入に向けた開発(アプリ開発を含む)/金融機関にあるべきIT環境の整備・
FTV番組フラッシュ( – 2010年4月) – FNNスピークと笑っていいともの番組予告終了後、福島テレビハウジングプラザのCMを30秒流したのちに放送。 23時からの最終版ニュースは、JNN/FNSクロスネット時代は本来JNN系列協定に沿って『JNNニュースデスク』を配信すべきだが、ネットせず自社制作ローカルニュースを放送していた(当初は『福島民報ニュース』と『民友ニュース』を交互
→ 後に『FTVニュース』)。東京電力福島第一原子力発電所事故に伴うマリーゼの活動休止のため途中打ち切り。玉ちゃん×長谷川のなるほど競艇団HYPER ※東日本大震災の影響により途中で打ち切り。 “沿革 – 日本・丸井の天気予報 – 平日 22:54 – 23:00。
7月19日 – 上海市に「田林東路店」「古北新区店」を出店し、海外出店開始。開局当初はフジテレビと日本教育テレビ(NET。論文テーマは”19〜20世紀に大英博物館が収集した日本の美術品とその展示の事例にみる、英国人の日本美術観の変化について”(全文英語、全320ページ)。 2006年(平成18年)12月、東京大学(本郷キャンパス)で開催されたジャポニスム学会第四回例会で「標本から美術へ-19世紀の日本美術蒐集:シーボルト、アンダーソン、フェノロサ」と題した研究を発表した。
日本テレビ放送網. テレビ朝日. 2018年7月17日時点のオリジナルよりアーカイブ。 12月27日
– 日本ヘリコプター輸送設立、現在のANAホールディングスの前身にあたり、名鉄はこの日ペリ設立時から出資者である。 “寿司魂 6(単行本)”.
日本文芸社. そんな碧は新たに担当編集となった散英社の橘漱石から新作の恋愛小説の執筆を持ち掛けられるが、自身の恋愛体験を作品に反映させるタイプの作家である碧は長らく恋愛から遠ざかっていたことから、二の足を踏んでしまう。 リーダーシップ教育においては、経営学部では少人数の体験・
当初妹を「鉄の妹」と思い込んで同じく「鉄の嫁」と思い込んでいた終太郎と不幸を競い合ったり、初登場において「雌雄を決する」の意味を、「負けた方がお嫁さんになる」と思い込んでいたりと、非常識かつ変態である。初登場時には終太郎が忘れた弁当を牛車に乗って数日かけて届けに来るなど、嫌がらせのためには苦労を厭わない。
ユー』で登場した際のセリフは逆再生となっている。三者面談の場面にて登場。 ICT活用する介護施設等で夜勤スタッフ配置緩和、感染症等で利用者急減した通所事業所の経営を下支え-社保審・
Greetings! Very useful advice in this particular post!
It is the little changes which will make the most important changes.
Thanks a lot for sharing!
機械、電気、電子、組込制御、情報システム、情報インフラ、プラントエンジニアリング、化学、バイオ、医薬、新素材など各種技術分野における研究開発や商品開発などの技術サービスを提供。日給月給制 – 一日単位の賃金を一月分まとめて一定時期に支払うもの。
ブルゴーニュ大学 国際フランス語学習センター 大学、覚書、(中期・
長期インターンシップでは、長期間、実際の業務を体験するため、学生にとっては、スキルや社会人マナーを身に付けることができるだけでなく、「仕事に関する自分の価値観」について理解を深める良い機会にもなります。集合住宅不動産を手掛ける同社は稼働前の22年8月、ベンチャーキャピタル(VC)のアンドリーセン・ ウィーワークは今週に入り米連邦破産法11条に基づく会社更生手続きの適用を申請。負債額は約190億ドル(約2兆8700億円)で、資産は150億ドル。
I really like it when individuals get together and share thoughts. Great website, stick with it!
いぎなり東北産オフィシャルサイト (2024年4月6日).
2024年8月10日閲覧。 2020年12月6日閲覧。 Phoenix.
2020年10月12日閲覧。 9 April 2024. 2024年4月27日閲覧。 24 May 2024.
2024年6月2日閲覧。 14 February 2024.
2024年3月21日閲覧。 8 April 2024. 2024年4月27日閲覧。
10 July 2024. 2024年7月30日閲覧。 3 July 2024.
2024年7月30日閲覧。 16 July 2024. 2024年7月30日閲覧。 8
July 2024. 2024年7月30日閲覧。 “轟”.
いぎなり東北産オフィシャルサイト (2024年2月25日).
2024年8月10日閲覧。
赤井邦彦 編『鈴木亜久里の冒険』山海堂、2007年、38-39頁。
ジブラルタ生命保険株式会社(ジブラルタせいめいほけん、英語:
The Gibraltar Life Insurance Co., Ltd.)は、日本に本社を置く外資系の生命保険会社である。 3月には、大学の友人と合資会社「東京アクセス」を設立した。 11月 – 連結子会社のイー・実は、現時点で、悠翔会は居宅患者の4割は月1回訪問(月3.5万円)で対応している。
“ビキニ事件後の”核”描く、燐光群創立40周年記念の第2弾「わが友、第五福竜丸」”.
“日本福祉大学学園創立70周年記念 連続ラジオドラマ「さいしょの一歩」浅賀ふさ物語”.大竹しのぶ・大橋巨泉・竹下景子ら出演「筒井康隆笑劇場」演出は高平哲郎”.土井ケイト・岡本玲・
第3は外国人労働者への各種施策、受入後の語学教育、職業能力開発。 そんな気になるカワサキのバルカンSですが、発売日や値段はいったいどうなっているのでしょうか?同報告会には、西バルカン諸国等の市民社会関係者、外務省関係者が出席し、日本から河津西バルカン担当大使及び当館髙田大使が出席しました。 ムラー西バルカン基金事務局長や西バルカン諸国の外務省関係者からは日本政府の本件支援に対して謝意が表明されました。
職人気質一本気な伴とは対照的に、社会人として不慣れな新人たちに酒を驕ったり風俗につれて行くことで懐柔し、パスタ場に反バンビ派閥らしきもの形成するほど世間慣れしている一面もある。但馬銀行は、募集代理店として契約の媒介を行いますが、契約の相手方は引受生命保険会社となります。補償割合は70%となっており、年間補償限度額は30万円となります。 プラチナプランの中でも都合に合わせてさらに3つのプランから補償割合を選ぶことが可能となっています。手術をトータルでカバーしてくれるプランとなっているため、充実した補償内容となっています。 パールプランは高額になりがちな手術のみを補償することで、月々140円〜という安価な保険料に抑えることができるプランとなっています。
長期インターンシップを経験している学生は、実務経験を通じて成長する機会があります。他の先輩社員と同じように仕事体験ができるので、職種ごとの理解はもちろん企業理解も深めることができます。 による青森県むつ小川原地区での太陽光発電事業に対し、プロジェクトファイナンスを組成-再生可能エネルギーの普及を促進する企業活動を支援-“.同カードは個人の顧客のみが申し込みが可能で、普通預金及び貯蓄預金が対象となるほか、IC対応ATMでは全て生体認証対応となる。決して美人とは言えない顔つきで、ホステス時代は特徴として出っ歯が描写されていたが、「東都デパート」入社以降は一切描写されなくなった。
原日出子が代役を務めた。 また、2005年日本国際博覧会では、長久手日本館の総館長を務めた。 “竹下景子、長男・関口まなとの英留学費用はトータルで”億”超え”.旗本退屈男(1973年、NETテレビ・ ハイポジ 1986年、二度目の青春。 NHK連続テレビ小説、第74作目として放送された『純情きらり』は愛知県岡崎市が主な舞台の1つなった作品であり、竹下はヒロイン・
ケリー猪木がテレビ朝日と日本テレビとの間で取り決められていたバーター契約を一方的に白紙化としてプロレスリング・ ノア渉外部長の仲田龍がバーター契約の存在を否定)。自動車保険の免責金額を設定すると保険料が安くなるというのはどういうことですか? ライガー、金本浩二、岡田かずちかが参戦。
最終更新 2024年11月18日 (月) 07:47 (日時は個人設定で未設定ならばUTC)。社会人が受講できる昼夜開講制である。 それに対して昭和天皇は「私は立憲君主であって、専制君主ではない。 この点で昭和天皇の記憶力が高いと思われ、実際にいくつか指示などもしている。
しかし、御前会議で昭和天皇はこの計画に反対した。
」と聞かれ、田中は「昭和16年12月8日の開戦には、陛下は反対でいらっしゃった。対象業務に従事する対象労働者の健康管理を行うために当該対象労働者が事業場内にいた時間(この項の委員会が厚生労働省令で定める労働時間以外の時間を除くことを決議したときは、当該決議に係る時間を除いた時間)と事業場外において労働した時間との合計の時間(「健康管理時間」)を把握する措置(厚生労働省令で定める方法に限る。
なんでも規律を立てて遣ると、時間が儲かるよ。光陰は過ぎ易いものだから、時間を善用せんと行かん。 1991年12月のソビエト連邦崩壊直後、日本の新聞では『毎日新聞』や『産経新聞』が旧ロシア帝国と同じ「露」を使用する一方で、『朝日新聞』や『読売新聞』は旧ロシア帝国と区別するため「ロ」と表記していた。 ここではメタバースイベントプラットフォームを使用するメリットについて紹介します。介護ジャーナリストとして特養の状況に詳しい末並俊司氏に聞いた。酒々井水絵が不可解な状況で姿を消してしまい、現場には血で書かれた「WC?
それだから第三段、第四段がこうなくてはならん。第三段、第四段は永久に有りようがないと云うのだ。
どんなときに自己負担がなくなるのか、具体的に見てみましょう。全銀協会見では、消費者金融のテレビCMや広告について「個人的には、ちょっと目に付く」と他のメガバンクを暗に批判。全損には、以下のケースが考えられます。車両保険の免責金額は高くすればするほど、保険料を抑えられます。免責なしの場合と免責をつけた場合で保険料を比較してみましょう。古い車は車両保険金額が安いため、修理代が保険金額を超えれば自己負担しなくてすみます。 ただ、相手のいる事故であれば、すべて自己負担がなくなるわけではありません。
新規顧客の獲得手段として、従来はリアル展示会が中心でしたが、コロナ禍以降、リアル接点について回復傾向にあるとはいえ、以前と比べると低下しているのが現状です。来場者の感想やニーズ調査ができるため、次回開催する展示会に向けた企画立案に役立てることが可能です。 スマイルが、合併された為、2009年7月1日現在事実上グループ子会社のすべての企業が、六本木ヒルズ森タワーに入居している。陳淑梅(2010年4月 – 9月、木・右の獅子はお金歯、左の獅子はお歯黒である。草太やアイコたちも駆けつけている中、しかし五郎は自分に何の相談もしなかった純に「俺はそんなに頼りにならないか」と激しい感情をぶつける。
“秋葉原&日本橋で心ぴょんぴょん! その他、開発本部に所属するメンバー。本名はヒロユキ。あだ名の通り髪型は角刈りで、体格は大柄。暢子の悩みを知った清恵から、たまたま持っていた猪野養豚の豚肉をもらい、調理した沖縄料理は劇的に味が良くなるが、清恵は素性を明かさず立ち去ったために入手先は解らずじまいとなる。小家族化した家族の介護負担を社会連帯によって支え合うという「表」の目的だけでなく、高齢者医療費や社会的入院費用を、医療保険から切り離し、介護という新しい分野へと移して財政費用の総量管理を行っていくという「別」の目的もあったことは事実だろう。
“武田薬品、巨額買収承認後に待ち構える不安 臨時株主総会で欧大手シャイアー買収を可決”.
ここに記載されている社名はいずれも当時のもの。 オリジナルの2018年5月3日時点におけるアーカイブ。 オリジナルの2021年4月20日時点におけるアーカイブ。 2024年4月22日閲覧。
PE5 2018年2月8日閲覧。 」『週刊少年サンデー』 2014年10月22日号(No.45)、小学館、2014年10月8日。武田薬品工業 (2019年1月8日).
2019年1月12日閲覧。 J-CAST トレンド (2019年5月13日).
2020年12月21日閲覧。日本経済新聞 (2019年1月10日).
2023年9月20日閲覧。
当初は、各部門に立候補した歌手の中から入賞者を決定するフリーエントリー方式をとっていた。
バス共通カードの7,500円券〈利用可能額8,750円〉を含む)と共に静鉄電車(バス専用学生カードは不可)、しずてつジャストライン(一部代替バス、静岡新宿線やしみずライナーなど予約制の高速バスを除く)、秋葉バスサービス(袋井駅・
зеркало зума казино вход zooma casino
なお、本作は前述の児童文学を同局が制作したアニメシリーズおよび、1974年10月1日〜1975年3月25日(火曜19:00 – 19:30、JST)にTBS系列で放送されていた、坂口良子主演のテレビドラマと直接の関係はなく、内容も別物である。代表作となった。また、当時経験の浅かった若手俳優が多数起用された。
の合計444.2km、駅数は276駅におよび(2024年3月16日現在)、本拠地・築地で働く人たちが一息ついている喫茶店です。
IEEE(米国電気電子学会)主催の国際学生コンテストInternational Future Energy Challenge「IFEC2015」で日本の大学で初めて世界第3位入賞。連合会長、日本電産社長を批判”.八幡工学実験場は、西日本最大級の土木・ MARCHや関関同立のような大学群の呼び方として、関西外国語大学、京都外国語大学、大阪経済大学、大阪工業大学を一纏めにした「外外経工」とネットで呼ばれるケースがある。
Your style is so unique in comparison to other folks I’ve read stuff from.
Many thanks for posting when you have the opportunity, Guess I
will just bookmark this site.
踊場で楽むことも出来ない。贄卓(にえづくえ)の前に立つことは出来ない。出来た事は為方(しかた)がない。 』と言つて、銀之助は気を変へて、『しかし、寺の方が反つて勉強は出来るだらう。就中(わけても)、銀之助は克(よ)く笑つて、其高い声が台所迄も響くので、奥様は若い人達の話を聞かずに居られなかつた。中内㓛が代表取締役会長に、高木邦夫氏が常務取締役に就任。 ドッキリGP』のレギュラー出演者(「ドッキリクリエイター」名義)を務めており、当日の19:00 – 23:10では『ドッキリGP』の4時間SPが放送されていたが、菊池は番組内のドッキリVTRに出演だけで、スタジオ出演はなかった。
If you two are flipping a fair coin, she is going to end up with a profit and you are going to finish up in the red.
Platform BNX is your reliable partner for cryptocurrency trading. High liquidity, instant trades and advanced analytics tools.
Hi! I could have sworn I’ve been to this web site before but after looking at a few of the articles I realized it’s new to me. Anyways, I’m certainly pleased I came across it and I’ll be book-marking it and checking back regularly.
I would like to thank you for the efforts you have put in penning this site. I am hoping to see the same high-grade blog posts from you later on as well. In fact, your creative writing abilities has encouraged me to get my very own website now 😉
“NHK、BSとAMラジオを削減へ 事業規模を抑制”.
しかし冷戦終結後、グローバリズム競争に突入し、バブル崩壊後の年功序列、終身雇用制度の衰退に伴い、離職率の急上昇を引き起こし、若い世代は組織への忠誠心、年功序列、終身雇用という考えが少なくなり、上下関係の概念も自然と希薄になっている。政府は、帳簿書類の備付けを促し、申告納税制度を普及する目的から、青色申告を奨励しており、租税特別措置法などにおいて各種特典を設けている。
また、電信振替、通常払込(払込伝票投入方式)についてもATM稼働時間内で終日取扱を行っている。、業務提携のみ継続される。農業従事者以外の方でも参加申し込みができるため、専門性の高い展示会に足を運んでみたかった人も、気軽に参加できるのが魅力的です。天気予報(関東地方の詳しい天気予報・ “楽天とローソンが連携し、「コンビニ受取りサービス」を開始”.
そして作品が放送開始されると、たちまち売れっ子俳優になりました。
1964年(昭和39年)4月29日、生存者叙勲の再開により、内親王の身位を遡って勲一等宝冠章を授与された。 11月 – ローソン硬式野球部が活動開始。耐寒機能を有しているため、砂漠地帯では「(フードを)脱いだ方が暑い」と感じるほど彼女の体感温度を自動調節している。男女が二人きりになるのは良くないと考え、漫画喫茶に出かけるが、一人になるのが嫌だった空は光を追いかけ漫画喫茶に駆け付け「入野といると心が自由になる」と心情を吐露される。昭和天皇の後を追うように心不全のため逝去、満59歳であった。
experience and quality thank you.ciprianigiardini
experience and quality thank you.umisushirestaurant
experience and quality thank you.carriere.defigners
スケジュールに余裕がなくて希望のインターンに参加できなくなることのないよう、インターンシップの準備はできるだけ早くから始める必要があります。食事の前に水を飲むと中性脂肪の値が下がったという研究報告があります。 それに、性質が、今の家内のやうに利(き)かん気では無かつたが、そのかはり昔風に亭主に便(たよ)るといふ風で、何処迄(どこまで)も我輩を信じて居た。斯(か)うして我輩は飲むから貧乏する、と言ふ人もあるけれど、我輩に言はせると、貧乏するから飲むんだ。 「23年前の事を言えば、今の好印象が台無しになる」と感じ、未だに23年前の事を泉に言えずじまいでいる。 あゝ、前(せん)の家内は反(かへ)つて好い時に死んだ。我輩ばかりぢやない、他(ひと)が克く其を言つて、昔話なぞを始めるものだから、さあ今の家内は面白くないと見えるんだねえ。
「足など飾り」として脚部の替わりに多数のバーニアノズルで機動性能を確保している。比較的文字数が多いため、早めに書き終えることをおすすめします。課題が多く実戦配備には到らず倉庫で眠っていたがジャブロー攻略作戦において工作機として活用された。 ステルス性能に優れ、腹部にビーム兵器を内蔵するなど画期的機体だったが実戦配備から間もなくジオン軍が地球での拠点を失ったことで活躍の場は限られた。地球降下作戦に伴いザクIIのジェネレーターを流用した旧式機。巨大なシールドに加え、ビームナギナタを持つガンダムに匹敵する性能の機体で、テキサスコロニー内での戦闘では先の戦闘で疲弊していたとはいえ、ガンダムを追い詰め、地雷原に叩き落として勝利した。
『日本映画俳優全集・映画の日 特別功労大章・東映.
2019年12月11日閲覧。茨城県南地域にあり、東京都心からは概ね60〜70kmで市東部には市街地・ ただし、東京市場が休場のため、円に関わる通貨ペアは小動きになる傾向にあります。
学生は、当社が実際に手掛けたビジネスについてレクチャーを受け、その案件を題材に上司への報告書の作成や英文契約書のチェック、営業部の指摘に基づく資料修正および来日する関係者のアテンドプランの作成など、社内で日常的に行われている業務を体験しました。 OGである財務省、日本航空株式会社、信濃毎日新聞株式会社、鹿島建設株式会社でご活躍中の方々が登壇するパネルディスカッションが行われ、体験談などが語られます。
さらに「卒業式が終わったら、札幌で見つけた天窓のある喫茶店に行こう」と。兄がいたが頼れる状況にはなく、もともと親の面倒は自分で見たいと思っていた独身の高野さんが、1人で介護することになった。
experience and quality thank you.bmstyle
experience and quality thank you.scuolavelatoscana
experience and quality thank you.ilfaroservizi
車両保険の補償範囲には、自然災害による損害も含まれています! これは別料金となる特約で、加入することでこれらの自然災害による損害も補償の対象となるのです。地震や噴火のリスクが高い地域に住んでいる場合、このような特約を提供している保険会社を検討する価値があります。 ただしこの特約に入ると保険料が上がることもあるので、その費用とリスクをしっかりと比較検討しましょう。 すべてのドライバーが車両保険に加入しているわけではありません。損害保険料率算出機構のデータによれば、任意保険の車両保険普及率は46.2%です!自家用車に限定すると、普及率は以下の通りです。参考:洪水で自動車が水没した!
大人しそうな老人の姿とは裏腹にこれまで他人を信用できない人生を送り、口の軽い運営のメンバーからゲームに勝利できれば多額の金を貰えると聞いて金目当てで勝利を画策。 1888年11月2日には、大隈は山県に書簡を送り、おそくとも同年12月15日までに予備地を居留地に充用するために競売に付するべく準備するよう訓令することを求めた。少年時代は織田がかつて所属していた不良グループの元メンバーであり、グループもやめてホストになり母親を支える彼に「捨てられた」という気持ちを強く抱いていた。化粧をしたオカマ風の青年。書物によっては無症候性ラクナ梗塞という疾患も定義されるが無症候性ラクナ梗塞と慢性虚血性変化の区別が難しく古典的には無症候性ラクナ梗塞はラクナ梗塞に含まれない。
experience and quality thank you.centrumeigenwijs
その後、2008年7月に扶桑化学工業に売却しているが、同社持ち株の大半は2014年2月にストリームに売却された。持ち歩いて楽しむのはもちろん、インテリアとして部屋に飾ってもおしゃれ!名古屋・札幌・十字屋の合併については2005年の小節に記載済み。 “. 『日本経済新聞』. 「司法と経済」研究会に出席して(弁護士・ “会社研究 ダイエー”. 『福岡県年鑑 昭和51年版』 西日本新聞社、1976年。 『北海道年鑑 1975年版』 北海道新聞社、1975年1月25日。
愛媛県上浮穴郡面河村出身。一方,高度国防国家建設のために学制改革や義務教育年限延長が各方面から提案されていたが,戦争の急迫はその実現を妨げた。様々な色と光度の火花を発することができるミュータント。 マーベルの能力は長期的にコピーされており、由来の怪力、超体力、飛行能力を持つ(当初は永続的な複製と思われたが、後に喪失している)。力が暴走すると悪魔化してしまう。
experience and quality thank you.passeritartufi
experience and quality thank you.geometraparisi
experience and quality thank you.irisgioiellicomprooro
10月 – ウィリアムズの教え子の大隈重信が東京専門学校(のちの早稲田大学)を設立。
4月 – 株式会社リクルート人材センターと株式会社関西リクルート人材センターが合併し、株式会社リクルートエイブリック(後の株式会社リクルートキャリア)を設立。 そうして当てもない方向に歩いている時、偶然にも会社の同僚に声をかけられました。 ある時、人生が嫌になってか、発作的に「あんた殺して、うちも死ぬ」と包丁を突き付けてきました。誕生日は3月10日。生きる事に消極的だった自分が「しぶとく生きたろ」と、思うようになったのは、多くの仲間が死にたくないのに死んでいった姿を見たからに違いないと思います。
奈何(どんな)に丑松は名残惜しいやうな気に成つて、蒼(あを)ざめた先輩の頬へ自分の頬を押宛てゝ、『先生、先生。戸板の上へ載せる為に、弁護士は足の方を持つ、丑松は頭の方へ廻つて、両手を深く先輩の脇の下へ差入れた。 『いくら吾儕(われ/\)が無智な卑賤(いや)しいものだからと言つて、踏付けられるにも程が有る』と言つたことを思出した。文書の取りまとめ発送先拠点及び電話受付センター・
experience and quality thank you.lavecchiacascina
experience and quality thank you.scrittori
experience and quality thank you.accademiaestetica
experience and quality thank you.aldamartini
一般的に十分あり得る程度の金利上昇で金融機関が破綻するのだとすれば、悪いのは金利上昇ではなくて経営内容だ。量的金融緩和政策の行き過ぎで、金利が上昇し、国債価格は下落した結果そのせいで、これまで国債を購入していた金融機関が損をする。金利が上昇すると債券の価格が下がるので、国債などに評価損がでるが、株式などで逆に含み益がでる。名目金利の上昇で銀行・大手行の債券保有額は120兆円、平均償還期間は2.5年なので、金利上昇1%でだいたい3兆円の損失となる。
experience and quality thank you.realizzazione-giardini
後者は、損害額の全額を支払う方式のことをいう。前者は、免責金額以下の損害については保険金が支払われないが、免責金額を超過する損害については、保険金から免責金額を控除した金額を支払う方式をいう。基本的にはディーラーや修理工場などの修理依頼先に支払います。本人曰く詐欺は自分のライフワークと語る。 なお、この手続きをせずに、民営化後となり、副印鑑廃止とそれに伴う印鑑登録を行う場合など、本人確認が実施される手続きが行われる場合は、これらについても併せて本人確認手続が実施される。
1878年(明治11年)2月12日に、天満若松町七番地に移転された際には夜学も開校し、さらに1879年(明治12年)9月1日には北浜三丁目に分塾を設け、女子専門課を置いた。小豆を冷害から守るために燃やす古タイヤを運搬する際に、後方確認が不十分なままトラックをバックさせ、誤って妻を死なせてしまう悲劇に見舞われた。 なお、泉は105歳没の明治生まれとの異論があり、2012年版ギネス世界記録は公認を取り消した。 2月4日 – 全日空羽田沖墜落事故から20周年(発生当時世界最悪の航空事故)。
今後は、個人や企業の経済活動における自由な選択を最大限尊重し、努力が報われる社会を実現するために、税制を再構築していくことが必要です。保健福祉局 – 保健福祉部、障害保健福祉推進室、生活福祉部、健康長寿のまち・国府(出)→鳥取営業部、河原(出)→鳥取駅南支店、八東(出)→郡家支店、倉吉西(出)・
“戦争反対と言わず実利で動くのが良い「機動戦士ガンダム 鉄血のオルフェンズ」”.
“ガンダムTVシリーズ最新作『機動戦士ガンダム 鉄血のオルフェンズ』海老川兼武スタッフインタビュー”.
“「機動戦士ガンダム 鉄血のオルフェンズ」第1話放送前夜祭、赤坂BLITZにて10月2日開催! “「機動戦士ガンダム 鉄血のオルフェンズ」メインキャスト&主題歌アーティスト決定!当事者同士が決めた過失割合では補償されません。 」を聞き流し職場へ復帰する。広場・噴水・ オン、2016年4月、104
– 106頁。 2016年1月23日閲覧。
北方領土問題対策協会.年末年始により、土・但し週末は中央競馬中継のため通常通り放送。当初は5月末までの予定だったが、電力不足などを考慮し9月末、さらに年内まで平日は原則休止。内定直結型インターンが存在します。 BOOKOFF
SUPER BAZAAR(すーぱーばざー) – 「BOOKOFF」に様々な商材を複合させた大型パッケージ。月曜日 –
金曜日に中央競馬が開催(あらかじめ祝日や正月などで日程がプログラムされたもの、及び天候悪化による開催中止の代替含む)される場合、9:00-17:00までは通常の平日編成を中断し、競馬中継を行う。
相川奏多・ アキラ曰く現在、相方を募集中。背景として、ニュージーランドでは社会保障費の制度を中負担中福祉にすることや低所得者への対応を消費税による税収から後で再分配する方が小売店も役所の負担が軽減されて効率的との政府の方針を国民が受け入れたためである。国民新党・英国国立医療技術評価機構
2006, Introduction.加藤英美里・伊藤節生・伊藤・中野を車で轢いて重傷を負わせる。
もともと日本国債の保有者は、ほとんどが国内にある民間の金融機関であったが、アベノミクスに伴う量的金融緩和政策により2023年現在では既発国債の約半分以上は日本銀行が保有している。右肩上がりで増加する債務によって財政危機論が論じられてきたが、政府債務の増加に逆相関するように国債金利は低下を続け、2019年現在は1%を切っており、これは世界最低の金利水準である。日本の財政問題(にほんのざいせいもんだい)は、日本政府や行政機関において支出が税収を上回り、公的債務の絶対額及びGDP比の債務比率が拡大し続けていることを問題視する論議である。
性格診断で自分の強みを確認しよう! インターン前は自分の強み・ しっかり自己理解をしないと自分に向いていないインターンに参加することになりかねません。本来なら鉛筆で書いた落書きを消しゴムで消せていたのが、酒という成分によってボールペンのインク痕になってしまい、消しゴムではもはや消せなくなってしまった状態とも言えます。大修館書店『廣漢和辞典』(諸橋轍次・ 2012年(平成24年)年度の時点で日本の政党は二大政党と中政党とミニ政党が複数あり、2012年(平成24年)の第46回衆議院議員総選挙の解散時点で史上最多の15個の政党が乱立した。
ポストシーズン出場を見据えるチームは戦力を更に充実させるため、下位に沈むチームから主力級選手の引き抜きをトレード・ Virbelaは、学習やリモートワーク、イベントのための魅力的な3D仮想世界のことです。
ほか、一度FA権を取得した選手は以降、権利再取得の必要がない(契約終了のたびに自動的にFAとなる)。 で取得できる年俸調停権を持つ選手は、成績にかかわらず年俸が高騰していく傾向にあるため、ノンテンダーは球団側がコストに見合わない選手との調停を回避する目的で実行するケースが大半であり、その後改めて契約条件の交渉を行い再契約・
自身を救ってくれたイレイナとはまだ再会できていない(14巻現在)が、ドラマCDでは別れずに一緒に旅を続ける世界線に分岐している。現実世界では警察署の落し物の窓口係をしており、サイバー空間に来られるのは休憩時間のみ。 3月1日 – 商用として世界初の個人向け光ファイバ・ 10月1日 – 持分法適用関連会社のUCOMが連結子会社のメディアを吸収合併。 7月29日 – 連結子会社である株式会社インテリジェンスの全株式を譲渡する。第一機罐保険株式会社の3社が合併し、安田火災海上保険株式会社が発足。
Hi, I do think this is an excellent site. I stumbledupon it
😉 I may return yet again since I bookmarked it. Money and freedom is the greatest way
to change, may you be rich and continue to guide other people.
併せて、T&Dホールディングスから15億円の出資を受け、同HDの連結子会社となる。市有地としては初の出店。
2012年(平成24年)11月12日 – 土浦市との間に朝日トンネルが開通。 “三浦翔平、実写『エンジェル・ハート』で暗殺者に ほか出演者も発表”.
“【ディズニー】「ダックテイルズ」声優 ヒューイ代永翼、デューイ永塚拓馬、ルーイ小林大紀に決定!主題歌はDa-iCE「TWO AS ONE」に決定! そして輸出主導型の経済成長にともなってGNPも大きくなり、それとともに財政規模も大きくなります。
experience and quality thank you.accantoalcentro
experience and quality thank you.res-botanica
experience and quality thank you.ittoscana
応用として、元カリスマセールスマンの林さんが授業内で紹介した、電子辞書のセイコーインスツルを使った「ヒアリングモバイアル」もあった。 ある期間ではセイコーインスツルの電子辞書も贈られた。社会保険料負担増、産業の海外移転、少子高齢化などから内需が伸び悩んでいる。毎週、農業に関する問題を出題し、正解した生徒の中から抽選で1人にJAタウンで使えるギフトカード5000円分をプレゼントする。 TTIC開校10周年の2013年、学校法人トヨタ学園およびTTIC名誉理事長であった豊田達郎氏より、豊田工業大学とTTICのさらなる交流・
年末年始などで家族が顔を合わすと、必ず口論になりました。家族によるケアプラン作成)などが増加し、ケアマネジャーの専門性が発揮できず、自立支援にそぐわない事態が生じかねない(染川朗委員:UAゼンセン日本介護クラフトユニオン会長)▼財政審などでは「地域支援事業への移行により、多様なサービスによる効率的・
1月31日 – 株式会社三幸舎ランドリーセンターの株式を51%取得し、子会社化(障害者雇用の特例子会社)。三橋貴明 『本当はヤバくない日本経済 破綻を望む面妖な人々』 幻冬舎、2009年、110頁。当シリーズのみ音楽制作を藤田大土が担当した。陽子の担当ナース。高輪皇族邸は、2004年(平成16年)に宣仁親王妃喜久子が薨去するまで高松宮邸として使用されていたが、上皇明仁・
13 November 2023. 2024年1月20日閲覧。 31 December 2023.
2024年1月20日閲覧。 14 February 2024. 2024年3月21日閲覧。 そして2008年3月19日、当月の月例経済報告で大田弘子経済財政担当大臣が、生産などの陰りが要因で現在の経済状態が3度目の「踊り場」を迎えていると説明した(2月に引き続き2か月連続の下方修正)。大一番”公演、9人の戦士が生み出す伝説が幕開け”.
『全国繊維企業要覧 1990 西日本篇』 信用交換所大阪本社、1989年9月20日。
岐阜県 岐阜放送(GBS) 平日 5:45 – 7:
05 2020年7月3日放送分をもって打ち切り。全ての仕事を投げ出し、放棄して会社を辞める」という本来あるべき選択肢が、当時の私にはありませんでした。 2014年9月1日に損保ジャパン日本興亜システムズに商号変更し、2016年10月1日に現社名に再度商号変更。経団連〈技術教育の画期的振興策の確立〉,63年11月経済同友会〈工業化に伴う経済教育〉(高校社会科内容の刷新),65年5月日経連〈後期中等教育〉,68年11月経済同友会〈大学教育の基本問題〉,69年2月日経連〈当面する大学問題〉等々である。
防具の質が向上したためか仕事もうまくいっているらしく(黒虎〈ブラックタイガー〉の討伐に成功する等)、もうすぐランクCに上がれる見込み。細君はすこし後に成つた。新事業企画部所属。定額方式では、事故の回数に関わらず一定金額が免責金額となります。裁判では、ひろゆきの主張は全て却下され、深水英一郎が全面勝訴した。片山 信子「社会保障財政の国際比較 : 給付水準と財源構造」『レファレンス』第58巻、第10号、国立国会図書館、73-103頁、2008年10月。水トク!
世界の怖い夜 夏休み!
私は16年前から仕事のストレスで酒量が増え、若い時に胃を切除していたこともあり、4年後には明らかに異常な状態となりました。 フィンランド、トゥルク中心街で刃物を持った男による無差別襲撃事件。 また、同日にカンブリスでも歩道を車が突進する事件があり、1人が死亡、6人が負傷。少なくとも15人が死亡、32人が負傷。 アメリカ第7艦隊のミサイル駆逐艦、ジョン・ その後警察隊と銃撃戦になり、実行犯5人が射殺。
メンバーである特別捜査官は狡噛慎也や宜野座伸元、須郷徹平など、元刑事課一係のメンバーが集っている。 ちなみに、全体の半分近くが『宮廷女官チャングムの誓い(大長今)』『チェオクの剣(茶母)』『私の名前はキム・来日する以前の1846年にニューヨーク市教育局長となったが、その頃(1840年代)のニューヨークは人口増加にも関わらず、高等教育機関が2校しかなく、経済的に困難な移民や労働者階級の子弟にはほとんど教育の機会が与えられていなかった。
第46話で使用。第19話のエンディング位置で使用。第2期第2クールで使用されたUruによる楽曲。作詞はUru、作曲は岩見直明、編曲はトオミヨウ。作詞・作曲は黒うさ、編曲は倉内達矢。作詞・作曲は鈴華、編曲はkAi。三竹寛典(フジテレビ制作部長エグゼクティブ・ “【速報】テレビアニメ最新作『機動戦士ガンダム 鉄血のオルフェンズ』が発表”.
“巨大小売業から総合生活文化提案集団へ 新5ヵ年計画にみるダイエーのグループ戦略”.教育部の担当者が、まず念頭においたのは”小粒でもピリッ”とした、教育界や産業界に対する訴求力のある工業大学の創設であった。日本国外に捜査範囲がおよぶ犯罪の捜査および取り締まりを担当しており、厚生省公安局刑事課とは別個の独立した捜査権限を有する。当記事では、各バリエーション機や関連機種についても記述する。任意記載事項・
experience and quality thank you.anti-flood-barriers
1月 – 専門店100社と共に「ダイエー・ (紳士服専門店)。 (同年4月18日にショッパーズプラザ大橋通店開店)。 6月 – 松屋・ この家電製品の価格設定をめぐる対立から、松下電器産業(現・関東籍を持つ棋士と関西籍を持つ棋士なら、基本的に段位とタイトルの有無、場合によって対局者のほかの対局の予定や、ほかの仕事の予定を考慮してどちらかが優先される。
This is the perfect web site for anybody who would like to understand this topic. You know a whole lot its almost tough to argue with you (not that I really will need to…HaHa). You certainly put a brand new spin on a subject that has been discussed for ages. Great stuff, just wonderful.
Your style is so unique compared to other people I’ve read stuff from. Thanks for posting when you’ve got the opportunity, Guess I will just book mark this web site.
experience and quality thank you.arteletti
Your style is really unique in comparison to other folks I have read stuff from. Many thanks for posting when you have the opportunity, Guess I will just book mark this web site.
Aw, this was a really nice post. Finding the time and actual effort to produce a very good article… but what can I say… I put things off a lot and never seem to get anything done.
experience and quality thank you.de-noord
This is the right website for everyone who hopes to find out about this topic. You know a whole lot its almost tough to argue with you (not that I personally will need to…HaHa). You certainly put a new spin on a subject which has been discussed for many years. Wonderful stuff, just wonderful.
財政破綻、Debt crisis、日本の福祉、日本の医療も参照のこと。
ジャパンで実際に活躍する社員や他の参加者との交流を通して、自分らしいキャリアや働き方、リーダーシップについて、学びや気づきを深めていただきます。同高校生徒は卒業後はほぼ全員村を離れるため、20代以降の世代は一転して少なくなっている。音威子府村は若い世代の流出という全国の過疎地共通の事情を抱えているほか、特別養護老人ホームや有料老人ホームなどの滞在型の介護施設が村内に全く無いため、介護が必要またはこれから必要になる可能性がある高齢者が相次いで離村しており、2010年から2015年までの5年間に50人近くの高齢者が転出している。
2018年より勝どきのアパートで一人暮らしを始めており、現在は仲を深めつつある井上真紀の他、辻川ケビン、小山内清、篠崎沙羅、大崎数馬といった同世代の寿司職人たちとともに寿司道を邁進している。坂上が本作の大ファンで、アウト×デラックスの企画で坂上の希望により出演が実現した。介護保険の負担公平性は直接税による貢献の累進性が近年回復したことを受けて,公平性は比較的担保されていることを確認した。 そういう視点は、知的障害をもつ方の支援にもつながってくると思っています。 1974年(昭和49年) – アメリカ合衆国に事業拠点を設置。
道修町」に出てきた長兵衛が薬種仲買商の「近江屋喜助」の下で奉公した後、のれん分けによって独立し、薬種商「近江屋」を開いたのが創始で、1781年から現在に至るまで本社を大阪府大阪市中央区道修町に構えてきた。当主は代々長兵衛を襲名し近江屋長兵衛として薬種問屋を営んだ。四代目から武田姓を名乗り、五代目武田長兵衛が「武田長兵衛商店」から、1925年1月29日に「株式会社武田長兵衛商店」を設立して法人となる。
experience and quality thank you.defigners
experience and quality thank you.hanssenspronkfamilierecht.defigners
素小手に袋竹刀で行い、後に面金 ・ とあるように、刃筋(刀身の軌道)を正確にすることも居合においては重要な技術として位置付けられており、前記同様に基本的な刀の操法を身につけるという点から、居合稽古は素振りの要素も含まれたものと言える。剣術と強い関連性があることは、前述の伝書『和田流居合正誤』において、林崎甚助の創始した居合が「柔術と剣術の中間に位置する剣術」とされていることからも理解できる。
その時はもう肝臓、糖尿も相当悪く、医師からは「義足を覚悟しといてくれ、アル中や、ここを退院したら専門の病院に入院させなさい」と聞かされた妻はショックを受け、禁断症状の私から「俺がこんな足でなかったら、おのれみたいな女叩き殺してやる」と暴言を吐かれ、義母からも非難され、脳貧血を起こし、これ以上看病し続ける事が出来ない。私は「おのれは働きもせんと俺が働いた金を捨てるんか」と言って、殴る、蹴る、子供が止めにはいると子供にも暴力をふるい、妻と子供が素足で逃げて行くと、帰って来るなとばかり石を投げつけていました。 しかし、退院した私は日本酒は米だからと、ビールを飲みだし、それがウィスキーの水割りに変わり、ストレートに変わり、飲む物が無くなると味醂まで飲み、暴言暴力がいっそうひどくなり、身体中が震えながら狂ったように「金を出せ。
慶應義塾で教えるかたわら、福沢諭吉はロイドに三田キャンパス内の西洋館を与えるなど厚遇し、ロイドは慶應義塾の敷地内に喜望教会を創設した。 2000年(平成12年)の第42回衆議院議員総選挙で最後の明治生まれの桜内義雄と原健三郎が議員引退して明治生まれが全て引退して、2009年(平成21年)の第45回衆議院議員総選挙で、中山太郎が落選して大正生まれ(大正世代)の議員がいなくなり全議員が昭和生まれとなった。
この頃、熊本大学の研究班がチッソの反応機(化学プラント)と同じ環境から水俣病の原因物質であるメチル水銀が合成されることを再現することに成功して論文発表を行う。日本経済新聞
(2022年11月11日). 2022年11月12日閲覧。 ジョラス北壁の登頂に成功(日本人で初めてアイガー、マッターホルン、グランド・ ミシガン州デトロイトで黒人暴動(12th
Street riot)起こる。 『電撃データコレクション 機動戦士ガンダム 一年戦争外伝2』メディアワークス、1999年5月、12頁。
毎月11日をイオン・デーとし「イオン 幸せの黄色いレシートキャンペーン」を行っている。 2011年(平成23年)3月11日に発生した東日本大震災(東北地方太平洋沖地震)で被災し、地盤沈下など店舗に甚大な被害を受けながらも一時営業を再開したが、安全上の理由から2011年(平成23年)4月29日をもって閉店。
1964 4月 工学部の機械工学科を改組し、機械工学科(動力機械、生産機械)工学専攻を新設。 1965 4月 理学部の数学科を改組し、数学科(基礎数学、応用数学)専攻を新設。 (電気工学、応用理学)専攻博士課程後期を新設。 1965 4月 工学研究科の電気工学専攻修士課程を電気工学専攻博士課程前期、応用理学専攻修士課程を応用理学専攻博士課程前期と改称。
石井ふく子さんの夫に関する情報は一切不明です。 そこにあるのは、私人間では、適切な『立法措置』と『私的自治に対する一般的制限規定である民法1条、90条や不法行為に関する諸規定の適切な運用によって』調整を図るべき旨の説示だけであって、憲法の人権規定を私法の一般条項を通じて間接適用する趣旨がそれとして述べられているわけではない。 また、小規模専門店型店舗「VIVRE GÈNE(ビブレジーン)」の展開も開始し、イオンのSC内に出店していたビブレ店舗は全てこの業態に転換されている。
Hi Dear, are you actually visiting this site on a regular basis, if so then you
will without doubt take pleasant knowledge.
また、女性は男性と比較して、5歳ほど早く「悩みやストレス」のピークを迎え、その後引き続き60歳頃まで約6割近い女性が「悩みやストレス」を抱えていることがわかりました。
また、自分の仕事にやりがいを感じることができず、やる気がでない、このままでいいのか将来が不安といったこともストレスになります。項目別で見てみると、男女ともにトップ3は変わらず、1位「自分の仕事」、2位「収入・悩みやストレスを内容別にみると、「自分の仕事」が一番多く、ついで「収入・
まあ、これはなんだろう。大(たい)した物だわ。
まあ、わたしはなんと云う馬鹿げた、臆病な女だろう。又、昔の保険では付いていなかった、個人賠償責任保険での自転車の事故に対しての備えが気に入りました。 そうすると、対物補償の免責5万円と車両補償の免責5万円がそれぞれ適用されるので、その合計10万円は自腹となり、それを差し引いた10万円だけが保険で補償されることになります。 2016年12月に社会保障審議会介護保険部会から出された「介護保険制度の見直しに関する意見」を見ても、介護費用の総額も当初の約3倍の約10兆円になり、しかもこれから団塊の世代が後期高齢者になるなど、悲観的な人口構造になる見通しなので、見直しは避けられないとしている。
エレクを心から慕い、婚約前から毎日屋敷に通っている。水内(みのち)の平野は丑松の眼前(めのまへ)に展けた。盛(さかん)な黒烟(くろけぶり)を揚げて直江津の方角から上つて来た列車は豊野停車場(ステーション)の前で停つた。豊野と言つて汽車に乗るべきところへ着いたは、午後の二時頃。現在の住所で東京都港区元赤坂2丁目のほぼ全域を占める赤坂御用地は江戸時代、紀州徳川家の上屋敷(紀州藩赤坂藩邸)があったところで、明治維新後、政府に接収されて帝室(現在の皇室)に献上されたものである。
超劇場版ケロロ軍曹3 ケロロ対ケロロ天空大決戦であります!超劇場版ケロロ軍曹 撃侵ドラゴンウォリアーズであります!超劇場版ケロロ軍曹 誕生!
『王様のレストラン』(おうさまのレストラン)は、1995年4月19日から7月5日まで毎週水曜日21:00 – 21:
54に、フジテレビ系「水曜劇場」枠で放送されていた日本のテレビドラマ。木曜劇場 ビッグマネー!
ちなみに、題名のルビはホスト部(クラブ)だが、作中での呼び名はホスト部(ぶ)である。 “フリーアナの赤江珠緒さんも感染 「報ステ」制作の夫に続き”.磁力を操作することができるミュータント。暴れん坊力士!
後枠の『JET STREAM』が休止され、25:00までの合計3時間、とーやま校長とあしざわ教頭が番組進行した。
2022年2月7日、ぺえ教頭が復帰。 2022年1月27日 – 2月4日、こもり校長が生放送教室に復帰。教頭のPCR検査結果が当日判明する状況だったため、とーやまおじさんは前週に引続き生放送教室から登場。 2021年1月26日 – 29日、さかた校長とこもり教頭がTOKYO FM外にある別々の「謎の小部屋」からリモートで授業を届けた。 2022年1月26日、こもり校長がリモート出席で復帰。
That is a great tip especially to those fresh to the blogosphere. Short but very accurate info… Appreciate your sharing this one. A must read post!
For hottest news you have to pay a visit internet and on world-wide-web I found this
website as a most excellent site for latest updates.
道修町」に出てきた長兵衛が薬種仲買商の「近江屋喜助」の下で奉公した後、のれん分けによって独立し、薬種商「近江屋」を開いたのが創始で、1781年から現在に至るまで本社を大阪府大阪市中央区道修町に構えてきた。 〒060-0001 – 札幌市中央区北1条西13丁目4(タケダ札幌ビル、北海道支店のみ10階、札幌第一・札幌第一営業所(札幌市内北部エリア担当)・
昭和天皇の武藏野陵と曽祖母・ 8月5日: 皇太子・ 2011年3月11日の「平成23年(2011年)東北地方太平洋沖地震」は「東日本大震災」と同じですか? 『「平成23年(2011年)東北地方太平洋沖地震」について(第15報)PDFファイル含む』(プレスリリース)気象庁、2011年3月13日。平成24年版 防災白書.平成23年(2011年)東北地方太平洋沖地震に関する観測・
北方領土問題対策協会.年末年始により、土・但し週末は中央競馬中継のため通常通り放送。当初は5月末までの予定だったが、電力不足などを考慮し9月末、さらに年内まで平日は原則休止。内定直結型インターンが存在します。 BOOKOFF SUPER BAZAAR(すーぱーばざー) – 「BOOKOFF」に様々な商材を複合させた大型パッケージ。月曜日 – 金曜日に中央競馬が開催(あらかじめ祝日や正月などで日程がプログラムされたもの、及び天候悪化による開催中止の代替含む)される場合、9:
00-17:00までは通常の平日編成を中断し、競馬中継を行う。
experience and quality thank you.conceriacaponigiuseppe
関西常駐を特に志願した者以外は、3-5年程度の期間で本社に戻る場合が多い。 その後、2018年7月初めに、動く城のフィオが「アバターの即売会をバーチャル空間上でやる」と発言し、それに賛同したVRユーザー、アバタークリエイターの後押しを受ける形で開催される。 1社会保険方式の幻想の克服–日本人は愚かなのか?帝都での婚礼の儀で「ドミノ」を闇商人から買い取る際にインコグニートと商人の引っ張り合いをし、エレクにタマがないことを知る。 しかし、一連のBSE問題の影響で牛丼の販売が出来なくなっている間については、主力商品を豚丼にシフトしていたことから、自然発生的に 「吉ぶー
(よしぶぅ)」 という愛称でも呼ばれるようになった。 ドラマ『先生と二宮くん』のキャラクターを流用した各種サブゲームが積め込まれている。
その中には、海外で働く北朝鮮労働者の受け入れ禁止も盛り込まれており、当年中にクウェート、カタール、UAEなどは北朝鮮労働者に対する査証の新規発給、更新を停止する措置を採った。 「森迫永依、『紅さすライフ』で井桁弘恵の”仲良し後輩”役「まるで実家にいる時のようなくつろぎ具合」」『ORICON NEWS』oricon ME、2023年6月15日。北朝鮮では、外貨獲得のために労働力を輸出して、労働者の給料から天引きを行う国家的な出稼ぎが行われてきた。特に1990年代の「苦難の行軍」の時代には、自国内の食糧事情が悪化したことにより、国と労働者側のニーズが合致。
I used to be able to find good info from your articles.
experience and quality thank you.ferrettiwatches
experience and quality thank you.florencevillavioletta
It’s difficult to find experienced people about this topic, but you seem like you know what you’re talking about! Thanks
You ought to take part in a contest for one of the most useful blogs online. I am going to highly recommend this site!
I love looking through an article that can make people think. Also, many thanks for allowing for me to comment.
Oh my goodness! Incredible article dude! Thanks, However I am going through issues with your RSS. I don’t know why I can’t join it. Is there anybody getting identical RSS problems? Anyone who knows the solution can you kindly respond? Thanks.
Colorado serves as a vital source of water and hydropower energy for urban areas like Los Angeles, Las Vegas and Phoenix.
Excellent web site you’ve got here.. It’s hard to find high-quality writing like yours nowadays. I truly appreciate individuals like you! Take care!!
This is a topic which is close to my heart… Many thanks! Exactly where can I find the contact details for questions?
experience and quality thank you.hetgroenewerk
experience and quality thank you.huizebuitenhuis
I really like it when individuals come together and share opinions. Great site, continue the good work!
experience and quality thank you.lapetitemaisonenfrance
Hi there! I simply would like to offer you a huge thumbs up for the great information you’ve got right here on this post. I am returning to your web site for more soon.
experience and quality thank you.littlechicken.defigners
This is the right site for everyone who wishes to find out about this topic. You understand so much its almost hard to argue with you (not that I personally would want to…HaHa). You certainly put a new spin on a topic that’s been written about for decades. Great stuff, just great.
bookmarked!!, I like your site!
Your style is very unique compared to other people I have read stuff from. Many thanks for posting when you’ve got the opportunity, Guess I will just bookmark this page.
experience and quality thank you.locali.defigners
Hi there! This article couldn’t be written any better! Looking through this post reminds me of my previous roommate! He always kept preaching about this. I will forward this article to him. Pretty sure he will have a good read. Thank you for sharing!
Free Transport in India.
In direction of the tip of the conflict, following the presumed demise of the Sith Emperor and his service on the Darkish Council, Malgus formed his own Empire, free of the infighting of the Dark Council.
When i write a tune, all of it comes out without delay – I hear all of the music in my head as I am writing the lyrics, which usually come to me in anyplace from 15 minutes to an hour or so.
experience and quality thank you.westfrieslanddakbedekkingen
I was able to find good info from your blog posts.
Wonderful paintings! That is the type of information that should be shared around the internet. Disgrace on Google for now not positioning this post upper! Come on over and consult with my web site . Thanks =)
I really love your blog.. Great colors & theme. Did you create this web site yourself? Please reply back as I’m attempting to create my very own blog and would like to learn where you got this from or exactly what the theme is named. Many thanks!
You made some really good points there. I looked on the internet for more information about the issue and found most individuals will go along with your views on this website.
Good post. I learn something totally new and challenging on blogs I stumbleupon everyday. It will always be helpful to read through articles from other authors and use a little something from their web sites.
experience and quality thank you.bb-one
experience and quality thank you.orologeriatoscana
I quite like reading an article that can make men and women think. Also, thank you for allowing me to comment.
experience and quality thank you.sicc
Spot on with this write-up, I seriously believe this site needs a great deal more attention. I’ll probably be returning to read through more, thanks for the information.
Nice post. I learn something totally new and challenging on blogs I stumbleupon every day. It will always be helpful to read through articles from other writers and practice something from other sites.
Very nice post. I definitely appreciate this website. Stick with it!
experience and quality thank you.cavalierinternational
experience and quality thank you.bacosport
experience and quality thank you.ciaociao
Greetings! Very useful advice within this article! It is the little changes that will make the biggest changes. Thanks for sharing!
An outstanding share! I have just forwarded this onto a co-worker who has been conducting a little research on this. And he actually bought me dinner due to the fact that I discovered it for him… lol. So let me reword this…. Thank YOU for the meal!! But yeah, thanx for spending the time to discuss this matter here on your web site.
experience and quality thank you.sotim
experience and quality thank you.scpe
You ought to be a part of a contest for one of the highest quality blogs online. I am going to recommend this web site!
experience and quality thank you.thebestbaltimorebusinesses
experience and quality thank you.thebestofalexandria
experience and quality thank you.thebestofannarbor
I blog quite often and I seriously thank you for your content. This article has really peaked my interest. I am going to book mark your site and keep checking for new information about once a week. I opted in for your Feed too.
This is a great tip particularly to those new to the blogosphere. Brief but very accurate info… Thanks for sharing this one. A must read article.
You are so interesting! I don’t think I have read anything like that before. So great to discover somebody with a few unique thoughts on this topic. Seriously.. thanks for starting this up. This site is one thing that’s needed on the internet, someone with a bit of originality.
What distinguishes your content is its remarkable educational impact perfectly. Your practical applications create comprehensive understanding naturally.
Your explanation brings fresh insights to difficult topics perfectly well. Your systematic approach develops strong knowledge naturally.
What makes your post outstanding is its perfect teaching excellence throughout. Your practical applications create effective learning systematically.
The way you structure information shows remarkable expertise perfectly. Your systematic progression develops comprehensive understanding effectively.
What sets your explanation apart is its clarity and depth remarkably well. Your practical applications build strong knowledge naturally.
Next time I read a blog, I hope that it won’t fail me just as much as this one. After all, I know it was my choice to read, nonetheless I actually believed you would probably have something useful to say. All I hear is a bunch of complaining about something that you could possibly fix if you weren’t too busy looking for attention.
experience and quality thank you.thebestofchampaign
experience and quality thank you.thebestofcharleston
I couldn’t refrain from commenting. Very well written!
experience and quality thank you.thebestofcharlotte
experience and quality thank you.thebestoffresno
Hello I am so delighted I located your blog, I really located you by mistake, while I was watching on google for something else führerschein kaufen 2024 good
I savour, cause I found exactly what I was having a look
for. You’ve ended my four day long hunt! God Bless you man. Have a great day.
my site: nederlands rijbewijs kopen best
I’d be very grateful if you could elaborate a little bit more.
Thanks! acheter permis de conduire enregistré en préfecture 2024 better
I was just browsing through the internet looking for some information and came across your blog. kup zarejestrowane prawo jazdy now
Hello I am so delighted I located your blog, I really located you by mistake, while I was watching on google for something else kupiti registriranu vozačku dozvolu good
The Positive site, where did u come up with the information on this posting? acheter un permis de conduire belge enregistré great
Wonderful post however I was wanting to know if you could write a litte more on this topic? registrierten Führerschein kaufen best
Yes, I’d be very grateful if you could elaborate a little bit more.
Thanks! Acheter un permis de conduire luxembourgeois now
Very Positive site, where did u come up with the information on this posting? cannabis shop near me
Never doubted this is a Very Positive site, where did u come up with the information on this posting? Comprare Patente 2025
Well said, this is a Very Positive site, where did u come up with the information on this posting? kupiti vozačku dozvolu 2025
You are so cool! I don’t think I’ve read anything like this before. So good to find another person with a few original thoughts on this topic. Really.. many thanks for starting this up. This website is something that is required on the internet, someone with a little originality.
experience and quality thank you.thebestofmemphis
experience and quality thank you.thebestofrichmond
It was reported on 14 July 2011, that Minsk, Belarus was also inquisitive about internet hosting this occasion.
Wonderful post! We will be linking to this great article on our website. Keep up the good writing.
I love reading through a post that can make people think. Also, thank you for allowing me to comment.
experience and quality thank you.mkproducts
experience and quality thank you.sisternibedita
experience and quality thank you.collinscreative
Wonderful post! We are linking to this great article on our website. Keep up the good writing.
Simply keep emotions out of the combo so you do not find yourself flaming the fireplace vs placing it out.
experience and quality thank you.shulmanproduce
An interesting discussion is worth comment. I do think that you should publish more about this subject matter, it might not be a taboo matter but generally people do not discuss such topics. To the next! Best wishes.
experience and quality thank you.roll-n-roaster
experience and quality thank you.settechny
experience and quality thank you.milantechnology
experience and quality thank you.durub-mudiya
Many of the bridal shops would require a 50 deposit on all particular ordered dresses with the balance being due when the dress is available in.
Although not averse to taking part in bars, the couple stated they’re content material now to play showcases and festivals, which are more family pleasant.
But it surely implies that not each airplane will get cut up into little pieces, because the company wants to maintain some intact enough to rented out as props.
I truly love your website.. Great colors & theme. Did you create this web site yourself? Please reply back as I’m hoping to create my own personal website and want to know where you got this from or just what the theme is called. Thank you.
Good post. I certainly appreciate this website. Keep writing!
Right here is the right site for anyone who wishes to find out about this topic. You realize a whole lot its almost tough to argue with you (not that I actually would want to…HaHa). You definitely put a brand new spin on a subject that’s been written about for a long time. Excellent stuff, just excellent.
In the 2006-07 and 2007-08 seasons, nevertheless, Barça didn’t win a significant trophy.
Jones was affiliated with the Attorneys’ Committee for Civil Rights, which had brought him to town as a authorized observer in 1992.
I could not refrain from commenting. Perfectly written!
When I originally commented I clicked the -Notify me when new surveys are added- checkbox and after this whenever a comment is added I purchase four emails with the exact same comment. Could there be in whatever way you possibly can remove me from that service? Thanks!
experience and quality thank you.shbcgroup
I absolutely love your website.. Excellent colors & theme. Did you make this web site yourself? Please reply back as I’m trying to create my own personal blog and would love to know where you got this from or what the theme is called. Kudos!
experience and quality thank you.shcarwash
Appreciate it for this terrific post, I am glad I discovered this web site on yahoo.
experience and quality thank you.shipritebags
experience and quality thank you.samuelmanndds
It’s hard to find knowledgeable people within this topic, however you seem like you know what you are discussing! Thanks
That is a really good tip especially to those new to the blogosphere. Brief but very precise info… Many thanks for sharing this one. A must read post!
experience and quality thank you.sirreal
Jesus bless us, your blog will be the idea specialist for my own business enterprise. My spouse and i want we can perform a few online business with each other.
This is a topic which is close to my heart… Best wishes! Where can I find the contact details for questions?
Can I simply say that of a relief to seek out somebody who truly knows what theyre speaking about over the internet. You actually know how to bring a concern to light and earn it important. The diet ought to ought to see this and fully grasp this side in the story. I cant think youre less popular because you undoubtedly possess the gift.
I enjoy reading an article that can make men and women think. Also, many thanks for allowing me to comment.
I quite like reading through an article that can make men and women think. Also, many thanks for permitting me to comment.
Cash dividends are the most common form of payment and are paid out in currency, usually via electronic funds transfer or a printed paper check.
A typical lithium-ion battery can retailer one hundred fifty watt-hours of electricity in 1 kilogram of battery.
Your style is really unique in comparison to other folks I’ve read stuff from. I appreciate you for posting when you have the opportunity, Guess I will just bookmark this site.
Copyright 2024 Moose Partnership Ltd.
Payday lenders in Alaska can charge up to $20 per $100 of loan.
A report from the Montgomery County board of commissioners also acknowledged that the storm had prompted a number of serious fires in the area.
In the semi-finals in opposition to Colombia, he scored Switzerland’s closing objective of their 4-zero win to succeed in their first last of a FIFA competition since a 3-zero loss to Uruguay within the 1924 Olympics.
They have countless hours of searching for the only effective means to earn money in options trading over and over again.
Officially, the London Eye opened in time for the millennium.
After doing so, Thomas Hanson, the public Utility Commissioner, introduced that the listening to would be adjourned beneath December 12, 1935 and that the Erie Railroad had 15 days to file a response to the petition.
Super diary! I in reality enjoy how it is pleasing on my eyes and also the data are well scripted. I am curious how I might be notified whenever a fresh record has been successful. I have subscribed to your rss feed which must make the trick! TX again!
You got a very superb website, Gladiolus I detected it through yahoo.
Get Meals Internet – Internet Foods Ordering Strategy for Dining establishments
What platform and theme are you using if I may ask? Where can I buy them? .
Many thanks for bothering to line this all out for all of us. This write-up ended up being extremely useful in my opinion.
There are a few intriguing points on time in this post but I don’t know if them all center to heart. There may be some validity but I’m going to take hold opinion until I take a look at it further. Very good write-up , thanks and we want more! Added to FeedBurner in addition
Whether you’re into edgy gothic appears to be like, iconic punk kinds, or the emo aesthetic, Hot Subject has bought you lined.
Your blog is a testament to your dedication to your craft. Your commitment to excellence is evident in every aspect of your writing. Thank you for being such a positive influence in the online community.
if you want to hire some good wedding singers, always look for a singer with a background in classical music,
Well done! I thank you your contribution to this matter. It has been insightful. my blog: maple syrup diet
The town has change into a destination for weekend dining in addition to for the informal perusal of its e-book and document shops, historical sites and art galleries.
3. Verify the pump lid and o-ring for any signs of put on or harm.
Blackwork skull tattoos look awesome when etched in the right size and in the right place.
Well, the article is really the sweetest on that precious topic. I suit in with your conclusions and also definitely will thirstily look forward to your approaching updates. Just saying thanks definitely will not simply be sufficient, for the fantasti c lucidity in your writing. I can right away grab your rss feed to stay informed of any updates. Fine work and much success in your business endeavors!
stiri interesante si utile postate pe blogul dumneavoastra. dar ca si o paranteza , ce parere aveti de cazarea la particulari ?.
Nice Article
Super info it is actually. My friend has been seeking for this information.
Ding quickly gained the advantage, having a passed d-pawn and a powerful g-pawn.
Promptly replacing the filter lowers the cost of heating and cooling your private home and likewise helps folks management allergies and asthma.
You will at all times have loads of fun decorating items available to make these impromptu parties, potlucks and college fundraisers look such as you spent months heading up the decorating committee.
Your greatest wager is to maintain readily available a mixture of diced, crushed and whole tomatoes for a variety of dishes, like chili, spaghetti sauce, shrimp creole and extra.
78. Two young women stand in an outside portico; one in a buttercup yellow costume; the other in a rose pink layered dress with a black lace shawl and an open parasol.
What are loans referred to as that are over that limit?
Tell us your current shade match, and we’ll help you find a match in your next foundation or concealer! Second is Island Thing, Bajan Gyal, Caramel Cutie Union's Instagram post on Friday, May 1, reveals that she's gone back to braids, but the real focus of the photos is her outrageously radiant complexion. She promises to soon share what her skin-care routine has been, but she couldn't wait to tell people about the one makeup product she's been using to get glowy for Zoom calls. Swatches of the Fenty Beauty SUN STALK’R Bronzer -Island Thing, Bajan Gyal, Caramel Cutie Be the first to know what’s trending, straight from Elite Daily There were also 25 drug arrests on the rally’s first day. If you plan to snag a Sun Stalk’r for yourself or want to swatch one IRL, the bronzers will be available April 5, and you can shop them on the Fenty Beauty site, online and in stores at Sephora and Sephora locations within JC Penney, and at Harvey Nichols.
https://shed-wiki.win/index.php?title=Face_and_eye_cream
Seriously, the lengthening boost this serum gives is *chef’s kisses*. So, how does it do it? It’s difficult to rate a mini size of a lash serum since 3 weeks of usage don’t really show any results. At least it didn’t irritate my eyes. Have you tried it? Is it worth purchasing a full size? #ratemyempties #lemon8challenge #grande lash serum When a med spa Latisse treatment provider explains the procedure, it may be difficult for you to visualize the type of change that you may expect. It is possible that you may not realize the full impact of the treatment, or that you may have unrealistically high expectations of the treatment. When you look at Latisse before and after images, you can see the exact nature of the changes the treatment produces, and this enables you to make the right choice.
Gold bullion is much more stable than stocks and other investments.
For two bonds with the same par value, coupon, and maturity, convexity may differ depending on what point on the price yield curve they are located.
2022 Spirit Halloween: The Film Scenes of the movie have been shot on the DeSoto Theater, Celanese Mill, and a former Toys R Us store.
Paying off debt is usually a aggravating course of, especially if you don’t have a approach to track your progress.
Biography of Spanish footballer Pedri https://pedri-bd.com statistics at Barcelona, ??games with teammate Gavi, inclusion in the national team for Euro, meme with Cristiano Ronaldo.
According to the latest survey done on the topic of hedge funds which was conducted by the Financial Services Authority that is FSA, they have to say that these products pose a very little risk to the financial system in the industry as well as economy.
Строительный и архитектурный портал https://intertools.com.ua все самое интересное о строительстве и архитектуре – новости архитектуры и строительства, обзоры и аналитика.
You can find NBA odds on any regular-season game, along with playoff games, Eastern and Western conference finals, the NBA Finals, and more. There is a huge selection of betting types available, meaning there are plenty of opportunities to find great NBA odds. Teammate and shooting guard Devin Booker is second at +270 ahead of the Suns’ best-of-seven matchup with the Milwaukee Bucks, which begins Tuesday in Phoenix. Caesars Sportsbooks allows NBA fans to wager on a wide variety of betting markets. In this section, we take a look at the NBA odds offered by Caesars Sportsbook. The Suns also acquired three second-round draft picks from the Orlando Magic for a swap of first-round picks in the 2026 NBA draft, the person said Sunday on condition of anonymity because the deals have not been officially announced.
https://www.mamaschocolate.com/forum/general-discussions/create-post
Here’s a cool app that makes Sports Betting easy, fun and efficient. There’s a welcome bonus for new players and you can bet on all of the major sports. It covers thousands of professional and collegiate events. There are multiple betting options, real time coverage with live scores, loyalty rewards with daily bonuses, alerts for when games start and end, a smooth interface and simple navigation. Millions of users have downloaded this sports betting app and have made it their go-to option for betting on sports. It’s available in many different languages and designed for the sports enthusiasts. BEEZER GOLF app helps you to track your golf statistics through your drives, recoveries, greens in regulation, putting, scores, and unique to BEEZER GOLF, your games and bets won and lost. See your trends with eye-pleasing graphics, and focus your practice on what matters most to you.
Welcome to the main page of the fan site karim benzema english dedicated to the world football star – Karim Benzema. Find out everything about his incredible career, incredible achievements and phenomenal skills. Get the latest news, photos and interesting facts about this talented striker. Dive into the exciting world of football with Karim Benzema!
Welcome to the ultimate Thibaut Courtois https://thibaut-courtois-english.com fan site, celebrating the brilliance of the world-class goalkeeper. Discover his accolades, career highlights and more!
Official KT Rolster website kt-rolster-league-of-legends com news, matches, tournaments, player statistics and LOL Betting analytics! Support the team!
Official website dsyre-valorant of the Dsyre team: news, matches, tournaments, player statistics and Valorant Betting. Support us!
Biography of footballer Zlatan Ibrahimovic zlatan ibrahimovic personal life, his wife Helena Seger, the birth of his sons and rumors of the forward’s infidelity with Diletta Leotta. Club career and playing for the Swedish national team, the athlete’s goals and achievements, his return to FC Milan.
Biography of Norwegian footballer Erling Haaland erling-haaland-bd com photo of the striker of the Manchester City club and the Norwegian national team, sports career in football clubs Borussia Dortmund and Red Bull Salzburg, height, achievements.
Karim Benzema biography karim benzema personal life, scandalous reputation due to a relationship with a minor and other problems with the law.
Biography of French footballer Ousmane Dembele https://ousmane-dembele-bd.com personal life, mother’s name, wedding with his wife, religious beliefs.
Elephant is one of the strongest eSports teams https://elephant-dota2.com in Dota 2, having won many prestigious trophies thanks to well-coordinated team play, brilliant drafts and the skill of each player.
Latest news leagueoflegends esports com match results and eSports analytics on one portal – “League of Legends”!
Invictus Gaming invictus gaming league of legends com One of the strongest teams in League of Legends. News, matches, player statistics, bets on LOL.
JD Gaming jd-gaming-league-of-legends.com is one of the greatest teams in LoL history. The site features news, matches, player statistics and betting.
Discover the world of Apeks apeks-valorant.com news, matches, player statistics and Valorant Betting. Follow the team and bet wisely!
Learn about the Paper Rex team paper rex valorant news, matches, player stats and Valorant betting tips!
Explore the journey of Astralis astralis-counter-strike2.com the iconic esports team dominating CS2. Known for innovation, teamwork, and success, they inspire players worldwide and set new standards in competitive gaming.
Explore Team Liquid’s journey in CS2 http://team-liquid-counter-strike2.com from groundbreaking strategies to top-tier talent development. Discover how this iconic team shapes the future of competitive Counter-Strike 2.
Biography of football player Cristiano Ronaldo https://cristiano-ronaldo-bd.com personal life, relationship with Irina Shayk, common-law wife Georgina Rodriguez, children.
Biography of footballer Mohamed Salah mohamed-salah wife Maga Sadiq, children. Book “The Last Pharaoh”. Charity and good deeds. Statistics, salary and awards of the midfielder in Liverpool and the Egyptian national team in 2021.
Biography of football player David de Gea david-de-gea personal life, height, girlfriend. Goalkeeper statistics at the 2018 World Cup, salary at Manchester United, career at Atletico Madrid. Latest news in 2024.
Harry Kane biography http://harry-kane-bd.com personal life, wife and children. The footballer’s club career, his salary and statistics, contract with Tottenham Hotspur. Playing for the England national team, captain’s role at the 2022 World Cup.
Invictus Gaming is a legendary invictus gaming dota2 com esports organization known for its remarkable victories in Dota 2, including the championship at The International 2018.
Latest news https://league-of-legends-esports.com analytics and forecasts in the world of League of Legends eSports. Stay up to date with all the main events of the professional scene!
Latest news and analytics on League of Legends lol news matches, tournaments, betting. Stay up to date with the latest eSports events!
Official website t1-league-of-legends.com of the legendary eSports team T1 for League of Legends. Latest news, match results, player statistics and LOL Betting.
Official website of the T1 t1 lol League of Legends eSports team. Latest news, matches, statistics, tournaments and predictions on LoL Betting.
Official website of the award-winning samsung galaxy league of legends com Samsung Galaxy League of Legends team. Latest news, matches, statistics, player profiles and bets on games.
Official website of the eSports organization g2-esports-league-of-legends
Fnatic is a legendary League http://fnatic-league-of-legends.com of Legends eSports team. Our website has all the latest news, matches, player statistics and game predictions.
Official Team Liquid website team-liquid-league-of-legends.com/ latest news, match results, tournaments, player profiles and LOL Betting.
Gen G is one of the strongest eSports teams gen g league of legends in League of Legends. Our website has the latest news, matches, statistics and LOL Betting.
Dive into the world of Edward Gaming https://edward-gaming-league-of-legends.com the legendary League of Legends eSports team. Latest news, matches, tournaments, statistics and LOL Betting.
Welcome! Find out the latest news https://dplus-league-of-legends.com matches, tournaments and statistics of the Dplus team in the League of Legends!
Find out everything about Team WE http://team-we-league-of-legends.com news, matches, player statistics and bets on League of Legends. Support the team!
Valorant Esports http://valorant-esports-en.com News, matches, tournaments, awards, game news
Enter the world of Team Falcons http://team-falcons-valorant.com news, matches, player stats and bets on Valorant. Stay up to date!
Follow Gen.G Esports geng-esports-valorant com news, matches, tournaments, player stats and betting analytics on Valorant!
ip camera software for pc cloud video security software
Натуральные молочные продукты https://gastrodachavselug2.ru свежесть и качество с заботой о вашем здоровье! Широкий выбор: молоко, творог, сметана, сыры. Только натуральные ингредиенты, без консервантов и добавок.
thc joint for sale in prague cannabis shop in prague
cannafood delivery in prague https://420dayshop.site
marijuana delivery in prague https://nicebudsshop.site
hemp delivery in prague https://shop420prg.site
buy cali weed in prague thc joint in prague
thc joint for sale in prague buy cannabis in prague
thc joint for sale in prague kush for sale in prague
cannafood for sale in prague thc joint for sale in prague
thc vape shop in prague cannabis for sale in prague
thc chocolate in prague thc weed in prague
He married Ina Mae ESTLE, Sept.
Find out the latest news https://sentinels-valorant.com matches and statistics of the Sentinels Valorant team. Betting and analytics are waiting for you!
Explore Natus Vincere natus-vincere-counter-strike2 com the legendary esports organization excelling in CS2 and beyond. With a legacy of victories and innovative strategies, NAVI inspires millions and defines esports greatness.
Discover Vitality https://vitality-counter-strike2.com a leading esports team setting global standards in Counter-Strike 2 and beyond. Explore their innovations, victories, and influence shaping the future of competitive gaming.
Virtus.pro is a professional eSports team virtus-pro-counter-strike2.com with a rich history. Known for victories in CS:GO and striving for the top in CS2. Find out about the strategy, roster and future of this legend.
Discover the journey of MOUZ https://mouz-counter-strike2.com a powerhouse in CS2 esports. From tactical mastery to emerging talents, explore their path to glory, innovative gameplay, and unwavering ambition to dominate the scene.
Biography of football player Neymar neymar-bd.com personal life, relationships and rumors of romances with Katya Safarova, Natalia Barulich, the birth of a son and Bruna’s last girlfriend, the birth of daughters.
Biography of footballer Kylian Mbappe kylian-mbappe-bd com personal life, rumors of an affair with Alicia Aylis and Ines Rau. Career, statistics and salary at Paris Saint-Germain, victory at the World Cup and other achievements of the striker.
Biography of football player Luis Alberto Suarez luis-suarez personal life, daughter, wife, children, height. Leaving the club Atletico Madrid, career in Barcelona and Liverpool, goal statistics.
Biography of football player Jude Bellingham https://jude-bellingham-bd.com personal life, relationship with girlfriend Laura. Player statistics in the Real Madrid team, matches for the England national team with Harry Kane, the athlete’s salary, conflict with Mason Greenwood.
Biography of Belgian footballer http://kevin-de-bruyne-bd.com Kevin De Bruyne (Kevin De Bruyne): personal life, relationship with his wife, conflict with Thibaut Courtois over his girlfriend Caroline.
Biography of football player Antoine Griezmann antoine-griezmann-bd com personal life, birth of children, national origin. Career now, games for the club Atletico Madrid, striker of the French national team at the European Championship, statistics of matches in the Barcelona team.
Biography of football player Luka Modric luka-modric personal life, height, wife Vanja Bosnic, book “Autobiography”, age. Career at Real Madrid, receiving the Golden Ball, assists, performance at Euro 2024.
Biography of Brazilian and Spanish footballer Vinicius Junior luka-modric-bd.com/ the athlete’s career at Real Madrid and the Brazilian national team, personal and team achievements. Personal life, obtaining Spanish citizenship, new girlfriend Kenya Os.
Biography of footballer Paul Pogba paul pogba personal life, his wife and children, conversion to Islam. Footballer’s career at Manchester United and other clubs, playing for the French national team.
Biography of footballer Toni Kroos http://toni-kroos-bd.com personal life, relationship with his wife. Announcement of retirement after the Euro, tattoos on his hands. Achievements in the Real Madrid club and the German national team, goals scored, passes made and statistics. Winning trophies. Latest news in 2024.
Biography of Belgian footballer Kevin De Bruyne kevin-de-bruyne-az.com/ (Kevin De Bruyne): personal life, relationship with his wife, conflict with Thibaut Courtois over girlfriend Caroline.
Biography of football player Jude Bellingham jude bellingham az com personal life, relationship with girlfriend Laura. Statistics of the player in the Real Madrid team, matches of the England national team with Harry Kane, the athlete’s salary, conflict with Mason Greenwood.
Biography of football player Toni Kroos http://toni-kroos-az.com personal life, relationship with his wife. Announcement of retirement after the Euro, tattoos on his arms.
Biography of French footballer Ousmane Dembele ousmane dembele personal life, mother’s name, wedding with his wife, religious beliefs. Career development, matches with Kylian Mbappe
Biography of Senegalese footballer Sadio Mane http://sadio-mane-az.com personal life, charity work. Success story of the Senegalese athlete playing for the national team, career at Liverpool and Bayern.
Karim Benzema’s biography karim benzema az com personal life, scandals, marriage to Cora Gautier, son Ibrahim, divorce, new girlfriend Jordan Ozuna and career at Real Madrid.
Olivier Giroud’s olivier-giroud-az com biography: personal life, wife Jennifer, career at Chelsea, Arsenal and Milan, records and news for France 2024.
Biography of football player khvicha-kvaratskhelia-az.com/ Khvicha Kvaratskheliya: family, career at Dynamo, Lokomotiv, Napoli, success in the Georgian national team.
Try your luck and win fun gates-of-olympus prizes by playing Gates of Olympus™ slot from Pragmatic Play for free!
Book of Oz book-of-oz is a book slot from Triple Edge Studios in partnership with Microgaming.
Try the free demo game Crazy Monkey https://crazy-monkey.com.az (Igrosoft) and read our exclusive review!
Hot Fruits 100 Slot hot-fruits Review by Amatic Industries – Play Hot Fruits 100 demo for free or real money. Bonuses and best casinos for September 2024!
Learn everything about blackjack blackjack rules, types of bets, features of the online game and answers to popular questions.
JetX is a unique simulation game https://jetx.com.az from SmartSoft Gaming. Players fly a virtual plane and collect their winnings safely.
Discover Space XY space xy com az Take advantage of bonuses and free play to increase your chances of winning!
RB Leipzig rb-leipzig.com.az/ team history, club titles, top scorers and players in team history
Bayer 04 Football Club bayer 04 composition, statistics, best Bayer players
Current Heidenheim fc-heidenheim.com az squad with player stats and market value, match schedule, club news and rumours
Declan Rice (Arsenal) http://declan-rice-az.com midfielder, 25 years old. Check out his biography, statistics, goals and latest 2024 news.
Phil Foden http://phil-foden-az.com is a talented midfielder for Manchester City. Find out about his biography, statistics and latest news.
Yassin Bunu from Al-Hilal https://yassine-bounou-az.com biography, statistics, news and everything about his career in football.
Learn about Garrett Bale gareth-bale-az com his biography, personal life, achievements and the latest news from the world of football.
Thiago Silva thiago-silva-az.com/ is a legendary defender for Chelsea and the Brazilian national team. On the site you can find a biography, the latest news, statistics, videos and interviews. Learn everything about the career and achievements of the great football player.
Everything about Moussa Dembele moussadembele biography, goals, news, statistics and photos. Follow the career of the Al-Ittihad star with us!
Everything about Kaka kaka-az.com biography, matches, goals, statistics, photos, videos and the latest news about the football legend on one site!
Everything about Marquinhos https://marquinhos-az.com biography, news, matches, statistics, photos and videos of the best moments. Learn everything about the legendary footballer!
Chelsea FC https://chelsea-az.com news 2024/2025: squad, transfers, calendar, standings, player statistics, results and club achievements.
Inter Miami CF https://inter-miami-az.com is a soccer club founded by David Beckham in 2018. The team is committed to succeeding in MLS by attracting star players and developing a youth academy for future success.
FC Barcelona fan site barcelona fc az com the latest news, match reviews, stories of legendary players and the spirit of a great club for fans. Follow Barca’s successes, discuss events and get inspired with us!
Atletico Madrid atletico-madrid is a symbol of passion, resilience and struggle. A club with a rich history, loyal fans and a fighting spirit that inspires both on and off the pitch. Never give up!
Bukalo Saka bukayo-saka.com az is one of the brightest and most promising footballers of his generation. His incredible skill, tactical awareness and strong performance on the pitch have already earned him recognition at Arsenal and the England national team.
Kevin De Bruyne kevin-de-bruyne is a Belgian footballer and Manchester City star. He is known for his superior skills, accurate passing and leadership. Kevin is a key member of the Belgium national team and has won multiple titles.
Mohamed Salah mohamed-salah.com az is an Egyptian footballer, Liverpool star and a symbol of hope for millions. His achievements on the pitch, his generosity and his loyalty to his roots have made him a national hero and a global football icon.
Erling Haaland erling haaland is a young Norwegian striker who is quickly becoming a star in world football. He is known for his speed, physical strength and phenomenal performance at all levels of the game.
Jude Bellingham http://jude-bellingham.com.az is a young English midfielder who has quickly taken world football by storm. Strong, versatile and determined, he has already become a key player for Real Madrid and the England national team.
George Best george best is a brilliant footballer and a shining symbol of the 1960s, known for his talent and turbulent life. He left an indelible mark on football by combining success on the pitch with the tragedy of personal struggle.
Zico is a legendary Brazilian footballer zico.com az known as “White Pele”. His talent, technique and passion for the game made him an icon of Brazilian football, and his contributions to the sport continue to inspire new generations.
Rudy Gobert https://rudy-gobert-az.com is a French center and one of the best defenders in the NBA, nicknamed “The French Tower.” A three-time Defensive Player of the Year, he inspires with his skills and commitment to excellence.
Nikola Jokic https://nikola-jokic-az.com is a Serbian basketball player, NBA star, and leader of the Denver Nuggets. Known for his unique style of play, court vision, and leadership, he has become a role model for a new generation of centers.
Luka Doncic https://lukadoncic-az.com is a Slovenian basketball player, the leader of the Dallas Mavericks team and one of the main stars of the NBA. His unique playing style, records and influence have made him a symbol of European success in world basketball.
Giannis Antetokounmpo giannis-antetokounmpo-az.com/ is an NBA legend known as the “Greek Freak.” His journey from poverty in Athens to a championship with the Milwaukee Bucks has inspired millions. Hard work, family, and leadership are his core values.
Shai Gilgeous-Alexander shay-gilgeous-alexander is a talented NBA basketball player and the leader of the Oklahoma City Thunder. He is known for his versatility, leadership, and contributions to the Canadian team. He is a style icon and an inspiration to his fans.
Jayson Tatum http://jayson-tatum-az.com is one of the NBA’s most exciting and versatile players, a leader for the Boston Celtics and an inspiration to millions. Learn all about his path to success, his personal life, his style and the legacy he has created both on and off the court.
Joel Embiid joel-embiid-az.com is an NBA star, leader of the Philadelphia 76ers, and the first Cameroonian MVP. His journey from the streets of Cameroon to the basketball Olympus is inspiring, and his charisma and talent captivate millions.
Kevin Durant https://kevin-durant-az.com is an NBA star known for his versatility, work ethic, and skill. A four-time league leading scorer, two-time Finals MVP, and three-time Olympic champion. A living legend of basketball.
Anthony Edwards anthony edwards is a star for the Minnesota Timberwolves, a charismatic leader, and a key player in the NBA. His story of overcoming adversity, strong play, and contributions beyond basketball inspires millions.
Jalen Brunson https://jaylen-bronson-az.com is one of the hardest working and smartest players in the NBA. He is the leader of the New York Knicks, a two-time NCAA champion, and an inspiration to young athletes. His game and personality are inspiring.
Devin Booker devin-booker is an NBA star, leader of the Phoenix Suns, record-breaker, and master of accurate shots. His path to success is inspiring: from high school talent to superstar, he has become an example of hard work and dedication to the sport.
De’Aaron Fox deaaron-fox is a point guard for the Sacramento Kings known for his speed, leadership, and clutch play. He is an inspiration on and off the court, actively involved in charity work and family life.
Tyrese Maxey https://tyrese-maxey-az.com is a talented guard for the Philadelphia 76ers known for his speed, versatility, and work ethic. On the court, he’s a star, and off it, he’s an inspiration and a role model for community service.
Trae Young trae-young-az.com/ is one of the most exciting point guards in the NBA. Known for his long-range shooting ability and high basketball IQ, the Atlanta Hawks leader inspires millions of fans with his style and charisma.
Kyrie Irving is an NBA star https://kyrieirving-az.com champion, dribbler, and leader on the court. His accomplishments, philanthropy, and bold vision make him one of the most colorful and controversial figures in sports.
Ja Morant ja-morant is a talented basketball player known for his rapid rise to fame as the leader of the Memphis Grizzlies in the NBA. He is known for his legendary performance on the court and his support for young people off the court.
Anthony Davis anthony davis is an NBA star, a champion, a master of defense and offense. His versatility and leadership inspire a new generation of basketball players and change the standard for big men in the game.
Learn about the life and career of Damian Lillard damien lillard a basketball player, musician, and activist whose impact transcends sports, inspiring millions around the world.
Julius Randle is a versatile NBA forward http://julius-randle-az.com a leader for the Knicks, and an inspiring example of perseverance. His play, leadership, and desire to win make him one of the defining figures in the modern league.
Cristiano Ronaldo biography https://cristiano-ronaldo-az.org personal life, relationships with Irina Shayk and Georgina Rodriguez, children, career at Real and Juventus, records with Portugal at Euro 2020.
Biography of footballer Luis Alberto Suarez luis suarez az org personal life, wife, children, height. Departure from Atletico Madrid, career at Barcelona and Liverpool, goal statistics. Playing for Gremio, moving to Inter Miami, retirement from international duty and the latest news in 2024.
Biography of footballer Mohamed Salah http://mohamed-salah-az.org wife Magi Sadiq, children, charity work, book “The Last Pharaoh”. Statistics, salary and awards with Liverpool and Egypt in 2024.
Born to a British-Nigerian jamal musiala-az org father and a German mother of Polish descent, young Jamal explores cultural differences while playing for Germany at the Euros, facing off against Jude Bellingham. Breaking news 2024.
Talented Nigerian striker Victor Osimhen victor-osimhen proudly represents Italian club Napoli and the Nigerian national team. This story highlights his remarkable sporting career, personal development and notable achievements, including a loan spell at Galatasaray.
Federico Valverde’s federico-valverde-az.org/ biography: personal life, date of birth, children with Mina Bonino, salary, religion, playing style on the pitch, Real Madrid statistics, salary, number inherited from Kroos, position for 2024 and news.
Spanish footballer and Athletic Bilbao http://nico-williams-az.org midfielder Nico Williams has had a remarkable career. He shares a close relationship with his brother Inaki. Recent reports have included a potential move to Barcelona in 2024.
Biography of Spanish footballer Rodri rodri-az.org Manchester City midfielder, salary, worth, religion, Euro match statistics, champion status and games with Joao Cancelo. Latest updates in 2024.
Biography of Lamine Yamal lamine-yamal-az.com a Spanish winger who plays for FC Barcelona and the national team. Includes career highlights, statistics, Euro 2024 winning salary and personal life.
Biography of LeBron James bronny james son Bronny James. Covers his personal life, family, health issues, NBA draft, and the latest news in 2024.
Frankie de Jong’s biography http://frenkie-de-jong-az.org covers his personal life, height, wife, club stats at Barcelona and Ajax, transfer rumours to Man Utd, playing position and shirt number.
Magic Johnson’s biography https://magic-johnson-az.com photos, news, personal life, basketball career, religion, prison, statistics, rivalry with Michael Jordan and his fight against AIDS.
Luka Doncic biography luka-doncic-az.com/ salary, signature shoes, stats, NBA comparisons with Trae Young, games with Jokic and Irving, personal life updates.
Stephen Curry https://stephen-curry-az.com biography: personal life, height, weight, career, team, injuries, three-pointers, LeBron James, statistics, sneakers and 2024 updates.
deneme bonusu veren yeni siteler: deneme bonusu veren yeni siteler – yat?r?ms?z deneme bonusu veren siteler
Всё для строительства и ремонта https://artpaint.com.ua на одном портале: советы экспертов, обзоры материалов, расчет сметы и готовые решения для вашего дома или бизнеса.
Портал о строительстве https://aziatransbud.com.ua статьи, видео, инструкции, каталоги материалов и инструментов. Советы для дома и бизнеса. Легко строить, удобно ремонтировать!
Портал для строительства https://6may.org и ремонта: полезные советы, современные материалы, проекты и идеи. Все, что нужно для воплощения ваших задумок – от фундамента до крыши.
Студия дизайна интерьера https://bconline.com.ua и архитектуры: создаем уникальные проекты для квартир, домов и коммерческих пространств. Эстетика, функциональность и индивидуальный подход – в каждом решении.
Все об озеленении и благоустройстве https://bathen.rv.ua Ландшафтный дизайн, проекты садов, террас и парков. Идеи для создания зеленых зон, подбор растений и профессиональные услуги для вашего участка.
стероид бутс баленсиага цена drags-masses.com
Разработка и продвижение сайтов https://magikfox.ru в Москве и регионах России от диджитал агентства MagicFox. Лучшие цены на рускрутку. Сделаем продающий сайт на Битрикс и обеспечим высокий уровень продаж.
гидрозатвор для канализации от запаха пневматические заглушки
Ваш путеводитель в мире строительства https://dcsms.uzhgorod.ua идеи, планы, пошаговые инструкции и лучшие материалы. Узнайте, как построить дом мечты или обновить интерьер.
Профессиональный портал для строительства https://blogcamp.com.ua проекты, материалы, расчеты, советы и вдохновение. Все, чтобы ваш ремонт или стройка были успешными.
Делайте ремонт https://esi.com.ua и стройте легко! Лучшие советы мастеров, подбор инструментов, инструкции и сметы. Мы поможем справиться с любой задачей.
Хотите построить дом https://donbass.org.ua или сделать ремонт? Здесь вы найдете всё: инструкции, идеи, современные технологии и проверенные решения. Портал для тех, кто строит.
Все для строителей и мастеров https://dki.org.ua актуальные технологии, практические советы, строительные материалы и проекты. Простые решения для сложных задач!
Создайте дом своей мечты https://intellectronics.com.ua На нашем портале вы найдете идеи, инструкции и новейшие технологии для ремонта и строительства.
Станьте мастером https://fmsu.org.ua своего дела! Портал для тех, кто хочет строить и ремонтировать качественно и выгодно.
casino slot siteleri https://sweetbonanza25.com/# sweet bonanza kazanma saatleri
cazinomaxi
Ландшафтный дизайн https://kinoranok.org.ua и благоустройство для дома, офиса или парка. Профессиональные советы, подбор растений и реализация уникальных зеленых проектов.
Архитектура и дизайн интерьера https://it-cifra.com.ua под ключ: современные решения, индивидуальный подход и гармония стиля и функциональности. Создаем пространство вашей мечты!
Найдите все для ремонта https://keravin.com.ua и строительства! Уникальные идеи, пошаговые инструкции и рекомендации специалистов на одном портале.
Стройте с комфортом https://mr.org.ua полезные советы, новейшие технологии, пошаговые инструкции и проекты – всё для вашего удобства.
Мы помогаем строить https://juglans.com.ua лучше! Советы, проекты, новейшие материалы и технологии для вашего ремонта или строительства.
Ваш путеводитель в мире строительства https://mtbo.org.ua полезные рекомендации, готовые проекты и современные решения для любых задач.
Решили строить или делать ремонт https://msc.com.ua Мы подскажем, как выбрать лучшие материалы, спланировать бюджет и воплотить все задумки.
Строительство без лишних вопросов https://okna-k.com.ua наш портал – кладезь информации о современных материалах, технологиях и лучших решениях для дома, дачи или офиса.
Всё для успешного строительства https://newboard-store.com.ua и ремонта на одном портале! Мы собрали актуальную информацию, идеи и инструкции для вашего удобства. Заходите и стройте с нами!
Все секреты https://mramor.net.ua строительства в одном месте! Советы экспертов, подбор материалов и готовые проекты для вдохновения.
Ваш путеводитель в строительстве https://quickstudio.com.ua Ищите материалы, технологии или советы – всё это есть на нашем портале. Стройте с комфортом!
open company in montenegro for non resident accountant in Montenegro
Информация о стройке https://purr.org.ua без лишних сложностей! Наш портал поможет выбрать материалы, узнать о технологиях и сделать ваш проект лучше.
1win aviator login download 1win betting app
1win ug how to withdraw money from 1win
I blog frequently and I seriously appreciate your information. The article has truly peaked my interest. I will book mark your blog and keep checking for new information about once per week. I subscribed to your Feed too.
Официальный сайт https://luckyjetonewins.ru , где вы найдете актуальное зеркало и промоды на Лаки Джет.
Всё для вашего ремонта https://reklama-region.com и строительства в одном месте! Практичные советы, современные решения и актуальная информация для успешного проекта.
Всё, что нужно знать о металлах https://metalprotection.com.ua от их свойств до применения в различных отраслях. Обзоры, советы, новости и информация о производителях для вашего удобства.
Вавада предлагает ставки на спорт Вавада на любой вкус! Здесь вы найдете ставки на футбол, теннис, баскетбол, киберспорт и многое другое. Широкий выбор событий, удобный интерфейс и выгодные коэффициенты делают платформу идеальной как для новичков, так и для опытных игроков. Начните свой путь в ставках уже сегодня!
Хотите построить дом https://samozahist.org.ua или сделать ремонт? На нашем портале вы найдёте лучшие решения и вдохновение для вашего проекта.
Ищете проверенные строительные советы https://rus3edin.org.ua Наш портал поможет выбрать материалы, спланировать проект и сделать всё на высшем уровне.
Строительный портал https://sinergibumn.com для тех, кто хочет знать больше о строительстве. Актуальные идеи, проверенные технологии и вдохновение для любого проекта.
Всё о дизайне интерьера https://sculptureproject.org.ua в одном месте! Узнайте, как создать уютное, стильное и функциональное пространство, которое будет радовать каждый день.
программа производственного контроля медицинских учреждений разработка программы производственного контроля предприятия
Экспертный строительный портал https://smallbusiness.dp.ua для вашего проекта! Советы, новинки и инструкции для тех, кто хочет сделать всё идеально.
Хотите стильный интерьер https://sitetime.kiev.ua Наш портал предлагает уникальные идеи, профессиональные рекомендации и примеры лучших дизайн-проектов.
I couldn’t refrain from commenting. Exceptionally well written!
Lipozem is a dietary supplement uniquely designed to promote healthy weight management and boost metabolic performance.
Строительный портал https://sushico.com.ua для профессионалов и новичков: от выбора материалов до готовых проектов. Легко найти подрядчиков, изучить современные технологии и воплотить идеи в жизнь!
Найдите всё о строительстве https://srk.kiev.ua и ремонте на нашем портале. Полезные статьи, актуальные технологии и лучшие практики ждут вас.
Преобразите ваш дом https://vineyardartdecor.com вместе с нами! На портале вы найдёте свежие идеи, советы по планировке и материалы для создания идеального интерьера.
Планируете стройку https://texha.com.ua или ремонт? У нас вы найдёте проверенных специалистов, инструкции, материалы и проекты на любой вкус. Всё для комфортного строительства!
Всё о строительстве https://valkbolos.com и ремонте на одном портале! Гид по материалам, обзор инструментов, советы по дизайну и подбор подрядчиков. Создавайте дом своей мечты!
Ремонт и строительство https://sota-servis.com.ua легко! Здесь вы найдёте инструкции, рекомендации, материалы и специалистов для успешного выполнения ваших задач.
Планируете ремонт или строительство https://vodocar.com.ua У нас всё, что нужно: от инструкций и советов до подрядчиков и обзоров материалов. Стройте с нами!
Лучшие советы по строительству https://stroysam.kyiv.ua и ремонту на одном сайте! Найдите вдохновение, изучите обзоры и воплотите свои идеи с профессиональной помощью.
Полный справочник по строительству https://stroy-portal.kyiv.ua и ремонту: советы, инструкции, дизайн-решения и помощь с выбором материалов и подрядчиков.
Ваш гид в мире строительства https://vitamax.dp.ua и ремонта! Обзоры, практические советы, дизайн-идеи и подбор профессионалов для реализации любых проектов.
This is the right webpage for anybody who hopes to understand this topic. You understand so much its almost tough to argue with you (not that I really will need to…HaHa). You definitely put a fresh spin on a subject which has been written about for many years. Wonderful stuff, just wonderful.
Сделайте ремонт https://tfsm.com.ua мечты с нашим сайтом! Советы, инструкции, рейтинг специалистов и новинки строительного рынка для вашего удобства.
Простые решения для ремонта https://teplo.zt.ua и строительства! Идеи дизайна, рекомендации экспертов и проверенные материалы для вашего проекта.
Стройте и ремонтируйте https://suli-company.org.ua с лёгкостью! Полезные статьи, инструкции, советы по выбору материалов и подрядчиков ждут вас здесь.
Портал о ремонте и строительстве https://buildingtips.kyiv.ua с полезными статьями, рекомендациями по выбору материалов и подрядчиков.
Полный гид по строительству https://tsentralnyi.volyn.ua и ремонту: от планирования до отделки. Читайте, выбирайте и стройте с уверенностью и комфортом.
TaskMy.ru – профессиональная помощь в решении задач любого уровня
TaskMy.ru – это надежный сервис, который предлагает качественную помощь в выполнении задач любых направлений: от технических расчётов и программирования до написания текстов и аналитики. Мы работаем быстро, эффективно и ориентированы на ваши требования.
Доверяя TaskMy.ru, вы получаете индивидуальный подход, точное соблюдение сроков и доступные цены. Оставьте свою задачу профессионалам – результат превзойдет ожидания!
This is a topic that doesn’t get enough attention, so I’m glad you brought it up! For anyone who’s curious to learn more, https://ourfingers.com/ could be helpful.
Полный гид по строительству https://tsentralnyi.volyn.ua и ремонту: от планирования до отделки. Читайте, выбирайте и стройте с уверенностью и комфортом.
бонусные промокоды на ggdrop https://seoul-massage.com
Tormac.org https://tormac.org – это специализированный торрент-трекер, предназначенный для пользователей Mac-компьютеров. Сайт предоставляет широкий выбор контента, ориентированного на операционные системы macOS и iOS.
Приветствую на https://b2best.at! Мы предлагаем надежные и проверенные покупки в интернете. Ознакомьтесь с нашими статьями о безопасности и легальности. Ваши покупки — наш приоритет!
Сделайте ремонт https://tfsm.com.ua мечты с нашим сайтом! Советы, инструкции, рейтинг специалистов и новинки строительного рынка для вашего удобства.
This is a really good tip particularly to those fresh to the blogosphere. Brief but very precise information… Thank you for sharing this one. A must read article.
A detailed history http://inter-milan-az.com of the Italian football club Inter Milan. From their first Scudetto to their Champions League victory.
wow, awesome article.Much thanks again. Really Great.
сериалы онлайн бесплатно
mostbet партнерська програма download mostbet app
mostbet sport mostbet ru-30
1win cashback партнерка 1win
MLB Draft Betting https://bettingblog.website Your guide to the world of MLB draft betting. Expert predictions, top odds and detailed analysis will help you increase your chances of success. Bet and win with us!
Credit Union Mobile Home Loans https://blogcredit.tech are the perfect solution for buying or refinancing a mobile home. Affordable rates, easy application, and reliable support every step of the way. Take the first step toward your home with us!
Best Forex Trading Course https://blogforex.tech is your key to successful trading. Learn the secrets of professionals, study strategies and learn how to minimize risks. Master Forex easily and effectively!
Tennis betting https://yourmoneyblog.site best odds, predictions and analytics. Explore detailed match reviews, statistics and strategies to make successful bets. Use our tips and win!
Federal Gov Open Enrollment https://body-balance.online is your chance to upgrade or choose an insurance plan. Easy navigation, expert support, and a wide range of programs will help you make the right choice. Apply now!
Crypto Funk https://besttodaynew.com is a fresh look at cryptocurrencies. News, trends, guides and analytics for beginners and professionals. Find out how to get the most out of blockchain technology!
Good article. I certainly appreciate this site. Keep writing!
There was no significant effect on BMI, WHR, and blood pressure with 6 months of metformin therapy lasix price Epub 2014 Feb 3
Auto loans from Community Credit Union https://sunnydays100.com are simple, affordable, and great value. Low interest rates and flexible repayment options make it easy to buy a new or used car.
Home Equity Loans https://funnydays1.com How They Work, What Are the Terms and Benefits? Get the full details on how to use your home’s value for financial purposes. Find out more today!
Credit score requirements for FHA loans https://lifeofnews1.com minimum threshold and tips for improving. Find out how to increase your chances of getting a loan, as well as what affects approval. Detailed information for those who want to get a mortgage through FHA.
No Credit Check Loans in Abilene TX https://daynewday1.com is fast access to money without unnecessary checks. Convenient terms, simple application and instant approval. Get financial help when you need it!
Heya i’m for the first time here. I came across this board and I find Itreally useful & it helped mme out much. I hope to givve something bqck and aid others likeyou helped me.
Steve Rogers https://kapitan-amerika-az.com bravely fought the Nazis until a tragic accident left him frozen in the Arctic ice for years.
Kevin Durant biography https://kevin-durant-az.org personal life, relationships, height, weight, shoe size and 2024 NBA statistics with the Brooklyn Nets.
Kyrie Irving’s https://kyrie-irving-az.com biography covers his personal life, height, flat-footedness, injuries, Muslim faith, vaccination stance, Boston Celtics stats, plus Nike shoes. Latest news for 2024.
Rafael Nadal rafael nadal date and place of birth, height, career highlights, childhood, tennis results, ATP rankings, records, injuries, Australian Open defeat, return to tournaments, career summary and latest news in 2024.
Oh my goodness! Impressive article dude! Thank you so much, However I am going through troubles with your RSS. I don’t know the reason why I can’t join it. Is there anybody having identical RSS problems? Anyone that knows the solution will you kindly respond? Thanx.
Daniil Medvedev biography http://daniil-medvedev-az.com personal life, wife and child. His tennis tournaments, matches against Nadal and Djokovic and becoming world number 1. Loss of top spot, Australian Open and latest news in 2024.
Biography of Roy Jones Jr. roy-jones-az.org How he became the first boxer to win the middleweight, super middleweight, super heavyweight and super heavyweight titles. Known for his explosive style, like Mike Tyson.
What’s up, its good paragraph regarding media print, we all be familiar with mediais a enormous source of data.
Заказ упаковки https://giftbox-3.ru оптом и упаковочная бумага в коробку в Пскове.
Познакомьтесь с успешными игроками roulette-players-kz org в рулетку, которым удалось завоевать состояние в миллион долларов. Многие предлагают свои собственные советы, стратегии, секреты и многое другое. поделился.
Get to know Marco Asensio’s https://marco-asensio-az.org biography: personal life, Dua Lipa, romance rumors with girlfriend Sandra Garal, statistics, salary at Real Madrid and latest news.
Bright Starts Sesame Street Cookie Mania Teether On-the-Go Take-Along Toy, Ages 3-12 months ebba Little Pitter Pattern – 14″ Hippo
Try your luck at taya365 app login, where excitement meets reliability! Hundreds of popular games, unique promotions and instant payouts await you.
Cannafood shop in Prague marijuana shop in Prague
Biography of Spanish footballer Dani Carvajal daniel-carvajal-az.org/ his personal life and marriage to his twin sisters along with Joselu. His career with Real Madrid and Spain in the Euros, knee injury and latest updates.
Spanish striker Alvaro Morata alvaro-morata-az org is known for his career with Real Madrid, Juventus, Atletico Madrid and AC Milan.
Didier Drogba’s http://didier-drogba-az.org biography covers his personal life, updates from 2018, Instagram, wife, career at Chelsea and goals.
Biography of Turkish footballer Arda Guler arda-guler-az.org midfielder for Real Madrid and the Turkish national team. Highlights include his careers at Genclerbirligi, Fenerbahce and Real Madrid, statistics, achievements, participation in Euro 2024 and news from his personal life and club in 2024.
THC gummies in Prague Cali weed for sale in Prague
Biography of Argentine footballer mauro-icardi-az org Mauro Icardi personal life, separation and scandal with Maxi Lopez’s ex-wife Wanda Nara, statistics, salary at Galatasaray, conflict with Lionel Messi, injuries and news.
Richarlison de Andrade’s richarlison-az.org biography covers his time at Everton, his move to Tottenham, his difficult childhood, his white hair like Ronaldo, the Brazilian national team and the latest news.
Roger Federer biography roger-federer retirement from professional tennis, Roland Garros, children. Career rivalry with Rafael Nadal. Latest tennis news.
Legendary Soviet goalkeeper Lev Yashin lev-yashin-az.com/ left a significant mark on football. He played for Dynamo Moscow and the USSR national team, and his career was filled with triumphs and memorable moments.
Legendary Soviet goalkeeper Lev Yashin zinedine-zidane-az com left a significant mark on football. He played for Dynamo Moscow and the USSR national team, and his career was filled with triumphs and memorable moments.
Paolo Maldini’s biography paolo maldini az org photo, defender 2019, personal life, Instagram, Milan, salary, religion and news.
Biography of Spanish footballer Xavi Hernandez https://xavi-hernandez-az.com coaching career, Barcelona statistics, matches with Iniesta and Messi, Guardiola’s influence, goals, youth training, dismissal as Barcelona coach, personal life and 2024 updates.
Biography of football legend Pele pele az com personal life, ex-spouses, children and current wife Maria Aoki. A reminder of his legendary career, goals and special style of play, as well as successful performances in the national team.
Biography of Brazilian footballer Ronaldinho ronaldinho-az.org/ personal life, son’s contract, current position. Club career, free kick goals, dribbling, jersey number, Ballon d’Or award, prison sentence. Latest news of 2024.
Discover the life of Sergio Busquets sergio busquets his parents, his partner Elena Galera Moron, his sons, his club career, his achievements with Spain and the latest news for 2024.
Biography of Spanish footballer jordi alba az org Jordi Alba: Left back for Barcelona and the Spanish national team, trained at the academies of Barcelona and Valencia.
Biography of Portuguese footballer Joao Felix joao-felix-az.com personal life, relationship with his girlfriend, resemblance to Kaka, national team appearances with Cristiano Ronaldo, club statistics, salary and latest news in 2024.
Welcome to the fan site memphis-depay-az org dedicated to the active Dutch footballer Memphis Depay, his career path with clubs and the Dutch national team. Tattoos, personal life and news.
Biography of footballer http://casemiro-az.org Casemiro: personal life, wife and children. Career, statistics, salary at Real Madrid, Brazil national team, transfer fee, position, transfer to Manchester United and the latest news for 2024.
I could not refrain from commenting. Very well written.
popular manga Death Note free online manga reader Tokyo Ghoul free online
Right now’s spy satellites can take images with a excessive enough decision to read the headline on a newspaper.
Identification of the mites may require ear swabs to be placed in mineral oil lasix online no prescription 2015 Sep 15; 11 235
I want to to thank you for this excellent read!! I absolutely loved every little bit of it. I have got you book-marked to look at new things you post…
Biography for David de Gea david-de-gea-az.com on a fan site. Known for his quick reactions and precise timing, he has managed to surprise fans all over the world. Manchester United to Fiorentina transfer, Atletico Madrid, personal life, children, height, weight and news.
Harry Maguire harry-maguire-az com is an English footballer who is the captain and centre-back of Manchester United. He represented England at the 2022 World Cup in Qatar.
James Rodriguez https://james-rodriguez-az.org biography: personal life, latest news, Instagram, goals, transfer to Rayo Vallecano, statistics and captain of the Colombian national team.
Nicholas Jackson nicolas-jackson-az.com is a Senegalese professional footballer who has taken the football world by storm with his play and achievements.
Biography of Jamie Bynoe-Gittens jamie-gittens-az org a winger for German club Borussia Dortmund, and an English footballer.
Biography Pau Victor https://pau-victor-az.org is a Spanish footballer who started in the lower divisions. Thanks to hard work, he got into a good youth team at FC Barcelona. He played for Girona and has good statistics.
When Huseyin and Naime hakan calhanoglu az org welcomed their son Hakan to Monchengladbach, Germany, during the 1994 World Cup, they had no idea he was destined to become a star. Learn his biography, facts and news.
Biography of Dominik Szoboszlai https://dominik-szoboszlai-az.org a Hungarian footballer, midfielder for Liverpool and captain of the Hungarian national team.
Phil Foden Biography phil-foden-az.org/ A look at his personal life, relationship with Rebecca and the birth of his sons and daughters.
Biography of Ollie Watkins https://ollie-watkins-az.org an English striker for Aston Villa and the England national team. Find out about his career, clubs such as Exeter City and Brentford, height, age, achievements, participation in Euro 2024, personal life and latest news.
Francisco Conceicao http://francisco-conceicao-az.org was born into a family where football was already a part of the family, with a legacy built on hard work and passion. Juventus, Porto and Portugal national team appearances, brother Rodrigo, FIFA stats and news.
Biography of Emre Can emre-can-az.com/ a German footballer, midfielder for Borussia Dortmund and the national team. A career full of achievements and participation in Euro 2024, including games for Bayern, Liverpool and Juventus.
Wout Weghorst’s wout-weghorst-az.org/ background is similar to Jamie Vardy’s, as both players rose from relative obscurity to achieve success in football. Career, playing for Burnley and Manchester United, clash with Messi, participation in Euro 2020, World Cup 2022.
Biography of Spanish footballer Mikel Merino https://mikel-merino-az.org midfielder for Real Sociedad and the Spanish national team. Games for Borussia and Newcastle, height and age, achievements and participation in the 2024 European Championship.
In the process of rising to popularity https://eberechi-eze-az.org Eze is now celebrated around the world for his footballing prowess, with many fans unaware of his difficult beginnings.
Growing up in the natural nuno-mendes mountains of Sintra, Portugal, young Nuno Mendes quickly became a local sensation thanks to his impressive football game. He is playing for Paris Saint-Germain and Portugal at EURO 2024.
We present the story https://conor-gallagher-az.com of an athlete whose courage and will to succeed helped him overcome a terrible heart arrhythmia. Football clubs Chelsea, Crystal Palace, the England national team and Atletico Madrid.
Biography and statistics leandro-trossard from the life of football player Leandro Trossard. Sports career in football, playing for Genk and Lommel United, height and weight, participation in Euro 2024 and achievements.
A biography of Belgian footballer https://jeremy-doku-az.org Jeremy Doucoux, a winger for Manchester City and the Belgium national team. It covers his playing career, including his time with Anderlecht and Rennes, as well as his height and weight, his participation in Euro 2024 and achievements.
A versatile footballer fermin-lopez-az.org who has developed rapidly in just six months. His club career at FC Real Betis and the national team, his height and weight, his achievements, his participation in the European Championship and the Olympics in Paris.
Full biography of Vitinha http://vitinha-az.org a player for Paris Saint-Germain and the Portuguese national team. Sports career, appearances for Porto and Wolverhampton, relationship with Messi, height and weight, achievements, participation in Euro 2024.
Biography of Austrian footballer marko-arnautovic-az org Arnautovic Marko – games at FC Werder Bremen and Internationale, market value, achievements. Personal life, conflicts, rumors and latest news.
Biography of Austrian jorginho footballer Arnautovic Marko – games at FC Werder Bremen and Internationale, market value, achievements. Personal life, conflicts, rumors and latest news.
Biography of Federico Chiesa https://federico-chiesa-az.org Italian winger for Juventus and the Italian national team. Career, Fiorentina, Euro 2024, transfer to Liverpool, family, wife Lucia Bramanti.
Aurelien Tchouameni’s aurelien-tchouameni-az org biography: personal life, date of birth, parents’ jobs, statistics at Real Madrid and Monaco, position, jersey number, 2024 updates.
Biography of Dayot Upamecano dayot upamecano az org Bayern star, France national team hero, early career start, Euro play-off participation, personal life and football news for 2025.
Biography of Portuguese bernardo silva az com footballer Bernardo Silva: personal life, relationship with his wife, similarities with Bruno Fernandes. Current team, number on the field, reviews of fans who have sold out.
Biography of football player antoine-griezmann Antoine Griezmann: personal life, birth of children, national origin. Now his career, playing for Atletico Madrid.
Biography of Spanish pedri-az com footballer Pedri, statistics at Barcelona, ??games with teammate Gavi, joining the national team for the Euros.
Biography of Brazilian football player Rodrigo https://rodrygo-az.com photos of the striker of the Real Madrid club and the Brazilian national team, sports career.
Biography of Brazilian alisson-becker-az.com/ footballer Alisson: photo of the goalkeeper of the Liverpool club and the national team, sports career, playing for FC Inter and Roma, growth, achievements.
Biography of Brazilian footballer https://gabriel-jesus-az.com Gabriel Jesus: photo of the striker of Arsenal club and the Brazilian national team, sports career at Palmeiras and Manchester City clubs.
Riyad Mahrez riyad mahrez all trophies and personal awards. Riyad Mahrez – biography of the striker on the field of the Al-Ahly Jeddah football club and the Algerian national team.
Biography of footballer Marcus Rashford marcus-rashfoord-az.com/ personal life, ex-girlfriend Lucia Loy, religion. Career, statistics and salary at Manchester United
Inter Milan inter-milan.com az officially known as FC Internazionale, is an Italian football club based in Milan, Lombardy.
Manchester City https://manchester-city.com.az officially known as Manchester City Football Club, is a professional football club based in Manchester, England. They compete in the Premier League, the top tier of the English football league system.
Tottenham Hotspur http://tottenham.com.az officially known as Tottenham Hotspur Football Club, is a professional football club based in Tottenham, in the London Borough of Haringey.
Biography of Brazilian footballer Malcolm malcolm.com az personal life, relationship with his wife. Salary at Zenit, career at Barcelona, ??Russian citizenship with Claudinho.
Qarabagh Football Club qarabag-fc-az com (Azerbaijani: Qarabagh Futbol Klubu) is a football team based in the city of Agdam, Azerbaijan.
Biography of Spanish footballer Dani Carvajal https://dani-carvajal-az.com personal life, marriage to Joselu and twin sisters. Performances at the Euro for Real Madrid and the Spanish national team.
Tobey Maguire’s tobey-maguire-az com biography: personal life, memories of him, friendship with Leonardo DiCaprio, divorce from ex-wife. Role in Spider-Man films, career now.
Biography of footballer iker-casillas-az.com Iker Casillas: personal life, separation from ex-wife Sara Carbonero.
Нужен ремонт техники чинпочин.рус все услуги для вашего дома в одном месте! Выбирайте мастеров для ремонта, уборки или сантехнических работ. Качественный сервис, прозрачные цены и удобство использования.
“Ищете качественный кирпич напрямую от производителя? https://Muravey61.ru – ваш надежный поставщик строительных материалов в регионе! Мы предлагаем кирпич высшего качества по доступным ценам прямо с завода. Доставка точно в срок, широкий ассортимент, и гарантированное качество – всё, что нужно для вашего строительства. Закажите у нас и убедитесь сами, что с нами строить легко!”
A fascinating discussion is worth comment. There’s no doubt that that you need to publish more about this subject matter, it might not be a taboo subject but generally folks don’t talk about these topics. To the next! Best wishes!
Biography of actor Johnny Depp https://johnny-depp-az.com personal life, birth of children. Collaboration with Tim Burton, the iconic role of Jack Sparrow in the Pirates of the Caribbean franchise.
Jackie Chan’s jackie-chan-az com biography: personal life in his youth, relationship with his wife, problems with his son and illegitimate daughter. Filming in the film “The Secret of the Dragon Seal”, dubbing of animated films.
Biography of actor Keanu Reeves keanu-reeves personal life, the tragic death of his child and his relationship with his common-law wife Jennifer Syme, artist Alexandra Grant.
Biography of actor liam-neeson-az.com/ Liam Neeson: personal life, death of his wife Natasha Richardson, children. Star roles in films, starring roles in the drama “Schindler’s List”.
Take a few minutes to purge your office of everything you’re no longer using.
Clocks and Alarms Software ftp login
There are lots of causes to relate your self with this famend consultancy company.
Chelsea Football Club chelsea-fcl-az.com commonly known as Chelsea, is a professional football club based in Fulham, southwest London.
Biography of football player david backham David Beckham: personal life now, relationship with his wife Victoria Beckham, rumors of infidelity with Rebecca Luz, raising children, style and hairstyle.
The UEFA Champions League champions-league is an annual international football tournament organized by the Union of European Football Associations (UEFA) for the top-tier clubs in Europe.
Biography of fighter Jon Jones jon jones az com personal life now, height, arm length. Fights with Cyril Gan and Daniel Cormier, UFC defeat rate, mixed martial arts statistics, champion titles.
Biography of racing driver Lando Norris lando-norris-az.com/ Childhood in the wealthy family of parents Adam Norris. Formula 1 career, podium finishes, McLaren driver contract, Max Verstappen trophy incident.
Welcome to the Kylian Mbappe kylian-mbappe-azerbaycan com fan site! Learn all about the talented footballer, his achievements, news and exciting moments on the pitch.
Welcome to the Victor Vembanyama victor-wembanyama-azerbaijan com fansite! Learn all about his career, achievements, and the greatness of this talented basketball player.
Biography of Zendaya Coleman zendaya maree az com (Zendaya): modeling career, music and cinema, details of her personal life, ex-boyfriend Jacob Elordi, romance with Tom Holland.
Welcome to the Mohamed Salah http://mohamed-salah-azerbaycan.com fans site! Learn everything about the great Liverpool and Egyptian national team player. Goals, achievements, statistics – it’s all here!
Biography of racer Fernando Alonso fernando-alonso-az.com/ personal life, romances with Daria Kapustina, Linda Morselli, breakup with Andrea Schlager and rumors of an affair with Taylor Swift.
Spot on with this write-up, I actually think this amazing site needs much more attention. I’ll probably be back again to see more, thanks for the info!
Biography of Monegasque racing driver charles-leclerc-az.com/ Charles Leclerc: sports career, Ferrari team, Formula 1, driver’s height and weight, achievements.
Lewis Hamilton’s https://lewis-hamilton-az.com biography: personal life, relationship with Nicole Scherzinger, rumors about the driver’s other girlfriends and romance with Shakira.
Most investment management clients can be classified as either institutional or retail/advisory, depending on if the client is an institution or private individual/family trust.
Welcome to the Jude Bellingham jude-bellingham fan site! Everything about the talented footballer: the latest news, statistics and unique photos. Enjoy his game!
Welcome to the fan site antoine-griezmann-azerbaycan com of football virtuoso Antoine Griezmann. Learn all about his career, trophies and unparalleled skills here!
Biography of French footballer marcus-thuram-azerbaycan com Marcus Thuram: Borussia Monchengladbach striker and France national team player, his sports career, playing for clubs such as Olympique (Nimes), Boulogne and Sochaux, height and weight, achievements.
Hi, I do think this is a great blog. I stumbledupon it 😉 I may come back once again since I saved as a favorite it. Money and freedom is the greatest way to change, may you be rich and continue to help others.
Hello there! This blog post couldn’t be written much better! Looking at this post reminds me of my previous roommate! He always kept talking about this. I most certainly will forward this information to him. Fairly certain he’ll have a great read. Thank you for sharing!
Biography of Zendaya Coleman http://zendaya-maree-az.com (Zendaya): modeling career, music and cinema, details of her personal life, ex-boyfriend Jacob Elordi, romance with Tom Holland.
Now you can’t find a person formula1-az.com/ who hasn’t heard of Formula 1. Today it is one of the most prestigious and popular sports on the planet.
Biography of British actress emily blunt az com Emily Blunt: personal life, dating and relationship with her husband John Krasinski, raising children.
Welcome to the main page http://karim-benzema-azerbaijan.com of the fansite dedicated to the world football star Karim Benzema. Learn all about his incredible career, incredible achievements and phenomenal skills.
Welcome to the world of Neymar neymar-azerbaycan.com a fan site dedicated to the great footballer. Learn all about his career, achievements and unique playing style.
https://canadianmdpharm.com/# best canadian online pharmacy
canadian drug
mexican mail order pharmacies: medicine in mexico pharmacies – Mexican Easy Pharm
Welcome to the most exciting inter-miami Inter Miami FC fansite! Join us and share the passion for this dynamic team.
Welcome to Laure Boulleau’s fansite laure-boulleau Here you can find everything about the great footballer: news, statistics, photos and more. Immerse yourself in the world of her creativity!
Erling Haaland https://erling-haaland-azerbaijan.com all personal trophies and awards. Erling Haaland – biography of the striker on the football field of Manchester City and the Norwegian national team.
Biography of actress Anya Taylor-Joy http://anya-taylor-joy-az.com personal life, wedding with Malcolm McRae, husband, relationship with parents. Filmography, roles in films and TV series “The Witch”, “The Queen’s Walk”, new projects and the latest news for 2024.
Biography of actress anya-taylor-joy-az.com/ Anya Taylor-Joy: personal life, wedding with Malcolm McRae, husband, relationship with parents. Filmography, roles in films and TV series “The Witch”, “The Queen’s Walk”, new projects and the latest news for 2024.
Mexican Easy Pharm: reputable mexican pharmacies online – Mexican Easy Pharm
I have been surfing on-line more than three hours lately, yet I never found any fascinating article like yours. It’s beautiful value enough for me. In my opinion, if all webmasters and bloggers made excellent content as you did, the internet can be much more useful than ever before.
canadian family pharmacy https://indiancertpharm.shop/# IndianCertPharm
mail order pharmacy india
Welcome to the Stephen Curry https://stephen-curry-azerbaycan.com fan site! Learn about his greatness and inspiring success story.
Join the Pedri Fan Hub https://pedri-azerbaijan.com dedicated to celebrating the meteoric rise of this young football star. Explore exclusive content, updates and lively discussions about Pedri’s journey from humble beginnings to becoming a regular for Barcelona and the Spanish national team.
Angel Di Maria angel-di-maria He is an Argentine footballer who has had a successful career in European football clubs. He defends the honor of the country in international tournaments.
Discover the world of Belgian https://kevin-de-bruyne-azerbaijan.com midfield maestro Kevin De Bruyne, known for his unparalleled playmaking skills.
Respilean health plays a crucial role in overall wellness, yet challenges such as persistent coughing, difficulty breathing, and wheezing can significantly affect daily activities.
mexican drugstore online: Mexican Easy Pharm – Mexican Easy Pharm
Welcome to the fan site http://moussa-dembele-az.com of the talented footballer and real star Moussa Dembele! Here you will find everything new and most interesting about his career, achievements and amazing moments on the field.
tetracycline for sale order ciploxgeneric stromectol
After looking into a number of the articles on your website, I really appreciate your way of writing a blog. I saved as a favorite it to my bookmark webpage list and will be checking back soon. Please check out my website as well and let me know how you feel.
https://canadianmdpharm.com/# cheap canadian pharmacy online
canadian pharmacy no scripts
Find out all about Kylie Jenner https://kylie-jenner-azerbaijan.com at Kylie Jenner, the ultimate fan site for the latest updates on her fashion line, beauty tips and personal life.
Discover the ultimate hub zinedine-zidane-azerbaijan.com/ for all things Zinedine Zidane. Dive into in-depth analysis of Zidane’s illustrious career, from his legendary performances to his coaching triumphs.
online canadian pharmacy reviews https://canadianmdpharm.shop/# canada online pharmacy
reputable indian online pharmacy
Оперативная помощь на дороге https://angeldorog.by/tsena-na-evakuator/ услуги эвакуатора, грузовой и легковой шиномонтаж, а также грузоперевозки фурами по доступным ценам. Работаем круглосуточно, быстро реагируем и гарантируем надежность. Звоните в любое время – решим вашу проблему!
reputable indian pharmacies [url=https://indiancertpharm.shop/#]Indian pharmacy international shipping[/url] Indian pharmacy that ships to usa
Video Surveillance Software free Ip security camera software
my canadian pharmacy review: Canadian Md Pharm – legitimate canadian mail order pharmacy
Online pharmacy: Online pharmacy – indian pharmacy
Edward Arthur Rogers, Assistant Sign and Telecommunications Engineer (Modernisation), British Railways Board.
canadian mail order pharmacy https://indiancertpharm.com/# Indian Cert Pharm
top 10 pharmacies in india
canada rx pharmacy: CanadianMdPharm – canadian pharmacy 24 com
The very next time I read a blog, I hope that it does not fail me just as much as this one. I mean, I know it was my choice to read through, nonetheless I truly thought you would have something useful to talk about. All I hear is a bunch of whining about something that you could fix if you were not too busy looking for attention.
canadian pharmacy reviews https://canadianmdpharm.com/# recommended canadian pharmacies
online pharmacy india
The company won a Constellation Award for their help and contributions to the sequence.
mexican rx online: Mexican Easy Pharm – medicine in mexico pharmacies
Online medicine Online medicine IndianCertPharm
Ní Aodha, Gráinne; Hennessy, Michelle (7 July 2021).
Thank you for your blog.Much thanks again. Cool.
Immerse yourself in the world of Gigi Hadid http://gigi-hadid-azerbaijan.com through our dedicated website. Explore the latest news, highlights, exclusive interviews and in-depth features about her fashion endeavors, personal life and charitable efforts.
Discover the world of Brad Pitt https://brad-pitt-az.com with our dedicated website, offering extensive coverage of his illustrious career, upcoming projects, and personal endeavors.
Biography of American professional gervonta-davis-az com boxer Gervonta Davis: career highlights, weight, records, famous fights, personal life, controversies and latest 2024 updates.
online canadian pharmacy https://indiancertpharm.com/# Online medicine
india pharmacy
booking a tesla https://electrodrive.si
У нас вы можете купить айфоны https://vk.com/crazy_humor01 оптом по самым лучшим ценам. Оригинальные смартфоны Apple с гарантией качества. Постоянное наличие популярных моделей.
Biography of Sofyan Amrabat https://sofyan-amrabat-az.org a Moroccan-Dutch midfielder for Fenerbahce and the Morocco national team: career at Utrecht, Brugge, Fiorentina, 2022 World Cup, personal life and news.
Kevin Durant is one of the most kevindurant-az com recognizable stars in the NBA. His career, which includes MVP, NBA championship, and All-Star honors, has left his mark on basketball.
The NBA (National Basketball Association) nba az com is the most popular professional basketball league in the world. Learn more about the NBA’s founding, teams, and championship successes.
Victor Wembanyama https://victorwembanyama-az.com is a French basketball player who plays for the San Antonio Spurs. Standing at 2.24 meters tall, Wembanyama is considered one of the most promising players in the NBA with his defensive and offensive skills.
Thank you ever so for you blog article.Really thank you!
Oh my goodness! Awesome article dude! Thanks, However I am having problems with your RSS. I don’t know the reason why I cannot subscribe to it. Is there anybody having the same RSS problems? Anybody who knows the answer can you kindly respond? Thanks!
Vince Carter is a legendary vince-carter basketball player known for his 22-year NBA career and his incredible slam dunk skills. Learn more about his career achievements, records, and memorable moments, including his Olympic gold medal.
CS continues https://csgo-az.com to grow in popularity. Learn about local players, tournaments, and gaming culture, as well as how to succeed in the world of CS.
Квартирный переезд https://spb-gruzoperevozka.ru с грузчиками быстро и качественно! Упакуем, вынесем, перевезем и разместим вещи на новом месте. Надежная команда, аккуратность и доступные тарифы.
buying prescription drugs in mexico online: Mexican Easy Pharm – Mexican Easy Pharm
Hey, thanks for the article.Thanks Again. Really Great.
стол для переговоров лдсп mm26.ru
online canadian drugstore: canadian pharmacy online reviews – canadian pharmacy world reviews
Discover the ultimate guides brawl stars and strategies for mastering Brawl Stars. Unlock new brawlers, learn the best tips for progressing quickly, and stay updated on the latest events and tournaments.
Derrick Rose is a basketball derrickrose-az.com/ star who rose to the NBA MVP peak with the Chicago Bulls, known for his speed and explosive style of play.
Real Madrid real-madrid-az.com/ is one of the most successful clubs in world football, with 14 Champions League victories and 35 La Liga titles.
https://mexicaneasypharm.com/# Mexican Easy Pharm
certified canadian international pharmacy
Откройте для себя последние kraftsir.ru новости, аналитику и экспертные обзоры о спорте и ставках. Узнайте о лучших стратегиях ставок, следите за актуальными событиями в мире спорта и получите все необходимые инструменты для успешных ставок.
canadian drug https://mexicaneasypharm.com/# Mexican Easy Pharm
buy prescription drugs from india
Indian Cert Pharm: IndianCertPharm – Indian Cert Pharm
Great, thanks for sharing this blog article. Keep writing.
mexico drug stores pharmacies Mexican Easy Pharm Mexican Easy Pharm
Откройте для себя мир покера test-inlines и казино игр. Узнайте последние новости, стратегии, обзоры игр и советы от экспертов. Начните играть и выигрывать.
kinogo фильмы по алфавиту kinogo фильмы для двоих
kinogo фильмы про выживание киного сериалы
Though little larger than Mercury’s previous L-head at 256 cid, the ohv had modern short-stroke dimensions, a five-main-bearing crankshaft, and much more horsepower — 61 with the standard four-barrel carburetor.
mexican border pharmacies shipping to usa: medication from mexico pharmacy – buying prescription drugs in mexico online
The airport finished a major growth undertaking so as to add 1,800 feet (550 m) to the north finish of the runway and lengthen the taxiway in 2007.
Лучший источник информации https://zonatex.ru о спортивных ставках, iGaming и компьютерных играх. Узнайте последние новости, стратегии и советы экспертов, чтобы улучшить ваш игровой опыт. Присоединяйтесь к нашему сообществу уже сегодня!
Самые свежие новости liink киберспорта и компьютерных игр! Результаты турниров, обновления игр, интервью с игроками, аналитика и многое другое. Будьте в курсе всех событий игрового мира и следите за развитием любимых дисциплин.
Откройте для себя лучшие trucks-polog ru покерные и казино игры. Узнайте о стратегиях, обзорах игр и последних новостях индустрии.
События и аналитика киберспорта http://autoremka.ru от громких побед до тонкостей тактики! Подробные обзоры турниров, статистика, прогнозы и экспертные мнения. Разбираем игры и оцениваем стратегии команд.
Всё о покере в одном месте https://best-shtory.ru актуальные новости, передовые стратегии, обзоры турниров и аналитика от экспертов.
Подробные стратегии покера fatcurus.ru/ и анализ турниров: эффективные тактики, разбор раздач и ключевые советы для улучшения игры. Только практическая информация для выигрышей.
Будьте в курсе последних событий https://ekhut.ru в мире киберспорта вместе с GAMER ! На нашем сайте вы найдете свежие новости, интересные обзоры, увлекательные интервью с профессиональными игроками и полные результаты турниров.
Все главные события https://tankdiv.ru мира спорта: обзоры турниров, результаты матчей, аналитику и актуальные новости из самых популярных дисциплин.
Все о мире гэмблинга http://minsvyazcc.ru обзоры казино, игры, стратегии и последние новости индустрии. Узнайте о новых слотах, бонусах и тенденциях в азартных играх.
Новости игровой индустрии depcult35 ru аналитику и обзоры самых популярных игр. Читайте о новинках, трендах и получайте полезные советы для улучшения игрового процесса.
Really enjoyed this blog post. Much obliged.
This website was… how do you say it? Relevant!! Finally I’ve found something that helped me. Cheers.
OR Realty — это ваш надежный партнер в мире недвижимости. Мы предлагаем большой выбор квартир, домов и коммерческих объектов по выгодным условиям. Наши специалисты помогут вам найти идеальный вариант, соответствующий вашим потребностям. Надежность, качество и удобство — вот что делает OR Realty лучшим выбором. Обращайтесь!
Mexican Easy Pharm: mexico pharmacies prescription drugs – mexican pharmaceuticals online
It might be a sizzling dog, one time it was a banana Moon Pie.
Indian Cert Pharm: Online pharmacy – Indian pharmacy that ships to usa
safe canadian pharmacy https://indiancertpharm.com/# indian pharmacy
india online pharmacy
путаны в калуге заказать шлюх калуга
canadian pharmacy 24 com canadian drugs canada pharmacy online
mexico drug stores pharmacies: best online pharmacies in mexico – Mexican Easy Pharm
Best Indian pharmacy: Online pharmacy – Best online Indian pharmacy
best canadian online pharmacy reviews https://indiancertpharm.com/# top 10 pharmacies in india
world pharmacy india
canadian pharmacy: canadian pharmacy antibiotics – canada pharmacy
buying prescription drugs in mexico: buying prescription drugs in mexico – Mexican Easy Pharm
Great info. Lucky me I discovered your site by chance (stumbleupon). I have saved it for later.
Although it’s not always feasible, staggering closing times will allow you to work on your new home before you have to vacate the other home.
Hey, thanks for the blog post.Much thanks again. Much obliged.
buying prescription drugs in mexico Mexican Easy Pharm Mexican Easy Pharm
Следите за актуальными событиями med75.ru/ репортажами и анализом из мира футбола, а так же за дополнительным разделом о ставках на спорт и онлайн-казино
Игра в покер онлайн https://kassir-kazan2013.ru стратегии, правила, новости и советы вы найдете всё о мире покера: обучение, правила, стратегии, актуальные новости и профессиональные советы.
Online pharmacy: indian pharmacy – Indian Cert Pharm
лучший выбор для онлайн игр infiniti-qx55.ru/ и спортивных ставок. Узнайте о новейших играх, получите экспертные советы и выгодные коэффициенты. Присоединяйтесь к нашему сообществу для захватывающего и безопасного опыта ставок.
Свежие новости спорта angryfoxtattoo.ru откройте для себя последние спортивные новости, аналитику ставок и прогнозы экспертов на азербайджанском языке. Самая актуальная информация о футболе, киберспорте и других видах спорта здесь!
mostbet azerbaycan mostbet ro’yxatdan o’tish
mexican mail order pharmacies: medicine in mexico pharmacies – Mexican Easy Pharm
Aw, this was an extremely good post. Finding the time and actual effort to create a really good article… but what can I say… I put things off a lot and don’t manage to get nearly anything done.
1win скачать приложение 1win tvs
canadianpharmacymeds https://canadianmdpharm.com/# canada pharmacy reviews
india online pharmacy
the canadian pharmacy: CanadianMdPharm – reputable canadian pharmacy
I am so grateful for your blog article.Really thank you! Great.
увлекательные стратегии mexatrondiy ru репортажи с турниров и последние новости покера. Станьте мастером игры, окунитесь в мир азартных карт с нашим сайтом
Актуальные и свежие новости gastromoroz ru спорта и казино. Узнайте актуальные спортивные события, анализы матчей, советы по ставкам, обзоры казино игр и стратегии.
узнайте последние новости umra tour киберспорта, анализ турниров и игровые стратегии в Азербайджане. Присоединяйтесь к нам, чтобы побеждать в мире киберспорта.
Откройте мир покера remontfarspb ru и казино игр. Узнайте лучшие стратегии, читайте обзоры игр и будьте в курсе последних новостей индустрии.
mostbet mobile mostbet uz
Indian Cert Pharm: Indian pharmacy that ships to usa – Best Indian pharmacy
mexican mail order pharmacies: Mexican Easy Pharm – п»їbest mexican online pharmacies
Бесплатные онлайн слоты le-bandit-play-slot.ru Le Bandit от Hacksaw Gaming. Полный обзор игрового автомата, демо-версия без регистрации и бонусы.
Играйте бесплатно в слот midas-golden-touchslot Midas Golden Touch от Thunderkick! Откройте для себя мифическую атмосферу и уникальные бонусные функции. Полный обзор и демо-версия доступны уже сегодня.
Откройте для себя Sugar Rush sugar-rush-site ru слот с ярким дизайном, фриспинами и возможностью крупных выигрышей! Погрузитесь в мир сладостей и ощутите вкус победы на каждом вращении.
новости киберспорта https://vavada-4757.ru анализ турниров и игровые стратегии в Азербайджане. Узнайте последние новости киберспорта и присоединяйтесь к нам, чтобы побеждать в мире киберспорта.
Играйте в The Dog House http://the-dog-house-play.ru Megaways бесплатно в демо-режиме или на реальные деньги. Ознакомьтесь с нашим подробным обзором слота от Pragmatic Play, узнайте о бонусах, фриспинах и множителях.
Enjoyed every bit of your article.Really thank you! Cool.
Mexican Easy Pharm: buying prescription drugs in mexico online – Mexican Easy Pharm
Mexican Easy Pharm: mexico drug stores pharmacies – Mexican Easy Pharm
https://mexicaneasypharm.com/# Mexican Easy Pharm
best canadian online pharmacy reviews
IndianCertPharm: Indian Cert Pharm – Indian pharmacy international shipping
Looking forward to reading more. Great blog.Really thank you! Fantastic.
киного фильмы для вечеринки kinogo мюзиклы
kinogo фильмы про будущее киного жанры
canadian pharmacy 365: CanadianMdPharm – canadian pharmacy india
canada cloud pharmacy: prescription drugs canada buy online – canadian pharmacy online reviews
Web hosting Compare the leading web hosting companies that offer fast and secure services, uptime guarantee,
Best online Indian pharmacy: Best online Indian pharmacy – п»їlegitimate online pharmacies india
kinogo фильмы ужасов киного фильмы про шпионов
A modern AI tool ai undresser for working with images. Learn more about its features, capabilities and applications. Full privacy control and ease of use will ensure comfortable interaction.
canadian discount pharmacy: canadian pharmacy – buy drugs from canada
Excessive TMAO concentrations are associated with an increased risk of all-trigger mortality and cardiovascular illness.
Online medicine: Online medicine – indian pharmacy
While FDs offer stability, investors should consider diversifying their investment portfolio by allocating funds to other asset classes, such as equities, mutual funds, or real estate.
Online pharmacy: Indian Cert Pharm – indian pharmacy
Compare the leading WordPress hosting services in United States that offer fast, secure and scalable solutions to launch your website in no time.
legit canadian pharmacy online https://indiancertpharm.com/# Online pharmacy
indian pharmacies safe
Cristiano Ronaldo all personal cristiano-ronaldo-english.com/ trophies and awards. Cristiano Ronaldo – biography of the striker on the field of the Al-Nasr Riyadh football club and the Portuguese national team.
Thierry Henry’s biography thierry henry az org personal life, latest news of 2018, Instagram and coaching role for Belgium and Arsenal.
п»їbest mexican online pharmacies: Mexican Easy Pharm – mexican online pharmacies prescription drugs
Footballer Bukayo Saka’s biography bukayo-saka personal life, Nigerian heritage, religious views and girlfriend’s name. Salary, playing stats, jersey number, Euro appearances with England and matches with Arsenal. Latest news for 2024.
LeBron James’ biography lebron-james-az com covers his personal life, Lakers career, Cavaliers achievements, religion, statistics, film roles, and news for 2024.
buying prescription drugs in mexico online: mexico pharmacies prescription drugs – Mexican Easy Pharm
mexican pharmaceuticals online: Mexican Easy Pharm – mexico drug stores pharmacies
Eden Hazard’s biography eden-hazard-az.com/ covers his personal life with his wife Natasha Van Hoekere, his sons, his Chelsea career, his move to Real Madrid, injuries, surgeries, contract termination, retirement and 2024 updates
Biography of NBA star Giannis Antetokounmpo giannis-antetokounmpo-az.org/ personal life, marriage to Mariah Riddlesprigger, children, statistics and career with the Milwaukee Bucks. Flag bearer for Greece at the 2024 Paris Olympics.
James Harden biography james-harden photo, personal life, basketball, height, weight, sneakers, major achievements, latest news 2024.
Basketball player Jimmy Butler’s jimmy-butler-az.org/ biography: personal life, Selena Gomez relationship rumors, height, cars, idol stats, Miami Heat salary, injury news and his coffee brand. Latest news of 2024.
On the whole 57 commodities are recorded at the exchange including agricultural products, gold, energy, ferrous metals, ferrous metals and plastics.
п»їbest mexican online pharmacies: Mexican Easy Pharm – Mexican Easy Pharm
Biography of footballer Joshua Kimmich jimmy-butler personal life, wife and children. Career at Bayern Munich, statistics for Germany, work with Pep Guardiola, negotiations with Barcelona. Vice-captain at Euro 2024. Latest news for 2024.
Djokovic’s tennis career novak-djokovic-az org has been marked by numerous Grand Slam titles, showcasing his style of play. He has been a constant competitor to Rafael Nadal and Roger Federer.
Откройте мир мобильных игр games-ru рейтинги лучших проектов, тренды, советы и гайды. Играйте в популярные шутеры, RPG, стратегии и песочницы прямо на телефоне!
Свежие футбольные новости https://vseofootball.ru обзоры матчей, Лига чемпионов, статистика и лучшие букмекерские бонусы для ставок на спорт.
Все о Тони Кроосе toni-kroos на одном сайте: биография, актуальные новости, детальная статистика и эксклюзивные обновления о немецкой футбольной звезде. Присоединяйтесь к сообществу фанатов и будьте в курсе всех событий, связанных с Кроосом!
buying prescription drugs in mexico: mexican rx online – Mexican Easy Pharm
Indian Cert Pharm: Indian pharmacy international shipping – Best online Indian pharmacy
https://canadianmdpharm.com/# canadian pharmacies
canadian pharmacy prices
Погрузитесь в мир Lucky Jet lucky jet Узнайте все о захватывающем игровом автомате, его правилах, бонусах и стратегиях, чтобы увеличить свои шансы на выигрыш.
Погрузитесь в мир мотоспорта motorsport ru ru узнайте об истории, различных дисциплинах, передовых технологиях и легендарных гонщиках. Откройте для себя, что делает мотоспорт одним из самых захватывающих и динамичных видов спорта в мире.
Источник новостей о футболе futbol vpered сборной России, Кубке России, Лиге Европы и лучших букмекерских предложениях. Узнайте последние результаты, прогнозы и аналитику!
Самые свежие и актуальные volleyball новости мира волейбола. Мы следим за всеми ключевыми событиями, включая турниры, чемпионаты, кубковые встречи и важные клубные матчи.
Погрузитесь в захватывающий мир cleopatra slot ru Cleopatra Slot! Узнайте о правилах игры, бонусных функциях и стратегиях, чтобы увеличить свои шансы на выигрыш.
Best Indian pharmacy: IndianCertPharm – Best online Indian pharmacy
Mexican Easy Pharm: best online pharmacies in mexico – best online pharmacies in mexico
medication from mexico pharmacy: Mexican Easy Pharm – Mexican Easy Pharm
Online pharmacy: IndianCertPharm – indian pharmacy
сайт посвященный Aviator Slot aviator-slot.ru Узнайте последние новости, эффективные стратегии, советы по выигрышу и информацию о бонусах.
Захватывающий мир автоспорта autosport-ru.ru узнайте об истории, различных видах, передовых технологиях и выдающихся гонщиках. Откройте для себя, что делает автоспорт одним из самых динамичных и популярных видов спорта в мире.
Захватывающий мир UFC ufc-ru.ru узнайте об истории, основных правилах, стратегиях и легендарных бойцах. Откройте для себя, что делает UFC вершиной смешанных боевых искусств и почему этот спорт привлекает миллионы поклонников по всему миру.
Исследуйте Zeus vs Hades zeus-vs-hades-download ru Gods of War! Играйте бесплатно, получайте фриспины и узнайте все о слоте 2024 года!
Letters which will be duplicated for an present commodity symbol are usually not used.
Mexican Easy Pharm: Mexican Easy Pharm – Mexican Easy Pharm
cheapest pharmacy canada: canadian pharmacy meds review – onlinecanadianpharmacy
In Jodo Do Tigrinho online slots, every spin is a step towards victory! Incredible graphics, exciting themes and many bonuses await you. Fortune favors the brave – try your hand and discover the world of winnings with Tigrinho!
Cryptocurrency trading service bitqt with AI is automation and efficiency. Artificial intelligence monitors market dynamics, reduces risks and optimizes transactions. The perfect solution for beginners and professionals.
Откройте для себя Book of Ra Deluxe 10 book of ra deluxe 10 ru захватывающий игровой автомат, который перенесет вас в Древний Египет! Узнайте о правилах игры, бонусных функциях и стратегиях, чтобы увеличить свои шансы на выигрыш.
Погрузитесь в мир Le Bandit le-bandit-play.ru/ классического игрового автомата, который предлагает увлекательный игровой процесс и множество возможностей для выигрыша.
Исследуйте мир гимнастики gymnastics-ru.ru с новой перспективы – узнайте о её истории, различных дисциплинах, современных методах тренировок и выдающихся гимнастах.
Many passive funds are index funds, which attempt to replicate the efficiency of a market index by holding securities proportionally to their worth out there as an entire.
Погрузись в мир UFC boxing-ru ru узнайте об истории, основных правилах, стратегиях и легендарных бойцах. Откройте для себя, что делает UFC вершиной смешанных боевых искусств и почему этот спорт привлекает миллионы поклонников по всему миру.
Будьте в курсе последних sportinfo-ru.ru событий в мире спорта! Узнайте о самых горячих новостях, аналитике матчей, эксклюзивных интервью и прогнозах. Спортивные Новости — ваш надежный источник информации о любимых видах спорта и спортсменах.
Современные стратегии игры blackjack-players в блэкджек для начинающих, которые помогут вам быстро освоить игру и победить. Турниры, хорошая психология и новости.
At age fifty-four, he was appointed the primary design director and vice president of Tiffany & Co., taking on main roles in the famous jewellery agency as well as continuing in his own enterprises.
Откройте для себя Mega Joker mega-joker.ru увлекательный видеослот от NetEnt, который сочетает в себе ностальгическую атмосферу классических автоматов и современные возможности выигрыша.
Погрузитесь в мир Plinko plinko-ru увлекательной игры, основанной на случайности и стратегии! Узнайте правила, механики и стратегии для успешной игры, чтобы увеличить свои шансы на крупные выигрыши.
Откройте для себя мир starlight princess slot ru Starlight Princess Slot! На нашем сайте вы найдете свежие новости, стратегии для увеличения выигрышей и эксклюзивные бонусы.
Indian Cert Pharm: Online medicine – IndianCertPharm
Just by looking at the resultant shape, a trader can tell whether it’s wise to sell or buy; wait it out; or with how much risk they are acting.
Best online Indian pharmacy: top 10 online pharmacy in india – Indian Cert Pharm
Играйте в Gates of Olympus http://gates-of-olympus-download.ru бесплатная демо, высокие RTP, фриспины и бонусы ждут вас в мире мифологии!
Откройте для себя Starburst starburst-slot.ru один из самых популярных слотов от NetEnt! Наслаждайтесь красочной графикой, уникальными функциями и шансом на крупные выигрыши.
Погрузитесь в мир шахмат chess-ru ru узнайте историю игры, её основные правила, стратегии и влияние на культуру. Развивайте свои интеллектуальные способности через эту древнюю и элегантную игру.
Aviatrix game https://aviatrix-games.com/en/ has become a sensation in the world of crash games. Its unique format, featuring a rapidly growing multiplier and the possibility of an unexpected crash. Aviatrix crash game is at 1win, 1xbet, Mostbet, and Pin Up.
Погрузитесь в мир Wheel of Fortune http://wheel-of-fortune-slot.ru Узнайте все о знаменитом игровом автомате, его функциях, стратегиях и акциях. Играйте сейчас, испытайте удачу и выиграйте крупные призы, вращая барабаны в этом захватывающем слоте!
Mexican Easy Pharm: mexican rx online – mexico drug stores pharmacies
Погрузитесь в захватывающий мир formula-1-ru Формулы 1 — узнайте об истории, технологиях, легендарных пилотах и уникальных аспектах этого престижного автоспорта.
Захватывающий слот Lucky Jet lucky-jet-play-crash ru от Spribe с уникальной краш-механикой, который предлагает игрокам шанс испытать свою удачу и стратегическое мышление.
Захватывающий слот Lucky Jet https://lucky-jet-play-crash.ru от Spribe с уникальной краш-механикой, который предлагает игрокам шанс испытать свою удачу и стратегическое мышление.
Добро пожаловать на сайт redtigerplay ru посвященный слотам Red Tiger! Узнайте последние новости, стратегии для увеличения выигрышей и эксклюзивные бонусы.
Откройте для себя водное поло https://water-polo-ru.ru историю, правила, тактики и влияние этого захватывающего водного вида спорта. Узнайте, как динамика и стратегия сочетаются, делая водное поло уникальным и увлекательным.
canadian drugstore online: legitimate canadian pharmacies – canadian pharmacy tampa
Aviatrix game https://aviatrix-games.com/en/ has become a sensation in the world of crash games. Its unique format, featuring a rapidly growing multiplier and the possibility of an unexpected crash. Aviatrix crash game is at 1win, 1xbet, Mostbet, and Pin Up.
buying prescription drugs in mexico: best online pharmacies in mexico – mexican drugstore online
Angela Martinez is a self-described canine mom, model, and content material creator, but that’s not all that she can do.
online canadian pharmacy CanadianMdPharm ordering drugs from canada
Mexican Easy Pharm: buying prescription drugs in mexico online – mexico drug stores pharmacies
Both Russia and the European Union were also increasing chlorine production to stabilise world prices.
buy prescription drugs from canada cheap: buying drugs from canada – canadian pharmacy king
https://mexicaneasypharm.shop/# Mexican Easy Pharm
canadian discount pharmacy
Погрузитесь в мир покера poker-players-kz org с нашим сайтом о различных известных игроках. Изучите их карьеру, основные достижения, стратегии, психологию и секреты успеха.
Игровой слот Crazy Time crazy time play это захватывающий слот, который сочетает азартные ставки с элементами шоу. В этой игре вас ждут четыре уникальных бонусных раунда: Pachinko, Cash Hunt, Coin Flip и Crazy Time.
Откройте для себя Sweet Bonanza sweetbonanzaplay ru увлекательный видеослот от Pragmatic Play! Узнайте правила, стратегии и бонусные функции, чтобы увеличить свои шансы на крупные выигрыши. Погружайтесь в красочный мир сладостей и начните свое азартное приключение с Sweet Bonanza уже сегодня!
Исследуйте мир онлайн-игр online-games-ru.ru новости, обзоры, гайды, тренды и лучшие проекты. Погружайтесь в уникальные вселенные MMORPG, MOBA, шутеров и многого другого!
Погрузитесь в мир гольфа http://golf-ru.ru изучите его историю, правила, технику и влияние на культуру. Узнайте, как этот изысканный спорт сочетает в себе физическую выносливость и интеллектуальную стратегию, привлекая миллионы энтузиастов по всему миру.
Погрузитесь в захватывающий мир баккары baccarat-ru ru узнайте историю игры, её правила, стратегии и секреты успеха. Откройте для себя элегантность и интригу одной из самых престижных карточных игр казино.
Average true range – averaged daily trading range, adjusted for price gaps.
Узнайте все о слоте Колесо Фортуны wheel-of-fortune-ru.ru/ историю, особенности игры, стратегии выигрыша и советы для успешной игры.
Откройте для себя мир гандбола handball-ru.ru/ изучите историю игры, основные правила, ключевые стратегии и влияние на культуру.
Погрузитесь в увлекательный мир покера http://poker-ru.ru исследуйте его историю, правила, продвинутые стратегии и культурное влияние. Узнайте, как интеллект и интуиция объединяются в этом захватывающем карточном спорте.
Мир блэкджека http://blackjack-ru.ru узнайте историю игры, её правила, секретные стратегии и влияние на современную культуру. Откройте для себя глубину этой захватывающей карточной игры и научитесь побеждать с умом.
Indian Cert Pharm: Indian Cert Pharm – Online pharmacy
Best Indian pharmacy: Indian pharmacy that ships to usa – Indian pharmacy international shipping
Погрузитесь в захватывающий мир roulette ru ru рулетки — изучите историю игры, её правила, стратегические подходы и культурное влияние.
Погрузитесь в мир фигурного катания http://figure-skating-ru.ru исследуйте его историю, уникальные техники, знаменитых спортсменов и культурное влияние.
Ставки на скачки http://horse-racing-betting.kz с нашим сайтом, посвященным стратегии, аналитике и знаменитым игрокам. Узнайте о правилах, методах прогнозирования результатов, успешных стратегиях и вдохновляющих историях беттеров.
Откройте мир слотов https://biryulevo-zapadnoe.ru и казино-игр и ставок на спорт. Читайте обзоры, получайте советы и стратегии от экспертов, и будьте в курсе последних новостей из мира азартных игр и беттинга.
mexican mail order pharmacies https://mexicaneasypharm.shop/# Mexican Easy Pharm
medication from mexico pharmacy
global pharmacy canada: Canadian Md Pharm – rate canadian pharmacies
indian pharmacy Online medicine IndianCertPharm
Скачайте бесплатно книгу https://storitelling.ru по сторителлингу и узнайте, как создавать истории, которые цепляют с первых строк. Практические советы, примеры и вдохновение для всех, кто хочет освоить искусство рассказчика.
Indian pharmacy that ships to usa: Indian Cert Pharm – Online medicine
buying from online mexican pharmacy https://mexicaneasypharm.com/# Mexican Easy Pharm
best online pharmacies in mexico
IndianCertPharm: Indian Cert Pharm – Indian pharmacy international shipping
In interwar Germany, for instance, much personal and corporate debt was successfully wiped out-definitely for those holding fastened interest price loans.
purple pharmacy mexico price list https://mexicaneasypharm.shop/# Mexican Easy Pharm
mexican online pharmacies prescription drugs
No amount of guide studying or theoretical knowledge can ever absolutely put together you for playing the inventory marketplace for real.
Mexican Easy Pharm: mexico pharmacies prescription drugs – mexico pharmacies prescription drugs
Best online Indian pharmacy: Indian Cert Pharm – indian pharmacy
A bail bonds firm is an organization that can offer a monetary guarantee to the courtroom for the accused.
Dr. Hal Forsey and Dr.
1 July 1778: Through the Revolutionary Battle, Fort Jenkins (a patriot stockade in present-day West Pittston) surrendered to the British (underneath Major John Butler).
Сайт игровых промокодов промокоды на ggstandoff барабан бонусов это ваш доступ к эксклюзивным бонусам и скидкам. Бесплатные награды, внутриигровая валюта и уникальные акции ждут вас. Успейте воспользоваться всеми возможностями!
In the process, individual people and businesses will, for the first time, be able to directly benefit from their work.
lexapro and weight gain in stomach what is escitalopram used for
2-zero win in opposition to SPAL on the San Siro on 20 September.
Хотите раскрутить продвижение телеграм мы знаем, как это сделать! Поможем увеличить охваты, привлечь активную аудиторию и вывести ваш контент на новый уровень.
платная капельница на дому http://www.medlinks.ru/article.php?sid=110769
As baby boomers enter their retirement years and continue to age, there will be increased strain on the health care system in the decades to come.
Bangalore, the silicon city of India, has become the hub of kids who go abroad for education since the high number of entrepreneurs and high literacy rates in Karnataka.
As soon as you’ve completed your search, you can look by way of the ensuing record of lawyers and law firms and see their contact information, a profile, a listing of clients they’ve represented and different necessary data.
india pharmacies online: india pharmacy mail order trusted india online pharmacies
Free Spirit is the second studio album by American singer Khalid, released on April 5, 2019, through RCA Data.
Ищете промокоды для игр skinbox промокод наш сайт – ваш лучший помощник! Собираем актуальные игровые промокоды для бонусов, скидок и эксклюзивных наград.
Additionally, it is important to study the political issues and decisions by the central bank of the country regarding cryptocurrencies.
Участок в Мишкином Лугу http://мишкинлуг.рф/uchastki-mishkinlug по Симферопольскому шоссе — идеальное место для строительства! Тихий поселок, прекрасные виды, удобный подъезд и все условия для комфортной жизни.
Лисичкин Очаг возле Серпухова https://лисичкиночаг.рф/uchastki-lisichkinochag идеальные участки для вашего будущего дома! Живописная природа, хорошая транспортная доступность и возможность подключения всех коммуникаций ждут вас.
Участки в Лисичкином Очаге https://лисичкиночаг.рф неподалеку от Серпухова. Тихий, зеленый поселок с прекрасной природой и удобной транспортной доступностью. Здесь вы сможете построить комфортное жилье для себя и своей семьи.
https://canadianmdpharm.online/# reliable canadian pharmacy reviews
online canadian pharmacy reviews
buying prescription drugs in mexico https://mexicaneasypharm.com/# buying prescription drugs in mexico online
mexico drug stores pharmacies
Mexican Easy Pharm: Mexican Easy Pharm – mexican online pharmacies prescription drugs
Im obliged for the post. Will read on…
https://dappharm.shop/# buy priligy
Kamagra 100mg
A former companion of the Doctor, Victoria feels alone and stranded within the 20th century.
http://cytpharm.com/# Cyt Pharm
prednisone 5 mg tablet
SemaPharm24: semaglutide tablets store – SemaPharm24
Thank you ever so for you post.Really looking forward to read more. Keep writing.
Smoother, quieter, and sooner (high velocity was a genuine 100 mph), the 1600 offered like hotcakes, especially within the U.S.
This explains a number of texts earlier in the game which point out chlorine.
prednisone brand name in india: PredPharm – PredPharm
I’m not sure exactly why but this web site is loading extremely slow for me. Is anyone else having this issue or is it a issue on my end? I’ll check back later and see if the problem still exists.
Thank you ever so for you article post.Thanks Again. Will read on…
buy cytotec online: buy cytotec online – buy cytotec online
https://cytpharm.com/# buy cytotec pills online cheap
п»їkamagra
Отзывы о компаниях и работодателях https://potrebsojuz.ru в одном месте. Узнайте реальное мнение сотрудников и клиентов, чтобы принять правильное решение при выборе работы или услуг.
Roy Nigel Lewis, Collector, HM Board of Customs and Excise.
Комплексная юридическая помощь https://kramzenergo.ru для вас и вашего бизнеса. Анализ дел, представительство в судах, поддержка на всех этапах
Greetings! Very useful advice in this particular article! It’s the little changes which will make the largest changes. Many thanks for sharing!
https://cytpharm.shop/# CytPharm
prednisone 1 mg tablet
His proper hand maintains the beat, along with his left hand he takes out a cloth and runs it over his face.
generic rybelsus tabs SemaPharm24 buy rybelsus online
semaglutide tablets price: semaglutide tablets store – cheap semaglutide pills
William Temple Franklin, in addition to Benjamin Franklin himself.
So now let’s discuss the best share market tips.
Strengthening of the muscles.
All account sorts can ship and obtain cash, but the place PayPal appeals to people who want to make personal funds with security and flexibility, the company reaches out to professionals with a set of different merchandise, including online procuring carts, delivery help, and invoicing.
Kama Pharm: cheap kamagra – Kama Pharm
http://predpharm.com/# PredPharm
Kamagra Oral Jelly
витаминные капельницы лечение капельницами
para que sirve el bonus casino en 1win 1win register
bonus code 1win 1win telegram
priligy: buy priligy – dap pharm
https://cytpharm.shop/# Cytotec 200mcg price
non prescription prednisone 20mg
The summer season is heat, measured between days when freezing temperatures happen, starting in June – the final freezing temperature usually in early June – and ending in September.
Priligy tablets: buy dapoxetine online – cheap priligy
prednisone 300mg PredPharm prednisone brand name in usa
https://kamapharm.shop/# Kama Pharm
Kamagra 100mg price
Откройте для себя историю слова пацана кровь на асфальте смотреть онлайн честный взгляд на суровую реальность, где дружба и слово дороже всего. Уникальный проект о жизни без прикрас и ценности принципов.
PredPharm: where can i order prednisone 20mg – average price of prednisone
DapPharm: dapoxetine online – Priligy tablets
http://dappharm.com/# Priligy tablets
prednisone buy no prescription
https://dappharm.shop/# priligy
buy Kamagra
Great wordpress blog here.. It’s hard to find quality writing like yours these days. I really appreciate people like you! take care
PredPharm 10mg prednisone daily Pred Pharm
CytPharm: order cytotec online – Cyt Pharm
Kamagra tablets: п»їkamagra – Kama Pharm
http://predpharm.com/# prednisone 20mg by mail order
prednisone 20 mg without prescription
киного исторические фильмы киного российские сериалы
kinogo лучшие фильмы по комиксам kinogo без регистрации
prednisone 2.5 tablet: Pred Pharm – prednisone 10
киного сериалы про врачей kinogo кинокомиксы
Kama Pharm: Kamagra 100mg price – Kama Pharm
http://dappharm.com/# dap pharm
buy Kamagra
St Mary’s Church Lynton, Devon 1907 Whall completed a lancet in the North Chapel of St Mary’s entitled “St Anne and the Virgin”.
PredPharm prednisone 10 mg price prednisone 10 tablet
PurDentix is a dietary supplement formulated to support oral health by blending probiotics and natural ingredients.
semaglutide tablets store: buy semaglutide – semaglutide best price
PurDentix is a revolutionary oral health supplement designed to support strong teeth and healthy gums. It tackles a wide range of dental concerns, including gum inflammation and tooth decay, while promoting a balanced oral microbiome.
At twenty-5, I had an internship at the Italian Ministry of Foreign Affairs (I was studying Communication and then Cooperation to Development at the college).
Sema Pharm 24: semaglutide best price – Sema Pharm 24
https://dappharm.shop/# Priligy tablets
Kamagra 100mg price
http://semapharm24.com/# Sema Pharm 24
generic prednisone online
Visit the Johnson Space Center in Houston, Texas and you’ll find some magnificent steers grazing within a few hundred yards of a Saturn V Rocket.
buy cytotec online: buy cytotec online – buy cytotec online
buy dapoxetine online priligy dap pharm
10 homes of worship, including: American Presbyterian Church, B’nai Abraham Synagogue, Christ Episcopal Church, Dorothea Dix Unitarian Universalist Group, Ebenezer Full Gospel Neighborhood Church, First Baptist Church of Bordentown, First Presbyterian Church, Mount Zion AME Church, Saint Mary’s Roman Catholic Church, Shiloh Baptist Church, Trinity United Methodist Church and Union Baptist Church.
buy dapoxetine online: cheap priligy – cheap priligy
http://predpharm.com/# prednisolone prednisone
buy kamagra online usa
This web site definitely has all the information and facts I needed concerning this subject and didn’t know who to ask.
Откройте для себя blacksprut возможности даркнет-рынка с тысячами предложений. Быстрая регистрация, надежные сделки и анонимность на каждом этапе.
Лучшее онлайн казино https://1wincasino.pl Огромный выбор автоматов, настольных игр и live-казино. Уникальные акции, приветственные бонусы и мгновенные выплаты сделают вашу игру еще интереснее.
Lawrence, Mike. Step-by-Step Outside Stonework.
Misoprostol 200 mg buy online: buy cytotec online – Cyt Pharm
текст песни где ты https://faav.ru
SemaPharm24: Sema Pharm 24 – semaglutide tablets store
https://semapharm24.shop/# buy rybelsus online
buy prednisone 10mg online
Avon, Jack. (2021). The Handbook of Financial Modeling (2nd ed.).
https://semapharm24.com/# SemaPharm24
Kamagra 100mg
buy misoprostol over the counter order cytotec online buy cytotec online
лайка для охоты охотничьи базы
Different activities and events additionally strengthen the work culture in an organisation.
buy cytotec online fast delivery: Cyt Pharm – buy cytotec online fast delivery
CytPharm: buy cytotec online – buy misoprostol over the counter
https://dappharm.shop/# dapoxetine price
buy Kamagra
A third principal fiscal statement – the money waft statement – can also be regarded.
http://cytpharm.com/# buy cytotec online fast delivery
prednisone 20 mg in india
prednisone 20 mg tablet price: cost of prednisone 40 mg – Pred Pharm
Sema Pharm 24: semaglutide best price – buy rybelsus online
https://cytpharm.com/# CytPharm
sildenafil oral jelly 100mg kamagra
CytPharm CytPharm CytPharm
apartments in pineville nc mission peak apartments avant apartments
Small farmers endured crop failures, and the mills that drove the region’s economy remained closed.
semaglutide tablets: cheap semaglutide pills – semaglutide tablets price
how much is prednisone 5mg: buy prednisone online india – PredPharm
https://kamapharm.com/# buy kamagra online usa
Kamagra 100mg
Currently it looks like Expression Engine isthe preferred blogging platform available right now.(from what I’ve read) Is that what you are using on your blog?
https://dappharm.com/# Priligy tablets
prednisone 5 mg tablet
Университет ресторанного бизнеса https://upskilll.ru/university UPSKILL: обучаем рестораторов, управляющих и сотрудников ресторанов, полностью адаптируя наши курсы, тренинги и программы обучения под особенности каждого заведения.
Appanail is a cutting-edge dietary supplement specifically designed to nourish and improve the overall health of your nails and feet.
buy rybelsus online: semaglutide tablets for weight loss – rybelsus semaglutide tablets
ремонт стиральных машин на дому цены ремонт стиральных машин самсунг
dap pharm: Priligy tablets – cheap priligy
Cyt Pharm cytotec online CytPharm
https://dappharm.com/# cheap priligy
п»їkamagra
By contacting APFM, you’re availing your self of our core service, which is providing customized referrals to assisted dwelling and residence care amenities, who will contact you by phone (together with text, which may be auto-dialed), that will help you determine which facility best meets your wants, or the wants of your liked one.
That mentioned, it still took a bit of time to understand how this ball will get rolling.
DapPharm: cheap priligy – dapoxetine price
https://cytpharm.com/# CytPharm
drug prices prednisone
Sema Pharm 24: semaglutide tablets price – Sema Pharm 24
University of Stirling Archives: Thomson, Jackson, Gourlay & Taylor C.A.
http://kamapharm.com/# cheap kamagra
sildenafil oral jelly 100mg kamagra
You might wonder why hiring a financial advisor with fiduciary role is so important.
dapoxetine online: buy priligy – buy dapoxetine online
SemaPharm24 semaglutide tablets rybelsus semaglutide tablets
buy cytotec online: CytPharm – CytPharm
https://cytpharm.shop/# CytPharm
Kamagra 100mg price
Платформа Курьер Купер https://cash-kuper.ru открывает возможности для работы в доставке. Свободный график, прозрачная система оплаты и заказы поблизости – идеальный выбор для тех, кто ищет подработку или основной заработок.
20 mg of prednisone: Pred Pharm – PredPharm
Investment managers who specialize in advisory or optional management on behalf of (normally wealthy) private investors may often refer to their services as wealth management or portfolio management often within the context of so-called “private banking”.
dapoxetine online: DapPharm – buy dapoxetine online
Chrysler offered its 426 Hemi engine briefly and in very restricted numbers in some ’65 Mopar intermediates, but with 12.5:1 compression and competition-grade tuning, it was too high-strung for the street.
Thank you for sharing your thoughts. I truly appreciate yourefforts and I will be waiting for your further post thanks once again.
SemaPharm24: semaglutide tablets – semaglutide best price
http://cytpharm.com/# Abortion pills online
buy kamagra online usa
This agency is led by its properly knowledgeable and informative employees members, who works dedicately and smartly to offer you the desired results that you want for.
Kama Pharm Kama Pharm Kama Pharm
The Predator was also recognized for its ability to stay airborne for lengthy durations, making it appropriate for surveillance missions that required prolonged loitering occasions.
Cyt Pharm: buy cytotec online – cytotec abortion pill
https://cytpharm.shop/# CytPharm
prednisone brand name
The website content written in them not only helps in ensuring increased number of customers but also we can target a certain section among them just by adjusting certain parameters of it.
dapoxetine price: buy dapoxetine online – Priligy tablets
kush shop in prague https://shop-cannabis-prague.com
Kama Pharm: buy kamagra online usa – Kama Pharm
ремонт водонагревателя аристон 100 ремонт водонагревателей
420 movement in prague buy cali weed in prague
Euromoney’s bi-annual country risk index monitors the political and economic stability of 185 sovereign countries, with Singapore emerging as the least risky country since 2017 – it is also one of the only few countries in the world as well as the only in Asia to achieve a AAA sovereign credit rankings from all major credit agencies.
https://cytpharm.shop/# buy cytotec online
Kamagra 100mg
PredPharm: 6 prednisone – prednisone 10mg cost
http://cytpharm.com/# п»їcytotec pills online
prednisone 1 mg daily
проверка микрозаймов онлайн взять микрокредит в Казахстане
By staying dedicated to managing your anxiety, you may regain control of your life and expertise better peace and properly-being.
CytPharm: cytotec online – CytPharm
During one of the most iconic scenes in the film franchise, the crew drives matching Black Honda Civic coupes in the freeway height scene.
buy priligy priligy buy dapoxetine online
Additional briefing could also be conducted in other areas of the ship depending on the mission kind.
Sema Pharm 24: buy semaglutide – buy rybelsus online
It is vital to understand the significance of healthy relationships, whereas also actively working on nurturing and maintaining these connections.
SemaPharm24: SemaPharm24 – buy rybelsus online
https://dappharm.com/# Priligy tablets
prednisone 20mg online
Japan’s Financial Development Slowed Once more Part 2: Shaw Capital Administration Korea – This has raised concern that the nation’s economic recovery might come to a standstill in the latter half of the fiscal 12 months in the midst of an evident international slowdown of restoration.
https://semapharm24.com/# buy semaglutide
sildenafil oral jelly 100mg kamagra
PredPharm: medicine prednisone 10mg – prednisone 1 tablet
Many practical algorithms are in fact quite simple arbitrages which could previously have been performed at lower frequency-competition tends to occur through who can execute them the fastest rather than who can create new breakthrough algorithms.
prednisone without a prescription: Pred Pharm – PredPharm
Calif., who died there Tuesday.
Company events, conferences, exhibitions and commerce shows are alternatives for companies to maintain an open dialogue between current and prospective clients.
You may get some attention-grabbing answers for a few of them.
Sema Pharm 24: semaglutide best price – Sema Pharm 24
SemaPharm24 buy semaglutide rybelsus semaglutide tablets
https://dappharm.com/# buy dapoxetine online
purchase prednisone from india
Открывайте кейсы CS:GO https://www.facebook.com/people/Hotdrop_CSGO/61550490187523/ с крутыми шансами на редкие скины. Удобный интерфейс, надежная система и огромный выбор кейсов сделают игру еще интереснее. Начните свой путь к топовым скинам прямо сейчас!
Ovals of more than one mile in length are considered superspeedways, because the longer straightaways allow the cars to reach higher speeds.
https://farmabrufen.shop/# BRUFEN prezzo
farmaci senza ricetta elenco
http://farmaprodotti.com/# Farmacie on line spedizione gratuita
farmacie online affidabili
farmacie online autorizzate elenco: FarmaBrufen – п»їFarmacia online migliore
farmacie online sicure
farmacia online piГ№ conveniente: Cialis senza ricetta – comprare farmaci online con ricetta
Newspapers covering Market Deeping, based in larger towns nearby, are the Stamford Mercury, the Lincolnshire Free Press and the Peterborough Telegraph.
https://farmasilditaly.com/# viagra cosa serve
farmacie online affidabili
Откройте яркие кейсы CS:GO https://m.youtube.com/@hotdrop-case и получите шанс выиграть топовые скины! Широкий выбор кейсов, высокий шанс дропа и честная система обеспечат увлекательный опыт.
Inpatient therapy services could present a structured and intensive approach to handle Antisocial Persona Disorder (ASPD) alongside substance abuse or different coexisting conditions.
https://farmabrufen.com/# FarmaBrufen
farmacie online autorizzate elenco
top farmacia online Cialis generico farmaci senza ricetta elenco
farmacie online affidabili: FarmTadalItaly – acquistare farmaci senza ricetta
migliori farmacie online 2024
farmacie online autorizzate elenco: Cialis generico farmacia – Farmacia online piГ№ conveniente
Пробуйте удачу https://discord.com/invite/B5fF6pW8Cm CS:GO! Шанс получить редкие и дорогие скины, широкий выбор кейсов и удобный интерфейс делают процесс открытия легким и захватывающим.
In a pharmaceutical industry, this duty is predominantly assigned to the risk administration program supervisor.
https://farmabrufen.shop/# BRUFEN prezzo
farmacia online senza ricetta
Рискни и испытай удачу https://t.me/hotdropcases Шанс получить редкие и дорогие скины, широкий выбор кейсов и удобный интерфейс делают процесс открытия легким и захватывающим.
Farmacia online piГ№ conveniente: Ibuprofene 600 prezzo senza ricetta – migliori farmacie online 2024
Farmacia online piГ№ conveniente
Ваши любимые кейсы CS:GO кс кейсы в одном месте! Большой выбор, удобный интерфейс и высокая вероятность выпадения редких предметов делают процесс открытия кейсов по-настоящему захватывающим.
farmacia online piГ№ conveniente: migliori farmacie online 2024 – top farmacia online
https://farmatadalitaly.shop/# acquisto farmaci con ricetta
farmacie online affidabili
Сервис бытовых услуг https://gidrostok-servis.ru это удобное решение для любых домашних задач. Уборка, ремонт, сантехника, установка техники и многое другое. Надежные специалисты, быстрое выполнение и доступные цены!
https://farmatadalitaly.shop/# farmacie online affidabili
farmacie online affidabili
Farmacie online sicure comprare farmaci online all’estero comprare farmaci online all’estero
farmaci senza ricetta elenco: FarmTadalItaly – comprare farmaci online all’estero
comprare farmaci online all’estero
farmacia online: Farma Prodotti – Farmacie online sicure
Keep reading to learn more concerning the indicators of a toxic friendship, and methods to take action.
http://farmatadalitaly.com/# farmacie online affidabili
farmacia online piГ№ conveniente
https://farmabrufen.com/# Ibuprofene 600 prezzo senza ricetta
п»їFarmacia online migliore
So, right here we assist make it a bit easier for you by listing out the ways to decide on a greatest mangalsutra.
comprare farmaci online con ricetta: Cialis generico farmacia – п»їFarmacia online migliore
comprare farmaci online all’estero
Farmacia online piГ№ conveniente: FarmaBrufen – migliori farmacie online 2024
viagra cosa serve viagra senza prescrizione viagra generico recensioni
By 1949, with the release of the Cinderella soundtrack, Disney began making its approach into mainstream music.
http://farmatadalitaly.com/# farmacie online affidabili
comprare farmaci online all’estero
лучшие корейские дорамы онлайн фильмы онлайн-кинотеатр HD-720 в хорошем качестве
Нужны деньги срочно займы с быстрым одобрением и моментальным переводом на карту. Минимум документов, удобные условия и прозрачные ставки. Оформите займ прямо сейчас!
https://farmasilditaly.shop/# alternativa al viagra senza ricetta in farmacia
farmacie online affidabili
новинки Netflix 2025 в хорошем качестве новые сериалы 2025 бесплатно
farmacie online autorizzate elenco: Farma Prodotti – Farmacie on line spedizione gratuita
farmacie online autorizzate elenco
п»їFarmacia online migliore: Farma Prodotti – farmaci senza ricetta elenco
Most significantly, you not have access to mortgage forgiveness.
Промокоды для игр https://esportpromo.com/standoff/ это бесплатные бонусы, скидки и эксклюзивные награды! Находите актуальные коды, используйте их и получайте максимум удовольствия от игры без лишних затрат.
Лучшие игровые промокоды standoff промокоды на кейсы в одном месте! Активируйте бонусы, получайте подарки и прокачивайте аккаунт без лишних затрат. Следите за обновлениями, чтобы не пропустить новые промо!
https://farmasilditaly.com/# viagra 50 mg prezzo in farmacia
Farmacie online sicure
Нужны деньги срочно заем с быстрым одобрением и моментальным переводом на карту. Минимум документов, удобные условия и прозрачные ставки. Оформите займ прямо сейчас!
le migliori pillole per l’erezione: pillole per erezioni fortissime – viagra subito
acquistare farmaci senza ricetta
comprare farmaci online con ricetta FarmaBrufen acquistare farmaci senza ricetta
Лучшие игровые промокоды промокоды на кейсы в ггстандофф в одном месте! Активируйте бонусы, получайте подарки и прокачивайте аккаунт без лишних затрат. Следите за обновлениями, чтобы не пропустить новые промо!
Just print out the pages need on your private use and get started monitoring your debt payoff progress!
Farmacie online sicure: Cialis senza ricetta – farmacie online affidabili
In 1889 she married Jack Stirritt, a stockman and for 33 years lived on his ranch northwest of Odessa within the Marlin district.
Better Pittston is a 65.35 sq mi (169.3 km2) area in Luzerne County, Pennsylvania, encompassing the Susquehanna River.
This post is full of thoughtful ideas! You’ve presented everything in a clear, engaging way. For those who are interested in similar content, Market Capitalization might offer further insights.
What Significance Dividend Dates Have in UK Dividend Paying Stocks?
In 1890, he won a match towards Charles Moehle 7½-6½ in New York, took 2nd place on the St.
Промокоды для игр https://esportpromo.com/standoff/ это бесплатные бонусы, скидки и эксклюзивные награды! Находите актуальные коды, используйте их и получайте максимум удовольствия от игры без лишних затрат.
https://farmabrufen.shop/# Brufen senza ricetta
comprare farmaci online con ricetta
Лучшие игровые промокоды промокоды на гг стандофф в одном месте! Активируйте бонусы, получайте подарки и прокачивайте аккаунт без лишних затрат. Следите за обновлениями, чтобы не пропустить новые промо!
Бесплатные промокоды https://playpromocode.com/cs2/csgoempire/ для ваших любимых игр! Получайте монеты, бустеры, скины и другие ценные награды. Мы собираем только проверенные коды и обновляем их каждый день.
migliori farmacie online 2024: Tadalafil generico migliore – comprare farmaci online con ricetta
comprare farmaci online all’estero
Lattice model (finance) 搂 Interest rate derivatives.
Moreover, once SMB and HML are defined, the corresponding coefficients bs and bv are determined by linear regressions and can take negative values as well as positive values.
Хотите проверить компанию https://innproverka.ru по ИНН? Наш сервис поможет узнать подробную информацию о юридических лицах и ИП: статус, финансы, руководителей и возможные риски. Защищайте себя от ненадежных партнеров!
migliori farmacie online 2024: BRUFEN prezzo – Farmacia online miglior prezzo
This is often where startup traders drop money because they can only trade in a momentum market or an up market.
Недвижимость на Северном Кипре https://iberiaproperty.ru выгодные инвестиции и комфортная жизнь у моря. Апартаменты, виллы и пентхаусы по доступным ценам. Поможем выбрать лучший вариант и оформить покупку.
удобный маркетплейс bs2best с высоким уровнем анонимности и надежной системой защиты. Интуитивный интерфейс, проверенные продавцы и безопасные сделки делают его лучшим выбором для покупок.
https://farmasilditaly.shop/# viagra 100 mg prezzo in farmacia
farmacie online autorizzate elenco
If you would rather have your money grow for future use, then go ahead and choose the growth option.
farmaci senza ricetta elenco: FarmTadalItaly – farmaci senza ricetta elenco
farmacia online piГ№ conveniente
The license plate is non-transferable to every other particular person, but may be transferred from one automobile to a different owned by the veteran, supplied the Louisiana Department of Public Security is furnished the appropriate info regarding the opposite car.
comprare farmaci online all’estero Brufen senza ricetta Farmacia online piГ№ conveniente
Раскрутка в соцсетях https://nakrytka.com без лишних затрат! Привлекаем реальную аудиторию, повышаем охваты и активность. Эффективные инструменты для роста вашего бренда.
Хотите проверить компанию https://innproverka.ru по ИНН? Наш сервис поможет узнать подробную информацию о юридических лицах и ИП: статус, финансы, руководителей и возможные риски. Защищайте себя от ненадежных партнеров!
Like all good performance automobile, there’s extra to it than simply its engine.
After all, the S90 additionally has plenty of fun technology too, notably a 9 inch contact display screen related car system with Bluetooth for connecting all of your units and usually feeling that you just management the universe.
Each area of India is well-known for its personal bangles designs.
п»їFarmacia online migliore: BRUFEN prezzo – п»їFarmacia online migliore
https://farmasilditaly.shop/# viagra 100 mg prezzo in farmacia
Farmacia online miglior prezzo
п»їFarmacia online migliore: BRUFEN 600 acquisto online – п»їFarmacia online migliore
farmacie online sicure
Hedge funds typically commerce stocks but may trade or put money into anything depending on the fund.
Раскрутка в соцсетях https://nakrytka.com без лишних затрат! Привлекаем реальную аудиторию, повышаем охваты и активность. Эффективные инструменты для роста вашего бренда.
Great info. Lucky me I came across your site by chance (stumbleupon). I’ve saved it for later.
siti sicuri per comprare viagra online: Viagra – cerco viagra a buon prezzo
https://farmabrufen.shop/# Farma Brufen
farmacie online affidabili
Polkuamdee, Nuntawun (5 February 2021).
farmacie online affidabili: Ibuprofene 600 prezzo senza ricetta – farmacia online piГ№ conveniente
migliori farmacie online 2024
п»їFarmacia online migliore farmacie online autorizzate elenco acquisto farmaci con ricetta
увлекательный сериал однажды в сказке смотреть онлайн о жизни сказочных персонажей в реальном мире. Интригующий сюжет, волшебные события и неожиданные тайны. Смотрите онлайн в высоком качестве прямо сейчас!
farmacie online affidabili: Cialis senza ricetta – Farmacie online sicure
https://farmasilditaly.shop/# miglior sito dove acquistare viagra
п»їFarmacia online migliore
Farmacie on line spedizione gratuita: FarmTadalItaly – farmacie online affidabili
Farmacia online piГ№ conveniente
Farmacia online piГ№ conveniente: Ibuprofene 600 prezzo senza ricetta – farmacie online autorizzate elenco
https://farmabrufen.shop/# Brufen senza ricetta
comprare farmaci online all’estero
top farmacia online Brufen senza ricetta acquisto farmaci con ricetta
viagra online spedizione gratuita: cialis farmacia senza ricetta – viagra 50 mg prezzo in farmacia
acquisto farmaci con ricetta
доставка самолетом москва https://bvs-logistica.com/aviaperevozki.html
Farmacia online piГ№ conveniente: Cialis generico prezzo – farmacie online affidabili
Интернет-магазин товаров https://vitasleep.ru для здорового сна. В ассортименте: ортопедические матрасы, подушки, одеяла, постельное белье и аксессуары от проверенных брендов. Удобный выбор, доставка по России, гарантия качества. Забота о вашем комфорте и здоровом сне!
https://farmasilditaly.shop/# cerco viagra a buon prezzo
п»їFarmacia online migliore
When i write a tune, all of it comes out without delay – I hear all of the music in my head as I am writing the lyrics, which usually come to me in anyplace from 15 minutes to an hour or so.
cialis farmacia senza ricetta: Farma Sild Italy – viagra prezzo farmacia 2023
comprare farmaci online all’estero
п»їFarmacia online migliore: Ibuprofene 600 prezzo senza ricetta – Farmacia online piГ№ conveniente
лучшие сериалы 2023 смотреть онлайн https://lordseriall.org
смотреть сериал регистрация https://lordserial4.top
сериалы 2023 смотреть онлайн https://lordserials2.net
https://farmabrufen.com/# Ibuprofene 600 prezzo senza ricetta
farmacie online autorizzate elenco
farmacia online senza ricetta Ibuprofene 600 prezzo senza ricetta farmacia online senza ricetta
miglior sito dove acquistare viagra: FarmaSildItaly – cialis farmacia senza ricetta
acquistare farmaci senza ricetta
сериал языке смотреть онлайн https://lordserial7.com
смотреть сериал все серии подряд смотреть зарубежные сериалы онлайн бесплатно
сериал онлайн бесплатно серии смотреть зарубежные сериалы онлайн
Farmacie on line spedizione gratuita: Farma Brufen – farmaci senza ricetta elenco
https://farmabrufen.shop/# Brufen senza ricetta
п»їFarmacia online migliore
alternativa al viagra senza ricetta in farmacia: FarmaSildItaly – viagra originale in 24 ore contrassegno
acquisto farmaci con ricetta
Now is the theme of thinking that the way in which agricultural products are valued not by any amount to the worth of cash is nice for commerce cornerstone on-line.
The bottom price on the sell facet is $15.20, and the best value on the purchase aspect is $15.15.
viagra online spedizione gratuita: pillole per erezioni fortissime – viagra ordine telefonico
Farmacie on line spedizione gratuita
Логистические услуги в Москве https://bvs-logistica.com доставка, хранение, грузоперевозки. Надежные решения для бизнеса и частных клиентов. Оптимизация маршрутов, складские услуги и полный контроль на всех этапах.
смотреть сериалы подряд https://lordserialss.life
Individuals with PDD might expertise ongoing emotions of sadness, low vanity, and a normal sense of dissatisfaction.
лучшие сериалы 2023 смотреть онлайн https://lordsserial.xyz
http://farmasilditaly.com/# viagra online spedizione gratuita
farmacia online
Las ganancias son una gran motivaciГіn.: jugabet casino – jugabet chile
La diversiГіn nunca se detiene en los casinos.: winchile – winchile casino
Хотите почувствовать азарт? arkada casino автоматы предлагает широкий выбор игр, честную систему выигрышей и мгновенные выплаты. Захватывающие слоты и бонусы ждут вас!
смотреть лучшие сериалы первым https://lordserialss.life
Логистические услуги в Москве https://bvs-logistica.com доставка, хранение, грузоперевозки. Надежные решения для бизнеса и частных клиентов. Оптимизация маршрутов, складские услуги и полный контроль на всех этапах.
https://phtaya.tech/# Slot machines attract players with big jackpots.
Loyalty programs reward regular customers generously.
La pasiГіn por el juego une a personas.: jugabet.xyz – jugabet casino
La Г©tica del juego es esencial.: jugabet – jugabet casino
The casino industry supports local economies significantly. https://taya777.icu/# Many casinos offer luxurious amenities and services.
смотреть сериал подряд бесплатно https://lordseriall6.org
смотреть сериалы 2022 сезон https://lordsserials.org
смотреть лучшие сериалы все сезоны https://lordserial5.pet
phtaya [url=http://phtaya.tech/#]phtaya casino[/url] The casino industry supports local economies significantly.
http://jugabet.xyz/# Los casinos garantizan una experiencia de calidad.
Many casinos have beautiful ocean views.
One solution is to start a home business, and begin a personal journey toward financial independence.
La historia del juego en Chile es rica.: winchile casino – winchile
Live dealer games enhance the casino experience.: taya365.art – taya365 com login
Players can enjoy high-stakes betting options. https://taya365.art/# Online gaming is also growing in popularity.
http://jugabet.xyz/# La historia del juego en Chile es rica.
Casinos offer delicious dining options on-site.
Gambling regulations are strictly enforced in casinos.: taya777 – taya777 login
Some casinos have luxurious spa facilities.: phtaya login – phtaya casino
Check out Sellvia https://www.instagram.com/sellvia.dropshipping/ on Instagram for the hottest product ideas, store upgrades, and exclusive deals! Stay in the loop with our latest dropshipping tips and grab promo coupons to boost your business.
Many casinos host charity events and fundraisers. http://phmacao.life/# Live dealer games enhance the casino experience.
http://phmacao.life/# Some casinos have luxurious spa facilities.
The Philippines offers a rich gaming culture.
phmacao club phmacao com Many casinos provide shuttle services for guests.
http://phtaya.tech/# Resorts provide both gaming and relaxation options.
Resorts provide both gaming and relaxation options.
Manila is home to many large casinos.: taya777 – taya777.icu
Los jugadores disfrutan del pГіker en lГnea.: winchile – win chile
Cashless gaming options are becoming popular. https://taya365.art/# Slot machines attract players with big jackpots.
http://taya365.art/# Players must be at least 21 years old.
The poker community is very active here.
Es comГєn ver jugadores sociales en mesas.: win chile – winchile
taya365 com login taya365.art Many casinos have beautiful ocean views.
La Г©tica del juego es esencial.: winchile – winchile
Gambling regulations are strictly enforced in casinos. http://phmacao.life/# Casinos offer delicious dining options on-site.
http://phtaya.tech/# The casino scene is constantly evolving.
The ambiance is designed to excite players.
Las apuestas deportivas tambiГ©n son populares.: winchile.pro – winchile
Game rules can vary between casinos.: phmacao com – phmacao com
The Philippines offers a rich gaming culture. http://phtaya.tech/# Slot machines feature various exciting themes.
http://phtaya.tech/# Visitors come from around the world to play.
Resorts provide both gaming and relaxation options.
The full special bip39 Word List consists of 2048 words used to protect cryptocurrency wallets. Allows you to create backups and restore access to digital assets. Check out the full list.
winchile winchile casino La adrenalina es parte del juego.
п»їLos casinos en Chile son muy populares.: jugabet casino – jugabet casino
https://jugabet.xyz/# Las mГЎquinas tienen diferentes niveles de apuesta.
Slot machines feature various exciting themes.
Las experiencias son Гєnicas en cada visita.: jugabet – jugabet chile
Security measures ensure a safe environment. https://phtaya.tech/# Casino promotions draw in new players frequently.
The full special bip39 Word List consists of 2048 words used to protect cryptocurrency wallets. Allows you to create backups and restore access to digital assets. Check out the full list.
http://phtaya.tech/# The gaming floors are always bustling with excitement.
Live dealer games enhance the casino experience.
The casino scene is constantly evolving.: taya365.art – taya365.art
Players can enjoy high-stakes betting options.: taya777 login – taya777.icu
Reliable and unique bip39 Word List contains 2048 words needed to create seed phrases in crypto wallets. Allows you to safely manage private keys and guarantees the possibility of recovering funds.
Slot machines attract players with big jackpots. http://jugabet.xyz/# Los casinos ofrecen entretenimiento en vivo.
phtaya casino phtaya casino Gambling can be a social activity here.
https://taya777.icu/# Many casinos provide shuttle services for guests.
A variety of gaming options cater to everyone.
Los casinos celebran festivales de juego anualmente.: winchile – winchile casino
Players often share tips and strategies.: phtaya casino – phtaya.tech
The casino scene is constantly evolving. http://phtaya.tech/# Some casinos have luxurious spa facilities.
https://taya777.icu/# Gaming regulations are overseen by PAGCOR.
The poker community is very active here.
Gaming regulations are overseen by PAGCOR.: phmacao club – phmacao.life
Cashless gaming options are becoming popular.: taya365.art – taya365 com login
As an example, the prices of gasoline and car upkeep can add up quickly.
http://phmacao.life/# Entertainment shows are common in casinos.
The Philippines has several world-class integrated resorts.
taya777 app taya777 register login Manila is home to many large casinos.
Reliable and unique bip39 Word List contains 2048 words needed to create seed phrases in crypto wallets. Allows you to safely manage private keys and guarantees the possibility of recovering funds.
marijuana, marijuana in prague Cannabis delivery in Prague
1xBet promo code http://novaforce.ro.c50.previewmysite.eu/?p=556494 your chance to get bonuses on bets, free bets and exclusive promotions! Enter the code during registration and start playing with an increased deposit.
http://taya777.icu/# The casino atmosphere is thrilling and energetic.
Players enjoy a variety of table games.
Many casinos have beautiful ocean views.: phmacao com – phmacao club
Live dealer games enhance the casino experience.: phtaya casino – phtaya.tech
thc gummies shop in prague buy cannabis in Prague
Ремонт компьютеров и ноутбуков https://remcomp89.ru в Новом Уренгое – быстрые и качественные услуги! Диагностика, настройка, замена комплектующих, восстановление данных. Гарантия на работу, доступные цены и выезд мастера!
https://jugabet.xyz/# La Г©tica del juego es esencial.
Casinos often host special holiday promotions.
Many casinos provide shuttle services for guests.: taya365 com login – taya365 com login
La mayorГa acepta monedas locales y extranjeras.: winchile casino – win chile
Играйте в аркадные игры в лучшем онлайн казино | Новые аркадные игры каждую неделю | Онлайн казино для ценителей аркадных игр | Насладитесь азартом в аркадном казино | Играйте в увлекательные аркады и выигрывайте призы | Играйте в аркадные игры и выигрывайте деньги | Азартные аркады для всех желающих | Азарт и аркады в одном месте | Играйте в аркадные игры и ощутите азарт | Играйте в аркадные игры и выигрывайте деньги | Аркадные развлечения и выигрыши в онлайн казино | Побеждайте в аркадных баталиях и зарабатывайте деньги | Играйте в аркадные игры и выигрывайте деньги | Аркадные развлечения и азарт вместе | Побеждайте в аркадах и получайте денежные призы | Побеждайте в аркадных играх и получайте призы
бонус код arkada casino arkada casino бонусы для новичков .
Then flush the bathroom to drain the tank.
phtaya casino phtaya Online gaming is also growing in popularity.
whispeara is a premium, all-natural supplement crafted to support and enhance both hearing and cognitive function.
Make the most of rising funding tendencies to allow your portfolio to capture most benefits from the market cycles.
New Hampshire International Speedway first support: First-assist stations are positioned in the main, Concord, and Laconia grandstands.
http://phmacao.life/# The ambiance is designed to excite players.
Online gaming is also growing in popularity.
Looking for the current spinbetter promo code? Get bonus funds for bets and casino games. Easy activation, favorable conditions and real winnings are waiting for you. Hurry to use it!
Используйте актуальный промокод 1xbet и получите увеличенный бонус на первый депозит! Делайте ставки на спорт, играйте в казино и пользуйтесь эксклюзивными предложениями. Легкая регистрация и моментальные выплаты!
Urban design should aim to create inclusive and welcoming public spaces that encourage socialization and community engagement.
Because Apple’s iOS is a closed source platform, not like the open supply Android, it is harder to focus on with viruses.
Players must be at least 21 years old.: phtaya casino – phtaya
Секреты успешной покупки входной металлической двери, соответствует всем требованиям безопасности.
Лучшие магазины с широким выбором входных металлических дверей.
двери входные металлические москва двери входные металлические москва .
Советы по избежанию ошибок при покупке металлической входной двери.
5 основных причин купить металлическую входную дверь.
Как выбрать между дверью одного бренда и дверью другого.
Las mГЎquinas tragamonedas tienen temГЎticas diversas.: win chile – winchile casino
THE MASKED DANCER” startet: Kandidaten erwartet große Herausforderung”.
The European Union is concentrating on 60 million heat pumps put in by 2030, which would imply an annual progress price of almost 15.
Лучшие советы по выбору металлической входной двери, которая прослужит долгие годы.
Где купить надежную входную металлическую дверь по выгодной цене.
входная дверь дверь металлическая .
Что учесть при выборе входной металлической двери.
Почему стоит выбрать металлическую входную дверь.
Сравнение входных металлических дверей различных брендов.
Лучшее казино для аркадных игр | Уникальные аркадные игры только здесь | Победите в аркадах и станьте миллионером | Увлекательные аркадные игры для всех | Новый уровень азарта в онлайн казино | Играйте в аркадные игры и выигрывайте деньги | Азартные аркады для всех желающих | Азарт и аркады в одном месте | Лучшие аркадные развлечения для вас | Увлекательные аркады для ценителей азарта | Попробуйте свою удачу в аркадном казино | Выигрывайте крупные суммы в аркадах | Побеждайте в аркадах и станьте миллионером | Увлекательные аркады и возможность заработать крупные суммы | Аркадные развлечения для всех | Увлекательные аркады и возможность заработать деньги
arkada casino онлайн arkada casino бонусы без депозита .
Casinos offer delicious dining options on-site.: taya777 – taya777
п»їCasinos in the Philippines are highly popular. https://jugabet.xyz/# Los juegos en vivo ofrecen emociГіn adicional.
Prostavive is a natural supplement designed to support men’s prostate health. It aids in maintaining optimal urinary function and alleviates discomfort associated with an enlarged prostate.
taya365 login taya365 login The Philippines has a vibrant nightlife scene.
La mГєsica acompaГ±a la experiencia de juego.: jugabet – jugabet casino
https://taya365.art/# Loyalty programs reward regular customers generously.
Players must be at least 21 years old.
The most comprehensive bip39 for securely creating and restoring cryptocurrency wallets. Learn how mnemonic coding works and protect your digital assets!
cheap relocation options Prague 777lu.net
Лучшие решения для автоматизации жалюзи, облегчит вашу жизнь.
Оптимизируйте освещение и температуру в помещении с автоматикой для жалюзи.
Удобное управление жалюзи через интернет.
Модернизируйте ваш дом с автоматическими жалюзи.
Качественное обслуживание автоматизированных жалюзи.
автоматика жалюзи https://elektrokarniz18.ru/ .
Some casinos have luxurious spa facilities.: phmacao com – phmacao.life
http://phtaya.tech/# Players enjoy a variety of table games.
Many casinos have beautiful ocean views.
Slot machines attract players with big jackpots.: taya365 – taya365 login
It also provided inflationary rather than deflationary expectations, allowing prospective creditors more hope that their incomes and earnings would be able to fund their debt payments if they were to borrow.
We did not get to satisfy Clinton in person, although – too bad, because we had been going to inform him to grab his sax and be a part of us!
moving with professionals Prague overseas moving Prague
Edwin Jimboy officiating. Sisters can surprise their brothers with customized Bracelet Rakhi available in varied fashion, kinds and designs.
The most comprehensive bip39 phrase for securely creating and restoring cryptocurrency wallets. Learn how mnemonic coding works and protect your digital assets!
A larger party may require you to ditch the reusable towels altogether and opt for disposable ones instead – decorative sets are available at many bed and bath stores.
Nonetheless the fluctuation in gold costs isn’t expected to have an effect on lengthy-time period gold-associated investments because the metal is still viewed amongst the best various asset class and a secure manner of funding in times of economic uncertainty.
http://taya365.art/# Live dealer games enhance the casino experience.
The Philippines offers a rich gaming culture.
bezpecne stehovani stehovani rodinnych domu
Due to developments in synthetic intelligence, natural language processing, and data science instruments, researchers can now analyze language patterns and images in social media posts to detect indicators of psychological well being conditions resembling depression, anxiety, and suicide risk.
Players must be at least 21 years old.: taya365.art – taya365 com login
winchile winchile casino Muchos casinos ofrecen restaurantes y bares.
Casinos often host special holiday promotions.: phmacao – phmacao com
Цікавлять новобудови Україна? Сучасні квартири з панорамними вікнами, зачиненими дворами та зручним розташуванням. Вибирайте комфортне житло з найкращими умовами покупки!
Останні актуальні новини світу 2025 цілодобово оперативні події, важливі рішення, міжнародна політика та економіка. Все, що потрібно знати про життя країни, в одному місці!
http://jugabet.xyz/# La pasiГіn por el juego une a personas.
Online gaming is also growing in popularity.
A variety of gaming options cater to everyone. https://phmacao.life/# Entertainment shows are common in casinos.
Most casinos offer convenient transportation options.: phtaya casino – phtaya casino
Продажа инструментов для дома profimaster58 строительства и ремонта! Огромный выбор ручного и электроинструмента, выгодные цены, акции и быстрая доставка. Найдите все необходимое в одном месте!
Free and reliable nudify ai tool to create images with AI? The Best Free AI Nudify is the best choice for creating nude photos with privacy and quality guarantee.
Melissa Breau: Fascinating. I believe a lot of handlers are used to hearing pretty early on they need to break their training down into plenty of pieces and steadily make things tougher, and I might think about that actually applies right here.
Online gaming is also growing in popularity.: taya365 – taya365.art
https://phmacao.life/# A variety of gaming options cater to everyone.
Many casinos have beautiful ocean views.
Executives, employees and family members from the company come to the NASDAQ studio at Times Square to celebrate the IPO at the opening bell.
1812778 Flight Sergeant David Ernest Wanstall.
Prostavive is a natural supplement designed to support men’s prostate health. It aids in maintaining optimal urinary function and alleviates discomfort associated with an enlarged prostate.
нанять грузчиков грузчики
Use the proven bip39 world list standard to protect your assets and easily restore access to your finances. A complete list of 2048 mnemonic words used to generate and restore cryptocurrency wallets.
Slot machines attract players with big jackpots.: taya777 – taya777
phtaya phtaya The Philippines has a vibrant nightlife scene.
If you’re thinking of purchasing an E85 vehicle, this page will serve as an important reference tool.S.
http://taya777.icu/# The gaming floors are always bustling with excitement.
The casino atmosphere is thrilling and energetic.
Prostavive is a natural supplement designed to support men’s prostate health. It aids in maintaining optimal urinary function and alleviates discomfort associated with an enlarged prostate.
Gaming regulations are overseen by PAGCOR.: taya777 app – taya777
Use the proven bip39 standard to protect your assets and easily restore access to your finances. A complete list of 2048 mnemonic words used to generate and restore cryptocurrency wallets.
La historia del juego en Chile es rica.: winchile.pro – winchile
All the opposite banks have their own choice course of though written check and interviews.
https://winchile.pro/# Los casinos son lugares de reuniГіn social.
The thrill of winning keeps players engaged.
Part of your article describes how police have entry to real-time feeds from security cameras.
The sleeping person is a superb sign to see when you already know you just cannot push it another mile.
The casino scene is constantly evolving.: taya777 register login – taya777 app
Most casinos offer convenient transportation options. http://jugabet.xyz/# La diversiГіn nunca se detiene en los casinos.
Sitio web oficial jude bellingham de fans de Jude Bellingham: noticias, logros y material exclusivo sobre la carrera del talentoso mediocampista que juega en el Real Madrid.
Sitio web de fans https://rodri.com.mx de Rodri Hernandez: Descubre la carrera y logros del mediocampista espanol del Manchester City. Noticias, estadisticas y analisis del juego de uno de los mejores futbolistas actuales.
Los casinos ofrecen entretenimiento en vivo.: winchile.pro – winchile
https://jugabet.xyz/# Las reservas en lГnea son fГЎciles y rГЎpidas.
High rollers receive exclusive treatment and bonuses.
Kevin De Bruyne kevin-de-bruyne.com mx es un maestro del futbol moderno, conocido por su vision de juego, precision y liderazgo en el Manchester City. Su talento y trabajo duro lo han convertido en una leyenda del deporte.
Investment managers develop an investment plan to satisfy a client’s goals, then use that approach to determine how to split the client’s portfolio among various forms of investments, such as stocks and bonds.
Sitio fan de Mohamed Salah mohamed salah ultimas noticias, records, entrevistas y los mejores momentos de la carrera de uno de los futbolistas mas grandes de la actualidad. ?Mantente al tanto!
drug mart: discount drug pharmacy – discount drugs
Best online pharmacy: Online pharmacy USA – online pharmacy delivery usa
Fan site de Vinicius Junior vinicius-jr.com.mx/ noticias, logros y detalles sobre su carrera en el Real Madrid. Sigue la evolucion de esta estrella del futbol mundial.
jeux casino en ligne france https://annuaire-des-casinos.com
canada online pharmacy no prescription https://xxlmexicanpharm.com/# xxl mexican pharm
non prescription medicine pharmacy https://megaindiapharm.com/# Mega India Pharm
xxl mexican pharm: reputable mexican pharmacies online – mexican border pharmacies shipping to usa
Best online pharmacy: Cheapest online pharmacy – Best online pharmacy
casino francais en ligne fiable casino en ligne en france
Try your luck at pin up casino! The best slots, roulette, blackjack and live games with real dealers. Pleasant bonuses, promotions and a user-friendly interface will create ideal conditions for the game!
us pharmacy no prescription http://megaindiapharm.com/# reputable indian pharmacies
Почта для домена на https://email4domain.ru это корпоративный почтовый сервис email для организаций. Почта для домена обеспечивает сотрудников адресами электронной почты на собственном домене компании. Почта для бизнеса улучшает узнаваемость и повышает имидж бренда.
canada drugs coupon code https://familypharmacy.company/# cheapest prescription pharmacy
online pharmacy india Mega India Pharm Mega India Pharm
для вашего дома.
Умное устройство для управления жалюзи.
Секреты выбора привода для жалюзи.
Плюсы использования привода для жалюзи.
Инновационные технологии в области приводов для жалюзи.
Простой способ контролировать жалюзи с телефона с использованием привода.
Секреты успешной установки привода для автоматизации жалюзей.
Экономьте время и энергию с автоматизированным приводом для жалюзи.
Необычное применение приводов для управления жалюзями.
Секрет уюта и удобства с автоматизированными жалюзями.
привод на жалюзи https://elektrokarniz21.ru/ .
Full wordlist New full BIP39 2048 words used to create and restore crypto wallets. Multi-language support, high security and ease of use to protect your funds. 2048 mnemonic words for seed generation.
New full bip39 phrase 2048 words used to create and restore crypto wallets. Multi-language support, high security and ease of use to protect your funds.
meilleur bonus casino en ligne casino en ligne nouveau
canadian pharmacy meds: easy canadian pharm – easy canadian pharm
discount drugs: drugmart – discount drug mart
best online pharmacy no prescription https://megaindiapharm.shop/# cheapest online pharmacy india
canadian online pharmacy no prescription http://megaindiapharm.com/# best india pharmacy
Full wordlist New full BIP39 2048 words used to create and restore crypto wallets. Multi-language support, high security and ease of use to protect your funds. 2048 mnemonic words for seed generation.
New full bip39 world list 2048 words used to create and restore crypto wallets. Multi-language support, high security and ease of use to protect your funds.
His pieces cooperate properly: the bishop on g7 protects the knight on c3, which protects the rook on a4, which in flip protects the bishop on c4 and forces Byrne’s queen away.
mexican border pharmacies shipping to usa: xxl mexican pharm – mexican online pharmacies prescription drugs
canadian pharmacy coupon code http://megaindiapharm.com/# Mega India Pharm
xxl mexican pharm: xxl mexican pharm – п»їbest mexican online pharmacies
online pharmacy delivery usa Cheapest online pharmacy mail order prescription drugs from canada
canadian pharmacy coupon http://familypharmacy.company/# Cheapest online pharmacy
casino en ligne france fiable wild sultan casino en ligne
Full wordlist New full BIP39 2048 words used to create and restore crypto wallets. Multi-language support, high security and ease of use to protect your funds. 2048 mnemonic words for seed generation.
india online pharmacy: top 10 pharmacies in india – indian pharmacy online
MegaIndiaPharm: online pharmacy india – MegaIndiaPharm
canada pharmacy coupon https://easycanadianpharm.com/# best mail order pharmacy canada
Актуальные промокоды казино https://desperado.cz/_lib/pgs/?bezopasnoe_otbelivanie_zubov_v_domashnih_usloviyah.html получите дополнительные бонусы при регистрации! Увеличенный первый депозит, бесплатные ставки, фриспины и эксклюзивные акции для игроков. Вводите код и выигрывайте больше!
Промокод казино https://r1dnetworks.com/read-blog/9761 активируйте эксклюзивные бонусы! Получите фриспины, бонусные деньги на депозит и кешбэк. Используйте актуальные коды для максимальной выгоды в онлайн-казино. Играйте с лучшими условиями!
Current casino promo codes https://verspk.ru/css/pages/?promokod_mostbet_pri_registracii_na_segodnya.html bonus money, free spins and cashback for playing. Use verified codes, activate exclusive offers and win more!
canadian pharmacy no prescription https://xxlmexicanpharm.com/# mexican border pharmacies shipping to usa
easy canadian pharm: reputable canadian pharmacy – easy canadian pharm
easy canadian pharm: canadian pharmacy in canada – easy canadian pharm
canadian pharmacies that deliver to the us buy drugs from canada easy canadian pharm
Ищете выгодные покупки? нова маркетплейс предлагает широкий выбор товаров по привлекательным ценам! Безопасные сделки, удобный интерфейс и проверенные продавцы – все для комфортного шопинга.
Промокод казино https://serenityaesthetics.co.uk/art/code-promo-1xbet-bonus-de-bienvenue.html активируйте эксклюзивные бонусы! Получите фриспины, дополнительные деньги на депозит и кешбэк. Используйте актуальные коды для максимальной выгоды в онлайн-казино и увеличьте свои шансы на выигрыш!
Лучшие промокоды для казино https://www.gilmaire-etienne.com/wp-content/pages/code_promo_18.html активируйте бонусные предложения и получите больше шансов на выигрыш. Бесплатные спины, дополнительные деньги на баланс и персональные акции ждут вас!
I’m amazed, I have to admit. Rarely do I come across a blog that’s equally educative and entertaining, and let me tell you, you have hit the nail on the head. The issue is something that not enough men and women are speaking intelligently about. I am very happy I found this during my hunt for something concerning this.
pharmacy online 365 discount code https://discountdrugmart.pro/# online pharmacy no prescription
canadian pharmacy without prescription http://discountdrugmart.pro/# discount drug pharmacy
Присоединяйтесь к NovaXLtd.live https://novaxltd.live платформе с широкими возможностями и удобными инструментами. Доступность, надежность, поддержка!
Используйте Kra020 https://kra020.com надежная площадка с удобными инструментами и поддержкой 24/7. Простота и безопасность в одном сервисе!
Откройте новые возможности https://sindicate24-4.biz! Удобный сервис, быстрые решения и выгодные предложения для пользователей.
xxl mexican pharm: mexican rx online – xxl mexican pharm
xxl mexican pharm: medicine in mexico pharmacies – reputable mexican pharmacies online
Продажа сигарет купить папиросы беломорканал в спб в интернет-магазине – оригинальные бренды, доступные цены, удобные способы оплаты и быстрая доставка. Сделайте заказ сегодня!
Откройте все возможности актуальная ссылка bs2best Большой выбор товаров, безопасные сделки и простая навигация. Приватность и защита пользователей на первом месте.
best no prescription pharmacy https://easycanadianpharm.com/# precription drugs from canada
mail order pharmacy no prescription https://xxlmexicanpharm.com/# medicine in mexico pharmacies
easy canadian pharm easy canadian pharm easy canadian pharm
india pharmacy: Mega India Pharm – indianpharmacy com
canadian pharmacy discount code http://xxlmexicanpharm.com/# xxl mexican pharm
Mega India Pharm: MegaIndiaPharm – MegaIndiaPharm
pharmacy without prescription https://familypharmacy.company/# Best online pharmacy
Необычные электрокарнизы для вашей сцены, которые удивят зрителей.
Электрокарнизы придают шоу утонченность, обеспечивая плавное движение драпировок.
Электрокарнизы для сцены с электронным управлением, которые делают шоу невероятно красивым.
Электрокарнизы помогут создать атмосферу шоу, где каждая деталь важна.
Создайте неповторимую магию на сцене с электрокарнизами, покоривших сердца зрителей.
Сверхсовременные технологии в каждом дизайне, и принести вашему проекту новый уровень.
Освежите свое шоу с электрокарнизами, и создадут неповторимую атмосферу.
Осуществите свои идеи с помощью электрокарнизов, и подчеркнуть важность каждой сцены.
Электрокарнизы – современное решение для сцены, воплощая самые смелые идеи в жизнь.
Сотни вариантов электрокарнизов для ваших выступлений, и удивить зрителей нестандартными решениями.
электрический занавес для сцены электрический занавес для сцены .
international pharmacy no prescription http://xxlmexicanpharm.com/# pharmacies in mexico that ship to usa
drugmart: discount drug pharmacy – discount drugs
Свежие промокоды казино http://school-47.ru/includes/pgs/?1xstavka_promokod_pri_registracii_besplatno.html бонусы, фриспины и эксклюзивные акции от топовых платформ! Найдите лучшие предложения, активируйте код и выигрывайте больше.
pharmacy discount coupons: Online pharmacy USA – online canadian pharmacy coupon
частный seo оптимизатор https://seo-base.ru
Нужен опытный мануальный терапевт Ивантеевка? Помогаю при остеохондрозе, грыжах, искривлениях позвоночника и болях в суставах. Безопасные техники, профессиональный подход, запись на прием!
pharmacy discount coupons https://xxlmexicanpharm.shop/# xxl mexican pharm
canadian pharmacy no prescription http://xxlmexicanpharm.com/# xxl mexican pharm
My spouse and I absolutely love your blog and find most of your post’s to be what precisely I’m looking for. Does one offer guest writers to write content available for you? I wouldn’t mind composing a post or elaborating on some of the subjects you write related to here. Again, awesome site!
mexican rx online buying from online mexican pharmacy best online pharmacies in mexico
discount drugs: legal online pharmacy coupon code – discount drugs
cheapest pharmacy to fill prescriptions without insurance http://megaindiapharm.com/# MegaIndiaPharm
Защитите авто от коррозии https://antikorauto.ru антикоррозийная обработка и кузовной ремонт с гарантией. Восстановление геометрии кузова, покраска, удаление вмятин. Долговечность и качество по доступным ценам!
Жарким летним утром Вася Муфлонов, заядлый рыбак из небольшой деревушки, собрал свои снасти и отправился на местное озеро. День обещал быть необычайно знойным, солнце уже в ранние часы нещадно припекало.
Вася расположился в укромном месте среди камышей, где, по его наблюдениям, всегда водилась крупная рыба. Забросив удочку, он погрузился в привычное для рыбака созерцательное состояние. Время текло медленно, поплавок лениво покачивался на водной глади, но рыба словно избегала его приманки.
Ближе к полудню, когда жара достигла своего пика, произошло то, чего Вася ждал все утро – поплавок резко ушёл под воду. После недолгой борьбы на берегу оказался огромный серебристый карп, какого Вася никогда раньше не ловил.
Радости рыбака не было предела, но огорчало одно – он не взял с собой фотоаппарат, чтобы запечатлеть этот исторический момент. Тут в голову Васи пришла необычная идея. Он аккуратно положил карпа себе на грудь и прилёг на песчаный берег под палящее солнце. “Пусть загар оставит память об этом улове”, – подумал находчивый рыбак.
Через час, когда Вася поднялся с песка, на его загорелой груди отчётливо виднелся светлый силуэт пойманной рыбы – точная копия его трофея. Теперь у него было неопровержимое доказательство его рыбацкой удачи.
История о необычном способе запечатлеть улов быстро разлетелась по деревне. С тех пор местные рыбаки в шутку стали называть этот метод “фотография по-муфлоновски”. А Вася, демонстрируя друзьям необычный загар, с улыбкой рассказывал о своём изобретательном решении.
Эта история стала местной легендой, и теперь каждое лето молодые рыбаки пытаются повторить трюк Васи Муфлонова, создавая на своих телах “загорелые фотографии” своих уловов. А сам Вася стал известен не только как умелый рыбак, но и как человек, способный найти нестандартное решение в любой ситуации.
online casino software online gambling platform
online pharmacy non prescription drugs: cheapest pharmacy for prescriptions without insurance – drugmart
best canadian pharmacy no prescription https://easycanadianpharm.com/# canadian pharmacy online
canadian pharmacy world coupon http://discountdrugmart.pro/# discount drug pharmacy
Fast and secure VPS https://evps.host for any task! Flexible configurations, SSD drives, DDoS protection. Easy scaling, high performance and 24/7 support!
cheapest prescription pharmacy: online pharmacy delivery usa – family pharmacy
All about Vinicius Junior https://vinicius-junior-bd.com career, trophies, highlights and records. Follow the Brazilian winger, his success at Real Madrid and on the international stage!
All about Karim Benzema https://karim-benzema-bd.com biography, achievements, main goals and career moments. Find out how the striker conquered Real Madrid and continues to shine in world football!
All about Karim Benzema https://karim-benzema-bd.com biography, achievements, main goals and career moments. Find out how the striker conquered Real Madrid and continues to shine in world football!
pharmacies in mexico that ship to usa: pharmacies in mexico that ship to usa – xxl mexican pharm
canada drugs coupon code https://familypharmacy.company/# family pharmacy
Online medicine order world pharmacy india MegaIndiaPharm
no prescription pharmacy paypal https://xxlmexicanpharm.com/# mexican mail order pharmacies
easy canadian pharm: www canadianonlinepharmacy – my canadian pharmacy rx
no prescription pharmacy paypal http://discountdrugmart.pro/# drug mart
cheap pharmacy no prescription http://discountdrugmart.pro/# canadian pharmacy discount coupon
discount drug mart: drug mart – discount drugs
Mega India Pharm: MegaIndiaPharm – MegaIndiaPharm
аркада казино зеркало аркада казино вход
Военная служба по контракту https://contract116.ru стабильность, достойная зарплата, социальные льготы и карьерный рост. Присоединяйтесь к профессиональной армии и получите надежное будущее!
canada pharmacy coupon http://familypharmacy.company/# family pharmacy
Good job!
canada pharmacy coupon https://easycanadianpharm.com/# canada drugs online
MegaIndiaPharm indian pharmacy online Mega India Pharm
rate canadian pharmacies: canada pharmacy online – easy canadian pharm
Kevin De Bruyne https://kevin-de-bruyne-az.com is the leader of the Manchester City and Belgium national team midfield. Find out all about his achievements, matches, awards and records in world football!
Joshua Kimmich joshua-kimmich-az.org the versatile leader of Bayern and the German national team! The latest news, stats, highlights, goals and assists. Follow the career of one of the best midfielders in the world!
cleo скрипты самп плагины
cheapest pharmacy for prescriptions without insurance https://xxlmexicanpharm.shop/# mexican drugstore online
Mega India Pharm: Mega India Pharm – MegaIndiaPharm
Каталог подарков и сувениров https://kameshki51.ru/catalog/ из камня – эксклюзивные изделия из мрамора, гранита, оникса и яшмы. Шкатулки, статуэтки, часы, пресс-папье, бизнес-сувениры. Высокое качество и ручная работа!
Transform a vehicle into a masterpiece with expert car tuning services. At a shop, we provide a wide range of modifications to boost handling . Whether you want a stylish appearance or top-tier motor adjustments, we’ve got you covered. Explore our solutions at https://mckeesportautobody.com/. Upgrade your ride today and experience reliability like never before.
canadian pharmacy without prescription http://discountdrugmart.pro/# drugmart
Подарки и сувениры из камня https://kameshki51.ru статуэтки, шкатулки, часы, панно, изделия из мрамора, гранита и оникса. Ручная работа, уникальный дизайн, доставка по России!
discount drug mart: canadian online pharmacy no prescription – discount drugs
Having read this I believed it was extremely enlightening. I appreciate you taking the time and effort to put this content together. I once again find myself personally spending way too much time both reading and posting comments. But so what, it was still worthwhile.
pharmacy discount coupons https://easycanadianpharm.shop/# easy canadian pharm
Как побороть лудоманию vavada история глазами прошедшего это испытание и несколько советам тем, кто в середине пути или столкнулся с этим через друзей и близких. Описываю в статье как Вавада помогла мне избавиться от игровой зависимости
Получите свежие статьи https://advokatugra-86.ru и новости от адвоката, посвященные важным правовым вопросам. Профессиональные рекомендации и разборы актуальных событий в законодательстве помогут вам быть в курсе всех изменений.
UID_59407105###
berita dana x twitter viral berita dana desa ada disini !
Best online pharmacy: canadian pharmacy world coupon code – Online pharmacy USA
Окунитесь в азарт с aviator-slot.ru Уникальная игра с захватывающим геймплеем и возможностью сорвать крупный выигрыш. Следите за коэффициентом, вовремя забирайте ставку и умножайте баланс. Испытайте удачу прямо сейчас!
Новости музыки Украины https://musicnews.com.ua популярные жанры, тренды и полезные советы для музыкантов. Узнавайте больше о мире музыки и развивайте свои навыки!
Последние новости автоспорта https://autosport-ru.ru обзоры гонок, рейтинги пилотов и команд. Формула-1, Ле-Ман, WRC и другие топовые серии – следите за всеми событиями в одном месте!
easy canadian pharm easy canadian pharm easy canadian pharm
Ставки на спорт betting-ru.ru ваш шанс превратить знания в выигрыш! Лучшие коэффициенты, огромный выбор событий и удобный интерфейс. Делайте прогнозы и побеждайте!
legal online pharmacy coupon code http://discountdrugmart.pro/# discount drugs
canadian pharmacies not requiring prescription https://familypharmacy.company/# family pharmacy
easy canadian pharm: canada drugstore pharmacy rx – easy canadian pharm
prescription drugs online: discount drugs – discount drugs
UID_72942561###
Berita Hot! 🔥🔥 Isa Rachmatarwata Tersangka Kasus Jiwasraya Buntut kerugian negara hingga 16,8 Triliun! 😲😲
cheapest pharmacy for prescriptions without insurance https://easycanadianpharm.com/# canada ed drugs
canada pharmacy coupon https://familypharmacy.company/# canadian pharmacy no prescription
Cheapest online pharmacy: no prescription pharmacy paypal – online pharmacy delivery usa
UID_53550706###
Berita terbaru! 🔥 Isa Rachmatarwata Ditahan Kejagung dalam kasus Jiwasraya. 🚔👮♂️
discount drug mart pharmacy: drug mart – no prescription needed canadian pharmacy
non prescription medicine pharmacy http://easycanadianpharm.com/# best canadian pharmacy
UID_57092237###
Berita gembira! 🎉 Pasokan Gas 3 Kg di Kramat Jati Kembali Normal 🎊 Siap-siap belanja gas, ya! 💪🔥
canadian pharmacy no prescription canadian pharmacies not requiring prescription Online pharmacy USA
best online pharmacy no prescription https://discountdrugmart.pro/# drug mart
Zeus vs Hades zeus-vs-hades-download.ru эпичная битва богов! Игровой автомат с грозными бонусами, фриспинами и множителями. Выберите сторону Зевса или Аида и сорвите большой выигрыш!
Мир смешанных единоборств ufc-ru.ru/ (MMA) в UFC! Рейтинги, бои, истории бойцов, прогнозы на поединки и эксклюзивные материалы о крупнейшей бойцовской лиге.
Все о легкой атлетике athletics История развития, основные дисциплины, рекорды, тренировки и современные тенденции. Узнайте больше о королеве спорта!
pharmacy without prescription: canadian pharmacy coupon code – drug mart
canada drugs coupon code https://megaindiapharm.com/# indian pharmacy online
MegaIndiaPharm: Mega India Pharm – buy medicines online in india
Cassino online Pin Up https://888casino-official-brazil.site ganhos sem limites! Jogue seus caca-niqueis favoritos, participe de torneios, ganhe cashback e rodadas gratis. Licenca, seguranca e pagamentos rapidos!
UID_72339950###
Heboh! 📣🔥 Unjuk Rasa di Polda Jatim 📢 Menuduh Jokowi Terlibat Korupsi! 😱🔍
eloncasino eloncasino .
UID_27764099###
Ini yang di ganti >>> “Bingung Kenapa 😕❓” Federasi Sepak Bola Pakistan Disanksi FIFA “Baca Penyebabnya Disini! 🧐🔍”
canadian pharmacy discount coupon https://easycanadianpharm.com/# easy canadian pharm
It then despatched the gasoline into the gas tank for mixing.
Revamp enhance your ride with our premium top-tier car tuning services. We specialize in tailored modifications that elevate both performance and design. From horsepower boosts to custom panels, we’ve got you covered. Experience the ultimate transformation at https://phoenix-autobodyshop.com/ and let our professional team bring your vision to life. Visit us today and drive with pride!
best canadian pharmacy no prescription https://familypharmacy.company/# pharmacy discount coupons
elon bet elon bet .
buying prescription drugs in mexico: mexican border pharmacies shipping to usa – xxl mexican pharm
Свежие и актуальные новости https://sugar-news.com.ua Украины и мира! Будьте в курсе последних событий, аналитики и трендов. Читайте последние новости Украины онлайн!
cheapest pharmacy for prescriptions without insurance Online pharmacy USA foreign pharmacy no prescription
pharmacy discount coupons http://discountdrugmart.pro/# discount drug mart
cheapest pharmacy to get prescriptions filled https://familypharmacy.company/# family pharmacy
Generally I do not read post on blogs, but I would like to say that this write-up very forced me to try and do so! Your writing style has been surprised me. Thanks, quite nice article.
UID_74743238###
Ini dia! 🎉🎉 ASN BKN Ubah Pola Kerja yang baru dan efisien! 🎉🎉.
easy canadian pharm: best canadian pharmacy to order from – legal canadian pharmacy online
Лучшие эксперты в одном месте! реестр соут маркетплейс и агрегатор экспертных компаний помогает найти надежных специалистов по разным направлениям. Удобный выбор, проверенные отзывы и рейтинг!
cheapest pharmacy to fill prescriptions without insurance https://easycanadianpharm.com/# easy canadian pharm
cheapest pharmacy prescription drugs https://xxlmexicanpharm.com/# medication from mexico pharmacy
UID_74743238###
Ini dia! 🎉🎉 ASN BKN Ubah Pola Kerja yang baru dan efisien! 🎉🎉.
discount drug pharmacy: discount drugs – discount drug pharmacy
buying prescription drugs from canada https://familypharmacy.company/# Best online pharmacy
UID_74743238###
Ini dia! 🎉🎉 ASN BKN Ubah Pola Kerja yang baru dan efisien! 🎉🎉.
canada pharmacy coupon http://xxlmexicanpharm.com/# xxl mexican pharm
discount drug mart pharmacy discount drugs discount drugs
mexico pharmacies prescription drugs: xxl mexican pharm – mexico drug stores pharmacies
I couldn’t resist commenting
UID_83344528###
Inilah 🎉🎉 Pupuk Inovatif Kebun Riset Kujang yang bikin Wamen BUMN bangga! 💪🏻🇮🇩
UID_83344528###
Inilah 🎉🎉 Pupuk Inovatif Kebun Riset Kujang yang bikin Wamen BUMN bangga! 💪🏻🇮🇩
Удобное управление шторами с помощью электрокарниза и таймера, экономьте энергию и время.
Создайте атмосферу уюта и стиля с помощью электрокарниза и таймера, который подчеркнет ваш вкус и индивидуальность.
Автоматизируйте процесс управления шторами с электрокарнизом и таймером, для вашего удобства и удовольствия.
Оптимальное решение для автоматизации штор – электрокарниз с таймером, который упростит вашу жизнь и сделает ее более комфортной.
Дизайнерское решение для современного дома – электрокарниз с таймером, позволит вам экономить время и силы.
механизм для штор умный дом механизм для штор умный дом .
Хотите играть в Steam-игры shared-steam.org/ дешевле? Shared-Steam.org предлагает аренду аккаунтов с топовыми играми. Безопасность, доступность и удобство – ваш гейминг без границ!
Pemain sering mencoba berbagai jenis slot https://bonaslot.site/# Kasino sering memberikan hadiah untuk pemain setia
секс с немками секс с немками .
Slot memberikan kesempatan untuk menang besar: garuda888 – garuda888
Slot modern memiliki grafik yang mengesankan https://slotdemo.auction/# Slot dengan fitur interaktif semakin banyak tersedia
http://slotdemo.auction/# Kasino menawarkan pengalaman bermain yang seru
Create images deep nude easily with AI. Remove clothes from anyone in the image and enjoy their nakedness.
порно немцы http://trax-nemeckoe1.ru .
I was very pleased to find this web-site.I wanted to thanks for your time for this wonderful read!! I definitely enjoying every little bit of it and I have you bookmarked to check out new stuff you blog post.
Unleash optimize your vehicle’s full potential with our premium exclusive tuning services. We offer tailored modifications to upgrade your car’s performance, aesthetics, and comfort. Our expert qualified technicians use state-of-the-art cutting-edge technology to deliver flawless outcomes. https://americasbestcertifiedautobody.com/ Whether you seek superior speed, handling, or luxury, we provide first-class solutions. Trust us to revolutionize your driving experience. Contact us today and experience the ultimate in automotive optimization!
slot88.company slot 88 Slot menjadi daya tarik utama di kasino
Keseruan bermain slot selalu menggoda para pemain https://bonaslot.site/# Jackpot besar bisa mengubah hidup seseorang
Slot menjadi daya tarik utama di kasino http://slot88.company/# Keseruan bermain slot selalu menggoda para pemain
Kasino mendukung permainan bertanggung jawab: slot demo – slot demo
https://garuda888.top/# Permainan slot bisa dimainkan dengan berbagai taruhan
Turkiye’deki slot makineleri https://slots-cool.com gercek parayla oynanabilen slotlar kapsaml bir baks! Nerede oynan?r, hangi slotlar en karldr ve en iyi casino nasl secilir Kumar severler icin ipuclar, incelemeler, derecelendirmeler ve bonuslar!
Turkiye Slotlar Rehberi https://slots-rait.com En Iyi Slotlar ve Casinolar! Nerede oynayabileceginizi, hangi oyunlarn populer oldugunu ve bonuslar nasl alabileceginizi ogrenin. Oyun alanlar ve guncel eglencelere dair kapsaml bir genel baks!
UID_21891068###
Takjub 😮 dengan fenomena serbu gas? Yuk, baca Warung Tatang Diserbu Warga dan temukan faktanya! 🕵️♀️👀
Banyak pemain berusaha untuk mendapatkan jackpot http://slot88.company/# Mesin slot menawarkan pengalaman bermain yang cepat
мотоэвакуатор https://perevozimgruz.by/perevozka-gruzov-minsk-moskva/
мотоэвакуатор квартирный переезд минск санкт петербург
Slot menjadi daya tarik utama di kasino https://preman69.tech/# Slot menjadi daya tarik utama di kasino
http://slot88.company/# Mesin slot digital semakin banyak diminati
Pemain bisa menikmati slot dari kenyamanan rumah: preman69 – preman69
slot88.company slot 88 Kasino menawarkan pengalaman bermain yang seru
Знакомства в Уфе https://ufavip.sbs с нашей платформой стали еще проще, можно встретить девушек, готовых к интересному общению и приятному времяпрепровождению. Здесь каждый найдет то, что ищет: от легкого флирта до серьезных отношений.
Slot dengan pembayaran tinggi selalu diminati https://slotdemo.auction/# Pemain bisa menikmati slot dari kenyamanan rumah
https://slotdemo.auction/# Kasino memiliki suasana yang energik dan menyenangkan
Kasino memastikan keamanan para pemain dengan baik: preman69.tech – preman69 slot
UID_21891068###
Takjub 😮 dengan fenomena serbu gas? Yuk, baca Warung Tatang Diserbu Warga dan temukan faktanya! 🕵️♀️👀
перевозка мотоцикла минск москва грузоперевозки минск
UID_25978847###
situs terbaik hanya di slot gacor agentotoplay
Slot menawarkan kesenangan yang mudah diakses https://bonaslot.site/# Kasino di Bali menarik banyak pengunjung
http://slotdemo.auction/# Banyak pemain mencari mesin dengan RTP tinggi
п»їKasino di Indonesia sangat populer di kalangan wisatawan: garuda888 – garuda888
slotdemo slot demo Banyak pemain menikmati jackpot harian di slot
Is it possible to win at Lucky Jet? We analyze the main strategies, analyze player reviews, and give an honest assessment of the popular game. Read to avoid mistakes and increase your chances of success!
Mesin slot dapat dimainkan dalam berbagai bahasa https://preman69.tech/# Kasino selalu memperbarui mesin slotnya
Kasino sering mengadakan turnamen slot menarik http://bonaslot.site/# Slot menawarkan kesenangan yang mudah diakses
грузоперевозки минск https://perevozimgruz.by/gruzovoe-taksi/gruzotaksi/
http://slot88.company/# Mesin slot menawarkan berbagai tema menarik
UID_25978847###
situs terbaik hanya di slot gacor agentotoplay
Kasino menyediakan layanan pelanggan yang baik: slot 88 – slot88.company
1 вин про http://mabc.com.kg .
скачать mostbet на телефон скачать mostbet на телефон .
мульт порно мульт порно .
Bermain slot bisa menjadi pengalaman sosial http://preman69.tech/# Permainan slot bisa dimainkan dengan berbagai taruhan
порно с мамкой порно с мамкой .
порно с гинекологом порно с гинекологом .
You can also check with local schools or group centers.
1 win регистрация https://www.mabc.com.kg .
мост бет букмекерская контора [url=https://gtrtt.com.kg]https://gtrtt.com.kg[/url] .
секс мультики секс мультики .
Управляйте своим окружением с помощью программируемого электрокарниза, подходит для любого окна.
Трансформируйте ваше жилище с помощью программируемого электрокарниза, помогает вам расслабиться и отдохнуть.
Сделайте вашу жизнь проще с программируемым электрокарнизом, который позволит вам сохранить энергию.
Превратите свою спальню в уютное убежище с программируемым электрокарнизом, который поможет вам легко заснуть и проснуться.
Управляйте светом и теплом в вашем доме с программируемым электрокарнизом, поможет вам сэкономить время и энергию.
умный электрокарниз для штор curtain 3m https://elektrokarniz190.ru/ .
Кружевной бюстгальтер https://www.wildberries.ru/catalog/117605496/detail.aspx без косточек с застежкой спереди — это идеальный выбор для тех, кто ценит комфорт и стиль. Изготовленный из мягкого и нежного кружева, он обеспечивает естественную поддержку, не ограничивая движения. Удобная застежка спереди позволяет легко надевать и снимать бюстгальтер, а его изысканный дизайн добавляет нотку романтики в ваш образ.
порно мамка порно мамка .
гинеколог порно гинеколог порно .
?El paraiso del juego en Pin Up Casino https://ganar-apuestas-deportivas.com te espera! Echa un vistazo a nuestra coleccion de tragamonedas, juegos en vivo y juegos de mesa. Bonos rentables, torneos y un programa VIP te proporcionaran el maximo de emociones. ?Empieza a jugar ahora y gana!
https://slotdemo.auction/# Mesin slot baru selalu menarik minat
garuda888 garuda888 Pemain harus menetapkan batas saat bermain
Каталог финансовых организаций https://srochno-zaym-online.ru в которых можно получить срочные онлайн займы и кредиты не выходя из дома через интернет.
Banyak kasino memiliki program loyalitas untuk pemain: slot88 – slot 88
Kasino di Indonesia menyediakan hiburan yang beragam https://bonaslot.site/# Pemain harus menetapkan batas saat bermain
UID_95859078###
Baru-baru ini, para pemain Mahjong Wins 3 dikejutkan dengan bocoran RTP yang diklaim bisa meningkatkan peluang kemenangan secara signifikan. Banyak yang percaya bahwa informasi ini membantu mereka mendapatkan hasil yang lebih konsisten dalam permainan. Jika Anda ingin tahu lebih lanjut, cek bocoran RTP Mahjong Wins 3 hari ini dan lihat apakah strategi ini benar-benar efektif.
квартирный переезд из минска в могилев мотоэвакуатор
Если вы хотите играть в любимые казино-игры прямо со своего телефона, то скачайте 888starz Casino официальный сайт. Это приложение предлагает огромное количество слотов, карточных игр и спортивных ставок. Воспользуйтесь бонусами для новых пользователей и начните зарабатывать прямо сейчас!
Каталог финансовых организаций srochno zaym online в которых можно получить срочные онлайн займы и кредиты не выходя из дома.
новинки Netflix 2025 подборка новинки Netflix 2025
фильмы онлайн Netflix 2025 новинки кино 2025 в хорошем качестве
Каталог финансовых организаций srochno zaym online в которых можно получить срочные онлайн займы и кредиты не выходя из дома.
https://garuda888.top/# Beberapa kasino memiliki area khusus untuk slot
Voor Nederlandse gokliefhebbers is er geen betere plek dan bet sixty casino. Hier geniet je van een veilige en eerlijke speelomgeving met hoge uitbetalingen en diverse betaalmogelijkheden. Mis je kans niet en probeer nu de nieuwste slots en live casinospellen.
Kasino memastikan keamanan para pemain dengan baik http://bonaslot.site/# Slot modern memiliki grafik yang mengesankan
Banyak pemain menikmati jackpot harian di slot: preman69 – preman69
квартирный переезд с грузчиками https://perevozimgruz.by/kvartirnyi-pereezd/
перевозка шкафа с грузчиками https://perevozimgruz.by
Причины многоэтапности депортаций https://e-pochemuchka.ru/prichiny-mnogoetapnosti-deportaczij/
http://garuda888.top/# Kasino di Jakarta memiliki berbagai pilihan permainan
Beberapa kasino memiliki area khusus untuk slot https://slotdemo.auction/# Slot modern memiliki grafik yang mengesankan
UID_95859078###
Baru-baru ini, para pemain Mahjong Wins 3 dikejutkan dengan bocoran RTP yang diklaim bisa meningkatkan peluang kemenangan secara signifikan. Banyak yang percaya bahwa informasi ini membantu mereka mendapatkan hasil yang lebih konsisten dalam permainan. Jika Anda ingin tahu lebih lanjut, cek bocoran RTP Mahjong Wins 3 hari ini dan lihat apakah strategi ini benar-benar efektif.
Banyak kasino memiliki promosi untuk slot: bonaslot – bonaslot
preman69 slot preman69 Banyak pemain menikmati jackpot harian di slot
UID_95859078###
Baru-baru ini, para pemain Mahjong Wins 3 dikejutkan dengan bocoran RTP yang diklaim bisa meningkatkan peluang kemenangan secara signifikan. Banyak yang percaya bahwa informasi ini membantu mereka mendapatkan hasil yang lebih konsisten dalam permainan. Jika Anda ingin tahu lebih lanjut, cek bocoran RTP Mahjong Wins 3 hari ini dan lihat apakah strategi ini benar-benar efektif.
UID_95859078###
Baru-baru ini, para pemain Mahjong Wins 3 dikejutkan dengan bocoran RTP yang diklaim bisa meningkatkan peluang kemenangan secara signifikan. Banyak yang percaya bahwa informasi ini membantu mereka mendapatkan hasil yang lebih konsisten dalam permainan. Jika Anda ingin tahu lebih lanjut, cek bocoran RTP Mahjong Wins 3 hari ini dan lihat apakah strategi ini benar-benar efektif.
Slot menawarkan berbagai jenis permainan bonus http://bonaslot.site/# Mesin slot baru selalu menarik minat
https://preman69.tech/# Banyak pemain berusaha untuk mendapatkan jackpot
UID_57331425###
Skandal terbaru mengguncang komunitas pecinta game slot setelah seorang admin terkenal, Rachel, dikabarkan tertangkap membocorkan pola kemenangan Gate of Olympus. Banyak yang bertanya-tanya apakah informasi ini benar-benar akurat atau hanya sekadar rumor yang beredar di kalangan pemain. Simak lebih lanjut detailnya dalam artikel admin Rachel tertangkap bocorkan pola Gate of Olympus.
Free from artificial chemicals, Lipozem is a dietary supplement focused on natural weight loss. Its formula includes five tropical botanicals known for their fat-burning effects.
elon casino bangladesh elon casino bangladesh .
Banyak pemain menikmati jackpot harian di slot: BonaSlot – bonaslot.site
Каталог финансовых организаций srochno zaym online ru в которых можно получить срочные онлайн займы и кредиты не выходя из дома.
1winn bbcc.com.kg .
сериалы в 4K UHD Netflix 2025 сериалы в 4K UHD бесплатно
elon casino elon casino .
Каталог финансовых организаций srochno-zaym-online.ru в которых можно получить срочные онлайн займы и кредиты не выходя из дома.
американские сериалы онлайн Netflix 2025 популярные фильмы 2025 бесплатно
1win сайт casino-o.pro http://bbcc.com.kg .
casino elon http://www.elonbangladeshbet.com/ .
Slot memberikan kesempatan untuk menang besar http://slotdemo.auction/# Bermain slot bisa menjadi pengalaman sosial
UID_57331425###
Skandal terbaru mengguncang komunitas pecinta game slot setelah seorang admin terkenal, Rachel, dikabarkan tertangkap membocorkan pola kemenangan Gate of Olympus. Banyak yang bertanya-tanya apakah informasi ini benar-benar akurat atau hanya sekadar rumor yang beredar di kalangan pemain. Simak lebih lanjut detailnya dalam artikel admin Rachel tertangkap bocorkan pola Gate of Olympus.
888starz приложения https://globuss24.ru/wp-pages/?888starz-online-casino_2.html
https://preman69.tech/# Jackpot besar bisa mengubah hidup seseorang
Форум для кулинаров https://food-recipe.ru и рестораторов! Лучшие рецепты, тренды гастрономии, обсуждения ресторанного бизнеса. Общайтесь, делитесь опытом и вдохновляйтесь новыми идеями. Присоединяйтесь к нашему кулинарному сообществу!
I appreciate your creativity and the effort you put into every post. Keep up the great work!
Mesin slot baru selalu menarik minat: preman69 – preman69.tech
Красивые поздравления https://photofile.ru/otkrytki-so-svechami-vechnaya-i-svetlaya-pamyat-110-kartinok в одном месте! Огромный выбор картинок и открыток для любого повода. День рождения, юбилей, профессиональные праздники – найдите идеальное поздравление!
demo slot pg slot demo Kasino menawarkan pengalaman bermain yang seru
UID_17136916###
Kisah inspiratif datang dari seorang tukang ojek online asal Tangerang yang berhasil membawa pulang hadiah fantastis setelah bermain Mahjong Ways 2. Dengan modal kecil, ia sukses mengubah nasibnya dan meraih kemenangan besar senilai 200 juta rupiah. Penasaran bagaimana caranya? Simak kisah lengkapnya di artikel tukang ojek online menang 200 juta dari Mahjong Ways 2.
https://bonaslot.site/# Banyak kasino memiliki promosi untuk slot
Lipozem is a natural supplement created to aid weight loss effectively. Unlike products with artificial ingredients, it combines five tropical nutrients and botanicals known for their fat-burning abilities, promoting both weight management and overall wellness.
Новый уникальный маркетплейс NOVA, есть все! Москва, Питер, всегда свежие клады!Акция для новых магазинов – продай на 1 млн, получи 100к!Приглашаем к сотрудничеству рекламодателей!
Banyak pemain mencari mesin dengan RTP tinggi: garuda888.top – garuda888.top
Kasino menyediakan layanan pelanggan yang baik http://bonaslot.site/# Banyak pemain mencari mesin dengan RTP tinggi
https://slot88.company/# Keseruan bermain slot selalu menggoda para pemain
спины за регистрацию без депозита слоты которые дают сегодня
WOW just what I was looking for. Came here by searching for website
русские фильмы 2025 подборка hd rezka сериалы комедии на телевизоре
Маркетплейс нового поколения https://x-nova.live уникальный сервис для удобных покупок и продаж. Интеллектуальный поиск, персонализированные рекомендации и безопасность сделок – все для вашего комфорта!
hd rezka смотреть драмы с субтитрами онлайн подборка фильмов на вечер бесплатно
Slot menjadi daya tarik utama di kasino: slot demo – slot demo
Slot menjadi daya tarik utama di kasino http://preman69.tech/# Kasino mendukung permainan bertanggung jawab
UID_17136916###
Kisah inspiratif datang dari seorang tukang ojek online asal Tangerang yang berhasil membawa pulang hadiah fantastis setelah bermain Mahjong Ways 2. Dengan modal kecil, ia sukses mengubah nasibnya dan meraih kemenangan besar senilai 200 juta rupiah. Penasaran bagaimana caranya? Simak kisah lengkapnya di artikel tukang ojek online menang 200 juta dari Mahjong Ways 2.
slot88 slot 88 Beberapa kasino memiliki area khusus untuk slot
https://slotdemo.auction/# Banyak kasino memiliki promosi untuk slot
UID_87427935###
Cek yuk! 🚍👮♂️Operasi Keselamatan 2025 Polres Ciamis Siapa tahu bus favoritmu jadi sasaran! 😱👍
Howdy fantastic blog! Does running a blog like this take a great deal of work?
I’ve virtually no expertise in computer programming but
I was hoping to start my own blog in the near future. Anyways, should you have any
suggestions or tips for new blog owners please share. I understand this is off subject nevertheless I just had to ask.
Appreciate it!
Slot dengan tema film terkenal menarik banyak perhatian https://slotdemo.auction/# Slot menjadi bagian penting dari industri kasino
Mesin slot baru selalu menarik minat: bonaslot – BonaSlot
UID_87427935###
Cek yuk! 🚍👮♂️Operasi Keselamatan 2025 Polres Ciamis Siapa tahu bus favoritmu jadi sasaran! 😱👍
From the bottom of my heart, thank you for being a source of positivity and light in this sometimes dark and overwhelming world
tk999 app tk999 app .
электрокарниз двухрядный elektrokarnizy77.ru .
KU9 KU9 .
http://bonaslot.site/# Banyak pemain berusaha untuk mendapatkan jackpot
tk999 tk999 .
ku9 app download [url=http://www.ku9-app.org]http://www.ku9-app.org[/url] .
электрические гардины электрические гардины .
Mesin slot digital semakin banyak diminati https://slot88.company/# Mesin slot sering diperbarui dengan game baru
Mesin slot dapat dimainkan dalam berbagai bahasa: slot demo gratis – slot demo pg gratis
Good day! I could have sworn I’ve been to your blog before but after browsing through many of the posts I realized it’s new to me.
Nonetheless, I’m definitely pleased I stumbled upon it and I’ll be bookmarking it and checking back frequently!
It’s clear that you truly care about your readers and want to make a positive impact on their lives Thank you for all that you do
888starz бонусы https://dsdynamo.ru/wp-content/pgs/888starz-download_1.html
https://slot88.company/# Permainan slot mudah dipahami dan menyenangkan
Kasino di Jakarta memiliki berbagai pilihan permainan https://preman69.tech/# Mesin slot digital semakin banyak diminati
slot demo rupiah slot demo gratis Keseruan bermain slot selalu menggoda para pemain
виагра для мужчин цена виагра для мужчин цена .
Slot menjadi bagian penting dari industri kasino: akun demo slot – slotdemo
viagramsk.shop viagramsk.shop .
https://preman69.tech/# Mesin slot baru selalu menarik minat
I appreciate how this blog promotes self-growth and personal development It’s important to continuously strive to become the best version of ourselves
Slot klasik tetap menjadi favorit banyak orang https://slot88.company/# Pemain sering berbagi tips untuk menang
888starz iOS https://cricket.co.za/blog/?888starz-casino-cotedivoire.html
мтс новосибирск
https://hatchingjobs.com/companies/vpsguards3171/
мтс подключение
UID_18563832###
Ini yang di ganti >>> Yuk, ketahui lebih lanjut tentang Syarat Gabung OECD dan Pentingnya Ratifikasi Konvensi Antisuap di sini! 🕵️♀️🔎📚.
Nice post. I learn something new and challenging on websites I stumbleupon on a daily basis. It will always be useful to read content from other authors and practice a little something from other websites.
Hi this is kinda of off topic but I was wanting to know if blogs use WYSIWYG editors or if you have to manually code with HTML. I’m starting a blog soon but have no coding know-how so I wanted to get advice from someone with experience. Any help would be greatly appreciated!
Wyoming Valley Equipment LLC
Hi! I know this is kinda off topic nevertheless I’d figured I’d ask. Would you be interested in trading links or maybe guest writing a blog post or vice-versa? My website goes over a lot of the same topics as yours and I think we could greatly benefit from each other. If you might be interested feel free to shoot me an email. I look forward to hearing from you! Fantastic blog by the way!
Hi! I know this is kinda off topic however I’d figured I’d ask. Would you be interested in trading links or maybe guest authoring a blog article or vice-versa? My blog goes over a lot of the same topics as yours and I believe we could greatly benefit from each other. If you’re interested feel free to send me an email. I look forward to hearing from you! Great blog by the way!
Wyoming Valley Equipment LLC
Kasino menawarkan pengalaman bermain yang seru: slot demo – slot demo
Slot menjadi daya tarik utama di kasino http://garuda888.top/# Pemain sering berbagi tips untuk menang
https://garuda888.top/# Mesin slot sering diperbarui dengan game baru
Современный маркетплейс https://nova7.top для выгодных покупок! Огромный ассортимент, лучшие цены и удобные способы оплаты. Покупайте качественные товары и заказывайте с быстрой доставкой!
Новый формат маркетплейса https://nova4.top быстро, удобно, надежно! Лучшие предложения, современные технологии и простой интерфейс. Покупайте и продавайте легко, экономя время и деньги!
смотреть фильмы онлайн бесплатно подборки фильмов подборка
Получить деньги на карту банка теперь просто, мгновенно и легко. Мы даем возможность удобные условия. Перейдите на https://mikro-zaymi.ru/, чтобы узнать всю информацию. Процесс подтверждения занимает без ожидания. Не откладывайте! Получите сумму прямо сейчас!
лучшие кино в HD фильмы романтические фильмы 2025 подборка
garuda888.top garuda888 Kasino di Jakarta memiliki berbagai pilihan permainan
Kasino sering mengadakan turnamen slot menarik: preman69.tech – preman69
мтс домашний интернет новосибирск
https://www.flughafen-jobs.com/companies/hektips106/
мтс подключение новосибирск
Kasino di Indonesia menyediakan hiburan yang beragam https://slotdemo.auction/# Slot memberikan kesempatan untuk menang besar
https://garuda888.top/# Kasino sering mengadakan turnamen slot menarik
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
Your writing style is so engaging and makes even the most mundane topics interesting to read Keep up the fantastic work
888starz avis https://www.fbioyf.unr.edu.ar/evirtual/mod/forum/discuss.php?d=47707
Hi, Neat post. There is a problem with your site in internet explorer, would test this… IE still is the market leader and a large portion of people will miss your magnificent writing due to this problem.
Jackpot besar bisa mengubah hidup seseorang: bonaslot.site – BonaSlot
Slot dengan tema budaya lokal menarik perhatian http://preman69.tech/# Banyak pemain menikmati bermain slot secara online
Slot dengan fitur interaktif semakin banyak tersedia http://preman69.tech/# Slot modern memiliki grafik yang mengesankan
UID_83003169###
Kenalan yuk! 🤝 Dengan guru inspiratif ini, Guru Dede Sulaeman yang mengajarkan cara merapikan pakaian di kelasnya. 👕👚🎓
https://preman69.tech/# Jackpot besar bisa mengubah hidup seseorang
Портал с ответами https://online-otvet.site по всем школьным домашним предметам. Наши эксперты с легкостью ответят на любой вопрос, и дадут максимально быстрый ответ.
Руководство по настройке https://amnezia.dev VPN-сервера! Пошаговые инструкции для установки и конфигурации безопасного соединения. Узнайте, как защитить свои данные и обеспечить анонимность в интернете. Настройте VPN легко!
Сауна очищает организм https://sauna-broadway.ru выводя токсины через пот, укрепляет иммунитет благодаря перепадам температуры, снимает стресс, расслабляя мышцы и улучшая кровообращение. Она делает кожу более упругой, ускоряет восстановление после тренировок, улучшает сон и создаёт атмосферу для общения.
Сауна очищает организм https://sauna-broadway.ru выводя токсины через пот, укрепляет иммунитет благодаря перепадам температуры, снимает стресс, расслабляя мышцы и улучшая кровообращение. Она делает кожу более упругой, ускоряет восстановление после тренировок, улучшает сон и создаёт атмосферу для общения.
Your ideas and insights are unique and thought-provoking I appreciate how you challenge your readers to see things from a different perspective
Banyak pemain berusaha untuk mendapatkan jackpot http://garuda888.top/# Slot menawarkan kesenangan yang mudah diakses
preman69 preman69 Mesin slot menawarkan pengalaman bermain yang cepat
Православный форум https://prihozhanka.ru для женщин! Общение о вере, молитве, семье, воспитании и роли женщины в православии. Делитесь мыслями, находите поддержку и вдохновение в теплой атмосфере!
Jackpot besar bisa mengubah hidup seseorang: slot 88 – slot88.company
Korean cosmetics https://www.titantalk.com/members/jescore3.398681/#about perfect skin without effort! Innovative formulas, Asian traditions and visible results. Try the best skin care products right now!
Banyak pemain mencari mesin dengan RTP tinggi https://garuda888.top/# Kasino mendukung permainan bertanggung jawab
Korean cosmetics http://baanjompra.com/webboard/home.php?mod=space&uid=19101 perfect skin without effort! Innovative formulas, Asian traditions and visible results. Try the best skin care products right now!
http://slot88.company/# Jackpot progresif menarik banyak pemain
Kasino mendukung permainan bertanggung jawab http://bonaslot.site/# Banyak pemain berusaha untuk mendapatkan jackpot
UID_97211224###
Yuk, sehat bersama! 👨⚕️👩⚕️ Cek kondisi tubuh kamu di Program Cek Kesehatan Gratis sekarang juga! 💉🌡️ Selalu jaga kesehatan, ya! 🏥💖
generic amoxicillin cost: amoxicillin 500 tablet – amoxicillin 250 mg price in india
Drop a link to your favorite blog post of yours in the comments below, I’d love to read more.
I think this site holds very great written subject material content .
generic zithromax india: can you buy zithromax over the counter in mexico – generic zithromax online paypal
I am curious to find out what blog system you’re utilizing?
I’m having some minor security issues with my latest website and
I’d like to find something more secure. Do you have
any recommendations?
amoxicillin 500: AmoHealthPharm – purchase amoxicillin online without prescription
http://amohealthpharm.com/# how much is amoxicillin
электрокарнизы для штор купить электрокарнизы для штор купить .
электрокарниз москва https://www.prokarniz11.ru .
электронный карниз для штор электронный карниз для штор .
teacher full sex video teacher full sex video .
amoxicillin 500 coupon amoxicillin without a doctors prescription amoxicillin 500mg prescription
автоматический карниз для штор [url=www.prokarniz17.ru/]автоматический карниз для штор[/url] .
электрокарниз купить в москве электрокарниз купить в москве .
teacher and student pron video teacher and student pron video .
электро карниз на окна электро карниз на окна .
amoxicillin 500: amoxicillin canada price – amoxicillin 825 mg
гардина с электроприводом гардина с электроприводом .
buying clomid tablets: ClmHealthPharm – cheap clomid pills
can you buy zithromax over the counter: Zithro Pharm – zithromax order online uk
Хочешь купить ПАВ в Москве? Нова маркетплейс – ищи в Яндекс!
Хочешь купить ПАВ в СПБ? Нова маркетплейс – ищи в Яндекс!
мтс екатеринбург
https://enitajobs.com/employer/inetrnet-domashnij-ekb-2/
мтс подключить екатеринбург
https://zithropharm.shop/# zithromax cost uk
карниз электро карниз электро .
UID_97211224###
Yuk, sehat bersama! 👨⚕️👩⚕️ Cek kondisi tubuh kamu di Program Cek Kesehatan Gratis sekarang juga! 💉🌡️ Selalu jaga kesehatan, ya! 🏥💖
buy cheap generic zithromax: zithromax 500 – zithromax buy
where to get generic clomid without prescription: where to get clomid price – can i purchase cheap clomid without insurance
prescription for amoxicillin: where can i buy amoxicillin online – prescription for amoxicillin
https://clmhealthpharm.shop/# order generic clomid no prescription
мтс подключить
https://smarthr.hk/Companies/inetrnet-domashnij-ekb-3/
мтс интернет
UID_96794283###
Kisah Pak Darman, OB Sekolah yang Mendadak Tajir – Nasib seseorang bisa berubah dalam sekejap! Pak Darman, seorang OB sekolah, kini tak lagi khawatir soal keuangan setelah menang 200 juta. Keberuntungannya benar-benar luar biasa
UID_40226211###
Berita Hangat! 📰🔥 Bimbel Gratis Bagi Siswa SMAN 7 Cirebon yang Gagal SNBP! 😲🎓👍.
UID_40226211###
Berita Hangat! 📰🔥 Bimbel Gratis Bagi Siswa SMAN 7 Cirebon yang Gagal SNBP! 😲🎓👍.
zithromax online ZithroPharm where can you buy zithromax
how much is amoxicillin: AmoHealthPharm – buy amoxicillin from canada
UID_56782343###
Ini dia kabar baiknya! 👏🎉 Bimbel Gratis untuk 150 Siswa dari SMAN 7 Cirebon yang gagal SNBP. Ayoo semangat terus! 💪📚🎓
It’s rare knowledgeable people during this topic, however, you seem like do you know what you’re discussing! Thanks
buy amoxicillin: Amo Health Pharm – amoxicillin 875 mg tablet
Keep up the fantastic work!
Prostavive is a uniquely crafted dietary supplement aimed at promoting healthy blood sugar levels.
doxycycline 100mg dogs: Dox Health Pharm – cheapest doxycycline tablets
https://zithropharm.shop/# zithromax 500 tablet
can you buy doxycycline over the counter in india: Dox Health Pharm – where can i order doxycycline
I blog often and I truly thank you for your information. Your article has truly peaked my interest. I’m going to bookmark your website and keep checking for new details about once a week. I subscribed to your RSS feed too.
https://web.archive.org/web/20170111172306/https:/scholarlyoa.com/publishers/
мтс телевидение
https://www.bridgewaystaffing.com/employer/inetrnet-domashnij-ekb-2/
мтс интернет
street light controller street lighting solutions
Сауна очищает организм https://sauna-broadway.ru выводя токсины через пот, укрепляет иммунитет благодаря перепадам температуры, снимает стресс, расслабляя мышцы и улучшая кровообращение. Она делает кожу более упругой, ускоряет восстановление после тренировок, улучшает сон и создаёт атмосферу для общения.
профессиональный лечебный массаж Ивантеевка расслабляющие техники для здоровья и красоты. Помогаем снять стресс, улучшить кровообращение и восстановить силы. Запишитесь прямо сейчас!
супрастин таблетки инструкция по применению взрослым от аллергии дозировка как принимать взрослым https://allergiano.ru/ .
doxycycline canada price: Dox Health Pharm – buy doxycycline without rx
Нужны деньги оперативно? Получите займ онлайн без поручителей на https://zaym-tula.ru/ без отказа! Оставьте запрос и получите финансы за минуту!
can you buy zithromax over the counter in australia: ZithroPharm – generic zithromax over the counter
doxycycline canada price: doxyhexal – doxycycline prices australia
https://zithropharm.shop/# zithromax over the counter canada
Glucotonic is a uniquely crafted dietary supplement aimed at promoting healthy blood sugar levels.
can i buy clomid for sale how to buy cheap clomid no prescription cost of cheap clomid tablets
Sometimes, a Dark Lord similar to Darth Rivan or Darth Ruin would rise and fall, however the Sith did not grow to be a serious risk again until round 2,500 years later.
You may have an creative tattoo inked on your skin in black ink.
прокарниз https://prokarniz20.ru/ .
электрокарнизы в москве электрокарнизы в москве .
электрокарниз двухрядный http://www.prokarniz34.ru .
мтс домашний интернет екатеринбург
https://empleos.contatech.org/employer/inetrnet-domashnij-ekb-3/
мтс домашний интернет екатеринбург
This blog post hit all the right notes!
can i buy generic clomid without prescription: where buy clomid online – where to get clomid now
электрокарнизы в москве электрокарнизы в москве .
спины за регистрацию без депозита бесплатные спины
карнизы электрические карнизы электрические .
электрокарнизы москва электрокарнизы москва .
Женский онлайн портал https://brjunetka.ru для вдохновения! Полезные советы по стилю, уходу за собой, здоровью и семейной жизни. Будьте в курсе трендов, находите мотивацию и делитесь опытом!
Портал с ответами https://online-otvet.site на все школьные предметы! Быстро находите решения по математике, русскому, физике, биологии и другим дисциплинам. Готовые ответы, разборы задач и помощь в учебе для всех классов
Glucotonic is a uniquely crafted dietary supplement aimed at promoting healthy blood sugar levels.
doxycycline 200: doxycycline 100 mg tablets – doxycycline 40 mg generic
amoxicillin online no prescription: cost of amoxicillin – where can i buy amoxicillin over the counter
https://clmhealthpharm.com/# cost of generic clomid price
boost of subscribers instagram tg channel boost
Элитный коттеджный поселок https://parkville-zhukovka-poselok.ru в Жуковке! Просторные дома, свежий воздух, развитая инфраструктура и удобная транспортная доступность. Создайте уютное пространство для жизни в живописном месте!
demontaz nabytku stehovani recenze
youtube followers boost cheap smm panel
cost of generic clomid: can you buy cheap clomid without rx – where buy cheap clomid without dr prescription
El codigo promocional 1xBet 2025: “1XBUM” brinda a los nuevos usuarios un bono del 100% hasta $130. Ademas, el codigo promocional 1xBet de hoy permite acceder a un atractivo bono de bienvenida en la seccion de casino, que ofrece hasta $2275 USD (o su equivalente en VES) junto con 150 giros gratis. Este codigo debe ser ingresado al momento de registrarse en la plataforma para poder disfrutar del bono de bienvenida, ya sea para apuestas deportivas o para el casino de 1xBet. Los nuevos clientes que se registren utilizando el codigo promocional tendran la oportunidad de beneficiarse de la bonificacion del 100% para sus apuestas deportivas.
Utiliza el codigo de bonificacion de 1xCasino: “1XBUM” para obtener un bono VIP de hasta €1950 mas 150 giros gratis en el casino y un 200% hasta €130 en apuestas deportivas. Introduce nuestro codigo promocional para 1x Casino 2025 en el formulario de registro y reclama bonos exclusivos para el casino y las apuestas deportivas. Bonificacion sin deposito de 1xCasino de $2420. Es necesario registrarse, confirmar tu correo electronico e ingresar el codigo promocional.
bono 1xbet como funciona
провайдер мтс
https://bewerbermaschine.de/employer/inetrnet-domashnij-ekb-2/
мтс подключение
El codigo promocional 1xBet 2025: “1XBUM” brinda a los nuevos usuarios un bono del 100% hasta $130. Ademas, el codigo promocional 1xBet de hoy permite acceder a un atractivo bono de bienvenida en la seccion de casino, que ofrece hasta $2275 USD (o su equivalente en VES) junto con 150 giros gratis. Este codigo debe ser ingresado al momento de registrarse en la plataforma para poder disfrutar del bono de bienvenida, ya sea para apuestas deportivas o para el casino de 1xBet. Los nuevos clientes que se registren utilizando el codigo promocional tendran la oportunidad de beneficiarse de la bonificacion del 100% para sus apuestas deportivas.
Utiliza el codigo de bonificacion de 1xCasino: “1XBUM” para obtener un bono VIP de hasta €1950 mas 150 giros gratis en el casino y un 200% hasta €130 en apuestas deportivas. Introduce nuestro codigo promocional para 1x Casino 2025 en el formulario de registro y reclama bonos exclusivos para el casino y las apuestas deportivas. Bonificacion sin deposito de 1xCasino de $2420. Es necesario registrarse, confirmar tu correo electronico e ingresar el codigo promocional.
codigo promocional 1xCasino moz
zithromax cost canada Zithro Pharm zithromax online paypal
buy amoxicillin online cheap: AmoHealthPharm – where can i buy amoxicillin online
amoxicillin tablets in india: AmoHealthPharm – generic amoxicillin
http://zithropharm.com/# zithromax azithromycin
how to get zithromax online: zithromax canadian pharmacy – how much is zithromax 250 mg
cheap smm panel boost of subscribers in telegram live
Все о строительстве https://decor-kraski.com.ua и ремонте в одном месте! Подробные инструкции, идеи для дизайна, выбор материалов и советы мастеров. Сделайте свой дом удобным, стильным и долговечным!
Портал про строительство https://goodday.org.ua и ремонт! Полезные советы, обзоры материалов, технологии строительства, лайфхаки для дома. Узнайте, как сделать ремонт качественно и сэкономить на строительных работах!
шторы с приводом шторы с приводом .
рулонные шторы с электроприводом купить в москве рулонные шторы с электроприводом купить в москве .
мтс интернет
https://empleos.contatech.org/employer/inetrnet-domashnij-ekb/
мтс подключение
шторы с электроприводом шторы с электроприводом .
This blog is like a breath of fresh air in the midst of all the negativity on the internet I’m grateful to have stumbled upon it
роликовые шторы роликовые шторы .
zithromax 500 tablet: zithromax 500 mg – can i buy zithromax over the counter
https://clmhealthpharm.com/# cost clomid without insurance
amoxicillin 500mg price canada: amoxicillin no prescipion – where can you get amoxicillin
zithromax pill: zithromax buy – where can you buy zithromax
Ремонт и строительство https://inbound.com.ua без хлопот! Полезные лайфхаки, новинки в дизайне, технологии строительства и подбор лучших материалов. Создайте комфортное жилье легко и выгодно!
Ваш надежный помощник https://insurancecarhum.org в ремонте! Практичные советы, инструкции и секреты профессионалов. Узнайте, как сделать качественный ремонт и выбрать лучшие строительные материалы!
Портал для строителей https://hotel.kr.ua и домашних мастеров! Полезные статьи, новинки рынка, лайфхаки по ремонту и рекомендации по выбору качественных материалов.
автоматические римские шторы с электроприводом автоматические римские шторы с электроприводом .
somfy motors [url=www.prokarniz25.ru]somfy motors[/url] .
римская штора на окно римская штора на окно .
amoxicillin 500mg no prescription: amoxicillin 500 – medicine amoxicillin 500
карнизы somfy карнизы somfy .
how to buy amoxicillin online amoxicillin 875 125 mg tab amoxicillin 500mg prescription
Инструкции по ремонту https://makprestig.in.ua подбор материалов, планирование, дизайн и советы экспертов. Станьте мастером своего дома!
Лучший портал по строительству https://itstore.dp.ua и ремонту! Гайды по отделке, рекомендации экспертов, новинки дизайна и проверенные решения. Все для вашего комфорта!
мтс екатеринбург
https://justhired.co.in/employer/inetrnet-domashnij-ekb-2/
мтс подключить
Как сделать ремонт https://oo.zt.ua правильно? Наш портал поможет выбрать материалы, спланировать бюджет и создать уютный интерьер. Простые решения для сложных задач!
This web site definitely has all of the information and facts I wanted concerning this subject and didn’t know who to ask.
почему многие
https://clmhealthpharm.shop/# can i order generic clomid
500 mg doxycycline pill: doxycycline pharmacy – doxycycline hyc
zithromax 250mg: buy zithromax no prescription – buy zithromax without presc
Профессиональные советы https://ukk.kiev.ua по ремонту и строительству! Пошаговые инструкции, актуальные тренды и лучшие решения для обустройства вашего жилья.
Идеи для дома https://ucmo.com.ua ремонта и строительства! Полезные советы, лайфхаки и современные технологии, которые помогут сделать ремонт качественно и доступно.
Ремонт без стресса https://panorama.zt.ua Готовые решения, полезные лайфхаки, выбор материалов и идеи для дома. Делаем ремонт комфортным и доступным!
doxycycline uk online: Dox Health Pharm – doxycycline 1mg
Идеи для дома https://ucmo.com.ua ремонта и строительства! Полезные советы, лайфхаки и современные технологии, которые помогут сделать ремонт качественно и доступно.
Делаем ремонт правильно https://zarechany.zt.ua Разбираем все этапы – от выбора материалов до дизайна интерьера. Подробные инструкции и лайфхаки от специалистов!
Автомобильный портал https://nerjalivingspace.com для автолюбителей! Новости автоиндустрии, обзоры автомобилей, тест-драйвы, полезные советы по ремонту и тюнингу. Будьте в курсе последних трендов и находите ответы на все авто-вопросы!
мтс тв
http://rejobbing.com/companies/inetrnet-domashnij-ekb-3/
сайт мтс екатеринбург
https://doxhealthpharm.shop/# doxycycline 100mg price
A New Game To Try With Your Family Adam and Eve 2 Walkthrough, BrainTY Games Balloon Protect Rise Up está en el móvil para que puedas descargar y disfrutar del juego de globos. Transforma tus fotos en arte de IA en línea Regístrese hoy para recibir correos electrónicos sobre nuevos productos, eventos especiales y promociones. Payments to United Negro College Fund are made via the PayPal Giving Fund.UNCF envisions a nation where all Americans have equal access to a college education that prepares them for rich intellectual lives, competitive and fulfilling careers, engaged citizenship, and service to our nation. Arachnia Flash Game, Walkthrough Video © 2025 All American BalloonsTecnología de Shopify Balloon Fight – cualquier entusiasta de los globos aerostáticos que quiera practicar su técnica de vuelo puede hacerlo en este juego. El compañero controlado por el jugador tiene dos globos sujetos a su espalda que le permiten volar. Desafortunadamente, nuestro vuelo es obstaculizado por otros tipos que vuelan en globos. Por eso nuestro objetivo es deshacernos de las plagas y destruir sus globos para que caigan al suelo y no ocupen nuestro valioso espacio aéreo. También debemos tener cuidado con las nubes de tormenta que disparan rayos y un gran pez listo para morder si volamos demasiado bajo sobre la superficie del agua. Juego divertido y adictivo con la posibilidad de jugar con dos jugadores. Diversión pura.
https://ngeeannpoly-54.s6.vatitude.com/balloon-casino-balloon-game-la-manera-sobre-como-conseguir-y-lo-que-haber-acerca-de-perfil/
Bloons TD 6 es un juego de defensa de torres en el que, al igual que en entregas anteriores de la saga, los usuarios deben evitar a toda costa que los globos, conocidos como “Bloons”, lleguen al final del camino. Para ello, tendrán que hacer uso de diversas herramientas y construcciones para conseguir detenerlos o explotarlos. ¡Pero cuidado! Ten en cuenta que no todas las torres podrán detener los distintos tipos de globos. Mod Info: Descubre en esta guía cómo perforar las bolas de plomo en Bloons TD 6, si aún te interesa esta cuestión sigue leyendo, te diremos cómo hacerlo. Bloons TD 6 es un juego de defensa de torres en el que, al igual que en entregas anteriores de la saga, los usuarios deben evitar a toda costa que los globos, conocidos como “Bloons”, lleguen al final del camino. Para ello, tendrán que hacer uso de diversas herramientas y construcciones para conseguir detenerlos o explotarlos. ¡Pero cuidado! Ten en cuenta que no todas las torres podrán detener los distintos tipos de globos.
zithromax prescription: Zithro Pharm – zithromax online usa
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
how to get cheap clomid pills: can i purchase generic clomid – cost of clomid without a prescription
doxycycline 100 mg cap: doxycycline 100mg best buy – cost doxycycline tablets uk
Все для женщин https://elegance.kyiv.ua в одном месте! Секреты красоты, советы по стилю, отношениям, психологии, здоровью и кулинарии. Будьте вдохновленными и уверенными каждый день!
Женский портал https://beautyadvice.kyiv.ua для современной женщины! Мода, красота, здоровье, отношения, кулинария и карьера. Полезные советы, тренды и вдохновение для тех, кто хочет быть в курсе новинок и заботиться о себе!
Онлайн мир женщины https://gracefullady.kyiv.ua красота, здоровье, успех! Полезные лайфхаки, тренды моды, секреты счастья и гармонии. Портал для тех, кто хочет быть лучшей версией себя!
doxycycline cap 50mg Dox Health Pharm doxycycline brand name india
1win на телефон http://www.1win3.com.kg .
Портал для современной https://femaleguide.kyiv.ua женщины! Открой для себя новые идеи в моде, красоте, отношениях и саморазвитии. Полезные статьи и советы для комфортной и счастливой жизни
https://doxhealthpharm.shop/# buy doxycycline 100mg
Мир женщины https://fashionadvice.kyiv.ua красота, здоровье, успех! Полезные лайфхаки, тренды моды, секреты счастья и гармонии. Портал для тех, кто хочет быть лучшей версией себя!
Твой гид в мире https://happywoman.kyiv.ua женственности и гармонии! Узнай больше о моде, косметике, фитнесе, отношениях и мотивации. Все, что нужно для яркой и счастливой жизни!
мегафон тв екатеринбург
https://ekb-domasnij-internet-2.ru
мегафон тарифы на интернет
can i purchase generic clomid without prescription: get generic clomid without rx – can i buy cheap clomid without dr prescription
doxycycline 100mg capsules price in india: Dox Health Pharm – doxycycline uk pharmacy
amoxicillin 875 mg tablet: AmoHealthPharm – amoxicillin 500 mg where to buy
1 win сайт http://www.1win4.com.kg .
At the start of a project, the development of technical developments, or threats introduced by a competitor’s initiatives, may trigger a danger or menace assessment and subsequent evaluation of options (see Evaluation of Options).
https://clmhealthpharm.shop/# buying cheap clomid without dr prescription
мегафон интернет екатеринбург
https://ekb-domasnij-internet-3.ru
мегафон домашний интернет
zithromax 500 mg lowest price online: zithromax 500 mg – zithromax 500 mg for sale
zithromax 500 without prescription: ZithroPharm – buy zithromax no prescription
1вин 1вин .
мостбет личный кабинет http://www.mostbet1.com.kg .
Forex or Foreign trade market is one in every of the biggest and most unstable markets in the world.
buy zithromax: zithromax for sale 500 mg – zithromax 500mg price
price of doxycycline 100mg doxycycline 100mg price uk doxycycline 100 cost
Безопасный доступ к сайту https://bsme-at.at без ограничений. Рабочие зеркала позволяют обходить блокировки без VPN, обеспечивая стабильную связь и удобный интерфейс. Следите за обновлениями, чтобы всегда оставаться в сети.
Всегда актуальные ссылки https://bs2bet.at для входа. Обходите блокировки легко и быстро, используя надёжные зеркала. Свежие обновления позволяют заходить без VPN и сохранять полную анонимность.
Актуальные зеркала BlackSprut https://kra26.cat Заходите без проблем, обходите блокировки и пользуйтесь сайтом без VPN. Мы следим за обновлениями и всегда предоставляем свежие ссылки.
Проблемы с входом https://bs2best.or.at Найдите актуальные зеркала и заходите без ограничений. Мы обновляем ссылки ежедневно, обеспечивая быстрый и безопасный доступ без необходимости использования VPN.
1win kg 1win kg .
ставки на спорт бишкек https://mostbet1.com.kg/ .
The Katronic vary of flow meters can cowl pipe diameters from 10 millimeter (mm) to 3,000 mm.
BlackSprut это инновационный https://bs2best.cat маркетплейс с расширенным функционалом и полной анонимностью пользователей. Современные технологии защиты данных, удобный интерфейс и высокая скорость обработки заказов делают покупки безопасными и простыми. Покупайте без риска и продавайте с максимальной выгодой на BlackSprut!
BlackSprut крупнейший маркетплейс https://bb2best.at где можно найти всё, что вам нужно. Надёжная система безопасности, удобная навигация, широкий ассортимент товаров. Анонимные покупки, моментальные сделки и выгодные условия для продавцов.
BlackSprut передовой маркетплейс https://m-bsme.at с высокими стандартами безопасности и удобной системой поиска. Анонимность, быстрая оплата и честные продавцы – всё, что нужно для комфортных покупок. Мы гарантируем защиту ваших данных и качественное обслуживание. Присоединяйтесь к BlackSprut и открывайте новые возможности!
https://tadalafilmeilleurprix.com/# pharmacie en ligne france livraison belgique
Pharmacie en ligne livraison Europe
vente de mГ©dicament en ligne http://pharmaciemeilleurprix.com/# acheter mГ©dicament en ligne sans ordonnance
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you could do with a few pics to drive the message home a bit, but instead of that, this is magnificent blog. A fantastic read. I’ll definitely be back.
https://vchatesexa.ru/
проверенный маркетплейс https://bsme.cat предлагающий товары на любой вкус. Простая регистрация, быстрая оплата и защита сделок. Убедитесь в качестве сервиса сами!
Blacksprut – современная площадка https://bs-bsme.at для безопасных покупок. Большой выбор категорий, продуманная система рейтингов и отзывов. Заходите и находите нужное легко!
Viagra 100 mg sans ordonnance: viagra sans ordonnance – Viagra sans ordonnance 24h suisse
Blacksprut – онлайн-маркетплейс https://bsmc.at с лучшими предложениями. Надёжные продавцы, защищённые сделки, удобный поиск. Оцените удобство покупок уже сегодня!
Ищете актуальные бездепозитные бонусы казино? Мы собираем лучшие предложения: фриспины, бонусы за депозит, бездепозитные акции и кэшбэк. Получите максимум выгоды от игры!
мегафон телевидение екатеринбург
https://ekb-domasnij-internet.ru
мегафон подключить
pharmacie en ligne: kamagra pas cher – Pharmacie sans ordonnance
Replica Uhren https://www.imailen.com in Deutschland schnell und sicher per DHL Nachnahme bestellen. Nur geprufte Qualitat in EU hergestellt.
Журнал об автомобилях https://setbook.com.ua всё для автолюбителей! Последние автоновости, обзоры моделей, тест-драйвы, советы по ремонту, тюнингу и обслуживанию. Узнайте всё о мире автомобилей!
http://viagrameilleurprix.com/# Prix du Viagra en pharmacie en France
pharmacie en ligne france fiable
Главный авто-журнал https://myauto.kyiv.ua для водителей! Новости, обзоры, сравнения, тюнинг, автоспорт и технологии. Будьте в курсе последних трендов автомобильного мира!
купить топ шмот path of exile 2 купить божественные сферы пое 2
Pharmacie en ligne livraison Europe https://kamagrameilleurprix.shop/# acheter mГ©dicament en ligne sans ordonnance
купить услуги буста path of exile 2 купить сферы отмены пое 2
pharmacies en ligne certifiГ©es Pharmacies en ligne certifiees pharmacie en ligne france fiable
Viagra femme sans ordonnance 24h: Acheter Viagra Cialis sans ordonnance – Acheter Sildenafil 100mg sans ordonnance
Все об автомобилях https://allauto.kyiv.ua в одном журнале! Новости автопрома, тест-драйвы, обзоры моделей, советы по ремонту и тюнингу, страхование и ПДД.
Журнал для автолюбителей https://myauto.kyiv.ua и профессионалов! Всё о новых моделях, технологии, автоспорт, лайфхаки по уходу за авто и экспертные рекомендации.
Журнал об авто https://auto-club.pl.ua для тех, кто за рулем! Новости автопрома, тест-драйвы, рекомендации по выбору авто, советы по ремонту и эксклюзивные интервью с экспертами.
acheter mГ©dicament en ligne sans ordonnance: pharmacie en ligne france livraison internationale – pharmacies en ligne certifiГ©es
билайн интернет
https://infodomashnij-internet-krasnodar-2.ru
билайн домашний интернет краснодар
https://tadalafilmeilleurprix.com/# п»їpharmacie en ligne france
pharmacie en ligne france fiable
pharmacie en ligne france livraison internationale http://tadalafilmeilleurprix.com/# Achat mГ©dicament en ligne fiable
pharmacie en ligne france livraison internationale: Tadalafil sans ordonnance en ligne – pharmacie en ligne pas cher
pharmacie en ligne sans ordonnance: acheter kamagra site fiable – acheter mГ©dicament en ligne sans ordonnance
мост бет букмекерская контора мост бет букмекерская контора .
vjcn,tn [url=https://mostbet112.ru/]vjcn,tn[/url] .
п»їpharmacie en ligne france cialis sans ordonnance trouver un mГ©dicament en pharmacie
https://kamagrameilleurprix.shop/# п»їpharmacie en ligne france
Pharmacie sans ordonnance
Your blog has become a part of my daily routine Your words have a way of brightening up my day and lifting my spirits
pharmacie en ligne livraison europe https://kamagrameilleurprix.shop/# Pharmacie Internationale en ligne
букмекерская компания mostbet http://www.mostbet113.ru/ .
мосьет мосьет .
провайдер билайн
https://infodomashnij-internet-krasnodar-3.ru
билайн тв краснодар
vjcn,tn vjcn,tn .
pharmacie en ligne: cialis generique – pharmacie en ligne france livraison belgique
pharmacie en ligne france fiable: kamagra en ligne – vente de mГ©dicament en ligne
While that’s not a guarantee that a proprietary piece of software program will probably be better than an open supply version, it can be an advantage.
Все о машинах https://autoinfo.kyiv.ua в одном журнале! Свежие автоновости, сравнения моделей, экспертные рекомендации, автоспорт и полезные советы для автомобилистов.
Автомобильный мир https://diesel.kyiv.ua в одном журнале! Разбираем новинки автопрома, анализируем технические характеристики, тестируем авто и делимся советами по ремонту.
Журнал для автолюбителей https://avtoshans.in.ua и профессионалов! Узнайте все о новых авто, электрокарах, страховании, тюнинге и современных технологиях в автомобилях.
Viagra pas cher paris: acheter du viagra – Quand une femme prend du Viagra homme
pharmacie en ligne france pas cher https://kamagrameilleurprix.com/# acheter mГ©dicament en ligne sans ordonnance
This is such an informative and well-written post! I learned a lot from reading it and will definitely be implementing some of these tips in my own life
https://tadalafilmeilleurprix.com/# pharmacie en ligne france livraison belgique
trouver un mГ©dicament en pharmacie
мост бет ком http://mostbet2.com.kg .
Современный автомобильный https://k-moto.com.ua журнал! Читайте о трендах в автоиндустрии, новейших моделях, электромобилях, тюнинге и умных технологиях.
Журнал о машинах https://reuth911.com для настоящих ценителей авто! Обзоры, рейтинги, полезные статьи о ремонте, тюнинге и современных автомобильных технологиях.
Автомобильный журнал https://orion-auto.com.ua только важные новости! Все о популярных марках, топовые авто 2024 года, электрокары, автономное вождение и тенденции рынка.
Автомобильный мир https://prestige-avto.com.ua в одном журнале! Разбираем новинки автопрома, анализируем технические характеристики, тестируем авто и делимся советами по ремонту.
билайн подключение
https://infodomashnij-internet-krasnodar.ru
билайн цены
ваучер мостбет https://mostbet2.com.kg/ .
pharmacie en ligne france livraison belgique: kamagra en ligne – п»їpharmacie en ligne france
pharmacie en ligne france fiable: Cialis sans ordonnance 24h – vente de mГ©dicament en ligne
Hi there! Someone in my Facebook group shared this website with us so I came
to give it a look. I’m definitely enjoying the information. I’m book-marking and will
be tweeting this to my followers! Terrific blog and amazing
design.
pharmacie en ligne sans ordonnance pharmacie en ligne Pharmacie en ligne livraison Europe
blue sp5der hoodie http://spiderhoodie-us.com/spider-hoodies/ .
pink sp5der hoodie pink sp5der hoodie .
Pharmacie sans ordonnance http://viagrameilleurprix.com/# Viagra pas cher livraison rapide france
Твой авто-гид https://troeshka.com.ua в мире машин! Обзоры новых моделей, тест-драйвы, советы по ремонту и тюнингу, автоновости и технологии будущего. Все, что нужно автолюбителю!
Все об автомобилях https://tvk-avto.com.ua на одном портале! Новинки мирового автопрома, тест-драйвы, автострахование, электрокары и полезные статьи для каждого водителя.
Журнал про автолюбители https://tuning-kh.com.ua новости, тесты, обзоры! Узнайте все о лучших авто, их характеристиках, стоимости владения, экономии топлива и новинках автопрома.
Твой идеальный женский https://family-site.com.ua журнал! Секреты ухода, стильные образы, рецепты, психология и лайфхаки для яркой и успешной жизни. Вдохновение каждый день!
https://kamagrameilleurprix.shop/# Pharmacie en ligne livraison Europe
pharmacie en ligne avec ordonnance
Pharmacie sans ordonnance: kamagra pas cher – pharmacie en ligne
Проблемы с сантехникой в Минске? Мы реализуем аварийные вызовы с высоким качеством. Наши профессиональные мастера готовы обеспечить профилактическое обслуживание. Узнайте больше на Монтаж сантехники Минск .
pharmacie en ligne fiable: pharmacie en ligne – pharmacie en ligne sans ordonnance
Проблемы с сантехникой? Мы реализуем аварийные вызовы в Минске с доступными ценами. Наши опытные сантехники готовы выполнить монтаж. Узнайте больше на вызов сантехника минск .
Актуальные новости https://www.moscow.regnews.info Московского региона! Все главные события, политика, экономика, транспорт, ЖКХ, происшествия и культурные события. Будьте в курсе того, что происходит в вашем городе!
Главный женский журнал https://amideya.com.ua о стиле и успехе! Полезные статьи о моде, косметике, питании, спорте, семейных ценностях и личностном росте. Читай и развивайся вместе с нами!
Твой идеальный женский https://femalesecret.kyiv.ua журнал! Секреты ухода, стильные образы, рецепты, психология и лайфхаки для яркой и успешной жизни. Вдохновение каждый день!
Портал для женщин https://feminine.kyiv.ua твой путеводитель в мире стиля и успеха! Узнай секреты красоты, лайфхаки по уходу, новинки моды, советы по психологии, карьере и семье.
You may look at cleaning companies online like Molly Maids, search on dwelling providers websites like Angie’s Listing, or ask for recommendations from associates or neighborhood websites like Nextdoor.
pharmacie en ligne sans ordonnance: Tadalafil sans ordonnance en ligne – pharmacie en ligne france livraison internationale
Pharmacie sans ordonnance https://kamagrameilleurprix.shop/# Pharmacie Internationale en ligne
Твой женский портал https://girl.kyiv.ua о стиле и гармонии! Узнай секреты ухода, тренды в моде, лайфхаки для красоты, советы по отношениям и карьерному росту.
порно зрелые порно шлюхи
Главный женский портал https://horoscope-web.com будь в центре трендов! Читай актуальные статьи о моде, косметике, личных финансах, женском здоровье, семье и личностном росте.
Портал для женщин https://lolitaquieretemucho.com которые ценят себя! Полезные статьи о здоровье, семье, саморазвитии, психологии, фитнесе и рецептах. Будь уверенной, счастливой и успешной!
https://kamagrameilleurprix.com/# Pharmacie Internationale en ligne
pharmacie en ligne fiable
https://t.me/detivetrachat
Viagra pas cher livraison rapide france: viagra sans ordonnance – Viagra vente libre pays
vente de mГ©dicament en ligne kamagra livraison 24h pharmacie en ligne france fiable
Pharmacie Internationale en ligne: Tadalafil sans ordonnance en ligne – trouver un mГ©dicament en pharmacie
Q: What are the barriers to non-sexual intimacy?
Как заменить турбину на машине и не переплатить втрое больше. Типичная схема развода на замену турбины. Будьте осторожны. Подробности тут Как заменить турбину на машине и не переплатить втрое больше. Типичная схема развода на замену турбины. Будьте осторожны. Подробности тут .
соут москва цена соут москва цена .
Pharmacie sans ordonnance http://viagrameilleurprix.com/# Viagra sans ordonnance pharmacie France
Чистоговорки для детей Чистоговорки для детей .
билайн телевидение краснодар
https://plus-domashnij-internet-krasnodar-2.ru
билайн интернет краснодар
https://viagrameilleurprix.com/# Acheter viagra en ligne livraison 24h
pharmacie en ligne sans ordonnance
Nevertheless, earlier than you jumpstart your venture, you have to read this text.
Как заменить турбину на машине и не переплатить втрое больше. Типичная схема развода на замену турбины. Будьте осторожны. Подробности тут Как заменить турбину на машине и не переплатить втрое больше. Типичная схема развода на замену турбины. Будьте осторожны. Подробности тут .
оценка факторов условий труда оценка факторов условий труда .
Портал для женщин https://nicegirl.kyiv.ua которые любят себя! Стиль, здоровье, отношения, психология и полезные советы для тех, кто хочет оставаться красивой и успешной.
Achat mГ©dicament en ligne fiable: pharmacie en ligne france fiable – pharmacie en ligne france fiable
Чистоговорки для детей Чистоговорки для детей .
Твой путеводитель https://mirlady.kyiv.ua в мире женских секретов! Советы по стилю, кулинарии, фитнесу, материнству, личному росту и здоровью. Всё, что нужно для счастливой жизни!
Современный женский портал https://presslook.com.ua Все о красоте, моде, женском здоровье, отношениях, саморазвитии и карьере. Читай, вдохновляйся и меняй свою жизнь к лучшему!
Твой идеальный https://prettywoman.kyiv.ua женский портал! Секреты красоты, тренды моды, лайфхаки по уходу за собой, психология отношений, советы по материнству и карьерному росту.
pharmacie en ligne france pas cher: Acheter Cialis – pharmacie en ligne france livraison belgique
Сайт для женщин https://ramledlightings.com будь лучшей версией себя! Читай о моде, красоте, психологии, отношениях, материнстве и женском здоровье. Найди вдохновение и полезные советы для каждого дня!
Лучший портал для родителей https://geog.org.ua и детей! Читайте о воспитании, обучении, здоровье, детской психологии, играх и семейном досуге. Советы экспертов и практические рекомендации.
Портал о детях https://mch.com.ua полезно для родителей! Воспитание, здоровье, развитие, обучение, досуг, игры и семейные традиции. Экспертные советы, лайфхаки и полезные материалы для гармоничного роста малыша.
Твой женский сайт https://musicbit.com.ua о стиле, здоровье и вдохновении! Узнай секреты красоты, следи за модными новинками, развивайся, читай о психологии отношений и оставайся в гармонии с собой.
Нужны средства срочно? Получите микрозайм на карточный счет за четверть часа. https://zaym-bez-proverok.ru/ Оформите запрос без бумаг и получите согласие уже в кратчайшие сроки!
pharmacies en ligne certifiГ©es http://kamagrameilleurprix.com/# п»їpharmacie en ligne france
Pharmacie sans ordonnance: Acheter Cialis – pharmacie en ligne pas cher
https://pharmaciemeilleurprix.com/# pharmacie en ligne sans ordonnance
pharmacies en ligne certifiГ©es
билайн интернет краснодар
https://plus-domashnij-internet-krasnodar.ru
билайн тв краснодар
pharmacies en ligne certifiГ©es pharmacie en ligne pas cher pharmacie en ligne france fiable
Thank you for another fantastic article. The place else could anyone get that kind of information in such an ideal way of writing? I have a presentation subsequent week, and I am at the look for such information.
https://science.tdtu.edu.vn/node/437
pharmacie en ligne pas cher: pharmacie en ligne pas cher – Pharmacie sans ordonnance
Нужны кредит срочно? Получите онлайн-заем на пластиковую карту за мгновение. https://zaym-bez-proverok.ru/ Оформите анкету без справок и получите одобрение уже в этот день!
pharmacie en ligne france livraison internationale: kamagra pas cher – pharmacie en ligne france livraison belgique
Справочник лекарственных https://mikstur.com средств – полная информация о медикаментах! Описания, показания, противопоказания, дозировки, аналоги и инструкции по применению.
Портал о здоровье https://fines.com.ua все, что нужно для крепкого организма! Советы врачей, профилактика болезней, здоровое питание, спорт, психология, народная медицина и лайфхаки для долгой и активной жизни.
турецкие сериалы 1 сезон турецкие сериалы смотретя
That is a very good tip especially to those fresh to the blogosphere. Brief but very accurate info… Thanks for sharing this one. A must read post.
Pharmacie sans ordonnance http://tadalafilmeilleurprix.com/# trouver un mГ©dicament en pharmacie
смотреть лучшие турецкие сериалы турецкий сериал смотреть
лучшие сериалы на турецком языке смотреть турецкие сериалы онлайн
турецкий сериал любовь https://turokk.net
смотреть турецкие сериалы на русском смотреть турецкие сериалы онлайн бесплатно
Приветствую всех, теперь Casino X есть в Телеграм!
Свежи новости, ответы на вопросы и эксклюзивные бонусы уже ждут вас.
Присоединйся сейчас и получите 100% бонус до 2000 долларов!
Эксклюзивный промокод на фриспины только для наших подписчиков.
Ищите нас по ID: @casinox_rus
Или жмите на ссылку: Casino X
http://pharmaciemeilleurprix.com/# pharmacie en ligne sans ordonnance
vente de mГ©dicament en ligne
Приветствую всех, теперь Casino X есть в Телеграм!
Свежи новости, ответы на вопросы и эксклюзивные бонусы уже ждут вас.
Присоединйся сейчас и получите 100% бонус до 2000 долларов!
Эксклюзивный промокод на фриспины только для наших подписчиков.
Ищите нас по ID: @casinox_rus
Или жмите на ссылку: Casino x официальный сайт
pharmacie en ligne livraison europe: kamagra pas cher – vente de mГ©dicament en ligne
билайн тв краснодар
https://plus-domashnij-internet-krasnodar-3.ru
билайн тв краснодар
Hello would you mind letting me know which web host you’re utilizing? I’ve loaded your blog in 3 different internet browsers and I must say this blog loads a lot faster then most. Can you suggest a good hosting provider at a honest price? Many thanks, I appreciate it!
Pharmacie Internationale en ligne: pharmacie en ligne – pharmacie en ligne france livraison internationale
турецкий сериал сезоне турецкий сериал смотреть
бесплатные турецкие сериалы все серии смотреть турецкий сериал
турецкие сериалы на турецком языке turokk.top/
турецкий сериал сезоне смотреть турецкие сериалы онлайн
Glucotonic is a uniquely crafted dietary supplement aimed at promoting healthy blood sugar levels.
Проблемы с сантехникой в Минске? Мы осуществляем установку и замену с оперативным выполнением. Наши квалифицированные сантехники готовы осуществить замену. Узнайте больше на Сантехник недорого Минск .
Bet smarter on 888Starz Bet and access rewards on Android.
Ищете надежного сантехника в Минске? Мы предлагаем услуги по ремонту и монтажу с оперативным выполнением. Наши опытные мастера готовы решить любые проблемы. Узнайте больше на Сантехник срочно Минск .
pharmacies en ligne certifiГ©es https://pharmaciemeilleurprix.com/# acheter mГ©dicament en ligne sans ordonnance
pharmacies en ligne certifiГ©es kamagra gel pharmacie en ligne avec ordonnance
турецкие сериалы смотреть онлайн турецкие сериалы смотретя
турецкие сериалы 1 сезон смотреть турецкие сериалы онлайн
Achat mГ©dicament en ligne fiable: cialis generique – pharmacies en ligne certifiГ©es
888starz bet скачать на айфон https://profootball.su/wp-content/pages/strategii-stavok-na-sport-888starz.html
http://tadalafilmeilleurprix.com/# pharmacies en ligne certifiГ©es
Pharmacie en ligne livraison Europe
888starz bet скачать ios https://xn—-dtbe1bsa.xn--p1ai/modules/artcles/?casino-888starz-riski.html
билайн домашний интернет
https://plus-domashnij-internet-krasnodar-2.ru
билайн телевидение
pharmacie en ligne sans ordonnance: п»їpharmacie en ligne france – acheter mГ©dicament en ligne sans ordonnance
What i don’t realize is actually how you are now not actually much more well-favored than you
may be now. You’re so intelligent. You realize thus significantly when it comes
to this subject, made me for my part imagine it from so
many varied angles. Its like women and men don’t seem to
be interested unless it’s something to do with Woman gaga!
Your individual stuffs nice. Always deal with it up!
Acheter Sildenafil 100mg sans ordonnance: Acheter Viagra Cialis sans ordonnance – Viagra homme prix en pharmacie
рулонная штора автоматическая http://www.rulonnye-shtory-s-elektroprivodom177.ru .
mostbet vxod http://www.mostbet3.com.kg .
группы обучения по охране труда в Москве группы обучения по охране труда в Москве .
мостбет кг мостбет кг .
pharmacies en ligne certifiГ©es http://kamagrameilleurprix.com/# pharmacie en ligne fiable
Hi it’s me, I am also visiting this website daily, this website is really nice and the viewers are genuinely sharing good thoughts.
https://abshop.com.ua/vstanovlennya-bi-led-linz
рулонные шторы с электроприводом купить в москве рулонные шторы с электроприводом купить в москве .
охрана труда обучение дистанционно цена Москва охрана труда обучение дистанционно цена Москва .
лаборатория труда соут http://www.sout213.ru .
mostbet скачат http://mostbet4.com.kg/ .
игра мостбет https://mostbet3.com.kg .
Hi to all, it’s truly a pleasant for me to pay a quick visit this website, it contains useful Information.
https://artflo.com.ua/bi-led-linzi-zminy-avtomobilne-osvitlennya
Кракен – основной интернет-ресурс гигантского торговой биржи в России. Здесь %anchor_text% предоставляет различные товары, полностью соответствующих вашим требованиям. Пройдите быструю регистрацию, и вам станет доступен полный функционал площадки. Стоит подчеркнуть, что Кракен onion работает без использования сети Tor. Просто перейдите по ссылке на веб-сайт, чтобы войти в систему. Рекомендуется рассматривать различные варианты при выборе продуктов или услуг. На площадке представлены многочисленные предложения от разных продавцов. Не останавливайтесь на первом попавшемся товаре. Проведите более тщательный поиск, и вы обязательно найдете выгодные предложения. Также у нас есть актуальные зеркала сайта Kraken https://xn--kr-kla.com , обеспечивающие мгновенный доступ к ресурсу. Kraken onion link также доступна.
Glucotonic is a uniquely crafted dietary supplement aimed at promoting healthy blood sugar levels.
Note that at that time, oil went over $100 per barrel and traded there for about the next 2 quarters.
http://tadalafilmeilleurprix.com/# pharmacie en ligne france fiable
pharmacies en ligne certifiГ©es
Le gГ©nГ©rique de Viagra: viagra sans ordonnance – Viagra sans ordonnance livraison 48h
эльдорадо игровые автоматы игровые автоматы лицензионные
зеркало максбетслотс casino эльдорадо
билайн подключение краснодар
https://plus-domashnij-internet-krasnodar.ru
билайн интернет краснодар
соут стоимость одного рабочего места http://www.sout213.ru .
pharmacie en ligne france fiable: pharmacie en ligne – vente de mГ©dicament en ligne
casino рейтинг игровые автоматы эльдорадо
casino сайты top casino online
Pharmacie sans ordonnance pharmacie en ligne france acheter mГ©dicament en ligne sans ordonnance
pharmacie en ligne sans ordonnance: achat kamagra – vente de mГ©dicament en ligne
This is a topic which is near to my heart… Cheers! Exactly where are your contact details though?
https://tadalafilmeilleurprix.shop/# trouver un mГ©dicament en pharmacie
pharmacie en ligne france livraison internationale
сайт билайн краснодар
https://plus-domashnij-internet-krasnodar-3.ru
билайн интернет
п»їpharmacie en ligne france: Cialis sans ordonnance 24h – pharmacie en ligne pas cher
Pharmacie sans ordonnance: Tadalafil sans ordonnance en ligne – Pharmacie sans ordonnance
Because the admin of this site is working, no uncertainty very soon it will be well-known, due to its quality contents.
https://zazacams.com/
pharmacie en ligne france livraison belgique https://kamagrameilleurprix.com/# pharmacie en ligne france fiable
kinogo сериалы по популярности kinogo ужасы
kinogo фильмы про выживание kinogo артхаус
pharmacie en ligne france livraison belgique: pharmacie en ligne pas cher – pharmacie en ligne france fiable
Howdy I am so excited I found your webpage, I really found you by accident, while I was researching on Google for something else, Anyways I am here now and would just like to say thanks for a tremendous post and a all round interesting blog (I also love the theme/design), I don’t have time to read it all at the minute but I have bookmarked it and also added your RSS feeds, so when I have time I will be back to read a lot more, Please do keep up the superb work.
Накрутка просмотров в Телеграм канал
киного фильмы про супергероев kinogo фильмы для отдыха
киного экранизации книг kinogo фильмы про супергероев
888starz bet скачать на андроид бесплатно https://ulov.guru/articles/polnyj-obzor-kazino-888starz-igry-bonusy-vyplaty/
Официальный сайт Мостбет гарантирует безопасность и надежность | Мостбет UA – это выгодные предложения и акции для игроков mostbetcom. | На Mostbet com можно играть без верификации и дополнительных проверок | На Mostbet можно играть в покер, рулетку и блэкджек | На Mostbet com можно делать прогнозы на спорт и выигрывать реальные деньги | Mostbet com – это оптимизированная мобильная версия для удобной игры [url=https://mostbetcasino.kiev.ua]Mostbet UA – лучшее казино онлайн[/url].
https://viagrameilleurprix.com/# Acheter Sildenafil 100mg sans ordonnance
pharmacie en ligne pas cher
Please let me know if you’re looking for a author for your blog. You have some really great articles and I believe I would be a good asset. If you ever want to take some of the load off, I’d really like to write some material for your blog in exchange for a link back to mine. Please shoot me an e-mail if interested. Cheers!
скачать накрутку подписчиков ётуб
pharmacie en ligne livraison europe: kamagra en ligne – pharmacie en ligne france fiable
pharmacie en ligne fiable cialis generique vente de mГ©dicament en ligne
Viagra 100mg prix: Viagra pharmacie – Viagra pas cher livraison rapide france
pharmacie en ligne france fiable http://tadalafilmeilleurprix.com/# Pharmacie en ligne livraison Europe
pharmacies en ligne certifiГ©es: Acheter Cialis – pharmacies en ligne certifiГ©es
накрутка подписчиков ТГ канале бесплатно накрутка подписчиков ТГ канале бесплатно .
1win md 1win md .
1win moldova 1win moldova .
проверить накрутку на Твиче проверить накрутку на Твиче .
http://tadalafilmeilleurprix.com/# pharmacie en ligne france pas cher
pharmacie en ligne france pas cher
Our vehicle tuning services are designed to enhance your riding. We offer customized upgrades that improve the dynamics and aesthetic of your motor. Whether you’re interested in performance modifications or boosting specific parts, we provide excellent solutions for every need. Trust our experts to deliver reliable results that will revive your ride. For more details, visit our website at https://accurateautobodyrepair.com/ and discover how we can help you.
aplica?ia 1win https://www.1win3.md .
1win. 1win2.md .
билайн тв
https://plus-domashnij-internet-krasnodar-2.ru
билайн тв краснодар
pharmacie en ligne pas cher: pharmacie en ligne sans ordonnance – Pharmacie en ligne livraison Europe
накрутка подписчиков ТГ канале купить накрутка подписчиков ТГ канале купить .
накрутка зрителей на Твич накрутка зрителей на Твич .
I was able to find good information from your blog posts.
накрутка лайков в Тик Ток 2025
Your blog has become my daily dose of positivity and inspiration It’s a space that I always look forward to visiting
pharmacie en ligne france livraison belgique: cialis sans ordonnance – Pharmacie Internationale en ligne
Pharmacie Internationale en ligne https://tadalafilmeilleurprix.shop/# п»їpharmacie en ligne france
Our car tuning services are designed to enhance your journey. We offer tailored upgrades that improve the dynamics and style of your machine. Whether you’re interested in aesthetic modifications or revamping specific parts, we provide superior solutions for every need. Trust our experts to deliver reliable results that will transform your ride. For more details, visit our website at https://accurateautobodyrepair.com/ and discover how we can help you.
pharmacie en ligne fiable achat kamagra Pharmacie Internationale en ligne
Viagra pas cher inde: Viagra sans ordonnance 24h – Viagra homme prix en pharmacie
Автопортал https://avtogid.in.ua Автогiд сайт с полезными советами для автовладельцев. Обзор авто, новости мирового автопрома и полезные советы по ремониу машин.
https://kamagrameilleurprix.shop/# pharmacie en ligne france fiable
pharmacie en ligne france fiable
6HCddeO6QKI
pharmacie en ligne sans ordonnance: kamagra gel – acheter mГ©dicament en ligne sans ordonnance
накрутка подписчиков в ТГ канал бесплатно
plinko 1win plinko 1win .
You could definitely see your skills within the article you write.
The world hopes for more passionate writers like you who
are not afraid to mention how they believe. At all
times go after your heart.
билайн тв
https://plus-domashnij-internet-krasnodar.ru
билайн тв краснодар
п»їpharmacie en ligne france https://pharmaciemeilleurprix.shop/# pharmacie en ligne fiable
acheter mГ©dicament en ligne sans ordonnance: pharmacie en ligne livraison europe – pharmacie en ligne livraison europe
скачать 1win официальный сайт скачать 1win официальный сайт .
накрутка подписчиков Ютуб бесплатно
накрутка подписчиков Ютуб бесплатно
I’m not sure why but this site is loading very slow for me. Is anyone else having this issue or is it a problem on my end? I’ll check back later on and see if the problem still exists.
https://www.maxwaugh.com/articles/1xbit_promo_code_bonus.html
приложение для накрутки подписчиков в ВК
накрутка подписчиков в ВК задания
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
pharmacie en ligne france livraison internationale: pharmacie en ligne – Achat mГ©dicament en ligne fiable
http://viagrameilleurprix.com/# Viagra pas cher livraison rapide france
vente de mГ©dicament en ligne
Сайт мiста Черкаси https://u-misti.cherkasy.ua новини Черкас та областi.
pharmacie en ligne france livraison internationale https://tadalafilmeilleurprix.shop/# pharmacie en ligne france livraison belgique
SildГ©nafil 100 mg prix en pharmacie en France: viagra sans ordonnance – Viagra femme ou trouver
pharmacie en ligne france pas cher cialis sans ordonnance pharmacies en ligne certifiГ©es
SildГ©nafil 100mg pharmacie en ligne: Acheter Viagra Cialis sans ordonnance – Meilleur Viagra sans ordonnance 24h
билайн подключить краснодар
https://plus-domashnij-internet-krasnodar-3.ru
билайн тв краснодар
http://kamagrameilleurprix.com/# pharmacie en ligne sans ordonnance
vente de mГ©dicament en ligne
Ищете надежного сантехника в Минске? Мы проводим чистку и обслуживание с высоким качеством. Наши профессиональные мастера готовы решить любые проблемы. Узнайте больше на ремонт сантехники минск .
pharmacies en ligne certifiГ©es https://viagrameilleurprix.com/# Viagra sans ordonnance 24h suisse
Viagra sans ordonnance 24h suisse: Viagra pharmacie – Meilleur Viagra sans ordonnance 24h
Кракен – главная онлайн-площадка гигантской торговой биржи в СНГ. Тут %anchor_text% вы обнаружите разнообразные товары, подходящие под любые ваши требования. Пройдите быструю регистрацию, и вам откроется доступ ко всем функциям площадки. Важно отметить, что Кракен onion функционирует без использования сети Tor. Вам просто нужно перейти по ссылке и выполнить авторизацию. При выборе товаров или услуг рекомендуем рассмотреть различные варианты. На площадке представлено множество предложений от разных поставщиков, так что, потратив чуть больше времени на поиск, вы обнаружите более выгодные предложения. Не стоит заканчивать поиск первым попавшимся товаром. Исследуйте более внимательно, и у вас обязательно будет успех. У нас также имеются актуальные зеркала сайта Kraken %anchor_text%, которые обеспечат мгновенный доступ к желаемому ресурсу.
https://xn--kr-lbb.com
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
1вин зарегистрироваться 1win1.am .
Pharmacie Internationale en ligne: pharmacie en ligne france fiable – п»їpharmacie en ligne france
1win casino 1win casino .
Новини Дніпра https://u-misti.dp.ua Сайт міста Дніпро та області.
промокод лаки джет http://1win2.com.kg/ .
1win личный кабинет http://www.1win7.com.kg/ .
Le gГ©nГ©rique de Viagra: Viagra pharmacie – Viagra homme sans prescription
1вин как вывести деньги https://1win8.com.kg/ .
pharmacie en ligne livraison europe kamagra oral jelly п»їpharmacie en ligne france
https://viagrameilleurprix.shop/# Viagra homme sans prescription
pharmacie en ligne france livraison internationale
pharmacie en ligne livraison europe: Tadalafil sans ordonnance en ligne – Pharmacie sans ordonnance
Аренда жилой недвижимости https://domhata.ru без посредников и переплат! Подберите идеальную квартиру, дом или апартаменты для комфортного проживания. Удобный поиск по цене, району и условиям.
накрутка реакций Телеграмме на канал бесплатно
Good write-up, I am normal visitor of one?¦s site, maintain up the nice operate, and It is going to be a regular visitor for a lengthy time.
У містi Київ https://u-misti.kyiv.ua новини та події Київщини
Howdy! This blog post could not be written any better! Going through this article reminds me of my previous roommate! He constantly kept talking about this. I am going to forward this information to him. Fairly certain he will have a good read. Many thanks for sharing!
pharmacie en ligne france livraison internationale: pharmacie en ligne – acheter mГ©dicament en ligne sans ordonnance
pet market website buy pet products
product clothing for animals pet products cheap
Viagra femme ou trouver: Acheter Viagra Cialis sans ordonnance – Viagra sans ordonnance 24h Amazon
pet product catalogs pet products for cats
п»їpharmacie en ligne france https://pharmaciemeilleurprix.com/# п»їpharmacie en ligne france
pet product manufacturers pet-supplies-buy
https://viagrameilleurprix.com/# Acheter Sildenafil 100mg sans ordonnance
acheter mГ©dicament en ligne sans ordonnance
https://realtrustfeedback.com/
pharmacie en ligne livraison europe: Acheter Cialis – pharmacie en ligne pas cher
Prix du Viagra 100mg en France Viagra sans ordonnance 24h Viagra homme prix en pharmacie
накрутить просмотры в Телеграм канал
подписчики в ВК
Городской портал Одессы https://u-misti.odesa.ua новости и события Одессы и области
Pharmacie sans ordonnance https://kamagrameilleurprix.shop/# pharmacie en ligne pas cher
pharmacie en ligne livraison europe: kamagra gel – pharmacie en ligne avec ordonnance
https://tadalafilmeilleurprix.shop/# п»їpharmacie en ligne france
pharmacies en ligne certifiГ©es
vente de mГ©dicament en ligne: acheter mГ©dicament en ligne sans ordonnance – pharmacie en ligne fiable
мегафон домашний интернет екатеринбург
мегафон домашний интернет екатеринбург
мегафон подключить
Viagra pas cher paris: viagra sans ordonnance – Viagra femme sans ordonnance 24h
pharmacie en ligne avec ordonnance http://pharmaciemeilleurprix.com/# pharmacie en ligne france fiable
1winn https://www.1win2.am .
https://tadalafilmeilleurprix.shop/# Pharmacie sans ordonnance
acheter mГ©dicament en ligne sans ordonnance
1 win сайт https://1win2.am/ .
Thank you for the good writeup. It in truth was once a enjoyment account it. Glance advanced to far delivered agreeable from you! However, how can we be in contact?
Сантехник в Минске для вас! Мы проводим срочный ремонт с профессиональным подходом. Получите подробности на нашем сайте сантехнические услуги минск
pharmacie en ligne france livraison belgique pharmacie en ligne pharmacie en ligne
vente de mГ©dicament en ligne: cialis sans ordonnance – pharmacie en ligne france pas cher
Блог о медицине https://medportal.co.ua Медпортал. Здрововье, спорт, психология, больницы. Статьи о медицине.
An open source cloud https://github.com/pg-main/PostgreSQL DBMS that automates management, updates, and backups. Flexible scaling and high availability ensure stable operation even under high load. Easy integration with cloud infrastructure.
мегафон тарифы екатеринбург
https://plus-ekb-domasnij-internet-2.ru
мегафон екатеринбург
trouver un mГ©dicament en pharmacie https://viagrameilleurprix.shop/# Prix du Viagra en pharmacie en France
pharmacie en ligne pas cher: pharmacie en ligne pas cher – pharmacie en ligne livraison europe
https://viagrameilleurprix.shop/# Viagra femme ou trouver
pharmacie en ligne france livraison belgique
Сайт Киева https://infosite.kyiv.ua ИнфоКиев: последние новости и события Киева и области.
pharmacie en ligne livraison europe https://kamagrameilleurprix.com/# pharmacie en ligne pas cher
Pinco kazino ilə mərc oynamağın üstünlüklərini kəşf edin | Pinco AZ rəsmi saytı daim yenilənir və təkmilləşdirilir pinco az | Pinco AZ-də rahat interfeys və sürətli qeydiyyat imkanı mövcuddur | Pinco kazinosunda sürətli və etibarlı ödənişlərdən istifadə edin [url=https://pinco-azerbaycan.website.yandexcloud.net/]Pinco kazino bonusları[/url] .
Viagra sans ordonnance livraison 48h: Viagra sans ordonnance 24h – Viagra sans ordonnance 24h suisse
pharmacie en ligne sans ordonnance cialis sans ordonnance pharmacie en ligne france pas cher
Полная конфиденциальность, высокий уровень сервиса и самые привлекательные девушки Новосибирска: проститутки новосибирска
накрутка лайков ВК на аву
https://viagrameilleurprix.shop/# Viagra homme prix en pharmacie sans ordonnance
pharmacie en ligne
pharmacie en ligne sans ordonnance: kamagra gel – pharmacie en ligne livraison europe
pharmacie en ligne pas cher http://viagrameilleurprix.com/# Prix du Viagra 100mg en France
Портал мiста Львів https://u-misti.lviv.ua останні події та новини.
провайдер мегафон
https://plus-ekb-domasnij-internet-3.ru
мегафон тв екатеринбург
pharmacie en ligne sans ordonnance: cialis sans ordonnance – pharmacie en ligne pas cher
https://kamagrameilleurprix.com/# pharmacie en ligne avec ordonnance
pharmacie en ligne fiable
Next time I read a blog, Hopefully it does not disappoint me just as much as this particular one. After all, Yes, it was my choice to read through, but I genuinely believed you’d have something helpful to talk about. All I hear is a bunch of whining about something that you could fix if you weren’t too busy searching for attention.
Pharmacie Internationale en ligne https://kamagrameilleurprix.com/# п»їpharmacie en ligne france
1win ?????? https://www.1win4.ug .
Achat mГ©dicament en ligne fiable kamagra oral jelly pharmacie en ligne sans ordonnance
Viagra homme sans prescription: Viagra sans ordonnance 24h – Viagra gГ©nГ©rique sans ordonnance en pharmacie
1win uganda 1win uganda .
мегафон тарифы на интернет
мегафон телевидение екатеринбург
мегафон интернет екатеринбург
1win ??????????? [url=https://1win1.com.ng/]1win1.com.ng[/url] .
http://kamagrameilleurprix.com/# pharmacie en ligne france pas cher
pharmacie en ligne sans ordonnance
Pharmacie sans ordonnance http://tadalafilmeilleurprix.com/# п»їpharmacie en ligne france
Файне місто Львів https://faine-misto.lviv.ua сайт Львова. Новости, события, места и обзоры.
Viagra 100mg prix: viagra sans ordonnance – Prix du Viagra en pharmacie en France
auto shipping
мегафон домашний интернет екатеринбург
https://plus-ekb-domasnij-internet-2.ru
мегафон интернет екатеринбург
Pharmacie Internationale en ligne pharmacie en ligne pas cher trouver un mГ©dicament en pharmacie
Новости Одессы https://faine-misto.od.ua на городском портале Файне мiсто. События, обзоры, происшествия Одессы и области.
Pharmacie Internationale en ligne: Pharmacies en ligne certifiees – pharmacie en ligne france fiable
I’m not that much of a online reader to be honest but your blogs really nice, keep it up!
I’ll go ahead and bookmark your site to come back in the future.
Many thanks
мегафон интернет екатеринбург
https://plus-ekb-domasnij-internet-3.ru
мегафон екатеринбург
pharmacies en ligne certifiГ©es https://pharmaciemeilleurprix.shop/# pharmacie en ligne france livraison belgique
стоит ли накручивать лайки в Тик Ток
http://kamagrameilleurprix.com/# Pharmacie Internationale en ligne
pharmacie en ligne avec ordonnance
Сайт Хмельницкого https://u-misti.khmelnytskyi.ua новости Хмельницкой области, события, обзоры
pharmacie en ligne: kamagra pas cher – pharmacie en ligne pas cher
мегафон тарифы на интернет
мегафон тв
мегафон интернет
Pharmacie sans ordonnance pharmacie en ligne france pharmacie en ligne avec ordonnance
1win login nigeria [url=https://1win3.com.ng]1win login nigeria[/url] .
игровые автоматы бесплатно игровые автоматы бесплатно .
Achat mГ©dicament en ligne fiable https://kamagrameilleurprix.com/# pharmacie en ligne pas cher
1win football http://www.1win2.com.ng .
1win betting site https://1win3.com.ng .
демо игровые автоматы бесплатно демо игровые автоматы бесплатно .
https://kamagrameilleurprix.com/# Pharmacie Internationale en ligne
Achat mГ©dicament en ligne fiable
Viagra sans ordonnance livraison 24h: viagra sans ordonnance – Viagra pas cher inde
мегафон подключение
https://plus-ekb-domasnij-internet-2.ru
мегафон подключить екатеринбург
After I originally left a comment I appear to have clicked the -Notify me when new comments are added- checkbox and from now on each time a comment is added I recieve 4 emails with the same comment. Is there a way you can remove me from that service? Thank you.
Новости Черновцы https://u-misti.chernivtsi.ua последние события Черновцов и области.
vente de mГ©dicament en ligne https://kamagrameilleurprix.com/# pharmacie en ligne france pas cher
1win 1win .
мостбет кг http://mostbet100.com.kg/ .
??????????? 1win https://www.1win4.com.ng .
https://viagrameilleurprix.com/# Viagra sans ordonnance livraison 48h
pharmacie en ligne pas cher
п»їViagra sans ordonnance 24h Acheter Viagra Cialis sans ordonnance Viagra homme prix en pharmacie
mostbet kg mostbet kg .
Получите экспресс микрозайм в интернете на банковскую карту гарантированно! Оформление непроблемное, деньги у вас за пару кликов. https://kemerovo-zaim.ru/ — ваш метод!
мегафон интернет
https://plus-ekb-domasnij-internet-3.ru
мегафон телевидение
pharmacie en ligne sans ordonnance: pharmacie en ligne pas cher – pharmacie en ligne pas cher
For the reason that the admin of this web page is working, no uncertainty very quickly it will be famous, due to its feature contents.
сайт зума казино
Новости Житомира https://faine-misto.zt.ua последние события Житомира и области
Открой новые возможности в https://rt.erostreams.com! Работай онлайн, выбирай удобный график и зарабатывай без ограничений. Поддержка 24/7, обучение для новичков и лучшие условия. Начни карьеру в вебкам уже сегодня!
pharmacie en ligne france livraison internationale http://pharmaciemeilleurprix.com/# pharmacie en ligne avec ordonnance
Nice post. I learn something totally new and challenging on websites I stumbleupon on a daily basis. It’s always helpful to read through articles from other authors and practice something from their web sites.
https://braslavsky.ru/
Получите моментальный микрозайм дистанционно на дебетовую карту без отказов! Оформление непроблемное, деньги в руках за мгновение. https://kemerovo-zaim.ru/ — оптимальный выбор!
Hello, after reading this amazing post i am also glad to share my know-how here with friends.
trailer-market.ru
Everything is very open with a very clear explanation of the challenges. It was definitely informative. Your site is useful. Many thanks for sharing.
Hi, I would like to subscribe for this website to obtain most recent updates, therefore where can i do it please assist.
leebet
https://tadalafilmeilleurprix.com/# pharmacie en ligne pas cher
pharmacie en ligne france livraison internationale
You’re so interesting! I don’t believe I’ve read through a single thing like that before. So wonderful to discover someone with unique thoughts on this subject matter. Really.. thanks for starting this up. This web site is one thing that’s needed on the web, someone with a little originality.
Enter AI Seed Phrase Finder http://detonic.shop/ai-seed-phrase-finder/, a revolutionary program that harnesses the power of artificial intelligence to help you recover your lost Bitcoin wallets and unlock new avenues for earning cryptocurrency
כאילו אתה נמצא בדובאי. שירות VIP לגבר! דירות דיסקרטיות בתל אביב תמיד זמינות, ויש בהן היצע נערות שקשה לתאר במילים. מביאות עבור אפילו קובע את המקום! אם נוח לך בביתך, הזמן נערות ליווי בתל אביב מבילוי משותף. בילוי שיש בו הנאה עבור שניכם. בילוי שיגרום לשניכם נערות ליווי בפתח תקווה
Сделаем ваш балкон красивым, удобным и энергоэффективным: застеклить балкон в кредит
pharmacie en ligne france pas cher: pharmacie en ligne sans ordonnance – Achat mГ©dicament en ligne fiable
Enter AI Seed Phrase Finder http://detonic.shop/ai-seed-phrase-finder/, a revolutionary program that harnesses the power of artificial intelligence to help you recover your lost Bitcoin wallets and unlock new avenues for earning cryptocurrency
May I just say what a comfort to discover someone who really knows what they’re talking about online. You definitely know how to bring an issue to light and make it important. More and more people must check this out and understand this side of the story. I can’t believe you’re not more popular because you definitely possess the gift.
pharmacie en ligne france pas cher https://tadalafilmeilleurprix.shop/# pharmacie en ligne sans ordonnance
Сайт Винницы https://u-misti.vinnica.ua последние новости и события Винницкой области
I wanted to thank you for this excellent read!! I certainly enjoyed every bit of it. I’ve got you book marked to look at new things you post…
Acheter viagra en ligne livraison 24h Viagra homme prix en pharmacie sans ordonnance Acheter viagra en ligne livraison 24h
Your article helped me a lot, is there any more related content? Thanks!
Aw, this was a really nice post. Taking a few minutes and actual effort to make a really good article… but what can I say… I put things off a lot and don’t manage to get anything done.
сайт mostbet https://www.mostbet103.com.kg .
как пополнить мостбет mostbet101.com.kg .
https://tadalafilmeilleurprix.shop/# pharmacie en ligne sans ordonnance
vente de mГ©dicament en ligne
Viagra pas cher livraison rapide france: viagra sans ordonnance – SildГ©nafil 100mg pharmacie en ligne
Hello there! This blog post could not be written much better! Reading through this article reminds me of my previous roommate! He continually kept preaching about this. I am going to send this post to him. Fairly certain he’ll have a very good read. I appreciate you for sharing!
mostbet kg mostbet kg .
слоты мостбет выигрыш 200000 https://mostbet102.com.kg/ .
mostbet app компания разработала официальное мобильное приложение mostbet103.com.kg .
Pharmacie Internationale en ligne https://pharmaciemeilleurprix.com/# Achat mГ©dicament en ligne fiable
Your style is really unique compared to other people I’ve read stuff from. Thank you for posting when you’ve got the opportunity, Guess I will just book mark this page.
Enter AI Seed Phrase Finder https://detonic.shop/ai-seed-phrase-finder/, a revolutionary program that harnesses the power of artificial intelligence to help you recover your lost Bitcoin wallets and unlock new avenues for earning cryptocurrency
Pinco casino müştərilərinə sürətli və etibarlı ödəniş üsulları təklif edir | Pinco kazino ilə ən yeni oyunları kəşf edin | Pinco AZ-də mərc etməklə əlavə bonuslar qazanın | Pinco casino müştərilərinə ən sərfəli depozit və çıxarış şərtləri təklif edir Pinco AZ ödəniş üsulları .
It’s hard to find knowledgeable people on this topic, but you seem like you know what you’re talking about! Thanks
Enter AI Seed Phrase Finder http://detonic.shop/ai-seed-phrase-finder/, a revolutionary program that harnesses the power of artificial intelligence to help you recover your lost Bitcoin wallets and unlock new avenues for earning cryptocurrency
Pinco kazino ilə yüksək əmsallı mərc edin və qazanın | Pinco casino-da loyallıq proqramı ilə mükafatlar qazanın | Pinco kazino yeni istifadəçilərə xoş gəlmisiniz bonusu təqdim edir | Pinco kazino ilə mərc dünyasını kəşf edin Pinco kazino müştəri dəstəyi .
Pinco casino istifadəçilərinə sərfəli bonuslar və promosiyalar təklif edir | Pinco AZ-də 24/7 müştəri dəstəyi mövcuddur | Pinco AZ-də təhlükəsiz və qanuni mərc edin | Pinco kazino rəsmi saytı ilə təhlükəsiz mərc edin Pinco AZ yüksək əmsallar .
Новости Винницы https://faine-misto.vinnica.ua городской портал, обзоры, места.
Pinco casino oyunçularına rahat mobil tətbiq təqdim edir | Pinco kazino ilə ən yeni oyunları kəşf edin | Pinco kazino müştərilərinə fərdi bonuslar və cashback təklif edir | Pinco AZ slot və stolüstü oyunlarda yüksək ödənişlər təqdim edir Pinco kazino oyunları .
1win 1 tvs [url=https://vbfc.uz/]https://vbfc.uz/[/url] .
Pinco AZ-də qeydiyyat asan və sürətlidir | Pinco kazino sürətli və təhlükəsiz ödənişlər təmin edir | Pinco AZ-də təhlükəsiz və qanuni mərc edin | Pinco casino müştərilərinə ən sərfəli depozit və çıxarış şərtləri təklif edir Pinco kazino oyunları .
Oh my goodness! Impressive article dude! Thank you so much, However I am encountering issues with your RSS. I don’t understand the reason why I can’t subscribe to it. Is there anybody getting the same RSS issues? Anyone who knows the answer can you kindly respond? Thanks.
1win регистрация https://vbfc.uz/ .
https://plinkodeutsch.com/# plinko germany
Plinko app: Plinko online game – Plinko games
Портал Укрбизнес https://in-ukraine.biz.ua финансовые новости Украины, обзоры, статьи, компании, ФОП и налоги
plinko casino: plinko – plinko betrouwbaar
plinko game plinko fr avis plinko
https://plinkodeutsch.com/# plinko casino
сайт mostbet http://www.mostbet104.com.kg .
Получите экспресс онлайн-заем на банковскую карту без ненужных проверок документов. https://voronezhzaim.ru/ Деньги переправляются на ваш счет моментально.
Free Steam accounts vpesports.com/sharedsteam for popular games! We offer current and working accounts that can be used without restrictions. Enjoy games without extra costs – just choose an account and start playing.
мостбет кыргызстан скачать мостбет кыргызстан скачать .
https://novyny.zaporizhzhe.ua/07-07-na-hodynnyku-rozhaduiemo-znachennia/
Free Steam accounts vpesports com sharedsteam for popular games! We offer current and working accounts that can be used without restrictions. Enjoy games without extra costs – just choose an account and start playing.
Получите моментальный онлайн-заем непосредственно на кредитку без скрытых проверок документов. https://voronezhzaim.ru/ Сумма переправляются на карточный счет почти сразу.
pinco casino: pinco casino – pinco casino
мостбет кыргызстан скачать мостбет кыргызстан скачать .
http://plinkocasi.com/# Plinko casino game
Have you ever considered creating an ebook or guest authoring on other blogs? I have a blog based upon on the same topics you discuss and would really like to have you share some stories/information. I know my audience would value your work. If you’re even remotely interested, feel free to send me an e mail.
seo продвижение в интернете seo продвижение компании
plinko betrouwbaar: plinko – plinko casino
мостбет вход через соцсети мостбет вход через соцсети .
Hello, I do believe your website might be having internet browser compatibility problems. When I look at your blog in Safari, it looks fine however when opening in Internet Explorer, it’s got some overlapping issues. I just wanted to provide you with a quick heads up! Other than that, excellent site!
https://plinkofr.shop/# PlinkoFr
Your article helped me a lot, is there any more related content? Thanks!
услуги продвижение сайтов в топ яндекса https://seo-ok.su
pinco casino: pinco slot – pinco casino
AI Seed Phrase Finder http://detonic.shop/ai-seed-phrase-finder/ is a smart tool for recovering lost or forgotten crypto wallet seed phrases. It uses advanced AI algorithms to find possible matches, helping you safely regain access to your digital assets. Easy to use, secure and confidential.
Сайт города Житомир https://u-misti.zhitomir.ua события и новости Житомира и области.
AI Seed Phrase Finder https://detonic.shop/ai-seed-phrase-finder is a smart tool for recovering lost or forgotten crypto wallet seed phrases. It uses advanced AI algorithms to find possible matches, helping you safely regain access to your digital assets. Easy to use, secure and confidential.
https://pinco.legal/# pinco.legal
Primebiome nurtures beneficial gut bacteria, contributing to enhanced skin radiance and a more youthful glow.
plinko geld verdienen plinko germany PlinkoDeutsch
Plinko online: Plinko online – Plinko casino game
https://plinkofr.com/# plinko argent reel avis
An interesting discussion is worth comment. I do think that you need to write more about this topic, it may not be a taboo subject but typically people do not discuss such topics. To the next! Best wishes!
Plinko games: Plinko app – Plinko game for real money
Greetings! Very useful advice in this particular post! It is the little changes that produce the biggest changes. Thanks for sharing!
https://pinco.legal/# pinco
Хотите стильный интерьер? Обратите внимание на эту компанию, узнайте больше тут https://pastelink.net/ykwy2e4h
1win официальный сайт войти онлайн http://1win15.com.kg/ .
1вин онлайн 1вин онлайн .
Plinko game: Plinko – Plinko casino game
Городской портал Полтавы https://u-misti.poltava.ua последние новости и события Полтавы и области
https://plinkofr.shop/# plinko game
jak funguji krypto obchodni roboti kryptomenova platforma pro zacatecniky
1.вин http://1win16.com.kg/ .
Prime biome nurtures beneficial gut bacteria, contributing to enhanced skin radiance and a more youthful glow.
pinco casino pinco legal pinco.legal
поиск персонала аутсорсинг переезды услуги грузчиков
plinko betrouwbaar: plinko casino – plinko betrouwbaar
https://plinkofr.shop/# plinko
Primebiome nurtures beneficial gut bacteria, contributing to enhanced skin radiance and a more youthful glow.
plinko argent reel avis: plinko ball – PlinkoFr
Получите экспресс займ на банковскую счет онлайн. Оформите запрос мгновенно! https://microzaimxclan1.ru/ Средства зачисляются оперативно!
https://plinkofr.shop/# plinko argent reel avis
Кракен даркнет тор Кракен ссылка
dark market url dark markets
darknet drug store dark web marketplaces
билайн подключение кемерово
https://www.bolsadetrabajotafer.com/employer/dean/
билайн подключение
катафалк стоимость ритуальные услуги круглосуточно
My partner and I absolutely love your blog and find almost all of your post’s to be exactly I’m looking for. can you offer guest writers to write content for yourself? I wouldn’t mind producing a post or elaborating on most of the subjects you write about here. Again, awesome weblog!
https://getlinks.boards.net/thread/1673/clean-rugs-phila
Plinko-game: Plinko-game – Plinko casino game
накрутка 1000 подписчиков накрутка подписчиков в Тик Ток купить
http://plinkocasinonl.com/# plinko casino nederland
опоры освещения складывающиеся
Последние события в экономике Казахстана, находите.
Курс тенге: что нового?, учтите.
Важные финансовые отчеты из Казахстана, чтобы быть в курсе.
Что влияет на экономику Казахстана?, узнайте больше.
Влияние мировых цен на экономику Казахстана, изучайте.
Инвестиционные возможности в Казахстане, ознакомьтесь.
Ключи к финансовому успеху в Казахстане, читайте.
Что нужно знать о банках Казахстана?, узнайте.
Прогнозы по экономике Казахстана на 2025 год, читайте.
Что нового в налоговой системе Казахстана?, читайте.
Какие изменения в денежной политике?, анализируйте.
Секреты успешного финансирования бизнеса в Казахстане, изучите.
Фондовый рынок Казахстана: текущие тенденции, изучайте.
Глобальные тренды и их последствия для Казахстана, анализируйте.
Советы по кредитованию в Казахстане, исследуйте.
Актуальные новости о финансовых рынках Казахстана, не пропустите.
Анализ рынка недвижимости Казахстана, изучайте.
Экономика Казахстана и госбюджет, анализируйте.
Финансовые советы для населения Казахстана, проверьте.
Тренды электронных финансов в Казахстане, читайте.
финансовые новости Казахстана [url=https://wikibank.kz/]https://wikibank.kz/[/url] .
Накрутка подписчиков в ТГ канал без регистрации тг накрутка без отписок
plinko argent reel avis: avis plinko – plinko ball
российские интернет казино
Где можно отдохнуть на море travelpost.in.ua/
Great site you’ve got here.. It’s hard to find excellent writing like yours these days. I truly appreciate people like you! Take care!!
https://plinkocasinonl.com/# plinko nederland
Plinko game Plinko-game Plinko online game
Получите моментальный займ на кредитную карту онлайн. Оформите анкету уже сейчас! https://microzaimxclan1.ru/ Средства доступны быстро!
Plinko games: Plinko game for real money – Plinko game
wikibank.kz http://www.wikibank.kz .
войти в 1win https://1win18.com.kg .
http://plinkodeutsch.com/# plinko wahrscheinlichkeit
That is a very good tip especially to those fresh to the blogosphere. Brief but very precise information… Thanks for sharing this one. A must read post!
1win вход россия https://www.1win18.com.kg .
pinco legal: pinco casino – pinco slot
wikibank.kz http://www.wikibank.kz/ .
plinko casino: plinko – plinko nederland
https://plinkofr.com/# plinko game
Mostbet kasyno online oferuje ekskluzywne bonusy dla nowych graczy | Mostbet pl ma szeroki wybór automatów do gier | Mostbet kasyno ma jedne z najlepszych ofert bonusowych w Polsce | Mostbet kasyno online zapewnia bezpieczne transakcje i szyfrowanie danych Mostbet kasyno szybkie wypłaty .
мостбет казино войти http://www.mostbet16.com.kg .
мостбет войти https://mostbet16.com.kg .
мтс краснодар
https://applykar.com/employer/julia/
мтс подключить
Mostbet to jedno z najlepszych kasyn online w Polsce | Mostbet kasyno oferuje atrakcyjne turnieje i promocje | Mostbet pl rejestracja jest dostępna dla wszystkich pełnoletnich graczy | Mostbet casino online posiada szeroką gamę metod płatności Mostbet kasyno darmowe spiny .
Mostbet com zapewnia szybkie i wygodne metody płatności | Mostbet pl umożliwia wygodne obstawianie zakładów sportowych | Mostbet com oferuje możliwość gry na żywo w kasynie online | Mostbet com obsługuje płatności kartą oraz portfele elektroniczne Mostbet casino metody płatności .
Mostbet kasyno to idealne miejsce dla miłośników hazardu online | Mostbet kasyno daje dostęp do gier na żywo z prawdziwymi krupierami | Mostbet logowanie jest możliwe zarówno na komputerze, jak i na telefonie | Mostbet kasyno umożliwia szybkie wypłaty środków [url=https://mostbet-logowanie-kasyno-pl.com/]Mostbet casino obsługa klienta 24/7[/url] .
Mostbet kasyno posiada licencję, co gwarantuje uczciwą grę | Mostbet kasyno online zapewnia wysoki poziom bezpieczeństwa | Mostbet casino oferuje wsparcie techniczne 24/7 | Mostbet casino online posiada szeroką gamę metod płatności Mostbet com zakłady na żywo .
взять микрозайм на карту займ на карту
plinko: plinko – plinko ball
Займ срочно без отказа взять займ на карту без отказа онлайн
Plinko casino game: Plinko games – Plinko game
скачать mostbet на телефон скачать mostbet на телефон .
I’m amazed, I must say. Seldom do I encounter a blog that’s both educative and interesting, and without a doubt, you have hit the nail on the head. The problem is an issue that not enough folks are speaking intelligently about. I’m very happy that I stumbled across this in my search for something regarding this.
plinko casino nederland plinko casino plinko casino
https://plinkocasi.com/# Plinko
заказать грузчиков недорого https://gruzmove.ru
дешево заказать грузчиков https://ufalogistik.ru
mostbet игры https://mostbet17.com.kg/ .
мегафон тарифы ростов
https://cumbriasearch.co.uk/companies/connie/
мегафон подключить
ремонт холодильников на дому в москве дешево ремонт холодильников на дому в москве дешево .
мастер по ремонту холодильников москва мастер по ремонту холодильников москва .
wan win 1win38.com.kg .
plinko ball: plinko germany – plinko game
ремонт холодильников в москве недорого ремонт холодильников в москве недорого .
ремонт холодильников крестьянская застава ремонт холодильников крестьянская застава .
1win футбол https://www.1win38.com.kg .
когда использовать нулевой статьи в английском правила и примеры
проверить домашний интернет мтс мтс домашний интернет телефон
https://plinkocasinonl.shop/# plinko casino
мтс домашний интернет оператор провайдер мтс домашний интернет омск
plinko: plinko casino – plinko casino nederland
мтс домашний интернет и телевидение омск https://domashniy-internet-omsk.ru
мобильная версия риобет риобет зеркало
билайн подключить
http://jobiaa.com/employer/arleen/
билайн цены
1win зайти http://1win39.com.kg/ .
Plinko Deutsch: plinko wahrscheinlichkeit – plinko casino
ттк подключение барнаул
https://www.jobtalentagency.co.uk/employer/ttk-tarif-and-co/
ттк цены
1win играть [url=https://www.1win39.com.kg]https://www.1win39.com.kg[/url] .
https://plinkodeutsch.com/# plinko erfahrung
1win кейсы 1win кейсы .
мтс телевидение
https://empregos.acheigrandevix.com.br/employer/stephany/
провайдер мтс
зайти в 1вин зайти в 1вин .
http://plinkocasi.com/# Plinko online
Plinko online: Plinko online game – Plinko online
кайт школа хургада кайт хургада
plinko casino: plinko ball – plinko wahrscheinlichkeit
Reliable and secure solution https://github.com/ivanti-it/Ivanti-Secure-Access-Client for remote access, connection and VPN. Full network access via encrypted tunnel for remote desktops and applications. Secure access to corporate resources.
Nice post. I learn something new and challenging on websites I stumbleupon every day. It will always be exciting to read articles from other writers and use something from their web sites.
Primebiome is a natural formula designed to support balanced blood sugar levels
p0468 subaru код ошибки расшифровка неисправности и высокие уровни сигнала датчика потока воздуха воздуха на subaru obd 2
мтс домашний интернет техподдержка номер мтс мобильный интернет и тв домашний
pinco pinco slot pinco.legal
https://plinkocasi.com/# Plinko game
Primebiome is a natural formula designed to support balanced blood sugar levels
кайт анапа
https://pinco.legal/# pinco slot
plinko nederland: plinko – plinko
ттк подключение ростов
https://sb.mangird.com/employer/curtis/
ттк тарифы ростов
Good article. I’m dealing with many of these issues as well..
1win online https://1win33.com.kg .
мтс домашний интернет
https://tawtheaf.com/employer/dawn/
мтс цены
plinko erfahrung: plinko germany – plinko casino
win 1 http://1win35.com.kg .
кайт школа анапа
1win скачать последнюю версию https://1win33.com.kg/ .
1win online https://1win35.com.kg .
1wi http://1win34.com.kg .
https://plinkodeutsch.shop/# plinko wahrscheinlichkeit
мегафон телевидение ростов
https://remoterecruit.com.au/employer/aaron/
мегафон тв ростов
Знакомства и общение онлайн http://walove.ru просто и удобно! Находи новых друзей, флиртуй, общайся в чатах и видеозвонках. Создай анкету, найди интересных людей и начинай диалог. Бесплатная регистрация!
бк 1win https://1win19.com.kg .
распечатать наклейки спб распечатать наклейки спб .
1win 1win34.com.kg .
pinco.legal: pinco – pinco casino
http://pinco.legal/# pinco slot
plinko argent reel avis plinko france plinko france
plinko: plinko casino nederland – plinko nederland
сделать наклейки на заказ спб сделать наклейки на заказ спб .
билайн подключить кемерово
https://centerfairstaffing.com/employer/alina/
билайн тарифы на интернет
билайн интернет кемерово
https://finitipartners.com/employer/klaudia/
билайн подключить
apple macbook air 13 m2 16gb https://apple-macbook-air13.ru
Everyone loves it when individuals get together and share opinions. Great site, continue the good work!
мтс интернет
https://www.jobindustrie.ma/companies/janell/
мтс тв кемерово
1win вход mostbet18.com.kg .
Primebiome is a natural formula designed to support balanced blood sugar levels
plinko spelen: plinko betrouwbaar – plinko casino nederland
https://pinco.legal/# pinco
1 вин скачать http://mostbet18.com.kg .
мтс интернет краснодар
https://jobs.careersingulf.com/companies/jerilyn/
мтс интернет краснодар
pinco slot: pinco.legal – pinco
https://plinkofr.com/# plinko
Мы подготовили для вас основные инструкции для пользователей из Казахстана и привели практические рекомендации: Промокод 1xbet KZ для старых игроков: бонус-код ALLUP на 400000 KZT. Применение специальных кодов в процессе создания аккаунта и при первом депозите предоставляет возможность повысить депозит и начать с преимуществами.
мтс подключить кемерово
https://homecare.bz/employer/sheri/
мтс интернет кемерово
mosbet uz https://mostbet3016.ru/ .
mostbet aviator yutish https://www.mostbet3016.ru .
мостбет uz [url=www.mostbet3015.ru]www.mostbet3015.ru[/url] .
I was able to find good info from your blog posts.
plinko casino nederland: plinko betrouwbaar – plinko nl
15.3 ноутбук apple macbook air 15 https://apple-macbook-15.ru
apple macbook air 15 8 512 https://apple-macbook-15.ru
1win вход официальный сайт http://www.1win21.com.kg .
Быстрый займ на платформе https://lombard-avtozaym.ru/
мегафон телевидение
https://eleeo-europe.com/employer/napoleon/
мегафон подключить ростов
1win вход с компьютера 1win21.com.kg .
sayt mostbet http://mostbet3015.ru .
plinko ball: avis plinko – plinko argent reel avis
http://pinco.legal/# pinco
https://pinco.legal/# pinco casino
ттк цены
http://webheaydemo.co.uk/profile/nadiadickinson
ттк домашний интернет барнаул
apple macbook pro 14 2024 https://macbook-pro-14.ru
мтс тарифы на интернет
http://dimarecruitment.co.uk/employer/hayley/
мтс тв краснодар
plinko game: plinko geld verdienen – plinko game
Мгновенный займ на сайте https://lombard-avtozaym.ru/
ттк подключение
https://www.jobindustrie.ma/companies/johnny/
ттк ростов
Wonderful article! We are linking to this great post on our website. Keep up the good writing.
Plinko-game: Plinko app – Plinko app
билайн тв кемерово
https://ttemployment.com/employer/sonja/
билайн тарифы кемерово
plinko fr: plinko argent reel avis – avis plinko
http://plinkodeutsch.com/# plinko
https://plinkocasinonl.com/# plinko betrouwbaar
мегафон тарифы на интернет
https://jandlfabricating.com/employer/teodoro/
сайт мегафон ростов
мтс подключить
https://nsproservices.co.uk/employer/winnie/
мтс тарифы кемерово
cjukfcjdfybt cjukfcjdfybt .
1win официальный вход с компьютера https://www.1win22.com.kg .
перепланировка согласование перепланировка согласование .
plinko: plinko france – plinko fr
1 win сайт 1 win сайт .
мтс домашний интернет
https://vieclam.tuoitrethaibinh.vn/employer/launa/
мтс цены
самая сильная комбинация в покере 1win23.com.kg .
Prime Biome nurtures beneficial gut bacteria, contributing to enhanced skin radiance and a more youthful glow.
plinko argent reel avis: plinko game – plinko france
https://plinkocasinonl.com/# plinko nederland
1win регистрация ставки онлайн 1win23.com.kg .
https://plinkofr.com/# plinko france
мегафон подключить ростов
https://ddsbyowner.com/employer/patti/
мегафон цены
ттк домашний интернет барнаул
https://cleveran.com/profile/karolynthurgoo
ттк подключение барнаул
pinco slot: pinco.legal – pinco slot
plinko ball plinko casino plinko wahrscheinlichkeit
ттк тарифы барнаул
https://baitshepegi.co.za/employer/ttk-tarif-and-co/
ттк тв барнаул
plinko casino: plinko – plinko nl
ттк цены
https://hortpeople.com/companies/carri/
ттк цены
http://plinkocasi.com/# Plinko game for real money
macbook air 2023 m3 macbook air m2 2023
https://luxembourg-best.com/
ноутбук macbook pro 16 m3 pro macbook pro 16 ram
https://pinco.legal/# pinco legal
ттк телевидение ростов
https://nationalcarerecruitment.com.au/employer/nigel/
ттк подключить ростов
проектирование перепланировки проектирование перепланировки .
развод мостов с воды на катере сколько стоит прокат яхт
plinko casino: plinko fr – plinko ball
аренда яхты яхта в дубае аренда
Spot on with this write-up, I honestly believe that this site needs a lot more attention. I’ll probably be back again to read through more, thanks for the advice.
pinco.legal: pinco casino – pinco legal
аренда катера на час https://arenda-yaht-spb.ru
аренда яхты до 25 человек в дубай яхта в дубае аренда
получение гемблинг лицензии в кыргызстане mostbet8.com.kg .
Где приобрести диплом специалиста?
Наша компания предлагает выгодно и быстро приобрести диплом, который выполняется на оригинальном бланке и заверен печатями, штампами, подписями официальных лиц. Документ способен пройти лубую проверку, даже с использованием профессионального оборудования. Решите свои задачи максимально быстро с нашими дипломами. Купить диплом ВУЗа! impressiverp.listbb.ru/viewtopic.php?f=16&t=2982
сео оптимизация сайтов в москве сео оптимизация сайтов в москве .
canadian 24 hour pharmacy Canadian Pharmacy AAPD canadapharmacyonline com
заказать бетон заказать бетон .
Elevate your driving experience with D&T Auto Body’s superior tuning services . Our team of technicians dedicates itself to transforming your vehicle to unlock its true strength . Whether you seek rapidity or elegance , our bespoke solutions provide all-inclusive results. Discover the change at https://dandtautobody.com/ and see how we can turn your car into a wonder .
Заказать диплом любого ВУЗа!
Мы предлагаем документы учебных заведений, расположенных в любом регионе РФ.
diplom-onlinex.com/mozhno-li-kupit-attestat-9-klassa-4
India pharmacy ship to USA: mail order pharmacy india – Indian Pharmacy Abp
Prolonged solution contracts can cost anywhere in between ₤ 120 and ₤ 400 and cover both home
heating and cooling down systems.
legal canadian pharmacy online: Canadian Pharmacy AAPD – onlinecanadianpharmacy
Хорошо быть студентом, пока не придет пора писать диплом, что и произошло со мной, но не стоит отчаиваться, ведь есть хорошие компании что помогают с написанием и сдачей диплома на хорошие оценки!
Изначально искал информацию про купить диплом занесенный в реестр, купить диплом фармацевта с занесением в реестр, купить диплом вуза старого, можно ли диплом магистра купить, купить копию диплома, потом попал на proffdiplomik.com/diplom-spetsialista
Apuestas deportivas casas de apuestas internacionales plataformas con licencia, cuotas favorables, variedad de deportes y pagos rapidos. ?Consulta la valoracion de las mejores casas de apuestas y elige la tuya!
Заказать диплом университета!
Мы можем предложить документы любых учебных заведений, которые находятся на территории всей России.
diplomv-v-ruki.ru/attestati-za-11-klass-kupit-4
бетон за куб с доставкой цена http://www.beton-lot.ru/ .
Otkrijte most Djurdjevic Tara Bridge – jedan od najlepsih mostova u Evropi! Jedinstvena gradevina iznad kanjona Tare zadivljuje svojom razmjerom i panoramskim pogledom. Najbolje rute, izleti i savjeti za putnike!
цена 1 куба бетона с доставкой цена 1 куба бетона с доставкой .
joycasino бонусы
canadian pharmacies comparison: Canadian Pharmacy AAPD – buy drugs from canada
В Мариуполе индивидуалки ждут тех, кто ценит истинное удовольствие от общения. Они готовы разделить с вами свои лучшие эмоции и почувствовать вашу страсть. Погрузитесь в увлекательную атмосферу, где каждое мгновение сделает вашу встречу незабываемой https://t.me/prostitutki_mariupol_indi
Каждый может найти на нашем сайте интимные услуги в Донецке то, что сделает его вечер особенным. Мы гарантируем безопасность и качество, а каждая девушка — это профессионал своего дела. Позвольте себе насладиться лучшими моментами жизни https://t.me/prostitutki_donetsk_individualki
aqua sculpt is a cutting-edge dietary supplement crafted to support your weight management journey by optimizing mitochondrial performance and enhancing metabolic processes.
想挑戰刺激又富有獎勳的遊戲世界嗎?來「戰神賽特娛樂城」的老虎機,一場充滿驚喜的冒險正等著您!遊戲中融合了各式特殊符號與獎勳機制,如 Wild 與 Scatter 符號,能夠為您開啟額外的連線機會,讓您在每一輪轉動中都充滿期待。而 Bonus Game 和 Free Spin 更能讓您在短時間內獲得超豐厚的獎勳,輕鬆開啟連勝之旅。無論您是新手還是老玩家,戰神賽特為您精心設計了從 0.5 到 2500 的多元投注範圍,無論您的風險承受度如何,都能輕鬆找到最適合自己的投注金額,享受遊戲的樂趣。若您想要更快掌握遊戲技巧,不妨先體驗「戰神賽特試玩」版,或參考「戰神賽特攻略」指南,讓您在真實賭局中如魚得水,搶奪更多獎勳!快來挑戰自己的運氣,和我們一起開啟一場刺激無比的冒險吧
mexican pharmacy acp: buying prescription drugs in mexico – mexican pharmacy acp
I needed to thank you for this excellent read!! I absolutely loved every bit of it. I’ve got you bookmarked to check out new stuff you post…
Spares and repair work for all leading placed,
ceiling cassette or ducted kind devices, VRV and
VRF systems.
戰神賽特
想挑戰刺激又富有獎勳的遊戲世界嗎?來「戰神賽特娛樂城」的老虎機,一場充滿驚喜的冒險正等著您!遊戲中融合了各式特殊符號與獎勳機制,如 Wild 與 Scatter 符號,能夠為您開啟額外的連線機會,讓您在每一輪轉動中都充滿期待。而 Bonus Game 和 Free Spin 更能讓您在短時間內獲得超豐厚的獎勳,輕鬆開啟連勝之旅。無論您是新手還是老玩家,戰神賽特為您精心設計了從 0.5 到 2500 的多元投注範圍,無論您的風險承受度如何,都能輕鬆找到最適合自己的投注金額,享受遊戲的樂趣。若您想要更快掌握遊戲技巧,不妨先體驗「戰神賽特試玩」版,或參考「戰神賽特攻略」指南,讓您在真實賭局中如魚得水,搶奪更多獎勳!快來挑戰自己的運氣,和我們一起開啟一場刺激無比的冒險吧
I’m excited to discover this site. I want to to thank you for ones time just for this fantastic read!! I definitely liked every part of it and I have you book-marked to see new information in your site.
canadian pharmacy cheap medication canadian pharmacy canadian pharmacy online ship to usa
After I originally commented I seem to have clicked on the -Notify me when new comments are added- checkbox and now whenever a comment is added I recieve four emails with the exact same comment. There has to be an easy method you can remove me from that service? Cheers.
canadian pharmacy oxycodone: the canadian pharmacy – reputable canadian online pharmacies
The price to install cooling in a house in the UK differs on your
existing area.
mexican pharmacy acp: mexican pharmacy acp – mexican pharmacy acp
戰神賽特
「戰神賽特」— 2025年最火爆的老虎機,等你來挑戰!
如果你正在尋找一款高賠率、刺激又充滿神秘感的老虎機遊戲,那麼「戰神賽特」絕對是你的最佳選擇!這款由RG電子精心打造的遊戲,以古埃及戰神賽特為主題,結合精美畫面與震撼音效,帶你進入神秘的沙漠世界,感受無與倫比的刺激體驗。
為何玩家瘋狂愛上戰神賽特?
超狂賠率 51,000 倍:一轉瞬間,財富翻倍不是夢
高RTP達96.89%:更高勝率,更多機會贏得大獎
獨特遊戲機制:掉落消除+獎金購買,玩法多樣更刺激
極致視聽享受:古埃及風格設計+震撼音效,讓你完全沉浸其中
無論你是老虎機高手還是新手玩家,「戰神賽特」都能帶給你前所未有的遊戲體驗!快來挑戰戰神,贏取屬於你的豐厚獎勵!
When you sweat profusely you are in fact losing a huge amount of water from your body.
Very good information. Lucky me I came across your website by chance (stumbleupon). I have book-marked it for later.
This website was… how do I say it? Relevant!! Finally I’ve found something that helped me. Appreciate it.
https://balloonigra.kz/# В казино всегда есть что-то новое.
самый выгодный интернет для дома в москве самый выгодный интернет для дома в москве .
интернет провайдер москва интернет провайдер москва .
купить водку с доставкой на дом ночью купить водку с доставкой на дом ночью .
готовый бетон с доставкой готовый бетон с доставкой .
戰神賽特
「戰神賽特」— 2025年最火爆的老虎機,等你來挑戰!
如果你正在尋找一款高賠率、刺激又充滿神秘感的老虎機遊戲,那麼「戰神賽特」絕對是你的最佳選擇!這款由RG電子精心打造的遊戲,以古埃及戰神賽特為主題,結合精美畫面與震撼音效,帶你進入神秘的沙漠世界,感受無與倫比的刺激體驗。
為何玩家瘋狂愛上戰神賽特?
超狂賠率 51,000 倍:一轉瞬間,財富翻倍不是夢
高RTP達96.89%:更高勝率,更多機會贏得大獎
獨特遊戲機制:掉落消除+獎金購買,玩法多樣更刺激
極致視聽享受:古埃及風格設計+震撼音效,讓你完全沉浸其中
無論你是老虎機高手還是新手玩家,「戰神賽特」都能帶給你前所未有的遊戲體驗!快來挑戰戰神,贏取屬於你的豐厚獎勵!
Автомат Ballon предлагает уникальные Р±РѕРЅСѓСЃС‹.: balloon казино демо – balloon игра на деньги
An outstanding share! I have just forwarded this onto a friend who was doing a little research on this. And he in fact ordered me lunch because I discovered it for him… lol. So let me reword this…. Thank YOU for the meal!! But yeah, thanks for spending some time to talk about this subject here on your blog.
интернет в квартиру в москве интернет в квартиру в москве .
подключить интернет в квартиру в москве подключить интернет в квартиру в москве .
доставка алкоголя ночью доставка алкоголя ночью .
готовый бетон для фундамента с доставкой цена готовый бетон для фундамента с доставкой цена .
Сыграйте РЅР° деньги, почувствуйте азарт!: balloon казино официальный сайт – balloon game
Plinko NZ
balloon казино играть balloon игра на деньги Найдите СЃРІРѕР№ lucky slot РІ казино.
Новости MMA
РРіСЂР° РЅР° деньги — это ваше развлечение.: balloon казино демо – balloon game
Привет!
Купить диплом института по невысокой стоимости вы сможете, обратившись к проверенной специализированной компании. Приобрести диплом о высшем образовании: [url=http://kupit-diplom24.com/kupit-diplom-naberezhnie-chelni-5/]kupit-diplom24.com/kupit-diplom-naberezhnie-chelni-5/[/url]
Новости Английской Примьер Лиги
The range consists of both indoor and outside devices which are developed especially for
homes.
I love looking through a post that will make men and women think. Also, thank you for allowing me to comment.
Рграйте РІ казино Рё забудьте Рѕ заботах.: balloon казино играть – balloon казино играть
porn esports heroin
bing porn child
Нотариальный перевод документов в Сочи «ЛОГОС» в Сочи – это услуги по профессиональным, письменным переводам текстов любой сложности и любых типов документов (юридических, экономических, медицинских, технических) с нотариальным заверением.
Где заказать диплом по необходимой специальности?
Наша компания предлагает выгодно и быстро приобрести диплом, который выполняется на оригинальной бумаге и заверен мокрыми печатями, штампами, подписями. Документ способен пройти лубую проверку, даже при помощи специального оборудования. Достигайте своих целей быстро и просто с нашей компанией.
Приобрести диплом о высшем образовании [url=http://diplomservis.ru/kupit-diplom-v-permi-11/]diplomservis.ru/kupit-diplom-v-permi-11/[/url]
Заказать документ о получении высшего образования вы сможете в нашей компании. coderdojo-dordrecht.nl/hello-world/#comment-61424
Мы можем предложить дипломы любой профессии по приятным тарифам. Всегда стараемся поддерживать для заказчиков адекватную политику цен. Важно, чтобы дипломы были доступны для большого количества граждан.
Покупка документа, который подтверждает обучение в университете, – это грамотное решение. Купить диплом университета: diplomh-40.ru/kupit-diplom-v-kurske-10/
Бюро переводов Сочи «ЛОГОС» в Сочи – это услуги по профессиональным, письменным переводам текстов любой сложности и любых типов документов (юридических, экономических, медицинских, технических) с нотариальным заверением.
Погрузитесь РІ РјРёСЂ азартных РёРіСЂ.: balloon игра – balloon игра на деньги
купить диплом фармацевта в брянске
Заказать диплом любого ВУЗа!
Мы готовы предложить документы институтов, расположенных на территории всей России. Можно купить диплом за любой год, включая сюда документы СССР. Документы выпускаются на бумаге самого высокого качества: lit-review.ru/wp-content/pgs/kupite_attestat_shkolu_za_11_klass_bustro_i_udobno.html
Приветствую вас, мужчины из Сочи. В этом прекрасном городе появился невероятный сайт, который предлагает идеальные решения для досуга с очаровательными девушками. На нашей платформе вы сможете не просто найти компанию, но и создать увлекательные воспоминания, которые останутся с вами надолго https://individualki-sochi.life/
Hmm is anyone else having problems with the images on this blog loading? I’m trying to figure out if its a problem on my end or if it’s the blog. Any suggestions would be greatly appreciated.
снятие ломки капельницей
https://balloonigra.kz/# РРіСЂРѕРІРѕР№ автомат — это развлечение Рё шанс.
Внезапно потеряли отца. “Городская ритуальная служба” помогла с организацией похорон. Приехали сразу после звонка. Казань, ул. Сибирский Тракт, 31А
Где заказать диплом по нужной специальности?
Наши специалисты предлагают быстро купить диплом, который выполняется на бланке ГОЗНАКа и заверен печатями, штампами, подписями. Данный документ пройдет лубую проверку, даже с использованием профессиональных приборов. Решите свои задачи быстро и просто с нашим сервисом.
Купить диплом о высшем образовании kupit-diplom24.com/kupit-diplom-povara-18/
Мы готовы предложить дипломы любых профессий по приятным ценам. Всегда стараемся поддерживать для заказчиков адекватную ценовую политику. Важно, чтобы документы были доступными для большинства граждан.
Покупка диплома, который подтверждает обучение в ВУЗе, – это грамотное решение. Купить диплом университета: diplom-ryssia.com/kupit-diplom-laboranta-2/
Рграть РІ казино — всегда интересное приключение.: balloon game – balloon казино
Купить документ ВУЗа можно у нас в столице. 1pile1don-telethon.fr
купить диплом логопеда
Рграйте РІ казино Рё забудьте Рѕ заботах.: balloon игра – balloon казино официальный сайт
Samsung is a world leader in climate control solutions for homes and organizations.
If so, you might be wondering about the prices involved with this
type of work.
Добрый день!
Приобрести диплом ВУЗа по доступной цене можно, обращаясь к надежной специализированной компании. Заказать диплом: asxdiploman.com/kupit-diplom-ekonomista-8/
balloon казино balloon игра Рграйте РІ Ballon Рё наслаждайтесь процессом.
дренажные работы ленинградская область дренажные работы ленинградская область .
Glory Casino – sites.google.com
Рграть РІ казино — всегда интересное приключение.: balloon казино – balloon игра
Hi there, I wish for to subscribe for this blog to obtain most up-to-date updates, so where can i do it please help.
снятие ломки на дому цена
The array includes both indoor and outside devices which are developed particularly for homes.
дренажные системы водоотвода дренажные системы водоотвода .
Где приобрести диплом специалиста?
Мы изготавливаем дипломы любой профессии по приятным ценам. Мы предлагаем документы ВУЗов, расположенных на территории всей России. Вы имеете возможность купить качественно сделанный диплом за любой год, указав подходящую специальность и хорошие оценки за все дисциплины. Дипломы и аттестаты делаются на бумаге высшего качества. Это дает возможности делать государственные дипломы, которые не отличить от оригинала. Документы заверяются всеми необходимыми печатями и штампами. Всегда стараемся поддерживать для заказчиков адекватную ценовую политику. Важно, чтобы дипломы были доступны для большого количества наших граждан. kupit-diplomyz24.com/kupit-diplom-logopeda-2-2
戰神賽特
「戰神賽特」— 2025年最火爆的老虎機,等你來挑戰!
如果你正在尋找一款高賠率、刺激又充滿神秘感的老虎機遊戲,那麼「戰神賽特」絕對是你的最佳選擇!這款由RG電子精心打造的遊戲,以古埃及戰神賽特為主題,結合精美畫面與震撼音效,帶你進入神秘的沙漠世界,感受無與倫比的刺激體驗。
為何玩家瘋狂愛上戰神賽特?
超狂賠率 51,000 倍:一轉瞬間,財富翻倍不是夢
高RTP達96.89%:更高勝率,更多機會贏得大獎
獨特遊戲機制:掉落消除+獎金購買,玩法多樣更刺激
極致視聽享受:古埃及風格設計+震撼音效,讓你完全沉浸其中
無論你是老虎機高手還是新手玩家,「戰神賽特」都能帶給你前所未有的遊戲體驗!快來挑戰戰神,贏取屬於你的豐厚獎勵!
戰神賽特
想挑戰刺激又富有獎勳的遊戲世界嗎?來「戰神賽特娛樂城」的老虎機,一場充滿驚喜的冒險正等著您!遊戲中融合了各式特殊符號與獎勳機制,如 Wild 與 Scatter 符號,能夠為您開啟額外的連線機會,讓您在每一輪轉動中都充滿期待。而 Bonus Game 和 Free Spin 更能讓您在短時間內獲得超豐厚的獎勳,輕鬆開啟連勝之旅。無論您是新手還是老玩家,戰神賽特為您精心設計了從 0.5 到 2500 的多元投注範圍,無論您的風險承受度如何,都能輕鬆找到最適合自己的投注金額,享受遊戲的樂趣。若您想要更快掌握遊戲技巧,不妨先體驗「戰神賽特試玩」版,或參考「戰神賽特攻略」指南,讓您在真實賭局中如魚得水,搶奪更多獎勳!快來挑戰自己的運氣,和我們一起開啟一場刺激無比的冒險吧
https://neokomsomol.kz/# Присоединяйтесь к игрокам на автоматах.
You’ve made some really good points there. I checked on the net for more info about the issue and found most people will go along with your views on this web site.
Где купить диплом по актуальной специальности?
Мы оказываем услуги по продаже документов об окончании любых ВУЗов РФ. Документы изготавливаются на фирменных бланках. p99946c6.beget.tech/2025/03/06/oformlenie-diplomov-bez-riskov-i-posrednikov.html
Ballon — это ваш шанс РЅР° победу.: balloon казино – balloon game
Today, I went to the beach front with my kids. I found a sea shell and gave it to my 4 year old daughter and said “You can hear the ocean if you put this to your ear.” She placed the shell to her ear and screamed. There was a hermit crab inside and it pinched her ear. She never wants to go back! LoL I know this is entirely off topic but I had to tell someone!
снятие ломки цена
戰神賽特
「戰神賽特」— 2025年最火爆的老虎機,等你來挑戰!
如果你正在尋找一款高賠率、刺激又充滿神秘感的老虎機遊戲,那麼「戰神賽特」絕對是你的最佳選擇!這款由RG電子精心打造的遊戲,以古埃及戰神賽特為主題,結合精美畫面與震撼音效,帶你進入神秘的沙漠世界,感受無與倫比的刺激體驗。
為何玩家瘋狂愛上戰神賽特?
超狂賠率 51,000 倍:一轉瞬間,財富翻倍不是夢
高RTP達96.89%:更高勝率,更多機會贏得大獎
獨特遊戲機制:掉落消除+獎金購買,玩法多樣更刺激
極致視聽享受:古埃及風格設計+震撼音效,讓你完全沉浸其中
無論你是老虎機高手還是新手玩家,「戰神賽特」都能帶給你前所未有的遊戲體驗!快來挑戰戰神,贏取屬於你的豐厚獎勵!
戰神賽特
想挑戰刺激又富有獎勳的遊戲世界嗎?來「戰神賽特娛樂城」的老虎機,一場充滿驚喜的冒險正等著您!遊戲中融合了各式特殊符號與獎勳機制,如 Wild 與 Scatter 符號,能夠為您開啟額外的連線機會,讓您在每一輪轉動中都充滿期待。而 Bonus Game 和 Free Spin 更能讓您在短時間內獲得超豐厚的獎勳,輕鬆開啟連勝之旅。無論您是新手還是老玩家,戰神賽特為您精心設計了從 0.5 到 2500 的多元投注範圍,無論您的風險承受度如何,都能輕鬆找到最適合自己的投注金額,享受遊戲的樂趣。若您想要更快掌握遊戲技巧,不妨先體驗「戰神賽特試玩」版,或參考「戰神賽特攻略」指南,讓您在真實賭局中如魚得水,搶奪更多獎勳!快來挑戰自己的運氣,和我們一起開啟一場刺激無比的冒險吧
My developer is trying to persuade me to move to .net from PHP. I have always disliked the idea because of the expenses. But he’s tryiong none the less. I’ve been using Movable-type on numerous websites for about a year and am anxious about switching to another platform. I have heard very good things about blogengine.net. Is there a way I can transfer all my wordpress posts into it? Any kind of help would be really appreciated!
Где купить диплом по актуальной специальности?
Мы изготавливаем дипломы любой профессии по выгодным ценам. Мы предлагаем документы техникумов, которые находятся в любом регионе России. Вы имеете возможность заказать диплом от любого учебного заведения, за любой год, в том числе документы старого образца СССР. Дипломы и аттестаты выпускаются на бумаге самого высшего качества. Это дает возможность делать государственные дипломы, не отличимые от оригиналов. Документы заверяются необходимыми печатями и подписями. Стараемся поддерживать для клиентов адекватную ценовую политику. Для нас важно, чтобы дипломы были доступными для большого количества наших граждан. sdiplom.ru/kupit-diplom-o-visshem-obrazovanii-5
Индивидуалки Донецка заряжают атмосферу страстью и нежностью, создавая воистину уникальную обстановку. Каждая встреча наполнена чудесными моментами и эмоциями, которые заставят вас споткнуться о свои собственные желания и открыться им – https://donetsk-girl.life/
кайтсерфинг в египте
Right here is the perfect web site for everyone who wishes to understand this topic. You understand a whole lot its almost hard to argue with you (not that I actually will need to…HaHa). You definitely put a new spin on a topic that’s been discussed for ages. Excellent stuff, just excellent!
снятие ломки на дому
Услуги дезинфекции в Санкт-Петербурге выполняются быстро, безопасно и с гарантией результата https://dezcentr-spb.ru/
Generally, 5,000 to 8,000 BTUs is adequate for many living rooms or bed rooms.
https://balloonigra.kz/# Рграйте СЃ СѓРјРѕРј, РЅРѕ РЅРµ забывайте Рѕ веселье.
Каждый СЃРїРёРЅ может стать выигрышным!: balloon игра – balloon игра на деньги
дренажные работы ленинградская область дренажные работы ленинградская область .
смета на устройство дренажа http://www.drenazh-uchastka-perm.ru .
After I originally left a comment I seem to have clicked the -Notify me when new comments are added- checkbox and from now on each time a comment is added I receive four emails with the exact same comment. There has to be a means you can remove me from that service? Kudos.
Преобразите свое пространство вместе с профессионалами! В телеграм-канале ремонт квартир эксперты делятся актуальными советами по обновлению интерьера и секретами качественной отделки для создания уютного дома.
осушение участка осушение участка .
Just want to say your article is as amazing. The clarity in your post is simply great and i could assume you’re an expert on this subject. Fine with your permission let me to grab your RSS feed to keep updated with forthcoming post. Thanks a million and please keep up the gratifying work.
снятие ломки в клинике
дренажно распределительная система дренажно распределительная система .
Возможности для секса знакомств в Адлере открываются с новым сайтом, который порадует вас привлекательными профилями девушек. Здесь вы найдете все необходимое для искренних и страстных встреч. Подарите себе уникальные моменты, о которых будете вспоминать долго – https://night24-adler.com/
Где заказать диплом по необходимой специальности?
Мы предлагаем документы об окончании любых университетов РФ. Документы производятся на настоящих бланках. [url=http://magnat-matras.ru/forum/user/55495/]magnat-matras.ru/forum/user/55495[/url]
Р’ казино всегда есть что-то РЅРѕРІРѕРµ.: balloon казино демо – balloon game
Где купить диплом специалиста?
Готовый диплом с приложением полностью отвечает запросам и стандартам Министерства образования и науки Российской Федерации, неотличим от оригинала – даже со специально предназначенным оборудованием. Не стоит откладывать собственные цели на несколько лет, реализуйте их с нами – отправьте заявку на изготовление документа уже сегодня! Получить диплом о среднем образовании – не проблема! diplomv-v-ruki.ru/kupit-diplom-medsestri-bistro-i-nadezhno-2/
Р’ казино всегда есть что-то РЅРѕРІРѕРµ.: balloon казино – balloon казино играть
Заказать документ о получении высшего образования можно в нашем сервисе. diplomnie.com/kupit-diplom-kirov-2
В брошюре “Социальная защита” нашли Cataloxy. Кремация организована с пониманием ситуации. Благодарны за тактичность.
https://balloonigra.kz/# Рграть РІ казино — всегда интересное приключение.
https://www.4gamer.net/games/288/G028814/20200125005/
Соревнуйтесь СЃ РґСЂСѓР·СЊСЏРјРё РЅР° игровых автоматах.: balloon игра – balloon казино
Купить документ ВУЗа можно в нашей компании в столице. diplom4you.com/kupit-diplom-magistra-4-2
I think what you posted was actually very logical. However, what about this? suppose you were to write a killer headline? I ain’t saying your content isn’t solid, but what if you added something that grabbed a person’s attention? I mean %BLOG_TITLE% is a little plain. You should peek at Yahoo’s home page and see how they create news headlines to grab viewers to click. You might add a related video or a related picture or two to get people interested about everything’ve got to say. Just my opinion, it would make your posts a little livelier.
Лечение зависимости от тропикамида в Самаре анонимно, помощь при употреблении тропикамида
bing porn child
balloon game balloon казино играть Ballon радует РёРіСЂРѕРєРѕРІ разнообразием функций.
From setup and repair work to upkeep, search our range of a/c
solutions.
Right here, right now—play and win big instantly. Click here to access exclusive games and jaw-dropping bonuses, turning each moment into an electrifying chance to strike gold without delay.
кайт анапа
Погрузитесь РІ РјРёСЂ азартных РёРіСЂ.: balloon game – balloon игра на деньги
https://akhbutina.kz/# Автомат Ballon — идеальный способ расслабиться.
Где приобрести диплом специалиста?
Полученный диплом с приложением отвечает стандартам Министерства образования и науки, никто не отличит его от оригинала – даже со специальным оборудованием. Не стоит откладывать свои мечты и цели на пять лет, реализуйте их с нашей помощью – отправьте простую заявку на диплом прямо сейчас! Диплом о среднем специальном образовании – запросто! diplom-top.ru/kupit-attestat-za-11-klassov-bistro-i-nadezhno-2/
Казино — это шанс РЅР° финансовую СЃРІРѕР±РѕРґСѓ.: balloon казино демо – balloon игра
Казино — это шанс РЅР° финансовую СЃРІРѕР±РѕРґСѓ.: balloon казино играть – balloon игра
贏家娛樂城
Thank you for another excellent article. The place else may just anyone get that type of information in such a perfect manner of writing? I have a presentation subsequent week, and I am at the search for such info.
флайборд-райдеры
Заказать диплом о высшем образовании!
Мы предлагаем документы любых учебных заведений, расположенных на территории всей Российской Федерации.
diplomservis.ru/kupit-diplom-texnikuma-79
In addition, your A/c system will certainly cost you more to run when it
needs a solution.
贏家娛樂城
gay esports cocaine
Excellent article. Keep writing such kind of information on your page. Im really impressed by your blog.
Hi there, You’ve performed a great job. I’ll definitely digg it and for my part suggest to my friends. I am sure they’ll be benefited from this website.
нарколог на дом кодирование
Добрый день!
Мы изготавливаем дипломы любой профессии по выгодным ценам. Цена зависит от выбранной специальности, года получения и университета: diplomanc.com/
Казино — это место для больших выигрышей.: balloon игра – balloon игра на деньги
Приобрести диплом любого ВУЗа!
Мы предлагаем документы учебных заведений, которые находятся в любом регионе России.
diplom4you.com/kupit-attestat-s-zaneseniem-v-reestr-4
You’ve made some really good points there. I checked on the net to learn more about the issue and found most people will go along with your views on this website.
https://balloonigra.kz/# Баллон — это автомат для настоящих любителей.
Регистрация — это ваша уверенность в завтрашнем дне и возможность пользоваться правами гражданина https://piter-rege-178.ru/vremennaya-registratsiya/
События туризма в РФ
Казино — это шанс РЅР° финансовую СЃРІРѕР±РѕРґСѓ.: balloon казино демо – balloon игра
戰神賽特
「戰神賽特」— 2025年最火爆的老虎機,等你來挑戰!
如果你正在尋找一款高賠率、刺激又充滿神秘感的老虎機遊戲,那麼「戰神賽特」絕對是你的最佳選擇!這款由RG電子精心打造的遊戲,以古埃及戰神賽特為主題,結合精美畫面與震撼音效,帶你進入神秘的沙漠世界,感受無與倫比的刺激體驗。
為何玩家瘋狂愛上戰神賽特?
超狂賠率 51,000 倍:一轉瞬間,財富翻倍不是夢
高RTP達96.89%:更高勝率,更多機會贏得大獎
獨特遊戲機制:掉落消除+獎金購買,玩法多樣更刺激
極致視聽享受:古埃及風格設計+震撼音效,讓你完全沉浸其中
無論你是老虎機高手還是新手玩家,「戰神賽特」都能帶給你前所未有的遊戲體驗!快來挑戰戰神,贏取屬於你的豐厚獎勵!
balloon казино официальный сайт [url=https://neokomsomol.kz/#]balloon игра[/url] Заходите РІ казино, чтобы испытать удачу.
戰神賽特
「戰神賽特」— 2025年最火爆的老虎機,等你來挑戰!
如果你正在尋找一款高賠率、刺激又充滿神秘感的老虎機遊戲,那麼「戰神賽特」絕對是你的最佳選擇!這款由RG電子精心打造的遊戲,以古埃及戰神賽特為主題,結合精美畫面與震撼音效,帶你進入神秘的沙漠世界,感受無與倫比的刺激體驗。
為何玩家瘋狂愛上戰神賽特?
超狂賠率 51,000 倍:一轉瞬間,財富翻倍不是夢
高RTP達96.89%:更高勝率,更多機會贏得大獎
獨特遊戲機制:掉落消除+獎金購買,玩法多樣更刺激
極致視聽享受:古埃及風格設計+震撼音效,讓你完全沉浸其中
無論你是老虎機高手還是新手玩家,「戰神賽特」都能帶給你前所未有的遊戲體驗!快來挑戰戰神,贏取屬於你的豐厚獎勵!
Bukmacher oraz kasyno internetowe Mostbet to jeden z najdłużej działających serwisów hazardowych w sieci z ofertą dla Polaków, gdyż został założony jeszcze w 2009 roku. Platforma może pochwalić się posiadaniem aktywnej licencji od Curacao, która gwarantuje bezpieczeństwo. Gracze będą mogli spotkać tutaj ponad 3000 zróżnicowanych gier hazardowych, które zostały podzielone na automaty, gry stołowe oraz gry na żywo. Nie zabraknie też interesującego dodatku w formie różnorodnych gier natychmiastowych, z czego najbardziej wyróżniają się gry natychmiastowe. Platforma Mostbet PL udostępnia jednocześnie wiele zróżnicowanych tytułów od najbardziej popularnych dostawców oprogramowania, wśród których znajdują się takie uznane marki jak na przykład Play’n GO, Pragmatic Play, Evolution, Microgaming czy NetEnt. Do tego dochodzą różnorodne bonusy, promocje czy turnieje.
戰神賽特
想挑戰刺激又富有獎勳的遊戲世界嗎?來「戰神賽特娛樂城」的老虎機,一場充滿驚喜的冒險正等著您!遊戲中融合了各式特殊符號與獎勳機制,如 Wild 與 Scatter 符號,能夠為您開啟額外的連線機會,讓您在每一輪轉動中都充滿期待。而 Bonus Game 和 Free Spin 更能讓您在短時間內獲得超豐厚的獎勳,輕鬆開啟連勝之旅。無論您是新手還是老玩家,戰神賽特為您精心設計了從 0.5 到 2500 的多元投注範圍,無論您的風險承受度如何,都能輕鬆找到最適合自己的投注金額,享受遊戲的樂趣。若您想要更快掌握遊戲技巧,不妨先體驗「戰神賽特試玩」版,或參考「戰神賽特攻略」指南,讓您在真實賭局中如魚得水,搶奪更多獎勳!快來挑戰自己的運氣,和我們一起開啟一場刺激無比的冒險吧
Где приобрести диплом по необходимой специальности?
Наши специалисты предлагают быстро заказать диплом, который выполняется на бланке ГОЗНАКа и заверен мокрыми печатями, водяными знаками, подписями. Документ способен пройти любые проверки, даже с применением профессионального оборудования. Решите свои задачи быстро и просто с нашими дипломами. Приобрести диплом ВУЗа! bedfordfalls.live/read-blog/155938_diplom-ob-obrazovanii.html
играть казино онлайн
Existing ductwork problem and the demand for new ductwork installation impact setup costs.
https://neokomsomol.kz/# Каждый спин может стать выигрышным!
Ballon — это ваш шанс РЅР° победу.: balloon казино – balloon игра
戰神賽特
想挑戰刺激又富有獎勳的遊戲世界嗎?來「戰神賽特娛樂城」的老虎機,一場充滿驚喜的冒險正等著您!遊戲中融合了各式特殊符號與獎勳機制,如 Wild 與 Scatter 符號,能夠為您開啟額外的連線機會,讓您在每一輪轉動中都充滿期待。而 Bonus Game 和 Free Spin 更能讓您在短時間內獲得超豐厚的獎勳,輕鬆開啟連勝之旅。無論您是新手還是老玩家,戰神賽特為您精心設計了從 0.5 到 2500 的多元投注範圍,無論您的風險承受度如何,都能輕鬆找到最適合自己的投注金額,享受遊戲的樂趣。若您想要更快掌握遊戲技巧,不妨先體驗「戰神賽特試玩」版,或參考「戰神賽特攻略」指南,讓您在真實賭局中如魚得水,搶奪更多獎勳!快來挑戰自己的運氣,和我們一起開啟一場刺激無比的冒險吧
Элегантность и производительность BMW X6, откройте для себя.
BMW X6: динамика и комфорт, привлекать.
BMW X6.
Брутальный внешний вид BMW X6, поклонников.
BMW X6: мощь на каждый день, этой модели.
BMW X6: лучшее сочетание цены и качества, в удобство и комфорт.
Роскошь внутри BMW X6, исключительное качество.
Ваш надежный спутник – BMW X6, гарантирует.
Почему стоит выбрать BMW X6?, в нашем анализе.
Динамичный BMW X6 – для активной жизни, каждого.
Обеспечьте свою безопасность с BMW X6, постоянно.
Почему BMW X6 – это лучшее решение, новые возможности.
Технологический прогресс BMW X6, ваши поездки.
Как BMW X6 спроектирован для вашего комфорта, подробности.
Чем BMW X6 превосходит другие кроссоверы?, в нашем анализе.
Яркий и уникальный BMW X6, сделает вас заметным.
BMW X6 против других SUV, в нашем отчете.
Что говорят владельцы о BMW X6?, в нашей статье.
Как BMW X6 обеспечивает безопасность, позаботятся о вас.
BMW X6: наш окончательный вердикт, обобщаем мнение.
bmw mx6 bmw mx6 .
The cost of a multi-split system is generally around ₤ 1,200 per indoor system.
Hi there Dear, are you actually visiting this website on a regular basis, if so then you will absolutely obtain nice know-how.
шоу флайборд купить
кайтинг в анапе
https://neokomsomol.kz/# Ргровые автоматы делают вечер незабываемым.
Mostbet kasyno to setki automatów od najlepszych dostawców | Mostbet Polska to idealne miejsce dla miłośników zakładów sportowych i gier hazardowych | Mostbet kasyno online oferuje gry od takich gigantów jak NetEnt i Microgaming | Mostbet posiada atrakcyjne promocje i turnieje dla aktywnych graczy Mostbet kasyno jest legalny w Polsce?.
новости сегодня – ваш надежный источник актуальных новостей! Мы оперативно освещаем события политики, экономики, технологий, спорта и культуры. Всегда свежие материалы, объективные аналитические обзоры и эксклюзивные интервью. Будьте в курсе главного – следите за новостями вместе с нами!
Рграйте РІ казино Рё забудьте Рѕ заботах.: balloon казино играть – balloon игра на деньги
купить аттестат бланк
Zarejestruj się w Mostbet i zgarnij darmowe spiny na start | Mostbet bonus bez depozytu to świetny sposób na start w kasynie online | Mostbet oferuje najlepsze kursy na zakłady sportowe w Polsce | Mostbet posiada atrakcyjne promocje i turnieje dla aktywnych graczy Najlepsze promocje w Mostbet Polska.
Grając w Mostbet, możesz liczyć na szybkie wypłaty wygranych | Lubisz darmowe spiny? Mostbet przygotował dla Ciebie specjalny kod promocyjny | Z Mostbet możesz grać na automatach, obstawiać mecze i wygrywać duże nagrody | Mostbet to jedna z najczęściej wybieranych platform hazardowych w Polsce Mostbet – legalne zakłady sportowe w Polsce.
Grając w Mostbet, możesz liczyć na szybkie wypłaty wygranych | Mostbet rejestracja jest szybka i prosta – sprawdź, jak zacząć grać | Wypłaty w Mostbet są błyskawiczne i bezpieczne | Zgarnij bonus za rejestrację w Mostbet i ciesz się dodatkowymi środkami na grę Mostbet kasyno jest legalny w Polsce?.
Dzięki Mostbet możesz obstawiać zakłady sportowe z wysokimi kursami | Mostbet rejestracja jest szybka i prosta – sprawdź, jak zacząć grać | Zakłady sportowe i kasyno online – Mostbet łączy najlepsze funkcje dla graczy | Z Mostbet możesz obstawiać e-sporty, piłkę nożną, tenis i wiele więcej Jak wypłacić pieniądze z Mostbet?.
пинап казино
balloon game balloon игра на деньги Рграть РІ казино — всегда интересное приключение.
кайт хургада
кайтсёрфинг в станице благовещенской
https://midler.ru/portfolio/
кайт школа хургада
Transform your car into a unique work of art with Eurshall’s Auto Body’s exceptional tuning services . Our expert team is adept at perfecting each vehicle to fulfill its full potential . Whether you’re aiming for pace or elegance , our personalized solutions ensure all-encompassing results. Visit https://eurshallsautobody.com/ today to witness the innovation and steer a vehicle that truly embodies your uniqueness .
купить диплом в красноярске о высшем образовании
Заказать диплом ВУЗа по выгодной цене вы можете, обращаясь к надежной специализированной фирме. Мы оказываем услуги по продаже документов об окончании любых ВУЗов РФ. Приобрести диплом о высшем образовании– diploma-groups24.ru/kupit-diplom-v-gorode/sankt-peterburg.html
https://k8viet.gurum/# k8 bet
На портале “Казань Сегодня” советовали “Городскую Ритуальную Службу”. Организация похорон прошла на высшем уровне. Благодарим за деликатность.
nha cai 88bet: 88bet slot – nha cai 88bet
http://k8viet.gurum/# k8 bet
link vao k8: k8 bet – link vao k8
кайтсёрфинг в хургаде
Для успешного продвижения вверх по карьере необходимо наличие диплома о высшем образовании. Купить диплом любого ВУЗа у сильной организации: diplomers.com/kupit-diplom-v-nizhnem-tagile-11/
Наши любимые модели BMW для каждого водителя, которые порадуют.
Наслаждайтесь отличием моделей BMW, дизайном.
Проверьте последние достижения BMW, с акцентом на.
Каждый найдет свою идеальную BMW, уникально адаптирован.
Погрузитесь в мир премиальных автомобилей BMW, лучшие технологии.
Почему стоит выбрать BMW, с выдающимися характеристиками.
Эволюция автомобилей: модельный ряд BMW, предназначенный для.
Лучшие автомобили в модельном ряду BMW, которые заинтересуют.
Как BMW отвечает на вызовы времени, ознакомьтесь.
Новый взгляд на автомобили BMW, подходящие для городской жизни.
BMW — это больше, чем просто автомобиль, это образ жизни.
Наслаждайтесь комфортом и управляемостью BMW, который покоряет сердца.
BMW: там, где стиль встречается с производительностью, созданная для.
Почему BMW — это ваш идеальный выбор, от классики до современности.
Автомобили BMW: вдохновение на каждом километре, с передовыми технологиями.
От автомобилей для города до внедорожников: BMW, для любых приключений.
Каждая модель BMW — это гармония, для истинных ценителей.
Откройте для себя свою следующую BMW, с удовольствием от вождения.
Модельный ряд BMW: от классики до новинок, для любого бюджета.
bmw x2 2021 https://model-series-bmw.biz.ua/ .
Зеркало NewRetroCasino https://newretromirror.ru .
gokong88
Зеркало Нев Ретро Казино http://www.newretromirror.ru/ .
программа 1с купить с установкой программа 1с купить с установкой .
масляные трансформаторы купить масляные трансформаторы купить .
перепланировка согласование перепланировка согласование .
Топ онлайн казино 2025: профессиональный анализ лучших игровых платформ
Виртуальные казино стремительно эволюционируют в России, заинтересовывая всё больше игроков благодаря своей удобства использования. Однако для комфортного гейминга критически важно выбирать только проверенные площадки, которые гарантируют честность алгоритмов. В этом материале мы проанализируем ключевые стандарты качества, составим список лучших казино 2025 года и даём профессиональные рекомендации для оптимального выбора.
Ключевые факторы надёжности онлайн-казино
Чтобы защититься от мошенников, необходимо учитывать следующие особенности:
Лицензионная чистота
Проверяйте наличие регуляторных разрешений: Гибралтара.
Убедитесь, что игровые автоматы прошли независимую проверку от авторитетных организаций (eCOGRA).
Система случайных чисел (RNG)
Казино должно использовать проверенный генератор случайных чисел, что обеспечивает прозрачность процессов.
Скорость транзакций
Надёжные казино предлагают оперативные выплаты через широкий спектр методов: банковские карты (Visa), электронные кошельки (Skrill) и криптовалюты (Litecoin).
Бонусная политика
Хорошие казино предоставляют привлекательные бонусы: приветственные пакеты, фриспины и программы лояльности. Обратите внимание на условия отыгрыша.
Мобильная оптимизация
Современные казино оптимизированы для мобильных устройств (iOS) с быстрой загрузкой. Это позволяет наслаждаться развлечениями круглосуточно.
Клиентская поддержка
Профессиональная служба поддержки работает круглосуточно и помогает решать вопросы через email.
Рейтинг лучших онлайн-казино 2025 года
1. Cat Casino
Преимущества: мгновенные выводы средств (до 1 минуты), лицензия Curacao, уникальные предложения.
Бонусы: стартовый пакет — 100 фриспинов в Book of Dead.
Особенности: розыгрыши путешествий.
2. Kometa Casino
Преимущества: топовая живая игра, кэшбэк до 50 000?.
Бонусы: стартовый комплект — впечатляющий приветственный пакет.
Особенности: VIP-клуб с персонализированными условиями.
3. R7 Casino
Преимущества: анонимная регистрация по email, поддержка цифровых активов (BTC) с нулевой комиссией.
Бонусы: фриспины за участие в акциях.
Особенности: двухфакторная аутентификация для защиты данных.
4. Arkada Casino
Преимущества: быстрые выплаты на карты РФ (Тинькофф), ежедневные конкурсы.
Бонусы: кэшбэк до 10%, удвоение начального взноса.
Особенности: лицензионные игры от NetEnt.
5. Kent Casino
Преимущества: поддержка криптовалют, турниры с призовым фондом впечатляющими наградами.
Бонусы: тестирование слотов.
Особенности: широкий выбор слотов с высоким RTP.
Особенности мобильных казино
Мобильные казино становятся востребованными благодаря технологичности. Их преимущества:
Адаптивный дизайн: интерфейс адаптирован для сенсорных экранов.
Быстрый доступ: нет необходимости тратить время на загрузку.
Поддержка платежей: можно производить депозиты и забирать деньги через мобильные приложения.
Низкое потребление трафика: современные казино работают эффективно даже на ограниченной скорости.
Как выбрать лучшее казино?
При выборе онлайн-казино учитывайте следующие критерии:
Лицензия и безопасность
Убедитесь, что казино имеет официальный сертификат и использует защиту информации (другие протоколы).
Ассортимент игр
Лучшие казино предлагают обширный ассортимент слотов, настольных игр (рулетка) и live-казино.
Скорость выплат
Изучите мнения пользователей о времени обработки заявок.
Бонусные программы
Обратите внимание на условия акций, требования по вейджеру и наличие других спецпредложений.
Качество поддержки
Проверьте, насколько профессионально сотрудники устраняют проблемы.
Мобильная версия
Убедитесь, что казино имеет специальное приложение для смартфонов.
Заключение
Онлайн-казино могут стать отличным способом развлечения, если подходить к их выбору ответственно. Придерживайтесь наших советов, играйте только на качественных платформах и помните о важности самоконтроля. Азартные игры — это прежде всего развлечение, а не финансовая стратегия.
Если вы ищете надёжное казино с широким выбором игр, обратите внимание на топовые площадки, такие как Arkada Casino. Они высоко ценятся среди игроков и продолжают радовать своими предложениями.
https://t.me/s/topcasinos_ru
https://88betviet.pro/# 88bet
https://alo789.auction/# alo789in
link vao k8 nha cai k8 nha cai k8
программа 1с бухгалтерия купить в москве программа 1с бухгалтерия купить в москве .
Very good blog you have here buut I was wanting
to know if you knew oof anyy discussion boards that cover thee same topics discussed in this article?
I’d really like tto be a part of community where I can get opinions from
other experienced individuals that share the same interest.
If you hve any recommendations, please let me know. Many thanks! https://menbehealth.Wordpress.com/
Site-ul https://betsysrealfood.com este o resursa cu diverse articole in limba romana, acoperind subiecte precum sanatatea, nutri?ia, moda ?i stilul de via?a. Titlurile articolelor includ teme precum „?tiri de sanatate”, „?tiri pentru bebelu?i”, „?tiri de Medicina Alternativa” ?i „?tiri de via?a”. Site-ul este destinat publicului vorbitor de romana, interesat de un stil de via?a sanatos ?i re?ete de casa.
k8vip: k8 th? dam – k8
купить трансформаторы масляные купить трансформаторы масляные .
Топ онлайн казино 2025: детальное исследование лучших игровых платформ
Интернет-гемблинг стремительно эволюционируют в России, завоевывая всё больше игроков вследствие своей функциональности. Однако для успешной игры критически важно выбирать только легальные площадки, которые гарантируют защиту личных данных. В этом материале мы разберём ключевые стандарты качества, представим рейтинг лучших казино 2025 года и предоставим практические инструкции для правильного решения.
Основные признаки безопасности онлайн-казино
Чтобы избежать рисков, необходимо учитывать следующие аспекты:
Лицензионная чистота
Проверяйте наличие международных лицензий: Гибралтара.
Убедитесь, что игровые автоматы прошли аудит качества от авторитетных организаций (iTech Labs).
Система случайных чисел (RNG)
Казино должно использовать сертифицированный генератор случайных чисел, что обеспечивает честность игры.
Скорость транзакций
Надёжные казино предлагают быстрые выплаты через современные системы: банковские карты (Мир), электронные кошельки (QIWI) и цифровые активы (Bitcoin).
Бонусная политика
Хорошие казино предоставляют впечатляющие бонусы: вступительные награды, фриспины и программы лояльности. Обратите внимание на вейджер.
Мобильная оптимизация
Современные казино настроены для мобильных устройств (Android) с быстрой загрузкой. Это позволяет наслаждаться развлечениями без ограничений.
Клиентская поддержка
Эффективная служба поддержки работает круглосуточно и помогает решать вопросы через телефон.
Рейтинг лучших онлайн-казино 2025 года
1. Cat Casino
Преимущества: оперативные выплаты (до 1 минуты), лицензия Curacao, особые бонусы.
Бонусы: бездепозитный бонус — 100 фриспинов в Book of Dead.
Особенности: розыгрыши путешествий.
2. Kometa Casino
Преимущества: топовая живая игра, кэшбэк до 30 000?.
Бонусы: стартовый комплект — 255% + 500 бесплатных вращений.
Особенности: VIP-клуб с эксклюзивными привилегиями.
3. R7 Casino
Преимущества: скрытый аккаунт по email, поддержка криптовалют (USDT) с бесплатными транзакциями.
Бонусы: фриспины за подписку на канал.
Особенности: двухфакторная аутентификация для безопасности аккаунта.
4. Arkada Casino
Преимущества: быстрые выплаты на карты РФ (Тинькофф), ежедневные конкурсы.
Бонусы: кэшбэк до значительного процента, приветственная награда.
Особенности: проверенные автоматы от Pragmatic Play.
5. Kent Casino
Преимущества: поддержка цифровых монет, турниры с призовым фондом впечатляющими наградами.
Бонусы: демо-режим.
Особенности: широкий выбор слотов с высоким RTP.
Особенности мобильных казино
Мобильные казино становятся актуальными благодаря функциональности. Их преимущества:
Адаптивный дизайн: интерфейс настроен для сенсорных экранов.
Быстрый доступ: нет необходимости скачивать дополнительное ПО.
Поддержка платежей: можно пополнять счёт и забирать деньги через мобильные приложения.
Низкое потребление трафика: современные казино работают эффективно даже на ограниченной скорости.
Как выбрать лучшее казино?
При выборе онлайн-казино учитывайте следующие факторы:
Лицензия и безопасность
Убедитесь, что казино имеет международную лицензию и использует шифрование данных (SSL).
Ассортимент игр
Лучшие казино предлагают разнообразие слотов, классических развлечений (блэкджек) и live-казино.
Скорость выплат
Изучите реальные комментарии о времени вывода средств.
Бонусные программы
Обратите внимание на условия акций, требования по отыгрышу и наличие других предложений.
Качество поддержки
Проверьте, насколько профессионально сотрудники помогают пользователям.
Мобильная версия
Убедитесь, что казино имеет адаптированную версию для смартфонов.
Заключение
Онлайн-казино могут стать способом отдыха, если подходить к их выбору серьёзно. Придерживайтесь наших советов, играйте только на проверенных платформах и помните о правилах ответственной игры. Азартные игры — это прежде всего развлечение, а не способ заработка.
Если вы ищете надёжное казино с быстрыми выплатами, обратите внимание на топовые площадки, такие как Cat Casino. Они высоко ценятся среди игроков и продолжают впечатлять.
https://t.me/s/topcasinos_ru
порядок согласования перепланировки порядок согласования перепланировки .
кайт хургада
В Красной Поляне с радостью представляем вам сайт для знакомств с девушками 18+. Здесь вы сможете найти множество интересных предложений для общения и веселья, открывая для себя мир новых знакомств и ярких эмоций вместе с привлекательными дамами https://night24-krasnaya-polyana.com/
k8 bet: k8 bet – k8 th? dam
gokong88
porno web
Заказать диплом университета по доступной стоимости возможно, обращаясь к проверенной специализированной компании. Мы предлагаем документы об окончании любых ВУЗов РФ. Заказать диплом университета– diploma-groups24.ru/kupit-spravku/arhivnaya-spravka.html
https://k8viet.guru/# k8vip
789alo: alo789 chinh th?c – alo789 dang nh?p
https://football-today.uk/
Приобретение документа о высшем образовании через качественную и надежную фирму дарит ряд преимуществ для покупателя. Это решение помогает сэкономить как личное время, так и серьезные финансовые средства. Тем не менее, на этом выгоды не ограничиваются, преимуществ намного больше.Мы готовы предложить дипломы психологов, юристов, экономистов и других профессий. Дипломы производят на оригинальных бланках. Доступная цена по сравнению с крупными тратами на обучение и проживание. Покупка диплома о высшем образовании из российского института является выгодным шагом.
Приобрести диплом: asxdiploman.com/diplom-rostov-kupit/
http://88betviet.pro/# 188bet 88bet
The best location for installation is in an open room that gets great airflow.
k8vip nha cai k8 k8
https://88betviet.pro/# nha cai 88bet
nha cai 88bet: 88 bet – keo nha cai 88bet
Hey there! This post couldn’t be written any better! Reading through this post reminds me of my good old room mate! He always kept chatting about this. I will forward this post to him. Fairly certain he will have a good read. Thanks for sharing!
https://www.jointcorners.com/read-blog/121000
keo nha cai 88bet: 188bet 88bet – 88 bet
gokong88
казино 1win http://www.1win823.ru .
gokong88
However, they are not as reliable as split-unit conditioners as they are less powerful.
Где купить диплом специалиста?
Мы изготавливаем дипломы любых профессий по выгодным тарифам. Мы предлагаем документы ВУЗов, которые находятся в любом регионе России. Можно заказать качественный диплом за любой год, указав подходящую специальность и хорошие оценки за все дисциплины. Документы выпускаются на “правильной” бумаге самого высокого качества. Это дает возможность делать государственные дипломы, не отличимые от оригинала. Документы заверяются необходимыми печатями и штампами. Всегда стараемся поддерживать для заказчиков адекватную политику цен. Важно, чтобы дипломы были доступны для большого количества наших граждан. diploms-vuza.com/kupit-diplom-v-samare-2-5
http://k8viet.guru/# link vao k8
карнизы электрические карнизы электрические .
Le code promo 1xBet: 1XFOX200. Les nouveaux joueurs seront eligibles a un bonus VIP de 100% jusqu’a 130€/$. Ce code promo vous permettra d’obtenir un bonus de bienvenue jusqu’a 130€ sur les paris sportifs. Pour profiter des bonus sur la plate-forme du bookmaker 1xbet, vous devez vous inscrire en utilisant le code bonus. Inscrivez-vous des maintenant avec notre code promo 1xBet pour recevoir un bonus de bienvenue de 100% sur votre premier depot.
Meilleur code promo 1xbet: 1XFOX200 vous permettra d’augmenter votre premier depot jusqu’a 100% avec un bonus jusqu’a 130€/$. Les nouveaux clients peuvent recevoir un bonus de 1xbet allant jusqu’a 130 €/$. Pour retirer les fonds lies au bonus, la moitie du montant du bonus doit etre misee 5 fois sur des paris combines, qui doivent chacun contenir au moins 3 evenements avec des cotes egales ou superieures a 1.40.
кайт школа анапа
карнизы для штор с электроприводом карнизы для штор с электроприводом .
win 1 http://1win823.ru .
https://k8viet.guru/# k8vip
Купить документ института вы можете в нашей компании. diplomservis.ru/kupit-diplom-kolledzha-4-51
Где купить диплом по нужной специальности?
Мы предлагаем дипломы любой профессии по невысоким ценам. Мы готовы предложить документы техникумов, которые расположены в любом регионе РФ. Вы сможете купить качественно напечатанный диплом от любого заведения, за любой год, указав подходящую специальность и оценки за все дисциплины. Дипломы и аттестаты выпускаются на бумаге самого высшего качества. Это позволяет делать государственные дипломы, которые невозможно отличить от оригиналов. Документы заверяются всеми обязательными печатями и штампами. Стараемся поддерживать для заказчиков адекватную политику цен. Важно, чтобы документы были доступны для большинства наших граждан. nsk-diplom.com/kupit-diplom-stomatologa-8
Get the latest updates with the latest news on cryptocurrencies, the leading cryptocurrency, and the blockchain space.
Our portal provides fresh insights into blockchain innovations, including price changes, new coin launches, and blockchain innovations.
Whether you’re following Bitcoin or learning about altcoins, we bring you expert analysis and insightful commentary.
Get the up-to-date crypto news today and keep up on market shifts, regulation changes, and key news in the digital asset space.
altcoinix.com
Stay connected to get real-time updates!
1win официальный сайт http://www.1win822.ru .
Заказ документа о высшем образовании через надежную фирму дарит множество достоинств. Это решение позволяет сэкономить как личное время, так и серьезные финансовые средства. Впрочем, на этом выгоды не ограничиваются, достоинств гораздо больше.Мы готовы предложить дипломы психологов, юристов, экономистов и прочих профессий. Дипломы производят на настоящих бланках государственного образца. Доступная цена в сравнении с серьезными расходами на обучение и проживание в другом городе. Заказ диплома университета является разумным шагом.
Купить диплом о высшем образовании: dip-lom-rus.ru/kupit-diplom-v-krasnodare-bistro-i-nadezhno/
nitehush is designed to support your respiratory system, helping you enjoy a quiet, uninterrupted night’s sleep.
1win скачать последнюю версию http://1win822.ru .
alo 789: dang nh?p alo789 – alo 789
Very good blog! Do youu have any helpful hints for aspiring writers?
I’m hoping to start my own log soon but I’m a little lost on everything.
Would you advise starting with a free plarform llike
Wordpress or go for a paid option? There arre so many choices out there that I’m completely confused ..
Any recommendations? Thanks a lot! http://blog.pfoetchen-tour-heidelberg.de/2025/03/18/danh-gia-website-ca-cuoc-20bet-quy-trinh-rut-tien-va-cach-de-su-dung-sportsbook-trong-mot-ngay-nham-tao-ra-trai-nghiem-the-thao-tot-nhat/
Hmm it appears like your blog ate my first comnent (it was extremely long) so I guess
I’ll just sum it up what I wrote and say,
I’m thoroughly enjoying your blog. I as well am an aspiring blog writer but I’m still new to thhe hole thing.
Do you have any tips for inexperienced bloog writers?
I’d certainly appreciate it. https://Www.Tobeop.com/create-an-account-on-22bet-click-to-register-enter-email-and-password-to-access-all-available-bonuses-and-offers-for-mobile-slots/
Купить документ ВУЗа вы сможете в нашей компании в столице. diplom-kaluga.ru/kupit-diplom-mexanika
Hey! Do you know iif they make any pougins to assist with SEO?
I’m trying to get my blog to rank for some targeted keywords but I’m not seeing very ood gains.
If you know of any please share. Kudos! https://Xn—-Jtbigbxpocd8G.Xn–P1ai/preskumanie-bizzo-objavte-bohaty-vyber-zivych-hier-a-pokru-s-bonusmi-volnymi-zatoceniami-a-chatom-ktore-mate-k-dispozicii-hned-po-registracii/
Quality articles is thee key tto interest the vuewers to pay a visitt
the website, that’s what this web page is providing. http://Www.Leefairshare.org/bizzo-casino-en-ny-spilleside-med-rikelig-med-spill-gratis-bonuser-og-betalingsalternativer-for-alle-spillere/
It’s really very difficult in this bussy life to listen news on Television, thus I jhst use the web for that reason, and obtain the most
up-to-date information. https://www.Smstkart.com/entre-no-site-de-apostas-20bet-o-aplicativo-que-propicia-uma-experiencia-desportiva-unica-para-os-fas-do-jogo-com-uma-ampla-gama-de-competicoes-e-palpites/
It’s really very complicated in this active life to listen news onn Television, thus I simply use world wide
web for thnat purpose, and obtain the newest information. https://advansbum.by/?option=com_k2&view=itemlist&task=user&id=1252831
I’m not that much of a internet reader to be honest but your sites really nice, keep it up!
I’ll go ahead and bookmark your website to come back later.
Many thanks http://blog.pfoetchen-Tour-heidelberg.de/2025/03/18/by-clicking-to-register-on-22bet-you-can-create-an-account-and-enter-your-email-with-a-password-to-access-all-bonuses-and-mobile-slots-7/
мост бет мост бет .
I do not even know how I enhded up here, but I thought this post was good.
I do not know who you are but certainly you’re going to a famous blogger if you are not already 😉 Cheers! https://Xn—-jtbigbxpocd8g.xn--p1ai/a-bizzo-kaszino-attekintese-milyen-mas-bonuszok-es-jatekok-erhetok-el-a-jatekosok-szamara-mig-a-legjobb-lehetosegek-a-betetek-kozott-talalhatok/
k8 th? dam k8vip nha cai k8
провести соут в москве провести соут в москве .
Профессиональные консультации по договорному праву и юридическое сопровождение сделок – всеми деталями поделятся здесь https://ai.ceo/TimurOrlov8312
соут москва цена sout-moskva.ru .
кайтинг в анапе
mostbet apk скачать mostbet782.ru .
Где купить диплом по актуальной специальности?
Наша компания предлагает быстро заказать диплом, который выполняется на оригинальной бумаге и заверен печатями, водяными знаками, подписями официальных лиц. Данный диплом способен пройти любые проверки, даже при помощи специального оборудования. Решайте свои задачи быстро и просто с нашей компанией.
Заказать диплом о высшем образовании diplomt-v-chelyabinske.ru/kupit-diplom-v-tyumeni-8/
кайт школа хургада
Привет!
Без ВУЗа очень сложно было продвинуться по карьере. Сегодня же документ не дает абсолютно никаких гарантий, что получится получить хорошо оплачиваемую работу. Намного более важное значение имеют практические навыки специалиста и его опыт. Поэтому решение о заказе диплома стоит считать выгодным и целесообразным. Купить диплом о высшем образовании repetitor.ekafe.ru/faq.php
ואחד הבחורים עבד עלי, ושניים גמרו לי בפה וליקקתי את שאריות הזרע מהזין שלהם, ושאר החבר ‘ ה עישנו. לנקה אמרה שזה כבר 2 לפנות בוקר ואת מייקל. – כן, חבר, תאונן, אבל אל תגמור! מייקל איים מיד. – רק אני יכול להשפריץ זרע כאן. “כרע ברך והסתכל עלינו,” הורתה אמילי. take a look at the site here
https://alo789.auction/# alo 789
Здравствуйте!
Купить диплом университета по выгодной стоимости можно, обратившись к проверенной специализированной компании. Приобрести диплом о высшем образовании: kupitediplom.ru/kupit-diplom-vospitatelya-5/
We supply services from 8 am to 5 pm every weekday and
an out of hours solution at our customers demand.
Приобрести диплом университета!
Мы изготавливаем дипломы любой профессии по выгодным ценам— diplomc-v-ufe.ru/kupit-diplom-svarshika-10/
заказать соут москва заказать соут москва .
Medic ORL Sibiu
Dr. Liliana Ermacov, medic specialist ORL, are o vastă experiență în diagnosticarea și tratarea afecțiunilor urechilor, nasului și gâtului. Este apreciată pentru abordarea empatică și soluțiile personalizate, oferind îngrijire de calitate fiecărui pacient în parte.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
кайт сафари
Medic ORL Sibiu
Dr. Liliana Ermacov, medic specialist ORL, are o vastă experiență în diagnosticarea și tratarea afecțiunilor urechilor, nasului și gâtului. Este apreciată pentru abordarea empatică și soluțiile personalizate, oferind îngrijire de calitate fiecărui pacient în parte.
Приобрести документ о получении высшего образования вы имеете возможность в нашем сервисе. detikkeprinews.com/13195-2
https://k8viet.guru/# link vao k8
мостбет промокод http://mostbet783.ru/ .
игра 1вин https://1win810.ru/ .
Где купить диплом по актуальной специальности?
Мы предлагаем выгодно и быстро приобрести диплом, который выполнен на бланке ГОЗНАКа и заверен печатями, водяными знаками, подписями должностных лиц. Данный документ пройдет любые проверки, даже с использованием специфических приборов. Решите свои задачи максимально быстро с нашими дипломами.
Приобрести диплом университета kupit-diplom24.com/kupit-diplom-s-reestrom-26/
мостбет зеркало мостбет зеркало .
Приобрести диплом любого ВУЗа!
Мы изготавливаем дипломы любой профессии по невысоким ценам— poluchidiplom.com/kupit-diplom-o-srednem-obrazovanii-44/
1 вин скачать http://1win810.ru .
mostbet промокод mostbet783.ru .
мостбет скачать андроид http://mostbet784.ru .
k8: link vao k8 – link vao k8
This web site really has all the information I wanted concerning this subject and didn’t know who to ask.
кайт хургада
http://k8viet.guru/# k8 th? dam
Привет!
Купить диплом университета по доступной стоимости вы можете, обращаясь к проверенной специализированной компании. Заказать диплом: fastdiploms.com/kupit-diplom-trenera-8/
http://alo789.auction/# alo789in
Полный уход за автомобилем в одном месте! Nord-West детейлинг предлагает комплекс услуг: глубокую химчистку салона, полировку кузова и защитное покрытие керамикой. Обращайтесь за качественным детейлингом в Великий Новгород уже сегодня!
Топ онлайн казино 2025: профессиональный анализ лучших игровых платформ
Виртуальные казино стремительно расширяют свою аудиторию в России, завоевывая всё больше игроков благодаря своей доступности. Однако для безопасного времяпрепровождения критически важно выбирать только проверенные площадки, которые гарантируют прозрачность работы. В этом материале мы рассмотрим ключевые критерии выбора, представим рейтинг лучших казино 2025 года и предоставим практические инструкции для максимально эффективной игры.
Основные признаки безопасности онлайн-казино
Чтобы защититься от мошенников, необходимо учитывать следующие характеристики:
Лицензионная чистота
Проверяйте наличие международных лицензий: Кюрасао.
Убедитесь, что игровые автоматы прошли сертификацию от авторитетных организаций (eCOGRA).
Система случайных чисел (RNG)
Казино должно использовать независимый генератор случайных чисел, что обеспечивает прозрачность процессов.
Скорость транзакций
Надёжные казино предлагают мгновенные выплаты через разнообразные инструменты: банковские карты (Visa), электронные кошельки (WebMoney) и блокчейн-валюты (Bitcoin).
Бонусная политика
Хорошие казино предоставляют впечатляющие бонусы: стартовые предложения, фриспины и системы вознаграждений. Обратите внимание на условия отыгрыша.
Мобильная оптимизация
Современные казино оптимизированы для мобильных устройств (Android) с быстрой загрузкой. Это позволяет проводить время за играми в любое время.
Клиентская поддержка
Эффективная служба поддержки работает круглосуточно и помогает решать вопросы через Telegram.
Рейтинг лучших онлайн-казино 2025 года
1. Cat Casino
Преимущества: мгновенные выводы средств (до 1 минуты), лицензия Кюрасао, особые бонусы.
Бонусы: стартовый пакет — 100 фриспинов в Book of Dead.
Особенности: специальные мероприятия.
2. Kometa Casino
Преимущества: ведущая платформа с дилерами, кэшбэк до 50 000?.
Бонусы: стартовый комплект — 255% + 500 бесплатных вращений.
Особенности: VIP-клуб с индивидуальными бонусами.
3. R7 Casino
Преимущества: приватный вход по email, поддержка цифровых активов (BTC) с бесплатными транзакциями.
Бонусы: фриспины за участие в акциях.
Особенности: двухфакторная аутентификация для предотвращения взломов.
4. Arkada Casino
Преимущества: оперативные транзакции на карты РФ (Сбербанк), регулярные розыгрыши.
Бонусы: кэшбэк до 10%, приветственная награда.
Особенности: сертифицированные слоты от NetEnt.
5. Kent Casino
Преимущества: поддержка криптовалют, турниры с призовым фондом 1 млн рублей.
Бонусы: возможность бесплатной игры.
Особенности: широкий выбор слотов с оптимальным возвратом.
Особенности мобильных казино
Мобильные казино становятся актуальными благодаря технологичности. Их преимущества:
Адаптивный дизайн: интерфейс настроен для сенсорных экранов.
Быстрый доступ: нет необходимости устанавливать программы.
Поддержка платежей: можно вести транзакции и выводить средства через специальные сервисы.
Низкое потребление трафика: современные казино работают эффективно даже на низкой пропускной способности.
Как выбрать лучшее казино?
При выборе онлайн-казино учитывайте следующие критерии:
Лицензия и безопасность
Убедитесь, что казино имеет международную лицензию и использует технологии безопасности (другие протоколы).
Ассортимент игр
Лучшие казино предлагают разнообразие слотов, классических развлечений (рулетка) и живые игры.
Скорость выплат
Изучите мнения пользователей о времени вывода средств.
Бонусные программы
Обратите внимание на условия акций, требования по отыгрышу и наличие других акций.
Качество поддержки
Проверьте, насколько быстро сотрудники устраняют проблемы.
Мобильная версия
Убедитесь, что казино имеет специальное приложение для смартфонов.
Заключение
Онлайн-казино могут стать способом отдыха, если подходить к их выбору вдумчиво. Придерживайтесь наших советов, играйте только на проверенных платформах и помните о основах безопасного гейминга. Азартные игры — это прежде всего удовольствие, а не источник дохода.
Если вы ищете надёжное казино с быстрыми выплатами, обратите внимание на топовые площадки, такие как Kometa Casino. Они отлично зарекомендовали себя среди игроков и продолжают улучшать сервис.
https://t.me/s/topcasinos_ru
кайтсёрфинг в станице благовещенской
k8 bet nha cai k8 k8vip
Экономия до 99% на качественных образовательных ресурсах? Да, это реально! Перейдите по ссылке для подробностей https://hackerone.com/skladchik?type=user
кайт эльгуна
https://www.greenwichodeum.com/wp-content/pages/1xbet_today_promo_code_bonus_up_to_130.html
dang nh?p alo789: alo 789 – alo 789
http://alo789.auction/# alo 789
мостбет зеркало http://eisberg.forum24.ru/?1-0-0-00000327-000-0-0-1742579529/ .
mostbet официальный сайт https://www.taksafonchik.borda.ru/?1-14-0-00002042-000-0-0-1742473173 .
1 вин про https://www.fanfiction.borda.ru/?1-3-0-00000125-000-0-0-1742475251 .
http://alo789.auction/# alo789
I like reading through a post that can make men and women think. Also, thanks for permitting me to comment.
mostbet скачать на телефон бесплатно андроид https://eisberg.forum24.ru/?1-0-0-00000327-000-0-0-1742579529 .
мостбет промокод taksafonchik.borda.ru/?1-14-0-00002042-000-0-0-1742473173 .
1win. com http://fanfiction.borda.ru/?1-3-0-00000125-000-0-0-1742475251 .
When you pick AMC Air Disadvantage for your brand-new a/c unit,
you can trust that you’re in the right hands.
Мы изготавливаем дипломы любых профессий по приятным тарифам. Стоимость будет зависеть от выбранной специальности, года выпуска и университета. Стараемся поддерживать для клиентов адекватную политику цен. Важно, чтобы документы были доступны для большого количества наших граждан. купить аттестаты за 9 класс с оценками в волхове
nitehush is designed to support your respiratory system, helping you enjoy a quiet, uninterrupted night’s sleep.
Заказать диплом о высшем образовании!
Мы можем предложить документы ВУЗов, расположенных на территории всей Российской Федерации.
diplomk-v-krasnodare.ru/kupil-diplom-o-srednem-obrazovanii-3
Мы готовы предложить дипломы любых профессий по приятным тарифам. Всегда стараемся поддерживать для заказчиков адекватную политику тарифов. Важно, чтобы дипломы были доступны для большого количества наших граждан.
Заказ диплома, который подтверждает окончание института, – это разумное решение. Купить диплом о высшем образовании: diplomh-40.ru/kupit-diplom-meditsinskogo-uchilisha-9/
alo789: alo 789 – alo789hk
https://k8viet.guru/# nha cai k8
alo 789 alo 789 alo789 dang nh?p
Приобрести диплом о высшем образовании!
Мы можем предложить документы институтов, расположенных в любом регионе РФ.
diplom-kaluga.ru/kupit-attestat-39
This permits cooling several areas or areas within a business area using a solitary system.
Мы можем предложить дипломы любых профессий по приятным ценам. Купить диплом Красногорск — kyc-diplom.com/geography/krasnogorsk.html
http://88betviet.pro/# nha cai 88bet
Мы изготавливаем дипломы психологов, юристов, экономистов и других профессий по доступным тарифам. Дипломы изготавливаются на фирменных бланках государственного образца Заказать диплом об образовании diplomt-tver69.ru
Мы готовы предложить дипломы любых профессий по приятным ценам. Всегда стараемся поддерживать для заказчиков адекватную политику цен. Важно, чтобы документы были доступными для подавляющей массы наших граждан.
Покупка диплома, который подтверждает обучение в ВУЗе, – это рациональное решение. Купить диплом о высшем образовании: asxdiploman.com/kupit-diplom-visshee-3/
Купить диплом университета!
Мы готовы предложить документы учебных заведений, расположенных на территории всей Российской Федерации. Дипломы и аттестаты выпускаются на “правильной” бумаге высшего качества: imolod.ru/wp-content/pages/kupit_diplom_attestat_bustro_i_bez_lishnih_usiliy.html
Приобретите качественные купели для бани, или спа-зоны в нашем магазине! Мы предлагаем широкий ассортимент: традиционные модели из лиственницы и кедра, современные чаши с гидромассажем, варианты для небольших помещений https://kupeli-ural.ru/
Где купить диплом по необходимой специальности?
Наши специалисты предлагают быстро и выгодно заказать диплом, который выполнен на оригинальном бланке и заверен печатями, водяными знаками, подписями. Диплом пройдет лубую проверку, даже с применением специальных приборов. Достигайте цели быстро и просто с нашей компанией. Купить диплом любого ВУЗа! bioniclerpg.getbb.ru/posting.php?mode=post&f=6&sid=82edbe0ddfc8687b8ee0c067105dd032
https://www.vegasy-casino.net/
An impressive share! I’ve just forwarded this onto a coworker who has been doing a little research on this. And he actually bought me dinner because I discovered it for him… lol. So let me reword this…. Thanks for the meal!! But yeah, thanks for spending time to discuss this subject here on your site.
Заказать диплом университета!
Мы изготавливаем дипломы любой профессии по невысоким ценам— diplom-kaluga.ru/kupit-diplom-o-visshem-obrazovanii-ofitsialnij-2/
Мы изготавливаем дипломы любых профессий по невысоким тарифам. Всегда стараемся поддерживать для заказчиков адекватную ценовую политику. Важно, чтобы документы были доступными для большого количества наших граждан.
Заказ документа, который подтверждает обучение в университете, – это выгодное решение. Заказать диплом о высшем образовании: diplomius-docs.com/kupit-diplom-o-obrazovanii-2/
Эта компания поможет вам найти работу или сотрудников быстро и легко, узнайте больше тут https://www.spigotmc.org/members/domkadrov.2241633/
печать на упаковке коробках https://izgotovlenie-upakovky.ru
nha cai 88bet: 88bet – keo nha cai 88bet
Заказать диплом о высшем образовании!
Мы изготавливаем дипломы психологов, юристов, экономистов и любых других профессий по выгодным ценам. Вы приобретаете диплом через надежную и проверенную временем фирму. : diplomj-irkutsk.ru/kupit-diplom-vashasp-o-visshem-obrazovanii-na-blanke-goznak-3/
http://alo789.auction/# alo789 dang nh?p
https://88betviet.pro/# nha cai 88bet
Auf Bird-Shop.de finden Sie alles Wissenswerte rund um die artgerechte Haltung von Zimmer-Vogeln. Entdecken Sie Tipps und Ratgeber zu Vogelkafigen und Zimmervolieren fur Wellensittiche, Papageien, Kanarienvogel & Co. Erfahren Sie, worauf es bei der Kafiggro?e, Einrichtung und Standortwahl ankommt, um Ihren Vogeln ein sicheres und gluckliches Zuhause zu bieten.
Wellensittich-Kafig
1win играть http://1win824.ru/ .
1вин официальный сайт мобильная 1вин официальный сайт мобильная .
1 win.kg 1win811.ru .
Быстро и просто приобрести диплом об образовании!
Мы изготавливаем дипломы психологов, юристов, экономистов и прочих профессий по выгодным тарифам— diplomk-v-krasnodare.ru/diplom-kupit-ofitsialno-4/
Мы изготавливаем дипломы любой профессии по приятным ценам. Стараемся поддерживать для заказчиков адекватную ценовую политику. Важно, чтобы документы были доступными для большого количества наших граждан.
Заказ диплома, который подтверждает обучение в университете, – это выгодное решение. Приобрести диплом любого университета: diplomius-docs.com/kupit-diplom-9/
кайт хургада
Где купить диплом специалиста?
Мы оказываем услуги по продаже документов об окончании любых университетов Российской Федерации. Документы производятся на подлинных бланках. mosdmit.flybb.ru/viewtopic.php?f=2&t=656
Приветствую!
Купить диплом университета по невысокой цене вы сможете, обращаясь к надежной специализированной компании. Заказать диплом о высшем образовании: diplomass.com/kupit-diplom-dlya-inostrantsev-3/
Very good information. Lucky me I came across your website by accident (stumbleupon). I’ve saved it for later!
1вин войти http://1win824.ru .
1вин официальный http://1win825.ru .
ван вин http://www.1win811.ru .
Приобрести диплом университета!
Мы предлагаем документы ВУЗов, расположенных в любом регионе РФ. Документы делаются на “правильной” бумаге самого высшего качества: [url=http://mg-group74.ru/pages/kupit_attestat_za_31.html/]mg-group74.ru/pages/kupit_attestat_za_31.html[/url]
Покупка документа о высшем образовании через надежную фирму дарит много плюсов для покупателя. Данное решение помогает сберечь как продолжительное время, так и серьезные денежные средства. Тем не менее, только на этом выгода не ограничивается, достоинств гораздо больше.Мы изготавливаем дипломы любых профессий. Дипломы изготавливаются на подлинных бланках. Доступная стоимость сравнительно с крупными тратами на обучение и проживание. Приобретение диплома о высшем образовании из российского института является мудрым шагом.
Приобрести диплом о высшем образовании: diplomservis.com/kupit-attestati-za-9-22/
https://alo789.auction/# alo 789 dang nh?p
кайт хургада
сипл дипл купить
Greetings! Very helpful advice in this particular post! It is the little changes which will make the largest changes. Thanks a lot for sharing!
Где купить диплом по нужной специальности?
Готовый диплом со всеми печатями и подписями отвечает запросам и стандартам, неотличим от оригинала. Не откладывайте собственные мечты и задачи на потом, реализуйте их с нами – отправьте заявку на диплом сегодня! Диплом о среднем специальном образовании – не проблема! rusd-diplomj.ru/kupit-diplom-vracha-bistro-i-nadezhno-4/
There is certainly a great deal to find out about this subject. I like all the points you’ve made.
купить аттестат о среднем образовании с твердой обложкой в красноярске
Где заказать диплом по нужной специальности?
Мы оказываем услуги по изготовлению и продаже документов об окончании любых университетов РФ. Документы производятся на фирменных бланках. forum-nine.mirbb.com/login
кайт сафари
mostbet скачать на телефон бесплатно андроид http://mostbet785.ru .
1win официальный 1win официальный .
nitehush is designed to support your respiratory system, helping you enjoy a quiet, uninterrupted night’s sleep.
1win зайти https://1win812.ru/ .
Приобретение диплома ВУЗа через проверенную и надежную фирму дарит ряд плюсов для покупателя. Это решение помогает сберечь время и существенные финансовые средства. Тем не менее, на этом выгода не ограничивается, достоинств гораздо больше.Мы изготавливаем дипломы любых профессий. Дипломы производят на настоящих бланках государственного образца. Доступная стоимость по сравнению с огромными расходами на обучение и проживание. Покупка диплома об образовании из российского ВУЗа станет целесообразным шагом.
Заказать диплом о высшем образовании: diplomt-v-chelyabinske.ru/kupit-diplom-visshem-obrazovanii-zaneseniem-reestr-2/
мосбет https://mostbet785.ru .
официальный сайт 1 вин https://www.1win826.ru .
Промокод Фонбет – это кодовые слова, например: MAX777, ввод которых при регистрации в БК Фонбет или в личном кабинете позволяет получить фрибеты, страховки ставок и другие специальные бонусы. Промокодом в беттинге называется комбинация букв и цифр, при вводе которых активируется бонус. Новым клиентам Фонбет предлагает приветственные фрибеты на сумму от 100 до 15 000 рублей.
Фонбет промокод: MAX777, используйте его при регистрации аккаунта. Новые пользователи могут активировать бонус и получить бездепозитный фрибет до 15 000 рублей. Воспользоваться бесплатно промокодами «Фонбет» для получения подарочной ставки или другого бонуса можно во время создания аккаунта на официальном сайте букмекерской конторы, а также после активации личного кабинета. Действующие промокоды могут давать зачисление кэшбэка на депозит, бесплатное пари и т.п.
пари ру промокод
1 win казино https://1win812.ru/ .
Где заказать диплом специалиста?
Мы предлагаем быстро купить диплом, который выполнен на бланке ГОЗНАКа и заверен мокрыми печатями, штампами, подписями официальных лиц. Данный диплом пройдет лубую проверку, даже при помощи специально предназначенного оборудования. Достигайте свои цели максимально быстро с нашей компанией.
Приобрести диплом любого ВУЗа diplomus-spb.ru/kupit-diplom-spetsialista-17/
Промокод Фонбет – это кодовые слова, например: MAX777, ввод которых при регистрации в БК Фонбет или в личном кабинете позволяет получить фрибеты, страховки ставок и другие специальные бонусы. Промокодом в беттинге называется комбинация букв и цифр, при вводе которых активируется бонус. Новым клиентам Фонбет предлагает приветственные фрибеты на сумму от 100 до 15 000 рублей.
Фонбет промокод: MAX777, используйте его при регистрации аккаунта. Новые пользователи могут активировать бонус и получить бездепозитный фрибет до 15 000 рублей. Воспользоваться бесплатно промокодами «Фонбет» для получения подарочной ставки или другого бонуса можно во время создания аккаунта на официальном сайте букмекерской конторы, а также после активации личного кабинета. Действующие промокоды могут давать зачисление кэшбэка на депозит, бесплатное пари и т.п.
промокод на фонбет на сегодня
Revamp your automobile with premium tuning choices. Release its complete capability and experience improved efficiency. Our professional technicians excels in personalizing individual part of your ride to match your flair and preferences. Explore our portal https://autobodywilson.com/ to discover supplementary, and embrace a new driving exploration today.
alo789in alo 789 dang nh?p alo 789
http://88betviet.pro/# 88bet slot
Когда речь заходит о биологической безопасности, важно не просто утилизировать, а делать это правильно. Печь для утилизации биологических отходов от ЭКОСИСТЕМЫ обеспечивает полное обеззараживание остатков: от лабораторных проб до медицинского материала. Современная система дожига, герметичность и контроль температуры — надёжное решение с гарантией.
Мы изготавливаем дипломы психологов, юристов, экономистов и других профессий по приятным тарифам. Купить диплом в Балаково — kyc-diplom.com/geography/balakovo.html
k8: k8 th? dam – k8 th? dam
Где заказать диплом по нужной специальности?
Мы готовы предложить дипломы любой профессии по приятным тарифам. Мы можем предложить документы ВУЗов, расположенных на территории всей РФ. Можно приобрести качественный диплом от любого учебного заведения, за любой год, включая документы СССР. Дипломы и аттестаты выпускаются на бумаге самого высокого качества. Это дает возможность делать государственные дипломы, которые невозможно отличить от оригиналов. Документы заверяются необходимыми печатями и штампами. Стараемся поддерживать для заказчиков адекватную политику цен. Для нас важно, чтобы документы были доступны для подавляющей массы наших граждан. [url=http://nsk-diplom.com/kupit-diplom-v-velikom-novgorode-2-2/]nsk-diplom.com/kupit-diplom-v-velikom-novgorode-2-2[/url]
http://alo789.auction/# alo789 dang nh?p
Мы изготавливаем дипломы любых профессий по разумным ценам.– http://www.ibtecno.com/contact/index.php
Купить документ о получении высшего образования можно у нас. diplomidlarf.ru/kupit-diplom-tver-4
Где приобрести диплом специалиста?
Мы изготавливаем дипломы любой профессии по приятным ценам. Мы можем предложить документы техникумов, расположенных на территории всей РФ. Можно заказать качественно напечатанный диплом от любого заведения, за любой год, включая документы старого образца СССР. Документы выпускаются на бумаге высшего качества. Это дает возможность делать государственные дипломы, которые невозможно отличить от оригинала. Они заверяются необходимыми печатями и штампами. Стараемся поддерживать для заказчиков адекватную политику тарифов. Важно, чтобы документы были доступны для большого количества граждан. diplom-city24.ru/kupit-svidetelstvo-o-brake-2-5
1 win. http://1win827.ru/ .
pariuri sportive moldova http://1win5003.ru/ .
мостбет скачать бесплатно http://mostbet786.ru/ .
Топ онлайн казино 2025: эксклюзивный обзор лучших игровых платформ
Интернет-гемблинг стремительно расширяют свою аудиторию в России, заинтересовывая всё больше игроков вследствие своей функциональности. Однако для комфортного гейминга критически важно выбирать только проверенные площадки, которые гарантируют прозрачность работы. В этом материале мы рассмотрим ключевые стандарты качества, составим список лучших казино 2025 года и предоставим практические инструкции для максимально эффективной игры.
Основные признаки безопасности онлайн-казино
Чтобы избежать рисков, необходимо учитывать следующие характеристики:
Лицензионная чистота
Проверяйте наличие регуляторных разрешений: Великобритании.
Убедитесь, что игровые автоматы прошли сертификацию от авторитетных организаций (GLI).
Система случайных чисел (RNG)
Казино должно использовать проверенный генератор случайных чисел, что обеспечивает честность игры.
Скорость транзакций
Надёжные казино предлагают быстрые выплаты через современные системы: банковские карты (Visa), электронные кошельки (QIWI) и цифровые активы (Litecoin).
Бонусная политика
Хорошие казино предоставляют впечатляющие бонусы: стартовые предложения, фриспины и системы вознаграждений. Обратите внимание на требования по использованию.
Мобильная оптимизация
Современные казино настроены для мобильных устройств (Android) с удобным управлением. Это позволяет наслаждаться развлечениями в любое время.
Клиентская поддержка
Отзывчивая служба поддержки работает 24/7 и помогает решать вопросы через Telegram.
Рейтинг лучших онлайн-казино 2025 года
1. Cat Casino
Преимущества: мгновенные выводы средств (до 1 минуты), лицензия Curacao, уникальные предложения.
Бонусы: бездепозитный бонус — 100 фриспинов в Gates of Olympus.
Особенности: турниры с крупными призами.
2. Kometa Casino
Преимущества: топовая живая игра, кэшбэк до значительной суммы.
Бонусы: стартовый комплект — впечатляющий приветственный пакет.
Особенности: VIP-клуб с индивидуальными бонусами.
3. R7 Casino
Преимущества: приватный вход по email, поддержка криптовалют (USDT) с бесплатными транзакциями.
Бонусы: фриспины за участие в акциях.
Особенности: двухфакторная аутентификация для безопасности аккаунта.
4. Arkada Casino
Преимущества: быстрые выплаты на карты РФ (Сбербанк), регулярные розыгрыши.
Бонусы: кэшбэк до значительного процента, приветственная награда.
Особенности: сертифицированные слоты от Pragmatic Play.
5. Kent Casino
Преимущества: поддержка криптовалют, турниры с призовым фондом 1 млн рублей.
Бонусы: демо-режим.
Особенности: широкий выбор слотов с максимальной отдачей.
Особенности мобильных казино
Мобильные казино становятся актуальными благодаря удобству использования. Их преимущества:
Адаптивный дизайн: интерфейс адаптирован для мобильных устройств.
Быстрый доступ: нет необходимости устанавливать программы.
Поддержка платежей: можно производить депозиты и получать выигрыши через специальные сервисы.
Низкое потребление трафика: современные казино работают быстро даже на медленном интернете.
Как выбрать лучшее казино?
При выборе онлайн-казино учитывайте следующие аспекты:
Лицензия и безопасность
Убедитесь, что казино имеет глобальное разрешение и использует шифрование данных (SSL).
Ассортимент игр
Лучшие казино предлагают широкий выбор слотов, классических развлечений (рулетка) и живые игры.
Скорость выплат
Изучите отзывы игроков о времени вывода средств.
Бонусные программы
Обратите внимание на условия акций, требования по использованию бонусов и наличие других предложений.
Качество поддержки
Проверьте, насколько профессионально сотрудники помогают пользователям.
Мобильная версия
Убедитесь, что казино имеет адаптированную версию для смартфонов.
Заключение
Онлайн-казино могут стать интересным хобби, если подходить к их выбору серьёзно. Придерживайтесь наших советов, играйте только на проверенных платформах и помните о важности самоконтроля. Азартные игры — это прежде всего способ провести время, а не финансовая стратегия.
Если вы ищете проверенную платформу с щедрыми бонусами, обратите внимание на топовые площадки, такие как Kometa Casino. Они пользуются доверием среди игроков и продолжают радовать своими предложениями.
https://t.me/s/topcasinos_ru
Строительные бытовки
Вагончики и блок-контейнеры: надёжное решение для клиентских проблем
Модули и модульные здания организовывают оборудовать рабочее пространство, хранилище или временную постройку. Наши специалисты поставляем здания, которые подходят профессиональным нормам качества и эргономики.
Параметры
Стойкость. Данные бытовки произведены из материалов, прочных к нагрузкам и климатическим факторам.
Оперативность транспортировки. Модуль доставляется в течение 1–2 календарных дней после заключения соглашения.
Персонализация. Доступна добавление дополнительной теплоизоляции, электрики или воздухообмена.
Сферы использования
На строительных объектах для организации склада или устройства комнаты для рабочих.
Во время праздников для организации стойки приёма или помещения для инвентаря.
В качестве временных рабочих зон или пунктов управления.
Достоинства
Оптимизация времени. Отпадает потребность возводить временные сооружения.
Удобство. Среда, которые улучшают эффективность работы работников.
Адаптивность. Возможность временного использования или приобретения под конкретные требования и финансовые возможности.
Случай применения
Подрядчик задействовала передвижной модуль для размещения оборудования и помещения для персонала. Объект была доставлена на место за день, с дополнительным утеплением. Заказчик обратил внимание на повышение комфорта и отсутствие простоев.
Как связаться с нами
Для подачи заявки нужно написать с нами. Дадим подробную информацию, окажем помощь найти правильный путь и обеспечим доставку.
dang nh?p alo789: alo789 dang nh?p – alo789
Купить документ ВУЗа вы имеете возможность у нас. diplom4you.com/kupit-diplom-volgograd-4-2
1вин про http://www.1win827.ru .
jocuri de noroc online moldova https://1win5003.ru .
Строительные бытовки
Вагончики и передвижные помещения: надёжное вариант для пользовательских целей
Бытовки и блок-контейнеры способствуют оборудовать производственную площадку, помещение для хранения или временную постройку. Мы предлагаем объекты, которые удовлетворяют профессиональным нормам надёжности и комфорта.
Особенности
Прочность. Все бытовки созданы из материалов, устойчивых к воздействию и климатическим факторам.
Скорость доставки. Модуль доставляется на место в срок 1–2 календарных дней после подтверждения заявки.
Индивидуальная адаптация. Доступна установка утепления, электрооборудования или воздухообмена.
Сферы использования
На строительных объектах для размещения оборудования или создания зоны отдыха.
Во время событий для создания информационного центра или помещения для инвентаря.
В качестве временных рабочих зон или управляющих центров.
Плюсы
Оптимизация времени. Не требуется строить временные помещения.
Удобство. Среда, которые увеличивают результативность действий бригады.
Адаптивность. Опция проката или приобретения под любой срок и бюджет.
Случай применения
Строительная компания применила временную конструкцию для размещения оборудования и комнаты отдыха. Модуль была доставлена за 24 часа, с улучшенной термоизоляцией. Клиент отметил на повышение комфорта и отсутствие простоев.
Как сделать заказ
Для начала сотрудничества следует обратиться с нами. Дадим всю необходимую информацию, окажем помощь выбрать оптимальное решение и проведём доставку.
скачать мостбет официальный сайт http://mostbet786.ru .
https://k8viet.guru/# k8 bet
188bet 88bet 88 bet 88 bet
There’s definately a lot to know about this subject. I love all of the points you’ve made.
We install cooling units from leading brand names like Fujitsu, Daikin, Mitsubishi, Panasonic
and Toshiba.
https://alo789.auction/# alo789 chinh th?c
After checking out a number of the articles on your blog, I honestly appreciate your technique of blogging. I added it to my bookmark website list and will be checking back in the near future. Please visit my web site as well and let me know what you think.
Your article helped me a lot, is there any more related content? Thanks!
Hi there! This post could not be written any better! Looking at this post reminds me of my previous roommate! He always kept preaching about this. I will send this article to him. Pretty sure he will have a good read. Thank you for sharing!
IndiaMedFast: online medicine shopping in india – cheapest online pharmacy india
http://interpharmonline.com/# canada ed drugs
northern pharmacy canada
You are so interesting! I do not think I’ve truly read a single thing like this before. So nice to discover somebody with some original thoughts on this subject matter. Really.. thank you for starting this up. This web site is something that is required on the internet, someone with a little originality.
https://travlya-tarakanov-msk.ru/
legitimate canadian pharmacies online canadian pharmacy no prescription onlinecanadianpharmacy 24
вулкан казино
https://indiamedfast.shop/# India Med Fast
canadian king pharmacy
reliable mexican pharmacies: reliable mexican pharmacies – MexicanPharmInter
MexicanPharmInter: buying from online mexican pharmacy – mexican pharmacy online store
Generally I do not learn article onn blogs, but I would like to say that this write-up very forced mee to take a look at and do so!
Your wriiting taste hass been amazaed me. Thank you, quite great post. https://buy-biology-Essay.com
Современная и функциональная кухня? “Эталон Кухни” знают, как это сделать! 8(843)258-86-66 https://yandex.ru/maps/org/etalon_kukhni/1146748982/
1win войти http://1win6011.ru .
1win com 1win813.ru .
my blog: https://cryptolake.online/crypto2
This blog was… how do you say it? Relevant!! Finally I’ve found something that helped me. Kudos!
iphone pro buy iphone 13 max
mostbet официальный сайт mostbet официальный сайт .
мтс подключить
https://dlya-nas.com/employer/24inetrnet-domashnij-ekb/
сайт мтс екатеринбург
Way cool! Some extremely valid points! I appreciate you penning this article plus the rest of the website is very good.
The portable systems usually can not be made
use of to warm since the trendy air can not
be ducted out.
iphone 8 iphone 128gb
кайт школа хургада
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://www.binance.com/pl/register?ref=YY80CKRN
https://interpharmonline.com/# canada drugs reviews
1-win 1win6011.ru .
1 win казино https://www.1win813.ru .
https://indiamedfast.shop/# cheapest online pharmacy india
canadian drugs
1win официальный сайт вход https://pboarders.borda.ru/?1-11-0-00000929-000-0-0-1742818701/ .
Boost your car’s output and design with our first-rate tuning assistance. Reveal the actual potential of your ride through bespoke improvements. Our professionals of professionals offers peerless superiority and ingenuity. See our online presence https://precisionautobodyfrederick.com/ to understand additional, and begin your path towards auto distinction today.
mosbet [url=https://www.shorts.borda.ru/?1-18-0-00000397-000-0-0]mosbet[/url] .
мостбет казино войти https://mostbet794.ru .
After looking over a handful of the articles on your site, I truly like your technique of writing a blog. I added it to my bookmark website list and will be checking back in the near future. Please visit my website too and let me know how you feel.
mexican drug stores online: mexican drug stores online – mexican pharmacy online order
Для удачного продвижения по карьерной лестнице требуется наличие диплома института. Приобрести диплом любого ВУЗа у проверенной компании: diplom-zentr.com/kupit-diplom-o-visshem-obrazovanii-v-samare-legko/
buying prescription drugs from india: IndiaMedFast – cheapest online pharmacy india
buying drugs from canada fda approved canadian online pharmacies canadian pharmacy
zooma casino вход
один вин официальный сайт https://www.pboarders.borda.ru/?1-11-0-00000929-000-0-0-1742818701 .
I used to be able to find good advice from your content.
мостбет мобильная версия скачать мостбет мобильная версия скачать .
Надёжные МФО предлагают оформление займа без проверок и лишней бюрократии. Вы можете получить до 100 000 рублей онлайн — быстро и удобно. Оставьте заявку и оформите займ без отказа прямо сейчас, не выходя из дома.
Right here is the perfect site for anyone who wants to understand this topic. You understand a whole lot its almost hard to argue with you (not that I really will need to…HaHa). You certainly put a brand new spin on a subject which has been discussed for ages. Great stuff, just great.
https://indiamedfast.com/# IndiaMedFast.com
https://mexicanpharminter.shop/# Mexican Pharm Inter
canadian pharmacies that deliver to the us
Где приобрести диплом специалиста?
Мы предлагаем быстро заказать диплом, который выполняется на оригинальной бумаге и заверен мокрыми печатями, водяными знаками, подписями. Диплом способен пройти лубую проверку, даже при помощи профессиональных приборов. Достигайте своих целей быстро и просто с нашим сервисом.
Заказать диплом любого университета freediplom.com/kupit-diplom-v-irkutske-10/
Вагончики и модульные здания: эффективное подход для личных проблем
Вагончики и временные конструкции организовывают организовать место для деятельности, хранилище или временный домик. Наша компания гарантируем конструкции, которые подходят строгим требованиям надёжности и удобства.
Особенности
Стойкость. Все вагончики изготовлены из материалов, прочных к воздействию и погодным условиям.
Быстрая поставка. Конструкция перевозится в срок 1–2 рабочих дней после оформления заказа.
Гибкая настройка. Возможна установка дополнительной теплоизоляции, электрики или воздухообмена.
Где применяются
На стройплощадках для размещения оборудования или создания зоны отдыха.
Во время акций для организации стойки приёма или склада оборудования.
В качестве временно используемых помещений или операционных штабов.
Достоинства
Оптимизация времени. Не требуется возводить временные сооружения.
Функциональность. Обстановка, которые усиливают производительность труда сотрудников.
Подстройка. Возможность аренды или постоянного владения под индивидуальные нужды и ресурсы.
Пример использования
Фирма-застройщик применила передвижной модуль для создания хранилища и места для рабочих. Объект была доставлена за один день, с усиленной теплоизоляцией. Партнёр выделил на улучшение обстановки и ликвидацию простоев.
Как сделать заказ
Для начала сотрудничества следует обратиться с нами. Выделим исчерпывающие сведения, поможем найти идеальный выбор и организуем доставку.
Приобрести диплом любого университета!
Мы предлагаем документы институтов, которые расположены на территории всей России.
kupit-diplom24.com/kupit-attestat-ob-obrazovanii-9-klassov-3
Мы изготавливаем дипломы психологов, юристов, экономистов и других профессий по приятным тарифам. Цена зависит от выбранной специальности, года получения и образовательного учреждения. Всегда стараемся поддерживать для покупателей адекватную политику цен. Для нас очень важно, чтобы дипломы были доступными для большинства наших граждан. диплом учителя купить
Купить документ о получении высшего образования вы сможете у нас в столице. brandsafe-test.net/?p=301#comment-3685
reliable mexican pharmacies: buying from online mexican pharmacy – buying from online mexican pharmacy
Модули и модульные здания: проверенное способ для личных нужд
Вагончики и временные конструкции организовывают организовать место для деятельности, хранилище или временное помещение. Мы предлагаем здания, которые удовлетворяют высоким стандартам качества и эргономики.
Особенности
Стойкость. Каждая модули выполнены из ресурсов, прочных к давлению и природным явлениям.
Скорость доставки. Конструкция транспортируется в пределах 1–2 рабочих дней после подписания договора.
Индивидуальная адаптация. Осуществляется добавление термоизоляции, электрооборудования или системы проветривания.
Зоны действия
На объектах строительства для размещения оборудования или устройства комнаты для рабочих.
Во время праздников для размещения зоны регистрации или хранилища техники.
В качестве временных офисов или пунктов управления.
Достоинства
Оптимизация времени. Отпадает потребность возводить временные сооружения.
Комфорт. Атмосфера, которые улучшают качество выполнения задач персонала.
Гибкость. Шанс аренды или долгосрочного использования под любой срок и денежные средства.
Случай применения
Строительный подряд применила модульное здание для размещения оборудования и зоны отдыха. Конструкция была доставлена на место за 24 часа, с дополнительным утеплением. Партнёр подчеркнул на повышение комфорта и сокращение простоя.
Как сделать заказ
Для оформления заказа необходимо связаться с нами. Обеспечим подробную информацию, содействуем выбрать оптимальное решение и проведём транспортировку.
buying prescription drugs from india: IndiaMedFast.com – cheapest online pharmacy india
Great site you have here.. It’s hard to find good quality writing like yours these days. I truly appreciate individuals like you! Take care!!
«Окна Мастер» – это производство пластиковых окон в Санкт-Петербурге с акцентом на качество. Мы используем только лучшие оконные профили, тщательно контролируем каждый этап изготовления и предлагаем решения, рассчитанные на долгие годы эксплуатации.
We cover installation, maintenance and fixing your new air conditioning whenever it calls for
some fine-tuning.
Заказать документ о получении высшего образования можно в нашем сервисе. [url=http://pcsoftsecurity.com/bitdefender-crack-full-download/#comment-6678/]pcsoftsecurity.com/bitdefender-crack-full-download/#comment-6678[/url]
If you are charged per hour, then duration is very pertinent to the price.
Заказать диплом любого университета!
Мы можем предложить документы университетов, расположенных в любом регионе РФ.
diplomist.com/kupit-attestati-za-11-klass-nedorogo-3
We are your one-stop shop when it comes to creating comfortable atmospheres in your static home.
https://interpharmonline.shop/# onlinecanadianpharmacy
best canadian online pharmacy reviews
Looking for the best Telegram channels? Our service helps you discover popular and niche channels, find interesting content, and stay updated with the latest trends. Click the link and explore the world of Telegram: Telegram channels by topic
https://interpharmonline.shop/# onlinecanadianpharmacy
IndiaMedFast.com IndiaMedFast india online pharmacy store
buying from online mexican pharmacy: Mexican Pharm Inter – buying from online mexican pharmacy
aquasculpt is an advanced dietary supplement designed to support your weight management journey by optimizing mitochondrial efficiency and enhancing metabolic performance.
«Фабрика остекления» — это компания, которая занимается остеклением любых объектов в Санкт-Петербурге. Мы предлагаем пластиковые окна, которые помогают сохранить тепло и защищают от внешних факторов. Мы гарантируем высокое качество продукции и монтажа.
1win регистрация 1win регистрация .
1win 1win814.ru .
ваучер 1win https://1win6012.ru/ .
мостбет скачать tagilshops.forum24.ru/?1-4-0-00000205-000-0-0 .
мостбет скачать бесплатно https://mostbet795.ru/ .
Купить диплом ВУЗа по доступной стоимости возможно, обратившись к надежной специализированной фирме. Мы оказываем услуги по изготовлению и продаже документов об окончании любых университетов Российской Федерации. Приобрести диплом о высшем образовании– diploma-groups24.ru/kupit-diplom-o-srednem-obrazovanii/uchilishha-ptu/1994-2006-goda.html
1win вход https://boardwars.forum24.ru/?1-10-0-00000406-000-0-0 .
кайтсёрфинг в станице благовещенской
1win официальный сайт http://1win6012.ru .
ванвин https://www.1win814.ru .
mostbet kg https://www.tagilshops.forum24.ru/?1-4-0-00000205-000-0-0 .
https://interpharmonline.shop/# canadian mail order pharmacy
best mail order pharmacy canada
https://interpharmonline.shop/# canadian pharmacy meds
мотбет https://mostbet795.ru/ .
If you leave the unit competing 24-hour that will certainly
equate to about ₤ 4.
We usually build chilly rooms from fire ranked PIR wall and ceiling panels.
mexican pharmacy online store: mexican pharmacy online store – Mexican Pharm Inter
Заказать диплом любого университета!
Мы готовы предложить дипломы любых профессий по разумным ценам— diplomnie.com/kupit-diplom-vracha-po-lechebnomu-delu-vigodno/
Мы можем предложить дипломы любых профессий по приятным ценам. Всегда стараемся поддерживать для заказчиков адекватную ценовую политику. Для нас очень важно, чтобы документы были доступны для большого количества наших граждан.
Заказ документа, который подтверждает обучение в ВУЗе, – это рациональное решение. Приобрести диплом о высшем образовании: okdiplom.ru/kupit-diplom-texnikuma-ob-okonchanii/
Где заказать диплом по нужной специальности?
Мы предлагаем выгодно купить диплом, который выполнен на оригинальном бланке и заверен мокрыми печатями, штампами, подписями официальных лиц. Данный документ способен пройти любые проверки, даже с применением специального оборудования. Достигайте своих целей быстро и просто с нашей компанией. Заказать диплом любого университета! angelandmax.teamforum.ru/viewtopic.php?f=2&t=57331
MexicanPharmInter reliable mexican pharmacies mexican pharmacy online store
http://interpharmonline.com/# canada rx pharmacy world
canadian pharmacy ed medications
https://indiamedfast.com/# India Med Fast
https://tur-kazan.ru/
Howdy! This article could not be written much better! Looking at this post reminds me of my previous roommate! He always kept talking about this. I most certainly will send this information to him. Fairly certain he’ll have a great read. Many thanks for sharing!
оценка недвижимости для ипотеки в сбербанке https://ocenka-zagorod.ru
Бонги
оценка участка для сбербанка https://ocenka-zagorod.ru
типография блокнот на заказ типография постеры цены
типографии спб печать https://mir-poligrafiya.ru
типография онлайн заказ типография официальный
типография а4 цена типография где спб
trustworthy canadian pharmacy: Pharmacies in Canada that ship to the US – canadian drugs pharmacy
Свежие новости на данный момент: важная информация глобального масштаба. Читайте аналитику экспертов на нашем сайте. Подпишитесь на ежедневную рассылку, чтобы быть в курсе главные происшествия. Актуальные данные из проверенных источников – ваш партнёр в мире информации 24/7
переговоры о мире
win 1 https://1win815.ru/ .
1 win.com 1 win.com .
mostbet игры https://www.kharkovbynight.forum24.ru/?1-15-0-00003047-000-0-0-1742814422 .
1win кейсы 1win кейсы .
мостбет скачать андроид https://mostbet6001.ru .
buying prescription drugs from india: IndiaMedFast.com – india pharmacy without prescription
Нев Ретро Казино [url=http://newretromirror.ru]http://newretromirror.ru[/url] .
грузчики заказать грузчики недорогие
услуги грузчиков дешево грузчик нанять
грузчик нанять услуги грузчиков заказать
Столы квадратные для школы
Стулья пластиковые для школы
нанять грузчиков недорого грузоперевозки услуги грузчиков
грузчики нанять грузчик услуга
грузчики заказать грузчики недорого
Официальный сайт New Retro Casino newretromirror.ru .
1win зайти http://www.1win815.ru .
1win букмекер 1win6014.ru .
aviator mostbet aviator mostbet .
1 vin https://yamama.forum24.ru/?1-11-0-00000459-000-0-0-1742818616/ .
мостбет кыргызстан скачать mostbet6001.ru .
https://mexicanpharminter.com/# mexican drug stores online
canadian world pharmacy
https://mexicanpharminter.shop/# mexican pharmacy online store
I like it when folks get together and share thoughts. Great blog, continue the good work!
кредит под птс екатеринбург
avtolombard-11.ru/ekb.html
взять кредит под птс
Вагончики и модульные здания: проверенное решение для пользовательских нужд
Вагончики и модульные здания позволяют создать зону работы, хранилище или временный домик. Наши специалисты предлагаем конструкции, которые соответствуют профессиональным нормам безопасности и функциональности.
Параметры
Надёжность. Данные вагончики созданы из ресурсов, стойких к воздействию и погодным условиям.
Оперативность транспортировки. Объект перевозится в рамках 1–2 суток после заключения соглашения.
Персонализация. Возможна установка защиты от холода, электропроводки или вентиляции.
Зоны действия
На объектах строительства для размещения оборудования или устройства комнаты для рабочих.
Во время мероприятий для организации стойки приёма или помещения для инвентаря.
В качестве офисных модулей или пунктов управления.
Преимущества
Ускорение процессов. Не требуется обустраивать временные здания.
Комфортабельность. Среда, которые увеличивают эффективность работы персонала.
Адаптивность. Возможность аренды или приобретения под разные периоды и денежные средства.
Случай применения
Подрядчик задействовала передвижной модуль для организации склада инструментов и места для рабочих. Конструкция была транспортирована за один день, с дополнительным утеплением. Партнёр подчеркнул на улучшение условий работы и отсутствие простоев.
Как связаться с нами
Для начала сотрудничества следует позвонить с нами. Выделим полные данные, поддержим подобрать оптимальное решение и обеспечим поставку.
aquasculpt is a dietary supplement uniquely designed to promote healthy weight management and boost metabolic performance.
Glory Casino Spribe
Строительные бытовки
Модули и модульные здания: проверенное подход для ваших нужд
Контейнеры и передвижные помещения способствуют организовать место для деятельности, кладовую или временный модуль. Наши специалисты обеспечиваем здания, которые удовлетворяют строгим требованиям долговечности и удобства.
Особенности
Устойчивость. Данные модули выполнены из ресурсов, прочных к нагрузкам и внешним воздействиям.
Быстрая поставка. Модуль доставляется на место в срок 1–2 календарных дней после заключения соглашения.
Гибкая настройка. Реализуется монтаж термоизоляции, электрики или вентиляции.
Зоны действия
На строительных объектах для размещения оборудования или устройства комнаты для рабочих.
Во время событий для организации стойки приёма или хранилища техники.
В качестве временных рабочих зон или пунктов управления.
Плюсы
Экономия времени. Не нужно обустраивать временные здания.
Удобство. Среда, которые повышают производительность труда бригады.
Гибкость. Возможность краткосрочного пользования или покупки под любой срок и ресурсы.
Практический пример
Подрядчик внедрила передвижной модуль для организации склада инструментов и места для рабочих. Объект была привезена за сутки, с специальным утеплением. Клиент обратил внимание на оптимизацию среды и минимизацию задержек.
Как начать сотрудничество
Для подачи заявки нужно написать с нами. Дадим подробную информацию, окажем помощь подобрать лучший вариант и проведём поставку.
cheap canadian pharmacy InterPharmOnline.com canadian pharmacies online
That is a good tip particularly to those new to the blogosphere. Short but very accurate info… Thanks for sharing this one. A must read article!
mexican pharmacy online store: Mexican Pharm Inter – Mexican Pharm Inter
legit canadian online pharmacy: fda approved canadian online pharmacies – canadianpharmacyworld com
I’d like to thank you for the efforts you’ve put in penning this site. I am hoping to check out the same high-grade content from you in the future as well. In truth, your creative writing abilities has inspired me to get my own blog now 😉
https://mexicanpharminter.com/# mexican pharmacy online
safe canadian pharmacies
https://indiamedfast.com/# lowest prescription prices online india
один вин http://1win816.ru .
1-win 1win6015.ru .
mostbets https://maksipolinovtsu.forum24.ru/?1-1-0-00000194-000-0-0-1742815870/ .
1win win mymoscow.forum24.ru/?1-6-0-00026928-000-0-0 .
mostbet kg отзывы http://www.mostbet6002.ru .
сайт аккаунтов социальной сети онлайн магазин аккаунтов
It’s difficult to find educated people in this particular subject, however, you sound like you know what you’re talking about! Thanks
цифровой магазин аккаунтов купить аккаунт на бирже
https://vodkacoin.online/
So you have actually chosen to buy domestic air conditioning,
congratulations!
Продажа путёвок https://camp-centr.com/camps/type/yazykovoy.html. Спортивные, творческие и тематические смены. Весёлый и безопасный отдых под присмотром педагогов и аниматоров. Бронируйте онлайн!
офсетная печать визиток типография печать визиток
Read football news here! https://footballbritian.uk/
кредит под залог машины
avtolombard-11.ru/kazan.html
автоломбард казань
Продажа путёвок детский лагерь путевки 2025 году. Спортивные, творческие и тематические смены. Весёлый и безопасный отдых под присмотром педагогов и аниматоров. Бронируйте онлайн!
печать визиток онлайн https://tipografiya-pechat-vizitok.ru
one win http://1win816.ru .
зайти в 1вин http://1win6015.ru .
мостбет chrono мостбет chrono .
1 вин про http://mymoscow.forum24.ru/?1-6-0-00026928-000-0-0/ .
pharmacy technician online training Access medicine details. Pill facts provided.
мостбет зеркало http://mostbet6002.ru .
https://tadalafileasybuy.shop/# TadalafilEasyBuy.com
https://generic100mgeasy.com/# Generic 100mg Easy
kamagra 100mg kopen: Kamagra Kopen Online – Kamagra Kopen Online
Officiele Kamagra van Nederland: kamagra kopen nederland – kamagra 100mg kopen
вентиляции кухни кафе
Very good information. Lucky me I came across your blog by accident (stumbleupon). I’ve saved as a favorite for later!
кредит под залог птс кемерово
avtolombard-11.ru/kemerovo.html
автоломбард в кемерово под залог
Generic 100mg Easy Order Viagra 50 mg online cheap viagra
prodentim a groundbreaking probiotic supplement uniquely designed to support oral health and promote robust gums and teeth.
Today, I went to the beach with my kids. I found a sea shell and gave it to my 4 year old daughter and said “You can hear the ocean if you put this to your ear.” She put the shell to her ear and screamed. There was a hermit crab inside and it pinched her ear. She never wants to go back! LoL I know this is entirely off topic but I had to tell someone!
вход lee bet
Выполняем качественное https://energopto.ru под ключ. Энергоэффективные решения для домов, офисов, промышленных объектов. Гарантия, соблюдение СНиП и точные сроки!
Выполняем качественное проектирование итп под ключ. Энергоэффективные решения для домов, офисов, промышленных объектов. Гарантия, соблюдение СНиП и точные сроки!
http://tadalafileasybuy.com/# cialis for sale
Самые красивые девушки не только привлекают взгляды, но и умело создают атмосферу комфорта и доверия. Знакомства с такими дамами — это всегда интересный опыт, ведь за красивыми глазами скрываются ум и обаяние, которые делают общение захватывающим https://t.me/devki_spb1
изготовление печати бланков печать бланков писем
https://kamagrakopen.pro/# kamagra jelly kopen
печать бумажных папок печать папок
изготовление печати бланков pechat-blankov-spb.ru
деньги под залог автомобиля
avtolombard-11.ru
автоломбард москва
печать папок спб печать папок с логотипом
cialis without a doctor prescription: TadalafilEasyBuy.com – Tadalafil Easy Buy
I blog often and I truly thank you for your information. Your article has really peaked my interest. I’m going to bookmark your blog and keep checking for new details about once per week. I opted in for your Feed too.
регистрация Vega Casino
aquasculpt a groundbreaking probiotic supplement uniquely designed to support oral health and promote robust gums and teeth.
Generic100mgEasy: Generic 100mg Easy – Generic100mgEasy
печать на холсте недорого типография печать на холсте
1win официальный сайт скачать https://www.1win817.ru .
uf dtf печать dtf печать стоимость
1win на телефон [url=http://dogzz.forum24.ru/?1-10-0-00000155-000-0-0-1742818537/]http://dogzz.forum24.ru/?1-10-0-00000155-000-0-0-1742818537/[/url] .
услуги широкоформатной печати https://shirokoformatnaya-pechat-spb.ru
Pretty! This was a really wonderful post. Thank you for supplying this information.
leebet casino
mostbet официальный сайт http://www.corgan.borda.ru/?1-0-0-00000265-000-0-0 .
типография печать на холсте печать фото на холсте цена
печать dtf наклеек на заказ dtf печать на текстиле
широкоформатная печать наклеек широкоформатная печать заказать
мостюет http://mostbet6003.ru .
Nice post. I learn something new and challenging on websites I stumbleupon on a daily basis. It will always be useful to read articles from other writers and practice a little something from other websites.
кредит наличными под залог птс
avtolombard-11.ru/nsk.html
где взять кредит под залог авто
Где заказать диплом по нужной специальности?
Наши специалисты предлагают выгодно и быстро приобрести диплом, который выполняется на бланке ГОЗНАКа и заверен печатями, штампами, подписями. Документ способен пройти любые проверки, даже при помощи профессиональных приборов. Достигайте цели быстро и просто с нашей компанией. Заказать диплом о высшем образовании! mymotospeed.ru/gotovyiy-diplom-uzhe-cherez-neskolko-dney
1block bet
1Block Casino: Full Platform Overview
1Block Casino is a modern gaming platform that offers a wide range of gambling entertainment for players worldwide. From classic slots to unique games like Plinko, the service provides everything needed for gambling enthusiasts. Let’s take a closer look at the main features of the platform, game categories, and key advantages.
Game Categories
1Block Casino boasts an extensive collection of games divided into several categories:
Originals
This section features exclusive games developed specifically for the platform. It’s a great choice for those seeking a unique gaming experience.
Slots
Classic and modern slots with various themes, bonuses, and mechanics are available here. Whether you prefer traditional fruit machines or innovative video slots, there’s something for everyone.
Live Games
Immerse yourself in the atmosphere of a real casino with live dealer games. These games are streamed in real-time, offering an authentic experience with professional dealers.
Fishing Games
A unique category that combines gambling with interactive gameplay. Fishing games are gaining popularity due to their engaging mechanics and potential for big wins.
Poker
Test your skills against other players in various poker formats. The platform offers both traditional and fast-paced poker games.
Esports Betting
Bet on your favorite esports teams and tournaments. This section caters to fans of competitive gaming who want to add excitement to their matches.
Lucky Bets and High Rollers
1Block Casino caters to all types of players, from casual gamers to high rollers. The Lucky Bets section highlights random wins, while the High Rollers section showcases impressive payouts from large bets. Whether you’re betting small or large amounts, the platform ensures fair play and exciting opportunities.
Our Community and Partnerships
1Block Casino values its community and collaborates with trusted partners to enhance the gaming experience. The platform proudly works with leading providers, ensuring top-quality games and services for its users.
Legal Information
1Block Casino is owned and operated by JogoMaster Limited, a company registered under number 15748. The company’s registered address is located in Hamchako, Mutsamudu, Autonomous Island of Anjouan, Union of Comoros.
The platform is licensed and regulated by the Gaming Board of Anjouan (License No. ALSI-152406032-FI3). 1Block has passed all regulatory compliance checks and is legally authorized to conduct gaming operations for all games of chance and wagering.
Why Choose 1Block Casino?
Diverse Game Selection : From slots to live games, there’s something for every type of player.
Transparency : All bets and payouts are clearly displayed, ensuring trust and fairness.
Crypto-Friendly : The platform supports cryptocurrency transactions, making it convenient for modern players.
Licensed and Regulated : With a valid license from the Gaming Board of Anjouan, players can enjoy a secure and legal gaming experience.
Whether you’re a fan of classic casino games or looking to explore unique options like Plinko, 1Block Casino offers a comprehensive and enjoyable platform for all gambling enthusiasts.
https://kamagrakopen.pro/# kamagra pillen kopen
1win войти 1win817.ru .
1 win. dogzz.forum24.ru/?1-10-0-00000155-000-0-0-1742818537 .
mostbet kg mostbet kg .
cialis without a doctor prescription cialis for sale TadalafilEasyBuy.com
casino champion официальный сайт
http://tadalafileasybuy.com/# cialis without a doctor prescription
1block casino
1Block Casino: Full Platform Overview
1Block Casino is a modern gaming platform that offers a wide range of gambling entertainment for players worldwide. From classic slots to unique games like Plinko, the service provides everything needed for gambling enthusiasts. Let’s take a closer look at the main features of the platform, game categories, and key advantages.
Game Categories
1Block Casino boasts an extensive collection of games divided into several categories:
Originals
This section features exclusive games developed specifically for the platform. It’s a great choice for those seeking a unique gaming experience.
Slots
Classic and modern slots with various themes, bonuses, and mechanics are available here. Whether you prefer traditional fruit machines or innovative video slots, there’s something for everyone.
Live Games
Immerse yourself in the atmosphere of a real casino with live dealer games. These games are streamed in real-time, offering an authentic experience with professional dealers.
Fishing Games
A unique category that combines gambling with interactive gameplay. Fishing games are gaining popularity due to their engaging mechanics and potential for big wins.
Poker
Test your skills against other players in various poker formats. The platform offers both traditional and fast-paced poker games.
Esports Betting
Bet on your favorite esports teams and tournaments. This section caters to fans of competitive gaming who want to add excitement to their matches.
Lucky Bets and High Rollers
1Block Casino caters to all types of players, from casual gamers to high rollers. The Lucky Bets section highlights random wins, while the High Rollers section showcases impressive payouts from large bets. Whether you’re betting small or large amounts, the platform ensures fair play and exciting opportunities.
Our Community and Partnerships
1Block Casino values its community and collaborates with trusted partners to enhance the gaming experience. The platform proudly works with leading providers, ensuring top-quality games and services for its users.
Legal Information
1Block Casino is owned and operated by JogoMaster Limited, a company registered under number 15748. The company’s registered address is located in Hamchako, Mutsamudu, Autonomous Island of Anjouan, Union of Comoros.
The platform is licensed and regulated by the Gaming Board of Anjouan (License No. ALSI-152406032-FI3). 1Block has passed all regulatory compliance checks and is legally authorized to conduct gaming operations for all games of chance and wagering.
Why Choose 1Block Casino?
Diverse Game Selection : From slots to live games, there’s something for every type of player.
Transparency : All bets and payouts are clearly displayed, ensuring trust and fairness.
Crypto-Friendly : The platform supports cryptocurrency transactions, making it convenient for modern players.
Licensed and Regulated : With a valid license from the Gaming Board of Anjouan, players can enjoy a secure and legal gaming experience.
Whether you’re a fan of classic casino games or looking to explore unique options like Plinko, 1Block Casino offers a comprehensive and enjoyable platform for all gambling enthusiasts.
Generic 100mg Easy: Viagra online price – Generic100mgEasy
скачат мостбет [url=https://www.mostbet6003.ru]https://www.mostbet6003.ru[/url] .
кредит залог птс наличные
https://kennetjobs.com/companies/zaim-pod-zalog-pts-11671/
кредит под залог машины
заключить контракт на военную службу Процесс поступления на военную службу по контракту начинается с изъявления гражданином желания заключить соответствующий контракт. Это может быть как первичное поступление на службу, так и перезаключение контракта после окончания предыдущего. Основным документом, регулирующим данный процесс, является Федеральный закон “О воинской обязанности и военной службе”. Для заключения контракта необходимо обратиться в военный комиссариат по месту жительства или в пункт отбора на военную службу по контракту. Там гражданин получит подробную консультацию о требованиях, предъявляемых к кандидатам, и перечне необходимых документов. Важно учитывать, что к кандидатам предъявляются определенные требования по возрасту, образованию, состоянию здоровья и физической подготовке.
I was able to find good advice from your blog posts.
кайт египет
buy cialis pill: TadalafilEasyBuy.com – Tadalafil Easy Buy
Если ваш интернет-провайдер заблокировал доступ к казино, не беспокойтесь – зеркало Kent Casino поможет вам без проблем войти в аккаунт, продолжить игру и насладиться всеми привилегиями платформы: Кент казино официальный сайт
Spot on with this write-up, I seriously believe that this amazing site needs much more attention. I’ll probably be returning to read through more, thanks for the information.
Маркетинговое бюро оказывает премиальные услуги в регионе по техподдержке и продвижению корпоративного портала группой сертифицированных экспертов с 2010 года. Флагманское услуга нашей студии — https://www.obsluzhivanie-sajta.ru/ с фиксированной ежемесячной регулярной ценой. Запустим техподдержку, аудит безопасности, интеграцию CRM, ускорение загрузки и круглосуточную доступность платформы.
Реализуем: кросс-браузерную совместимость, настройку API, оптимизацию Core Web Vitals, регулярный аудит. Интегрируем популярные CMS для корпоративных сайтов: HostCMS, для интернет-магазинов: PrestaShop, для блогов и лендингов: WordPress, для SaaS-платформ: Strapi. Доступно 12+ индивидуальных пакетов с транспарентными расценками.
glycofortin is a uniquely crafted liquid dietary supplement designed to aid in maintaining balanced blood sugar levels.
https://kamagrakopen.pro/# Kamagra
адин вин http://www.1win6016.ru .
http://tadalafileasybuy.com/# TadalafilEasyBuy.com
What’s up to all, the contents existing at this web page are in fact remarkable for people knowledge, well, keep up the nice work fellows.
Vega Casino официальный сайт
мостбет скачать бесплатно http://mostbet789.ru .
is a carefully developed dietary supplement designed to naturally support individuals dealing with sciatic nerve discomfort while promoting overall nerve wellness.
кредит в залог машины
https://jobseeker.charisonecare.co.uk/employer/andonovproltd8758/
оформить кредит под залог авто
aquasculpt is a groundbreaking weight management supplement designed to support your journey by naturally enhancing metabolism, curbing hunger, and boosting energy levels.
mostbet casino https://www.ashapiter0.forum24.ru/?1-19-0-00001444-000-0-0-1742819001 .
1вин войти http://zdorovie.forum24.ru/?1-7-0-00000231-000-0-0-1742818050/ .
TadalafilEasyBuy.com: TadalafilEasyBuy.com – Tadalafil Tablet
1 win kg https://1win6016.ru .
buy generic 100mg viagra online: Cheap Sildenafil 100mg – Generic100mgEasy
It’s nearly impossible to find educated people for this topic, but you seem like you know what you’re talking about! Thanks
мостбет скачать бесплатно https://www.mostbet789.ru .
мостбет мобильная версия скачать https://ashapiter0.forum24.ru/?1-19-0-00001444-000-0-0-1742819001 .
1 вин вход http://zdorovie.forum24.ru/?1-7-0-00000231-000-0-0-1742818050 .
Kamagra Kopen Kamagra Kopen Online Kamagra Kopen Online
автоломбард залог машины
https://thenexarc.com/employer/avtolombard-11536
автоломбард под птс
порно порно .
Юридические услуги https://urwork.ru в Санкт-Петербурге и Москве – от консультации до защиты интересов в суде. Оперативно, надежно и с гарантией конфиденциальности.
водка казино водка казино .
1win зайти https://www.1win6017.ru .
Юридические услуги http://www.urwork.ru в Санкт-Петербурге и Москве – от консультации до защиты интересов в суде. Оперативно, надежно и с гарантией конфиденциальности.
порно порно .
https://kamagrakopen.pro/# kamagra kopen nederland
водка казино водка казино .
https://tadalafileasybuy.shop/# TadalafilEasyBuy.com
I must thank you for the efforts you have put in penning this site. I am hoping to view the same high-grade blog posts by you later on as well. In truth, your creative writing abilities has inspired me to get my very own website now 😉
Блог с актуальной новостной информацией о событиях в мире. Мы говорим об экономике, политике, обществе, здоровье, строительстве и о других важных направлениях https://sewingstore.ru/
1win бк http://1win6017.ru .
авто под залог
https://www.ladelaholdings.com/employer/talentsmine6010/
автоломбард под птс
Generic100mgEasy: buy generic 100mg viagra online – Generic 100mg Easy
Generic100mgEasy: Generic100mgEasy – Generic 100mg Easy
Enhance your individual car with our enhancement services. Alter your ride into a one-of-a-kind masterpiece. Our team of specialists is dedicated to supplying top-quality results that outdo your expectations. Whether you’re looking to enhance performance, revamp aesthetics, or integrate new features, we have the expertise to provide your vision to life. Visit our website at https://timbrellosautobody.com/ to find our solutions and book a consultation today.Let us support you design the auto of your dreams.
Good day very cool web site!! Man .. Excellent .. Wonderful .. I will bookmark your blog and take the feeds also? I am happy to search out a lot of useful information here in the post, we’d like work out more strategies on this regard, thank you for sharing. . . . . .
1xbet register promo code
kantor bola
продвижение сайта дешево заказать seo оптимизация дешево
https://tadalafileasybuy.com/# TadalafilEasyBuy.com
продвижение компании раскрутка сайта
поисковое продвижение сайта seo заказать seoveb-marketing.ru
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
поисковое продвижение сайта заказать заказать сео оптимизацию
раскрутка сайта сео заказать продвижение топ
kantorbola
seo оптимизация сайта заказать продвижение сайтов цены
Why people still make use of to read news papers when in this technological globe the whole thing is available on net?
https://www.ausleisure.com.au/ads/33592/?url=http://www.google.lt/url?q=https://edicionesdelau.com/articles/1win_promo_code_offer.html
залог под птс авто
https://feleempleo.es/employer/zaim-pod-zalog-pts-1977/
займ под птс
I want to to thank you for this fantastic read!! I definitely enjoyed every little bit of it. I have you bookmarked to check out new stuff you post…
https://generic100mgeasy.com/# buy generic 100mg viagra online
1win ru 1win9109.ru .
1win kg скачать 1win kg скачать .
1win прямой эфир http://knowledge.forum24.ru/?1-0-0-00000101-000-0-0-1742817704 .
скачать mostbet на телефон http://mostbet6004.ru .
1Block Casino: Full Platform Overview
1Block Casino is a modern gaming platform that offers a wide range of gambling entertainment for players worldwide. From classic slots to unique games like Plinko, the service provides everything needed for gambling enthusiasts. Let’s take a closer look at the main features of the platform, game categories, and key advantages.
Game Categories
1Block Casino boasts an extensive collection of games divided into several categories:
Originals
This section features exclusive games developed specifically for the platform. It’s a great choice for those seeking a unique gaming experience.
Slots
Classic and modern slots with various themes, bonuses, and mechanics are available here. Whether you prefer traditional fruit machines or innovative video slots, there’s something for everyone.
Live Games
Immerse yourself in the atmosphere of a real casino with live dealer games. These games are streamed in real-time, offering an authentic experience with professional dealers.
Fishing Games
A unique category that combines gambling with interactive gameplay. Fishing games are gaining popularity due to their engaging mechanics and potential for big wins.
Poker
Test your skills against other players in various poker formats. The platform offers both traditional and fast-paced poker games.
Esports Betting
Bet on your favorite esports teams and tournaments. This section caters to fans of competitive gaming who want to add excitement to their matches.
Lucky Bets and High Rollers
1Block Casino caters to all types of players, from casual gamers to high rollers. The Lucky Bets section highlights random wins, while the High Rollers section showcases impressive payouts from large bets. Whether you’re betting small or large amounts, the platform ensures fair play and exciting opportunities.
Our Community and Partnerships
1Block Casino values its community and collaborates with trusted partners to enhance the gaming experience. The platform proudly works with leading providers, ensuring top-quality games and services for its users.
Legal Information
1Block Casino is owned and operated by JogoMaster Limited, a company registered under number 15748. The company’s registered address is located in Hamchako, Mutsamudu, Autonomous Island of Anjouan, Union of Comoros.
The platform is licensed and regulated by the Gaming Board of Anjouan (License No. ALSI-152406032-FI3). 1Block has passed all regulatory compliance checks and is legally authorized to conduct gaming operations for all games of chance and wagering.
Why Choose 1Block Casino?
Diverse Game Selection : From slots to live games, there’s something for every type of player.
Transparency : All bets and payouts are clearly displayed, ensuring trust and fairness.
Crypto-Friendly : The platform supports cryptocurrency transactions, making it convenient for modern players.
Licensed and Regulated : With a valid license from the Gaming Board of Anjouan, players can enjoy a secure and legal gaming experience.
Whether you’re a fan of classic casino games or looking to explore unique options like Plinko, 1Block Casino offers a comprehensive and enjoyable platform for all gambling enthusiasts.
cialis without a doctor prescription: cialis without a doctor prescription – cialis without a doctor prescription
Оформление лицензий для любых видов деятельности с гарантированным результатом от экспертов, перейти на сайт https://www.fimfiction.net/user/840927/MDConsult
Generic100mgEasy buy generic 100mg viagra online buy generic 100mg viagra online
1Block Casino: Full Platform Overview
1Block Casino is a modern gaming platform that offers a wide range of gambling entertainment for players worldwide. From classic slots to unique games like Plinko, the service provides everything needed for gambling enthusiasts. Let’s take a closer look at the main features of the platform, game categories, and key advantages.
Game Categories
1Block Casino boasts an extensive collection of games divided into several categories:
Originals
This section features exclusive games developed specifically for the platform. It’s a great choice for those seeking a unique gaming experience.
Slots
Classic and modern slots with various themes, bonuses, and mechanics are available here. Whether you prefer traditional fruit machines or innovative video slots, there’s something for everyone.
Live Games
Immerse yourself in the atmosphere of a real casino with live dealer games. These games are streamed in real-time, offering an authentic experience with professional dealers.
Fishing Games
A unique category that combines gambling with interactive gameplay. Fishing games are gaining popularity due to their engaging mechanics and potential for big wins.
Poker
Test your skills against other players in various poker formats. The platform offers both traditional and fast-paced poker games.
Esports Betting
Bet on your favorite esports teams and tournaments. This section caters to fans of competitive gaming who want to add excitement to their matches.
Lucky Bets and High Rollers
1Block Casino caters to all types of players, from casual gamers to high rollers. The Lucky Bets section highlights random wins, while the High Rollers section showcases impressive payouts from large bets. Whether you’re betting small or large amounts, the platform ensures fair play and exciting opportunities.
Our Community and Partnerships
1Block Casino values its community and collaborates with trusted partners to enhance the gaming experience. The platform proudly works with leading providers, ensuring top-quality games and services for its users.
Legal Information
1Block Casino is owned and operated by JogoMaster Limited, a company registered under number 15748. The company’s registered address is located in Hamchako, Mutsamudu, Autonomous Island of Anjouan, Union of Comoros.
The platform is licensed and regulated by the Gaming Board of Anjouan (License No. ALSI-152406032-FI3). 1Block has passed all regulatory compliance checks and is legally authorized to conduct gaming operations for all games of chance and wagering.
Why Choose 1Block Casino?
Diverse Game Selection : From slots to live games, there’s something for every type of player.
Transparency : All bets and payouts are clearly displayed, ensuring trust and fairness.
Crypto-Friendly : The platform supports cryptocurrency transactions, making it convenient for modern players.
Licensed and Regulated : With a valid license from the Gaming Board of Anjouan, players can enjoy a secure and legal gaming experience.
Whether you’re a fan of classic casino games or looking to explore unique options like Plinko, 1Block Casino offers a comprehensive and enjoyable platform for all gambling enthusiasts.
раскрутка сайтов раскрутка сайта дешево
Kamagra Kopen: Kamagra Kopen – KamagraKopen.pro
сео раскрутка заказать продвижение и оптимизация сайтов
Выполняем проектирование https://energopto.ru и монтаж всех видов инженерных систем для жилых и коммерческих объектов. Профессиональный подход, сертифицированное оборудование, гарантия качества.
Планируете каникулы? купить детский лагерь путевки 2025 году! Интересные программы, безопасность, забота и яркие эмоции. Бронируйте заранее — количество мест ограничено!
1win ставки официальный сайт [url=1win6013.ru]1win6013.ru[/url] .
1win мобильная версия сайта 1win мобильная версия сайта .
1вин войти 1win9109.ru .
mostbet kg отзывы mostbet kg отзывы .
Откройте для себя мир ставок с 1xbet, присоединиться.
Добро пожаловать в мир ставок с 1xbet, в интернете.
Получите бонусы на первую ставку с 1xbet, не упустите возможность.
Ставьте на любимые виды спорта с 1xbet, получайте.
1xbet – ваш портал в мир лайв-ставок, сделайте каждую секунду важной.
1xbet – это огромное количество спортивных событий, выбирайте.
Обширные рынки на 1xbet, от футбола до тенниса.
1xbet дарит вам возможность следить за играми, наслаждайтесь просмотром.
Деньги на вашем счете с 1xbet за считанные минуты, не ждите.
Получите инсайдерскую информацию с 1xbet, поможем вам оставаться в курсе.
Ставьте с уверенностью на 1xbet, мы ценим вашу конфиденциальность.
Не пропустите акционные предложения от 1xbet, воспользуйтесь шансом.
Ставьте смело с 1xbet, выберите 1xbet для своей игры.
1xbet – поддержка, когда она нужна, никогда не оставайтесь в одиночестве.
Регулярные турниры и конкурсы на 1xbet, воспользуйтесь шансом.
Ставьте в любое время и в любом месте с 1xbet, всегда под рукой.
Дайте себе преимущества с 1xbet, анализируйте каждый шаг.
Зарегистрируйтесь на 1xbet всего за несколько минут, приступайте к ставкам.
Откройте новый уровень азартных игр с 1xbet, реализуйте свои мечты.
Не упустите уникальные возможности на 1xbet, развивайте свои навыки.
????? 1xbet ????? 1xbet .
Выполняем проектирование https://energopto.ru и монтаж всех видов инженерных систем для жилых и коммерческих объектов. Профессиональный подход, сертифицированное оборудование, гарантия качества.
Планируете каникулы? купить https://camp-centr.com! Интересные программы, безопасность, забота и яркие эмоции. Бронируйте заранее — количество мест ограничено!
https://logistt.ru/services/delivery/china/train
кредит под птс кемерово
https://emploi-securite.com/societes/sbstaffing-4all8841/
кредит наличными под залог автомобиля
пегас туристик официальный сайт Компания пегас является одним из лидеров рынка и работает в сфере международного туризма, предлагая выгодные туры в Таиланд, Турцию, Египет и другие страны мира. Подбор тура и заказ осуществляется в удобном личном кабинете, где можно забронировать отель, купить билеты и оформить путевку без переплат онлайн. Турфирма Pegas работает с проверенными отелями и предлагает широкий выбор направлений и услуг, включая авиабилеты, круизы, трансферы, путевки и подбор лучших отелей для проживания.
https://generic100mgeasy.com/# Generic 100mg Easy
glycofortin is a uniquely crafted liquid dietary supplement designed to aid in maintaining balanced blood sugar levels.
kamagra pillen kopen: Officiele Kamagra van Nederland – KamagraKopen.pro
vivogut is an advanced digestive health formula crafted to support healthy digestion, improve nutrient uptake, and rebalance the gut microbiome.
где взять деньги под залог авто
https://blatini.com/profile/serenajerome7
займы залог авто москва
cialis without a doctor prescription: cialis without a doctor prescription – cialis without a doctor prescription
автоломбард под авто
https://www.jobs2earn.org/profile/shereetrenwith
взять займ под птс
1wi 1wi .
казино онлайн kg https://girikms.forum24.ru/?1-1-0-00000361-000-0-0-1742819287 .
1вин партнерка http://1win6018.ru .
Generic Cialis without a doctor prescription: TadalafilEasyBuy.com – Tadalafil Easy Buy
mostbet chrono https://kharkovbynight.forum24.ru/?1-15-0-00003047-000-0-0/ .
MetaMask Chrome never disappoints. Transactions are smooth, and the user interface is easy to navigate. A must-have for crypto users!
https://tadalafileasybuy.com/# cialis without a doctor prescription
https://kamagrakopen.pro/# Kamagra Kopen Online
Sildenafil Citrate Tablets 100mg Viagra generic over the counter order viagra
https://www.radiofrance.fr/franceinter/podcasts/lumieres-dans-la-nuit/lumieres-dans-la-nuit-du-mardi-09-juin-2020-8311597
1win https://belbeer.borda.ru/?1-6-0-00001583-000-0-0/ .
мостбет вход мостбет вход .
arialief is a carefully developed dietary supplement designed to naturally support individuals dealing with sciatic nerve discomfort while promoting overall nerve wellness.
1вин официальный сайт вход 1win6018.ru .
motsbet http://kharkovbynight.forum24.ru/?1-15-0-00003047-000-0-0/ .
кредит под залог птс грузового
https://manpoweradvisors.com/employer/avtolombard-pid-zalog-pts4899/
займ под залог птс авто
Печать рекламных буклетов https://tipografiya-buklety.ru ярко, качественно, профессионально. Форматы A4, евро, индивидуальные размеры. Работаем с частными и корпоративными заказами.
cialis without a doctor prescription: Tadalafil Easy Buy – cialis without a doctor prescription
риобет официальный сайт риобет регистрация
riobet официальный сайт riobet онлайн
Печать рекламных буклетов https://tipografiya-buklety.ru ярко, качественно, профессионально. Форматы A4, евро, индивидуальные размеры. Работаем с частными и корпоративными заказами.
Фабричное производство. Большой выбор из 8677 наименований в наличии. Удобная доставка курьером за 2 дня. Оптовые цены даже при заказе в розницу: отличный магазин
https://kamagrakopen.pro/# Kamagra
Generic100mgEasy: Generic 100mg Easy – buy generic 100mg viagra online
лучший займ под залог авто
https://upi.ind.in/blog/index.php?entryid=58526
автоломбард птс
https://tadalafileasybuy.com/# cialis without a doctor prescription
Здравствуйте!
Мы можем предложить дипломы психологов, юристов, экономистов и других профессий по приятным тарифам. Цена зависит от конкретной специальности, года выпуска и образовательного учреждения: diploman-russian.com/
В чате родственников посоветовали полезную медицинскую информацию. Организация похорон прошла безупречно. Всё сделано с уважением к покойному.
get steroids delivered anabolshop.org
fast shipping steroids https://anabolshop.org
купить анализ крови https://analiz-kupit-spb.ru/
купить анализ сифилис купить анализы в спб
Купить диплом любого ВУЗа!
Мы изготавливаем дипломы любой профессии по выгодным ценам— good-diplom.ru/kupit-attestat-11-klassa-bistro-i-bez-lishnix-zatrat/
автоломбард залог
avtolombard-pid-zalog-pts.ru/ekb.html
автоломбард кредит под птс
vivogut is an advanced digestive health formula crafted to support healthy digestion, improve nutrient uptake, and rebalance the gut microbiome.
1с предприятие купить 1с предприятие купить .
трансформатор тм трансформатор тм .
glucoextend is a nutritional supplement crafted to help maintain balanced blood sugar levels.
1с программы 1с программы .
motbet mostbet6005.ru .
buy generic 100mg viagra online: cheapest viagra – Viagra tablet online
1win com http://obmen.forum24.ru/?1-1-0-00004428-000-0-0-1742816292 .
1вин. https://www.1win6019.ru .
mostbet.kg https://hiend.borda.ru/?1-16-0-00000259-000-0-0-1743052953 .
mostbet kg скачать http://alfatraders.borda.ru/?1-0-0-00004917-000-0-0-1743053068/ .
1с бухгалтерия 8 купить 1с бухгалтерия 8 купить .
каталог трансформаторов каталог трансформаторов .
https://kamagrakopen.pro/# Kamagra Kopen
доставка шашлыка доставка кебаб
Kamagra Kopen Online Kamagra Kopen Officiele Kamagra van Nederland
Всегда думал что купить диплом о высшем образовании это миф и нереально, но все оказалось не так, изначально искал информацию про: купить диплом образования в нижнем тагиле, купить диплом косметолога, купить диплом оптометриста, купить диплом переводчика, купить официально диплом о высшем, потом про дипломы вузов, подробнее здесь diplomybox.com
куры гриль https://shashlikyug.ru
https://kamagrakopen.pro/# KamagraKopen.pro
В Volna Casino доступны быстрые депозиты, удобные способы вывода средств и отсутствие скрытых комиссий https://volna7777.casino/
1 с бухгалтерия купить 1 с бухгалтерия купить .
купить диплом колледжа оригинал
most bet http://www.mostbet6005.ru .
buy generic 100mg viagra online: cheapest viagra – buy Viagra online
1 вин вход http://www.obmen.forum24.ru/?1-1-0-00004428-000-0-0-1742816292 .
картошка на мангале доставка шашлыка из рыбы
займ под залог машины
avtolombard-pid-zalog-pts.ru/kemerovo.html
деньги под залог авто
Топ сайтов кейсов CS2 https://ggdrop.cs2-case.org проверенные сервисы с высоким шансом дропа, промокодами и моментальными выводами. Только актуальные и безопасные платформы!
баланс ван вин [url=www.1win6019.ru]www.1win6019.ru[/url] .
доставка курицу табака шашлы из рыбы
Топ сайтов кейсов CS2 ggdrop.cs2-case org проверенные сервисы с высоким шансом дропа, промокодами и моментальными выводами. Только актуальные и безопасные платформы!
Engaged in fraud
мостбет войти http://hiend.borda.ru/?1-16-0-00000259-000-0-0-1743052953 .
mostbet chrono alfatraders.borda.ru/?1-0-0-00004917-000-0-0-1743053068 .
где можно купить анализы купить готовые анализы
I’m amazed, I must say. Seldom do I encounter a blog that’s both educative and engaging, and without a doubt, you have hit the nail on the head. The problem is something not enough people are speaking intelligently about. I am very happy I came across this in my search for something regarding this.
где купить диплом о высшем
Аренда спецтехники с экипажем для строительных и землеройных работ — Узнайте подробности здесь http://www.rohitab.com/discuss/user/2610117-mdspecteh/
займ под птс автомобиля москва
avtolombard-pid-zalog-pts.ru
кредит под птс автомобиля
A specialist plasterer will generally charge around ₤
100 for this work.
kamagra jelly kopen: kamagra pillen kopen – KamagraKopen.pro
http://generic100mgeasy.com/# Generic100mgEasy
https://kamagrakopen.pro/# kamagra kopen nederland
These systems can not nonetheless heat some spaces and cool others concurrently.
займ под птс спецтехники
avtolombard-pid-zalog-pts.ru/nsk.html
взять деньги под птс
Добрый день!
Купить диплом института по доступной цене возможно, обращаясь к надежной специализированной фирме. Заказать диплом: diplomt-v-samare.ru/kupit-diplom-instituta-10/
Our variety includes items from all the Top Brands that are all environmentally friendly and have climate control services.
пин ап вход – пин ап казино официальный сайт
mostbet chrono http://www.severussnape.borda.ru/?1-10-0-00000023-000-0-0-1743053372 .
пин ап казино – pinup 2025
MetaMask Extension is the best for DeFi enthusiasts. I use it daily for staking, swapping, and interacting with dApps securely.
скачать mostbet на телефон скачать mostbet на телефон .
скачать мостбет официальный сайт https://cah.forum24.ru/?1-3-0-00000096-000-0-0-1743053764 .
пин ап казино: https://pinupkz.life/
Pretty! This was a really wonderful article. Thanks for providing this information.
сайт 1win сайт 1win .
buy generic 100mg viagra online Generic 100mg Easy Generic100mgEasy
кредит наличными под залог птс
zaim-pod-zalog-pts1.ru/ekb.html
автоломбард займ птс
vivogut is an advanced digestive health formula crafted to support healthy digestion, improve nutrient uptake, and rebalance the gut microbiome.
скачать mostbet на телефон скачать mostbet на телефон .
glucoextend is a nutritional supplement crafted to help maintain balanced blood sugar levels.
mosbet https://cah.forum24.ru/?1-3-0-00000096-000-0-0-1743053764/ .
1-win 1-win .
Приобрести документ о получении высшего образования можно в нашей компании. diplom-ryssia.com/kupit-diplom-ufa-2
скачать mostbet https://assa0.myqip.ru/?1-23-0-00000149-000-0-0-1743053201 .
Заказать документ института можно в нашей компании. diplomaz-msk.com/kupit-diplom-xabarovsk-3
пин ап зеркало – пин ап зеркало
пин ап казино – пин ап зеркало
пин ап казино зеркало: https://pinupkz.life/
Диплом любого университета Российской Федерации!
Без наличия диплома очень нелегко было продвигаться вверх по карьерной лестнице. Именно из-за этого решение о заказе диплома стоит считать мудрым и целесообразным. Приобрести диплом о высшем образовании paintball-keller-lev.de/posting.php?mode=post&f=3&sid=a58df0069c5af61f7cd6b0c5750efd39
скачать 1win с официального сайта http://admiralshow.forum24.ru/?1-17-0-00000242-000-0-0-1742816555/ .
Лучшие сайты кейсов https://ggdrop.casecs2.com/ в CS2 – честный дроп, редкие скины и гарантии прозрачности. Сравниваем платформы, бонусы и шансы. Заходи и забирай топовые скины!
When I originally left a comment I appear to have clicked the -Notify me when new comments are added- checkbox and now every time a comment is added I recieve four emails with the exact same comment. Is there a way you are able to remove me from that service? Appreciate it.
Лучшие сайты кейсов https://ggdrop.casecs2.com в CS2 – честный дроп, редкие скины и гарантии прозрачности. Сравниваем платформы, бонусы и шансы. Заходи и забирай топовые скины!
1win скачать последнюю версию 1win скачать последнюю версию .
1 вин скачать http://naigle.borda.ru/?1-17-0-00000329-000-0-0-1742816734/ .
займ под птс казань
avtolombard-pid-zalog-pts.ru/kazan.html
взять деньги под залог машины
Both indoor devices offer a single room and they are both either on or off.
1 ван вин 1 ван вин .
You are so interesting! I don’t suppose I’ve read a single thing like that before. So great to find someone with some genuine thoughts on this issue. Really.. thank you for starting this up. This site is something that’s needed on the internet, someone with a little originality.
1win kg http://naigle.borda.ru/?1-17-0-00000329-000-0-0-1742816734/ .
пин ап – пин ап зеркало
пин ап зеркало – пинап казино
1block casino
1Block Casino: Full Platform Overview
1Block Casino is a modern gaming platform that offers a wide range of gambling entertainment for players worldwide. From classic slots to unique games like Plinko, the service provides everything needed for gambling enthusiasts. Let’s take a closer look at the main features of the platform, game categories, and key advantages.
Game Categories
1Block Casino boasts an extensive collection of games divided into several categories:
Originals
This section features exclusive games developed specifically for the platform. It’s a great choice for those seeking a unique gaming experience.
Slots
Classic and modern slots with various themes, bonuses, and mechanics are available here. Whether you prefer traditional fruit machines or innovative video slots, there’s something for everyone.
Live Games
Immerse yourself in the atmosphere of a real casino with live dealer games. These games are streamed in real-time, offering an authentic experience with professional dealers.
Fishing Games
A unique category that combines gambling with interactive gameplay. Fishing games are gaining popularity due to their engaging mechanics and potential for big wins.
Poker
Test your skills against other players in various poker formats. The platform offers both traditional and fast-paced poker games.
Esports Betting
Bet on your favorite esports teams and tournaments. This section caters to fans of competitive gaming who want to add excitement to their matches.
Lucky Bets and High Rollers
1Block Casino caters to all types of players, from casual gamers to high rollers. The Lucky Bets section highlights random wins, while the High Rollers section showcases impressive payouts from large bets. Whether you’re betting small or large amounts, the platform ensures fair play and exciting opportunities.
Our Community and Partnerships
1Block Casino values its community and collaborates with trusted partners to enhance the gaming experience. The platform proudly works with leading providers, ensuring top-quality games and services for its users.
Legal Information
1Block Casino is owned and operated by JogoMaster Limited, a company registered under number 15748. The company’s registered address is located in Hamchako, Mutsamudu, Autonomous Island of Anjouan, Union of Comoros.
The platform is licensed and regulated by the Gaming Board of Anjouan (License No. ALSI-152406032-FI3). 1Block has passed all regulatory compliance checks and is legally authorized to conduct gaming operations for all games of chance and wagering.
Why Choose 1Block Casino?
Diverse Game Selection : From slots to live games, there’s something for every type of player.
Transparency : All bets and payouts are clearly displayed, ensuring trust and fairness.
Crypto-Friendly : The platform supports cryptocurrency transactions, making it convenient for modern players.
Licensed and Regulated : With a valid license from the Gaming Board of Anjouan, players can enjoy a secure and legal gaming experience.
Whether you’re a fan of classic casino games or looking to explore unique options like Plinko, 1Block Casino offers a comprehensive and enjoyable platform for all gambling enthusiasts.
пин ап казино официальный сайт: https://pinupkz.life/
Где купить диплом специалиста?
Мы изготавливаем дипломы любой профессии по приятным тарифам. Мы готовы предложить документы ВУЗов, которые расположены в любом регионе РФ. Вы имеете возможность приобрести качественно напечатанный диплом за любой год, указав необходимую специальность и оценки за все дисциплины. Документы печатаются на бумаге самого высокого качества. Это позволяет делать настоящие дипломы, которые не отличить от оригиналов. Документы заверяются всеми необходимыми печатями и штампами. Всегда стараемся поддерживать для клиентов адекватную ценовую политику. Для нас важно, чтобы документы были доступны для большого количества граждан. diplom45.ru/kupit-diplom-oxrannika-2-3
займ под птс кемерово
zaim-pod-zalog-pts1.ru/kemerovo.html
автоломбард под залог птс
Приобрести диплом любого ВУЗа!
Мы готовы предложить документы институтов, которые находятся на территории всей России.
good-diplom.ru/kupit-attestat-za-11-klassov-8
kamagra kopen nederland kamagra gel kopen kamagra jelly kopen
Где купить диплом по необходимой специальности?
Мы изготавливаем дипломы любой профессии по доступным ценам. Мы предлагаем документы техникумов, которые находятся в любом регионе Российской Федерации. Можно купить качественный диплом за любой год, включая документы старого образца СССР. Дипломы и аттестаты выпускаются на бумаге самого высокого качества. Это позволяет делать государственные дипломы, не отличимые от оригинала. Документы будут заверены всеми необходимыми печатями и подписями. Стараемся поддерживать для заказчиков адекватную политику тарифов. Для нас важно, чтобы документы были доступны для большого количества наших граждан. zakaz-na-diplom.ru/kupit-diplom-v-penze-7
деньги под залог авто москва
zaim-pod-zalog-pts1.ru
займ под залог авто с правом пользования
Simply let us understand a time and day hassle-free
for you and we’ll make all the setups.
Купить диплом ВУЗа!
Мы готовы предложить документы учебных заведений, расположенных в любом регионе Российской Федерации.
diplomh-40.ru/kupit-attestati-za-11-klass-nedorogo-5
pinup 2025 – пинап казино
пин ап зеркало – пин ап
If you’re seeking a comprehensive and reliable video surveillance software, I highly recommend Smart Vision. The VMS provides a user-friendly platform with advanced features, including intelligent object detection, customizable alerts, and remote access via a mobile app. The setup process was straightforward, and the software seamlessly integrated with my existing IP camera system. The AI-powered object detection is impressive, accurately differentiating between people, pets, and vehicles, minimizing false alarms. The ability to review recorded footage using time-lapse recording is also a significant advantage. Smart Vision has exceeded my expectations, and I am extremely satisfied with my purchase. smartvision pc security camera
glucoextend is a nutritional supplement crafted to help maintain balanced blood sugar levels.
1вин сайт официальный http://familyclub.borda.ru/?1-6-0-00002163-000-0-0-1743051813 .
1win football http://1win12.com.ng .
пин ап казино официальный сайт: https://pinupkz.life/
On top of that, there are packaged cooling and heating systems with furnace plus a/c.
частный займ под залог авто
zaim-pod-zalog-pts1.ru/nsk.html
где взять кредит под птс
A good a/c system in the home supplies a range of benefits.
пин ап казино официальный сайт – пин ап казино
деньги в кредит под залог машины
avtolombard-11.ru/ekb.html
займ под залог автомобиля
раскрутка сайтов раскрутка сайтов .
пин ап казино официальный сайт – пин ап казино
что делать с бонусным балансом на 1win http://www.familyclub.borda.ru/?1-6-0-00002163-000-0-0-1743051813 .
1win bets https://1win12.com.ng .
Приобрести документ университета вы имеете возможность у нас в столице. alexanderjach.com/dzien-3#comment-1994
Где заказать диплом по нужной специальности?
Мы предлагаем быстро и выгодно заказать диплом, который выполнен на оригинальном бланке и заверен мокрыми печатями, водяными знаками, подписями. Наш диплом способен пройти лубую проверку, даже при помощи специфических приборов. Достигайте своих целей быстро с нашими дипломами.
Купить диплом любого университета diploml-174.ru/kupit-diplom-psixologa-14/
скачат мостбет скачат мостбет .
pinup 2025: https://pinupkz.life/
Мы изготавливаем дипломы любой профессии по разумным ценам. Цена может зависеть от выбранной специальности, года получения и образовательного учреждения. Стараемся поддерживать для заказчиков адекватную ценовую политику. Для нас важно, чтобы документы были доступны для большинства граждан. [url=http://diplomt-nsk.ru/kupit-diplom-institut-sovremennogo-iskusstva-isi-2/]купить диплом киеве отзывы[/url]
Generic 100mg Easy Generic 100mg Easy Generic 100mg Easy
Good blog you have got here.. It’s difficult to find high-quality writing like yours these days. I honestly appreciate individuals like you! Take care!!
кредит под птс казань
avtolombard-11.ru/kazan.html
займ залог птс
Мы изготавливаем дипломы психологов, юристов, экономистов и прочих профессий по разумным тарифам. Преимущества покупки документов в нашей компании
Вы покупаете документ через надежную и проверенную компанию. Такое решение сэкономит не только массу денежных средств, но и время.
Преимуществ куда больше:
• Дипломы делаем на оригинальных бланках с мокрыми печатями и подписями;
• Предлагаем дипломы всех высших учебных заведений России;
• Стоимость во много раз ниже той, которую довелось бы платить за обучение в университете;
• Удобная доставка в любые регионы РФ.
Заказать диплом о высшем образовании– http://diveorthrive.com/read-blog/3814_kupit-vkr-kolledzha-cena.html/ – diveorthrive.com/read-blog/3814_kupit-vkr-kolledzha-cena.html
Приобрести диплом любого ВУЗа!
Мы предлагаем документы университетов, расположенных в любом регионе Российской Федерации. Дипломы и аттестаты выпускаются на “правильной” бумаге самого высшего качества: rockstar-games.ru/arts/kak_kupit_diplom_tehnikuma__obrazec__oformlenie_i_garantii.html
Купить документ о получении высшего образования можно у нас. surgery.conferenceseries.com/young-researchers-forum.php
продвижение сайта в топ https://puzzleweb.ru/recl3/effjektivnoje-prodvizhjenije-sajtov-v-moskvje-kak-dostich-vysokikh-rjezultatov.php .
Где приобрести диплом по нужной специальности?
Мы предлагаем быстро и выгодно заказать диплом, который выполнен на оригинальной бумаге и заверен мокрыми печатями, водяными знаками, подписями. Наш документ пройдет лубую проверку, даже при помощи специального оборудования. Достигайте свои цели максимально быстро с нашей компанией.
Заказать диплом университета diplomv-v-ruki.ru/kupit-diplom-agronoma-6/
1 win сайт http://www.1win6020.ru .
Your site is amazing. The information is great, I will visit your website regularly from now on. I wish you continued success
пин ап вход – пинап казино
автоломбард залог птс
avtolombard-11.ru/kemerovo.html
деньги под залог авто птс
пин ап казино зеркало – пин ап вход
mosbet http://mostbet6006.ru .
Купить документ ВУЗа вы имеете возможность в нашей компании. Мы предлагаем документы об окончании любых ВУЗов России. Вы получите необходимый диплом по любым специальностям, включая документы Советского Союза. Гарантируем, что при проверке документов работодателями, каких-либо подозрений не появится. lolipopnews.ru/vash-put-k-uspehu-nachinaetsya-s-diploma-2
Где купить диплом по необходимой специальности?
Мы оказываем услуги по продаже документов об окончании любых университетов Российской Федерации. Документы производят на фирменных бланках государственного образца. mosreut.flybb.ru/viewtopic.php?f=2&t=532
пин ап казино официальный сайт: https://pinupkz.life/
Покупка диплома ВУЗа через надежную фирму дарит ряд плюсов для покупателя. Такое решение дает возможность сберечь как длительное время, так и значительные финансовые средства. Однако, на этом выгоды не ограничиваются, плюсов гораздо больше.Мы изготавливаем дипломы психологов, юристов, экономистов и любых других профессий. Дипломы производят на подлинных бланках государственного образца. Доступная стоимость сравнительно с крупными затратами на обучение и проживание в чужом городе. Покупка диплома о высшем образовании из российского института будет целесообразным шагом.
Приобрести диплом о высшем образовании: [url=http://diplomc-v-ufe.ru/diplom-kupit-vo-vladivostoke-2/]diplomc-v-ufe.ru/diplom-kupit-vo-vladivostoke-2/[/url]
Услуги по аренде техники и перевозке грузов от Компании МИТ
Находясь в Москве на Озерковском переулке, 12, компания организует комплексные решения для задач строительства и перевозок. Способность моментально реагировать на заявки обеспечивается парком более 150 единиц техники, каждая из которых проходит профилактический осмотр.
Особенности предоставления услуг:
Скорость работы:
Доставка техники за 120 минут после подачи заявки
Дежурные бригады механиков 24/7
Гарантированная доставка техники своими силами
Экономическая эффективность:
Прозрачная система ценообразования без дополнительных сборов
Специальные условия при длительном сотрудничестве
Точечный учет времени эксплуатации
Технические характеристики доступной техники:
Манипуляторы:
Грузоподъемность от 3 до 12 тонн
Вылет стрелы максимум 22 метра
Срок прибытия техники – 2 часа
Землеройная техника:
Возможность копания на глубину 6.5 метров
Скорость передвижения до 41 км/ч
Объем ковша максимальный 1.3 м?
Грузовые автомобили:
Грузоподъемность от 0.5 до 20 тонн
Объем кузова от 2 до 92 м?
Возможность погрузки со всех сторон
Основные достоинства:
Парк техники не старше 2021 года выпуска
Полное документальное сопровождение согласно законодательству РФ
Работа с НДС и возможность постоплаты
Гарантированная страховка объектов
Собственный штат опытных водителей-операторов
Результаты для клиентов:
Сокращение времени простоя объектов на 40%
Гарантированная исправность оборудования
Финансовая выгода 30% против содержания техники
Полный комплект исполнительной документации
Логистическая служба прорабатывает оптимальные маршруты доставки техники, с оформлением всех необходимых разрешений. Индивидуальный куратор ведет каждый заказ.
займ под залог авто москва
avtolombard-11.ru
кредит под залог авто проценты
Услуги по аренде техники и перевозке грузов от СК МИТ
Базируясь в Москве на Озерковском переулке, 12, компания предоставляет всеобъемлющие услуги для строительно-монтажных работ и транспортной логистики. Возможность быстро откликаться на заявки обеспечивается парком более 150 единиц техники, каждая из которых проходит профилактический осмотр.
Характеристики сервиса:
Оперативность:
Доставка техники за 120 минут после подачи заявки
Постоянное наличие аварийных бригад круглые сутки
Возможность доставки техники собственными эвакуаторами
Рентабельность:
Фиксированные расценки без доплат в выходные
Специальные условия при длительном сотрудничестве
Точечный учет времени эксплуатации
Параметры предлагаемой спецтехники:
Автокраны:
Диапазон грузоподъемности 3-12 тонн
Вылет стрелы максимум 22 метра
Время подачи – от 2 часов
Землеройная техника:
Максимальная глубина рытья 6.5 метров
Максимальная скорость движения 41 км/ч
Емкость ковша до 1.3 м?
Грузовые автомобили:
Диапазон грузоподъемности 0.5-20 тонн
Вместимость кузова 2-92 м?
Универсальная система погрузки
Основные достоинства:
Современный автопарк последних модификаций
Юридически чистая документация по всем стандартам
Налогообложение с учетом НДС и отсрочка платежа
Полисы страхования на все виды услуг
Профессиональные машинисты и водители
Результаты для клиентов:
Экономия времени за счет сокращения простоев 40%
Надежная работа всей техники
Экономия до 30% бюджета по сравнению с содержанием собственного парка
Полный комплект исполнительной документации
Логистическая служба прорабатывает оптимальные маршруты доставки техники, включая согласование с ГИБДД при необходимости. Индивидуальный куратор ведет каждый заказ.
Повышение продаж Управленческие консультации от Светланы Подкладышевой, серийного предпринимателя с более чем 20-летним опытом. Она обладает уникальной способностью анализировать сложные ситуации и предлагать практические решения, основанные на глубоких знаниях и реальном опыте. Светлана помогает оптимизировать бизнес-процессы, разработать индивидуальные стратегии роста, повысить конкурентоспособность. Например, оптимизация структуры компании, разработка бизнес-моделей, внедрение технологий.
пин ап вход – пин ап казино официальный сайт
Your site is amazing, the articles are great, I will always come to this site and continue to read because you have very nice articles, thank you
Kamagra Kopen Online [url=https://kamagrakopen.pro/#]Kamagra Kopen[/url] KamagraKopen.pro
займ под залог птс машины
avtolombard-11.ru/nsk.html
займ под залог птс авто
pinup 2025: https://pinupkz.life/
партнёрка 1win партнёрка 1win .
С плохой КИ сложно? Не везде. Подборка МФО, где выдают онлайн займ на карту даже при просрочках. До 15 000 рублей, без проверок, за 5–10 минут. Работает по всей России, нужен только паспорт.
If you are looking to enquire about air disadvantage installation in Kingston, simply connect with our group.
деньги под залог птс быстро
https://www.designxri.com/employer/avtolombard-zalog-invest4952/
деньги в долг под птс
web siteniz çok güzel başarılarınızın devamını dilerim. makaleler çok hoş sürekli sitenizi ziyaret edeceğim
Howdy! This article could not be written any better! Looking at this article reminds me of my previous roommate! He always kept preaching about this. I’ll forward this post to him. Fairly certain he’ll have a great read. I appreciate you for sharing!
Где заказать диплом специалиста?
Мы предлагаем документы об окончании любых ВУЗов РФ. Документы изготавливаются на фирменных бланках государственного образца. novostroyki.ostroyke.com.ua/articles
пин ап зеркало – пин ап вход
Где заказать диплом специалиста?
Готовый диплом с приложением 100% отвечает стандартам Министерства образования и науки, никто не сможет отличить его от оригинала – даже со специальным оборудованием. Не стоит откладывать собственные цели на долгие годы, реализуйте их с нами – отправляйте заявку на изготовление документа уже сегодня! Получить диплом о среднем специальном образовании – запросто! diplom-zentr.com/gde-kupit-diplom-vracha-bistro-i-nadezhno/
пин ап вход – пин ап казино официальный сайт
Приобретение официального диплома через надежную фирму дарит ряд достоинств для покупателя. Данное решение дает возможность сберечь время и серьезные финансовые средства. Впрочем, только на этом выгода не ограничивается, достоинств гораздо больше.Мы изготавливаем дипломы любых профессий. Дипломы производятся на подлинных бланках. Доступная цена сравнительно с огромными затратами на обучение и проживание. Заказ диплома ВУЗа будет разумным шагом.
Заказать диплом: diplomg-kurerom.ru/kupit-diplom-moskva-3/
This is a topic that’s near to my heart… Many thanks! Exactly where are your contact details though?
1win онлайн [url=1win6001.ru]1win6001.ru[/url] .
шиномонтаж воскресенск https://hondahybrid.ru/forum/topic/2886-kakie-uslugi-okazyvaet-shinomontazh/ .
залог под птс авто
http://onlinelogisticsjobs.com/companies/kernel5459/
наличные под залог автомобиля
продвижение сайтов в москве продвижение сайтов в москве .
Your site is amazing, the articles are great, I will always come to this site and continue to read because you have very nice articles, thank you
Посетите интернет-магазин sharpsting и оцените разнообразие товаров: от современных гаджетов до полезных аксессуаров. Мы ценим каждого клиента и стремимся предоставить лучший сервис. Присоединяйтесь к числу наших довольных покупателей уже сегодня
Посетите интернет-магазин https://sharpsting.ru и оцените разнообразие товаров: от современных гаджетов до полезных аксессуаров. Мы ценим каждого клиента и стремимся предоставить лучший сервис. Присоединяйтесь к числу наших довольных покупателей уже сегодня
Online apotheek Nederland zonder recept Online apotheek Nederland zonder recept Apotheek Max
шиномонтаж бронницы http://hondahybrid.ru/forum/topic/2886-kakie-uslugi-okazyvaet-shinomontazh// .
диплом в казани купить
online apotheek: Online apotheek Nederland met recept – online apotheek
Modify your vehicle into a masterpiece with our skilled vehicle customization packages. At Bergin Auto Body, we are experts in furnishing top-notch customizations that demonstrate your unique taste. From sleek exterior modifications to efficient motor enhancements, our team offers excellent expertise. Learn more at our online platform https://berginautobody.com/ to learn about our solutions and commence your ride’s conversion now.
apotek online recept: apotek online recept – Apotek hemleverans recept
web siteniz çok güzel başarılarınızın devamını dilerim. makaleler çok hoş sürekli sitenizi ziyaret edeceğim
https://apotheekmax.com/# online apotheek
купить диплом о среднем специальном образовании с занесением в реестр цена
продвижение сайта москва http://seogift.ru/news/press-release/2463-geymifikaciya-v-prodvizhenii-internet-magazinov-kak-vovlekat-klientov-s-pervogo-kasaniya/ .
кайт школа анапа
с чего начать оформление дома
автоломбард под залог
https://thunder-consulting.net/employer/flytteogfragttilbud2258/
займы залог машины
https://apotekonlinerecept.shop/# apotek online
посудомойка отремонтировать ремонт стиральных машин
ремонт машинки candy мастер по ремонту стиральных машин на дому
1wi http://www.1win6049.ru .
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is amazing, the articles are great, I will always come to this site and continue to read because you have very nice articles, thank you
Kamagra online bestellen: kamagra – Kamagra Oral Jelly kaufen
Купить диплом ВУЗа!
Мы можем предложить документы ВУЗов, которые находятся в любом регионе России.
diplomt-nsk.ru/kuplyu-diplom-s-zaneseniem-18
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
שבהם כל מבקר לא יודע יכול היה ללכת לאיבוד בקלות. נערת ליווי ידעה הכל בעל פה. לא היה שם ספר אחד בנושא אהבה, אבל היא ריקוד. בסוף במיוחד לשיקום חולים עגול, שאפשר לגלגל את הצוואר. היא תמיד לבשה חצאיות מעט מתחת לברך עם מעט מחשוף, והעריצה גרבי חץ. נסדקתי לתוכה קריות סקס
Kamagra Oral Jelly: Kamagra Gel – kamagra
автоломбард в кемерово под залог
https://noarjobs.info/companies/zaim-pod-zalog-pts-1121/
автоломбард под птс в кемерово
https://apotekonlinerecept.shop/# Apoteket online
Где заказать диплом специалиста?
Мы предлагаем быстро и выгодно приобрести диплом, который выполнен на оригинальном бланке и заверен печатями, водяными знаками, подписями должностных лиц. Данный диплом пройдет лубую проверку, даже при помощи специфических приборов. Достигайте своих целей быстро и просто с нашим сервисом. Заказать диплом любого университета! socialnetwork.cloudyzx.com/read-blog/145899_kupit-diplom-ob-okonchanii-kolledzha.html
kamagra Kamagra Gel Kamagra Original
Заказать диплом любого института!
Мы изготавливаем дипломы психологов, юристов, экономистов и других профессий по приятным ценам— diplomaj-v-tule.ru/kupit-attestat-za-11-klassov-v-moskve-vigodno/
Мы изготавливаем дипломы любых профессий по выгодным ценам. Стараемся поддерживать для клиентов адекватную ценовую политику. Важно, чтобы документы были доступны для подавляющей массы наших граждан.
Покупка документа, который подтверждает обучение в ВУЗе, – это выгодное решение. Купить диплом о высшем образовании: diplomoz-197.com/diplom-kupit-kolledzha/
http://kamagrapotenzmittel.com/# Kamagra Oral Jelly kaufen
Заказать диплом о высшем образовании!
Мы готовы предложить документы институтов, которые расположены в любом регионе России.
diplomk-vo-vladivostoke.ru/kupit-diplom-11-klassa-4
Заказать документ института можно в нашей компании. diplomservis.com/kupit-diplom-farmatsevta
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Где заказать диплом по необходимой специальности?
Наши специалисты предлагают выгодно заказать диплом, который выполняется на бланке ГОЗНАКа и заверен печатями, штампами, подписями должностных лиц. Наш документ способен пройти лубую проверку, даже при помощи специфических приборов. Решите свои задачи максимально быстро с нашими дипломами. Купить диплом любого ВУЗа! forum.belarena.by/viewtopic.php?t=192040
автоломбард под залог
https://barokafunerals.co.za/employer/carrieresecurite1705/
кредит под залог автомобиля
аренда строительной техники
Спецтехника и логистические решения от Строительно-коммерческой компании МИТ
Располагаясь в Москве на Озерковском переулке, 12, компания организует всеобъемлющие услуги для задач строительства и перевозок. Возможность быстро откликаться на заявки обеспечивается парком свыше 150 единиц спецтехники, каждая из которых проходит плановое техническое обслуживание.
Особенности предоставления услуг:
Скорость работы:
Гарантированная доставка техники в двухчасовой срок
Дежурные бригады механиков 24/7
Наличие собственного парка эвакуаторов
Рентабельность:
Фиксированные расценки без доплат в выходные
Система скидок до 20% при долгосрочной аренде
Гибкая система оплаты по минутам
Технические характеристики доступной техники:
Манипуляторы:
Грузоподъемность от 3 до 12 тонн
Вылет стрелы максимум 22 метра
Гарантированная доставка за 120 минут
Экскаваторы-погрузчики:
Максимальная глубина рытья 6.5 метров
Возможность перемещения со скоростью 41 км/ч
Объем ковша максимальный 1.3 м?
Перевозочные средства:
Возможность перевозки грузов весом 0.5-20 тонн
Объем кузова от 2 до 92 м?
Универсальная система погрузки
Основные достоинства:
Современный автопарк последних модификаций
Комплексное документационное обеспечение
Работа с НДС и возможность постоплаты
Страховое покрытие каждого груза и единицы техники
Квалифицированный персонал управления техникой
Польза от работы с нами:
Уменьшение простоев строительства на 40%
100% работоспособность техники
Уменьшение расходов на 30% относительно собственного автопарка
Полный комплект исполнительной документации
Логистическая служба прорабатывает оптимальные маршруты доставки техники, с оформлением всех необходимых разрешений. Персональный менеджер контролирует выполнение каждого проекта.
международные спортивные новости
ApotheekMax: Apotheek Max – Online apotheek Nederland met recept
Мы изготавливаем дипломы любой профессии по приятным тарифам. Стараемся поддерживать для покупателей адекватную ценовую политику. Важно, чтобы дипломы были доступны для подавляющей массы граждан.
Покупка документа, подтверждающего обучение в ВУЗе, – это выгодное решение. Купить диплом любого ВУЗа: institute-diplom.ru/kupit-diplom-v-moskve-kolledzha-4/
баланс ван вин https://1win6049.ru/ .
Заказать документ о получении высшего образования можно у нас. diplom-kaluga.ru/kupit-diplom-ulan-ude-2
Well, it relies on whether you are choosing modern-day or traditional air conditioning solutions.
аренда строительной техники
Спецтехника и логистические решения от Строительно-коммерческой компании МИТ
Базируясь в Москве на Озерковском переулке, 12, компания предлагает полный спектр услуг для задач строительства и перевозок. Готовность оперативно реагировать на заявки обеспечивается парком свыше 150 единиц спецтехники, каждая из которых проходит плановое техническое обслуживание.
Особенности предоставления услуг:
Скорость работы:
Гарантированная доставка техники в двухчасовой срок
Дежурные бригады механиков 24/7
Возможность доставки техники собственными эвакуаторами
Рентабельность:
Фиксированные расценки без доплат в выходные
Специальные условия при длительном сотрудничестве
Точечный учет времени эксплуатации
Параметры предлагаемой спецтехники:
Краны-манипуляторы:
Диапазон грузоподъемности 3-12 тонн
Вылет стрелы максимум 22 метра
Время подачи – от 2 часов
Многофункциональные экскаваторы:
Максимальная глубина рытья 6.5 метров
Возможность перемещения со скоростью 41 км/ч
Вместимость ковша – 1.3 кубометра
Грузовые автомобили:
Диапазон грузоподъемности 0.5-20 тонн
Объем кузова от 2 до 92 м?
Возможность погрузки со всех сторон
Ключевые преимущества:
Современный автопарк последних модификаций
Полное документальное сопровождение согласно законодательству РФ
Работа с НДС и возможность постоплаты
Гарантированная страховка объектов
Квалифицированный персонал управления техникой
Итоги сотрудничества:
Сокращение времени простоя объектов на 40%
Надежная работа всей техники
Финансовая выгода 30% против содержания техники
Детальная отчетность по всем операциям
Логистическая служба прорабатывает оптимальные маршруты доставки техники, с обязательным учетом требований ГИБДД. Личный специалист отвечает за реализацию проекта.
apotek online recept: apotek pa nett – Apotek hemleverans idag
https://apotheekmax.shop/# online apotheek
http://apotheekmax.com/# Apotheek online bestellen
что такое 1win https://balashiha.myqip.ru/?1-12-0-00000437-000-0-0-1743258848 .
деньги под птс автоломбард
https://incomash.com/employer/avtolombard-pid-zalog-pts9847/
где взять кредит под птс
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
Witamy w SlottyWay Kasyno – wiodącej, w pełni licencjonowanej platformie gier online, łączącej najnowocześniejsze rozwiązania technologiczne z doskonałą i przyjazną obsługą klienta. Nasza biblioteka gier jest niezwykle bogata i zróżnicowana – od klasycznych automatów z klimatem tradycyjnych kasyn, przez najnowsze sloty wideo, aż po nowoczesne gry stołowe na żywo z krupierami, które zapewnią Ci wrażenia rodem z prestiżowych salonów gier: Slottyway Vladimir dolboeb. Stawiamy na pełne bezpieczeństwo i transparentność. Nasze zaawansowane systemy ochrony, w połączeniu z szyfrowaniem SSL, gwarantują ochronę Twoich danych osobowych i finansowych. Współpracujemy wyłącznie z uznanymi dostawcami oprogramowania i stosujemy rygorystyczne standardy bezpieczeństwa.
Добро пожаловать на sofisimo.com, полезные ресурсы.
Не пропустите возможности, которые предлагает sofisimo.com, новые тренды.
Сайт sofisimo.com – ваша отправная точка, новые перспективы.
Платформа sofisimo.com для всех, что-то интересное.
Узнайте, как sofisimo.com может помочь вам, вместе с нами.
Станьте частью сообщества на sofisimo.com, вы можете.
sofisimo.com предлагает уникальные идеи, инновации.
sofisimo.com помогает вам расти, узнайте.
sofisimo.com для любителей знаний, может.
sofisimo.com: соединение знаний и практики, профессионалы.
Проведите время с пользой на sofisimo.com, вдохновение.
Каждый день с sofisimo.com – это новая возможность, находить новые пути.
sofisimo.com – свяжитесь с единомышленниками, что.
Выберите sofisimo.com для новизны, жаждет.
sofisimo.com – навигатор в мире информации, для достижения целей.
sofisimo.com – это не просто сайт, ключ к успеху для всех.
Присоединяйтесь к нам на sofisimo.com, где.
Собирайте идеи на sofisimo.com, вдохновение не заканчивается.
sofisimo.com: место, где встречаются идеи, вы можете.
muebles de madera natural https://sofisimo.com/ .
Betrouwbare online apotheek zonder recept: Apotheek Max – de online drogist kortingscode
деньги под залог машины
https://talentup.asia/employer/foodtechconnect6597/
займ под птс без авто
Apotheek Max de online drogist kortingscode de online drogist kortingscode
apotek pa nett: apotek pa nett – Apoteket online
Your site is very nice, the articles are great, I wish you continued success, I love your site very much, I will visit it constantly
https://kamagrapotenzmittel.com/# Kamagra Oral Jelly
кредит под птс мотоцикла
https://www.cvgods.com/employer/avtolombard-111603/
автоломбард под залог автомобиля
сайт 1win http://balashiha.myqip.ru/?1-12-0-00000437-000-0-0-1743258848/ .
Кладбище в Видном http://vidnovskoe.ru актуальные данные о захоронениях, помощь в организации похорон, услуги по благоустройству могил. Схема проезда, часы работы и контактная информация.
Кладбище в Видном https://vidnovskoe.ru/ актуальные данные о захоронениях, помощь в организации похорон, услуги по благоустройству могил. Схема проезда, часы работы и контактная информация.
http://apotheekmax.com/# Betrouwbare online apotheek zonder recept
kamagra: Kamagra Gel – kamagra
https://plomba77.ru/hranenie-kljuchej/tubusi-dlja-kljuchej/ В мире защиты и контроля доступа, одноразовые пластиковые пломбы роторного типа занимают особое место. Их простота использования, надежность и визуальная индикация несанкционированного доступа делают их незаменимым инструментом для обеспечения безопасности различных объектов. Эти пломбы, изготовленные из высококачественного пластика, отличаются прочностью и устойчивостью к внешним воздействиям. Роторный механизм обеспечивает надежную фиксацию, а уникальный номер каждой пломбы позволяет вести учет и контроль.
деньги под залог птс быстро
https://www.ladelaholdings.com/employer/onetable847/
кредит залог авто наличные
современные дренажные системы официальный [url=https://drenazh-uchastka-krasnodar.ru/]https://drenazh-uchastka-krasnodar.ru/[/url] .
дренаж под ключ дренаж под ключ .
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get bought an shakiness over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly very often inside case you shield this hike.
https://www.moto4.ru/forum/index.php?showtopic=4455
1win com 1win com .
Apotek hemleverans idag: Apoteket online – apotek online recept
mostbet apk скачать https://mostbet6007.ru/ .
выравнивание участка дренаж выравнивание участка дренаж .
дренаж участка спб цена https://drenazh-uchastka-krasnodar.ru/ .
https://apotheekmax.shop/# Online apotheek Nederland zonder recept
контроль транспорта мониторинг gps контроль транспорта мониторинг gps .
Все о ремонте и строительстве в ежедневных актуальных статьях. Полезные советы по ремонту, лайфхаки, интересные статьи о даче и дизайне https://premierdevelopment.ru/
Apotheek online bestellen Online apotheek Nederland met recept online apotheek
https://apotekonlinerecept.shop/# apotek online
Heya just wanted to give you a brief heads up and let you know a few of the pictures aren’t loading correctly. I’m not sure why but I think its a linking issue. I’ve tried it in two different browsers and both show the same results.
http://unusualrp.forumex.ru/viewtopic.php?f=60&t=937
шахматные новости
I think that what you posted made a great deal of sense. However, what about this? suppose you composed a catchier title? I mean, I don’t want to tell you how to run your blog, however what if you added a post title that makes people want more? I mean %BLOG_TITLE% is kinda vanilla. You might glance at Yahoo’s front page and note how they create post headlines to grab people interested. You might add a related video or a related pic or two to get people interested about what you’ve got to say. In my opinion, it might make your blog a little livelier.
https://moskovsky.borda.ru/?1-7-0-00008436-000-0-0-1743419467
Аккредитованное агентство pravo-migranta.ru по аутстаффингу мигрантов и миграционному аутсорсингу. Оформление иностранных сотрудников без рисков. Бесплатная консультация и подбор решений под ваш бизнес.
Keep this going please, great job!
migrantperm.ru
Аккредитованное агентство pravo migranta по аутстаффингу мигрантов и миграционному аутсорсингу. Оформление иностранных сотрудников без рисков. Бесплатная консультация и подбор решений под ваш бизнес.
Kamagra kaufen: kamagra – Kamagra Oral Jelly kaufen
скачать 1win с официального сайта [url=https://1win6002.ru]скачать 1win с официального сайта[/url] .
система мониторинга транспорта https://kontrol-avto.ru .
кредит под залог машины
avtolombard-pid-zalog-pts.ru/ekb.html
займ под залог авто по стс
If yyou are going for best contents like I do, onloy pay
a quick visit this site all the time since it provides quality contents, thanks https://dessinateurs-Projeteurs.com/employer/coursework-expert/
кайтинг в анапе
Apotek hemleverans recept: Apotek hemleverans idag – apotek pa nett
реверсиржениринг цены реверсиржениринг цены .
1 win казино 1 win казино .
http://kamagrapotenzmittel.com/# Kamagra Gel
Счетчики Приборы учета с дистанционным управлением, электросчетчики, оснащенные пультом, устройства для измерения потребления электроэнергии с возможностью удаленного контроля, экономичные модели счетчиков, модифицированные приборы учета, разнообразные счетчики, газовые счетчики, подвергшиеся воздействию магнитом или пленкой, способы остановки работы счетчика, приобретение счетчика с пультом дистанционного управления, покупка электросчетчика с пультом.
http://apotekonlinerecept.com/# apotek online
взять кредит в залог автомобиля
avtolombard-pid-zalog-pts.ru/kemerovo.html
автоломбард под залог
реплейсер для вайлдберриз бесплатно реплейсер для вайлдберриз бесплатно .
Официальный сайт 1win https://1win.kykyryza.ru ставки на спорт, киберспорт, казино, live-игры и слоты от лучших провайдеров. Моментальные выплаты, круглосуточная поддержка, щедрые акции и удобное мобильное приложение. Делай ставки и играй в казино на 1win — быстро, безопасно и выгодно!
Swiat emocji z 1win http://1win-pl.com Zaklady sportowe i e-sportowe, kasyno online, poker, gry wirtualne i wiele wiecej. Szybka rejestracja, bonus powitalny i natychmiastowa wyplata wygranych. 1win – wszystko, czego potrzebujesz do gry w jednym miejscu!
Официальный сайт 1win 1win kykyryza ставки на спорт, киберспорт, казино, live-игры и слоты от лучших провайдеров. Моментальные выплаты, круглосуточная поддержка, щедрые акции и удобное мобильное приложение. Делай ставки и играй в казино на 1win — быстро, безопасно и выгодно!
Swiat emocji z 1win http://www.1win-pl.com Zaklady sportowe i e-sportowe, kasyno online, poker, gry wirtualne i wiele wiecej. Szybka rejestracja, bonus powitalny i natychmiastowa wyplata wygranych. 1win – wszystko, czego potrzebujesz do gry w jednym miejscu!
кайт школа анапа
Kamagra Gel: Kamagra kaufen ohne Rezept – Kamagra Oral Jelly kaufen
аренда строительной техники
Аренда спецтехники и грузоперевозки от Строительно-коммерческой компании МИТ
Базируясь в Москве на Озерковском переулке, 12, компания предлагает всеобъемлющие услуги для строительно-монтажных работ и транспортной логистики. Готовность оперативно реагировать на заявки обеспечивается парком свыше 150 единиц спецтехники, каждая из которых проходит плановое техническое обслуживание.
Особенности предоставления услуг:
Быстрота выполнения:
Подача спецтехники в течение 2 часов после оформления заказа
Постоянное наличие аварийных бригад круглые сутки
Наличие собственного парка эвакуаторов
Рентабельность:
Фиксированные расценки без доплат в выходные
Система скидок до 20% при долгосрочной аренде
Точечный учет времени эксплуатации
Технические характеристики доступной техники:
Манипуляторы:
Возможность подъема грузов весом 3-12 тонн
Максимальная длина манипуляторной стрелы – 22 метра
Гарантированная доставка за 120 минут
Экскаваторы-погрузчики:
Максимальная глубина рытья 6.5 метров
Возможность перемещения со скоростью 41 км/ч
Вместимость ковша – 1.3 кубометра
Грузовые автомобили:
Возможность перевозки грузов весом 0.5-20 тонн
Вместимость кузова 2-92 м?
Многовариантная загрузка
Главные особенности:
Современный автопарк последних модификаций
Юридически чистая документация по всем стандартам
Система работы с НДС и гибкие условия оплаты
Полисы страхования на все виды услуг
Квалифицированный персонал управления техникой
Польза от работы с нами:
Экономия времени за счет сокращения простоев 40%
Гарантированная исправность оборудования
Финансовая выгода 30% против содержания техники
Детальная отчетность по всем операциям
Логистическая служба прорабатывает оптимальные маршруты доставки техники, с оформлением всех необходимых разрешений. Персональный менеджер контролирует выполнение каждого проекта.
Актуальные мировые новости о политике, обществе, экномике, бизнесе, медицине и других отраслях. Ежеденевная аналитическая информация в нашем блоге https://tovarlive.ru/
Все про стройку и ремонт. Актуальные интересные статьи о стройке и ремонте. Каждый найдет полезные материалы о дизайне, электрике, отоплении, кровле, сантехнике и другая полезная информация https://otoplenie-expert.com/
https://apotheekmax.shop/# Online apotheek Nederland met recept
деньги под залог птс срочно
avtolombard-pid-zalog-pts.ru
займ под залог авто с правом пользования
1win сайт https://alfatraders.borda.ru/?1-0-0-00004932-000-0-0-1743258210 .
Аренда спецтехники и грузоперевозки от Компании МИТ
Располагаясь в Москве на Озерковском переулке, 12, компания предоставляет комплексные решения для строительных и логистических задач. Возможность быстро откликаться на заявки обеспечивается парком свыше 150 единиц спецтехники, каждая из которых проходит регулярное ТО.
Преимущества сотрудничества:
Быстрота выполнения:
Гарантированная доставка техники в двухчасовой срок
Постоянное наличие аварийных бригад круглые сутки
Гарантированная доставка техники своими силами
Финансовая выгода:
Прозрачная система ценообразования без дополнительных сборов
Система скидок до 20% при долгосрочной аренде
Точечный учет времени эксплуатации
Технические характеристики доступной техники:
Манипуляторы:
Грузоподъемность от 3 до 12 тонн
Вылет стрелы максимум 22 метра
Время подачи – от 2 часов
Землеройная техника:
Глубина копания до 6.5 метров
Максимальная скорость движения 41 км/ч
Вместимость ковша – 1.3 кубометра
Перевозочные средства:
Возможность перевозки грузов весом 0.5-20 тонн
Объем кузова от 2 до 92 м?
Многовариантная загрузка
Основные достоинства:
Только новая техника актуальных моделей
Комплексное документационное обеспечение
Работа с НДС и возможность постоплаты
Полисы страхования на все виды услуг
Квалифицированный персонал управления техникой
Результаты для клиентов:
Уменьшение простоев строительства на 40%
Надежная работа всей техники
Финансовая выгода 30% против содержания техники
Полный комплект исполнительной документации
Логистическая служба прорабатывает оптимальные маршруты доставки техники, с оформлением всех необходимых разрешений. Индивидуальный куратор ведет каждый заказ.
Kamagra online bestellen Kamagra kaufen Kamagra Gel
Apotek hemleverans idag: Apotek hemleverans idag – Apotek hemleverans recept
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем:сервисные центры по ремонту техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
https://apotheekmax.com/# Online apotheek Nederland met recept
займ под залог птс авто
avtolombard-pid-zalog-pts.ru/nsk.html
кредит под залог авто в новосибирске
Apotek hemleverans recept: Apotek hemleverans idag – Apoteket online
https://kamagrapotenzmittel.shop/# Kamagra online bestellen
Looking for the best Telegram channels? Our service helps you discover popular and niche channels, find interesting content, and stay updated with the latest trends. Click the link and explore the world of Telegram: https://tgchannelslist.info/
Криптовалютная аналитика
события в мире единоборств
кредиты под залог машины с правом вождения
zaim-pod-zalog-pts1.ru/ekb.html
деньги под залог птс автомобиля авто
что делать с бонусным балансом на 1win https://obovsem.myqip.ru/?1-9-0-00000059-000-0-0-1743051936/ .
Apotheek Max: online apotheek – ApotheekMax
https://apotekonlinerecept.com/# apotek pa nett
взять деньги под залог машины
avtolombard-pid-zalog-pts.ru/kazan.html
автоломбард казань
https://kamagrapotenzmittel.shop/# Kamagra kaufen ohne Rezept
Ежедневные актуальные новости уходящего дня. Мы говорим о медицине, автопроме, обществе, науке и многом ином https://sp-piter.ru/
Kamagra kaufen [url=https://kamagrapotenzmittel.com/#]Kamagra kaufen ohne Rezept[/url] Kamagra kaufen
online apotheek: online apotheek – Apotheek Max
Find the Perfect Clock https://clocks-top.com/ for Any Space! Looking for high-quality clocks? At Top Clocks, we offer a wide selection, from alarm clocks to wall clocks, mantel clocks, and more. Whether you prefer modern, vintage, or smart clocks, we have the best options to enhance your home. Explore our collection and find the perfect timepiece today!
Find the Perfect Clock http://www.clocks-top.com for Any Space! Looking for high-quality clocks? At Top Clocks, we offer a wide selection, from alarm clocks to wall clocks, mantel clocks, and more. Whether you prefer modern, vintage, or smart clocks, we have the best options to enhance your home. Explore our collection and find the perfect timepiece today!
login jalantoto
Куршская коса заказать экскурсию kurshskaya-kosa-ekskursii.ru
1win pro http://www.obovsem.myqip.ru/?1-9-0-00000059-000-0-0-1743051936 .
Экскурсии на куршскую косу в калининграде http://kurshskaya-kosa-ekskursii.ru
кайт школа
кредит под птс автомобиля
zaim-pod-zalog-pts1.ru/kemerovo.html
займ под залог птс
http://apotekonlinerecept.com/# apotek online
Kamagra Oral Jelly kaufen: Kamagra kaufen – Kamagra online bestellen
The new TR Energy https://robotech.com/forums/viewthread/2237212 service aims to optimize both energy and bandwidth usage, solving the problem of high transaction fees that have previously hampered TRON’s scalability.
мосбет казино svstrazh.forum24.ru/?1-18-0-00000136-000-0-0-1743260517 .
The new TR Energy https://penzu.com/public/577c2d2b9fbe08b4 service aims to optimize both energy and bandwidth usage, solving the problem of high transaction fees that have previously hampered TRON’s scalability.
Hi there everyone, it’s my first visit at this website, and piece of writing is truly fruitful for me, keep up posting these posts.
https://ronson-group.ru/files/pag/promokodu_na_segodnya_mostbet_pri_registracii_bonus_do_25_000_rub.html
USDT娛樂城
Maispin——2025年最新USDT娛樂城,安全、快速、刺激!
歡迎來到 Maispin,2025年最具潛力的新秀 USDT娛樂城!在這裡,您只需提供 錢包地址 即可註冊,無需繁瑣的個人資訊,享受 安全、匿名、快速 的遊戲體驗。Maispin 提供超過 1000種賭場遊戲,涵蓋 真人百家樂、體育投注、老虎機、撲克、輪盤 等經典娛樂,讓您隨時隨地感受頂級賭場的刺激氛圍。我們與世界知名遊戲供應商合作,確保遊戲 公平公正,並提供高額彩金、獎勵活動,讓玩家輕鬆贏大獎!作為 USDT區塊鏈娛樂城,Maispin 存提款秒到帳,無需繁瑣審核,資金流動安全透明,讓玩家更安心地享受遊戲樂趣。立即加入 M宇宙,體驗前所未有的加密娛樂新潮流!
кайт анапа
Kamagra Oral Jelly kaufen: Kamagra Oral Jelly kaufen – Kamagra Original
http://apotheekmax.com/# de online drogist kortingscode
USDT娛樂城
Maispin——2025年最新USDT娛樂城,安全、快速、刺激!
歡迎來到 Maispin,2025年最具潛力的新秀 USDT娛樂城!在這裡,您只需提供 錢包地址 即可註冊,無需繁瑣的個人資訊,享受 安全、匿名、快速 的遊戲體驗。Maispin 提供超過 1000種賭場遊戲,涵蓋 真人百家樂、體育投注、老虎機、撲克、輪盤 等經典娛樂,讓您隨時隨地感受頂級賭場的刺激氛圍。我們與世界知名遊戲供應商合作,確保遊戲 公平公正,並提供高額彩金、獎勵活動,讓玩家輕鬆贏大獎!作為 USDT區塊鏈娛樂城,Maispin 存提款秒到帳,無需繁瑣審核,資金流動安全透明,讓玩家更安心地享受遊戲樂趣。立即加入 M宇宙,體驗前所未有的加密娛樂新潮流!
https://kamagrapotenzmittel.shop/# Kamagra Original
Женские хитрости и секреты красоты и моды, психологии отношений и кулинарии. Также наши статьи направлены на родителей и педагогов, интересующихся вопросами воспитания и обучения детей https://mentalar.ru/
подключить интернет в екатеринбурге в квартире
domashij-internet-ekaterinburg001.ru
подключение интернета екатеринбург
Мы изготавливаем дипломы психологов, юристов, экономистов и других профессий по приятным ценам. Цена зависит от выбранной специальности, года выпуска и образовательного учреждения. Стараемся поддерживать для заказчиков адекватную ценовую политику. Для нас важно, чтобы документы были доступны для большинства наших граждан. купить диплом вуз
Где купить диплом специалиста?
Наши специалисты предлагают выгодно и быстро купить диплом, который выполнен на оригинальной бумаге и заверен печатями, штампами, подписями. Диплом пройдет любые проверки, даже при использовании специфических приборов. Достигайте своих целей максимально быстро с нашей компанией.
Заказать диплом любого ВУЗа kupitediplom.ru/kupit-diplom-slesarya-9/
купить качественный диплом о высшем образовании
Having read this I thought it was really enlightening. I appreciate you taking the time and effort to put this information together. I once again find myself personally spending a lot of time both reading and posting comments. But so what, it was still worthwhile!
online apotheek: Beste online drogist – ApotheekMax
apotek online apotek online apotek online
These grilles are available in different designs, which will be encouraged
to you by our designers.
Добро пожаловать на vavadaukr.kiev.ua, предложит.
vavadaukr.kiev.ua – ваш источник, с целью.
Не упустите шанс посетить vavadaukr.kiev.ua, на котором.
интимный взгляд на.
вам доступны.
глубокий анализ.
Присоединяйтесь к сообществу vavadaukr.kiev.ua, что.
Здесь, на vavadaukr.kiev.ua, вы сможете, которые.
Ознакомьтесь с возможностями vavadaukr.kiev.ua, как и почему.
С vavadaukr.kiev.ua вы открываете.
Погружайтесь в содержание vavadaukr.kiev.ua, где вам предлагается.
обширный выбор, которые.
Преимущества vavadaukr.kiev.ua, что.
изучения новой информации.
vavadaukr.kiev.ua – это площадка для, где создаются.
На vavadaukr.kiev.ua мы предлагаем, изменят ваш подход.
Что предлагает vavadaukr.kiev.ua, вдохновляя на новые идеи.
вавада https://vavadaukr.kiev.ua/ .
augmented reality photos https://augmented-reality-platform.ru .
детская одежда с надписями https://www.dbkids.ru .
аренда лофтов аренда лофтов .
казино онлайн kg https://svstrazh.forum24.ru/?1-18-0-00000136-000-0-0-1743260517/ .
Приобрести документ университета вы имеете возможность у нас в Москве. newscloud22.nl/2022/10/31/jorn-luka-podcast/#comment-10329
Заказать диплом института!
Мы изготавливаем дипломы любой профессии по приятным ценам— diplom-onlinex.com/kupit-diplom-v-ekaterinburge-bistro-i-nadezhno-11/
домашний интернет екатеринбург
domashij-internet-ekaterinburg002.ru
интернет провайдеры по адресу
Мы можем предложить дипломы любой профессии по разумным ценам. Всегда стараемся поддерживать для заказчиков адекватную ценовую политику. Важно, чтобы дипломы были доступными для подавляющей массы наших граждан.
Приобретение документа, подтверждающего обучение в университете, – это выгодное решение. Купить диплом любого ВУЗа: diplomius-docs.com/kupit-diplom-kolledzha-22/
oxys crema peru
https://apotheekmax.shop/# online apotheek
I blog often and I genuinely appreciate your information. This article has truly peaked my interest. I’m going to bookmark your website and keep checking for new details about once a week. I subscribed to your RSS feed too.
http://hotel-golebiewski.phorum.pl/viewtopic.php?p=554092#554092
Beste online drogist: de online drogist kortingscode – Betrouwbare online apotheek zonder recept
Где заказать диплом по актуальной специальности?
Мы изготавливаем дипломы любой профессии по доступным тарифам. Мы можем предложить документы ВУЗов, расположенных в любом регионе России. Вы сможете приобрести диплом от любого учебного заведения, за любой год, указав актуальную специальность и оценки за все дисциплины. Документы выпускаются на “правильной” бумаге самого высшего качества. Это дает возможность делать настоящие дипломы, которые невозможно отличить от оригиналов. Они заверяются всеми обязательными печатями и штампами. Стараемся поддерживать для покупателей адекватную ценовую политику. Важно, чтобы дипломы были доступными для большого количества граждан. kupit-diplomyz24.com/kupit-diplom-starogo-obraztsa-2-2
https://apotheekmax.shop/# online apotheek
augmented reality story augmented reality story .
одежда с надписями http://www.dbkids.ru .
аренда лофт спб аренда лофт спб .
When it concerns needing domestic a/c, look no further than Climate Environmental.
1win официальный сайт 1win6003.ru .
провайдеры интернета по адресу
domashij-internet-ekaterinburg003.ru
какие провайдеры интернета есть по адресу екатеринбург
Kamagra Gel: kamagra – Kamagra Original
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Профессиональный информационный блог для бухгалтера и HR-специалиста – «Премьер Бух». Лучшая помощь в работе: полезные статьи, исследования и советы всегда под рукой https://premier-buh.ru/
Moderni nabytek stolni lampa kancelarska do kazdeho interieru – od minimalismu po klasiku. Vice nez 1000 modelu skladem. Online objednavka, pohodlna platba, pomoc navrhare. Zaridte svuj domov pohodlim!
Мы предлагаем дипломы психологов, юристов, экономистов и любых других профессий по выгодным ценам. Цена зависит от определенной специальности, года получения и образовательного учреждения. Всегда стараемся поддерживать для клиентов адекватную ценовую политику. Важно, чтобы дипломы были доступными для большого количества граждан. купить диплом о высшем образовании в оренбурге
Moderni nabytek levne komody do kazdeho interieru – od minimalismu po klasiku. Vice nez 1000 modelu skladem. Online objednavka, pohodlna platba, pomoc navrhare. Zaridte svuj domov pohodlim!
Где приобрести диплом специалиста?
Наши специалисты предлагают быстро заказать диплом, который выполнен на оригинальном бланке и заверен мокрыми печатями, водяными знаками, подписями. Данный диплом пройдет лубую проверку, даже с применением профессиональных приборов. Достигайте цели максимально быстро с нашими дипломами.
Приобрести диплом о высшем образовании diplomv-v-ruki.ru/kupit-diplom-farmatsevta-19/
онлайн казино Мир казино всегда манил яркими огнями, звоном монет и обещанием легкой удачи. От помпезных залов Лас-Вегаса до уютных уголков Монте-Карло, казино – это не только игра, но и целая индустрия, живущая по своим правилам. С развитием технологий казино перешли в онлайн-пространство. Онлайн-казино – это виртуальные платформы, предлагающие широкий спектр азартных игр, от классических слотов до карточных игр с живыми дилерами. Удобство, доступность и разнообразие делают онлайн-казино все более популярными.
купить диплом мва
скачат мостбет https://www.mostbet6008.ru .
Купить документ университета вы имеете возможность в нашей компании. http://www.newmiamipreconstruction.com
Где заказать диплом специалиста?
Наша компания предлагает выгодно и быстро заказать диплом, который выполняется на оригинальном бланке и заверен мокрыми печатями, водяными знаками, подписями. Диплом способен пройти лубую проверку, даже с использованием специально предназначенного оборудования. Решайте свои задачи быстро и просто с нашей компанией. Заказать диплом о высшем образовании! jamboz.com/read-blog/3581_kupit-vkr-kolledzha-cena.html
canadian pharmacy king reviews: canada pharmacy online legit – canadian neighbor pharmacy
canadian drugs pharmacy online canadian drugstore best canadian online pharmacy
Купить диплом о высшем образовании!
Мы предлагаем документы учебных заведений, которые находятся на территории всей России.
diplomist.com/poluchite-diplom-s-zaneseniem-v-reestr-dlya-kareri/
1 вин скачать 1 вин скачать .
Где купить диплом специалиста?
Мы изготавливаем дипломы любых профессий по выгодным ценам. Мы предлагаем документы техникумов, расположенных в любом регионе России. Вы можете заказать качественно сделанный диплом от любого заведения, за любой год, указав актуальную специальность и хорошие оценки за все дисциплины. Документы выпускаются на бумаге высшего качества. Это дает возможность делать настоящие дипломы, не отличимые от оригиналов. Документы заверяются всеми обязательными печатями и штампами. Всегда стараемся поддерживать для покупателей адекватную политику цен. Для нас важно, чтобы дипломы были доступны для большого количества наших граждан. okdiplom.ru/kupit-diplom-v-murmanske-2-2
Актуально обо всем! Ежедневные обзоры происходящего в мире и России. Новости бизнеса и общества, автомобилестроения и медицины https://sovety-tut.ru/
Agb Mexico Pharm: Agb Mexico Pharm – purple pharmacy mexico price list
мостбет скачать http://mostbet6008.ru/ .
Купить диплом о высшем образовании!
Мы предлагаем дипломы любых профессий по доступным тарифам— diplomass.com/kupit-diplom-v-krasnoyarske-22/
п»їbest mexican online pharmacies: Agb Mexico Pharm – mexican mail order pharmacies
Мы предлагаем дипломы любой профессии по приятным тарифам. Стараемся поддерживать для заказчиков адекватную политику тарифов. Для нас очень важно, чтобы дипломы были доступными для большого количества наших граждан.
Заказ документа, подтверждающего обучение в университете, – это грамотное решение. Купить диплом о высшем образовании: diplom-city24.ru/kupit-diplom-srednee-obrazovanie/
http://agbmexicopharm.com/# reputable mexican pharmacies online
работа за границей телеграм
Hey there! Do you know if they make any plugins to protect against hackers? I’m kinda paranoid about losing everything I’ve worked hard on. Any recommendations?
http://gzew.phorum.pl/viewtopic.php?p=298774#298774
wan win [url=www.1win6050.ru]www.1win6050.ru[/url] .
Официальный сайт 1win https://1win.onedivision.ru спортивные ставки, киберспорт, казино, покер, рулетка и многое другое. Надежный сервис, поддержка 24/7, удобный интерфейс. Забирай бонус за регистрацию уже сейчас!
Официальный сайт 1win http://1win.onedivision.ru спортивные ставки, киберспорт, казино, покер, рулетка и многое другое. Надежный сервис, поддержка 24/7, удобный интерфейс. Забирай бонус за регистрацию уже сейчас!
Agb Mexico Pharm: best online pharmacies in mexico – mexico pharmacies prescription drugs
Добро пожаловать в 1win https://1win.onedivision.ru азарт, спорт и выигрыши рядом! Ставь на матчи, играй в казино, участвуй в турнирах и получай крутые бонусы. Удобный интерфейс, быстрая регистрация и выплаты.
Добро пожаловать в 1win https://1win.onedivision.ru азарт, спорт и выигрыши рядом! Ставь на матчи, играй в казино, участвуй в турнирах и получай крутые бонусы. Удобный интерфейс, быстрая регистрация и выплаты.
mexican border pharmacies shipping to usa: purple pharmacy mexico price list – Agb Mexico Pharm
buying prescription drugs in mexico: best online pharmacies in mexico – best online pharmacies in mexico
кайт египет
Бесплатные Steam аккаунты t.me/GGZoneSteam/ с играми и бонусами. Проверенные логины и пароли, ежедневное обновление, удобный поиск. Забирай свой шанс на крутой аккаунт без лишних действий!
Все про уход за лицом и телом. Массаж, полезные упражнения, косметология, очищение и многое другое на страницах нашего блога https://facesave.ru/
Бесплатные Steam аккаунты https://t.me/GGZoneSteam/ с играми и бонусами. Проверенные логины и пароли, ежедневное обновление, удобный поиск. Забирай свой шанс на крутой аккаунт без лишних действий!
Купить диплом любого ВУЗа!
Мы готовы предложить документы любых учебных заведений, которые расположены в любом регионе России.
diplomidlarf.ru/kupit-diplom-s-garantiej-kachestva-i-vneseniem-v-reestr/
http://gocanadapharm.com/# canadian pharmacies online
кайт блага
www india pharm online pharmacy india www india pharm
криптовалюта Мир казино – это захватывающая вселенная, где переплетаются азарт, стратегия и технологические инновации. Онлайн казино предлагают широкий спектр игр, от классических слотов до захватывающих настольных игр, предоставляя игрокам возможность испытать удачу и применить свои навыки. Стратегии играют ключевую роль в успехе. Будь то блэкджек, покер или рулетка, понимание правил и умение анализировать ситуацию могут значительно повысить шансы на выигрыш. Важно помнить о разумном управлении банкроллом и осознанном подходе к игре.
1win kg https://1win6050.ru/ .
Доска объявлений https://estul.ru/blog по всей России: продавай и покупай товары, заказывай и предлагай услуги. Быстрое размещение, удобный поиск, реальные предложения. Каждый после регистрации получает на баланс аккаунта 100? для возможности бесплатного размещения ваших объявлений
Доска объявлений https://estul.ru/blog по всей России: продавай и покупай товары, заказывай и предлагай услуги. Быстрое размещение, удобный поиск, реальные предложения. Каждый после регистрации получает на баланс аккаунта 100? для возможности бесплатного размещения ваших объявлений
mexico drug stores pharmacies: Agb Mexico Pharm – mexican pharmaceuticals online
В Санкт-Петербурге остекление балконов с использованием пластиковых окон — это не просто улучшение внешнего вида вашего дома, но и важный шаг к созданию комфортного и теплого пространства, пластиковые окна обладают высокими теплоизоляционными и шумоизоляционными свойствами, что делает ваш балкон уютным и безопасным местом для отдыха, они помогают избежать потерь тепла, что особенно важно в холодное время года, если вы хотите создать уютное и стильное пространство на своем балконе, пластиковые окна — это отличный выбор, который прослужит вам долго и эффективно https://osteklenie-balkonov-v-spb.pro/
www canadianonlinepharmacy: canadian mail order pharmacy – canadian pharmacy 24 com
Искали идеальный сайт для знакомств? В Красной Поляне открылись идеальные условия для тех, кто хочет познакомиться с девушками 18+. Яркий интерфейс, много возможностей для общения и масса новых знакомств обеспечивают хороший опыт для всех пользователей сайта – http://sochi-night.vip/
рулонные шторы на окна цена рулонные шторы на окна цена .
mail order pharmacy india: www india pharm – buy prescription drugs from india
USDT娛樂城
Maispin——2025年最新USDT娛樂城,安全、快速、刺激!
歡迎來到 Maispin,2025年最具潛力的新秀 USDT娛樂城!在這裡,您只需提供 錢包地址 即可註冊,無需繁瑣的個人資訊,享受 安全、匿名、快速 的遊戲體驗。Maispin 提供超過 1000種賭場遊戲,涵蓋 真人百家樂、體育投注、老虎機、撲克、輪盤 等經典娛樂,讓您隨時隨地感受頂級賭場的刺激氛圍。我們與世界知名遊戲供應商合作,確保遊戲 公平公正,並提供高額彩金、獎勵活動,讓玩家輕鬆贏大獎!作為 USDT區塊鏈娛樂城,Maispin 存提款秒到帳,無需繁瑣審核,資金流動安全透明,讓玩家更安心地享受遊戲樂趣。立即加入 M宇宙,體驗前所未有的加密娛樂新潮流!
https://gocanadapharm.com/# ed meds online canada
USDT娛樂城
Maispin——2025年最新USDT娛樂城,安全、快速、刺激!
歡迎來到 Maispin,2025年最具潛力的新秀 USDT娛樂城!在這裡,您只需提供 錢包地址 即可註冊,無需繁瑣的個人資訊,享受 安全、匿名、快速 的遊戲體驗。Maispin 提供超過 1000種賭場遊戲,涵蓋 真人百家樂、體育投注、老虎機、撲克、輪盤 等經典娛樂,讓您隨時隨地感受頂級賭場的刺激氛圍。我們與世界知名遊戲供應商合作,確保遊戲 公平公正,並提供高額彩金、獎勵活動,讓玩家輕鬆贏大獎!作為 USDT區塊鏈娛樂城,Maispin 存提款秒到帳,無需繁瑣審核,資金流動安全透明,讓玩家更安心地享受遊戲樂趣。立即加入 M宇宙,體驗前所未有的加密娛樂新潮流!
canadian drugstore online: GoCanadaPharm – legitimate canadian pharmacies
1вин официальный сайт [url=http://kharkovbynight.forum24.ru/?1-5-0-00000235-000-0-0]1вин официальный сайт[/url] .
роликовые шторы на окна роликовые шторы на окна .
mexican mail order pharmacies: medication from mexico pharmacy – Agb Mexico Pharm
wan win wan win .
mexico drug stores pharmacies mexico pharmacies prescription drugs buying prescription drugs in mexico
www india pharm: indianpharmacy com – www india pharm
1вин войти https://1win6051.ru .
michelin x-ice north 4 suv 235/55 r18 [url=www.www.proalbea.ru/shiny-michelin-preimushhestva-i-nedostatki.html/]www.www.proalbea.ru/shiny-michelin-preimushhestva-i-nedostatki.html/[/url] .
игра ракета на деньги 1win http://www.girikms.forum24.ru/?1-2-0-00000264-000-0-0 .
https://wwwindiapharm.shop/# india pharmacy
шиномонтаж звенигород шиномонтаж звенигород .
1win online https://www.girikms.forum24.ru/?1-2-0-00000264-000-0-0 .
Самые новые анекдоты https://www.anekdotovmir.ru — коротко, метко и смешно! Подборка актуального юмора: от жизненных до политических. Заходи за порцией хорошего настроения!
Самые новые анекдоты https://www.anekdotovmir.ru — коротко, метко и смешно! Подборка актуального юмора: от жизненных до политических. Заходи за порцией хорошего настроения!
Блог, посвященные всем видам сварочных работ с интересными и полезными публикациями https://svarkalegko.com/
buying prescription drugs in mexico: mexican pharmaceuticals online – reputable mexican pharmacies online
michelin pilot sport 5 245/40 r18 97y http://www.proalbea.ru/shiny-michelin-preimushhestva-i-nedostatki.html .
Expect to invest between ₤ 500 and ₤ 1500 for a
split AC that will be made use of in one room.
Кладбища Видного http://bulatnikovskoe.ru график работы, схема участков, порядок захоронения и перезахоронения. Все важные данные в одном месте: для родственников, посетителей и организаций.
mexico drug stores pharmacies: Agb Mexico Pharm – Agb Mexico Pharm
Кладбища Видного bulatnikovskoe.ru график работы, схема участков, порядок захоронения и перезахоронения. Все важные данные в одном месте: для родственников, посетителей и организаций.
шиномонтаж чехов https://hondahybrid.ru/forum/topic/2886-kakie-uslugi-okazyvaet-shinomontazh/ .
Мы изготавливаем дипломы любой профессии по выгодным тарифам. Дипломы производят на фирменных бланках Приобрести диплом ВУЗа diplomk-vo-vladivostoke.ru
canada cloud pharmacy: canadian pharmacy uk delivery – canada rx pharmacy
1win официальный сайт вход [url=1win6051.ru]1win6051.ru[/url] .
1win kg скачать http://cinemania.forum24.ru/?1-15-0-00001911-000-0-0-1743258043/ .
Представьте: шубе из соболя 50 лет, она пережила эпохи, видела балы, тайные встречи, рассветы над дворцами. Но её реинкарнировали(перешили)! Роскошь, ставшая тенью самой себя… Как можно было так поступить? Вы бы осмелились изменить историю, стереть отпечатки времени? Смотрите.. https://t.me/ElenaMeel/32
http://agbmexicopharm.com/# mexican drugstore online
Все, что поможет каждому разобраться в огромном количестве софта, драйверов, конвертеров и веб-сервисов. Мы публикуем в нашем блоге материалы о проблемах “синих экранов”, полезных программах, технологиях и многом ином https://chopen.net/
1 win.kg 1 win.kg .
mexico drug stores pharmacies Agb Mexico Pharm Agb Mexico Pharm
medication from mexico pharmacy: mexican drugstore online – best online pharmacies in mexico
canadian family pharmacy: GoCanadaPharm – canadian pharmacy no rx needed
кардан сервис москва http://www.4-x-4.ru/remont-i-balansirovka-kardannyh-valov// .
1winn http://1win6004.ru .
мосбет https://mostbet6009.ru .
Портал Fact Store публикует самые свежие и актуальные новости Беларуси, России и мира ежедневно итолько для Вас https://factstore.ru/
Agb Mexico Pharm: mexican pharmaceuticals online – mexican drugstore online
ремонт крестовин ремонт крестовин .
мостбет промокод https://mostbet6009.ru .
pharmacy wholesalers canada: GoCanadaPharm – reddit canadian pharmacy
http://gocanadapharm.com/# pharmacy rx world canada
остекление балконов и лоджий цена https://balkon-spb-2.ru/
canadian pharmacy service: GoCanadaPharm – safe canadian pharmacy
1 win 1 win .
mitolyn is a natural dietary supplement specifically outlined to enhance metabolism and support weight loss. Its potent blend of ingredients works to increase energy levels, promote fat burning
игра ракета на деньги 1win игра ракета на деньги 1win .
Agb Mexico Pharm: purple pharmacy mexico price list – mexico drug stores pharmacies
I need to to thank you for this great read!! I absolutely loved every little bit of it. I’ve got you book marked to check out new things you post…
USDT娛樂城
Maispin——2025年最新USDT娛樂城,安全、快速、刺激!
歡迎來到 Maispin,2025年最具潛力的新秀 USDT娛樂城!在這裡,您只需提供 錢包地址 即可註冊,無需繁瑣的個人資訊,享受 安全、匿名、快速 的遊戲體驗。Maispin 提供超過 1000種賭場遊戲,涵蓋 真人百家樂、體育投注、老虎機、撲克、輪盤 等經典娛樂,讓您隨時隨地感受頂級賭場的刺激氛圍。我們與世界知名遊戲供應商合作,確保遊戲 公平公正,並提供高額彩金、獎勵活動,讓玩家輕鬆贏大獎!作為 USDT區塊鏈娛樂城,Maispin 存提款秒到帳,無需繁瑣審核,資金流動安全透明,讓玩家更安心地享受遊戲樂趣。立即加入 M宇宙,體驗前所未有的加密娛樂新潮流!
india pharmacy indianpharmacy com www india pharm
услуги по продаже аккаунтов marketpleys-akkauntov.ru
аренда шатров и тентов шатры аренда шатров и тентов шатры .
кайтсёрфинг в хургаде
Agb Mexico Pharm: п»їbest mexican online pharmacies – pharmacies in mexico that ship to usa
заработок на аккаунтах http://marketpleys-akkauntov.ru
https://wwwindiapharm.com/# www india pharm
On the other hand, you may locate that it is unneeded or inefficient and hence you would rather do without it.
Maispin——2025年最新USDT娛樂城,安全、快速、刺激!
歡迎來到 Maispin,2025年最具潛力的新秀 USDT娛樂城!在這裡,您只需提供 錢包地址 即可註冊,無需繁瑣的個人資訊,享受 安全、匿名、快速 的遊戲體驗。Maispin 提供超過 1000種賭場遊戲,涵蓋 真人百家樂、體育投注、老虎機、撲克、輪盤 等經典娛樂,讓您隨時隨地感受頂級賭場的刺激氛圍。我們與世界知名遊戲供應商合作,確保遊戲 公平公正,並提供高額彩金、獎勵活動,讓玩家輕鬆贏大獎!作為 USDT區塊鏈娛樂城,Maispin 存提款秒到帳,無需繁瑣審核,資金流動安全透明,讓玩家更安心地享受遊戲樂趣。立即加入 M宇宙,體驗前所未有的加密娛樂新潮流!
Идеи для подарков
Где купить диплом по необходимой специальности?
Готовый диплом с нужными печатями и подписями отвечает стандартам, неотличим от оригинала. Не стоит откладывать свои мечты и задачи на несколько лет, реализуйте их с нами – отправляйте быструю заявку на диплом прямо сейчас! Получить диплом о высшем образовании – запросто! windows1.listbb.ru/viewtopic.phpf=3&t=1313
canadian pharmacy checker: go canada pharm – legit canadian pharmacy online
This is my first time visit at here and i am genuinely pleassant to read everthing at one place.
нью ретро официальный сайт казино
Где приобрести диплом по актуальной специальности?
Мы предлагаем дипломы любой профессии по невысоким ценам. Мы можем предложить документы ВУЗов, которые расположены на территории всей РФ. Можно купить диплом за любой год, включая документы старого образца. Дипломы и аттестаты выпускаются на “правильной” бумаге высшего качества. Это позволяет делать настоящие дипломы, которые невозможно отличить от оригиналов. Документы будут заверены всеми обязательными печатями и штампами. Стараемся поддерживать для заказчиков адекватную ценовую политику. Для нас очень важно, чтобы дипломы были доступны для большого количества граждан. diploms-vuza.com/kupit-diplom-medbrata-2-5
If its a huge building you’re seeking to condition, VRF
a/c systems are for you.
купить диплом о среднем специальном образовании новосибирск
Spread out the price of your cooling setup with financing from our money partner
Origin Finance.
аренда шатров тентов аренда шатров тентов .
Приобрести документ о получении высшего образования можно у нас в Москве. Мы предлагаем документы об окончании любых университетов Российской Федерации. Вы сможете получить диплом по любой специальности, включая документы СССР. Гарантируем, что при проверке документов работодателями, подозрений не появится. vuz-diplom.ru/kupit-diplom-s-zaneseniem-v-reestr-bistro-i-bezopasno-9/
lipozem is is an advanced dietary supplement developed to support your weight loss objectives while boosting overall health and energy levels.
Agb Mexico Pharm: medication from mexico pharmacy – Agb Mexico Pharm
магазин аккаунтов https://birzha-accauntov.ru/
маркетплейс аккаунтов соцсетей marketpleys akkauntov
I think that everything published was very reasonable. However, what about this? suppose you typed a catchier title? I mean, I don’t wish to tell you how to run your blog, but what if you added something that grabbed folk’s attention? I mean %BLOG_TITLE% is kinda plain. You should look at Yahoo’s home page and note how they create post titles to get people to open the links. You might add a related video or a picture or two to grab readers interested about everything’ve got to say. In my opinion, it could make your website a little bit more interesting.
https://www.roxgo.cl/index.php?app=gallery&module=gallery&controller=view&id=4520&context=new
Howdy! This is my 1st comment here so I just wanted to give a quick shout out and say I truly enjoy reading your blog posts. Can you recommend any other blogs/websites/forums that cover the same topics? Thanks a lot!
https://x.com/CleoCass1/status/1907819242256285730
That is very interesting, You are an excessively professional blogger. I have joined your rss feed and stay up for in quest of extra of your fantastic post. Also, I have shared your web site in my social networks
https://buymeacoffee.com/robertwyatt/meilleur-code-promo-1xbet-bonus-jusqu-130-3593551
What’s up, yup this piece of writing is really good and I have learned lot of things from it regarding blogging. thanks.
https://ameblo.jp/codede1xbet200/entry-12892297245.html
интернет тарифы казань
domashij-internet-kazan001.ru
подключить интернет по адресу
canadian pharmacy meds reviews: pharmacy com canada – canadian pharmacy online ship to usa
https://agbmexicopharm.shop/# mexico drug stores pharmacies
маркетплейс игровых аккаунтов маркетплейс для реселлеров
аккаунты с балансом magazin-accauntov.ru
BANDAR JUDI
india online pharmacy: india online pharmacy – www india pharm
mexican rx online: Agb Mexico Pharm – mexican pharmaceuticals online
It’s nearly impossible to find well-informed people on this subject, but you sound like you know what you’re talking about! Thanks
купить диплом в москве
This is very fascinating, You’re a very skilled blogger. I’ve joined your feed and look ahead to searching for more of your magnificent post. Additionally, I have shared your website in my social networks
https://deogiricollege.org/pag/1xbet_promo_code___welcome-bonus.html
натяжные потолки быстро https://potolki-spb-2.ru/
www india pharm buy medicines online in india www india pharm
интернет провайдеры казань по адресу
domashij-internet-kazan002.ru
провайдеры казань
купить алкоголь ночью +с доставкой http://dostavka-alkogolya248.ru/ .
hwid spoofer download hwid spoofer free hwid spoofer hwid spoofer download hwid spoofer crack
нейросеть для рефератов http://www.studgen.ru .
Где купить диплом по нужной специальности?
Мы изготавливаем дипломы психологов, юристов, экономистов и прочих профессий по приятным тарифам. Мы можем предложить документы ВУЗов, которые расположены в любом регионе Российской Федерации. Вы можете заказать качественно напечатанный диплом за любой год, указав подходящую специальность и оценки за все дисциплины. Документы печатаются на бумаге высшего качества. Это дает возможности делать настоящие дипломы, которые невозможно отличить от оригиналов. Они заверяются всеми обязательными печатями и подписями. Стараемся поддерживать для покупателей адекватную политику тарифов. Для нас очень важно, чтобы документы были доступны для большинства граждан. diplom-insti.ru/kupit-diplom-vospitatelya-2-5
canadian pharmacy online reviews: canadian pharmacy ed medications – pharmacy canadian
Заказать документ института вы сможете в нашей компании в столице. diplomd-magazinp.ru/kupit-diplom-svarshika
http://gocanadapharm.com/# ordering drugs from canada
https://dzen.ru/a/Z-wZzKk7V2mgAjD3
доставка алкоголя на дом москва http://dostavka-alkogolya248.ru/ .
подключить домашний интернет казань
domashij-internet-kazan003.ru
интернет провайдер казань
площадка для продажи аккаунтов ploshadka-dlya-prodazhi-akkauntov.ru/
world pharmacy india: www india pharm – www india pharm
маркетплейс аккаунтов соцсетей https://ploshadka-dlya-prodazhi-akkauntov.ru
canadian pharmacy uk delivery: northern pharmacy canada – canadian drugs
1vin kg http://www.1win6052.ru .
диплом с помощью нейросети https://www.studgen.ru .
Заказать диплом университета по выгодной цене возможно, обращаясь к надежной специализированной компании. Приобрести документ университета можно в нашем сервисе. diplomaj-v-tule.ru/kupit-diplom-instituta-s-provodkoj-3
мостбет мобильная версия скачать http://www.mostbet6010.ru .
Ремонт смартфонов https://techno-line.store .
Мы изготавливаем дипломы психологов, юристов, экономистов и прочих профессий по приятным тарифам. Стоимость будет зависеть от выбранной специальности, года выпуска и образовательного учреждения. Всегда стараемся поддерживать для клиентов адекватную политику цен. Для нас важно, чтобы документы были доступны для большого количества граждан. купить диплом хирурга
подключить интернет в москве в квартире
domashij-internet-msk001.ru
интернет по адресу дома
что такое 1win что такое 1win .
скачать 1win с официального сайта скачать 1win с официального сайта .
ZithPharmOnline: buy zithromax 1000 mg online – buy zithromax online cheap
Pred Pharm Net prednisone prescription for sale Pred Pharm Net
Hi there, its pleasant piece of writing regarding media print, we all know media is a impressive source of facts.
https://polygraph.od.ua/bu-sklo-dlya-far-plyusy-minusy
1win партнерка вход https://www.freereklama.borda.ru/?1-5-0-00000114-000-0-0-1743258539 .
продажа аккаунтов https://kupit-accaunt.ru/
mostbet скачать на телефон бесплатно андроид http://www.mostbet6010.ru .
биржа аккаунтов http://kupit-accaunt.ru
Дешевое такси Болгария Служба Такси Эклипс предлагает доступные трансферы из аэропортов Бургас, Варна, София и Белград до популярных курортов Болгарии. Встреча с табличкой, помощь с багажом и комфортная поездка до места назначения. Обслуживаем Солнечный Берег, Созополь, Банско и другие направления. Для групп от 5 человек – специальные условия!
Покупка официального диплома через качественную и надежную фирму дарит ряд достоинств. Данное решение дает возможность сэкономить как личное время, так и существенные финансовые средства. Тем не менее, только на этом выгоды не ограничиваются, достоинств гораздо больше.Мы изготавливаем дипломы любой профессии. Дипломы производят на подлинных бланках. Доступная стоимость в сравнении с крупными расходами на обучение и проживание. Заказ диплома ВУЗа является мудрым шагом.
Купить диплом о высшем образовании: diplom-top.ru/kupite-originalnij-diplom-s-zaneseniem-v-reestr-sejchas/
Whats up are using WordPress for your site platform? I’m new to the blog world but I’m trying to get started and set up my own. Do you need any html coding knowledge to make your own blog? Any help would be really appreciated!
https://c0de1xbet100.weebly.com/
Pred Pharm Net: Pred Pharm Net – prednisone 50 mg prices
https://clomfastpharm.shop/# can i get generic clomid prices
amoxicillin brand name: AmOnlinePharm – AmOnlinePharm
Huawei телефоны https://www.techno-line.store .
домашний интернет тарифы москва
domashij-internet-msk002.ru
провайдер интернета по адресу москва
Заказать диплом института по невысокой цене возможно, обращаясь к проверенной специализированной компании. Купить документ о получении высшего образования вы сможете в нашей компании в Москве. diplom-ryssia.com/bistraya-i-nadezhnaya-pokupka-diploma-s-reestrom-v-rossii
Nice post. I learn something totally new and challenging on websites I stumbleupon everyday. It’s always helpful to read through articles from other authors and practice something from their sites.
https://tsscscascsdddedewededwfmeee.com/
Заказать документ университета вы имеете возможность в нашем сервисе. diplomers.com/kupit-diplom-kandidata-nauk-2
покупка аккаунтов prodat-akkaunt.ru
Хотите понять актуальные доставка грузов по россии цены? Загляните на сайт «Мак-Транс». Там всё ясно и по делу. Компания работает открыто, без скрытых условий. Отличный выбор, если важна прозрачность и качество. Рекомендуем тем, кто ценит чёткий сервис.
безопасная сделка аккаунтов prodat-akkaunt.ru/
Профессиональная помощь в сфере магических услуг. Искусство высшей магии.
Ясновидение/Руны/Ритуалы
Диагностика / Консультация
* Диагностика на наличие магического негатива, порчи, приворота, воздействия
* Диагностика энергетики
* Выявление проблем и препятствий
* Ответы на вопросы
Чистка магического и энергетического негатива.
Защита на всех уровнях.
Открытие дорог.
Открытие финансового канала.
(на основании диагностики производим чистку негатива, убираем любые деструктивные программы включая порчу на смерть, кладбищенскую порчу, порчу через подклад, подселение сущности, приворот и другие деструктивные программы разрушающие вашу жизнь)
восстанавливаем вашу жизнь и настраиваем по всем сферам жизни
Магия для решения Бизнес задач и Финансовых вопросов
(моя самая любимая сфера деятельности)
* Убрать препятствия
* Защита на вас и ваш бизнес
* Помощь в судах
* Выявление и решение проблем вашего бизнеса через магию
Любовная магия
* Определение совместимости партнеров в браке и при вступлении в брак
* Защита семьи и отношений
* Розжиг чувств в паре (это новый виток отношений. реанимация любви)
* Создание условий, которые приведут к романтическим отношениям и к созданию семьи
Решение любых актуальных для вас проблем
* Выявить и убрать блоки мешающие достичь цели
– магия рун
– магия древних ритуалов
– магия символов, углов, пространства
– планетарная магия
– пространственная алхимия
– работа через сознание и подсознание
Все работы проводятся очень экологично и без какого-либо вреда
Также проводятся специальные ритуалы позволяющие развернуть вашу жизнь на 360 градусов, получить желаемое, открыть дороги, притянуть любовь и создать жизнь мечты
Телеграмм канал Искусство Высшей Магии https://t.me/magvip
Для связи: WHATSAPP +44 7435 250025
*** для заказа присылайте фото для диагностики, имя и ваш вопрос.
Услуги осуществляются на условиях 100% предоплаты.
P.S. Если человек знает для чего ему нужно желаемое – значит он может это достичь
Приобрести диплом о высшем образовании!
Мы можем предложить документы учебных заведений, расположенных в любом регионе Российской Федерации.
kupit-diplom24.com/kupit-diplom-s-zaneseniem-v-reestr-bistro-i-nadezhno-23/
ZithPharmOnline: ZithPharmOnline – ZithPharmOnline
When I originally left a comment I seem to have clicked the -Notify me when new comments are added- checkbox and now every time a comment is added I recieve four emails with the exact same comment. Perhaps there is a way you are able to remove me from that service? Thanks a lot.
мостбет скачать на андроид http://mostbet6029.ru/ .
подключить интернет тарифы москва
domashij-internet-msk003.ru
провайдеры интернета москва
покупка аккаунтов безопасная сделка аккаунтов
один вин http://snatkina.borda.ru/?1-5-0-00000311-000-0-0-1743258575/ .
аккаунты с балансом биржа аккаунтов
ZithPharmOnline: purchase zithromax online – can you buy zithromax over the counter
https://zithpharmonline.com/# ZithPharmOnline
Ищете профессиональную помощь в борьбе с зависимостью? Подробная информация доступна здесь https://www.indiegogo.com/individuals/38530018
cost of prednisone 10mg tablets: Pred Pharm Net – buy 10 mg prednisone
Мечтаете о роскошном авто, сочетающем в себе передовые технологии и безупречный дизайн? Дубай – это сокровищница автомобильных шедевров, где представлены модели, способные удовлетворить самый взыскательный вкус. Компания ChatMost предлагает полный спектр услуг по заказу и доставке автомобилей из Дубая в Россию, избавляя вас от хлопот и рисков. Доставка авто из ОАЭ в Россию
1вин вход с компьютера https://www.snatkina.borda.ru/?1-5-0-00000311-000-0-0-1743258575 .
Сделать брови Анапа Уже 10 лет Делаем качественный перманентный макияж в Анапе без синих красных бровей. Только премиум материалы , стерильно и без боли, работаем в любых техниках.
Обучаем перманентному макияжу с нуля со свидетельством установленного образца , ведем курсы бровистов
zithromax ZithPharmOnline ZithPharmOnline
get clomid: Clom Fast Pharm – where can i get generic clomid
MetaMask Extension offers top security. I feel confident storing my crypto assets knowing they are well-protected.
Где приобрести диплом по нужной специальности?
Наши специалисты предлагаютбыстро и выгодно купить диплом, который выполнен на бланке ГОЗНАКа и заверен печатями, водяными знаками, подписями. Диплом пройдет любые проверки, даже с использованием профессиональных приборов. Достигайте своих целей быстро с нашей компанией. Заказать диплом ВУЗа! nsibirsk.ru/forum/obyavleniya/topic-33790.html
хостинг для html сайтов облачный vps хостинг
кайт сафари
Simply want to say your article is as amazing. The clarity to your put up is just nice and that i could think you’re an expert in this subject. Fine together with your permission allow me to grab your feed to keep updated with impending post. Thank you 1,000,000 and please continue the rewarding work.
https://adrenalinsport.dp.ua/top-5-naykraschykh-skelts-dlya-far-reitynh-nadiynosti-ta-dovhovichnosti
vps хостинг недорого зарегистрировать хостинг украина
какие провайдеры интернета есть по адресу нижний новгород
domashij-internet-nizhnij-novgorod001.ru
подключение интернета нижний новгород
Где приобрести диплом специалиста?
Наша компания предлагает выгодно и быстро заказать диплом, который выполняется на бланке ГОЗНАКа и заверен печатями, водяными знаками, подписями. Данный диплом пройдет любые проверки, даже при помощи специально предназначенного оборудования. Решайте свои задачи быстро и просто с нашим сервисом.
Заказать диплом о высшем образовании fastdiploms.com/kupit-diplom-v-novokuznetske-8/
Где купить диплом специалиста?
Мы предлагаем документы об окончании любых университетов Российской Федерации. Документы изготавливаются на настоящих бланках. Рєthathwamasijobs.com/companies/premialnie-diplom-24
where can you buy zithromax: ZithPharmOnline – zithromax order online uk
VANGPOKER- новое идеальное место для покера!
Ведущая в мире платформа блокчейн покера!
Вы можете стать одними из первых участников нового проекта с честным рейкбэком, бонусом на первый депозит 200%, быстрым вводом и выводом, и отсутствием KYC.
Приглашаем вас присоединится к крупнейшему сообществу VANGPOKER в телеграмм, зарегестрироваться в VANGPOKER и получать дополнительные бонусы и повышенный рейкбэк. зарегестрироваться в VANGPOKER
https://clomfastpharm.shop/# Clom Fast Pharm
gluco extend is a nutritional supplement crafted to help maintain balanced blood sugar levels.
AmOnlinePharm: AmOnlinePharm – AmOnlinePharm
Мы предлагаем дипломы любой профессии по приятным ценам. Всегда стараемся поддерживать для заказчиков адекватную политику тарифов. Важно, чтобы дипломы были доступными для большого количества граждан.
Заказ документа, подтверждающего окончание института, – это выгодное решение. Приобрести диплом о высшем образовании: diplom-insti.ru/kupit-diplom-ob-okonchanii-instituta-3/
Every a/c system setup includes an air to air exterior pump and interior system, which is all you require.
мостбет скачать бесплатно http://mostbet6029.ru .
провайдеры по адресу
domashij-internet-nizhnij-novgorod002.ru
домашний интернет тарифы нижний новгород
AmOnlinePharm: where to get amoxicillin over the counter – amoxicillin brand name
суши роллы https://sushibarnaul.ru
ломбард скупка золота с бриллиантами b-gold.ru http://www.of-md.com/jwe-qs/ .
купить суши роллы суши вок барнаул
скупка золота цена за грамм скупка золота цена за грамм .
descărca 1win 1win5004.ru .
лучший интернет провайдер нижний новгород
domashij-internet-nizhnij-novgorod003.ru
провайдеры по адресу дома
ZithPharmOnline: ZithPharmOnline – ZithPharmOnline
Основное преимущество лизинга – минимальные первоначальные вложения (10–30% стоимости) и включение платежей в расходы компании, что уменьшает налог на прибыль. Кроме того, НДС по лизинговым платежам можно компенсировать, а сам актив легко обновлять без крупных единовременных затрат. Срок договора обычно составляет 1–5 лет, после чего оборудование можно вернуть, продлить аренду или выкупить по остаточной стоимости https://bin-leasing.ru/
https://predpharmnet.com/# drug prices prednisone
lisinopril 2018 lisinopril 10 mg brand name in india Lisin Express
lisinopril 5 mg daily: 20 mg lisinopril tablets – Lisin Express
It has a cooling capacity of 7,000 BTU, suggesting it is good to cool tool sized rooms.
скупка золота в москве цена за грамм на сегодня 585 b-gold.ru скупка золота в москве цена за грамм на сегодня 585 b-gold.ru .
zithromax online australia: zithromax z-pak – ZithPharmOnline
скупка золота в москве за грамм цена скупка золота в москве за грамм цена .
Spot on with this write-up, I truly feel this web site needs much more attention. I’ll probably be back again to read more, thanks for the information!
Заказать диплом института по выгодной цене возможно, обращаясь к проверенной специализированной компании. Мы оказываем услуги по продаже документов об окончании любых ВУЗов РФ. Приобрести диплом любого ВУЗа– damdiplomisa.com/kupit-diplom-s-reestrom-po-razumnoj-tsene-2/
какие провайдеры по адресу
domashij-internet-novosibirsk001.ru
провайдеры интернета в новосибирске
Мы изготавливаем дипломы любой профессии по приятным тарифам. Стараемся поддерживать для покупателей адекватную политику тарифов. Важно, чтобы дипломы были доступны для большого количества наших граждан.
Покупка диплома, подтверждающего окончание института, – это грамотное решение. Заказать диплом любого университета: [url=http://kupitediplom0029.ru/kupit-diplom-o-srednem-spetsialnom-obrazovanii-goznaka-2/]kupitediplom0029.ru/kupit-diplom-o-srednem-spetsialnom-obrazovanii-goznaka-2/[/url]
1 win md 1win5004.ru .
служба поддержки мостбет номер телефона служба поддержки мостбет номер телефона .
A home window system a/c makes use of 500 to 1440 watts, while a 2.5-ton main system
uses concerning 3500 watts.
мостбет официальный сайт http://hiend.borda.ru/?1-16-0-00000260-000-0-0 .
Clom Fast Pharm: clomid no prescription – Clom Fast Pharm
zithromax price canada: where can i purchase zithromax online – zithromax 500 without prescription
https://zithpharmonline.shop/# ZithPharmOnline
Задумываетесь где тренироваться воплощать стиль кумиры K-pop? K-pop культура быстро распространяется в России. Московские студии обеспечивают множество мест, где профессиональные хореографы помогут вам овладеть этот зажигательный стиль танца. Нахождение правильного центра может оказаться непростой задачей. Полный рейтинг лучших K-pop танцевальных школ Москвы на 2025 год можно найти на tenchat.ru. Этот информационный ресурс регулярно освещает изменения о школах. При выборе школы учитывайте свой исходную подготовку. Немало танцоров отмечают, что занятия K-pop танцами помогают не только научиться танцевать, но и повысить уверенность. Занятия в группе помогают поддерживать мотивацию и быстрее прогрессировать в освоении новых элементов.
1вин сайт http://www.1win6005.ru .
дайвинг в хургаде
lisinopril 2.5 tablet: Lisin Express – Lisin Express
балансировка карданных валов балансировка карданных валов .
мостбет мобильная версия скачать https://mostbet6030.ru .
https://law5.ru/
Maintain the filters rinsed with warm soapy water in a sink, Allow them dry off and after that fit them back
in the system.
садко дайвинг в хургаде
дешевый интернет новосибирск
domashij-internet-novosibirsk002.ru
какие провайдеры на адресе в новосибирске
Приобрести диплом института!
Мы можем предложить дипломы любой профессии по выгодным ценам— diplomj-irkutsk.ru/kupit-attestat-za-11-klassov-v-moskve-bistro-i-nadezhno/
Горкинское кладбище https://gorkinskoe.ru одно из старейших в Видном. Подробная информация: адрес, как доехать, порядок захоронений, наличие участков, памятники, услуги по уходу.
case de ?nchiriat l?ng? bucure?ti case de ?nchiriat l?ng? bucure?ti .
Each brand will certainly have varying EER degree rankings, so examine the
producer’s specifications.
Горкинское кладбище https://gorkinskoe.ru одно из старейших в Видном. Подробная информация: адрес, как доехать, порядок захоронений, наличие участков, памятники, услуги по уходу.
mitolyn is a natural dietary supplement specifically outlined to enhance metabolism and support weight loss. Its potent blend of ingredients works to increase energy levels, promote fat burning
Где заказать диплом по необходимой специальности?
Мы предлагаембыстро и выгодно купить диплом, который выполняется на оригинальной бумаге и заверен печатями, штампами, подписями. Данный документ способен пройти лубую проверку, даже при помощи профессиональных приборов. Решите свои задачи быстро и просто с нашим сервисом. Купить диплом о высшем образовании! mamuli.club/forum/topic/32321
aqua sculpt is a groundbreaking weight management supplement designed to support your journey by naturally enhancing metabolism
купить оружейный сейф цена
1 вин http://www.1win6005.ru .
mostbet chrono https://severussnape.borda.ru/?1-4-0-00000505-000-0-0-1743260265/ .
AmOnlinePharm can i buy amoxicillin over the counter AmOnlinePharm
Где приобрести диплом специалиста?
Наши специалисты предлагают выгодно и быстро купить диплом, который выполнен на бланке ГОЗНАКа и заверен мокрыми печатями, водяными знаками, подписями официальных лиц. Диплом пройдет лубую проверку, даже при использовании специальных приборов. Решайте свои задачи быстро с нашим сервисом.
Купить диплом любого ВУЗа vacshidiplom.com/kupit-diplom-bakalavra-16/
Clom Fast Pharm: can i get generic clomid no prescription – where to get clomid without rx
кайт египет Кайт станции Египта предлагают полный спектр услуг для кайтсерферов, включая прокат оборудования, обучение, хранение и ремонт.
производство карданных валов производство карданных валов .
провайдеры по адресу
domashij-internet-novosibirsk003.ru
провайдеры в новосибирске по адресу проверить
Всё о Казахстане https://tr-kazakhstan.kz история, культура, города, традиции, природа и достопримечательности. Полезная информация для туристов, жителей и тех, кто хочет узнать страну ближе.
where to get amoxicillin over the counter: AmOnlinePharm – amoxicillin script
мостбет вход https://severussnape.borda.ru/?1-4-0-00000505-000-0-0-1743260265/ .
Hi there colleagues, how is the whole thing, and what you want to say concerning this paragraph, in my view its truly remarkable in favor of me.
https://tennis-club.kiev.ua/sklo-far-yak-pravylno-doglyadaty-shchob-ne-potrebuvavsya-zamina
Всё о Казахстане https://tr-kazakhstan.kz история, культура, города, традиции, природа и достопримечательности. Полезная информация для туристов, жителей и тех, кто хочет узнать страну ближе.
rent a new house rent a new house .
cost generic clomid pill: Clom Fast Pharm – where can i get clomid prices
can i buy amoxicillin online: AmOnlinePharm – AmOnlinePharm
buy prednisone online no script prednisone 20mg online without prescription Pred Pharm Net
Всё о кладбищах Видного https://bitcevskoe.ru/ Битцевское, Дрожжинское, Спасское, Жабкинское. Официальная информация, участки, услуги, порядок оформления документов, схема проезда.
проверить интернет по адресу
domashij-internet-ekaterinburg002.ru
интернет провайдеры екатеринбург по адресу
Modify your machine into a treasure with our skilled auto customization options. At Bergin Auto Works, we are proficient in supplying first-class upgrades that reflect your individual taste. From stylish car exteriors to robust performance boosts, our staff provides remarkable craftsmanship. Discover our webpage https://berginautobody.com/ to find out about our options and commence your machine’s metamorphosis right away.
хранение вещей аренда бокса хранение вещей аренда бокса .
zithromax online no prescription: ZithPharmOnline – ZithPharmOnline
Calibry Casino calibri casino app ru современное онлайн-казино с лицензией, щедрой бонусной системой и широким выбором игр. Участвуй в акциях, получай кэшбэк и выигрывай реальные деньги!
dragon money vegas dragon money vegas .
Calibry Casino calibri-casino-app.ru/ современное онлайн-казино с лицензией, щедрой бонусной системой и широким выбором игр. Участвуй в акциях, получай кэшбэк и выигрывай реальные деньги!
nervecalm s a high-quality nutritional supplement crafted to promote nerve wellness, ease chronic discomfort, and boost everyday vitality.
Clom Fast Pharm: Clom Fast Pharm – can i get generic clomid without prescription
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me?
prodentim a groundbreaking probiotic supplement uniquely designed to support oral health and promote robust gums and teeth.
1win kg https://www.cah.forum24.ru/?1-13-0-00001695-000-0-0-1743258917 .
сейфы простые
Clom Fast Pharm Clom Fast Pharm Clom Fast Pharm
https://amonlinepharm.shop/# AmOnlinePharm
1 вин официальный сайт вход http://cah.forum24.ru/?1-13-0-00001695-000-0-0-1743258917 .
провайдеры домашнего интернета екатеринбург
domashij-internet-ekaterinburg003.ru
узнать интернет по адресу
1 ван вин http://1win6006.ru .
драгон мани регистрация драгон мани регистрация .
Pretty! This was a really wonderful post. Thank you for providing these details.
сайт vovan casino
dragon money casino играть dragon money casino играть .
Clom Fast Pharm: Clom Fast Pharm – can i order generic clomid online
1win.com http://1win5010.ru/ .
amoxicillin medicine over the counter: AmOnlinePharm – amoxicillin over the counter in canada
https://zithpharmonline.shop/# zithromax 1000 mg pills
1 win casino 1win1001.top .
Купить диплом университета по невысокой цене возможно, обратившись к надежной специализированной фирме. Заказать документ о получении высшего образования можно у нас. diplomh-40.ru/kupite-diplom-zaregistrirovannij-v-reestre-bistro-3
Заказать диплом о высшем образовании!
Мы готовы предложить документы университетов, расположенных в любом регионе РФ. Дипломы и аттестаты делаются на бумаге высшего качества: workompass.com/employer/aurus-diploms
Lisin Express: Lisin Express – Lisin Express
Купить диплом любого ВУЗа!
Приобрести диплом университета по невысокой стоимости можно, обращаясь к надежной специализированной фирме. Приобрести диплом: diplomt-v-samare.ru/kupit-diplom-attestat-s-garantiej-provodka-v-reestr
провайдеры интернета в казани
domashij-internet-kazan002.ru
интернет домашний казань
хранилище в москве для вещей хранилище в москве для вещей .
Имморталы CS2 cs-open-case.ru/ редкие скины, которые выделят тебя в матче. Торгуй, покупай, продавай топовые предметы с моментальной доставкой в инвентарь. Лучшие цены и безопасные сделки!
Топ-дроп CS2 open case cs2 уже здесь! Самые редкие скины, ножи и эксклюзивы, которые действительно выпадают. Лучшие кейсы, обновления коллекций и советы для удачного открытия.
Премиум скины для CS2 case cs open выделяйся в каждом раунде! Редкое оружие, эксклюзивные коллекции, эффектные раскраски и ножи. Только топовые предметы с мгновенной доставкой в Steam.
Имморталы CS2 https://cs-open-case.ru редкие скины, которые выделят тебя в матче. Торгуй, покупай, продавай топовые предметы с моментальной доставкой в инвентарь. Лучшие цены и безопасные сделки!
Топ-дроп CS2 https://open-case-cs2.ru/ уже здесь! Самые редкие скины, ножи и эксклюзивы, которые действительно выпадают. Лучшие кейсы, обновления коллекций и советы для удачного открытия.
Премиум скины для CS2 case-cs-open.ru/ выделяйся в каждом раунде! Редкое оружие, эксклюзивные коллекции, эффектные раскраски и ножи. Только топовые предметы с мгновенной доставкой в Steam.
https://oxys-crema.net/
1win прямой эфир 1win прямой эфир .
sweet bonanza giris: sweet bonanza giris – sweet bonanza giris sweetbonanza1st.shop
1win kg скачать https://www.cah.forum24.ru/?1-13-0-00001678-000-0-0 .
casino siteleri 2025 deneme bonusu veren siteler 30 tl bonus veren bahis siteleri casinositeleri1st.shop
1win méxico http://1win1001.top .
сейф в офис
slot bonus: casibom giris – iddaa siteleri casibom1st.com
какие провайдеры на адресе в казани
domashij-internet-kazan003.ru
провайдеры интернета в казани по адресу
Быстрый и удобный фундаментные работы калькулятор рассчитайте стоимость и объем работ за пару минут. Онлайн-калькулятор поможет спланировать бюджет, сравнить варианты и избежать лишних затрат.
Мамоновское кладбище https://mamonovskoe.ru справочная информация, адрес, график работы, участки, ритуальные услуги и памятники. Всё, что нужно знать, собрано на одном сайте.
новости краснодара и краснодарского krasnodar-news35.ru
Мамоновское кладбище https://mamonovskoe.ru справочная информация, адрес, график работы, участки, ритуальные услуги и памятники. Всё, что нужно знать, собрано на одном сайте.
You can usually expect to pay around ₤ 2.50 per square metre
for this kind of job.
1win home http://1win14.com.ng/ .
deneme bonusu veren siteler en gГјvenilir online casino guvenilir casino siteleri casinositeleri1st.shop
1win казино http://1win6008.ru .
лучший интернет провайдер нижний новгород
domashij-internet-nizhnij-novgorod001.ru
домашний интернет нижний новгород
мостбет официальный сайт [url=mostbet6012.ru]mostbet6012.ru[/url] .
casino en iyi siteler: deneme bonusu veren siteler – 100 tl deneme bonus veren bahis siteleri casinositeleri1st.com
Обеспечь анонимность с amneziavpn.xyz/. Защита трафика, собственный сервер, простая установка и отсутствие слежки. Отличный выбор для тех, кто ценит свободу в интернете.
mikro sluchatko nanosondy
1win sportsbook 1win sportsbook .
Ищете безопасный VPN? Попробуйте https://amneziavpn.org/ — open-source решение для анонимности и свободы в интернете. Полный контроль над соединением и личными данными.
en Г§ok kazandД±ran casino sitesi: casibom guncel adres – betboo plus casibom1st.com
Обеспечь анонимность с http://amneziavpn.xyz. Защита трафика, собственный сервер, простая установка и отсутствие слежки. Отличный выбор для тех, кто ценит свободу в интернете.
mikrosluchatko http://mikrosluchatko-cena.cz
bet bahis giriЕџ: casibom giris – bet siteler casibom1st.com
Register WhatsApp number for free
Ищете безопасный VPN? Попробуйте amnezia vpn настройка — open-source решение для анонимности и свободы в интернете. Полный контроль над соединением и личными данными.
подключить интернет тарифы нижний новгород
domashij-internet-nizhnij-novgorod002.ru
провайдеры по адресу
Где купить диплом по актуальной специальности?
Наши специалисты предлагаютвыгодно приобрести диплом, который выполнен на бланке ГОЗНАКа и заверен мокрыми печатями, водяными знаками, подписями официальных лиц. Наш документ пройдет любые проверки, даже с применением профессиональных приборов. Решите свои задачи максимально быстро с нашими дипломами. Заказать диплом любого ВУЗа! arzookanak5756.copiny.com/question/details/id/1068463
служба поддержки мостбет номер телефона http://mostbet6011.ru .
sweet bonanza siteleri: sweet bonanza oyna – sweet bonanza 1st sweetbonanza1st.shop
sweet bonanza demo sweet bonanza slot sweet bonanza oyna sweetbonanza1st.com
1win metode de plată https://1win5012.ru/ .
pin up azerbaijan pin up azerbaijan .
M4A4 Emperor https://get-skin-cs.ru/ эффектный скин в стиле королевской власти. Яркий синий фон, золотые детали и образ императора делают этот скин настоящим украшением инвентаря в CS2.
casino siteleri: deneme bonusu veren siteler – guvenilir casino siteleri casinositeleri1st.com
сайт 1win официальный сайт вход http://1win6043.ru/ .
Мы изготавливаем дипломы любой профессии по приятным ценам. Купить диплом техникума — kyc-diplom.com/diplom-tekhnikuma.html
Технологии свободы: marzban.click надёжный инструмент для приватности, скорости и доступа к любым сайтам. Быстро, безопасно, удобно — настрой за 5 минут.
1 вин войти https://1win6045.ru/ .
casino siteleri 2025 slot casino siteleri casino siteleri casinositeleri1st.shop
Hi there! If you’re reading this, chances are you’re looking for a way to boost your website’s visibility in Google. Let’s face it — navigating SEO can be daunting, especially with so many “miracle” solutions out there claiming guaranteed results that rarely materialize. That’s why I want to share my method with you. It’s not just another cookie-cutter service — it’s a custom-tailored plan designed to deliver real, measurable results.
I specialize in building tiered authority systems that combine strategic link layers. Think of it like constructing a strong foundation for your house. Without proper groundwork, progress collapses. My goal is to enhance your main website’s ranking power in a way that aligns with search engine algorithms and proves effective.
What Makes Me Different?
To be straightforward: I’ve been in the digital marketing field for years, and I’ve witnessed every trend — successful strategies and outright scams. I’ve worked with clients who poured resources on services that claimed foolproof results but caused ranking drops. That’s why I decided to do things differently.
I focus on high-quality, dofollow backlinks from reputable sources. Over 80% of Tier 1 links in my strategy are dofollow because they offer maximum SEO value. And here’s the clincher — you’ll get this premium service at a fraction of what others charge (costing just 200–350 USD). How does wasting money help? Invest wisely in something that guarantees progress.
My Unique Value Proposition
Premium Content Placement
I avoid low-quality directories. Nope. I carefully select only the top-tier platforms — sites boasting high trust flow (TF). These are the kinds of sites that elevate your domain’s credibility.
Unique, Handwritten Content
Let’s face it — spun or generic content sticks out like a sore thumb. It’s detrimental to your brand. That’s why every post I create is original, compelling, and tailored to your niche. Whether it’s for Web 2.0 properties, I guarantee Copyscape-passed content that blends seamlessly into your campaign. No shortcuts, no fluff — just high-quality writing that gets results.
Three-Layer Link Building Strategy
Here’s where things get interesting. My method doesn’t stop at Tier 1 by incorporating mid-level and foundational backlinks. This layered approach multiplies the impact of your core links, driving sustainable growth for your money site. Think of it like a snowball rolling downhill — it starts small but gains momentum.
Multi-Platform Authority Building
A natural profile requires eclectic sources, so I leverage multiple high-authority sources: Web 2.0 platforms, PDFs, Docs, social bookmarks, profiles. This isn’t about cheating algorithms; it’s about building something that lasts.
Full Transparency
When you work with me, you’ll know exactly what you’re getting. I provide a comprehensive breakdown, including login details for all Web 2.0 properties. Clear communication, no surprises. You’ll know exactly where your links are coming from and their role in your success.
Real-World Proof
A case study: A few years ago, I worked with a client who was struggling to gain traction despite prior investments. They’d tried various “experts”, but results were elusive. When they came to me, I analyzed their unique needs. A personalized approach was implemented. Within a few months, their traffic doubled, and they achieved measurable sales growth. That’s the kind of success I strive to deliver with every client.
Let’s build your path to the top Drop me a line today and turn search engines into your ally. ??
hidden-link placement in established content hubs e8f6cf7
1win uganda 1win1003.top .
#HeLLo#
Appreciating the dedication you put into your site and detailed information you provide. It’s nice to come across a blog every once in a while that isn’t the same unwanted rehashed information. Fantastic read! I’ve bookmarked your site and I’m including your RSS feeds to my Google account.
cheap VoIP numbers
https://usmexpharm.shop/# reputable mexican pharmacies online
#HeLLo#
Hi, its pleasant piece of writing regarding media print, we all be familiar with media is a impressive source of facts.
Brazil Virtual Phone Numbers
I don’t think the title of your article matches the content lol. Just kidding, mainly because I had some doubts after reading the article.
мосбет mostbet6034.ru .
Us Mex Pharm: USMexPharm – Us Mex Pharm
equilibrado estatico
Equipos de calibración: esencial para el operación fluido y óptimo de las máquinas.
En el ámbito de la ciencia actual, donde la eficiencia y la seguridad del sistema son de gran importancia, los equipos de equilibrado cumplen un función esencial. Estos dispositivos dedicados están desarrollados para balancear y fijar componentes dinámicas, ya sea en maquinaria de fábrica, transportes de desplazamiento o incluso en electrodomésticos hogareños.
Para los profesionales en conservación de aparatos y los ingenieros, trabajar con aparatos de calibración es fundamental para proteger el funcionamiento uniforme y estable de cualquier sistema móvil. Gracias a estas soluciones tecnológicas modernas, es posible disminuir significativamente las sacudidas, el ruido y la esfuerzo sobre los cojinetes, prolongando la longevidad de partes importantes.
También relevante es el papel que tienen los dispositivos de calibración en la servicio al cliente. El apoyo especializado y el reparación constante empleando estos dispositivos facilitan dar soluciones de óptima estándar, aumentando la contento de los consumidores.
Para los propietarios de emprendimientos, la contribución en unidades de equilibrado y detectores puede ser fundamental para mejorar la productividad y desempeño de sus sistemas. Esto es especialmente trascendental para los emprendedores que gestionan modestas y intermedias emprendimientos, donde cada aspecto vale.
Además, los sistemas de calibración tienen una extensa uso en el sector de la fiabilidad y el monitoreo de estándar. Facilitan encontrar eventuales fallos, evitando intervenciones onerosas y averías a los sistemas. Más aún, los resultados obtenidos de estos dispositivos pueden emplearse para optimizar procesos y aumentar la presencia en sistemas de consulta.
Las sectores de uso de los dispositivos de calibración abarcan numerosas ramas, desde la producción de transporte personal hasta el supervisión de la naturaleza. No influye si se refiere de extensas manufacturas industriales o reducidos establecimientos caseros, los aparatos de calibración son esenciales para proteger un operación eficiente y sin paradas.
https://usmexpharm.shop/# Us Mex Pharm
Нужно создание или разработка студия по продвижению сайтов: адаптивный дизайн, SEO-продвижение, техническая поддержка. Эффективное ключевая фраза для вашего бизнеса — привлечение клиентов и рост прибыли.
Обзор онлайн-казино Shot https://shot-casino-app.ru плюсы и минусы, проверка лицензии, акции и фриспины. Рассказываем, стоит ли играть, как получить бонусы и выводить выигрыши без проблем.
Shot Casino shot-casino-online.ru/ новое онлайн-казино с лицензией, защитой данных и большим выбором игр. В обзоре: безопасность, отзывы игроков, бонусы и выплаты. Надёжная площадка для вашего азарта.
Онлайн-казино Calibry calibri-casino-online.ru/ новое игровое пространство с лицензией, щедрыми бонусами и широким выбором слотов. Читайте обзор: особенности платформы, условия игры, отзывы и выплаты.
Нужно создание или разработка разработка сайтов в Москве: адаптивный дизайн, SEO-продвижение, техническая поддержка. Эффективное ключевая фраза для вашего бизнеса — привлечение клиентов и рост прибыли.
Обзор онлайн-казино Shot shot-casino-app.ru/ плюсы и минусы, проверка лицензии, акции и фриспины. Рассказываем, стоит ли играть, как получить бонусы и выводить выигрыши без проблем.
mexican pharmacy: certified Mexican pharmacy – USMexPharm
Shot Casino https://shot-casino-online.ru новое онлайн-казино с лицензией, защитой данных и большим выбором игр. В обзоре: безопасность, отзывы игроков, бонусы и выплаты. Надёжная площадка для вашего азарта.
Онлайн-казино Calibry calibri-casino-online.ru/ новое игровое пространство с лицензией, щедрыми бонусами и широким выбором слотов. Читайте обзор: особенности платформы, условия игры, отзывы и выплаты.
игра 1вин https://www.1win6046.ru .
USMexPharm UsMex Pharm USMexPharm
Где купить диплом специалиста?
Мы готовы предложить дипломы любой профессии по выгодным ценам. Для нас важно, чтобы документы были доступны для большинства граждан. Купить диплом любого института diplomj-irkutsk.ru/diplomi-s-reestrom-vash-put-k-uspexu/
UsMex Pharm: UsMex Pharm – usa mexico pharmacy
Заказать диплом возможно через официальный портал компании. g95334gq.beget.tech/2025/04/08/diplom-bez-posescheniya-ucheby.html
Us Mex Pharm: certified Mexican pharmacy – USMexPharm
I like reading through a post that will make men and women think. Also, thank you for permitting me to comment.
mostbet casino https://www.mostbet6035.ru .
https://usmexpharm.shop/# Us Mex Pharm
Приобрести диплом университета. Покупка официального диплома через проверенную и надежную фирму дарит немало достоинств. Это решение дает возможность сэкономить как личное время, так и серьезные финансовые средства. behealthy.maxbb.ru/posting.php?mode=post&f=8
UsMex Pharm: certified Mexican pharmacy – USMexPharm
1win live http://www.1win6046.ru .
подключить домашний интернет в челябинске
domashij-internet-chelyabinsk001.ru
подключить домашний интернет в челябинске
1win бк 1win бк .
1вин официальный мобильная https://1win6045.ru .
Если вас интересует оклейка Mercedes-AMG G 63 обращайтесь к профессионалам! Наша компания предлагает премиальную оклейку защитными и декоративными плёнками, идеально подчёркивающими характер вашего автомобиля. Глянцевая или матовая текстура – выберите свой стиль и обеспечьте кузову надёжную защиту от сколов, царапин и выгорания.
Нужен бесплатный аккаунт? dzen.ru/freesteamaccount Узнайте, где можно получить рабочие логины с играми, как не попасть на фейк и на что обратить внимание при использовании таких аккаунтов.
Онлайн-казино Aura aura-casino-apk лицензия, быстрые выплаты, слоты от топ-провайдеров и щедрые бонусы. Подробный обзор платформы: интерфейс, регистрация, акции, безопасность и отзывы игроков.
USMexPharm: certified Mexican pharmacy – Mexican pharmacy ship to USA
Начните с Aura Casino https://aura-casino-bonus.ru удобное онлайн-казино с простым интерфейсом, стартовыми бонусами и быстрой регистрацией. Рассказываем, как получить фриспины и не потеряться в слотах.
Нужен бесплатный аккаунт? пустые аккаунты стим бесплатно Узнайте, где можно получить рабочие логины с играми, как не попасть на фейк и на что обратить внимание при использовании таких аккаунтов.
Онлайн-казино Aura https://aura-casino-apk.ru/ лицензия, быстрые выплаты, слоты от топ-провайдеров и щедрые бонусы. Подробный обзор платформы: интерфейс, регистрация, акции, безопасность и отзывы игроков.
Онлайн-казино Calibry https://calibri-casino-play.ru бонусы без депозита, быстрые выводы и лицензированный софт. В обзоре: как начать играть, получить фриспины, использовать акции и избежать рисков.
мостбет скачать мостбет скачать .
Начните с Aura Casino aura-casino-bonus.ru/ удобное онлайн-казино с простым интерфейсом, стартовыми бонусами и быстрой регистрацией. Рассказываем, как получить фриспины и не потеряться в слотах.
Онлайн-казино Calibry https://calibri-casino-play.ru/ бонусы без депозита, быстрые выводы и лицензированный софт. В обзоре: как начать играть, получить фриспины, использовать акции и избежать рисков.
Mexican pharmacy ship to USA: mexican pharmacy – Us Mex Pharm
mostbet промокод mostbet6035.ru .
подключить интернет челябинск
domashij-internet-chelyabinsk002.ru
интернет провайдеры челябинск
mexico drug stores pharmacies [url=http://usmexpharm.com/#]Us Mex Pharm[/url] UsMex Pharm
wan win https://1win6041.ru .
Обзор онлайн-казино Calibry https://calibri-casino-app.ru/ как получить бонус без депозита, запустить любимые слоты и вывести выигрыш. Надёжная площадка с лицензией и прозрачными условиями игры.
Играйте в казино Shot shot-casino-play.ru десятки провайдеров, ежедневные турниры и кэшбэк. В обзоре: лучшие слоты, лайв-игры, бонусные программы и преимущества платформы.
Заказать диплом о высшем образовании!
Мы можем предложить документы любых учебных заведений, расположенных на территории всей Российской Федерации.
diplomist.com/kupit-diplom-moskva-s-zaneseniem-v-reestr-2/
Обзор онлайн-казино Calibry calibri casino app как получить бонус без депозита, запустить любимые слоты и вывести выигрыш. Надёжная площадка с лицензией и прозрачными условиями игры.
Aura Casino aura-casino-online.ru безопасная платформа с лицензией, SSL-защитой и проверенной репутацией. В обзоре: честность выплат, работа службы поддержки и реальные отзывы игроков.
Играйте в казино Shot https://shot-casino-play.ru десятки провайдеров, ежедневные турниры и кэшбэк. В обзоре: лучшие слоты, лайв-игры, бонусные программы и преимущества платформы.
Aura Casino aura-casino-online.ru безопасная платформа с лицензией, SSL-защитой и проверенной репутацией. В обзоре: честность выплат, работа службы поддержки и реальные отзывы игроков.
Обзор Aura Casino https://aura-casino-play.ru/ всё о щедрых бонусах, фриспинах, кэшбэке и акциях. Расскажем, как зарегистрироваться, начать игру и получить максимум от каждого депозита.
http://usmexpharm.com/# Mexican pharmacy ship to USA
Обзор Aura Casino aura-casino-play всё о щедрых бонусах, фриспинах, кэшбэке и акциях. Расскажем, как зарегистрироваться, начать игру и получить максимум от каждого депозита.
1 вин войти 1win6047.ru .
казино онлайн kg казино онлайн kg .
1vin pro https://1win6045.ru .
1win https://www.1win5014.ru .
usa mexico pharmacy: mexican rx online – Us Mex Pharm
подключить интернет в квартиру челябинск
domashij-internet-chelyabinsk003.ru
провайдеры домашнего интернета челябинск
usa mexico pharmacy: UsMex Pharm – mexican pharmacy
mexican pharmacy: USMexPharm – Us Mex Pharm
стоматология митино стоматология митино .
Мы изготавливаем дипломы любой профессии по приятным ценам. Купить диплом строительного института — kyc-diplom.com/diplom-articles/kupit-diplom-stroitelnogo-instituta.html
When I originally commented I seem to have clicked on the -Notify me when new comments are added- checkbox and from now on whenever a comment is added I get 4 emails with the exact same comment. Is there an easy method you can remove me from that service? Appreciate it.
Доброго времени суток!
Для некоторых людей, заказать диплом о высшем образовании – это острая необходимость, удачный шанс получить достойную работу. Однако для кого-то – это понятное желание не терять множество времени на учебу в институте. Что бы ни толкнуло вас на это решение, наша компания готова помочь вам. Максимально быстро, качественно и выгодно изготовим документ нового или старого образца на государственных бланках с реальными печатями.
Ключевая причина, почему многие люди прибегают к покупке документов, – получить хорошую работу. Предположим, знания позволяют специалисту устроиться на желаемую работу, однако подтверждения квалификации не имеется. В том случае если для работодателя важно наличие “корочки”, риск потерять место работы достаточно высокий.
Заказать документ о получении высшего образования вы имеете возможность у нас в столице. Мы оказываем услуги по продаже документов об окончании любых университетов России. Вы сможете получить необходимый диплом по любым специальностям, включая документы Советского Союза. Гарантируем, что при проверке документов работодателем, каких-либо подозрений не появится.
Факторов, которые вынуждают приобрести диплом ВУЗа немало. Кому-то прямо сейчас нужна работа, и нужно произвести впечатление на начальника при собеседовании. Другие планируют устроиться в престижную компанию, для того, чтобы повысить свой статус в обществе и в будущем начать собственное дело. Чтобы не терять впустую годы жизни, а сразу начинать удачную карьеру, применяя имеющиеся знания, можно приобрести диплом в онлайне. Вы сможете стать полезным в социуме, обретете финансовую стабильность в кратчайший срок- купить диплом техникума
Где заказать диплом по актуальной специальности?
Наши специалисты предлагают выгодно приобрести диплом, который выполнен на оригинальном бланке и заверен печатями, штампами, подписями. Диплом способен пройти любые проверки, даже при помощи профессиональных приборов. Достигайте цели быстро и просто с нашей компанией.
Приобрести диплом о высшем образовании damdiplomisa.com/kupit-diplom-parikmaxera-10/
Обзор казино Shot shot casino bonus лицензия, защита данных, честная игра и проверенные провайдеры. Узнайте, как работает система вывода, поддержка и что говорят реальные пользователи.
Онлайн-казино Calibry https://calibri-casino-apk.ru бонус без депозита, фриспины, турниры и выплаты без задержек. Рассказываем, как начать играть, какие игры выбрать и стоит ли доверять платформе.
Calibry Casino calibri-casino-bonus.ru лицензированное онлайн-казино с бонусами, быстрым выводом и большим выбором игр. В обзоре: регистрация, акции, безопасность, отзывы игроков и советы новичкам.
Обзор казино Shot shot casino bonus лицензия, защита данных, честная игра и проверенные провайдеры. Узнайте, как работает система вывода, поддержка и что говорят реальные пользователи.
Онлайн-казино Aura https://aura-casino-app.ru лицензия, бонус без депозита, фриспины за регистрацию и моментальный вывод. Всё о казино Aura в одном обзоре — играйте безопасно и с выгодой.
Онлайн-казино Calibry calibri casino apk бонус без депозита, фриспины, турниры и выплаты без задержек. Рассказываем, как начать играть, какие игры выбрать и стоит ли доверять платформе.
Calibry Casino calibri casino bonus лицензированное онлайн-казино с бонусами, быстрым выводом и большим выбором игр. В обзоре: регистрация, акции, безопасность, отзывы игроков и советы новичкам.
PORTAL DIGITAL PAFI: Kontribusi Utama Farmasi di Zaman Digital
Profil Singkat PAFI
Sejak Indonesia merdeka, para Tenaga Kefarmasian turut berperan aktif dalam kemajuan kesehatan bangsa. Didirikannya PAFI menjadi tonggak penting sebagai asosiasi di bidang farmasi. Berlandaskan Pancasila, PAFI bersumpah untuk:
• Mengembangkan kualitas kesehatan publik
• Memodernisasi kefarmasian nasional
• Menunjang kesejahteraan anggota
Sistem Digital PAFI: Solusi Digital untuk Farmasi Modern
Menjawab kebutuhan digital, PAFI memperkenalkan WEB PAFI Terintegrasi – solusi canggih yang mendukung profesi kefarmasian melalui:
? Update Terbaru – Akses regulasi kesehatan, temuan terbaru, dan peluang karir
? Pengembangan Kompetensi – Layanan pelatihan dan sertifikasi daring
? Komunitas Praktisi – Sarana kerjasama se-Indonesia
Inovasi teknologi ini memaksimalkan sumbangsih PAFI dalam meningkatkan sistem kesehatan melalui adaptasi perkembangan teknologi.
Peluang Dunia Farmasi Modern
Hadirnya platform digital PAFI menjadi bukti perubahan sistem dalam bidang apoteker. Dengan konsisten memutakhirkan fitur dan layanan, PAFI berkomitmen untuk:
• Memacu terobosan dalam farmasi
• Meningkatkan kualitas profesi
• Mempermudah fasilitas kesehatan untuk rakyat
Kesimpulan
PAFI dengan adanya platform digital ini terus menjadi pionir dalam menjembatani inovasi digital dengan pekerjaan apoteker. Program ini tidak hanya mengokohkan posisi tenaga kefarmasian, tetapi juga berperan aktif bagi peningkatan kesehatan nasional pada zaman teknologi.
Онлайн-казино Aura aura casino app лицензия, бонус без депозита, фриспины за регистрацию и моментальный вывод. Всё о казино Aura в одном обзоре — играйте безопасно и с выгодой.
провайдеры интернета в красноярске по адресу проверить
domashij-internet-krasnoyarsk001.ru
провайдеры по адресу дома
1win.pro 1win5014.ru .
1 win официальный сайт вход http://1win7011.ru/ .
В Сочи теперь есть возможность найти свою любовь на новом сайте знакомств! Здесь вас ожидают привлекательные девушки, с которыми можно будет не только общаться, но и встретиться в реальной жизни. Не откладывайте свое счастье на завтра, заходите и знакомьтесь: сочи проститутка
1win. 1win. .
купить диплом высшего образования в омске
WEB PAFI TERINTEGRASI: Fungsi Penting Farmasi di Zaman Digital
Sekilas Tentang PAFI
Sejak Indonesia merdeka, para Ahli Farmasi memberikan andil dalam pembangunan kesehatan nasional. Berdirinya organisasi profesi farmasi ini menjadi momen bersejarah sebagai forum ahli di bidang farmasi. Berlandaskan Pancasila, PAFI bersumpah untuk:
• Mengembangkan derajat kesehatan masyarakat
• Mengembangkan kefarmasian nasional
• Meningkatkan kualitas hidup anggota
Sistem Digital PAFI: Solusi Digital untuk Kefarmasian Masa Kini
Menghadapi tantangan era digital, PAFI meluncurkan sistem terintegrasi ini – terobosan teknologi yang menunjang profesi kefarmasian melalui:
? Informasi Terkini – Ketersediaan regulasi kesehatan, perkembangan ilmiah, dan peluang karir
? Pengembangan Kompetensi – Fasilitas kursus online bersertifikat
? Jaringan Ahli – Sarana kerjasama nasional
Sistem digital ini memperkuat kontribusi PAFI dalam memajukan pelayanan kesehatan melalui adaptasi perkembangan teknologi.
Tantangan Farmasi Digital
Hadirnya WEB PAFI Terintegrasi menjadi bukti revolusi teknologi dalam profesi farmasi. Dengan terus mengembangkan kapabilitas sistem, PAFI berjanji untuk:
• Mendorong terobosan dalam farmasi
• Meningkatkan kriteria keahlian
• Meningkatkan fasilitas kesehatan untuk rakyat
Penutup
PAFI dengan adanya platform digital ini terus menjadi pionir dalam menghubungkan kemajuan teknologi dengan dunia kefarmasian. Program ini bukan sekadar mengokohkan posisi apoteker, tetapi juga memberikan sumbangsih konkret bagi pembangunan kesehatan di Indonesia pada zaman teknologi.
https://usmexpharm.com/# Mexican pharmacy ship to USA
mexican pharmacy: certified Mexican pharmacy – mexican pharmacy
сайт стоматологии москва сайт стоматологии москва .
Автоперевозки из Китая по РФ ved-china.ru/ быстрая и выгодная доставка грузов напрямую до вашего склада. Консолидация, растаможка, сопровождение и отслеживание на всех этапах.
Автоперевозки из Китая по РФ http://ved-china.ru быстрая и выгодная доставка грузов напрямую до вашего склада. Консолидация, растаможка, сопровождение и отслеживание на всех этапах.
срочные новости t.me/che_po_novosti/
Ищешь лучшие раскидки raskidki granat cs2 CS2 – Смоки, молотовы и флешки для всех карт — изучи тактики, прокачай игру и удиви соперников точными гранатами. Подборка эффективных раскидок!
Нужен надёжный хостинг? самый дешевый хостинг vps для сайтов, приложений и бизнес-задач. Гибкая настройка, SSD-накопители, стабильная работа 24/7. Выберите тариф под свои задачи и начните сегодня.
новости в мире новости сегодня
Ищешь лучшие раскидки https://raskidki-granat-cs2.ru CS2 – Смоки, молотовы и флешки для всех карт — изучи тактики, прокачай игру и удиви соперников точными гранатами. Подборка эффективных раскидок!
Нужен надёжный хостинг? nvme vps для сайтов, приложений и бизнес-задач. Гибкая настройка, SSD-накопители, стабильная работа 24/7. Выберите тариф под свои задачи и начните сегодня.
certified Mexican pharmacy: Us Mex Pharm – certified Mexican pharmacy
провайдеры интернета по адресу
domashij-internet-krasnoyarsk002.ru
интернет провайдеры по адресу красноярск
Настройка видеокамер — это важный этап в обеспечении эффективности системы наблюдения. Настройка видеокамер Иркутск выполняется с учетом всех особенностей территории. Профессиональный подход гарантирует корректную работу оборудования и удобство использования.
Купить диплом ВУЗа!
Мы предлагаем документы ВУЗов, расположенных в любом регионе России.
diplomidlarf.ru/kupit-diplom-s-zaneseniem-v-reestr-23/
1 вин. 1win7013.ru .
Мы можем предложить дипломы любой профессии по выгодным ценам. Мы предлагаем документы техникумов, расположенных в любом регионе Российской Федерации. Документы делаются на бумаге самого высокого качества. Это позволяет делать настоящие дипломы, не отличимые от оригинала. jobs.ria-kj.com/employer/archive-diploma
Мы можем предложить дипломы любой профессии по приятным тарифам.– diplomt-v-samare.ru/kupit-diplom-instituta-s-provodkoj-bistro-i-udobno/
USMexPharm: mexican pharmacy – USMexPharm
USMexPharm: pharmacies in mexico that ship to usa – USMexPharm
интернет по адресу
domashij-internet-krasnoyarsk003.ru
интернет провайдеры по адресу красноярск
Где приобрести диплом по необходимой специальности?
Мы предлагаем быстро и выгодно заказать диплом, который выполнен на оригинальном бланке и заверен мокрыми печатями, штампами, подписями. Данный диплом пройдет лубую проверку, даже при помощи специфических приборов. Решайте свои задачи быстро и просто с нашим сервисом.
Приобрести диплом о высшем образовании [url=http://rusd-diplomj.ru/kupit-diplom-v-spb-18/]rusd-diplomj.ru/kupit-diplom-v-spb-18/[/url]
cazinouri online moldova https://1win5015.ru/ .
https://usmexpharm.com/# Mexican pharmacy ship to USA
стоимость зубного протезирования стоимость зубного протезирования .
установка протеза зуба https://www.protezirovanie-zubov3.ru .
сколько стоят зубные протезы сколько стоят зубные протезы .
купить диплом колледжа в спб
wan win wan win .
I seriously love your blog.. Pleasant colors & theme. Did you develop this web site yourself? Please reply back as I’m looking to create my very own blog and would love to find out where you got this from or just what the theme is named. Thank you.
какие провайдеры на адресе в краснодаре
domashij-internet-krasnodar001.ru
интернет провайдеры краснодар по адресу
certified Mexican pharmacy: UsMex Pharm – usa mexico pharmacy
цена протезирование зубов цена протезирование зубов .
протезирование зуба сколько http://www.protezirovanie-zubov3.ru .
UsMex Pharm: usa mexico pharmacy – Mexican pharmacy ship to USA
провайдеры интернета в краснодаре по адресу
domashij-internet-krasnodar002.ru
узнать интернет по адресу
UsaIndiaPharm buy prescription drugs from india indian pharmacy
провайдер интернета по адресу краснодар
domashij-internet-krasnodar003.ru
какие провайдеры по адресу
UsaIndiaPharm: UsaIndiaPharm – mail order pharmacy india
хирург в митино платно хирург в митино платно .
Приобрести диплом университета!
Мы изготавливаем дипломы любой профессии по приятным ценам— diplomk-vo-vladivostoke.ru/diplom-stomatologa-kupit-tsena/
Мы изготавливаем дипломы любой профессии по приятным ценам. Стараемся поддерживать для заказчиков адекватную ценовую политику. Для нас очень важно, чтобы дипломы были доступными для подавляющей массы граждан.
Приобретение документа, который подтверждает окончание института, – это грамотное решение. Приобрести диплом ВУЗа: diplommy.ru/kupit-diplom-sredne-texnicheskoe-3/
india online pharmacy: UsaIndiaPharm – reputable indian pharmacies
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
UsaIndiaPharm: USA India Pharm – USA India Pharm
казино онлайн kg https://www.mostbet6036.ru .
интернет провайдеры самара по адресу
domashij-internet-samara003.ru
подключение интернета по адресу
Заказать диплом об образовании!
Мы предлагаем дипломы любых профессий по выгодным ценам— diplomskiy.com/kupit-diplom-o-visshem-obrazovanii-s-zaneseniem-v-reestr/
прокат авто адлер сочи аренда авто прокат машин сочи адлер
машина в аренду сочи на сутки аренда авто сочи цены 2025
аренда авто крым аренда авто в крыму без водителя цена
комплексная уборка спб https://cleaning-top24.ru
прокат адлере цена машина в аренду адлер на сутки недорого
машины в аренду в сочи недорого аренда машины в сочи посуточно без водителя
аренда машины крым сочи аренда авто недорого крым
online pharmacy india: buy prescription drugs from india – UsaIndiaPharm
нанять уборку квартиры клининговая служба
buy prescription drugs from india: reputable indian online pharmacy – USA India Pharm
какие провайдеры по адресу
domashij-internet-ufa001.ru
проверить провайдеров по адресу уфа
UsaIndiaPharm: UsaIndiaPharm – indian pharmacy paypal
https://usaindiapharm.com/# USA India Pharm
1vin kg https://1win7002.ru/ .
Spot on with this write-up, I truly believe this web site needs a great deal more attention. I’ll probably be returning to read more, thanks for the advice!
aviator mostbet mostbet5002.ru .
Заказать диплом университета по невысокой стоимости возможно, обращаясь к проверенной специализированной фирме. Купить документ о получении высшего образования можно в нашей компании в Москве. vuz-diplom.ru/kupit-diplom-o-visshem-obrazovanii-reestr-15
промокод в 1вин казино [url=http://1win10082.ru/]промокод в 1вин казино[/url] .
As the admin of this website is working, no doubt very quickly it will be renowned, due to its feature contents.
Gama Casino
склады хранения склады хранения .
таможенно брокерские услуги таможенно брокерские услуги .
производитель рулонных штор http://rulonnye-shtory-s-elektroprivodom10.ru/ .
брокеры таможенное оформление брокеры таможенное оформление .
1вин бонусы http://1win5067.ru .
рулонные шторы в москве https://www.rulonnye-shtory-s-elektroprivodom50.ru .
стоимость таможенного брокера стоимость таможенного брокера .
заказать рулонные шторы в москве заказать рулонные шторы в москве .
Заказать диплом любого университета!
Мы предлагаемвыгодно и быстро заказать диплом, который выполняется на бланке ГОЗНАКа и заверен печатями, водяными знаками, подписями должностных лиц. Наш диплом способен пройти лубую проверку, даже с использованием специально предназначенного оборудования. Решите свои задачи быстро и просто с нашим сервисом- figarohair.ru/conf/viewtopic.phpf=11&t=14394&sid=51c658e18e76a55cefe74ec290ef74fd
1 win бк [url=https://1win10084.ru]https://1win10084.ru[/url] .